►
From YouTube: IETF103-IPWAVE-20181106-1120
Description
IPWAVE meeting session at IETF103
2018/11/06 1120
https://datatracker.ietf.org/meeting/103/proceedings/
A
B
B
C
C
So
this
is
the
agenda
for
today's
session.
We'll
do
some
initiative
stuff
at
the
beginning
and
then
we'll
focus
into
them
into
working
with
documents,
the
one
about
ipv6
over
dot,
11
ocv
and
then
the
Primus
teaming
and
use
cases
document
and
then
time
allowing
we
will
have
a
short
presentation
and
neighbor
discovery
for
ipv6
and
another
one
on
TLS
using
80s.
But
this
is
time
permitting
so
on.
B
This
was
posted
to
the
mail
list
a
while
ago.
We
received
it
on
the
3rd
of
September.
They
just
want
to
make
us
aware
of
this
work
and
if
we
have
anything
to
say
about
it,
they'd
love
for
to
hear
about
it,
but
basically
they're
calling
for
volunteers
to
participate
in
this
focus
group.
If
you're
interested
you
don't
need
to
come
through
us,
just
talk
to
the
ITU
directly
focus
groups,
don't
have
the
same
formal
membership
requirements
as
some
other
ITU
activities.
B
C
So
short
working
with
status
update,
so
we
have
you
know
two
documents
in
working
group
process,
the
one
the
first
one
isn't:
the
transmission
of
ipv6
over
all
the
yield
2.11
of
seaweed.
This
document
has
been
stuck
for
a
while
due
to
some
six-month
trace
issues.
Concerns
will
see
just
after
this
presentation
from
the
authors
and
then
we
will
discuss
how
to
move
forward
on
this
document,
and
then
we
have
another
document.
C
That
is
the
promise
teaming
and
use
cases
document
that
has
been
through
some
reviews,
but
we
still
need
some
some
additional
reviews
to
to
make
this
document
move
to
the
next
stage.
We
will
discuss
that
later
as
well,
so
these
the
status
that
you
can
see
we
are
late
on
on
the
original
on
the
original
deadlines.
We
are
very
much
aware
of
that.
We
will
we'll
see
how
to
actually
speed
up
things
during
the
meeting.
C
We
believe
that
there
are
things
that
are
still
to
be
done
and
we
are
discussing
some
some
ways
of
approaching
this
or
addressing
this,
maybe
adding
some
new
litter
may
may
help,
but
is
still
under
discussion,
and
but
we
believe
that
document
is
not
ready
yet
and
we
will
need
to
do
some
work
and
then
submit
to
the
exhibit,
but
not
before
the
six-month
basically
agrees
with
the
document.
As
stated
in
our
charter
that
the
six-month
has
to
review
the
document
that
we
produced.
C
These
are
the
first
one
on
the
second
one
and
the
survey
Pro
and
statement
use
cases
document.
We
got
some
preview
since
last
ITF
million-
that's
very
good
because
we
managed
to
get
something.
That
is
a
good
starting
point,
as
actually
some
other
reviewers
summation,
but
we
need.
We
do
need
additional
reviews.
C
I
mean
this
is
starting
point,
but
we
need
more
mature
reviews
on
this
iteration,
not
only
to
improve
the
quality
of
the
document
to
a
level
that
is
good
enough
to
for
publication,
but
also
to
to
provide
some
proof
that
the
working
room
has
energy
to
do
additional
stuff,
because
otherwise
there
is
no
point
in
having
a
praana
statement
document.
If
there
is
no
problem,
then
to
be
solve,
so
we
knew
we
really
need
at
least
two
additional
detail
reviews.
C
So
it's
not
about
typos
editorial
kind
of
review,
but
really
on
the
on
the
on
the
content
of
the
document
before
ITF
104,
and
we
need
a
new
version
of
the
document
before
the
meeting
and
by
before
the
meeting.
I
don't
mean
two
days
before
the
submission
deadline,
but
at
least
one
full
iteration
before
so.
Basically,
two
additional
versions
before
idea,
104,
otherwise
I
guess
we
have
been
waiting
for
quite
a
long
time,
so
we
will
be
may
be
forced
to
drop
the
document.
D
D
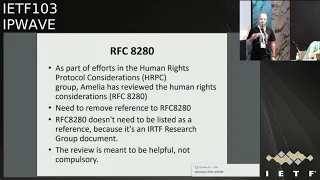
So
as
part
of
efforts
of
the
human
right
motor
consideration.
Amelia
has
reviewed
the
human
rights
consideration
and
suggested
to
remove
the
reference
to
that
RFC,
which
is
880
280,
because
it
doesn't
need
to
be
listed
in
the
reference
as
it's
an
IRC
F
research
group
of
documents
and
its
review
is
meant
to
be
helpful
and
in
no
case
a
mandatory.
D
So
the
main
comments
that
we
have
received
from
6-man
are
related
to
impart
to
the
neighbor
discovery.
