►
From YouTube: IETF104-IDR-20190328-1050
Description
IDR meeting session at IETF104
2019/03/28 1050
https://datatracker.ietf.org/meeting/104/proceedings/
A
Hey
everybody,
despite
the
fact
that
we
have
enough
space
and
no
weird
pillars
in
the
middle
of
the
room,
and
all
that
this
is
IDR
and
we're
going
to
start
in
just
a
minute
or
two.
So
you
know
please
start
finding
a
place
to
sit.
If
sitting
is
your
thing
bring
your
conversation
to
a
close
stuff
like
that.
A
A
Okay,
everybody
I
see
sue
coming
back
in
the
room,
things
are
circulating,
people
have
settled
down,
let's
get
started.
The
note
well
is
the
same
note.
Well
that
I
projected
last
time.
It's
still
attending
little
eye
chart
sorry,
and
you
know,
as
always,
by
participating
in
the
ITF.
You
actually
are
sort
of
implicitly
clicking
on
the
the
shrink-wrap
having
to
do
with
intellectual
property.
C
B
A
D
E
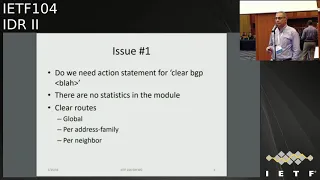
Right
so
I'm
gonna
talk
about
the
BGP
yang
model
and
before
I
get
started.
Let
me
be
clear:
I'm,
not
a
BGP
expert
I'm
on
the
staff,
simply
because
my
yang
expertise.
So
if
you
don't
like
the
model,
the
way
it's
written,
you
can
complain
to
me
if
you
don't
like
BGP
at
the
structure
of
it.
I'll
ask
one
of
the
co-authors
to
pitch
in
alright
so
status
with
the
0-5
version
of
the
draft.
E
We
now
have
support
for
the
routing
management
module
and
that
outing
policy
module
the
RFC,
83
49
brought
us
support
for
it,
and
you
will
see
great
many
pages
in
added
to
the
to
the
draft.
For
that
there
was
a
request
to
support
TTL
security.
I
have
added
that
as
a
feature
we're
not
going
to
support
it
in
the
draft.
It
allows
for
any
implementation
to
do
it
by
declaring
the
feature
we
did
add
support
for
BFT
that
not
only
the
features
statement,
but
also
for
PFD
configure
client
configuration
for
liveliness
check
when
I
started.
E
F
Aysen
know
I
know
everybody
might
not
want
to
stay
around
to
the
bitter
end
tomorrow,
so
that
routing
policy
module
we're
getting
ready
for
to
try
and
take
it
to
at
least
there
were
a
first
working
group
last
call
and
yang
doctorate
review.
So
I'd
encourage
everybody
to
read
it
I
clarified
a
lot
of
the
ways
the
recurse
of
Miss
worked
and
the
way
I
did.
It
is
I.
Did
it
the
way
we
map
the
open,
config
model?
F
E
E
G
G
Sorry
is
this
better,
so
actually,
wiping
routes
out
from
the
ribs
is
somewhat
controversial.
Some
implementations
only
allow
you
to
do
that
as
part
of
knocking
at
peering
session
over,
so
that
one
probably
needs
be
protected
by
a
feature
at
best.
Okay,
the
statistics
I
think
my
comment.
There
is
that
the
stuff
covered
by
the
nips
probably
is
worth
putting
into
the
base
module
and
I'd
suggest
that
go
in
as
part
of
the
base,
rather
than
extensions.
G
E
B
State
change,
if
you
go
from
a
particular
state
to
another
state,
these
are
notifications
which
can
or
cannot
be
turned
off
notice
or
the
push
notification
Joe.
You
go
back
and
go
back
to
the
first
issue.
Nothing.
My
brain
was
in
idea
our
chair
mode,
just
restate
what
you
had
problems
with
yeah
for.
B
G
G
G
B
G
You
know
a
backdoor
sly
to
for
issues
number
two
notifications
for
neighbor
state
change.
That
makes
sense
those
correspond
to
the
4273
traps
that
we
have
for
that.
Although
there's
some
warnings
and
4273
about
noises
and
the
state
machine
from
backward
transitions
as
we
go
through,
the
state
machine,
I
would
suggest
taking
the
warning
from
that
one.
G
E
G
So
the
problem
with
that
is
from
the
filtering
mechanisms
that
net
comfort
defined
this
is
so
noisy.
You'll
melt
the
router.
This
is
something
that
should
only
be
able
to
be
enabled
by
configuring
a
filter
in
some
fashion
and
propagating
down
to
the
BTB
module.
The
direct
analogy
is
turning
on
tracing
for
bgp,
updates
and
prefixes,
and
usually,
and
about
four
out
of
the
five
implementations
of
familiar
with
that
will
increase
your
CPU
used
to
like
no
one
hundred
and
fifteen
percent
of
what
you
previously
did.
I
see.
H
A
So,
by
the
way,
just
a
not
exactly
a
point
of
order,
but
something
this
is
good
conversation
and
please
continue
having
it
it's
fine
to
have
it
at
the
mic,
but
a
lot
of
it
is
also
stuff
that
is
highly
appropriate,
for
you
know
like
actual
document
review
and
feedback
that
goes
to
the
list,
because
it's
it's
the
kind
of
detail
that
gets
lost
even
in
good
minutes.
Yeah.
G
I
Works
so
I
have
a
clarification
on
the
previous
slide
again.
The
clear
BGP
most
useful
form
I
have
been
using
it
for
a
long
time.
It's
actually
with
the
little
knob,
let's
say
with
one
limitation,
soft
in
which
doesn't
clear
so
to
say,
but
generates
route
refresh
to
appear
and
then
I'm
synchronizing,
whatever
I'm
getting
again
from
the
peer
locally.
So
do
you
have
that
concept
here
or
it's
foreign
I,
CQ.
