►
From YouTube: IETF104-WGTLGO-20190327-1500
Description
This Technology Deep Dive from IETF 104 covered:
* "Spherical Routers"
* Spencer
* Forwarding Plane Realities + Q&A
* Frank Brockners, John Scudder, Toerless Eckert
* Summarizing implications for protocol designers
* All - this is a working session
* Next Steps for the summary of implications for this topic
* Chairs
* Next Steps for Technology Deep Dives on other topics
* Chairs and AD
More info at:
https://datatracker.ietf.org/meeting/104/materials/agenda-104-wgtlgo-02
https://datatracker.ietf.org/meeting/104/proceedings/
B
C
C
Okay,
we're
going
to
get
started,
welcome
you
to
the
technology
deep
dive
on
spherical,
rubbers,
40,
plane,
realities
and
implications
for
protocol
designers,
and
we
are
at
least
for
now
working
on
whether
we
have
consensus
to
pronounce
it
as
we
got
Lego
I'm
Spencer
dawkins.
This
is
the
lovely
alvaro
available
Karen
to
my
left
and
we
will
be
your
host
for
the
next.
D
E
E
C
And
so
this
is
a
IETF
activity,
so
we
put
the
note
well
slide
and
trust
that
people
have
read
it
and
then
they
will
make
the
choices.
So
we
had
this
as
our
agenda
and
bashing.
It
is
okay,
just
to
do
administrivia
and,
like
we
said
so,
the
pronunciation
is
we
got
Lego
for
until
we
come
up
with
a
better
one,
it
stands
for
we
got
the
last
good
one,
because
Warren
said
all
the
good
ones
are
taken
with
Cindy
asking
for
an
acronym
and
I
said:
oh
no,
we
got
the
last
good
one.
C
It's
gonna
be
like
this.
The
whole
afternoon
guys
have
fun,
so
we
did
the
know.
Well
we're
willing
to
bash
the
agenda.
You
know:
wouldn't
talk
for
a
few
minutes
about
what
we
do
at
a
technology.
Deep
dive,
I'm
gonna
talk
for
a
few
minutes
about
spherical
routers,
smart
people
about
40
playing
realities.
We're
going
to
talk
about
forwarding
plane
realities
could
be
frank,
john
and
taurus
we're
going
to
be
summarizing
implications
for
protocol
designers,
and
this
is
the
part
that
I
want
everybody
to
go
into
this
with
the
right
mindset.
C
This
is
a
working
session.
It's
not
tutorial
it's
a
working
session,
so
we
we
hope
to
all
come
out
of
here,
smarter
than
we
came
in,
not
just
not
just
some
of
us,
and
we
want
to
talk
a
little
bit
about
the
next
steps
for
the
summary
of
implications
for
this
topic,
and
we
want
to
talk
about
next
steps
for
technology
if
you
dives
on
other
topics
and
we'll
be
bringing
up
our
sponsor
URI
director,
the
lovely
warrant.
C
C
So
when
we
start
talking
about
doing
this,
we
were
saying
first
assume
a
spherical
router
with
it
zero
gravity
in
zero
degrees
temperature.
This
is
basically
the
you
know.
These
simplifying
assumptions
that
people
make
that
help
them
do.
Math
we've
hit
spherical
cows
at
the
ITF
for
a
very
long
time.
This
is
actually
Heather's
company
and
and
group.
You
can
see
the
spherical
calendar
business
cards,
saying
Moo,
but
this
is
now
spherical
rubbers.
Some
routers
really
are
spherical
thing.
C
They
we
say
they
exist,
but
most
routers
are
spherical
and
what
that
really
means
is
the
too
many
working
groups
encounter
a
contentious
cross
area
or
late.
Ietf
last
call
issues
most
recently
if
you've
been
involved
in
less
called
and
balloting
discussions
about
draft
that
was
using
ipv6
extension
hitters
in
a
kind
of
an
interesting
way,
but
there's
others-
and
you
know
these
are
late-
surprises
for
too
many
working
groups.
So
we
were
hoping
to
do
better.
One
and
I
thought
a
technology
team
that
I
might
be
useful.
C
Like
I
said
in
another
tutorial,
people
understand
how
routers
work
in
general.
What
we're
talking
about
is
a
cross
area
working
session
on
a
complex
topic,
so
I
started
recruiting
people
to
help
with
a
deep
dive
on
mother
router
sign
and
that
morphed.
Of
course
it
always
does
at
the
IETF,
and
here
we
are
now
what
we're
hoping
for
a
technology
deep
dives
we
to
complain
about
unstructured
time.
The
working
group
chairs
complained
about
unstructured
time
during
the
working
group
chair
session
on
Tuesday.
C
The
community
will
complain
of
the
IHG
about
construction
time
at
the
whiz
day.
Plenary
open
mic
in
just
a
couple
of
hours-
and
you
are
here
somewhere
in
the
middle,
so
I
would
encourage
you
to
aim
those
comments
where
they
are
most
likely
to
be
received.
Well,
so,
if
we're
not
doing
a
tutorial,
what
are
we
doing?
And
you
know
we
are
doing
and
Lauren
maybe
used
the
word
information-sharing,
but
he
was
the
one
that
actually
said.
Oh
great
could
speak
on
a
complex
cause
area
topic.
C
C
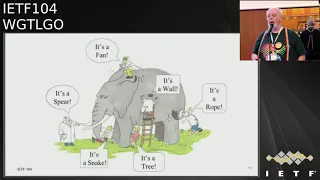
This
is
the
classic
picture.
What
I
think
we're
talking
about
we're
a
bunch
of
blindfolded
people
are
grabbing
pieces
of
an
elephant
and
they
know
very
clearly
what
they've
got
ahold
of,
but
they
don't
know
that
they've
got
ahold
of
an
elephant,
and
so
I
say
this
is
the
classic
picture
and
it
kind
of
see
it
kind
of
does
a
better
description
of
what
we're
talking
about
here
then
I
could
possibly
do
in
words
I.
C
E
E
Alright,
so
those
of
you
who,
who
looked
at
your
agendas
early
in
the
week
might
have
made
the
mistake
of
coming
in
here.
Thinking
that
we
were
going
to
talk
about.
You
know
some
kind
of
vision
for
the
future,
and
you
know
what
what
routers
for
the
22nd
century
are
going
to
be
and
actually
because
I
think
the
title
was
modern,
router
architectures
or
something
like
that.
But
but
it
turns
out
that
that
title
was
more
in
the
sense
of
my
undergraduate
class
on
modern
literature,
which
meant
19th
century
literature.
E
E
E
So
we
you
know,
start
out
by
talking
a
little
bit
about.
What's
a
what's
a
taxonomy
of
how
we
build
routers,
oh
and
one
sort
of
disclaimer
I
want
to
throw
in
right
at
the
beginning
and
by
the
way,
if
you
guys
yeah,
you
got
a
mic
too
so
whatever,
but
at
various
points
in
the
in
the
deck
I.
Think
we
talk
about
things
like
you
know:
high
performance,
routers,
large
routers
and
so
on.
It
turns
out
that
most
routers
now
are
high
performance
routers.
E
You
know,
according
to
this
definition
because
of
you
know,
economic
realities
and,
and
that
kind
of
thing
we
dive
into
focusing
on
one
particular
flavor,
affording
architecture
which
is
a
very
relevant
for
affording
architecture
and
end
up
kind
of
spitballing
on
what
are
some
things
that
protocol
designers
should
know
and
at
various
points
in
the
past
evidently
happened
because
oh
and
I
should
also
add
one
more
thing,
which
is
that
I
do
not
design
chips.
I
am
a
software
guy
and
I.
E
You
know
you
can
think
of
me
as
like
a
sock
puppet
operated
by
a
remote
guy
who
actually
does
design
chips
and
helped
craft
the
original
slide
deck
and
his
his
name
is
in
the
fine
print
there.
It's
only
in
fine
print
because
we
took
his
deck
and
butchered
it,
but
and
I'm
sure
there
are
people
in
this
room
right
now
who
know
more
about
designing
router
hardware
than
I
do
and
I
hope
that
you'll
come
up
to
the
mic
at
will
and
I
think
we're.
E
E
So
we've
all.
We
all
know
this.
We've
all
heard
this,
but
it
only
applies.
You
know
good
fast,
cheap
pick
to
it
only
applies
on
my
stuff
right
on
on
your
stuff.
I
want
you
to
have
all
of
it,
and
this
is
you
know,
kind
of
if
we
can
come
away
with
just
one
understanding
from
from
the
next
hour
or
whatever
it
is
it's
that
yeah
this?
This
applies
to
you
to
your
router
hardware.
Also.
G
There
is
an
so
I
wanted
to
maybe
start
before
getting
into
you
know
the
the
details
we
want
to
talk
about
for
most
of
the
presentation
to
give
a
little
bit
an
overview
of
you
know
what
we
may
consider
to
be
the
landscape
of
the
different
realities
of
router
platforms
that
we
have
today,
primarily
also
to
you
know,
make
sure
that
is
understood
that
we
can't
talk
about
everything.
So
if
we
start
in
this
picture,
traditional
new,
you
know
the
original
routers,
maybe
in
the
70s
or
so
were
starting
to
be
just
general-purpose.
G
G
You
know
the
capabilities
of
them.