So
the
main
neighbor
discovery
challenge
were
suggested
by
six
men
and
by
mr.
eric,
not
Marc.
They
were
addressed
in
version
26
and
30.
30
is
the
latest
version
that
we
have.
The
respective
change
are
listed
in
the
changelog.
D
So
if
you
want
to
have
more
says
about
all
the
chances
that
we
have
between
version
26
and
30,
you
can
just
compare
the
chance
rocks,
so
they
are
in
for
in
in
30
in
the
version
30
a
clarification
on
the
reliability
of
ND
/,
o
CB
+
/
8
result
of
11
links.
So
we
added
the
following
paragraph:
the
neighbor
discovery
protocol
is
used
over
eight
or
two
dots,
11,
o
CB
links.
The
reality
of
the
ND
protocol
over
80,
so
totally
philosophy
is
the
reliability
of
the
delivery
of
nd
multicast
messages.
D
E
If
you
go
back
to
the
site,
so
the
Eric
nutbag,
so
the
second
paragraph
is
a
sorry
second
sentence
is
actually
incorrect.
Two
things
is
incorrect.
One
is
Andy
uses
both
unicast
and
multicast.
2
nd
actually
sends
multiple
messages.
So
if
a
single
message,
it's
lost
its
you're,
not
dead
right.
So
the
wording
here
can
need
some
use
of
improvements.
E
The
thing
that's
important
to
keep
in
mind
for
OCD
is
that
unicast
is
as
unreliable
as
multicast,
which
is
different
than
Wi-Fi
right.
What
people
have
done
on
Wi-Fi
is
saying
not
ok
if
you
can
switch
to
unicast
or
better
off,
because
it's
more
reliable
we
have
ads,
but
but
it
might
make
sense
to
state
that
fact
that
OCB,
because
it
doesn't
have
acts
because
there
are
associations,
even
justices,
badass
multicast
or
is
good
whatever
that's
fine,
but
but
you
should
actually
fix
that
second
sentence,
because
I
think
it
confute
in
you
to
confuse
people.
E
E
D
Back
to
version
26
of
the
draft,
so
we
moved
the
text
from
slack
section
and
from
design
consideration
append
this
about
privacy
into
a
new
privacy.
Consideration
subsection
of
the
security
section,
as
has
been
suggested
by
in
in
the
mailing
lists,
or
if
M,
rated,
the
slack
and
ID
section
to
stress
only
link
locals,
does,
can
use
UI,
64
removed
the
GOP,
Wireshark
explanation
or
reformulated
the
slack
and
ll
sections.
D
Continuing
on
the
comment
from
six
men,
we
added
a
brief
mention
of
the
need
of
use
of
link
local
clarified
to
text
about
mark
address
changes,
dropped
the
Dhoni
discussion
and
change
title
of
section
describing
an
example
of
packet
forma
for
the
privacy
protections
of
vehicles,
which
is,
it
has
been
also
comments
that
we
have
received
from
deck
and
Emilia.
So
we
added
that
paragraph
that
you
can
see
in
the
so
we
need
you
to
add
this
paragraph
in
future.
D
C
Okay
think
reveal
so
I
guess
you
didn't
get
like
kind
of
the
blessing
from
six-month
right.
I
mean
the
last
revision
has
not
been
reviewed
by
six
month
as
such.
So
we
need
that,
because
I
I
believe
that
the
sixth
month
will
not
be
happy
with
the
current
version
either.
So
we
need
to
to
probably
get
another
review
from
them
to
highlight
the
things
that
need
to
be
addressed.
F
So
I
one
more
thing
is
like
probably
also
the
check
with
the
IPV
working
group
to
see
if
they're
happy
with
the
changes,
because
I
don't
see
like
you
know,
like
the
closing
the
loop
in
the
working
group.
So
maybe
we
can
probably
do
like
a
one-week
last
call
or
something
not
this
week,
but
the
week
after
say
like
okay,
like
you
know,
are
you
happy
with
the
changes
that
are
being
made
since
the
last
book
in
the
last
call,
because
I
think
it's
pretty
significant
amount
of
changes,
since
the
last
working
group
last
call?
F
So
once
that's
done,
probably
I'll
do
the
same
process
for
six
month
to
ship
it
over,
but
I.
Think
doing
this
in
lockstep
is
probably
not
gonna
work,
so
we
can
probably
close
one
off
and
then
go
again
do
another
shot,
because
I
think
it's
gonna
be
very
difficult
to
try
to
do
a
last
call
on
both
the
places
at
the
same
time,
because
there
might
be
somebody
who
might
come
up
like
even
like
stuff.
F
Like
you
know,
Eric
was
talking
about
like
some
fairly
obvious
things
that,
like
shouldn't,
be
controversial,
seem
to
be
controversial
right,
like
some
appendix
or
something
right,
so
I
I,
just
don't
want
to
like
you
know,
correlate
these
two
things
at
the
same
time.