E
And
I
know
this
is
hard
to
read,
but
hopefully
you
can
go
back
to
the
slides.
What
I'm
showing
is
route
metadata
for
local
rib
and
the
set
of
parameters?
If
there's
anything
that
you're
missing
feel
free
to
comment
on
the
mailing
list
or
give
me
feedback,
bgp
sound
community
type
definition.
This
is
what
we
have.
E
If
this
is
good
enough,
let
it
be,
but
if
you
want
to
further
constrain
it
do
let
us
know
same
thing
for
extended
community
types:
I
don't
have
the
whole
printout
here,
but
it's
in
the
draft
issue
8
through
17.
Now
we
have
placeholders
for
specific
configuration.
The
expectation
is
that
each
yang
module
for
that
for
each
one
of
these
P
is
going
to
augment
the
BGP
based
model.
E
My
very
quick
and
the
last
two
days
just
going
through
some
of
the
draft,
says
that
there
are
some
tasks
that
do
it
like
ipv4,
unicast,
l3
VPN
is
augmenting
the
base
model,
but
then
we
have
a
whole
set
of
drafts
that
are
not
so
just
to
point
out
to
the
authors,
some
of
them
who
are
sitting
here.
Please
make
sure
that
your
augmenting
the
base
model.
J
A
J
Morning
folks,
k
Patel
I'm
going
to
talk
about
the
status
of
tunneling
katstra,
so
as
part
of
the
status
update
version,
11
was
published
fairly
recently
in
February
and
as
part
of
version
on
as
part
of
version
12
going
forward.
We
have.
We
now
have
a
new
core
through
sri
hari
from
Juniper
Eric
Rosen
has
already
retired.
Who
was
the
primary
co-author
on
the
draft?
The
draft
is
in
fairly
stable
state.
We
have
received
numerous
feedbacks
from
lots
of
folks,
including
shiri.
We've
also
received
a
feedback
as
part
of
chef
Shepherd
review
from
John
Scudder.
J
The
draft
has
changed
and
the
text
has
been
simplified.
The
comments
have
been
incorporated
version
12
to
be
published
soon
and
multiple
partial
implementations
for
this
draft
exists.
So
maybe
an
implementation
report
going
forward
to
document
some
of
these
things
here
are
the
high-level
changes
that
are
coming
in
from
version
11
to
12.
Of
course,
all
the
references
to
the
tunnel
types
have
been
moved
from
informative
to
normative
error.
J
K
Yes,
this
is
Linda
tumba
from
Huawei
I
have
sent
several
number
of
emails
asking
to
result
some
of
the
issue
in
this
draft.
For
example,
you
have
this
introducer.
You
have
this
remote
endpoint
tre
sub
theories
and
his
stated
can
be
inserted
with
every
tre.
So
if
I
have
a
route
which
you
can
go
traverse
like
multiple
egress
ports,
when
ports
and
I'm
not
sure
I
cannot
find
anywhere
in
the
document
should
I
have
like
multiple
remote
and
pointy
always
attach
the
route
or
should
I
have
announced
this
three
times
for
that
update
I.
J
A
So
can
I
just
interject
a
thing
from
the
chair
and
or
document
Shepherd
I
get
mixed
up
with
these
hats,
but
I
believe
there's
been
sort
of
will
it
or
will
have
been
enough
provisions
to
the
draft
that,
even
though
we
completed
one
working
group
last
call,
it's
probably
gonna
be
appropriate
to
take
it
through
another
one.
So
you
know
definitely
make
sure
that
you
get
in
your
comments
by
then,
if
not
before-
and
you
know-
that's
as
part
of
the
working
group
last
call
we'll
be
tracking
and
making
sure
that
we've
got.
K
That'd
be
great.
A
second
issue:
I
see
that
in
the
5512
you
have
bgp
speakers,
local
endpoint
address
to
be
included
in
in
a
in
the
update,
and
in
this
one
doesn't
mention
that.
So
I
asked
the
question
doesn't
mean
a
third
person
like
if,
between
our
two
sending
the
route
update,
if
there's
ex
concern
the
same
route
update
on
behalf
of
our
two,
whether
that
would
be
accepted
or
not,
it
is
not
clearly
stated
in
the
document.
So
that's
one
thing,
I
thought.
K
J
We
left
it
or
possibly
open,
but
if
you
think
there
is
any
vulnerability
issues
or
if
you
think
that
has
any
super
say,
because
typically
the
draft
text
doesn't
prohibit
an
implementation
from
doing
exactly
what
you
say.
Having
said
that,
if
you
see
an
issue
with
that
or
a
concern
with
that,
now
is
a
good
time
to
highlight
it
to
the
work
on
a
meaningless
I.
Do.
K
B
Review
a
review
of
that
draft
found
some
of
these
questions
that
Linda
mentioned,
and
we
were
looking
at
the
12
draft.
How
do
you
want
us
to
handle
questions?
Are
you
in
mid-flight
of
making
some
other
edits?
Should
we
refer
to
12?
Do
you
want
them
private
or
on
list
I
mean
normally,
you
know
I
always
like
on
list
stuff,
but
if,
if
you're
in
the
middle
of
edit
for
next
version,
how
do
you
want
to
take
the
time.
J
E
A
J
A
That's
exactly
you
know
what
you
outlined
is
like:
you've
got
a
12,
almost
ready
to
go,
put
it
out
there
and
then
it'll
be
a
good
time.
You
know
a
good
use
of
people's
time
to
go
and
review
at
that
point
and
let's
just
have
the
whole
conversation
on
the
list,
just
to
be
clear:
John,
there's
a
12
out
there
right
now:
okay,
sorry,
whatever
you,
it
sounds
like
you
have
something
in
your
edit
buffer
ready
to
push
out
as
that.
Yes,.
B
A
Okay,
so
before
I
would
like
to
have
that
conversation,
I
I
would
like
to
give
care
the
opportunity
to
finish
his
last
two
slides
just
in
case.
It
answers
any
of
the
other
questions
that
are
coming
up
to
the
mic.