These
systems
have
a
lot
of
interesting
properties,
primarily
they're,
normally
an
ideal
world
for
protocol
designers,
because
they
are
pretty
much.
You
know
the
more
general
they
are.
You
know
the
less.
You
know
constraints
you
have
by
oh,
they
have
different
line
cards
and
so
on
they
become
fairly
spherical
and
that's
very
often
what
in
the
past
protocol
designers
expected
all
routers
to
be,
and
obviously
you
know
the
more
you
look
through
the
landscape,
the
less
that's
true,
the
main
issue.
I.
G
Think
for
them
is
you
have
all
the
flexibility,
but
you
have
really
no
way
to
predict
performance.
So
whenever
we've
been
trying
to,
you
know
predict
for
particularly
deployment
the
performance
of
a
combination
of
all
type
of
features
and
the
forwarding
plane.
Well,
you
know
it
just
gotta
measure
it
right,
because
it's
so
flexible,
specifically
for
the
aisle
for
for
the
IETF
I.
G
Think
what's
interesting
is
that
in
the
low
end,
like
let's
say
in
the
IOT
space,
CPU
forwarding
routers
are
pretty
much
the
only
game
in
town,
8-bit,
16-bit,
32-bit,
CPUs,
that's
kind
of
the
range
to
which
they
go
embedded
devices,
small
memory
routers.
There
are
a
lot
of
you-
know:
IETF
working
groups
that
work
with
routers
in
that
space
and
also
because
they
have
the
flexibility
of
this
almost
spherical
router
they're.
They
basically
can
design
protocol
solutions
that
we
have
really
a
hard
time.
G
You
know
to
scale
up
to
a
higher
platform,
so
my
typical
example
is
the
wonderful
source
routing
header
that
was
done
in
the
role
working
group
for
Ripple
low-end.
You
know
took
us
a
long
time
to
get
to
that
point
as
well.
Let's
say
with
SRP
6
in
you
know
higher
end
routers
and
that's
because
you
know
CPU
lot
more
flexible,
faster
to
get
to
the
protocol
stage
that
you
want.
So
then,
actually,
you
know
the
next
step
that
happened
in
the
90s
was
really
heart,
we're
switching
the
most
cost
optimized.
G
G
For
primarily,
you
know
it's
a
matter
of
you
know
business
case
right
if,
basically,
what
you're
trying
to
achieve
and
solve,
as
the
use
case
with
your
new
solution
in
the
ITF,
is,
if
it's
big
enough,
somebody
will
build
you
a
dedicated
device
to
do
this
example
of
this.
Actually,
you
know
I,
Triple,
E
and
friends.
Kind
of
these
you
know
layer
to
type
of
standards,
bodies
they're
much
more
centric
to
that
approach.
G
You
know:
individual
chip
designs,
we'll
see
how
that
is
more
going
forward
in
the
future.
One
I
think
very
interesting
aspect
that
came
out
of
the
data
center
was
kind
of
the
idea
to
make
the
consumption
model
of
the
chip
in
the
forwarding
plane
somewhat
more
open
right,
because
if
you
look
at
it
CPU
forwarding,
yes,
everybody
could
program
routing
a
nice
dual
program,
routing
on
CPUs.
Almost
nobody
can
do
that.
You
know
on
the
fixed
forwarding,
Asics
in
layer,
2
layer,
3,
switching
on
the
right-hand
side
and
in
the
middle.
G
It's
also
very
hard
been
traditionally
to
get
access
to
any
type
of
program
ability
of
the
forwarding
plane
other
than
maybe
you
know,
establishing
5
type
of
forwarding
entries
as
the
best
thing
of
something
like
open
floor.
So
but
that's
not
what
I
would
consider
programmability,
and
so
the
question
was
always
you
know:
how
can
people
outside
of
the
core
vendors
get
into
programming
of
these
multistage
programming,
forwarding
entries
and
so
P
4
was
one
of
those
you
know
today,
probably
as
a
programming,
most
successful
ways
to
attempt
opening
up
that
programming
to
other
players.
G
I
think
it
has
certainly
been
very
successful
in
the
research
world,
because
you
know
a
lot
of
researchers
have
started
that
are
doing.
You
know
networking
to
consider.
You
know
trying
to
prototype
their
forwarding,
play
notes
and
before
and
therefore
be
more
exposed
to
the
limitations
of
what
an
actual
forwarding
plane
has
not
ideally
but
a
lot
better
if
you
as
if
you
were
just
starting
to
build
forwarding
plane,
let's
say
for
Linux
kernel
or
something
like
that
or
DP
DK
right.
So
that's
basically
I
think
a
very
interesting
aspect
for
the
future.
G
Maybe
even
when
you're
doing
things
on
the
protocol
side,
that's
associated
with
certain
things
in
the
forwarding
plane,
you
know
how
do
you
want
a
prototype
that
forwarding
plane
if
you're,
not
one
of
the
vendors?
So
what
else
do
we
have
there
in
this
bucket?
So
beside
what
existing
details,
they
were
doing.
I
think
at
the
end
of
the
presentation,
I'm
going
to
talk
a
little
bit
more
about
that
I.
G
Think
in
this
space
there
is
a
lot
of
good
work
that
could
be
done
for
more
intelligent
forwarding
planes
and
I
think
you
know
two
of
these
areas
that
are
very
important
in
my
opinion,
but
that
are
you
know,
even
at
the
at
the
edge
of
what
the
the
forwarding
plane
into
you
could
do
is
programmable
qsr
I
think
that's
very
hard
and
then
the
telemetry
as
well.
That
Frank
has
done
a
lot
for
and
in
general
you
know,
chip
building
has
become
a
lot
easier
in
the
last
ten
years.
G
So
then
the
other
part
that
I
wanted
to
mention
is
that
beside
the
forwarding
plane
that
we're
going
to
take
talk
for
the
rest
of
the
presentation
about
there
also
is
the
port
forward.
It,
the
the
poor
control
plane
right.
So
the
I
wanted
to
call
this
the
reference
router
from
hell
and
everything
you
could
do
wrong
on
this
space
here,
but
a
little
bit
too
afraid
to
write
that
down,
but
I
think
most
people
won't
understand
high-level.
You
have
your
control
plane
and
you
have
your
memory
in
there
there's
some
CPUs
there.
G
Then
you
basically
have
these
magic
forwarding
chips
that
are
doing
things
and
they'll
also
have
a
lot
of,
or
maybe
not,
memory,
T
commentry
on
and
off
chip.
That's
going
to
be
talked
about
in
the
presentation,
a
lot
more,
but
a
lot
of
my
experience
in
the
past
with
protocol
designs,
weren't
necessarily
only
the
oh.
We
just
designed
the
next
forward
in
shape.
What
did
you
want
to
do?
Oh,
no,
sorry,
it
just
came
two
weeks
too
late.
Please
wait!
G
So
if
you
want
to
send
to
ten
line
cards,
it's
even
ten
times
slower
right,
so
the
router
from
hell,
obviously
I,
haven't
luckily
found
a
single
router
that
has
all
of
these
problems,
but
trust
me.
You
know
each
of
okay
notice,
your
report,
admittedly,
but
something
similarly
slow.
So
that's
the
problem
over
all
right
that
basically
trying
to,
for
example,
have
more
money
in
a
router
spent
on
the
control
plane.
G
When
you
build
the
box
is
something
very
hard
to
argue,
because
at
the
gist
of
it,
the
real
metrics
and
I
had
that
on.
The
previous
slide
is
really
what
data
plane
throughput.
Do
you
need,
and
then
basically
you
know
how
much
does
it
cost
per
bit
as
far
as
buying
the
box,
the
size
of
the
box
and
how
much
power
goes
through
the
box
right,
and
so
that's
that's.
G
Why
always
in
in
the
majority
of
box
designs,
the
poor
control
plane,
part
of
the
solution
is
a
way
on
the
back
end
burner
and
in
many
cases
it
might
actually
better
to
you
know,
start
buying
routers
that
don't
have
the
control
plane
and
basically
could
connect
a
fast
PC
with
a
hundred
gigabit
port
to
it
and
use
that
as
a
high-performing,
control,
plane,
router
just
from
past
experiences.
So
what's
anything
else,
I
wanted
to
say
from
this
I
think
this
was
good
enough.
So
let
me
pass
back
here
to
John.
E
E
You
know
that
sort
of
spans
the
whole
range
of
flexibility
from
completely
programmable
to
completely
set
in
silicon.
A
slightly
different
picture
of
the
same
thing
and
I
think
you
know
the
thing
to
emphasize
here
is
that
yeah
you've
got
all
the
functions
in
the
box,
which
makes
it
kind
of
attractive
to
think.
Okay,
look
I've
got
a
nice,
you
know
general
purpose
CPU
over
there
on
the
left
and
I've
even
got
another
one
over
there
on
the
right,
and
so
I
can
really
do
everything.
E
And
it's
true,
you
really
can
do
everything
as
long
as
you
don't
mind
taking
you
know
something
like
a
two
order
of
magnitude
hit
in
performance.
Every
time
you
cross
one
of
those
domain
boundaries,
or
maybe
worse,
I,
don't
think
I'm
to
say
a
whole
lot
about
the
fabric
based
architectures.
