►
From YouTube: IETF104-BIMI-20190328-1610
Description
BIMI meeting session at IETF104
2019/03/28 1610
https://datatracker.ietf.org/meeting/104/proceedings/
A
Come
to
order!
Thank
you.
This
is
Billy.
Be
me,
depending
on
your
pronunciation,
that
is
not
your
intended
destination.
This
is
your
last
chance.
This
is
the
ietf
note
well,
which
didn't
render
too
well
in
the
it
was
faded
in
the
PowerPoint
I
uploaded,
but
when
they
converted
its
PDF,
currently
that
the
bid
the
gamma
didn't
quite
make
it
through
anyway,
you've
all
probably
seen.
The
note
is
that
better,
okay,
so
you've,
all
probably
seen
no
well
elsewhere,
check
the
relevant
documents
they
all
apply.
You.
B
A
This
is
a
hard
to
read
agenda
yet
another
slide
that
didn't
render
well
the
kind
of
usual
Boff
treatment
here.
So
we've
got
an
overview
of
the
problem.
We've
got
some
outline
of
the
mechanisms
that
are
required
to
meet
this
solve
that
problem,
some
proposals
for
how
to
how
to
implement
those
mechanisms,
and
then
some
time
for
discussion
at
the
end,
most
of
its
gonna,
be
driven
by
these
guys
here.
A
The
questions
we're
trying
to
address
here
just
to
kind
of
get
get
folks
focused
on
what
kind
of
comments
you
might
be
wanting
to
make
the
questions
we
have
here
as
a
non
working
group
forming
ball
for
not
trying
to
answer
the
typical
Boff
questions.
This
is
more
about
kind
of
problem
scoping.
What
problems
in
this
space
might
be
reasonable
for
the
IETF
to
work
on
which
problems
are
definitely
not
good
problems
for
the
eye
you
have
to
work
on
and
where
there
is
that
overlap.
A
What
what
might
be
some
good
points
in
that
space
and
to
kind
of
put
this
in
Ben
diagram
form,
because
I
know
ITF
folks,
like
math
and
sets
the
idea
is
to
kind
of
we
should
be
kind
of
trying
to
focus
on
identifying
this
dashed
black
line
here.
What
is
the
the
shape
of
this
area
of
overlap
so
the
degree
in
which
there's
overlap
between
what
Benny
needs
and
what
the
ietf
works
on
and
then
what
are
some
of
these?
These,
like
squares
here,
wasn't
potential
good
starting
points,
so
it
can
saplings.
C
A
D
All
right
so
we're
here
today
to
talk
about
brand
indicators
for
message
identification.
We
call
it
Vimy.
My
name
is
Alex
Brockman
and
we're
gonna
go
through
some
of
this.
In
a
little
bit
of
phases,
I'll
go
first
and
then
they'll
be
some
others
following
up
so
we're
gonna
go
through.
This
is
an
overview.
What
we're
going
to
talk
about
so
agenda?
I'm!
Sorry!
So
there's
gonna
be
an
overview.
We'll
talk
about
some
of
why
we're
doing
this.
Why
are
we
here?
Quite
yet
my
two
lamb.
E
B
D
No,
no!
No
so
this
presentation
broken
into
these
four
sections,
we're
gonna,
ask
you,
try
to
hold
your
questions
until
the
end
of
one
two
three
and
then
when
we
get
to
four.
So
one
will
be
this
overview.
Some
of
why
we're
here
and
what
we're
doing,
what
we're
asking
some
use
current
day
situations,
the
mechanisms
and
in
the
current
proposal
and
then
longer
discussion.
D
And
there
are
some
seats
up
front
still,
if
you,
if
you're
interested
I,
don't
know
no
okay.
So
if
you
look
at
this
today,
this
appears
to
be
a
pretty
average
email,
and
this
looks
like
something
that
I
would
potentially
get
in
my
inbox
and
sometimes
we
can't
always
tell
what's
going
on
in
this
particular
case.
The
contact
looks
legitimate.
It
looks
like
a
real
person,
the
content
looks
good
and,
unfortunately,
even
if
it
passes
authentication
methods,
it
has
week
policy
enforcement.
D
So
what
we're
trying
to
so
in
this
particular
case,
the
customer
may
be
fooled
into
clicking
the
link
and
doing
the
things
they
needed.
You
know
that
the
attacker
is
intending
so
one
of
the
reasons
or
some
of
the
reasons
we're
doing
this
is
SPF
and
DKIM
and
Demark
are
all
very
important.
They
help
with
increasing
message
security,
so
the
adoption
is
is
growing,
but
it's
not
where
we
would
like
it
to
be.
It's
not
coming
along
as
fast
as
we
would
like
and
in
certain
sectors
of
the
industry.
D
Where
it
may
be
more
important,
it's
definitely
not
where
we
would
like
it
so
we're
potentially
gonna
try
to
Inc
provide
an
incentive
for
the
those
those
senders
to
adopt
a
stronger
Demark
policy,
stronger
authentication
methods
so
that
we
can
make
for
a
safer
ecosystem.
So
again,
we
would
like
stronger
authentication.
D
Sanders
would
like
some
really
neat
logos
and
I'll
cover
this
in
a
minute,
but
we
also
because
ok,
yeah,
ok,
I'll
talk
about
this
more
in
a
second,
but
this
already
exists
in
some
some
state
on
several
several
platforms
as
it
is
so
we're
gonna
try
to
have
Binney.
You
know
tie
all
this
together.
It's
hi
logos
to
the
authenticated
messages.
D
So
today
we
do
have
some
systems
out
there
that
do
create
tie
logos
to
messages
through
whatever
method.
We
actually
don't
know
unless
you
work
that
company.
So
today
that
a
receiver,
they
have
some
manual
systems,
they
have
inconsistent
systems,
they
have
where
something
like.
If
the
logo
Changez
somebody
else
has
to
come
and
update
it,
it's
it's
all
on
those
individual
receivers
and
it's
is
cumbersome.
It's
there's!
D
No
there's
no
clear
and
consistent
way
for
a
receiver
to
do
this
today,
and-
and
we
can-
we've
had
discussions
in
the
past
as
a
group
about
some
of
the
ways
that
happens
today
and
we're
only
gonna
go.
That's
a,
but
it's
it's
clear
that
there's
there's
just
it's
lacks
consistency
and
it's
it's
not
manageable
in
at
scale
and
so
for
Sanders.
They
sort
of
have
the
flipside
of
the
same
issue.
They
they
have
no
control
over
their
logos.
D
So
if,
let's
say
I
were
to
source
a
logo
today
and
I
and
and
and
the
company
that
that
I'm
showing
this
logo
for
changes
their
logo
two
weeks
from
now,
they
have
they
have
to
wait
for
me
to
do
it,
there's
no
way
for
them
to
change
that
today,
so
we
can
be
confusing,
it
could
take
weeks.
It
could
take
months.
We
don't
know,
there's
no
and
there's
also
no
control
over
how
the
sender's
logo
is
displayed
in
the
platform
they
have.
It
could
be
some
portion
of
it.
D
D
D
Those
are
you
know
they
can
sort
of
the
it's
more
important
thing
for
the
sender's
and
it
is
for
for
the
receiver,
but
it's
sort
against
sort
of
the
carrot
to
help
them
move
along
having
a
standardized
process
for
each
each
one
of
those
is
good
and
then
again
having
the
ability
to
change
the
logo
as
they
go,
I
mean
there's
you
may
have
regional
logos,
you
may
have
seasonal
logos.
There
could
be
things
like
this.
D
That
makes
sense
for
your
organization
that
you
know
the
this
receiver
may
not
be
aware
of,
and
then
for
as
a
mailbox
I
mean
we
would
love
to
have
more
authenticated.
Mailed
helps
us
have
a
better
ecosystem
and
help
help
sort
of
fight
abuse
and
again
the
having
the
silo
systems
where
each
group,
each
organization
does
their
own
validation
is
really
hard.
I
mean
if
we've
talked
to
again
some
of
the
people
do
this
and
they
don't.
It's
it's.
D
You
know
somebody's
looking
at
a
logo
making
sure
it's
correct,
you
know
making
sure
it's
in
the
correct
use
case,
that
sort
of
thing
and
then
there's
the
the
last
point
on
there
is
that
some
assurances
that
the
sender's
are
you
providing
logos
that
are
actually
theirs.
So
we
have
to
have
a
way
to
ensure
that,
for
instance,
if
Google
is
wants
to
use
a
logo
that
is
actually
Google,
that
is
using
the
proper
logo
and
that
they
have
permission.
We
use
that
logo
or
any
other
sender
in
that
case.
So
your.
F
All
right,
hi
Neil
next
we
want
to
do-
is
give
you
sort
of
a
broad
overview
of
what
Emmy
is.
So
it's
a
way
to
publish
a
way
to
retrieve
and
a
way
to
validate
logos
that
are
attached
to
a
message.
The
TLDR,
the
quick
set
of
steps
that
we
have
encapsulated
in
bimmy
today
is
first,
the
sender
needs
to
implement
d
mark.
It
needs
to
have
a
policy
of
either
quarantine
or
reject.
Second,
the
sender
needs
to
go
through
some
process
of
validation.
F
There
is
a
method
for
self
assertion,
but
we'll
talk
about
that
when
we
get
to
the
validation
methods.
Third,
the
center
needs
to
publish
a
DNS
record
pointing
to
its
logo
and
the
method
of
validation
that
they
used
and
from
their
mailboxes
can
retrieve.
The
logo
confirm
the
form
of
validation
that
went
through
and
decide
whether
to
display
it
or
not.
So
why
do
this
for
senders?
I
think
alex
covered
a
lot
of
it,
but
it's
a
standardized
way
to
publish
their
logos
to
various
receiving
platforms
and
for
mailboxes
a
receiver.