If
you're
sure
that
you
know
your
question
isn't
going
to
be
answered.
If
it's
clarification
about
something,
that's
already
come
up,
go
ahead.
G
J
Sounds
like
a
fair
comment,
absolutely
again
as
part
of
changes.
Separate
IANA
registries
have
been
now
created
to
cover
flag
fields
within
end
caps
of
tlvs.
This
is
just
as
a
part
of
a
good
cleanup
same
for
the
label
handling
sub
TLB
field
as
well.
There
is
a
modification
to
best
part
mechanism
wherein
a
rule
is
been
added
which
says
hey.
J
If
a
path
is
considered,
paths
to
a
path
would
be
considered
unreachable
if
tunnel
and
cap
address
is
no
longer
reachable,
so
this
has
to
be
some
kind
of
an
reach
ability
check
that
needs
to
be
done.
The
routing
considerations
section
has
been
modified
to
ensure
data
forwarding,
prefers
tunnel
paths
over
a
non
tunnel
path,
or
or
rather
a
next
hop
path
for
that
particular
path
in
which
the
tunneling
and
pay
tribute
was
to
seal,
which
means,
if
you
receive
this
attribute,
please
make
sure
to
make
use
of
it.
J
I
Robert
hook,
so
that's
more
general
observation:
how
about
historically
Erik
didn't
want
to
add
anything
here
for
IPSec
and
DTLS,
because
he
didn't
want
to
put
crypto
in
BGP
and
that's
fine
right.
However,
there
is
use
cases
like
you
will
see
in
next
presentation
we're
just
indication
of
that
pier
which
is
willing
to
established
IPSec
with
someone
else
or
DTLS
for
someone
else,
it's
useful
right.
So
the
question
is:
why
don't
you
just
address
it
here,
adding
twinned
pipes
and
be
done
with
that
in
the
same
document,
so.
J
When
we
started
off
this
draft,
the
idea
of
this
draft,
at
least
with
the
quarters
that
started
of
this
effort,
was
to
replace
five
five
one
two,
and
if
you
notice
the
old
five
I
won't
do
it
in
carry
an
IPSec
attribute,
it's
done
as
part
of
a
separate
RFC.
So
we
say
it
as
follow
on
once
we
have
tunnel
and
caps
in
place,
and
once
we
have
an
appropriate
infrastructure
in
place,
we
would
go
and
cover
the
IPSec
as
part
of
the
separate
document.
Just
so
happens,
someone
has
done
it.
J
I
A
A
Anything
that's
in
there.
That's
wrong,
obviously
has
to
be
covered.
If
anything
that
looks
like
you
know,
a
new
tunnel
type
or
extension
I
I
would
love
to
see
that
come
along
as
a
follow-on
draft,
just
because
I
don't
want
to
have
this
thing
open
for
writing
forever
and
it's
designed,
as
you
know,
a
modular
and
extensible
framework.
A
So
let's
move
this
one
forward
and
extend
it
and
I
think
that
what
you're
describing
is
a
perfect
I,
don't
want
to
process
more
drafts
than
we
have
to
you
know:
let's
not
have
a
million
drafts
just
for
fun,
but
on
the
other
hand
you
know
we
got
to
sort
of
say
you
know
close
for
writing
now.
You
know
at
some
point,
so
you
know
I'm
not
saying
absolutely
not,
but
I
am
saying:
let's,
let's
not
churn
it
infinitely.
J
A
A
Probably
if
I
you
know
we
had
to
go
back
and
do
again.
I'd
say
you
know
what
would
be
awesome
would
be
to
do.
You
know
kind
of
the
the
skeleton
part
and
in
one
document
you
know-
or
maybe
do
it
with.
You
know
just
one
exemplary
atomic
tunnel
type
and
then
do
all
the
tunnel
types
in
follow-ons,
because
then
it's
clear
that
your
your
implementation
piece
has
copper
is
covered,
but
what
we
have
is
we
have
a
document.
That's
got
six
tunnel
types
call
out
in
Section.
A
Three
plus,
you
know
several
other
modes
called
out
in
section
three,
and
my
guess
is
that
either
no
one
or
almost
no
one
is
going
to
go
and
you
know
implement
all
of
those
tunnel
types
in
their
first
ship
and
if
we
insist
on
having
every
single
tunnel
type
checked
off
in
our
implementation
report.
This
thing
they
stay
and
draft
for
a
long
time.
A
So
my
hope
is
that
the
working
group
is
going
to
be
satisfied
by
saying
you
know
what
we're
gonna
we're
gonna
check
off
the
you
know,
sort
of
basic
functionalities
and
say
we
implement
at
least
one
tunnel
type
and
it
seems
to
work
and
move
forward
on
that
basis.
It's
not
it's
not
perfect,
but
I
hope
that
sort
of
you
know
satisfies
enough
of
the
requirement
so.
J
Speaking
as
a
co-author
on
the
document
and
I'm,
pretty
sure,
I'm
speaking
on
behalf
of
all
the
other
co-authors
is,
as
we
start
to
take
on
version,
12
and
publish
version,
12
I
am
sure
we
will
get
feedback.
That
means
we
will
be
editing
the
document
and
why
we
are
editing.
The
document
it'd
be
great
if
we
can
take
that
call,
because
we
have
no
problem
splitting
split
splitting
the
documents,
but
we,
if
we
do
it,
we
do
it
now,
rather
than
we
don't
take
a
call.
And
year
from
now
we
take
that
call
y-yeah.
F
Ac
Linda
yeah
I
would
really
support
bringing
this
to
completion
and
one
thing
we
had
with
the
segment
routing
drafts
in
iGPS.
We
had
a
specific
piece.
It
was
actually
an
encoding
of
our
SPE
like
ER
o
and
those,
and
we
talked
to
among
the
I,
was
the
shepherd
I
talked
to
him
on
the
co-authors
and
I
said
I
know
when
nobody's
implemented
this
are
we
ever
going
to
implement
it
and
they
all
said?