So
like
kill
it
close
off
your
send
it
off
the
six
man,
bring
up
the
issues
here
again
and
gone.
So
even
if
it
takes
time,
I
think
it
makes
more
sense
and
that
way.
E
G
E
Look
at
the
diffs
to
actually
figure
out
what
was
actually
changed
right
because
to
change
log
in
the
document
is
extremely
brief,
so
I
haven't
pulled
up
the
diffs
yet
to
see
what
actually
did
change
but
but
doing
that
stuff
so
that
people
can
actually
see
that.
Okay,
you
did
change
something
in
response
to
this,
or
at
least
you
responded
saying:
oh
no
you're
confused.
You
know
we
don't
need
to
change
the
document.
Okay,.
F
That
that's
kind
of
what
I
was
implying
by
closing
the
loop
right,
like
you
know,
there's
like
people,
don't
know
that
you
made
the
change
like
our.
What
change
actually
tried
to
make
for
a
given
things
like
at
least
four
Eric's
email
right,
like
you
listed
like
you
know,
what
are
the
changes
he
made,
but
all
the
six
man
comments
right
doesn't
there's
no
closure
in
six-man
for
the
comments
that
came
in
right,
saying,
okay,
this
is
what
we
changed
in
the
graph.
F
F
D
D
F
So
we
just
probably
go
through
it
like
separate,
be
useful
for
you,
Carlos
Andres.
If
I
set
up
an
issue
tracker
for
this,
so
you
can
actually
keep
track
of
the
issues
and
close
them
off
and
and
go
on,
because
I
feel
it's
very
weird
like
to
get
an
issue
tracker
here
to
go
through
this
like
side
process
to
get
one.
But
I
can
get
your
issue
tracker,
for
this
is
that
you
think
I'll
have
I'm.
B
C
G
C
Guys
meet
a
new
version
with
all
the
changes
that
this
thing
at
this
point
were
necessary.
You
send
an
email
summarizing
all
the
changes
you
made
were
those
comments
came
from
like
six
month.
It
says
it
is
this
a
wave.
We
have
address
a
comment.
If
it
is
a
comment,
didn't
reach
an
agreement,
you
say
like
we
didn't
reach
an
agreement,
so
this
is
still
open.
H
Hello,
this
is
a
war
zone
from
sang-gyun
University
in
Korea.
The
bottom
of
the
slide
lists
up
our
co-authors.
So
at
least
talking
about
about
the
problem
statement
addressing
what
is
next,
the
staff
for
IP
wave.
If
we
can
and
also
show
the
several
use
cases,
the
actor
material,
meaning
we
updated
the
two
of
virgins
so
the
especially
as
a
comment
from
volunteer
divers
Eric
and
the
Turk
and
prong
choice
and
be
sure
and
Ally
yeah:
okay,
Amalia,
okay,
so
except
the
Amelia.
That
is
a
human
lie
to
leave
you.
H
So
what
is
lighted
at
the
human?
Try
to
point
of
view
so
highlight
are
her
the
lib
you
most
of
focus
and
the
security
stop.
So
I
tried
to
address
especially
privacy
issue.
So
I
can
polish
up
our
problem
statement
document,
but
other
technical
part
I,
believe
I
addressed
all
so
we
agreed
just
a
Picasa
3.
Our
key
work
items
that
the
first
one
is
neighbor
discovery.
The
second
one
is
the
mobility
management.
The
third
one
is
security
and
privacy.
H
So
the
major
of
changes
is
a
neighbor
discovery.
I
would
say,
pick
your
neighbor
discovery
if
we
Andy.
So
last
time
the
adding
node
mark,
he
asked
the
what
is
definition
of
a
particular
link
model.
So
this
drug
we
tried
to
address
the
link
model,
so
maybe
we
can
discuss
this
very
important.
The
second
one
is
the
neighbor
discovery
based
proactive,
a
handover
to
support
the
transporter
layer
session
continuty.
So
we
can
take
advantage
of
Lincoln
layer
parameter
such
as:
let's
see
the
channel
power
indicator
and
also
location
of
our
ICU
and
it's
a
coverage.
H
So
we
can
predict
when
the
mobile
vicar
will
move
out
over
the
communication.
Ranger
RCU
and
the
Odyssey
also
can
determine
what
is
the
timing
to
perform
the
handover.
So
we
can
take
advantage
of
that
information,
so
that
is
a
second
one.
Our
sort
of
one
is
a
vicar
law
on
that
architecture.
Try
to
clarify
the
Cure
link
model,
the
last
one
is
also
our
see
you
on
that.
Talk
is
connected
to
a
vehicle
cloud,
so
I
will
explain
one
step
at
a
time.
This
figure
shows
the
picture
to
Architecture.
H
So
you
can
see
the
bottom.