There's
an
interconnect
so
yeah
packet,
forwarding
engines
like
I
said,
are
the
the
things
that
do
the
the
work
to
figure
out
what
to
do
with
your
packets
right.
E
They
they,
you
know,
do
they
analyze
the
packet,
they
do
the
lookups
they
take
care
of
the
buffering
they
take
care
of.
You
know
they
be
simple
or
complicated,
queuing
that
you
want
to
do,
and
they
you
know
again.
The
the
programming
model
can
can
run
the
gamut
and
really
you
know
a
lot
of
what's
coming
up
here.
Is
there
is
no
new
thing
under
the
Sun
we
only
know
a
certain
number
of
ways
to
build
computers
and
a
certain
number
of
ways
to
make
them
fast,
and
you
know
it's
sort
of
clock
scores.
E
E
You
know
again
there's
this
is
sort
of
general
computer
system
design
and
and
not
unique
to
routers
it's
attractive
for
all
kinds
of
reasons,
to
put
everything
on
one
chip,
if
you
can-
and
sometimes
you
can-
and
sometimes
you
can't
so
there's
you
know
our
cartoony
reference
model
of
of
what
these
things
are
same
thing
you
know
put
on
two
axes.
Also,
cartoon
acts
is
not
to
scale
where
your
general-purpose
compute
engine
is.
E
E
Why
are
you
buying
those
gates
and
probably
never
using
them?
And
you
know
all
the
way
over
on
the
other
side?
Is
you
know
the
thing
that's
completely
set
in
silicon
or
you
know
more
likely
is
the
the
multi-stage
thing.
That's
somewhat
programmable,
but
the
stages
are,
you
know,
really
separate
Hardware
units
and
god
help
you.
If
you
forget
that.
H
E
So
I
think
the
first
bullet
has
been
sufficiently
belaboured,
but
you
know.
So
what
are
the
kinds
of
trade-offs
that
that
we're
making
when
we,
when
we
put
these
things
together?
This
is
an
example
trade-off.
But
in
my
mind
anyway,
is
maybe
the
most
critical
one,
because
it's
a
thing
that
gets
baked
in
and
then
you
really
can't
change
it
once
you've
taped
out
the
router,
and
then
you
know
if
you
and
that
this
will
be
repeated
with
with
more
pictures
in
a
few
slides,
but
typically
when
you're
forwarding
a
packet
you've
got.
E
E
If
you
can
get
to
it
at
all,
and
of
course,
as
with
all
system
designs,
the
the
trick
is
to
be
as
inflexible
as
you
can,
while
still
being
able
to
do
everything
you
have
to
do,
and
the
problem
is
that
when,
when
you're
building
hardware,
if
you
guess
wrong,
your
guesses
lasts
a
long
time,
I'm
sure
there
are
people
in
this
room
that
can,
you
know
tell
us
horror
stories
about.
You
know
just
how
old
the
oldest
router
in
their
network
is
it's
probably
very
old.
I
All
right,
I
think
I'd
like
to
go
on
baseline,
the
thing
even
a
little
further,
so
some
really
motherhood
and
apple
pie
trade-offs.
So
we
have
a
piece
of
real
estate
as
our
chip
right,
our
dye
and
it
up.
It
is
up
to
us
how
we
want
to
go
and
utilize
that
piece
of
real
estate,
so
you
have
a
set
of
gates.
You
can
use
these
gates
to
do
forwarding.
I
So
you
can't
shrink
the
gate
anymore,
so
you
started
to
go
and
pile
things
on
top
of
each
other
and
you're
just
going
denser,
and
that
means
also
that
static
power
is
a
significant
concern
these
days
right,
so
the
the
denser
we
pack
the
more
static
power,
ie
leakage
we
have
that
we
have
to
go
and
deal
with,
and
that's
just
the
tip
the
stuff
that
you
push
into.
The
system
also
needs
to
go
out
of
the
system
again,
and
that
is
cooling
and
I.
I
Remember
one
of
our
routers
a
little
while
back
I
think
we
spent
more
power
on
the
fans
than
on
actually
driving
bits
in
the
system
just
because
we
had
to
bend
the
air
three
times
as
it
passed
through
the
system.
Now
that
you
have
the
air
outside
the
system,
you
need
big,
yellow,
well,
cool
it
down
again
and
that's
okay.
If
you
may
have
a
single
router,
it's
not
so!
I
Okay,
if
you
have
many
routers
in
a
relatively
constrained
environment
like
if
you're
a
data
center
so
against
something
to
take
care
of,
unless
we
always
want
to
go
and
put
a
power
plant
next
to
a
datacenter,
which
is
what
people
do
right.
So
if
I
am
a
data
center
person,
my
my
design
constraints
from
an
optimization
perspective
will
be
very
different
than
I'm
just
operating
one
corridor.
I
Despite
the
fact
that
I
have
this
recurring
cost
off-off-off
power
that
and
you
spend
anyways.
The
other
thing
is,
as
I
said
earlier
on,
like
is
memory
and
where
do
I
spend
my
money
on
if
I
want
to
go
and
well
spend
space
on
on
the
die,
if
I'm
a
service
provider
Percy
I
want
fast
convergence
and
a
large
routing
tables,
so
I
want
really
rapid
updates.
That's
what
what
tourist
was
referring
to
earlier
on
and
so
I
want
the
memory
on
chip.
I
I
Then
I
go
off
chip
and
put
the
memory
off
chip,
but
then
I'm
spending
connectors
that
I
could
use
for
customer
interfaces
to
go
and
go
off
chip
to
the
memory
again,
a
trade
off
and
well,
if
somebody's
asking
me
for
well,
I
ideally
I
want
memory
at
the
speed
of
l1
cache
for
everything,
but
that
doesn't
exist
right
and
so
the
further
you
go
away,
the
more
you
pay
for
going
away
problem
and
then
also
I
think.
Can
we
it's
2019
by
now?
I
Do
we
really
need
hierarchical
queuing
all
the
way
we
needed
a
twenty
years
ago,
because
if
my
broadband
home
connection
is
one
gig
I,
don't
really
care
about
that
qsr
configuration
on
my
router
anymore.
It's
just
works
right.
Do
we
need
to
go
and
built
that
really
into
the
system
against
spent
gates
on
hierarchical
settling?
Well,
maybe
we
can
go
design
around
that.
I
The
other
thing
is
stats
and
there's
earlier
right.
So
a
couple
of
key
guys
around
back
to
packet
processing
and
that's
just
8
X
86
set
together
and
set.
We
want
better
stats
on
VPP
and
then
Allah
chimed
in
and
Dave
Barak
out
of
the
key
guy
for
VPP.
You
invented
the
whole
chimed
in
and
said
what
should
I
go.
Do
should
I
go
and
collect
stats,
or
do
you
want
me
to
forward
packets,
I.
I
Want
both
know
so
I
can
either
spend
a
cycle
on
collecting
something
or
I'm
spending
cycles
on
forwarding
something
and
so
yeah
I
think
they
came
up
with
an
architecture
that
allows
for
rapid
collection
of
stats.
But
well
there
is
a
price
that
you
pay
and
the
question
is
also:
how
often
do
you
want
to
go
and
collect
that
and
in
many
systems
yeah,
you
can
poll
the
system
every
say
one
to
three
seconds,
but
it's
all
the
same,
because
heart
were
only
updates.
I
The
counter
every
30
seconds
and
that's
the
trade-off
and
what
you
see
in
core
routing
is
we're
doing
that
right
off
of
you
go
fast,
you
have
shitloads
of
table
and
and
memory,
but
you
might
compromise
on
the
statistics
that
you
gather
because
again
you
can't
have
it
all.
If
you
want
ultimate
stats,
then
you
might
want
to
go
and
compromise
somewhere
else
and
people
build
dedicated
machinery
to
go
and
do
top
talkers
and
whatever.
But
again
we
pay
for
that
with
either
less
memory
on
chip
or
less
14
tacit
e.
I
So
there
is
trade-offs
and
I
just
put
some
examples
from
classic
SP.
Where
we've
been
optimizing
around
fit
table
sizes
stats,
flexibility,
qsr
buffering.
So
there
is
a
shitload
of
memory
on
the
chip
arranged
in
eventually
hire
a
case,
but
we
said
well,
we
don't
deploy
to
many
of
these
systems,
so
we're
okay
to
go
and
maybe
not
go
that
optimal
on
power,
whereas
in
the
data
center
environment
on
the
right
hand,
side
it's
all
around
power
and
bandwidth
and
speed,
and
these
guys
eventually
don't
even
want
large
buffers,
because
large
buffers
mean
delay.
J
E
So
yeah
here's
the
cartoon
that
I
promised
earlier
about
a
pipeline
forwarding
architecture
and
it's
you
know
like
I,
said
it's
a
cartoon
and
the
important
piece
of
takeaway
here
is
that
when
a
packet
comes
in
some
of
it
goes
north
and
some
of
it
goes
south,
and
you
know
the
two
really
only
meet
when
you
get
to
the
the
output
port.
So
so
you've
got
your
your
first
end.
Bites
they
go
up
towards
the
forwarding
complex
you've
got
the
rest
of
you
know.
Your
your
whole
thing
goes
into
your.
E
You
know
you
you
buffer
it
towards
your
egress,
and
maybe
you
do
another
look
up
on
the
egress
and
it
goes
back
out
onto
the
wire,
the
header
you're,
those
those
first
end
bites
get
processed.