No,
probably
not
so
we
took
it
out.
F
K
This
is
Linda
dumper,
so
I
support
having
those
skeleton
document
explaining
really
well.
How
do
you
update
the
route?
How
do
you
go
through
the
egress
ports
and
how
do
you
report
and
then
potential
problems
of
third
party
announced
for
you
all
those
mechanism
to
be
described
well
and
then
you
may
have
may
be
appended
to
describe
different
kind
of
encapsulation
because
they
are
all
can
be
treated
the
similar
way
except
IPSec.
M
B
N
Hello,
everyone
topic
here
is
to
use
IB
chick
PGP
to
ice
Aikido.
The
IP
set
configuration
I.
Think
five
minutes
discussion
is
about.
Do
we
want
to
put
this
into
the
current
draft
or
the
one-stop
race
as
separated
document?
For
me,
I
am
fine
with
it
either
way,
I
mean,
but
this
presentation
about
what
it
means.
So,
let's
put
that
aside
for
a
minute,
just
focus
on
the
air
talking
decide
so
probably
I
think
probably
it's
pretty
straight
wood.
The
problem
I
will
try
to
solve.
N
Is
that
in
some
large
networks,
your
big
number
of
routers
and
then,
if
you
want
to
secure
either
power
traffic
or
the
traffic
850
million?
Typically
today
you
have
to
do
is
that
you
create
a
large
number
of
IP
second
mesh
tunnels
between
then
sometimes
you
know
to
manager
and
the
provision,
those
pycnometer
knows
it
cumbersome
and
it's
a
quite
big
overhead.
So
we
need
a
better
solution
to
address
such
a
problem,
so
design
considerations.
N
N
N
So
here
are
the
changes.
First,
we
need
a
new
theory
for
IPSec
tunnel,
so
I
here
proposed
to
use.
We
use
current
look
at
the
value
of
n
o4,
which
is
a
liquid
by
the
5s
disks,
to
reuse
that
as
a
basic
ESP
tunnel
mode,
because
for
a
H
mode
it's
rarely
used
and
I
think
they're
right
now.
They'll
change
at
least
well
from
nice
things
to
deprecate
H
mode,
so
I
propose
that
we
only
support
is
returnable.
N
N
So
today,
I
know
you
many
deployments,
people
actually
using
the
same,
or
instance
for
both
load
and
the
tunnel
packets,
but
for
secure,
isn't
there
should
be
possibility
to
separate
this
to
so
we
need
a
separate
top
tier
V
to
signal
that
and
then
there's
a
new
sub
theory
for
remote
address
prefix.
So
in
my
piece
of
Caetano
case
there's
the
idea
of
the
there's
a
concept
of
the
trophy
selector,
which
defines
what
type
of
our
source
and
destination
traffic
is
allowed
on
a
tunnel
or
the
particular
traders
say.
N
So
we
need
to
signal
that,
because
that's
quite
important
for
the
greedy
IPSec
tunnel,
since
user
may
want
to
enforce
what
type
Ralph
or
what
type
sauce
is
allowed
to
access
the
somewhere
behind
me.
So
there
are
two
so
if
I'm
to
here
it
will
rise
for
remote
while
for
the
local.
So
those
are
all
for
receive
point
of
view
and
condition.
N
Yesterday
with
the
robot
I
think
the
no
one
we
could
be
optional
could
be
other
way
to
freedom
by
using
recourse
next
I
look
up
to
achieve
same
purpose,
but
I
think
a
local
band
is
that
is
necessary
and
also
it
reuse.
Some
existing
sub
terribly
defining
the
counter
craft,
for
example
remote
endpoint,
which
give
you
the
IP
sector.
Nine
point
dress
the
color.
Actually,
the
color
we
use
here
to
signal
the
large
part
of
our
preset
confusion
like,
for
example,
your
most
importantly,
your
crypto.
N
What
crypto
you
want
to
enforce
that
the
other
end
to
use
to
reach
you
and
some
just
a
mother,
whatever
either
IPSec
infusion.
You
wish
to
map
into
this
color.
Actually
severity
of
II
and
last
real
I
also
want
to
reuse
the
embedded
label
hindering
sub
here.
We
because,
although
IPSec
tunnel
is
for
IP
tunnel
payload
but
in
case,
for
example,
in
unicast
VPN
address
family
there's
a
label
there,
but
for
IPSec
case
because
the
during
the
icon
of
negotiation,
you
are
aware
which
private
or
distance
that
you
are
mapping
to
each.
N
N
So,
in
this
case,
given
such
requirements,
both
R
1,
R,
2
or
provision
with
the
PKI
keys
and
certificate
for
us
AMCA
so
again
here,
so
this
draft
does
not
propose
anything
to
for
the
authentication
credential
in
BGP.
We
leave
that
outside
on
purposely
outside
the
documents,
because
it
with
BK
I
can
easily
to
achieve
that.
Scalable
credential
provision
in
the
network.
N
So
here
those
are
two
provisions,
certificate,
keys
from
same
CA
and
are
while
we
advise
upland
a
in
BGP
which
has
a
tunnel
in
custody
attribute
that
contain
IPSec
theories
so
which
contain
two
theories.
First,
why
is
our
point
with
panel?
Our
are
wise
endpoint
address,
the
color
will
be
red
and
sublet
in
the
local,
perfect,
subject,
V,
so,
basically
two
verses
in
order
for
the
source
of
her
own
subnet
P
to
reach
some
net
a
behind
me.
N
You
need
to
use
red
configuration
actually
conversion
to
reach
me
as
similar
for
theory
2,
which
is
says
most
remote,
subnets
C
to
reach
a
from
the
a
you
need
to
use.
Color,
yellow
as
an
IPSec
configure
except
sedation
then
are
two
other
also
advised
subnet
B,
which
has
a
1-ton
or
encapsulate
attribute
that
contains
one
IPSec
theory
with
more
than
power,
be
the
are
truth,
endpoint
and
colors
of
red
and
a
in
the
local
preciousness
sub
Theory.