F
Talking
about
what
Benny
is
not?
This
is
not
a
standard
that
we're
trying
to
position
as
something
that
directly
increases
user
trust.
So
it
is
not
a
positive
security
indicator.
It
is
not
an
anti
phishing
standard
in
and
of
itself
beyond
inspecting.
The
adoption
of
authentication,
which
we
do
feel
is
useful.
It
is
not
a
method
for
arbitrary
Doge
logo
display,
so
the
ability
to
assert
any
logo
from
any
sender
so
not
similar
to
like
a
favicon
or
Gravatar.
It's
also
not
a
guarantee
of
logo
display.
F
So
what
we
mean
by
that
is,
even
if
you
go
through
the
set
of
steps
necessary
to
validate,
assert
and
publish
your
logo,
we're
not
making
a
guarantee
that
as
a
receiver,
we
will
display
it.
Anti-Abuse
infrastructure
will
still
kick
in.
If
there
are
things
about
the
message
that
do
not
look
legitimate,
we
will
not
show
the
logo
and
finally
we're
trying
to
position
that
this
is
something
that's
not
solely
email.
F
So
talking
just
about
a
few
known
implementations
of
logo.
Today,
some
of
the
larger
receivers,
Google,
Verizon
and
Microsoft
all
have
various
forms
of
logo
display.
But,
as
Alex
was
talking
about
earlier,
these
things
are
very
fragmented
in
nature
and
as
the
sender,
not
only
do
you
have
to
jump
through
different
hoops
for
each
one
of
these
receivers,
you
have
to
jump
to
other
groups
and
other
places
as
well.
So,
as
we've
started
to
talk
to
folks
about
potential
adoption,
there's
a
lot
of
interest
that
we've
seen
from
Google's
perspective.
F
I
think
this
is
a
problem
that
we
would
like
to
solve
and
solve
it
in
a
way
that
applies
to
everybody,
we're
taking
a
look
at
the
standard
and
we
will
adopt
it
as
things
go
on,
assuming
they
move
in
sort
of
a
direction
that
we're
comfortable
with
Verizon.
Media
is
working
on
an
implementation
now
and
we
have
SH
written
off
on
the
call.
You
can
speak
to
that
as
well.
There's
also
a
number
of
other
parties
that
are
interested
in
adoption
of
Bennion
furthering
the
standard.
F
So
why
are
we
here
we're
here?
For
a
few
reasons,
first,
we
wanted
to
make
sure
that
we
engage
IETF
early.
A
lot
of
the
ideas
were
discussing
our
preliminary
ones.
They
think
we
think
they're
the
right
approach,
but
we
want
to
get
feedback
on
that.
We
want
to
adapt
based
on
that
feedback,
and
we
want
to
do
this
before
we
go
through
and
actually
implement.
This
at
scale,
we'd
like
to
seek
advice
from
the
atf
community.
F
So,
briefly,
pausing
on
some
of
the
common
concerns.
We're
calling
them
out
early
in
the
presentation
will
be
addressing
some
of
these
as
we
talk
through
the
specific
mechanics
in
Bamie.
But
we
wanted
to
be
upfront
about
some
of
the
larger
problems
we
see
to.
Let
you
know
that
we're
cognizant
of
them
and
we
are
taking
a
look
and
seeing
how
we
want
to
how
we
can
solve
these
problems.
F
F
There
is
concern
that
senders
that
all
senders
and
mailboxes
won't
be
able
to
use
Bennie.
So
it's
something
that
will
only
be
applicable
to
larger
platforms
and
smaller
platforms
may
not
have
the
resources
to
be
able
to
adopt.
This
there's
concern
that
the
logos
themselves
may
be
a
carrier
for
attacks
and,
finally,
there's
a
concern
that
at
some
point
in
time,
if
we
go
down
this
path,
maybe
will
become
mandatory
frame
box
placement.
Second,
the
validation
mechanism
for
figuring
out
whether
somebody
actually
has
rights
to
a
logo
is
actually
not
a
trivial
problem
to
solve.
F
The
different
mechanisms
were
looking
at
will
require
human
intervention,
there's
varying
laws
around
brand
imagery
around
the
world.
So
we
have
to
find
a
way
to
consistently
tackle
that
problem
and
some
of
the
existing
validation
systems
that
we
know
about,
such
as
Evi
rbirtle
and
they're
prone
to
abuse.
G
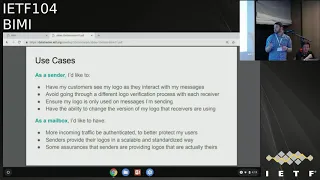
Standing
so
I
guess
I'm,
just
like
go
back
to
I,
don't
know
three
or
four
slides
back
where
you
said
that
the
so
you're
trying
to
accomplish
with
what
it
is.
They
use
cases
yeah
like
okay,
so
I'm,
just
like
trying
to
understand
like
so.
This
third
point
ensure
my
logo
is
only
used
on
messages,
I'm
sending
right
and
then
later
you
say
that
it's
not
enough
gonna
miss
bread
fishing,
but
that
in
fact
those
are
all
the
same
thing
like
well.
G
F
Yes,
I
think
what
we're
trying
to
say
is
that
the
adoption
of
Demark
will
help
from
a
perspective
of
giving
receivers,
larger
reputational
signals
to
hook
things
on
right,
so
I
make
sounds
I,
don't
quite
so.
This
response
to
what
I
said:
okay,
no,
but
what
I'm
saying
is
from
that
point
onwards.
The
idea
is,
we
don't
believe
that
the
presence
of
an
image
in
front
of
a
user
will
actually
cause
them
to
make
better
security
positions,
but.
F
G
G
F
G
H
So
if
you
go
back,
you
don't
need
to
go
back
to
the
slides,
but
I
didn't
actually
see
any.
But
you
are
X
mentioned
a
problem.
I
heard
you
say
things
you'd
like
to
do
and
then
going
back
to
Richards
slides
I,
you
your
slide
with
a
lifespan
diagram.
It
made
me
wonder:
what's
the
shape
of
the
null
set,
shade
you're
looking
for
problems
and
I'm,
not
seeing
problems
other
than
so.
Can
you
articulate
what
the
problem
is
as
opposed
to
what
the
opportunity
for
marketing
is?
Yes,.
F
I
think
one
of
the
things
that
we're
starting
with
is
the
fact
that
logo
display
is
sort
of
a
thing
Yumiko
system.
Today,
a
lot
of
receivers
have
systems
in
place
already
they
do
this,
but
do
this
in
a
very
fragmented
and
non-standard
method,
and
that
makes
it
harder
for
senders
to
go
through
these
various
processes
and
do
them
one
by
one
in
a
scalable
fashion.
F
So
it's
sort
of
one
problem
and
the
second
problem
that
we're
trying
to
solve
from
a
receiver
standpoint
is,
as
Alex
mentioned,
we
have
not
seen
the
adoption
of
B
markets
sort
of
the
scale
and
the
velocity
at
which
we'd
like
so
one
of
the
things
we're
trying
to
do
is
figure
out
how
we
create
an
incentive
to
move
that
along
quicker.
Okay,.
H
So
and
okay,
the
first
one
people
have
problems
doing
their
marketing
more
thoroughly,
fair
enough.
Yep
I'm,
not
clear
on
the
logic
in
the
second
one.
How
just
playing
about
goes
and
don't
have
anything
to
do
at
the
market
option.
But
okay,
so
that's
that's
one
thing,
I
think
also
the
top
line
there.
The
web
bug
I
mean
that's
just
horrendous
yeah.
H
H
H
J
Yeah
yeah
d'arco
Eriksson,
so
this
may
might
actually
be
clearer
later,
but
I
still
won't
provide
one
piece
of
feedback
here.
That
I
mean
this
discussion
at
least
had
a
problem
with
the
terminology
of
validation,
because
I
actually
see
two
different
issues
here.
One
one
needs
to
make
sure
that
your
domain
actually
intended
use
a
particular
logo
and
and
and
and
file
reference
and
whatnot,
and
so
that
that's
one
thing
that
that
that's
really
easily
solvable.
J
K
D
So
I
mean
think
for
all
of
us
sort
of
have
the
goal
to
make
this
as
accessible
as
possible.
This
is
a
concern,
that's
been
stated
to
us
and
we're
trying
to
do
our
best
to
make
sure
that
this
is
accessible
to
large
and
small
senders,
because
we
understand
I
mean
when
we
first
discussed
this
with
people
outside
of
our
group.
That
was
one
of
the
first
things
we
heard
was
how
you
know:
how
does
this
impact
small
senders
and
small
receivers?
So
we're
definitely
want
to
take
that
into
consideration.
We
do.
D
M
L
D
There
was
a
slide
that
showed
a
an
image
of
a
message
that
could
have
been
construed
as
phishing.
Is
that
what
the
one
you're
talking
about
I'm,
okay,
I
mean
I,
was
more
as
trying
to
show
that
the
this
the
message
had
weak
authentication,
not
so
much
that
I
mean
it's.
It's
still
ultimately
up
to
the
receiver,
you
know
is
the
message
spam.
How
do
we
interpret
the
signals
that
we
get
for
those
messages?
I
mean
I.
D
D
L
L
M
D
L
Have
and
we're
in
a
new
venue
with
lots
of
new
people,
so
unfortunately
we
get
to
rehash
some
of
these
things,
so
the
value
proposition
I
think
is
pretty
simple.
That
beanie
is
offering
and
would
encourage
you
to
the
extent
that
what
I'm
about
to
say,
doesn't
quite
match
I'd,
encourage
you
to
formulate
and
constantly
use
the
value
proposition
in
short
form.
That
is
accurate.