You
have,
oh,
you
know
some
large
number
of
stages
and
potentially
a
large
number
of
cores
each
one
of
which
has
a
large
number
of
stages.
E
E
Notably,
when
your
headers
get
too
big
that
it
drives
real
cost,
because
you
know,
then
you
know
you,
you
really
are
that
that
all
is
l1
cache,
and
you
know
if
you
tell
me
that
I
need
to
have
twice
as
much
l1
cache.
Well,
Frank
just
talked
about
that.
On
the
other
hand,
the
data
goes
through
Ram,
which
looks
a
lot
like
commodity
Ram
and
acts
a
lot
like
it
too
and
is
slow
like
it
too.
E
So
I
think
compared
to
four
years
ago,
when
this
was
written.
Probably
a
lot
more
people
are
used
to
thinking
about
pipelines,
because
you
can't
turn
around
without
I
mean
everybody
all
of
you
have
like.
You
know,
16
cores
that
you're
reading
your
email
on
right
now
and
you
can't
do
anything
unless
you
think
about
how
to
break
a
task
down.
E
So
you
know
very
much
so
in
packet
forwarding
what
you
want
to
do
is
you.
You
want
to
break
down
the
forwarding
tasks
into
a
bunch
of
pipeline
stages,
each
one
of
which
ideally
provides
its
output
to
the
next
one,
and
you
know
moves
on
to
the
next
packet,
and
you
know,
of
course
you
can
make
these
things
arbitrarily
complex,
but
see
previous
discussion
and
yeah,
basically
anywhere
anytime,
that
you
have
to
make
a
decision
in
one
of
these
pipeline
stages
or
you
don't
know
how
many
times
you're
going
to
have
to
recur.
I
E
E
E
Yeah
so
I
think
this
is
worth
spending
a
few
minutes
on,
though,
which
is
that
typically
there's
a
fixed
header
vocabulary.
So
you
know
at
some
point
early
on
in
the
pipeline.
You've
got
a
thing
that
that
knows
how
to
crack
the
header
up
into
you
know
it's
fields,
and
you
know
so,
and
they're
they're.
E
E
K
K
One
of
the
promise
that
we
have
is
that
our
control
plane
are
coming
with
restrictions
because
of
our
system
architecture.
If
we
could
solve
some
stuff
in
the
control
plane,
we
would
not
need
some
of
the
characteristics
in
the
hardware,
for
example,
if
you
would
have
a
good
control
plane
that
we'll
be
doing
you
know
good
traffic
engineering,
you
don't
need
as
the
buffers
you
can
save
that
space.
You
know
for
other
functionalities
instead
of
the
buffers.
K
So
then
the
other
part
is
how
the
vendors
are
organizing
the
packet
forwarding
in
fixed
ways
where
there
are
some
flexibility,
because
it
ties
to
their
business
models.
That
is
another
problem
where
they
are
not
willing
to
reuse
the
same
trips
that
give
it
to
the
developers
that
they
can
organize
the
tables
dynamically
based
on
the
applications
that
you
want
to
run.
So
you
have
the
capability
to
size.
K
The
memory
in
different
you
know
in
tables,
but
in
inside
the
ASIC
in
in
different
sizes
that
you
need,
but
none
of
the
vendors
are
really
willing
to
expose
that
unless
you're
working
directly
with
the
ACF
render
and
you
have
the
access
to
those
api.
So
that
would
be
also
in
those
some
of
the
things
that
could
help
you
I
bet.
K
I
G
K
I
K
K
L
L
E
Yeah
I
I
mean
part
of
what
I've
been
trying
to
motivate.
Here,
though,
is
that
the
those
pipeline
architectures
are
probably
not
going
to
go
away
because
they're
very
cost-effective
I
mean
this
is
kind
of
the
you're
being
cheap,
no
I'm,
being
realistic.
Kind
of
argument
and
I
can
only
sell
what
people
want
to
buy
and
they
buy
what
they
need
and
what
they
need
in
certain
cases.
Is
you
know
if
you
go
back
to
two
francs?
You
know
cool
circles,
you
know
is
sometimes
you
know,
density,
speed
and
and
BTUs,
but.
I
I
think
to
a
point,
so
the
pipelines
are
just
one
example
of
multistage
and
there
are
certain
constraints
that
apply
to
pipelines
that
might
not
apply
to
other
multistage
architectures
like
if
you
have
multi
stage
with
run
to
completion.
You
don't
necessarily
need
a
past
memory
around
for
the
individual
steps,
so
there
is
trade-offs
among
that
I
think.
We
pick
one
example
forward
in
architecture,
because
it's
quite
well
used
across
the
industry
and
maybe
I
think
from
a
considerations
perspective.
Most
of
them
still
apply.
Maybe
we'd
go
through
the
the
considerations
and
then
yeah.
I
E
That's
that
sounds
fine,
I
mean
I.
Guess
the
we'll
take
your
thing
also,
of
course,
but
I
want
to
just
jump
in
and
say
you
know
to
some
extent
what
I'm
trying
to
you
know,
at
least
from
my
point
of
view
or
trying
to
describe,
is
like
a
bottleneck,
and
you
know
it's
it's
useful
to
analyze
bottlenecks
and
you
guys
can
fight
over
who
talks
next.
L
Actually,
what
they
wanted
to
get
to
is
that,
despite
a
multitude
of
protocols
that
may
be
needed
to
be
implemented
onto
the
forwarding
plane,
the
basic
elements
that
need
to
be
executed
are
quite
clear
and
I.
Based
on
my
experience
on
at
least
three
different
designs
that
three
different
major
network
equipment,
vendors.
So
from
his
perspective,
I
mean
you're.
Basically,
gonna
have
a
such
an
election
and
I.
G
To
get
back
to
the
point
from
then
about,
you
know
exposing
lower
layers
of
the
platform,
so
so
I
mean
the
lower
layer
of
the
platform
you're,
exposing
the
more
expensive
it
becomes
to
support
that
right.
So
that's
basically
I
think.
One
of
the
reasons
why
you
know
there
have
been
various
attempts
of
API
is
another
in
the
past.
You
know
the.
How
do
you
consume
it
right?
Most,
most
customers
really
come
with
requirements
or
functionality
at
a
higher
layer,
and
you
know
that's.
G
Why
also
thinking
that
the
programmability,
like
you
know
some
programming
language
before
whatever
it
would
be,
ultimately
gives
you
another
way
as
a
customer
to
approach
the
vendors
right.
It's
not
specific
to
particular
vendors
chip
itself,
but
you
can
go
and
say
this
is
what
I
want
to
run.
Show
me
that
it
does
I,
don't
know
400
million
packets.
You
know
what
whatever
performance
you
need,
and
that
goes
across
the
vendors
and
that's
at
least
you
know
in
another
stage
of
engaging
with
the
vendor,
by
being
able
to
do
that.
G
K
You
go
back
to
your
to
Frank's.
It
was
back
this
one,
so
you
have
the
SP
style
and
the
DC
style,
and
what
I'm
trying
to
say
is
that
in
the
ASIC
you
have
memory
and
it's
being
laid
out
in
fixed
tables.
You
know
that
are
using
that
memory
on
the
ASIC.
If
you
would
have
better
control
of
those
table,
layouts
that
you
can
dynamically
change
it.
You
know,
based
on
the
application
you
would
have.
K
So
some
of
the
you
know
some
of
the
vendors
basic
vendors
are
trying
to
give
you
more
flexibility
in
that
way
how
you
can
lay
out
in
order
to
get
some
of
you
know
better
the
trade-offs
where
some
of
the
you
know,
but
it's
very
hard
to
get
to
that
layer
and
when
you
are
talking
as
a
protocol
designer
what
you're
trying
to
do,
you
are
seeing
you're
getting
hit
by
those
restrictions.
I
mean.
G
In
the
existing
model,
where
you're
only
coming
you
know
with-
and
you
know,
solution
requirements,
it's
basically
that
the
product
already
has
to
be
in
the
different
market
spaces.
And
then
you
know
the
vendor
will
figure
out
how
to
reconfigure
it
accordingly,
but
other
than
that
I
think
it's
very
going
to
be
very
hard.
So.
C
If
I
could
just
do
a
cheering
rod
for
a
second,
so
so,
basically
we
are
to
slide
number
30
and
we're
kind
of
hoping
to
talk
about
things,
to
keep
in
mind
when
designing
a
new
protocol.
I
think
we
are
kind
of
assuming
that
people
will
continue
to
approve
routing
and
continue
to
improve
routers,
but
we
also
wanted
to
talk
about
what
people
are
supposed
to
be
doing
in
the
meantime
and
then
includes
people
that
are
not
working
or
routers.
C
E
This
is
hopefully
okay.
First
of
all,
this
is,
you
know,
I
am
100%
sure,
not
a
complete
list,
but
it's
trying
to
take
actually
some
of
the
you
know
one
of
the
earlier
questions
or
comments
rather
was
there.
There
are
a
certain.
You
know:
universal
truths,
that
people
who
have
done
this,
a
bunch
of
times
have
have
observed,
and
this
is
kind
of
trying
to
distill
them
down
and
present
them
as
a
is
a
set
of
almost
aphorisms
and.