We
have
two
7s
7
at
107,
a
2,
so
this
figure
is
very
important,
so
you
can
see
the
RSU
you
1rs
you
to
to
others.
You
are
sharing
the
same
prefix,
so
we
try
to
construct
the
multi-link
a
subnet,
which
means
one
beaker
p1
configured
by
the
prefix
announced
by
RSU
one
and
then
he
moving
to
another
R
to
you.
Well,
it's
a
virtual
long
link.
H
It
doesn't
necessarily
be
configure
our
game
because
the
same
muscle
in
cassava
net,
we
tried
to
reduce
address
of
the
computation
overhead
right
because
you
can
see
usually
our
ICU
or
will
be
deployed
intersection
earlier,
sometimes
highway
cases
of
intermediate
over
our
bottle.
Aways.
Most
of
the
cases,
the
urban
area,
the
particular
people
think
intersection,
is
a
good
position,
so
you
can
see
the
usually
intersection.
Distance
is
less
than
100
meter
in
the
United
States
case.
In
the
case,
every
RG
you
visit
changing
new
address
is
not
efficient,
so
I
envision.
H
We
try
to
construct
a
more
technical
subnet
and
then
we
can
allow
just
a
one-time
others
configuration.
It
will
be
enough.
However.
Sometimes
another
RC
you
three
can
have
another
estaba
net.
Prefix,
so
in
that
case,
it's
somehow
we
needed
to
perform
some
handover,
so
3
and
I
get
discussed
so
mobility
anchor.
This
structure,
similar
to
a
proximal
arrive
here,
such
as
RMA.
So
this
one
can
hinder
our
different
subnet,
prefix
I,
think
that
is
it
some
different
from
proximal
variety
structure.
H
So
we
try
to
take
advantage
of
the
position
of
original
and
trajectory
of
a
vicar
because
the
vicar
can
equip
with
GPS
navigator.
So
we
can
lock
on
our
easy
positions,
feed
the
direction
that
information
really
adequately
deported
to
RSU,
and
you
can
share
that
information
with
the
neighbor
Ric
you
also.
It
can
be
poor
to
mobility
anchor,
so
mobility
anchor
is
a
kind
of
control,
caravan
or
mobility
management.
So
I
think
this
is
a
new
link
of
model.
H
Also
important
thing
is,
secondly,
the
big
helicase,
the
communication
between
picker
to
beaker
shield
p2p
later
than
a
pre,
I
and
I
to
be
it
takes
time.
So
we
sport,
b2b
or
so
pre
I
simultaneously.
This
one
is
I
think
a
different
from
traditional
or
infrastructure
face
the
wall,
its
communication,
so
we
need
to
support
two
posts,
so
this
figure
shows
up
with
two
I
communication
scenario
you
can
see.
This
is
the
left
hand,
side
the
picker
in
peak
collateral
and
the
right
hand.
H
Sides
are
see
you
in
internal
network,
so
nowadays
the
industry
they
are
trying
to
make
internal
lateral,
using
Gigabit
Ethernet,
providing
some
diagnosis
or
other
some
sensing
for
some
adaptive
cruise
control
purposes.
Many
there
are
can
be
generated,
so
we
can
see
this
one
is
moving
router.
Okay,
it
is
a
communicate
with
another
router.
H
This
is
the
keep
in
mind
the
RSU,
so
this
interface
is
used
to
access
cloud
connected
to
a
poverty
anchor
to
take
a
some
internet
services
over
communicate
with
this
vicar.
Another
vicar
locate
he
to
add
another
southern,
a
blink
okay.
So
we
needed
to
consider
this
kind
of
internal
letter
as
well.
Okay,
our
second
one
is
that
the
beaker
to
bicker
case
can
communicate
each
other.
So
in
this
case
we
can
say
one
important:
the
application
in
the
driverless
autonomous
our
vicar
scenario
case.
We
can
learn
some
the
control
context-aware
navigator.
H
They
can
communicate
to
each
other
to
aware
the
neighboring
vicars
also
neighboring
are
pedestrians
to
avoid
conflict
or
accident.
So
in
the
case
of
some
application,
learning
some
hosted
to
another
cruise
control
application
laying
another
host
within
in
beaker
Network.
They
should
communicate
to
each
other.
So
the
question
is
how
to
provide
this
kind
of
communication,
so
that
is
a
different
from
other
existing
manner
or
other
some
DMA
and
other
Asian
area.
H
You
can
see
the
VQ
okay
depending
on
transmission
power,
also
interference
in
air,
so
one
transmission
not
necessarily
guarantee
the
other,
a
transmission
right,
so
a
symmetry
in
the
connected
exist
and
also
the.
Lastly,
you
can
see
the
multi-link
a
serve
on
a
case.
Take
xu
the
leech
over,
even
though
the
multi-link
a
so
connect
consists
of
a
multiple
or
wall.