L
My
simplistic
summary
some
creators
of
email
want
to
get
their
logo
displayed
to
recipients,
companies
like
brand
impressions
and
that
term
is
used
in
the
overview
document
they
like
to
get
brand
impressions.
It
is
hoped
that
some,
that
some
expectation
of
getting
logos
displayed
in
a
privileged
location
will
incentivize
these
creators
to
adopt
me
transport
authentication
standards.
That's
that's
way
more
verbose
than
one
would
like,
but
it's
what
I
ended
up
typing
into
the
chat
window?
Oh.
L
A
B
N
Florencetravel
and
Bri
are
just
maybe
strange
question,
but
how
are,
for
example,
blind
people
supposed
to
check
these
mobiles
and
if
you
have
to
get
an
alternate
way
to
display
well,
this
Center
has
been
verified,
shouldn't
green
mark
that
this
domain
has
been
verified,
be
enough
and
if
brands
want
to
show
their
brand,
they
should
just
use
the
same
domain
names
that
are
related
to
that
brand
and
not
some
random
from
address.
That's
some
CDN
light
mass
mail.
N
D
I
The
one
other
thing
I'd
say
at
that
point
is:
we've
talked
about
other
things
that
could
be
transmitted
along
with
this,
but
if
we
can't
solve
the
logo
use
case,
then
the
other
use
cases
sort
of
melt
the
way,
and
if
we
can
solve
it,
then
we
would
love
to
do
more.
The
only
thing
I
want
to
ask
before
we
move
on
is
I.
Think
we
have
one
questions
was
actually
will
this
actually
help
incent
off
and
I?
I
Think
we
have
someone
on
who
can
speak
to
that
for
a
second
and
on
Kurt
from
Sanger
Dodd
he's
actually
been
working
with
people
who
have
been
having
trouble
getting
off
in
place
and
saying:
hey,
there's
this
thing
being
discussed
called
bimmy
you
need
off
to
to
actually
get
Timmy
has
helped
them
start
the
process
of
getting
SPF,
D
command,
D
mark
in
place,
and
so
people
want
to
hear
it.
I
had
asked
him
to
speak,
otherwise
we
can
continue
on.
A
I
We
want
to
chat
about
how
do
we
make
any
work
right?
How
would
how
do
we
take
an
industry
that
wants
to
incent
off
users
who
want
to
display
logos
and
how
do
we
get
them
to
the
right
place
without
how
do
we
connect
the
dots
and
do
the
right
things?
So
we
don't
have
fraudulent
use
of
logos,
and
so
to
do
that
there
are
basically
five
things
you
have
to
be
able
to.
I
As
a
domain
assert
your
logo,
you
need
to
actually
be
able
to
say
yes,
this
logo
is
valid
and
we're
gonna
have
lots
of
conversation
points
there
and
then,
as
on
the
receiving
side,
you
have
to
consume
it,
and
then
we'd
also
like
to
make
sure
there's
some
reporting
component
to
this,
and
we
need
a
way
to
fix
problems.
The
ecosystem
when
the
wrong
things
happen
and
I'm
going
to
go
through
this
relatively
quickly,
because
I
think
if
we
dive
until
all
the
details,
we'll
be
here
forever.
I
But
basically
there
are
four
primary
ways:
we've
looked
at
for
publishing
a
logo
I'm
a
domain
and
I
want
you
to
know
what
I
want
to
use
right.
So
you
can
put
it
in
a
message:
header
field
like
X
face.
You
could
attach
it
to
a
mess
or
something
like
s
mine.
You
can
use
a
method
like
vouch
by
reference
or
you
can
publish
this
in
the
DNS
in
the
same
way
as
DK,
MD,
mark
and
SPF
are
currently
done.
I
I
I
So
after
logo
has
been
published
right,
you
have
to
get
it
validate
right
this.
This
doesn't
work
without
validation.
It
just
turns
into
hey.
This
is
me
and
that's
phishing
bonanza
territory
for
everyone
right,
and
so
there
are
a
few
ways
to
do
this
right
that
the
least
scalable
way
is
hey.
If
you
have
a
reputation
system,
you
can
just
leverage
your
reputation
system
to
display
a
logo
and
that
works,
if
you're
a
few
of
the
big
people
and
doesn't
work
for
anyone
else,
and
so
it's
a
place
where
things
could
be
started
and
tested.
I
But
it's
not
a
place
where
we
want
this
to
end
up
right.
Then
there
are
existing
registries,
dot
bank,
the
organizations
that
have
members
who
can
say
hey
these
are
valid
domains.
We
know
they're
good
and
if
they
self
assert,
the
logo
is
good,
and
that
also
has
a
really
really
high
bar
for
participation.
I
I
This
is
my
logo
and
the
third
party
would
go
through
a
checklist
and
basically
go
through
and
do
diligence
on
the
logo
on
the
entity
requesting
on
the
person
requesting
it
and
come
out
with
an
attestation
and
saying
we're
willing
to
put
our
reputation
as
a
third
party
on
the
line,
and
we
believe
this
legitimate
and
provide
a
remediation
look
and
the
final
method
here
is
someone
to
self
attest
right,
I,
say
hey.
This
is
my
domain
that
doesn't
even
anyone
else.
I
Next,
the
validator
logo
has
to
be
consumed.
So
a
mail
system
make
sure
authentication
is
in
place,
make
sure
the
bimmy
record
is
valid
checks,
the
validation
mechanism
against
the
logo.
That's
been
provided
and
can
say
great
I
want
I'm,
ready
to
use
this
logo
I
believe
it's
good.
They
retrieve
it,
they
cash
it
cashing.
It
is
critical
to
avoid
the
web
bug
problem
and
then
they
could
display
it
when
a
message
is
received
based
on
their
own
policy
in
their
own
signals
about
the
message.
I
One
thing
that's
missing
today
is
any
sort
of
reporting
or
feedback
loop
from
customers
and
brands
that
have
been
interested
in
implementing
bid
me.
They
all
want
to
know
its
efficacy
and
same
as
with
Demark
when
a
Demark
report
is
used
to
say
where
are
things
not
authenticated?
We're
looking
at
this
primarily
as
a
mechanism
to
say:
okay
well
I'm
using
bimmy,
but
it's
not
working
here.
Oh
here's,
why
it's
an
invalid
record?
It
didn't
validate,
something's,
been
cropped
in
the
flow
and
you
can
go
figure.
It
figure
it
out.
I
But
specifically,
we
don't
want
reporting
to
be
about
here's.
How
many
messages
were
displayed.
It
can't
be
used
as
a
web
web
bug
and
it
can't
say
it
can't
be
a
signal
to
spammers
to
say:
hey,
oh
I'm,
able
to
use
a
Dimi
report
to
figure
out
what
got
delivered
and
then.
Finally,
we
think
bimmy
needs
a
remediation
mechanism
and,
to
be
perfectly
frank,
we
really
don't
have
a
meaningful
clue
as
to
how
this
is
going
to
work
right.
I
think
we
know
remediation
systems
at
scale
for
things
like
this.
I
Just
haven't
historically
work
and
the
question
is
this
makes
sense
to
have
right
if
a
if
a
large
receiver
sees
oh,
we
figured
out
that
this
domain
is
using
a
fraudulent
logo
and
wants
to
yank
it.
Everyone
should
get
that
benefit
and
the
flipside,
if
a
small,
a
small
receiver
in
a
region
that
many
people
don't
see,
figures
out
things
fraudulent.
That
domain
shouldn't
be
able
to
use
their
logo
anywhere
else
in
the
world
either,
and
so,
just
in
general,
the
50,000
foot
level
about
these
mechanisms.
Are
there
any
comments
or
questions.
H
H
I
A
I
One
of
the
things
we
believe
is
required
here
is
the
MTA
needs
to
say:
I
have
done.
The
me
validation
and
here
is
a
logo
that
you
pull
from
me.
That's
been
cashed
that
you're
allowed
to
use.
You
would
never
pull
from
the
actual
source
in
a
vineyard,
so
the
there
there
is
a
whole
bunch
of
content
in
the
draft
we've
written
for
that
and
we
don't
love
it.
So
the
answer
is
that
that
still
needs
some
work.
A
L
I
P
Hi
Jim
Fenton
I
certainly
understand
the
role
of
SPF
and
DKIM
validation.
Here
I'm
wondering
what
the
role
of
D
mark
is
in
in
setting
this
up
I
I
guess
you
need
to
establish
a
binding
to
the
from
address
of
the
message
which
SPF
and
DKIM
lack
correct.
But
in
order
to
do
that,
do
you
actually
need
to
have
a
D
mark
record
or
or
do
you
simply
say
in
this
specification
that
SPF
and
Deacon
have
to
have
to
correspond
to
the
from
address
so
we're
specifically
trying
to
incentivize
SPF,
deacon
and
d
mark?
P
Authentic
ating,
the
message
making
sure
that
it
corresponds
to
the
from
address
well
I
understand
how
that
how
that
would
be
a
prerequisite
to
doing
anything
with
Vimy,
but
I
don't
understand
why
actually
publishing
a
Demark
policy
is
required
in
order
to
do
that
and
I
think
that
if
you
simply
set
it
up
as
an
incentive,
it's
there
isn't
technical
reason
to
do
that.
I!
Don't
I,
don't
see
how
you
can
how
you
can
legitimately
say
that
you
need
a
dimeric
record
in
order
to
accomplish
this
so
I.
I
G
I
think
I
want
to
step
back
for
the
mechanism
for
a
minute,
because
I
want
to
stipulate
it's
certainly
possible,
listen
late,
which
really
can
makes
invent
some
that
was
like
there
were
like
if
we
assume
that
there's
like
we
have
a
way
of
constructing
a
binding
between
like
sending
two
main
names
and
logos
I'm
certain
we
can
invent
some
mechanism
so
like
the
receiver
to
like
display
those
logos
when
it
when
it
is
a
self
letter
to
me
that
the
theme
for
the
domain
name
I.