I
I'm
John
I
think
this
is
a
very
valid
discussion
that
we
have
right
now,
with
extension,
headers
and
and
using
them
extensively
like
what
we
do
with
say,
for
instance,
I.
So,
depending
on
what
you
have,
how
come?
How
deep
here?
Can
you
parse?
What
information
goes?
Where
can
my
header
go
first,
please
so
that
I
can
parse
it
because
I
don't
care
about
your
header,
so
I
think
that's
a
very
valid
discussion.
I
The
other
thing
is:
that's
the
parsing
part
right
and
we're
very
aware
of
that
that
there's
limits
and
people
have
been
pushing
these
limits
pretty
far
out
so
there's
been.
If
we
go
a
couple
of
years
back,
people
were
able
to
parse
a
couple
of
hundred
bytes
into
the
packet.
People
are
not
been
using
that
capacity
at
that
point,
because
extension
headers
didn't
take
off
the
way.
The
way
we
were
thinking
they
were
taken
off
and
then
people
were
suddenly
pulling
back
again
from
a
possibility
perspective.
I
So
that
also
happens
if
certain
things
don't
get
where
they
get,
that
it
get
implemented,
but
they
don't
get
used.
I
think
that's
also
something
that
we
see
as
a
dynamic,
because
vendors
react
to
what's
been
built
and
what's
been
used
and
the
other
field
is
like
128
bits
are
really
a
challenge,
so
if
we
would
be
able
to
do
lookups
unless,
if
you
design
new
things
that
use
less
bits,
that
would
be
good
right.
Yeah.
E
Yep
I
think
this
is
you
know
again.
This
is
just
saying:
headers
that
can
be
composed
in
arbitrary
order
is
quite
painful,
as
especially
for
certain
architectures
that
have
a
fixed
order
of
axiom.
You
know
of
units,
so
don't
do
that,
inventing
new
kinds
of
headers,
if
you,
if
you
invent
a
key
that
looks
just
like
a
key
in
a
different
kind
of
header
and
kind
of
sort
of
similar
semantics.
E
So
I
can
you
know
rejigger
my
lookup
unit
to
do
a
slightly
different
kind
of
lookout,
but
it
still
look
up
on
a
thing
that
looks
about
the
same.
That's
probably
fine,
taking
a
header
layout-
and
you
know
saying:
oh
I-
can
abuse
this
into
it
in
a
new
way
because
it
has
the
right
number
of
bits
and
but
I'm
by
the
way
going
to
you
know,
change
the
semantics
in
some
non-trivial
way
is
you're
not
necessarily
going
to
be
able
to
reuse
your
existing
hardware,
also
recycling,
packets,
sucks,
it's
the
last
bullet
there.
E
This
is
Floyd
edification,
so
don't
panic
what
we're
talking
about?
There
is
entropy
identification
and
unfortunately
we
have
done
a
terrible
job
at
this
and
continue
to
not
do
a
terrific
job,
but
it
would
be
really
nice
to
do
a
better
job
at
this
in
the
future
and
to
put
entropy
at
a
fixed
offset
from
the
beginning
of
the
header.
E
I
F
Me
so
identify
flows
for
ecmp.
We
have
it
it's.
There
was
expressly
designed
for
this
purpose.
As
far
as
I
know,
it's
not
it's
being
set
on
the
internet.
Now
is
it
being
used
by
these
routers
and
it
gives
you
exactly
the
properties
you
want.
It's
at
a
fixed
location,
easy
to
process.
It's
always
in
the
Iceni
pv6
header.
E
F
F
E
F
We
just
talked
about
header
size
so
now,
if
I
have
to
go
down
and
find
transport
headers,
that's
gonna.
So
something
has
to
give
here.
You,
like
Frank,
said
you
can't
have
everything
so
I
can't
have
an
easier
way
to
identify
flows
and
yet
short
parsing
buffer.
So
there's
got
to
be
a
trade-off
somewhere.
H
Okay,
part
Visia
gandhi.
Are
we
a
great
background
and
the
history
of
the
routing,
and
there
is
a
paradigm
shift
in
industry-
I'm,
not
clear.
If
you
guys,
you
can
really
spend
a
few
minutes
to
see
how
that
would
really
impact
the
future
of
IETF
and
the
protocol
machinery
of
IETF.
It
seems
to
me,
okay,.
E
M
C
And
just
just
to
make
sure
that
I'm
doing
the
right
thing
for
everybody
in
the
room,
I'm,
hoping
that
the
discussion
starts
at
the
end
of
the
session.
If
this
sounds,
if
we
can
solve
all
the
problems
of
router,
routers
and
the
way
in
forwarding
and
furcal
interactions
in
this
room
by
five
o'clock,
that
would
be
awesome.
But
just
in
case
we
don't
I
also
want
to
be
talking
with
you
all
about
how
we
can
continue
their
discussion.
O
Element
Kirchner
just
on
the
last
point:
ideally,
yes,
fluid
identification
and
packet,
three
or
fragment
reordering
from
a
chip
perspective
would
be
ideal.
However,
there
are,
if
you
look
at
the
real
end-to-end
thing.
I
mean
there
are
security
considerations
and
you
know
stateful,
firewalls
and
so
on.
So
if
chips
drop
that
feature,
others
will
have
problems.
So
we
can't
optimize
for
chip
level
and
forget
that
you
know
we
are
trying
to
do
entrain
stuff.
Remember.
E
You
know
I,
don't
think
I
do
have
something
on
that.
Let
let
me
just
fly
through
the
next
things
and
then
I
we
can
sort
of
open
it
up,
for
you
know
be
sure
that
we've
we've
checked
off
all
our
boxes,
no
pun
intended
so
yeah
check
sums
are
expensive,
don't
use
them
just
for
fun,
don't
invent
new
ones
just
for
fun.
E
N
I
And
well
I
think
one
one
again:
I
hate
to
say
that,
because
I
love
multicast,
but
from
a
hardware
perspective,
it's
a
load
of
effort
and
people
put
dedicated
replication
engines.
It
makes
the
chip
much
more
complex
and
so
I
think
how
much
replication
you
need.
Consider
that
how
much
application
we
want
at
a
particular
point
in
time.
I
Consider
that
so
it
is
a
a
real
trade-off
that
people
have
to
go
and
make,
which
is
why,
if
you
look
back
loads
of
people
were
blaming
certain
devices
not
to
do
proper,
multicast
yeah,
it
was
a
design
decision
right
and
they
traded
unicast
capability,
or
maybe
sometimes
cost
plus
unicast
for
the
multicast
thing.
So
I
think
that's
some
of
the
background
that
happens
there
and
if
you
feel
forward
to
one
more
I,
think
that's
a
wrap-up
thing
right
that
we
want
to
go
to
jointly.
So.
I
Just
two
more
sentences
and
then
I
think
it's
free
format
anyway.
So
and
we
can't
do
everything
at
no
cost.
The
other
thing
is
and
I
think
that's
something
that
we
might
want
to
go
inspire
as
a
discussion
topic
is.
Should
we,
when
writing
a
draft
and
completing
the
draft,
have
some
of
these
considerations
that
people
think
what
their
protocol
should
go
do
and
what
some
of
the
assumptions
is
are
should
that
be
documented
in
the
document
and
written
down,
so
that
not
some
of
these
things
are
not
implicit
but
explicit.
I
So
I
assume
that
I
can
parse
packets
up
to
say
200
300,
bytes,
Steve
I
can
do
this.
I
can
do
that.
Should
we
go
and
document
that
I
think
there
is
a
problem
with
certain
things
are
designed
for
a
particular
domain,
and
it
might
well
be
that
today
this
domain
exists
tomorrow
we
don't
know
the
future,
so
it
could
well
be
that
this
domain
becomes
something
else.
I
The
requirements
that
you
have
in
mind
for
certain
things
from
my
perspective
would
make
sense
so
that
loads
of
these
implicit
assumptions
are
put
on
the
table,
especially
when
it
comes
to
what
the
forwarding
capacity
should
be
be
all
about
and
I
think
that's
one
of
the
discussions
that
when
we
did,
the
prep
calls
with
Spencer
or
our
own
team
that
they
wanted
to
go
see
surface,
which
is
why
we
put
it
here
and
now.
It's
all
yours,
sorry.
L
So,
thank
you,
I'm,
lucky
to
be
the
first
one
now
insecure,
going
back
to
your
previous
slide
regarding
with
keeping
state
information.
But
again
it
is
a
matter
of
Archie
and
it
is
architecture
dependent.
There
are
certain
architecture
already
out
for
more
than
10
years,
for
which
this
is
not
an
issue.
I
would
have
been
happy
to
see
other
elements
being
included
like
search
types
that
you
may
have
it.
L
These
are
directly
in
impending
regular
design,
no
matter
what
type
of
architecture
you
do
have,
so
something
like
Brickley,
favor,
hashing
or
favor,
exact
match,
favor
prefix,
matching
versus
generic
packet
classification
and
so
and
so
on.
Unfortunately,
after
staying
in
this
presentation
is
like
I
slept
for
15
years
and
I
could
have
come
up
with
the
same
type
of
discussion
15
years
ago.
That
is
not
rushed.