So
again,
so
r2
will
advance
similar
saying
for
some
nasty.
N
So
when
I
one
received
a
packet
from
top
and
a
test
angel
suffered
B
since
BT
update,
inclusive
a
also
conclude,
a
clue
contains
a
IPSec
tonneau
encapsulate
repute
and
there's
no
existing,
try
to
say
that
could
use
for
the
traffic.
So
I
will
choose
theory
one
because
he
will
match
the
package
source
and
destination
address
with
the
local
prefix
in
the
received
updates,
and
then
here
truth
here,
v1
and
years,
accurate
to
three
steps
eternal
and
also
because
the
there's
a
there's
a
carriage
built
in
the
IPSec
theory.
N
He
will
know
what
kind
crypto
overcome
for
eyepiece
the
confusion
he
should
use
to
Estep
Gitano
so
that
they
will
config.
They
were
creating
exactly
to
create
his
first
try
testing
and
the
corresponding
ESP,
transform
the
Kryptos
and
with
a
trophy
selector
that
accordingly
and
then
after
the
time
is
created,
I
1,
R
2
now
can
for
traffic
between
sublet,
a
and
B.
So
what
they
try
to
say
well
and
if
next
hour
received
another
package
from
suffered
a
to.
N
This
is
something
to
see
because
in
this
case,
although
I
already
have
a
try
to
say
one,
but
that
one
is
only
for
to
each
other
sublet
a
and
B,
so
that
they
cannot
use
that
so
I
try
to
say
so.
He
need
to
create
an
just
try
to
say
for
these
packets
same
same
same
process
happen
in
the
previous,
but
now
because
there's
already
I
can
say
credit
in
previous
step
to
the
same.
N
Pier
so
can
you
use
that
I
can
say
to
create
a
second
child
si
with
different
crypto,
in
this
case
North
Christian,
with
sha-256
and
with
a
different
set
of
chopsticks
elector?
So
now,
after
these
two
steps,
our
two
can
forward
traffic
between
subnet,
a
and
sub.
Let's
see
with
the
trial
will
try
to
sa.
To
this
way,
both
r1
r2
does
not
have
provision
people
in
all
those
tunnels,
pretty
pretend
it's
all
packet
triggered
or
dynamic.
N
N
Second,
is
by
reusing
IP
equity,
which
is
a
field
PO
field
proven
mature
protocol
which
make
sure
that
exchange
is
secure
and
last
we
all
need
to
do.
The
limit
change
track,
B
to
be
no
change
to
activity
and,
and
last
is
that
we
allow
interpreter
routers
that
are
not
supposed
draft
which
allow
gracefully
transition.
K
This
is
Linda
Dunbar
I
just
put
my
hair,
the
head
of
the
iTunes
that
working
group
chair
this
particular
IP
sac
configurations
through
controller,
has
been
discussed
in
the
ITSM
in
the
security
area
for
over
a
year.
So
there
are
lots
of
controversial.
Is
there
and
so
I
think
this
starting
here
will
be
better
to
align
with
what
has
being
discussed
in
the
security
area
to
align
with
what
they
have
done,
at
least
maybe
bring
it
over
there
or
align
with
there
or
wait
until
they
finish
and
adopt
yeah
it
comments
over
there
a.
N
K
K
So
that
need
to
be
addressed,
so
that's.
My
first
concern
is
the
duplication
of
the
discussion.
Parallel
discussion
in
security
area,
and
here
second
concern
I,
have
is
for
the
traffic
selection
for
IPSec
traffic
selection
is
not
only
based
on
destination
like
the
route.
Like
you,
li
PGP
update,
you
update
your
your
routes.
It
can
be
associated
with
source
and
destination
and
ports
and
many
other
parameters
so
that
using
PGP
to
to
to
advocate
that
propagate
that
the
remote
end
doesn't
really
know
the
particular
policy.
K
The
policy
has
to
be
coming
from
the
controller,
not
from
the
peer
third
part
is
when
you
advertise
the
traffic
the
routes,
the
local
local
device,
has
to
be
able
to
be
secured
enough
to
authenticate
the
peer.
So
the
the
IPSec
introduced
a
whole
different
dimension
because
you're
giving
with
the
port
facing
the
untrusted
Network
it's
different
from
the
other
network.
We
deal
with
where
everything
is
in
the
walk-in
garden,
yeah.
N
I
think
I
said
question
one
by
one.
So
first
one
is
that,
like
I
said
I'm
not
trying
to
be
a
stn
solution
here
and
not
everybody
want
to
use
a
controller
in
the
network
and
understand
it
pretty
hard
topically
right
now,
but
not
that
it's
not
like
everybody
know
what
we're
starting
using
controller
in
tomorrow.
So
second,
my
drafter
really
is
just
extension
of
a
current
canon.
Captioned
patient
dropped
within
the
idea
to
cover
the
IPSec
tunnel
case.
N
Nothing
was
in
that
and
the
second
and
more
that
IPSec
that
traffic
has
protocol
port
range
I've
been
working
I'm
secure
for
ten
years
now
so
I'm
aware
that,
but
here
in
specially
in
the
network,
routing
internationally
use
case,
people
usually
do
not
use
protocol
or
put
range
here.
So
that's
why
I
want
to
simplify
my
draft.
That's
wrong.
Put
too
much
into
the
watch.
Change
on
the
BGP.
I
Robert
hooke,
so
it's
not
the
question
to
you.
It's
actually
a
general
observation
for
the
working
group.
You
brought
it
up.
That's
why
it
comes
now,
so
you
are
asking
for
edition
of
the
local
critics
and
that's
very
useful,
but
it's
also
applicable
to
all
types
as
currently
defined
in
the
tunnel
and
capsulation
attribute,
because
that's
very
useful
information
to
have
ability
to
specify
from
that
source
to
the
destination
go
through
that
end.