Imagine.
G
You
concern
it
like
now
that
is
me
of
you
all
summer.
They
may
it
be
sucky,
but
I'm
pretty
confident
that
they
can
be
achieved
on
the
part.
I'm
like
still
struggling
with
honestly
is
the
part
that,
like
I,
just
sort
of
stipulated,
which
is
how
we
create
that
binding
mm-hm
and
like
I
guess
I'm,
just
not
finding
the
story.
You're
offering
me
particular
persuasive,
you
know,
on
like
slack,
has
have
like
three
different
logos
in
the
past
like
three
months.
So
you
know
so
like
I
mean
really
like.
G
It's
like
I'm,
like
like,
is
very,
very
common
to
see
logos
which
look
very
much
like
each
other,
so
I
mean,
like
certainly
I
agree.
It's
like
unlikely
they'll,
be
able
to
register
coca-cola.
So
it's
a
cool
but
like
for
anything
anything
in
the
longtail
I'm.
Just
like
you
know,
I'm,
really
not
following
how
you
believe
you
have
mechanism
that
will
stop.
That
will
stop
that
and
it
seems
we
have
several
worked
examples
of
this.
G
We
have
logo
types
in
stupidest
completely
failed
and
we
have
Eevee
where
it's
been
like
proving
very,
very
easy
to
get
on
for.
Basically,
anything
long
tail
to
get
to
get
names,
the
Matt
jump
right
and
so
II,
despite
the
fact
that
Evo
led
the
TV
is
a
much
simpler
system
with
a
much
simpler,
like
name
that
or
they're
much
like
we're
matching
algorithm,
and
you
know
and
like
and
so
like,
like
don't
like
help
me
feel
better
at
this
like
when
we
understand
like
why
this
is
gonna
work.
So.
G
I
Of
all
it's
a
very
important
point,
especially
about
the
attacks
on
TVs.
We
actually
have
a
couple
slides
about
those
attacks
and
how
we
think
we've
addressed
some
of
them,
but
part
of
the
reason.
We're
here
is
we're
not
thrilled
with
our
story.
We
think
we've
solved,
there's
a
big
surface
area
and
we
have
part
of
it
solved
in
a
corner
that
we
don't
think,
is
big
enough
and
we
need
help
there
to
expand
this
and
make
this
more
applicable.
Sure.
G
I
get
I
guess
so
this
is
not
something
I
ate
yet
as
well.
You
know
I
mean
this
is
this
is
a
social
means
like
like
again
like
I'm,
quite
confident,
if
you
gave
me
a
goal
which,
like
math
to
me,
names
don't
like
the
Lord
knows:
I
could
deliver
like
the
logos
on
to
the
screen,
and
that's
saying
we
do
quite
well.
G
Well,
maybe
we
do
but,
but
like
the
thing
we
don't
do
well
is
because
our
systems
for
like
a
dealing
with
like
Gordon
and
it's
quite
the
contrary,
like
in
the
in
the
again
far
simpler
case
of
just
validating
that
people
certificates,
the
macula
domain
names
they've
actually
been
issued,
but
it's
like
actually
comp.
You
know
we
like
put
that
off
to
like
your
other
people
right.
A
Going
to
summarize
I
think
the
data
point
here
is
that
there
are
mechanisms
you
know,
policy
mechanisms
validate
definitional
met,
questions
about
you
know
what
this
validation
is.
That
will
probably
be
worked
out
outside
of
the
IETF
I
mean
the
analogy.
I
think
I
was
making
to
the
cab
forum
rules
around
evey
mm-hm.
O
I
That's
exactly
right
there.
There
are
many
things
about
validation.
We
don't
think
we
can
solve
at
the
ITF.
I
think
that's
actually
part
of
the
final
slide
here
is
is
what
what
we
think
is
work
to
be
done
here
on
what
we
think
isn't,
but
there
are
also
many
things
that
influence
that,
where
we
don't
know
what
we
don't
know
and
the
IDF
is
a
repository
of
knowledge
of
what's
failed
here
and
what
we
take
into
account
as
we
dig
in
so.
E
Branko
goanna
I
was
about
to
backseat
chair
and
basically
say
that
the
answer
to
most
of
the
questions
here
have
been
their
slides
about
this
in
the
future.
How
about
we
actually
see
the
slides
rather
than
asking
questions
are
just
gonna
be
answered,
there's
more
slides
because
that's
a
waste
of
everybody's
time.
E
I
wanted
to
answer
the
one
specific
thing
about
a
web
bug
in
a
client
and
the
idea
that
if
you
have
a
client
that
supports
Jimmy
and
yet
doesn't
understand
about
the
fact
that
the
server
doesn't
support
B
me,
it
might
display
the
image
well
short,
but
it
will
might
display
random
URLs
from
the
HTML
content
as
well.
If
you've
got
a
client,
that's
fetching
random,
URLs
and
isn't
following
the
spec
know.
Spec
is
going
to
protect
against
that.
So
that's
not
a
realistic
threat
model.
It's.
K
Good
user,
good
user,
they
they
latch
on
to
things
right.
So
if
they
start
seeing
a
icon
in
a
corner
and
it's
you
know
privileged
or
whatever
they
start,
believing
that
icon,
no
matter
where
it
exists,
they
prefer
it
over
text.
That's
actually
why
we're
much
better
at
recognizing
icons,
and
we
aren't
looking
the
text
underneath
the
app
on
my
phone
I.
Don't
go,
read
every
single
word
when
I'm
looking
for
an
app
I
look
for
the
icon,
so
the
instant
they
see
it.
They
begin
to.
K
K
You
know
point
of
attack,
there's
no
incentive
for
the
MTA
not
to
just
include
the
picture
without
actually
checking
the
validation,
because
you
know
why
would
they
go
through
the
trouble
if
they're
like
a
cheaper
startup
that
just
wants
to
display
a
logo
right,
they
can
just
go
pull
it.
There's
no
incentive
on
that
side.
So
there
seems
to
be
a
you
know:
you're
trying
to
create
a
carrot
for
large
businesses
to
display
a
logo
and
advertising
it
as
a
security
solution
with
decent
amount
of
holes
in
it.
M
I
Q
Q
So
one
thing
about
very
validated
logos
is
I.
That
I
truly
think.
That's
no
such
thing
exists.
What
I?
What
I
do
think
exists
is
claimed
logo
from
validated
entities
you
know
so
we
can
have
validated
entities
who
we
know
who
they
are
and
we
can
nail
them
if
they
act
dishonestly
and
we
can
document
what
they
are
claiming
to
be
a
representation
of
their
them
and
their
brand,
and
that
might
actually
be
very
good
enough
for
a
lot
of
applications.
So
that
is
the
point.
I
would
like
to
think.
I
You've
just
given
way
as
part
of
the
presentation
for
him
so
before
we
give
the
current
proposal.
Let's
start
with
a
couple
of
things
that
we
know
are
still
really
problematic.
First,
one
is
that
the
the
group
of
us
that
put
this
proposal
together.
We
represent
mostly
larger
US
companies,
and
there
was
just
an
inherent
bias
and
how
we've
thought
of
this.
We
believe
we're
well
represented
downstream
of
that,
but
we're
looking
for
feedback
we're
looking
for
awareness,
we
don't
know,
we
don't
know
here.
I
I
Finally,
even
if
we
don't
trust
the
self
attested
logo,
you
still
have
to
determine
who
you
trust,
which
third
parties
do
I
trust,
for
instance,
and
so
we
still
have
you
still
to
pick
and
choose
also
to
I
think
the
point
that
ekor
was
making
before
look-alike
logos,
especially
in
the
long
tail
or
our
problem.
We
have
not
solved
that
yet,
and
finally,
this
is
call
it
a
few
times,
but
if
you
don't
cache
logos,
there
is
a
definite
web
bug,
and
that
is
a
problem
with
the
current
solution
for
sure.
I
So,
there's
a
document
for
this
current
proposal.
That's
actually
there's
this
one
and
a
guidance
document.
The
current
proposal
says,
takes
DNS
publishing
of
a
record.
It's
really
straightforward.
It's
got
a
location
of
the
image
and
then
a
validation,
Mehcad
mechanism
attached,
and
you
basically
say
that
the
hash
that
come
out
of
the
validation
record
mechanism
matched
the
hash
of
the
logo.
I
There
are
a
couple
of
people
who
may
have
reputation,
systems
or
whitelists,
who
are
confident
they
can
display
these,
but
in
general
this
is
a
terrible
idea
and
a
huge,
huge
security
problem.
So
you
shouldn't
use
self
attested
logos,
especially
if
you've
just
got
your
own
mail
system,
so
I'm
gonna
hand
off
the
way
to
talk
about
validation
and
how
we
do
at
the
stations
of
logos.
O
All
right,
hopefully,
you
can
all
hear
me
on
so
I'm,
going
to
talk
about
the
third-party
method.
To
do
these
sort
of
attestations
talk
about
some
of
the
validations
and
basically
try
to
say
you
know
why
we're
doing
this
particular
method
and
also
we're
trying
to
to
point
out
that
there's
actually
a
number
of
questions
that
need
to
be
answered
in
this,
and
you
know,
we'd
love
help
from
the
IGF
community
on
how
to
get
better
answers
for
these
things.
O
If
we
need
to
so
here,
there's
actually,
you
know
I'm,
posing
that
there's
sort
of
two
different
methods
for
doing
these
sort
of
attestations
of
this
validation.
You
know,
there's
this
traditional
x.509
certificate,
that's
going
to
be
using
a
trust
model,
a
CA
based
trust
model,
and
then
this
other
this
JSON
web
token.
That's
going
to
be
passed
through
via
an
API
and
that
we
have
a
question.