I
And
the
deck
was
started
in
2015
I,
think
yeah,
well,
loads
of
business,
motherhood
and
apple
pie,
and
they
just
wanted
to
go
and
cook
us.
I
was
cooked
that
up
as
a
game,
so
I
think
that's
a
good
point.
What
we
can't
do
could
do
as
a
follow-up
is
maybe
just
focus
something
just
on
look
up
in
the
next
go-around.
P
Sliding
hares
and
tunnels
flew
back
way
too
flew
by
way
too
fast.
We
have
increasing
amounts
of
tunneling
cap
protocols
in
the
IETF.
Increasing
design
expectations
that
end
cap,
D
cap
and
cross
header
processing
on
D
cap
will
occur
at
line
speed.
Would
you
care
to
comment
on
what
to
do
and
what
not
to
do
in
this
space?
You.
G
Think
it's
very
generic
right
I
mean
I.
Think
where
we're
looking
in
the
cases
where
we
feel
it's
it's
it's
its
worst
and
how
much
we
can
optimize
it
and
if
we
think
we
can
live
with
the
optimization
right.
So
if
you
have
an
ongoing
chain
of
you
know,
D
cap
an
end
cap
with
the
same
thing.
Obviously
you
can
optimize
that
quite
well,
but
because
even
the
links
doesn't
change,
you
just
need
to
figure
out
if
you
can
flatten
the
processing
to
actually
recognize
that
situation
so
but
yeah
in
general.
K
K
You
know
what
we
have
the
problems,
but
if
you
would
have
lay
out
whether
your
restrictions
and
what
will
be
recommendations
from
the
hardware
perspective
for
certain
protocol
adoption
to
be
faster,
that
would
be
very
helpful
because
the
we
can
try
to
optimize
one
thing
that
we
have
as
much
as
possible,
but
if
you're
adding
a
new
header
that
requires
new
parsing
and
you
want
to
do
it
fast.
As
you
mentioned,
you
have
to
wait
a
couple
of
years
and
they've
get
being
put
into
the
you
know.
I
Silence
right
so
I'd
rather
have
spelled
out.
What
do
you
want,
or
the
assumptions
that
you
have
as
opposed
to
there
is
some
generic
rules
from
our
perspective,
I
think
you
learn
on.
You
can
design
the
hardware
around
your
needs
and
then
your
additional
adder
I
can
slap
on
without
any
effort.
It
just
depends
on
what
the
underlying
system
is
built
towards
and
I.
Think
that's
why
I
do
believe
that
something
that
spells
out
the
assumptions
or
requirements,
it's
much
better
than
having
something
that
well
talks
to
spherical
routers,
but.
C
So
I
should
probably
say
something
just
for
a
second
here,
so
I
think
that
we're
talking
about
yeah
I
think
you
had
a
perfect
question
for
the
next
little
section,
which
is
where
I'm
hoping
we're
going
to
talk
about
is
not
how
a
some
specific
problems
like
that
so
issues.
It
stupid,
specific
problems
that
have
been
named
here,
but
how
we
solve
you
know
how
we
solve
those
problems
or
keep
them
from
happening
going
forward.
C
You
know
you're
right,
you
know
when
you're
asking
about
is
there
are
there
recommendations
that
we
can
make
so
that
people
will
quit
tripping
over
their
own
shoelaces
I?
Think
that's
a
conversation.
I
really
want
to
have
with
the
room
so
I'd
like
to
let
you
know
we
could
bring
the
queue
and
everything
if
you
guys
talk
fast
but
I'd
like
to
avoid
to
you,
give
these
guys
a
chance
to
finish
up
their
section
and
then
turn
over
to
the
room
for
us
to
figure
out
what
the
next
steps
look
like.
I
think.
H
We
are
focusing
on
a
box
called
the
router.
We
want
to
make
this
box
look
really
nice
air
bigger,
faster.
That's
not
the
point.
The
point
is
you
have
to
look
at
the
bigger
picture.
Like
Frank
already
mentioned
that
telemetry,
the
partner
is
not
only
if
a
packet
forwarding,
my
drone
is
only
a
small
piece
of
it.
Ok,
so
that
is
where
Spencer.
When
we
have
time
I,
guess
John,
you
said
we
are
going
to
talk
about
that.
We
are
making
this
box,
which
is
a
router
look
better,
faster
or
John.
Q
Have
a
few
points
on
the
slice
we
just
went
through?
Should
I
wait
or
should
I
go
through
him?
Okay,
Magus
Allen
says
good
agreement,
alright.
So
in
the
slide
31,
this
is
Rajee
by
the
way
so
slide.
31
said
parsing,
48
or
32
or
64.
That's
great,
but
128-bit
did
we
forget
to
send
a
memo
to
the
chase.
Ik
folks
that
ipv6
addresses
are
actually
128
bits
that
has
been
so
for
last
20
years.
So
so,
but.
G
Q
Not
but
that
it's
it's
that
mean
parsing,
128,
bits
and
I
feel
so
it
seems
like
we
still
rooted
in
ipv4
lingo
from
32
64
bits.
So
it
is
there
still
a
merit
in
having
to
restrict
I
mean
granted
I.
Get
that
the
you
know.
We
can't
just
keep
parsing
hundreds
and
hundreds
and
hundreds
of
bytes
in
a
packet
for
obvious
reasons,
but
there
has
to
be
at
least
a
guideline.
What's
optimally
minimal
right
as
we
go
along
the
timeline?
Q
Okay,
so
second
point
now
I'm
thinking
about
this
and
then
slide
37,
we're
saying
wait
heaping
state
or
not
keeping
state
on
slide
37
in
the
forwarding.
Node
is
better
well,
but
that
means
keeping
states
somewhere
else.
So
mostly
now
it
is
that's
in
the
packet,
but
if
you
are
keeping
state
in
the
packet,
that
means
you're
putting
more
information
or
highlighting
the
need
to
parse
that
packet,
a
bit
more
intelligently,
which
takes
us
back
to
the
problem
of
parsing.
Some
scratching,
my
head
on
that
and
the
last
one
and
I'll
pause
is
degrading.
Q
Multicast
unicast
I
think
what
we're
really
saying
degrading
the
ability
to
be
replicating
that
has
the
world
that
is
part
of
Martha
cos,
but
nowadays
we
also
do
that
with
unique.
Ask
so
am
I
correct
to
understand
that
when
you're
saying
degrading
Moloch
has
we
really
saying
well
degrade
having
to
replicate
the
packets
on
the
boss,
maybe
I'm
not
getting
that
right,
but
at
least
the
sent
the
statement
is
making
a
scratch.
My.
G
Head
this,
this
is
all
from
the
perspective
of
keeping
heart,
we're
simple
right.
Obviously,
that's
that's
one
end
of
the
side
and
obviously
I
think
we
would
all
agree.
We
don't
want
a
network
where
we
don't
have
ipv6.
So
sorry,
chip
designer
you
have
the
pain
there
right,
but
basically
ongoing.
We
should
still
consider
this.
You
know
poor
chip,
design
effects
into
account
right
so
before.
B
B
D
So
I
should
just
make
a
small
announcement.
We've
just
published
our
FCAT
5
or
7,
which
gives
you
64-bit
addresses
for
that
protocol.
Okay,
it's
meant
as
a
joke,
though.
If
you
didn't
get
it
but
but
go
and
read
or
see
a
table.
Oh
seven
I
would
load.
That
was
the
intention
all
right.
You
guys
or
someone.
We.
E
R
Your
whether
it
is
a
good
idea
to
try
and
document
some
of
these
things,
I
think
the
answer
is
clearly:
yes,
whether
that
ends
up
being
an
RFC
or
BCP
or
just
you
know,
a
wiki
page
I,
don't
know
that
I
have
a
strong
preference
on,
but
I
think
it's
really
great.
If
we
can
be
clear
about
what
your
behavior
is
good
for
router
and
also
what
behavior
protocols
are
sort
of
expecting
from
their
routers.
R
Yeah
definitely
I
have
another
point.
So
there's
a
slide
that
was
talking
about
how
avoiding
flow
identification
and
your
being
able
to
accept
packet
and
fragment
reordering
would
help
the
hardware
and
I
guess
my
sort
of
question
Michael.
My
question
was
sort
of
who
would
need
to
coordinate
to
make
a
reality
and
we
have
people
that
are
designing.
Quick
and
they're
saying
you
know,
we
don't
need.
Are
your
packets
to
arrive
in
order
and
we
can
build
into
quick
what
you
know
we
do
we
order
that.
M
R
You
know
that
would
not
be
so
good
if
the
stateful
firewall
is
seeing
things
out
of
order,
like
other
everything,
is
on
path
that
need
to
look
at
this.
I
don't
have
a
great
picture
of
of
who
would
need
to
like
how
many
people
would
need
to
change
in
order
to
make
that
happen,
that
we
can
tolerate
the
reordering.
S
Hi
Tony
Lee
some
router
vendor
one
of
many
I'd
like
to
respond
to
the
comment
about
128
bits
have,
after
being
there,
we
did
take
the
comment
about
128
bits
to
the
ASIC
folks
and
they
came
back
with
a
different
comment,
which
was
no
128.
Bits
are
bad
and
the
IETF
chose
not
to
listen.
Okay,
we
specifically
asked
for
variable
length
addresses
and
the
IETF
said
no
blank
blank.