Cap
versus
the
other
end
cap.
I
G
As
I
have
two
comments
about
two
and
half
comments,
first
I
do
think
this
is
very
useful.
Work,
configuration
and
use
of
IPSec
tunnels
has
been
somewhat
painful
and
BGP
before
people
have
several
ways
of
doing
it,
and
many
of
them
are
annoying.
Which
brings
me
to
my
two
points.
Point
number
one,
your.
You
should
add
a
operational
consideration
section
to
your
draft
talking
about
how
issues
that
I
ke
now
become
part
of
your
troubleshooting
mechanism
for
BGP.
If
Ike
doesn't
work,
your
tunnel
doesn't
come
up
your
route
stop
resolved
and
no.
G
G
N
G
The
place
where
this
can
be
additionally
useful-
and
this
is
somewhat
problematic
in
terms
of
how
the
T
path
attributes
likely
to
be
deployed
for
a
short
period
of
time.
Having
you
know,
some
general
is
PA
and
some
generally
is
pzd
will
completely
far
ends
of
things
trying
to
interconnect
with
each
other
and
basically
doing
IPSec
over
the
Internet
is
a
thing
that
is
already
done
today.
But
again
it's
C
prior
comment.
It's
a
very
difficult
thing
because
coordinating
things
like
the
ike
services
across
the
internet
is
a
tricky
thing.
Yeah.
N
A
And
so
two
things,
one
is
I'd
like
to
say
we're,
cutting
the
line
aftercare
and
the
other
is.
This
is
valuable
conversation
and
I
just
I
mean
this
is
a
general
comment.
Any
time
you
make
a
comment
at
the
mic
actually
is
send
a
follow-up
email,
because
it's
really
hard
for
presenters,
who
do
not
you
know,
are
not
taking
notes
as
they're
presenting
to
remember
all
the
comments
and
we
try
to
get
them
in
the
minutes,
but
send
email.
Thank
you.
Go
ahead.
Stephanie.
P
My
idea
was
to
try
to
find
just
one
solution.
If
it's
possible
to
cover
all
the
cases,
I'm,
not
sure
that
it
will
be
doable
but
yeah,
we
need
absolutely
to
set
up
the
minimum
set
of
building
blocks.
That
could
be
reused
for
the
various
use
case
after
eyes.
Just
where
is
the
home
for
his
work?
Do
you
do
it
in
idea?
P
A
B
B
B
Some
of
the
things
that
are
different
with
Linda's
in
my
graph
is
we're
looking
at
gaps
in
their
draft
okay
and
we're
trying
to
work
with
them
and
work
with
the
I
to
intercept
I
I
would
just
note
that
it
might
be
useful
for
you.
As
an
author.
That's
just
a
comment.
I
have
two
questions.
The
new
subnet
he'll
be
for
remote
address,
prefix
and
local
address
prefix.
We
explain
why
you
felt
that
was
necessary
in
addition
to
the
addresses,
because.
N
N
B
B
B
N
B
Just
let
me
repeat,
backs
who
understand
it.
You've
said
that
it's
only
under
the
IPSec
color
and
that's
where
it
is
be.
You've
said
that
you're
gonna
have
multiple
people
using
that
IP
upset
color.
Otherwise
you
wouldn't
be
using
BGP
and
you're,
not
gonna
define
how
it's
going
to
be
working.
My
comment
then
stands:
how
are
you
gonna?
Have
people
not
clash?
No,
that's.
R
S
N
B
N
N
A
R
Elisa
Jesse
Cisco,
even
just
the
building
up
on
the
question
that
who
made
the
security
VPN
I.
Guess
you
haven't
had
a
chance
to
read
it
right.
Sorry,
secure
a
VPN,
Jeff
I!
Guess
you
haven't
had
a
chance
to
read
it:
okay,
because
some
of
the
material
in
here
overlaps
and
would
be
good
to
you
know
to
see
what
the
overlap
is
and
how
we
do
it
in
that.
R
R
R
R
R
Okay,
all
right
so
just
a
quick
note
that,
in
terms
of
the
setting
it
up,
the
security
VPN
talks
about
how
to
discover
and
set
up
the
IP
succession,
as
well
as
how
we
can
in
for
take
their
instead
of
using
the
I,
could
beat
you
or
we
can.
Instead
of
having
a
measure
of
the
itv2,
we
can
use
one
single
point-to-multipoint
signaling.
You
guys.
R
A
J
Patel
arcus
the
comment
that
Robert
made
about
taking
the
list
of
prefixes
and
probably
moving
that
TLB
into
the
base
draft
happy
to
do
that
happy
to
work
with
you
on
that.
So
no
problem
at
all
the
other
side
comment:
I
have
I,
don't
know
who
to
probably
target
on
this,
but
a
general
comment
that
there
are
four
different
solutions:
none
of
their
those
solutions
list
out
what
route
announcement
rules
should
be
across
the
AAAS
or
whether
should
this
be
at
this
attribute
be
leaked
across
yes
willingly
and
willingly.
A
N
B
O
O
Problem
statement,
PFD
IFC
v
a2,
enables
routers
to
monitor
data
playing
connectivity
and
detect
boarding.
Pass
failure
in
BGP
leverages
on
this
specification
by
using
EFT
to
enhance
the
faster
convergence
II.
Today,
BGP
neighbor
session
establishment
is
independent
from
the
PFD
session,
a
PFD
State,
because
of
that
there
are
some
possible
failure
scenarios
when
BTP
interaction
with
PFD
scenario,
a
a
PGP
session
may
be
established
while
EFT
session
is
still
down.
O
Sanera,
PE,
articulated
or
poor-quality
link
may
be
lots
in
the
corresponding
PFD
session
going
up
and
down
frequently
when
PTP
session
is
established,
so
particularly
for
a
BGP.
A
typical,
a
BGP
peel
can
be
multi.
Hop
away
on
those
scenarios
are
likely
to
be
observed.