So
we,
you
know
we
were
really
doing
our
design
based
on
x.509
and
hence
you'll
see.
A
lot
of
our
documentation
is
based
on
that
assumption
of
x.509.
O
O
However,
there's
also
other
very
important
differences.
Of
course,
x.509
has
things
like
you
know,
because
it's
more
mature,
it's
well
established.
It
has
good
references
for
things
like
governance
like
how
we
go
about
doing
these
sort
of
validations,
you
know,
extended
validation
can
be
a
model
that
we
build
upon
and
use
an
extent.
Similarly,
you
know
things
that
we
need
for
long-term
security.
You
know,
such
as
having
audits
in
place
standards
about
doing
those
types
of
audits.
Those
exist
over
an
x.509.
O
O
R
O
O
Okay,
so
so
certificates
bring
with
it
some
well-known
problem.
Kirkley,
you
know,
coming
for
the
webby
v-world
is
been
around
for
a
long
time.
It's
been
basically
a
bunch
of
times,
and
this
is
you
know,
acknowledgment
of
some
of
those
types
of
attacks
that
we're
aware
of
them.
You
know,
for
example,
a
lot
of
there's
a
lot
of
edge
cases
about
the
notion
of
identity,
and
you
know
how
those
edge
cases
can
be
basically
misused
to
attack
on
users.
O
So
you
know
to
two
examples
right
here:
first
security
researcher,
Ian
Carroll
like
demonstrated
that
it
wasn't
very
hard
actually
to
use
jurisdictional
concerns
as
a
way
of
of
going
after
this
notion
of
identity.
So
stripe,
Inc
of
Delaware's,
the
well-known
credit
card
processor,
he
was
able
to
basically
create
a
shell
company
in
Kentucky
and
basically
get
himself
a
valid
evie
certificate,
at
least
for
a
while,
and
then
another
researcher,
James
Carroll,
basically
was
able
to
create
another
company,
just
called
identity
verified
and
then
a
user
seeing
identity
verified.
O
Might
just
assume
yes,
just
you
know
website
was
verified
and
that
would
be
misleading.
Also
there's
a
number
of
problems
about
Miss
assurance,
basically
intentional
or
mistaken,
by
by
certain
CAS.
So,
for
example,
you
know
Symantec
issued
a
number
of
test
certificates
for
google.com.
There
are
other
examples
like
I
guess.
An
Egyptian
CA
was
also
doing
I'm
going
after
google.com
and
that's
because
of
poor
governance,
because
I
was
a
registration
authority
change
through
a
number
of
steps.
Forget
how
many
steps
I
mean.
O
O
So
what
do
we
want
from
these
attestations?
You
know-
and
you
know
how
what
are
the
things
that
are
going
to
be
contained
in
these
attestations
to
help
a
receiver
understand
what
it
is
that
it's
looking
at,
so
these
attestation,
through
brenner,
carry
first
a
notion
of
you
know
what
was
this
trusted
party
that
did
the
validation,
this
notion
of
a
trusted
would
anchor
and
so
the
the
reason
the
receiver
is
going
to
have
to
make
some
sort
of
determination,
which
particular
set
of
trusted
validators
is
going
to
use.
O
So
that's
you
know,
then,
the
the
test,
testing,
token
or
certificate
is
going
to
have
to
have
a
number
of
things
describing
what
it
is
that
it
has
validated,
and
these
are
things
like
you
know.
What
is
that
legal
entity
that
is
going
to
have
the
the
rights
to
that
logo,
or
potentially
also
a
name?
It's
also
going
to
have
a
binding
to
domain
names
associated
with
that
that
particular
logo
and/or
name,
and
in
addition,
you
know
with
that
validation.
O
You
know
it
has
logos,
of
course,
as
part
of
the
registration,
it
provides
a
set
of
standards
for
doing
you
know
things
like
determining
you
know
what
what
are
the
different
things
you
know,
comparing
basically
the
logo
to
other
things.
It
also
provides
things
like
you
know,
public
records
that
can
be
used
for
that
validation
and
also
even
having
things
like
a
review
process
to
ensure
that
you
know
other
things
out.
There
aren't
going
to
conflict
with
that
identity.
O
So
there's
this
notion,
I
mean
in
in
registered
trademarks
of
basically,
you
know
proving
that
it's
not
going
to
be
confusable
with
some
other
other
logos.
There's
a
legal
test
in
the
trademark
process.
Registration
process
called
likelihood
of
confusion
tests
and
that's
one
of
the
things
that
can
be
helpful
in
preventing
some
of
the
potential
attacks.
Basically,
it
also
provides
means
for
in
that
review
process
of
at
least
you
know,
removing
things
like
a
bijection
ball
and
its
leading
content.
O
O
So
the
logo
types
was
proposed
is
at
least,
and
this
is
basing
largely
on
what
was
done
in
x.509-
there's
two
ourseives
about
logo
types
RFC.
You
know
three,
seven,
zero,
nine,
as
well
as
six
months
md
that
helps
specify
you
know
what
we
proposed
to
use
and
where
we
propose
to
use
for
at
least
a
logo
format
its
SVG
and
in
order
to
secure
it,
we
need
to
use
a
particular
profile.
First,
you
know
the
SVG
tiny
profile
is
targeted
at
low
memory
footprint,
clients,
and
it
also
cannot,
you
know,
have
script
tags.
O
O
We
also
want
to
make
sure
that
this
logo
type
is
associated
to
a
particular
jurisdiction.
That
says
where
it's
going
to
be
valid
and
we
want
there
to
be
a
name
so
see
it's
optional,
but
what
would
speak
to
is,
as
was
noted
before
this
is
a
way
of
you
know,
answering
that
question
about
accessibility,
so
no
blind
users
could
potentially
have
an
identity
that
they
could
understand
and
then
also
one
of
the
open
questions
with
this
is
basically
you
know.
What
could
you
about?
You
know
multiple
jurisdictions.
O
So
when
you
know
a
sender
sends
out
a
message,
they
may
not
know
where
that
message
ends
up
in
and
then
so
how
right
now
the
current
spec
that
we've
published
basically
only
allows
for
one
logo
and
name.
Potentially,
this
is
a
problem
for
localization
and
that's
an
open.
How
we
do
that's
an
open
question,
so
going
back
to
that,
you
know
some
of
the
evita
type
attacks
and
then
maybe
some
of
the
remediations
that
this
particular
process
may
provide.
O
You
know
first,
for,
like
you,
know,
striping
of
Delaware
versus
Kentucky.
You
know
first
off
one,
of
course,
is
you
know,
state
versus
in
national
level,
but
actually
really
what
it
is
is
saying
that
okay,
these
things
are
only
going
to
be
valid
for
a
particular
jurisdiction,
and
you
know,
probably
the
process
would
be
to
to
put
that
information
in
and
and
have
clients
use
it.
O
Then
what
we
also
could
do
is
you
know
if,
since
we
proposed
that
it's
a
really
good
idea
to
have
some
sort
of
transparency
mechanism
as
part
of
this
process,
and
that
we
could
consider
that
this
transparency
process
may
even
provide
a
means
by
I'm
having
a
review
period
during
issuance?
That
may
help
with
some
of
these
problems.
O
Now
that
you
know
having
having
review
period
as
part
of
issuances
a
new
thing
that
that
you
know
hasn't
been
specified,
but
you
know
it's
a
concept
that
I
think
has
been
thought
about
before
it's
one
that
we
think
could
be
really
helpful
in
particularly
for
these
types
of
identities,
the
identity
verified
case.
You
know,
so
we
note
that
the
the
registration
process
is
meant
to
also
filter
out.
You
know
misleading
indicators
and
names.
You
know,
potentially,
that
review
process
may
have
caught
something
like
identity
verified.
O
You
know,
possibly
and
again
you
know
things
like
transparency,
potentially
with
the
you
know
that
preview
process
could
be
helpful
and
mitigating
or
certainly
scoping,
out,
identity
attacks
like
that
and
then,
with
regards
to
this
issuance
intentional
or
unintentional.
That
again,
you
know
it's
something
that
perhaps
is
best
addressed
by
some
sort
of
transparency
mechanism.
O
Okay,
so
a
certificate
transparency,
so
certificate
transparency,
you
know,
RFC
1662
is
a
mechanism
by
which
you
know
what
what
it
allows.
The
echo
system
to
have
is
some
sort
of
way
of
getting
a
global
view
of
the
echo
system
and
that's
been
particularly
helpful
in
finding
a
scope
of
a
particular
problem
once
when
it's
found
it
is.
It
is,
of
course,
a
retrospective
technique.
O
O
One
of
the
issues
that
we've
recently
come
across
is
a
concern
that
okay,
so
these
these
trademarks,
they
have
legal
properties
attached
to
them.
They
also
may
contain
content
that
is
very
problematic,
potentially
that
very
problematic
content
may
be
checked
during
the
registration
process,
but
it
may
be
missed,
particularly
by
a
very
insecure
in
some
sense,
issuer
or
maybe
intentionally
attacked.
O
That
would
be
a
problem,
and
then
you
know
what
to
do
about
when
this
trademark
material
has
either
expired
or
due
to
some
court
order,
has
changed,
basically
ownership
and
what,
if
that
new
owner
wants
to?
Basically
you
know
remove
that
content,
it's
it's
potentially,
it
is
simply
a
difficult
problem
and
you
know
how
do
we?
How
do
we
solve
that
that
that's
a
in
some
sense?
It's
been
I,
believe
I've
heard
it's
been
a
problem.
That's
been
fought
quite
a
bit
about
in
the
you
know,
the
few
key
community,
but
I
think
it'll,
be.