T
U
Lot
of
us
have
been
doing
this
stuff
for
20
plus
years,
so
we
should
learn
that
kind
of
rule
of
thumb.
You
want
to
build
it.
Well,
you
want
to
design
it.
Well,
you
respect
clear
boundaries,
you
do
a
polish
ability
from
policies
and
the
we
are
going
like
a
pendulum
it.
It
reminds
discussion
about
fully
centralized
versus
fully
distributed.
N
Brian
various
people
have
suggested
that
we
write
down
basically
a
forwarding
specification
or
a
specification
for
how
this
works.
Well.
My
first
IETF
was
I
80s
16
in
1990
and
I
went
there
because
we
were
just
starting
to
work
on
and
the
rewrite
of
Rooter
requirements.
No
one
has
ever
successfully
written
that
down.
The
world
is
orders
of
magnitude,
more
complex,
the
optimizations
and
the
economics
are
orders
of
magnitude
more
complex.
All
we
can
do
is
to
do
some
tutorial,
but
never
more
than
tutorial.
I.
V
Have
a
draw
or
comment
which
is
a
little
bit
beyond
just
about
the
packet
forwarding.
One
thing:
that's
very
kind
of
strange
to
me
coming
to
this
meeting
was
I
was
expecting
something
to
tell
me
how
we're
going
to
do
forwarding
in
the
future
and
how
we're
going
to
get
things
better.
I
understand
that
we
want
to
have
simplicity
and
I
understand.
V
V
V
S
W
Of
an
idealistic
comment,
the
original
internet
architecture
was
supposed
to
make
hosts
robust
and
more
complex
than
the
inner
network.
Routers
we're
supposed
to
move
packets
fast
and
do
nothing
else.
That's
the
way
we
started
building
router
companies
but
turns
out
router
companies
didn't
want
to
be
commoditized,
so
they
had
to
put
additional
features
in.
Do
you
realize
most,
the
real
estate
on
any
die
on
any
router
is
a
huge
tee
comp
for
access
lists.
The
access
list
table
is
larger
than
the
FIB
table.
W
What
the
hell
are
we
doing
why,
in
the
middle
of
the
network,
we
have
to
check
if
a
package
to
be
dropped
or
forward
based
on
policy
shouldn't
it
be
done
in
the
control
plane
shouldn't
that
be
done
in
the
edge.
So
the
the
problem
is,
if
you
guys
want
to
build
fast
routers
and
make
these
hard
trade-offs,
you
have
to
can't
keep
changing
the
problem
set
if
you
want
to
keep
changing
the
problem
set,
build
a
general-purpose
programmable
forwarding
engine.
W
G
One
interpretation
of
the
next
slide
I'm
going
to
give
one
example,
the
simple
interpretation,
obviously
it
couldn't
work
and
it
had
to
be
painful
it
because
it
was
multicast
like
what
said
on
the
last
slide.
My
perspective
is
actually
a
little
bit
different.
It
was
basically
perfect.
Combination
of
you
know
bad
code
and
bad
IETF
specs.
That
basically
was
not
taking
into
account.
G
You
know
the
need
to
document
forwarding
pain
problems
in
a
way
that
really
they,
you
know,
must
be
implemented
correctly,
and-
and
this
is
basically
my
story
from
the
beginning
of
2000s,
when
we
were
using
the
router
alert
mechanism,
anybody
who
doesn't
know
what
router
alert
is.
Please
leave
the
room,
No,
okay,
fine.
G
So
what
we
did
was
a
reliable
multicast
protocol
called
PGM
and
basically,
that
was
using
router
assist
in
message
and
signaling
packets
to
basically
let
the
router
help
the
end-to-end
communication
of
the
transport
protocol
by
imploding,
necks
or
caching
and
retransmitting
packets.
You
could
say
it's
similar
to
ICN
just
a
decade
earlier,
but
be
that
as
it
may,
that
was
a
you
know,
in
our
opinion,
a
perfectly
well
working
solution.
G
Unfortunately,
when
we
started
to
deploy
it
in
customer
networks,
what
happened
was
that
this
router
alert
packets
were
perfectly
preceded
by
the
routers
in
the
network
that
understood
PGM
as
they
should
and
they
were
designed
to
have
the
performance
needed,
unfortunately,
also
a
lot
of
other
routers
that
had
never
heard
the
word
PGM
in
their
code
at
all.
We're
also
punting
these
packets
because
well
it's
obviously
a
router
alert
packet.
So
let
me
punt
this
to
the
you
know.
Aforementioned
remember
my
first
slide
at
M
CPU.
You
know
that
can
just
may
be
software
forward.
G
Let's
say
1,000
packets
as
opposed
to
500,000
as
the
ASIC
at
that
point
in
time
and
yeah.
Obviously
they
got
completely
overloaded
and
killed,
because
the
only
thing
they
were
doing
is
looking
the
packet
and
saying
what
router
alert
next
protocol
PGM.
What
the
heck
is
that
I
have
no
idea
simply,
let's
forward
it
in
in
software,
and
so
what
happened
was
that
the
specifications
that
we
have
in
the
ITF
were
basically
not
making
it
clear
that
you
really,
you
know
to
get
workable,
router
alert.
G
You
must
only
punt
the
packets
that
are
of
interest
to
you
and
that's
not
just
any
router
alert
packet,
but
it's
basically
the
packets
of
protocols.
Next
protocol.
There
is
also
a
particular
value
field
that
it
could
have
different
content.
You
know
the
combinations
that
you
know
you're
going
to
do
something
with
it.
You
know
in
your
software
control,
plane
forwarding
plane.
G
Don't
know,
definitely
on
a
lot
of
platforms
where
it
failed
to
do
so,
but
today,
obviously
it's
a
total
no-go,
but
still
we
don't
have
RFC's
that
mandate,
this
level
of
requirement
against
the
behavior
of
a
functionality,
because,
in
general
my
perception
is
Oh
were
not
about
to
specifies
internal
of
the
notes,
so
we're
always
trying
to
wriggle
our
way
around
it.
I
was
giving
here
an
italic
one
way
on
how
I
could
try
to
wiggle
my
self
around,
but
obviously
it
would
be
a
lot
easier
if
we
had
more
freedom
in
even
normative
rfcs.
G
To
make
specific,
you
know
requirements
that
today
we
might
consider
to
be
internal
only,
even
though
you
know
I
think
it's
very
nicely
externally
be
visible,
that
you
know.
Oh,
your
packet
throughput
went
from
500
thousand
per
second
to
1,000
per
second
right.
That
is
externally
visible
right.
So
this
is
basically
my
example.
Slide
of
you
know,
it's
not
only
a
problem
of
the
hardware,
but
there
is
also
the
problem
of
bad
code
and
that
ITF
specification.
E
Jump
in
produced
a
second
tour
list
and
say
that
I
think
what
I
hear
you
saying
is
that
we
have,
for
a
long
time,
had
a
religion
of
like
we're
not
going
to
mandate
architecture.
It's
not
our
business
right
so
and
you
know
sort
of
we
earlier
had
dancing
almost
the
opposite
of
saying.
You
know
just
give
me
the
cookbook
and
tell
me
how
to
fit
into
your.
You
know,
architecture
and
I'll.
Do
it
yeah,
but.
G
E
And
and
I
and
I
think
that
you
know
and
and
Frank
said
something
a
little
bit
different
again
and
I
think
what
I'm
hearing
is
we
sort
of
need
to.
You
know,
lose
a
little
bit
over
the
religion
and
we
don't.
We
still
should
not
be
mandating
architecture,
but
maybe
it's
okay
to
acknowledge
that
architecture
exists.
Let.
G
G
Let's
say
in
data
center
switches
and
you
know
I
think
in
our
evolution
we've
seen,
you
know,
hope,
I
hope,
headers
fragmentation,
reassembly
we've
been
trying
to
push
back
on
that.
It's
actually
not
only
packets
that
by
themselves
need
to
be
software
forwarded.
If
the
hardware
can't
do
it,
but
it's
also
what
you
know,
at
least
in
the
IP
multicast
work.
G
We
also
have
a
draft
for
where
we
basically
put
into
NP
you
in
our
prototypes
for
basically
a
lightweight
equivalent
of
RSVP
to
basically
establish
forwarding
state
at
the
speed
of
NP
U,
as
opposed
to
at
the
speed
of
control
plane,
and
that
actually
is
a
totally
different
protocol
design.
Because
when
you
look
at
it,
you
need
to
change
the
called
to
be
lightweight
enough
to
be
processed
by
the
NP.
G
You
similar
to
the
I
to
the
IOM
stuff,
where
you
can't
have
a
lot
of
you
know,
acknowledgement,
exchanges
or
so
so
you
know,
protocols
might
actually
start
running.
You
know
in
accelerated
forwarding
plane,
maybe
takes
a
decade
or
so
we
don't
know
right.
So
how
do
we
deal
with
the
conflict
of
you
know?
On
the
one
hand,
side
we
heard
ninety
minutes
about,
you
know
make
it
simpler
so
that
it
can
be
cheap
and
fast.
G
On
the
other
hand,
how
do
we
open
up
the
opportunity
to
you
know,
explore
more
intelligent
forwarding,
planes
and
leverage?
You
know
their
speed
and
and
flexibility
the
the
last
point
may
be.