The
consequence
of
the
impact
will
be
the
traffic
being
black
hole
raj
in
june,
and
the
network
interruptions.
O
O
O
O
Only
if
both
the
local
PGP
speaker
and
its
remotely
to
be
peer
have
a
PFD,
Street
mode
enabled
then
BGP
session
establishment
will
be
prevented
until
it's.
If
these
sessions
up,
if
is
appear,
has
not
advertised
beach
ppfd
capability
with
street
mode
enabled,
then
a
BGP
session
should
not
be
required.
Prayer
to
the
BGP
session
establishment.
O
O
It
also
enables
a
page
of
his
speak
to
signal
its
peer
additional,
be
of
the
extension
using
an
optional
parameter.
Pfd
capability
follow
in
the
proposed
the
street
mode
operations.
We
avoided
a
situation
which
results
in
the
routing
true
and
in
minimized
impact
of
networking
interruptions
and
next.
O
T
O
I
mean
the
situation.
Part
of
situation
now
come
on
to
all
the
control
protocol.
I
think
if
you
refer
to
the
section
4
point
wine
of
IFC
5
a
2,
it
also
described
the
control
protocols,
neighbor
session
establishment
problem.
This
is
the
commencing
right,
so,
if
you
want
using
so
we
have
to
do
the
single
no
need
to
break
the
the
locking
issue
of.
T
I
Robert
Rashad,
so
this
strict
mode
has
been
proposed
in
OSPF
and
and
Averell
groups
as
well
for
BFD,
but
your
slides
said
something
interesting
that
you
don't
want
to
establish
bgp
session
when
the
link
quality
is
poor.
That
sounds
perfectly
great,
except
PFD.
Today
doesn't
really
determine
link
quality,
as
such
an
encounter
may
mean
different
things
for
different
people.
Bfd
today
gives
you
ability
to
sign
out
the
purists
up
or
down
right.
There
are
proposals
in
VFD
to
actually
enhance
BFD
to
do
more.
C
O
A
H
H
O
Okay
also
and
you
and
you
can
correct
them,
okay,
so
the
major
issue
is
to
avoid
that
the
potential
deadlock-
okay,
if
you
prevent
you
peer,
doesn't
know-
or
sometimes
you
hear-
maybe
waiting
for
a
session
come
up
before
they
create
the
PFD
session,
so
deadlock
situation
coming
they'll
never
be
able
to
step.
It
should
be
a
few
new
session.
D
F
Vendors
already
support
strict
mode,
including
us.
There
are
situations
in
which
you
you,
you
have
it
configured
on
both
sides
and
normally
you
want
to
use
it,
but
you
may
have
a
situation
like
immediately
after
an
upgrade
or
something
where
you
don't
want
to
use
it.
One
time
when
you
come
up
and
this
way
by
signaling
it
you
can
handle
those
situations
where
you
don't
want
to
use
it
and
they're.
Also.
What
pointed
out
there's
been
bugs,
where
there's
been
a
deadlock
between
different
implementations
of
strict
code.
J
Okay
or
brittle
arcus
I,
actually
like
the
document,
so
I
have
no
problems
with
that,
but
I
would
be
really
interested
in
knowing
exactly
what
Alexander
asked.
Why
would
you
need
capability?
You
could
hold
the
peering
session
at
your
end
locally,
when
you
need
it
and
42
71,
which
is
the
base
bgp
specification,
actually,
as
nice
section
of
connection
collision
in
built
or
define
in
there
so
at
the
worst,
both
ends
will
keep
on
retrying.
That's
about
it,
but
I
really
don't
see
the
need
of
capability.
Q
Himanshu
from
Siena,
so
this
is
good,
but
I
think
this
has
a
limited
application
in
the
sense
that
it
doesn't
take
care
of
the
route
reflector
clients.
So
you
have
a.
You,
may
be
okay
without
processing
establishment
with
the
route
reflector
server
in
the
client,
but
between
the
two
clients,
where
there
is
no
bgp
session,
and
you
could
have
a
bad
connection
and
all
that
stuff,
so
it
real.
That
part
is
missing
here.
Obviously,
for
the
sessions
they
are
fine,
I'm,
just
saying
that
it
it
has
the
scope
of
that
application
is
somewhat
limited.
U
G
G
The
fundamental
issue
is
that
at
what
point
in
the
beach
B
state
machine,
do
you
insist
that
BFD
either
get
started
or
to
be
up
and
stable
before
you
do
things,
and
we
do
have
day-to-day
Interop
problems,
not
always
necessarily
for
just
bringing
up
the
session,
but
first
things
like
no
keep
down
type
behaviors
when
the
protocols
actually
do
say
the
FDS
down.
When
do
they
allow
to
come
back
up?
G
A
G
G
So
the
motivation
here
is
that
without
some
sort
of
signaling
it
was
like
again
what
part
of
the
state
machine.
Do
you
bring
it
up?
If
you
do
it
at
connect
or
no
connect,
retry
I
pick
your
favorite
piece
of
that
state
machine.
You
don't
necessarily
know
which
behavior
do
you
do?
Do
you
do
the
one
that
you've
been
doing
for
years
or
do
you
do
the
one
that
is
tied
into
the
new
behavior
at
a
single
point
that
we
can
interoperate
it?
G
V
For
Deutsche,
Telekom
and
I'm,
looking
at
the
description
of
what
you
are
trying
to
do
and
what
you're
doing
I
note
when
I
advise
my
customers
to
establish
PFD
on
bgp
sessions,
my
thinking
and
my
goal
is
that
they
tear
down
the
BGP
when
something
bad
happens.
What
you
are
doing
here
is
kind
of
the
other
end
of
a
BGP
session.
You
only
want
to
open
it
or
delay
the
actual
open
until
you
know
that
the
path
is
clean
and
I
think
there
might
be
a
different
approach
to
deal
with
that
situation.
V
I
would
think
that
it
is
not
necessary
that
you
delay
trying
to
open
the
BGP.