O
You
know,
become
more
of
a
much
more
of
a
pressing
problem
if
when,
if
and
when
we
start
doing
these
trademarks
inside
these
certificates
and
lastly,
if
we
go
down
the
right
of
doing
token,
transparency
which
are
going
to
be
short-lived,
especially
very
short-lived
tokens,
what
happens
when
we
have
to
log
all
the
tokens?
There
are
already
scaling
issues
inside
certificate
transparencies.
This
would
definitely
amplify
it.
How
do
we
solve
those
types
of
problems?
A
I
Yes,
so
so
this
is
the
the
our
our
final
wrap-up
of
the
scary
problems
that
still
remain.
Even
after
all,
this
is.
We
haven't
solved
the
look-alike
indicator
on
a
look-alike
domain
problem
and
that's,
that's,
obviously,
an
issue,
but
that's
still
a
problem
that
exists
today.
It's
not
an
it's,
not
a
new
problem,
that's
being
created,
but
it's
it's
not
a
fun
one
then
there's
also
for
those
similar
ones
like
PayPal,
vers.
I
Pandora
comes
up
all
the
time
when
you
talk
about
logos,
but
that's
not
a
phishing,
better
they're
not
going
to
attack
each
other
unless
one
of
them
screws
up
they're
off
and
then
someone
can
use
bad
off
on
one
to
attack
the
other
so
that
we
want
to
open
up
to
everything.
So
if
I
got
everyone
join
me
up
here
and
let's,
let's
firing
squad
time,
let's
do
this,
did
you
about
that
next
slide,
yeah,
and
so
this?
This
is
one
yep,
and
this
is
this-
is
what
we're
proposing.
We
know.
A
Open
up
the
floor,
I
just
wanted
to
do
a
little
bit
of
scoping.
Sorry,
thanks
so
I
think
just
to
put
a
little
bit
of
framing
around
the
discussion
here,
especially
around
this
validation
question.
I.
Think
some
of
the
earlier
questions
have
established
that
you
know
the
IETF
is
not
going
to
define
validation
procedures
here.
The
validation
is
largely
going
to
be
outside
of
this,
so
I
think
the
guidance
there's
already
a
piece
of
feedbags.
A
The
proponents
here
that
you
know,
there's
gonna,
be
a
threshold
question
for
doing
any
IETF
work
that
there
there
be
some
plausible
process
there.
You
know.
So
it's
a
before
you
come
back
and
actually
make
it
proposals.
If
you
work
like
you,
don't
need
to
have
a
plausible
proposal
there
and
so
I
think
for
the
most
part.
Let's
consider
you
know
kind
of
stipulate
that
that's
something
to
be
done
in
the
future,
and
you
know
the
focus
of
the
IETF
work
here.
A
R
Campbell
and
I
hope
this
is
an
easier
question,
because
you
just
put
up
a
lot
of
scarier
things
after
I
thought
about
it.
When
you
talk
about
shortly
certificates
of
short-lived
tokens,
especially
we
talk
about
very
short-lived
tokens.
These
things
to
me
make
sense
when
we're
talking
about
the
TLS
world,
but
I
wonder
what
you've
thought
about.
When
we
talk
about
mail
as
a
very
different
time
horizon,
you
know,
conceivably
things
can
take
a
few
days
to
get
from
the
sender
to
the
receiver.
That's
not
that's!
R
Not
common,
but
more
commonly
I
have
at
least
15
years
of
archives.
So
what
is
your
expectation
of
what
happens
to
old
male
that
has
logos
on
it
when
those
certificates
or
or
such
have
expired
now,
I'm?
Assuming
that
the
relying
party
is
the
MTA
and
I
never
looks
at
that
mail
again,
which
would
make
me
assume
these
logos
will
continue
to
get
displayed,
but
I
don't
know
if
that's
the
right
thing,
especially
if
one
of
them
turned
out
to
be
malicious
and
that's
why
they
were
allowed
to
expire
a
revoked
or
something.
R
O
Mean
well,
I,
I
think
we
all
agree.
This
is
a
problem
that
is,
it's
basically
still
open.
I
mean
we
can
think
of
mechanisms
by
which
we
can
remediate
some
of
these
things.
You
know,
certs
are
long
live
for
example,
and
they
have
like
a
revoke
a
ssin
process
if
you
know,
even
if
they're
long
lived,
but
that
introduces
a
new
set
of
problems
or
we
can
make
them
very
short-lived,
but
then
you
know
we
have
a
lot
more
in
sometimes
work
to
do
to
basically
refresh
refetch,
and
so
there's
this
trade-off
and
I.
O
S
Maximal
equivalent,
a
couple
of
considerations
when
you
were
comparing
JWT
is
with
x.509
certificates.
You
notice
that
there's
a
completely
set
of
support
for
the
two
types.
This
comes
from
the
fact
that
my
opinion
one
tries
to
assert
identities.
The
other
try
to
give
you
permissions
to
do
something.
This
is
the
way
they
were
born
and
usually
the
two
in
a
good
system
are
kept
orthogonal,
so
you
assert
the
identity,
and
then
you
get
your
so
I.
S
Don't
see
that
to
be
something
one
or
the
other,
it
would
be
probably
more
one
endian,
probably
in
the
final
technical
solution
which
I
don't
know
exactly
how
that
might
be.
This
second
thing
is
about
you
know,
discussion
about
validations,
etc.
We
deal
with
that
all
the
time,
and
since
that
you
know
we
have
lots
of
vendors.
They
said
that
they
wants
to
put
logos
in
in
our
products
or
cable
related
stuff,
and
we
have
very,
very
strict
procedures
for
that.
S
That
means
that,
for
example,
when
you
request,
if
you
get
even
with
validated
you
once,
we
continue
to
validate
you
and
your
rights
to
use
that
particular
name
every
single
time.
This
is
completely
different
than
the
web.
Pki
I
understand
that,
but
we
are
very
strict
on
that
and
it's
true
what
we
shall
say
is
a
policy
decision,
and
so
PKI
can
come
with
policies
and
all
the
procedures
related
to
audits,
etc.
That
doesn't
mean
if
the
web
trust
old
it.
S
It
means
that,
if
you,
if
you
start
your
ecosystem
for
the
main
purposes
right
for
the
meal
to
validate
email,
logos,
etc,
it
could
be
a
completely
separate
PKI
that
might
be
trusted
by
browser
mm.
Tas
or
you
know,
is
their
choice
right
and
as
long
as
you
define
the
good
rules
to
validate
these
topics,
for
example,
only
set
trademark
logos-
and
you
know
and
add
this
very
set
procedures,
then
then
there.
S
T
O
O
Also
on
your
second
point
that,
yes,
there's
a
you
know
a
a
scope
of
governance
choices,
and
this
is
also
something
we
would
like
to
have
discussion
about.
As
to
you
know
what
is
sort
of
the
right
approach
for
the
governance
I
mean
granted.
Some
of
the
things
are
not
necessarily
ITF
issues,
but
is
something
we're
very
cognizant
of,
and
you
know
we
we
would
like
feedback
basically
about.
U
I
Sorry,
I
I
think
I
glanced
over
that
in
the
effort
to
be
fast,
they're,
basically
published
HTTPS
URLs
that
are
SVG's,
and
you
can
store
that
anywhere,
there's
no
binding
to
the
domain
so
that
you
can
change
that
as
you
need
to
as
long
as
the
Hat
matches.
What's
validated,
it's
the
appropriate.
Oh,
that's
also
why
we
didn't
feel
the
need
for
DNS
SEC
on
that,
because
the
certificate
is
stored
somewhere
else.
We
validated
and
you're
looking
for
the
hatch
hashes
to
manage,
then.
U
I
It's
that's
what's
published
in
the
DNS,
that's!
What's
in
what
we're
calling
an
assertion
record
for
bimmy
right
and
that
way
you
can
pull
it
and
cache
that
and
that's
on
a
per
domain
basis
and
then
a
message
from
that
domain
right:
it
can
be
completely
transparent.
No
one
in
the
middle
needs
to
be
wise.
What
happens.
V
The
large
corporations
that
aren't
currently
doing
Demark
to
protect
their
users
from
fishing
will
be
incented
because
now
they'll
get
their
logo
displayed.
Is
that
in
the
get
their
logo
properly
displayed
in
the
right
place
because
well
first
of
all
is
that's
true
incentive?
Okay,
so
that
users
will
then
a
miracle
will
happen
in
users,
will
learned
or
mta's
will
reject
non
Demark
mail
because
it's
posted
the
right,
because
the
mail
will
not
go
through
if
there's
no
D
mark
record.
So
the
idea
being
that
the
logo
is
a
good
enough
incentive.
V
V
The
only
way
to
make
that
work,
it
seems
is
you
need
a
globally
a
global
level
playing
field,
legal
regime
of
intellectual
property.
Is
that
correct?
Do
you
know
of
one
that's
my
point,
I
know
of
one
instance
where
it
was
been
tried.
So
far,
the
ICANN
domain
top-level
domain
trademark
resolution
policy.
W
John
Peterson
I
do
some
of
that
stir
stuff
that
you
were
talking
about.
I
guess,
I
found
yeah
I
mean
I
mean
I
was
coming
up
here
to
talk
about
that
kind
of
distinction
between
the
the
cert
and
the
job,
and
we
obviously
in
the
stirrer
work
kind
of
we
generate
these
jobs,
not
to
start
the
same
kind
of
purpose
as
a
syrup
right.
It
seemed
the
way
you
presented
it
kind
of
like
an
apples
and
oranges
conversation
because
certs
are
intended
to
be
very
long-lived.
W
Identifiers
used
to
signing
the
test
things
and
the
jobs
like
the
kind
of
thing
gets
signed
by
them
on
like
a
per
call
or
per
attestation
basis.