H
It's
linked
with
the
same
prefix,
so
the
how
to
hinder,
and
also
the
peculiar
case,
the
initial
attack
Network
case,
even
though
sometimes
within
some
subnet
domain,
but
maybe
take
disconnected
because
of
a
some
communication
range
right.
So
in
the
case
we
need
to
communicate
using
our
seu
relay
something
like
that.
So
so
this
is
very
different
from
traditional.
H
So
as
a
leader
we
have
some
new
features
for
particular
neighbor
discovery,
so
Eric
suggested
are
lightweight.
Dat
are
using
a
ND
optimization
from
6lowpan
6lowpan.
The
major
concern
is
energy
consumption,
so
they
try
to
avoid
nd
a
broadcast.
So
if
some
IOT
device
requires
some
address
prefix
case,
just
unicast
based
router,
solicitation
message
delivered
and
louder
can
be
saved
and
then
handler
using
multi
hub
at
the
ad.
H
So
in
the
same
way
we
take
advantage
of
this
one
imagine
you
can
see
the
one
intersection
area
100
over
200
beakers
moving
around
what
they
try
to
reconfigure.
So
in
that
case
we
need
to
minimize
traffic
overhead.
That
is
I,
think
important.
Also
it
moving
to
another
subnet.
Try,
the
idea
again
is,
you
can
say,
inefficient
approach.
So
that's
why
we
need
to
consider
this
one.
So
single
address,
comparation,
more
technical,
subnet
I
think
is
enough.
H
Also
the
handle
bar
among
our
seu
and
the
MA
mobility
anchor
can
be
used.
Support,
take
advantage
of
our
trajectory
and
the
position
information
over
the
baker.
Also,
we
have
their
dynamic,
topology
ARPANET,
also
multi-link
a
subnet
forwarding.
We
need
consider
P
P
over
P
IIT
bleah,
so
we
new
consider
that
one
depending
on
the
location
of
Vickers,
okay
and
then,
let's
move
on
our
mac
address
pseudonym
for
privacy.
I
My
name
is
Charlie
Perkins.
Can
you
go
to
the
last
slide
just
for
a
moment?
Okay,
there's
a
document,
that's
just
about
done
in
six
loads
called
sixty
authorities,
775,
update
and
I-
think
it
really
deserves
consideration
here,
because
there's
a
lot
of
discussion
about
how
to
have
multi-hop
registration
for
these
devices
as
well,
as
you
might
say,
some
improved
verification
capability
which
might
come
in
handy
here
as
well.
Okay,
so.
H
I
E
H
H
Layer
session
should
be
the
maintained
right,
so
we
need
to
consider
all
that,
so
we
can
take
advantage
of
existing
our
mobility
management
scheme.
Maybe
it
is
not
good
enough.
We
needed
to
adding
more
and
also
v2.
Visionary.
Okay
is
prefixed
dissemination
exchange
very
important,
I
explain
the
previous
slide
free
to
be
scenario
and
the
mobility
management,
so
efficient
mobility
management,
simulates
connectivity
and
timely
data
exchange.
H
So
we
can
take
advantage
of
a
mobility
information
sharing
or
with
the
infrastructure
load,
our
ICU
and
mobile
T
anchor
and
the
peakers
so
proactive
a
handover
can
be
used.
So
I
delivered
the
trajectory
page.
The
mobility
management
can
be
used.
Okay,
nowadays,
every
user
or
driver
holding
a
smartphone
over
thicker
nowadays
a
desk
the
system
providing
the
vision
system.
We
can
take
advantage
of
that
mobility
information
for
our
mobility
management.
H
Also
with
that
kind
of
prediction
over
the
vicar
mode
model
T,
we
came
for
from
efficient
the
da
de
terre
poverty
and
the
handover
for
active
manner.
There
is
item
very
important,
unique
point
and
also
we
take
advantage
of
a
link
of
layer
parameter
such
as
receive
the
channel
power
indicator
over
our
SSI
over
the
outer
layer
frame.
We
cannot
use
it
so
next
step
is
Carol
mentioned
that
we
text
to
intensive
live
year.
H
C
So
for
the
the
reviews,
so
we
need
to
three
reviews
before
next
ITF,
so
you
suggested
three
I,
don't
know
if
you
can
do
it,
okay,
so
one
thank
you
provides,
certainly
what's
also
mesh.
Well,
I,
don't
know
if
mentioned
I
was
thinking
in
some
it
tell
me.
Can
you
take
a
look
at
the
at
the
current
version
of
provides
and
comments
as
well.
K
From
our
technologies,
I
have
a
question
regarding
the
mobility
scenarios
that
I've
mentioned.
One
of
the
things
that
wave
has
done
is
removed.
Some
handshakes
and
they've
updated
the
authentication
scheme
at
the
lower
layer,
just
so
that
it
reduces
additional
additional
are
td's.
You
know
that
I
know
more
and
now
at
the
ball
layer
with
60s
67
75
updates.