You
know
there
was
a
really
nice.
You
know
research
project
that
I
solve
from
Berkeley
two
years
ago
and
they
were
actually
looking
at
exactly
what
we
always
fear
to
be
really
bad,
so,
let's
say
make
learning
in
802
dot,
one
in
bridging
right
totally
always
data
triggered
events.
G
Data
packets,
come
along,
you'll,
learn
a
dressing
from
it
right
and
there
we're
taking
it
forward
and
saying
hey.
We
can
do
this
in
NP.
You
know
they
program
prototype
in
P
for
right.
Basically,
if
you
can
do
it
now
in
hardware
and
it
works
at
line
rate
speed,
it's
really
a
great
simplification
of
things.
So
we'll
really
need
to
find
to
counter.
You
know
these
two
sides
of
the
equation
of
how
we
deal
with
forwarding
thing.
C
So
we're
going
back
to
other
presentation,
so
so
this
is
where
we
were
when
we
came
into,
though
when
we
came
into
the
room
this
morning
this
afternoon,
which
is
basically
the
chairs
and
and
warrant
okie
with
people
around
here
that
we
had,
you
know
kind
of
here's,
here's
here's
problems
that
we
know
we've
tripped
on
and
then
from
thank
and
Charlotte
or
less
we.
Oh,
he
said.
Oh
here's
more
gaiden
ears,
guidance
that
we
we
are
giving.
C
C
C
So,
like
you
know
my
question,
my
question
was:
basically:
we
could
publish
minutes
from
this
secession
and
thank
everyone
because
we've
solved
all
the
problems.
We
could
publish
informational
report
from
this
session.
We
could
request
a
mailing
list
to
continue
discussion.
We
could
shorter
work
on
recommendations
or
BCPs.
What
Benjamin
mentioned
looking
for
this
kind
of
thing?
Can
we
talk
to
approval
and
expectations
and
I'm
very
interested
in
hearing
other
suggestions
from
you
all.
W
This
is
Dina.
I
just
want
to
make
two
points
about
multicast
in
going
in
reverse
order.
The
data
driven
events
thing
toilets.
You
were
there
ever
so
you
know
the
history.
It
turns
out.
We
wanted
to
signal
sources
in
the
network
by
using
a
control
plane,
and
this
is
the
Tony
Lee's
point.
We
asked
the
IETF
to
have
a
request
to
send
message
and
it
was
not
in
the
current
way
that
multicast
service
model
was
defined,
so
it
was
said
no,
but
we
actually
did
get
something
out
of
it
that
we
could
have
used.
W
We
could
have
hacked-up,
because
there
was
this
thing
called
the
RSVP
path
message,
because
we
needed
to
signal
from
the
source
to
do
reservations,
but
not
to
do
multicast
state,
so
interesting
change
of
events
there
and
then
the
one
slide.
There
was
a
reference.
The
multicast
needs
to
be
degraded
to
unicast.
It
turns
out,
if
you're
a
fit
programmer.
The
hardest
thing
to
do
is
to
program
18
line
cards
and
make
them
in
sync
in
the
shortest
amount
of
time.
You
need
multicast
on
your
your
switch
fabric
or
there's
no
way.
K
Many
of
the
network
management
issues
that
could
be
solved
in
a
different
way.
We
are
trying
to
solve
in
protocols
which
are
then
impacting
you
know,
essentially
our
basic
designs.
There
is
really
no
need
for
the
operator
to
say:
oh
if
alcohol
is
in
there,
it
should
be
never
deleted
and
it
just
grows
and
grows
and
grows,
and
they
just
put
it
indiscriminately
across
the
network,
and
many
therefore
note
because
they
said
it's
better-
that
it's
there,
then
it's
not.
That
is
there
and
there
is
a
lack
of
network
management
tools.
I.
W
C
H
Kayani
my
earlier
question:
it's
the
vision
of
IETF
and
if
the
life
goes
on
in
ITF,
using
the
old
mindset
today,
if
you
really
look
at
the
application
layer
or
networking
infrastructure,
the
framework
is
widely
known
and
deployed
it's
being
deployed.
So
there
there
is
a
vision
there
that
the
actual
function,
which
reflects
the
reality
of
a
business
value
in
this
case
for
IETF
the
business
value,
is
how
fast
you
can
move
package
yeah.
How
fast
you
can
move
packets.
H
So
that's
when
you
move
from
a
PMF,
PMF
user,
like
a
physical
box
today
or
we
enough
there,
an
effete
he'll
be
enough,
and
now
we
have
C
enough.
We
she's
containerized
natural
function
in
the
world
of
CNF.
You
don't
have
to
deal
with
PMF
issues.
This
is
this
is
my
maybe
you
learning
from
the
routing
switching
coming
to
n
Fe,
and
now
we
are
talking
about
CNS.
H
My
question
for
IETF
is
okay.
If
the
application
layer,
networking
infrastructure
is
well
designed,
well
established
and
it's
been
deployed,
we
can
basically
use
the
same
concept
and
apply
it
to
layer
two
and
three,
a
layer,
one,
the
networking.
Why
not?
We
can
indeed
take
the
core
function,
which
is
packet
forwarding,
and
then
we
take
everything
else
is
not
packet
forwarding.
It
doesn't
have
to
be
Sdn
like
centralized
controller,
you
can
have
that
distributed
well,
distributed
functionality
of
something
like
envoy
in
a
context
of
like
service
mesh.
H
As
a
matter
of
fact,
I
don't
know
if
Eddie's
here
or
not,
there
is
a
an
effort
going
on
in
industry
that
how
you
take
the
IETF
protocols
as
tools
and
apply
to
this
new
concept,
I
want
the
people
that
were
talking
like
Frank
and
John
and
Hollis
to
talk
about
this.
How
that
would
impact
the
future
or
IETF,
not
necessarily
from
a
rafting
perspective,
the
overall
IETF
political
machinery,
and
how
does
connect
go
today
to
the
next?
Perhaps
this
serve
this
purpose
of
the
industry
for
the
next
decade,
or
so
so.
N
Another
elephants
and
I
think
it
may
be
a
reference
to
that.
In
the
previous
comments,
the
co-prime
is
people
want
to
do
virtualization
down
at
these
sorts
of
layers
and
do
the
sort
of
things
that
we
do
in
the
sort
of
virtual
moving
applications
around
where
I'll
remind
people
that
holographic
networking
is
currently
expected
to
need
a
terabit
per
second
per
user,
and
if
you
don't
get
the
latency
way
way
way
down,
the
user
feels
sick.
N
C
P
Black
sure
I
got
to
try
to
say
some
of
the
questions
on
your
side
on
the
slide
Spencer,
so
I'm
I'm
from
Transport
I,
don't
work
directly
on
routing,
but
I
use.
It
I'd
like
to
believe
that
the
protocol
design
work
I
do
has
some
cognizance
of
what
it
takes
to
make
her
out,
make
routing
effective,
so
I'm,
very
interested
in
the
output
of
this
session
and
I'd
encourage
to
go
beyond
the
beyond
the
what
was
said
minutes
to
an
informational
report.
P
Summing
up
things,
the
rest
of
us
can
use
BCPs
would
be
wonderful,
I'm,
not
holding
my
breath.
If
you
want
a
mailing
list,
that's
nice
I
can
expect
to
sign
up
because
I
want
to
see
the
output
I,
don't
care
I,
don't
care
to
be
one
of
those
who
make
who
who
makes
the
sausage.
So
there's
there's
there's
some
quick
stuff
that
you
want.
F
Tom
Robert,
so
on
one
of
the
earlier
slides
there
was
a
really
nice
taxonomy
of
various
routers
and
they
were
everything
from
IOT
devices
to
too
high
on
I
think
somewhere
in
the
later
slides,
we
were
more
secured
towards
high-end
when
we
start
talking
about
header
length,
even
checksum.
The
problem
that
we
face
and
David
might
have
alluded
to
this
as
a
like-
a
transport
protocol
designer.
If
we
want
something
to
work
in
the
general-purpose
Internet,
we
have
to
design
for
the
least
common
denominator.
F
G
So,
just
maybe
to
get
back
to
David
stuff
right
I
mean
we
were
very
centric
on
forwarding
and
basically
you
know
the
qsr
things
in
the
hardware
that
you
know
relate
to
the
transport
functions.
You
just
add
a
zero
to
any
time
that
you
have
how
long
it
takes
to
get
things
done
it
over
in
the
forwarding
plane,
because
that's
our
experience
how
long
it
takes
to
get
a
QAM
or
ezn
or
any
of
these
other
qsr
things
into
a
network
as
soon
as
you
get
out
of
CPU
space.
Okay,.
C
I'd
like
to
thank
you,
everybody
for
coming
and
I'd
like
to
thank
especially
Frank
and
John,
and
tourists
for
putting
together
their
work,
the
information
they
put
together
for
this
and
thank
my
co-chairs.
We
do
have
a
we
are
going
to
have
a
survey
on
this
and
we
need
to
adjust
a
couple
of
questions
on
it,
so
it
will
be
right
tomorrow,
they're
just
you
know,
we'll
hook
up
the
note
to
the
IEEE
IETF
104
attendee
list,
and-
and
we
will
let
you
know
when
it's
time
to
jump
on
that.
But
but
thank
you.