Right
and
I
mean
I
guess
when
I
was
listening,
the
conversation
I
kind
of
assumed
that
the
cert
then
would
be
where
the
logo
lives,
and
that
whoever
the
circuit
Authority
was
would
be
the
one
attesting
the
logo
but
I
guess
that's
not
right.
I
I
The
original
intent
was,
you
published
the
logo,
and
then
you
could
have
a
number
of
different
validations,
some
of
which
don't
use
certificate,
or
what
have
you
so
that
it
was
a
uniform
mechanism,
no,
regardless
of
validation
type
through
the
certificate
that
way
proposed.
The
logo
is
also
in
the
certificate.
Okay,
it.
I
W
So
a
couple
points
about
that
one
is
in
terms
the
web
bug
speaking
us
is
a
bit
of
the
DNS
provider.
I
here
are
some
DNS
people
like
to
track
users
to
and
that
querying
that
doesn't
actually
a
gate.
Any
of
the
concerns
that
we
have
about
these
things,
websites,
it
just
changes,
who's
gonna,
be
able
to
mine
your
data
I,
also
again,
I.
Think
I'm
interested
in
things
like
this
for
start
right
and
I
believe
that
there
are
a
couple
of
probable
solvable
problem
spaces
solvable
problem
spaces
are
in
this,
like
actual
winnable
games.
W
But
doing
this
all
is
one
big
thing
that
is
like
linking
in
certificates
and
email
and
the
DNS
and,
like
all
this
WIPO
kind
of
stuff
is
what's
really
over-the-top.
Oh
this,
you
know
and
I'd
be
happy
to
talk
to
you
guys
about.
We
used
to
chop
this
up
into
things
that
might
be
more
module
or
potentially
solvable
in
some
small
areas.
Also,
if
you
guys
actually
looked
at
WIPO
at
their
global
intellectual
property
database
that,
like
actually
has
like
logo
listings
that
are
registered
in
it,
and
here
it's.
O
Why
soil
my
understanding
to
it
is
that
eight
it
provides
a
means
to
do
registration
across
many
different
jurisdictions.
Vulcania
Slee.
It,
however
itself
doesn't
I,
think
assert
a
certain
it's
effectively
legal
registration.
It
depends
on
other
member
countries
to
do
that,
for
it
so
I
mean
it
can
help.
W
O
Yeah
I
mean
if
international
fear
I
forget
the
details,
if
it's
through
the
UN
or
it
might
have
actually
existed
actually
before
the
UN
I.
Don't
don't
remember
the
details,
but
but
the
thing
is
the
registrations
it
has.
It
simply
identifies
a
registration,
but
it
references
other
things
that
become
the
sort
of
legal
home
for
those
things.
Okay,.
X
Hello,
David,
Skinner's
e
first
clarifying
question
so
in
maybe
I
miss
something
because
I'm
a
little
confused
at
the
beginning
of
the
talk
you
mentioned
that
the
you
you
aren't
planning
on
the
user
behaving
differently
with
this
image.
So,
if
like
how
the
image
looks-
and
there
is
not
aimed
at
having
the
user
react
to
it
and
change
their
security
behavior,
what's
the
benefit
of
signing
it?
Why
why
not
just
have
a
system
that
puts
an
image,
that's
like
similar
to
how
five
icons
work,
I.
O
X
O
X
Just
to
clarify
my
understanding,
so
let's
say
I'm,
not
MasterCard
and
I,
send
you
I,
send
a
user,
an
email,
pretending
to
be
MasterCard.
I
have
a
fishing
domain
and
I
have
a
logo
that
looks
like
MasterCard.
Are
you
saying
that
this
proposal
prevents
them
from
or
makes
it
less
likely
that
they'll
click
on
the
phishing
link,
because
you
seem
to
you
said
that
that
was
out
of
scope
and
not
what
you
wanted
to
do
with
this
at
the
beginning,
so,
like
I'm
I'm,
just
missing
the
whole
point
of?
X
O
So
what
we
don't
want
to
do,
because
there's
academic
research
on
this
is
that
if
users
see
something
they
you
know,
some
sort
of
users
are
in
fact
going
to
trust
that
logo
and-
and
you
know,
go
click
on
that
link
and
all
of
that
stuff.
However,
I
think
what
you're
asking
is
do
these
things
provide
some
sort
of
positive
security?
That
users,
in
fact
really
good,
should
always
go
look
for
these
things,
and
actually
the
research
is
showing
no,
they
don't
really
pay
attention
in
the
general
place
two
weeks.
So,
ok.
Y
X
Y
Asking
how
it
works,
I'm
asking.
What
does
this
give
me
as
a
user?
If
you're
a
phishing
site,
publishing
image
of
MasterCard
from
your
domain,
then
it
wouldn't
display
if
the
system
works
properly,
all
right
unless
you've
got
a
somebody
vouch
for
it
and
that
image
not
displaying.
What's
the
benefit.
X
Sorry
I'm
trying
to
tease
this
apart,
because
that
the
first
slide
said
that
the
benefit
was
not
to
have
users
click
on
phishing
or
not
like.
If
that
was
one
of
the
first
slides
I
thought.
That
was
the
benefit.
That's
what
I
assumed
when
I
walked
into
the
room.
That
was
to
help
prevent
attacks
like
fishing,
but
that
was
an
on
goal,
so
I'm
asking
what
the
benefit
is.
So
the
the
benefit
was
specifically
about.
Z
U
X
AA
X
X
This
goal
and
benefit
seems
incredibly
limited
to
me
and
the
problems
you've
like
that,
a
really
good
job
of
describing
and
these
studies
and
all
these
things
like
sound
incredibly
hard,
not
to
mention
very
likely
impossible.
So
the
cost
here
in
the
ITF
would
be
high.
I
see
a
lot
of
very
smart
people
in
this
room
who
are
spending
a
lot
of
time
for
this,
a
lot
of
smart
people
on
the
mailing
list.
So
my
ask
is:
please:
please
do
not
continue
this
work
in
the
ITF.
The
benefits
are
not
worth
the
cost.
Z
And
I
wasn't
going
to
either
but
Wendy
seltzer
and
yes,
I
sort
of
following
up
on
David's
point.
I
was
sitting
having
a
very
difficult
time
figuring
out
what
a
mail
user
agent
would
be
doing
for
its
end
user,
the
mail
reader
because
I,
don't
know
a
lot
of
end
user
mail
recipients
who
say
I
want
more
logos
in
my
inbox
and.
D
There
are
already
a
number
of
implementations
of
this
today
that
already
exist.
I
mean
that
it's.
This
is
not
the
first
time
we're
not
proposing
this
as
a
new
thing,
I
mean
they
already
exist
today,
I
mean
I,
can
pull
out
my
phone
and
show
you
I
have
a
pile
of
logos
in
my
inbox
from
from
a
mail
provider,
so
I
does
that
sort
of
answer
I
mean
I,
don't
know
if
it
becomes
a
competition
thing
to
say
like
oh,
you
know
now,
Apple
needs
it.
Thunderbird
needs
it.
D
Z
And
then
my
other
point
as
a
lawyer
and
perhaps
I
don't
know
if
there
are
other
lawyers
in
the
room,
but
the
collection
of
trademark
problems
that
that
you
identified
has
tangled
the
crowd
over
at
ICANN
and
the
trademark
Clearinghouse
in
knots
for
years
and
years
and
hundreds
of
millions
of
dollars,
and
so
I
would
advise
that.
Bringing
that
problem
into
this
space
is
not
going
to
help
us
to
make
progress.
E
AA
The
the
questions
that
you
sort
of
looked
at
when
you
come
into
working
into
a
boss
like
this
is
you're
looking
to
see
that
there's
a
group
of
people
who
are
interested
in
doing
the
work
that
seems
reasonably
well
understood
that
the
work
is
possible
and
I
snag
on
that
point.
I
think
we're
seeing
that
here
and
with
we've
got
one.
AA
These
people,
in
this
room
and
probably
the
community
at
large
that
what
you're
doing
is
possible
and
when
I
say
possible,
I
mean
you're
gonna
ship
it
and
people
are
going
to
believe
it
and
you're
not
going
to
be
subject
to
to
fishing
and
I.
Don't
think,
there's
any
expectation,
there's
a
ridiculously
high
standard
here
for
any
of
this.
If
the
paypal
pandora
thing
isn't
addressed,
then
I
think
we
might
say
that.
AA
Oh
well,
that's
that's
a
remarkably
good
system
that
we're
now
worrying
about
that
particular
aspect
of
of
the
problem,
but
we've
got
such
a
long
way
to
go
before
we
get
to
that
point
and
the
confusable
problems.
The
trademark
disputes
the
whole
system
of
establishing
who
owns
what
and
all
of
that
business
is
so
fraught
that
if
you
come
back
and
have
another
buff
and
we're
having
this
discussion
and
people
are
being
convinced,
I'll
be
surprised
but
impressed
at
the
same
time.
AA
L
J
So
I
think
this
discussion
about
the
the
the
costs
and
benefits
is,
is
potentially
a
key
for
for
this
effort
or
an
approach
to
think
about.
That
would
be
useful.
I
I
guess
I'm
joining
the
list
of
people
who
are
calling
for
please
figure
out
what
you
know.
The
high
level
business
legal.
Your
restriction
thing
is
before
you
do.
The
protocol
design
at
this
point
seems
a
little
early,
so
I
and
and
I
I,
don't
wanna,
discourage
anybody
and
and
I.
J
You
know
the
world
is
taken
forward
by
people
who
actually
think
about
new
things
and
design
new
structures,
and
maybe
we
need
something
in
this
basement.
Maybe
not,
maybe
you
can
decide
it,
maybe
not,
but
but
I
think
that's
the.
That
is
the
step.
One
like
you
figure
out
the
high
level
design,
not
not
the
protocol
design,
but
but
the
business
and
legal
legal
parts.