We
are
going
to
introduce.
K
K
Layer
to
view
has
changed
their
handshake
mechanism
so
as
to
reduce
the
number
of
parties
that
are
involved
for
certain
scenarios.
Right
and
now
we
are
adding
those
are
tt's
at
the
bow
layer.
So
what
I'm
trying
to
understand
is?
Is
there
any
hardbound
that
has
been
placed
by
the
wave
standard
on
the
on
what
what
amount
of
time
can
be
spent
in
this?
This
authentication,
handshake
or
any
other
handshake
that
is
involved
at
the
I'm,
just
worried
that
at
the
hive
layer
we
are
introducing
those
handshake
and
increase
in
the
time
bound.
G
H
Those
currently
as
I
long
as
understand
the
wave
case
say
they
are
focused
on
three
to
be
scenario
lighter
than
three
to
I,
so
because
the
handover
usually
involved
with
the
IP
right
so
communicate
with
some
other
corresponding
located
to
some
other
subnet.
So,
but
that
is
exactly
our
IP
way
will
help
or
working
on
that.
So
I
think
that
is
a
no
reference.
Yet
as
long
as
I
understand,
okay
yeah.
Probably
that
is
a
very
important
yeah.
You
right.
K
L
So
Rob
oh
you're,
saying
that
is
more
able
to
set
up
the
time.
Okay.
So,
but
here
we
are
not
talking
about
the
solution
approach,
yet
I
I
know
even
Paul
is
talking
about.
Even
the
is
talking
about
the
different
mobility
management
approaches.
We
are
not
sure
if
you're
going
to
build
it
layer
to
the
me.
You
know,
one
approach
is
RS
here,
routed
or
a
bridge
all
right.
L
Essentially
in
one
model,
you
can
have
some
higher-level
aggregation
K
to
build
a
large
l2
domain
right
like
today,
how
capped
at
this
right,
if
you
keep
it
very
close
to
kpop
kind
of
architecture.
That
is
one
we
need
to
look
at
how
that
impacts.
Our
you
know
different
mobility
management
scenarios,
but
if
you
look
at
RSU
as
more
as
a
l3
router,
then
what
Paul
is
talking
about
like
a
handoffs
and
all
of
that
in
that
model
we
need
to
say
how
it
impacts,
so
we
haven't
discussed
any
of
the
solutions.
L
M
H
G
H
E
Not
necessarily
comment
on
this
graph,
but
it
might
sort
of
fall
in
between
the
two
graphs
and
so
I
realized
going
through
the
various
comments
that
well.
One
thing
that
we
haven't
specified
as
far
as
I
know
is
the
base
case
of
the
vehicle
is
talking
to
one
RSU
and
the
second
later
is
talking
to
another
one,
because
it
drove
down
the
road
right
and
how
does
that
actually
perform
today
and
what
sort
of
level
of
tuning
is
needed?
You
know
we
have
these
various
or
a
advertisement
interval.
E
We
have
ways
of
setting
router
lifetimes
and
reachable
time
and
other
things
right
and
I.
Don't
know
if
anybody's
done
any
experiment
without
with
sort
of
current
code
and
see
how
does
this
behavior
if
a
new
RSU
shows
up
every
second
or
whatever
right
I
mean
even
if
he
you
you're,
not
trying
to
get
global
routing
to
work,
but
you
just
want
to
be
able
to
ping
the
default
router
as
you're
driving
it
on
the
road
right.
E
Changes,
but
at
least
you
need
to
figure
out
what
sort
of
tuning
is
needed
here.
So
that's
a
lot
simpler
than
this.
Your
your
mobility
management
here
assumes
that
you
will
find
out
about
I'm
now
talking
the
new
RSU
I
should
stop
talking
to
do
block
right
and
I
can
run
my
mobility
protocols
on
top
of
that,
but
you
need
to
find
that
out
in
a
recently
timely
manner,
so
mm-hm
anybody
on
experiment.
H
H
Alternatively,
my
lab
are
working
in
simulation
based,
realistic,
later-model,
fading
model,
try
to
peer
out
what
is
the
limitation
of
the
current
yet
existent
or
so
testify
next
slide,
we
tried
to
come
up
with
a
new
some
approach
for
Lincoln
model
and
the
neighbor
discovery
mobility
issues,
so
we
are
working
on
assimilation,
so
hopefully,
next
the
problem
eating
I
bring
my
student
to
try
to
demonstrate
what
is
the
limitation
away
this
team
protocol
right?
It's
the
our
proposal,
so
at
least
the
simulation
after
that
we
can
moving
out
there.
Implementation.
C
You
yeah,
okay,
thank
you,
so
any
additional
volunteer
for
reviewing
the
document.
As
we
discussed,
we
need
to
three
reviews
before
we
even
consider
going
for
working
group
last
cause
we
got
to,
although
one
is
from
Charlie
that
is
I
just
realized,
that
is
a
contributor
coaster,
but
I
mean
anyway.