You
just
have
to
delay
actually
using
the
announcements
and
potentially
hold
back
on
the
announcements
and
I
have
the
gut
feeling
that
the
deadlocking
that
has
been
talking
about
is
be
can
be
completely
avoided.
If
you
take
that
approach.
A
A
And
just
as
alex
is
getting
set
up
here,
I
want
to
say
I
know
that
we
promised
a
discussion
on
the
BG
pls
bissell
and
anybody
who's
looking
at
their
watch
will
see
that
we
just
aren't
going
to
have
time
for
that.
I'm.
Very
sorry,
I
encourage
people
who
are
interested
in
contributing
to
that
to
find
Katyn,
and
you
know,
provide
input
in
you
know
as
time
allows.
H
There
was
a
lot
of
changes,
mergers
with
other
documents
and
again
changes
in
the
finality,
so
on
so
on,
but
the
key
principle
was
preserved
unchanged,
so
the
root
leaks
are
happening
because
of
policy
violations
and
the
root
cause
of
these
violations
is
mistakes;
mistakes
that
amazed
by
network
engineers
that
do
not
understand
how
to
apply
peering
for
a
represent
peering
policy
in
their
configuration.
So
these
draft
just
fuels
this
gap.
H
It
provides
a
native
way
to
represent
your
peering
policy
into
the
configuration
so
you're
just
sitting,
you're
you're
impulsive,
the
configuration
and,
after
that,
every
the
filtering
is
done
automatically.
So,
let's
jump
to
the
role
specification.
As
you
see,
most
of
the
roles
are
native.
If
you
are
a
customer,
your
all's
customer,
if
you
are
a
provider,
you're
always
provider,
but
what
is
if
you
are
route
server,
you
know
form
from
the
mathematical
standpoint.
H
The
answer
is
clear:
there
is
no
difference
between
genetic
change
points
that
provides
partial
connectivity
and
Internet
service
provider
that
can
also
provide
partial
connectivity.
So
I
thought
that
everybody
will
be
happy
to
they're
out
server.
Is
a
provider
and
go
on
with
this,
and
I
was
wrong,
even
people
that
were
carefully
reading
the
draft
were
confused
and
so
the
in
the
last
version
of
the
draft
we
changed
it.
H
So
if
you
are
providing
a
router
if
your
router
you're
always
router,
if
you
are
my
interpreter,
your
own
Kauai
interpreter
so
I
hope
these
will
solve
the
problem
with
uncleanness
and
uncertain.
I
was
really
not
happy.
Dropping
the
idea,
math
model,
but
simplicity
is
the
winner.
So
with
this
I
would
like
to
ask
for
working
group
last
call.
We
have
three
open
source.
Implementations.
I
would
be
glad
to
see
other
vendors
during
the
party.
So
that's
all.
That's
all
any
questions.
A
S
S
Five,
seven
seven,
seven
five
yeah
have
defined
the
BGP
prospects
occasion
as
I
for
the
beach
refers
back
and
already
defined
in
many
many
component
types
were
they
acted
before
IP
prefix
IP
protocol
and
for
some
draft
have
defined
they
layer,
2
VPN
VLANs,
for
the
component
types
so,
for
this
draft
have
adjusted
to
defined
to
new
component
types,
were
they
seed
of
I?
Sorry,
six,
so
the
first,
the
first
component
I
pays
for
the
whole
128
bits
of
seed,
even
the
host
eight.
S
We
also
use
a
pair
of
operator
in
the
value
2
for
the
match
rule
in
the
operator
type
operator
bytes.
We
have
seen
the
last
less
than
greater
than
and
the
yuko
and
the
value
should
be
the
whole
seed
128
assist
for
together
with
the
oak
returns
at
the
value
we
can
indicate
how
about
they
are
certain
exactly
in
seed
or
a
range
of
the
city
to
match.
For
the.
S
So
we
give
another
type,
come
on
and
type
2
to
match
some
field
or
some
feats
of
this
city
to
match
such
as
we
also
use
a
pair
of
operator
and
the
Vario
to
indicate
the
morrow.
So
in
the
operator
we
defined
the
type
field
to
indicate
which
children
or
which
speeds
who
want
to
march.
So
now
it
gives
four
bits
for
the
in
the
future.
We
may
have
very
flexible
extent,
so
you
know
we
just
came
44
times.
First,
one
is
for
the
locator.
S
Second
is
function,
ID,
and
also
some
group,
together
with
function,
locator
and
a
function
or
function,
arguments
so
for
the
very
office
we
use
seed
and
mosque.
Two
flexible
two
together
indicate
the
value
about
there's
some
fielder's
piece
off
the
seat.
So
together
they
say
it's
for
the
second
component
type.
So
for
this
two
times,
so
it
gives
not
only
the
whole
128
in
situ
margin,
but
also
some
beads
and
feels
too
much
okay.
So
it's
very
easy
to
understand
just
to
give
two
components
for
the
newest,
re6
Network.
So
sorry,
okay,.
W
From
Holly
from
our
point
of
view,
because
the
s
are
actually
the
coulomb
for
the
match,
but
because
of
the
I
sorry
see
that
can
be
used
as
a
v6
the
destination,
but
it
is
a
totally
different
from
the
ipv6
address.
So
that's
either
we
properly
so
type
user
can
match
the
IP
destination
address
of
the
ipv6,
the
packet,
the
path
a
user
can
use
that.
As
a
sorry
succeed.
X
S
C
A
Any
further
questions
or
comments
all
right.
Thank
you
very
much.
We
have
two
minutes
left,
but
that's
just
clearly
not
enough
time
to
have
a
useful
conversation
about
the
BG
pls,
miss
I'm.
Again,
sorry
about
that,
encourage
you
to
find
k10
and
talk
to
him
about
it.
Thanks
everybody!
This
was
I
thought
a!
You
know
very
interactive,
interesting
session,
see
you
next
time,
blue
sheets,
please.