J
If
you
have
an
answer
for
that
and
and
I
might
be
also
surprised
others
if
we
find
an
answer
to
that,
that'd
be
great,
but
let's
do
that
first
and
then
then
come
back.
If
you
have
an
answer
and
and
there's
I
mean
you're,
actually
an
interesting
problem,
I
I
would
like
rather
think
about
that
and
some
of
the
protocol
details
and
certificates
and
such-
and
there
are
also
many
pitfalls
there.
In
addition
to
everything
that's
been
discussed,
you
could
fail
in
multiple
different
ways.
You
could,
for
instance,
try
to
have
something.
That's
you
know.
J
K
K
So
the
ietf
we
try
to
solve
technical
issues
right
so
as
Pete
nicely
put
a
minute
ago.
What's
the
benefit
to
the
receiver
and
thus
under
where?
Where
is
the
problem
between
those
two
that
we
are
fixing
with
a
solution
and
the
problem
as
I
see?
It
is
that
you
actually
have
a
business
case
that
you're
actually
trying
to
put
forth
right,
because
the
reality
is
the
the
carrot
that
you're
using
is
entirely
business
incentive
right,
there's
no
security
attached
to
it.
You
see
you've
stated
that
there's
no
desire
to
do
anti-phishing
or
anything.
K
So
the
purpose
of
displaying
an
EB
cert
thing
goes
away,
because
what
web
browsers
would
never
display
a
needy,
cert
symbol
for
an
needy
cert
that
would
like
shoot
them
and
then,
but
on
this
half
there
is
nothing
to
DN,
sent
avise
a
mail
reader
from
forming
a
business
relationship
to
display
a
logo.
Anyway,
right
all
your
entire
mechanism
can
be
circumvented
with
cash
right.
K
A
company
can
come
forward
and
say
you
know
mail
reader
I
want
I,
want
to
pay
you
to
put
my
logo
there
anyway,
I,
don't
I,
don't
want
to
go
through
d
mark
I!
Don't
want
to
you
know,
do
everything
else,
I
just
want
to
give
you
cash
and
I
bet
you
that
most
people
would
take
it
right,
because
there's
no
D
incentive
for
them
not
to
display
the
logo.
It's
entirely
a
business
relationship.
K
This
greatly
eases
that
business
relationship,
because
now
there's
a
mechanism
for
you
to
publish
it
in
one
location
as
opposed
to
every
company
having
to
go
to
multiple
locations
to
get
their
logo
displayed.
So
the
the
discrepancy
here
is
that
the
ATF
is
very
focused
on
a
technical
solution,
and
yet
this
is
this
is
tying
a
business
solution
to
a
technical
solution
and
that
is
historically
not
fared.
Well,
unfortunately,
all.
H
Right
Steven
file,
Edie,
try
not
be
repetitive,
I,
don't
think
anybody
said
it
explicitly
as
a
user
I
would
not
like
this.
I
would
rather
not
have
this
and
I
don't
want
my
may
user
agents
to
start
adding
this
and
then
not
to
have
a
checkbox
to
turn
it
off.
So
it's
I.
Don't
think
that
anybody
had
said
that,
but
I'd
say
aren't.
H
I
use
Thunderbird,
but
nonetheless,
regardless
of
I,
don't
sorry
there's
a
data
point
there
that
not
all
users
will
want
this
covered,
in
fact,
I
think
so.
I
think
we're
on
again
back
to
the
red
book
thing.
You
have
an
implicit
kind
of
assumption
that
if
you,
even
if
your
MTA
you're
in
Belmonte
I,
did
cache
this
logo,
for
you
Ben's
point
about
opening
up
old
emails
kind
of
means.
They
have
to
keep
a
binding
between
that
URL
and
the
original
one
forever.
E
From
gondwana
I've
been
putting
together
a
summary
of
what
I
thought
everyone's
been
saying
here
that
the
goal
for
the
sender
is
to
get
the
brand
loader
logo
displayed
in
front
the
end
user.
They
will
make
an
effort
for
that
goal,
for
the
mailbox
provider
is
to
get
more
signed,
email
and
upgrade
the
ecosystem,
so
they
will
accept
this
to
get
that
result
for
the
end
user.
The
goal
is
that
they
get
less
fraudulent
email
and
I.
E
Think
that's
probably
the
least
well
to
find
out
of
this,
given
that
you
can
fake
out
looks
calm,
given
that
the
brand
identifier
is
not
going
to
be
recognized
anyway,
outlook
with
a
zero
and
it
all
over
instead,
again
I
think
the
end
user
probably
gets
the
least
value
out
of
this,
and
we've
got
a
roomful
of
a
lot
of
people
who
end-user,
as
their
main,
I,
guess
experience
with
this.
Rather
than
being
a
sender
or
a
mailbox
provider,
so
obviously
to
anyone
in
the
end-user
position.
This
doesn't
look
particularly
valuable,
I
guess.
E
S
S
Maybe
you
could
try
to
test
as
actually
adding
value
like
security,
for
example
like
if
you
take
this
as
a
business
business
requirement
that
you
have
combined
that
with
something
that
is
really
valuable
for
the
idea,
maybe
increment
the
security
of
email.
What
about
what
about?
If
we
do
an
experiment
where
we
use
certificate
with
logo,
so
we
don't
have
to
write
specification
initially,
you
you
have
your
mail
server,
signing
the
emails
that
you
want.
S
You
know
in
this
experiment
that
you
want
the
user
to
visualize
with
the
logos
that
might
be
a
way
to
understand.
First
of
all,
how
use
it
my
my
respond
to
that
and
you
can
cooperate
with
some
open-source
software
to
see
how
to
integrate
this
display,
which
should
not
be
in
the
body
of
the
email,
of
course,
in
a
dedicated
indicator,
because
otherwise
it
would
be
spoof
Ileana.
S
This
is
this
will
be
great
and
I
would
suggest
that
you
look
into
this
combined
using
the
business
require
that
you
have
to
finally
be
try
to
deploy
this
no
certificate
or
security
as
mine
for
the
large
majority
of
your
users.
That
would
be
amazing
and
I.
Would
love
that
but
I?
Fortunately,
don't
think
that
this
is
the
right
way
to
do
it,
not
nothing
about
technical,
but
just
not
combining
this
added
value.
Try
to
do
that
and
I
think
that
this
community
would
be
a
lot
more
open
to
discuss.
X
X
Since
then,
I've
been
to
brand
indicators
org,
which
I
think
is
related
to
your
effort
and
on
the
first
page
of
why
brand
indicators
it
says,
stop
fishing
so
I
and
now
change
my
assessment
of
like
not
very
great,
to
actively
harmful
I
think
this
brings
a
sense
of
false
security
and
is
actually
harmful
to
the
ecosystem
as
a
whole.
My
points
earlier
about
asking
for
this
work
to
not
continue
in
the
ITF
still
halt.
AB
Jeffrey
askin
I've
heard
concerns
earlier
that
male
will
agents
will
display
the
logo
without
requiring
Demark
because
they
get
paid
or
whatever,
because
there's
no
technical
reason
to
tie
those
for
the
existing
systems
that
are
showing
logos.
Do
you
know
if
they
are
requiring
Demark
in
order
to
do
so,.
I
AC
D
I
AA
N
E
I
Do
you
wanna
take
so
the
the
this
short
answer
to
that
is
right.
Now,
logos
are
coming
from
all
sorts
of
different
places,
and
the
point
of
this
is
to
say:
let's
stop
doing
this
in
a
haphazard
way
and,
let's
make
sure
we
use
a
source
and
that
source
is
validated
and
we
know
it's
tied
to
the
message
being
authenticated
and.
I
Of
course
not,
but
this
builds
over
time
and
adds
value
and
there's
a
clear
path
to
this
doing
a
lot
more
good.
The
short
term
is
clearly
fragmented.
That's
why
we're
here
talking
about
figuring
out
a
way
to
do
it
in
a
standard
manner,
but
your
point
is
accurate
right,
like
that,
that's
exactly
the
that's
the
short
term
adoption
problem,
but
adoption.
N
C
A
Right
so
we
are
just
a
couple
minutes
left
from
the
end
of
our
slot.
This
is
a
Boff,
but
it
is
not
a
working
group
forming
buffets
I
would
call
it
a
more
feedback
collection
broth.
So
we're
not
going
to
ask
the
difficult
off
questions,
but
let
me
ask
the
proponents
here:
like
our
you
know,
you've
got
a
lot
of
feedback.
Are
there
any
things
that
you
know
you
were
hoping
to
cover
that
you
didn't
cover
and
a
lot
you'd
like
to
bring
up
in
the
last
couple
minutes.
No.
I
I
think
we
covered
what
we
covered.
We
covered
the
problems,
we
got
some
new
ones
and
that's
why
we're
here
right?
We
we
understand,
we
don't
have
a
perfect
understanding
of
the
problem
space,
and
this
has
been
very,
very
helpful
and
you
know
we
well
as
I
think
Martin
said.
The
second
ball
will
either
be
a
surprise
or
really
think
but
know
this.
This
is
this
is
why
we're
here
is
for
those
feedback,
and
we
thank
you
all
for
participating
and
also
we
got
one
final
question
or
is
that
you
Barry
no.
S
It's
just
say
just
a
comment:
as
a
user
and
differently
from
I
would
like
to
have
something
that
adds
security,
and
if
it
comes
with
a
logo-
and
you
figure
out,
you
know
the
trademark
etc
say
not
here,
I
would
be
happy
with
to
have
something
so
I
would
not
discourage
you
to
not
do
it,
but
not
do
it
in
this
way,
I
would
try
to
look
look
in
your
business
case
if
there's
the
case
for
really
adding
real
security.
As
you
know,
the
indication
on
the
website
says
you
know.