That
would
be
helpful.
The
other
one
is
for
three
and
any
other
volunteer
I.
H
So
the
introduction
so
motivation
of
the
vehicle,
our
neighbor
discovery
is.
We
need
to
some
concrete
to
some
idea.
So
I
would
say
this
is
not
necessarily
a
solution,
but
it
can
provide
some
kind
of
line
for
our
father
moving
places.
So
the
subjects
are
handled
by
this.
A
trapped
is
definition
of
the
link
model
for
vehicle
over
wireless
links
now.
Secondly,
neighbor
discovery,
optimization
with
multi-hop
tid
and
the
soda
was
proactive
handover
with
pixel
unable
discovery
in
the
mobility
management.
Last
one
is
our
MAC
addresses.
You
don't
need
Henry.
H
So
again,
this
is
a
picture.
You
understand
the
right
so
so
we
try
to
provide
b2b
and
the
P
to
I.
Consider
our
merger
linkers
of
Annette
scenario
so
again,
UK
the
vicar
is
a
registered
through
our
ECU
and
this
address
and
actually
register
into
a
mobility
anchor.
So
this
link
coverage
case
the
its
neighbor
castes
entry
having
the
vicar's
address
information.
Also
that
address
information
is
delivered
to
our
mobility
anchor.
H
So
as
a
result,
another
vehicle
try
to
register
using
this,
our
c2
and
our
to
try
to
register
address
here
if
address
come
completely
happen,
which
means
the
daily
fared.
Okay,
it
is
called
the
multi
half
deity
and
then
notify,
and
then
it
tried
modified,
configure
again
otherwise
register.
So
in
this
mechanism,
we
can
provide
that
one
shut.
Tid
is
enough.
Okay
and
then
it
can
move
in
out
so
mobility
point
of
view
we
can
using
the
proper
IP
it
can
handle
okay,
okay,
three
so.
H
Kind
of
proxy,
so
let
me
show
you
this
one,
this
one,
so
the
beaker
or
sending
other
try
to
send
an
S
with
the
rest,
restoration
and
then
honestly
received
so
first
of
all,
it
has
a
neighbor
cast,
it
can
cache
it
each
address
and
then
using
duplicate
the
rest
restoration.
This
one
has
a
30,
ATK
/,
the
rester
take
off
look
at
its
the
ad
table.
It
pretty
conflict.
The
case
this
to
address
confirmation,
saying
there
is
a
complex.
H
L
So
again,
going
back
to
my
earlier
comment:
if
you
make
look
at
our
SC
as
an
access
point
right
and
essentially,
mobility
anchors,
like
you
know,
somewhat
an
aggregation
gateway
like
our
Sun
controller.
Alright,
if
you
look
at
kpop
architecture
now,
if
do
you
still
need
this
kind
of
bridge?
You
know
so
if
now
in
that
l2
model
right,
how
is
it
impacting
this
call
flow
here?
In
other
words,
you
know
keep
everything
all
the
state
on
a
mobility
anchor
make
RSU
more
as
l2
pipe
right
between
our
SEO
and
mobility.
H
L
If
you
deploy
RSC
every
300
meters
right
now,
if
I'm
going
at
90,
km/h
I
think
this
model
may
not
work
I
think
we
need
to
really
really
think
whether
RSU
is
an
IP
node
or
at
l2
node
and,
like
I,
think
we
need
to
look
at
the
scenario.
Maybe
you
know,
building
a
large
l2
domain
is
one
approach,
I
think,
but
but
we
need
more
discussion.
Yeah
you're.
F
Suresh
krisshnan
so,
first
to
like
make
sure
everybody
understands.
This
is
like
a
future
proposed
work
item
for
this
working
group
right.
We
really
want
our
deliverables
done
before
anything
like
this
happens,
and
the
second
thing
that
I
found
confusing
I
don't
know
if
other
people
did
is
the
relationship
between
this
draft
and
brass
young
right
and
they
like
kind
of
interrelated.
But
it's
not
like
very
clear
how
they're
interrelated,
so
I
would
really
recommend
that
you
try
to
put
them
together
so
because
I'm
I
don't
really
understand
why
they're
separate
oh.
H
H
So
I
think
there
is
a
main
idea
and
that
we
can
hinder
pseudonym
and
the
mobility
take
out
the
panty
here.
What
are
se?
You
I
explained
the
problem
statement,
the
document,
so
our
next
step
is
once
we
are
finished
a
problem
statement.
We
need
to
start
never
this
copy
for
p2p
with
UI.
That
is
my
intention,
this
document,
so
to
proof
of
concept
we
improvement.
H
Currently
we
are
implemented
line.
Now
we
finished
up
the
basic
labor
discovery
protocol
implementation.
Next
step,
we
implement
our
proposer.
So
next
the
hackathon
project
we
try
to
come
up
with
so
as
a
one
information
I,
also
leading
some
I
to
another
hackathon,
we
seven
times,
hackathon
alternates,
working,
very
energetic.
We
you
can
tackle
it,
the
working
guru,
a
Lara.
You
know
what
interrupt
so
more
than
sixty
seventy
percent
are
our
ad
groups,
so
I
want
bring
in
energy
into
this
walking
or
using
the
deer
walking
code.
Thank
you
for
your
comment.
Okay,.
C
Project,
we
are
also
a
word
that
I
think
now.
Will
you
have
some
implementation
work
going
on
right
on
the
basic
ipv6
overall
CV
with
some
students?
That's
correct
or
not.
So
my
question
is:
if
you
do
also,
you
have
also
some
implementation
on
the
basic
ipv6
over
ocv
stuff,
because
if
that
is
the
case,
it
will
be
very
valuable.
You
go
for
this
kind
of
hackathon,
where
you
do
it
some
interrup
tests
on
the
basic
draft.
C
That
will
be
very
helpful
for
that
draft
to
to
progress,
to
understand
what
are
the
issues
and
then
that
will
be
also
very
hopefully
understanding.
What
are
the
potentiality
that
need
to
be
improved
in
a
potential
future
work,
as
shouldas
mentioned,
nothing
will
happen
until
we
are
really
done
with
them
into
documents.
C
So
I
think
we
should
focus
on
those
two
main
documents
so
basically
on
the
implementation
of
the
ocv
basic
stuff,
and
that
will
be
very
very
helpful
if
you
can
do
a
hackathon
kind
of
interrupt
in
the
ex
idea
and
if
that's
the
case,
we
should
prepare
and
advertise.
So
many,
maybe
some
other
implementations
or
some
other
people
can
join.
Ok,
but
it
will
make
mainly
meet
the
hackathon
around
the
ipv6
oversee
the
main
stuff.
Ok,.
D
This
is
noble
again.
Thank
you.
Thank
you
for
this
suggestion
we
have
indeed
in
the
last
IES
african
internet
sandwich.
We
have
done
a
hackathon
and
there
were
three
trucks,
one
of
them
it
was
around
a
IP
wave,
so
we
brought
some
network
cards
rated
to
OCB
and
it
was
a
successful
because
we
have
been
able
to
implement
those
cards
in
in
Linux
and
Linux
recompile,
the
the
current
etc,
and
make
the
pink
between
two
to
two
notes
that
there
are
virtual
vehicles
because
of
dot
cards,
and
we
got
some
good
results.
Yes,
so.
H
N
Hi
I'm
Mira
from
Kampala
tech
present
to
you
today
the
the
extension
of
transport
layer,
security
code
to
support
the
vehicular
certificate
at
sea
and
I
Triple
E
certificate.
So
the
agent
of
this
presentation,
I,
will
really
start
by
these
currents.
Our
motivation
use
cases
of
the
extension
and
the
extension
how
it
works
on
terra's,
so
cooperative,
intelligent
transport
system
are
very,
very
mobile,
highly
mobile
system
with
a
limited
bandwidth.
That's
why
we
are
not
using
knowing
certificate
unknown
security
tools.
N
N
N
We
can
use
it
also
for
to
connect
to
make
connection
to
cloud
services
connected
on
containment
and
also
to
connect
a
client
vehicle
to
to
company
using
daily
servers
like
rent
company,
rent
company
and
car
manufacturers,
and
also
wireless
electrical,
the
electric
vehicle
charging,
the
extension,
how
we
make
it
really
in
Telus
it
just
adding
a
new
certificate
type
to
existing
types,
x.509
or
a
public
key
and
the
third
one.
It
will
be
1609
the
two
and
to
define
its
structure.
N
Entry
structure
on
on
TLS
and
here
I'm,
describing
an
example
of
handshaking
where
the
client
search
the
client
is
proposing
to
use
X
1609,
the
two
and
the
server,
and
he
gives
to
the
server
the
possibility
to
use
one
of
this
authentication
method.
The
first
one
x.509,
the
second
one,
is
raw
public
key
and
the
third
one
is
1609
the
two,
and
so
the
plant
will
keep
his
certificate
1609
dot,
two
for
authentication
and
the
server
will
choose
the
default,
one
which
is
x.509.
It's
a
hybrid
utilization
of
such
certificate
with
x.509.
N
N
It's
I
mean
if
so,
it's
a
profile,
so
it's
we
verify
the
certificate
in
the
same
way
and
we
serve
its
it's
the
same
fields
just
for
example,
on
Etsy.
Some
fields
are
optional,
are
deactivated
by
default
and
on
I
Triple
E
is
more
general,
let's
say
definition,
but
on
the
verification
you
we
have
to
follow
the
algorithm,
the
verification
algorithm
of
I
Triple
E,
even
for
HC
certificate.
Okay,.
