►
From YouTube: IETF104-IPSECME-20190328-1050
Description
IPSECME meeting session at IETF104
2019/03/28 1050
https://datatracker.ietf.org/meeting/104/proceedings/
A
B
B
D
B
C
E
Right
so
I
think
it's
time
to
start
so
I'm,
giving
this
a
check,
Amy
working
group
meeting
and
we
have
a
quite
tight
schedule,
so
we'll
probably
go
forward
very
quickly.
This
blue
suit
should
be
sorry.
These
are
not
well.
You
probably
have
seen
this
at
least
once
before
this,
so
we
have
Bruce
it's
going
around
and
I
mean
it
would
like
to
have
a
couple
of
note
takers.
We
are
using
the
eater
pad.
So
take
note.
E
D
E
E
Alright
follow
the
helper
alright,
so
so
we
have
chopper,
we
have
a
mythical.
We
have
an
interpreter,
that's
wrong,
URL
and
we
have
an
here's.
Our
agenda,
and
it
is
we're
still
have
has
your
two
minutes
before
dinner
code
here,
but
we
are
going
to
be.
We
have
lots
of
10-minute
systems
which
are
you
know,
going
to
be
hard
to
keep
in
time,
because
people
are
always
want
to
have
a
discussion
under
not
very
many
the
time
for
you
know,
crystals,
alright.
E
D
E
F
E
G
E
E
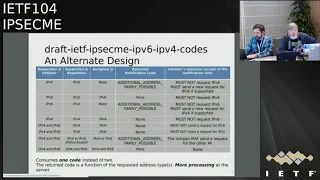
If
you
haven't
heard
it
here
is
the
first
line,
it's
an
ipv4
requested
and
the
respondent
support
ipv6.
It
can,
of
course,
I
can't
allocate
any
adverse.
It
just
says:
return
error
code,
I
think
he
seeks
only
allowed
and
so
on
and
and
same
thing.
If
he
you
know,
if
you
request
ipv6
and
it
supports
ipv6.
This
gives
you
like
pv6
Anderson,
still
says
you
that
ipv6
only
allowed
meaning
that,
if
even
if
you
ask
before
separately,
he
wouldn't
be
getting.
E
You
wouldn't
be
getting
you
that
and
if
you
ask,
you
know
ipv6
and
that
respond
only
supports
ipv4.
It
will
not
assign
you
anything
and
keeps
you
on
with
the
ipv4
allowed
and
same
thing
with
ipv4.
You
know
only
stuff
and
1011
little
bit
more
interesting
stuff.
If
you
requester
asks
both
ipv4
and
six
and
the
responder
only
supports
I
mean
before
he
of
course
gives
you
an
idea
up
in
four
hundred
sees
and
says:
I
do
before
all
allowed
and
same
for
ipv6.
And
then,
if
you
have
a
policy,
they
are
saying
that.
E
Oh
yes,
three
question
asked
both
ipv4
us
out
to
be
six,
but
the
responder
supports
it
so
that
you
you
can
have
either
one
of
them,
but
not
at
the
same
time.
So
he
returns.
You
know
one
of
them
and
he
doesn't
return
any
error
code
because
it's
no,
it's
not
only
ipv4
ipv6
supported
and
the
last
one
is
that
we
support
both
ipv6
and
ipv4
in
both
ends,
and
we
return
both
of
them
and
aware,
of
course,
I.
E
Did
it
like
this
proposal
because
there's
two
not
two
testing
codes
and
we
already
have
these
cases
in
some
other
places
where
we
have
this
kind
of
additional
xxx.
You
know
a
lot
of
a
possible
what
we
have
in
traffic
selectors.
We
have
additional
traffic
selectors
possible
or
or
something
like
that.
If
you
try
asking
something
and
you
get
something
back,
but
you
know
that's,
not
everything
you
could
get
more.
E
If
you
ask
more
questions
so
so
in
here,
if
you
ask
I'd
be
before
address,
ponder
only
support,
you
know:
ipv6,
it
returns
you,
it
doesn't
return,
do
anything
because
you
got
it
can't
fulfill,
but
it
says
that
then,
if
you
ask
you
know
something
else
like
wrapping
e6
address,
you
will
get
that
and
if
you
ask
ipv6
hundred
and
you
get
ipv6
address,
that's
what
you
only
get.
No,
no
error
codes
and
same
thing.
E
If
you
ask
ipv6-
and
you
know
responder
soup
or
something
before
you
and
and
you
know
it
doesn't,
give
you
anything
but
returns
an
error
code,
and
these
next
three
months
are
it's
just
that's
what
you
ask
you
know
without
any
error
code,
because
there's
only
one
option
today.
The
second
last
one
is
the
interesting
one
is.
If
you
ask
I
p,
v6
and
ipv4,
both
and
responder
has
a
policy
that
oh
we
can
I
can
do
why
baby
six
and
I
can
do
ipv4,
but
I
can't
do
them
on
the
same
essay.
E
It's
it's
most,
the
same
addictive.
The
one
that
does
you
know.
I
just
know
thing
is
something
that
we
have
used
earlier.
The
other
one
is
it's
bit
more
explicit,
saying
that
only
this
one
is
supported
only
that
is
supported
in
the
original
versions.
They
had.
You
know
a
couple
of
more
extra
codes
that
we
got
eliminated
and
but
do
you
have
any
anybody
have
any
comments
and
nobody
has
any
feelings
for
how
to
build
it.
Well,.
F
It
was
me
who
tested
well
anyway.
It's
mine
idea
is
first
not
to
use
our
status
top
talent
if
ocation
status,
notifications
that
you
start
a
stopped
notification,
because
it's
a
ignore
it.
If
you'd
understand
it,
it's
okay
and
don't
well,
don't
say
only
this
about
it
in
supported,
beautiful
I,
support,
ipv6
and
minimize.
The
Rainbows
is
notification,
so
a
since
the
terrace
design
is
good
and
my
design
was
good
enough.
It's
it
was
very
similar,
so
the
draft
is
nothing
to
be
changed
to
accommodate
these
ideas.
It's
my
opinion.
So.
E
All
right,
I
think
we
need
to
continue
this
something
mystical
rather
I.
Don't
think
we
have
enough
people
commenting
here
and
if
you
have
only
one
or
two
people
and
at
the
outer
in
the
other
side,
I
think
it's.
We
don't
have
a
clear
consensus
that
both
of
those
are
actually
acceptable
and
I.
Don't
think
they
I,
don't
think,
there's
anything
wrong
with
their
choice.
It's
just
that
would
be
more.
You
know
nicer
to
have
less
codes
as
well.
Alright,
so
I
think
that's
that
covers
our
current
crafts
that
we
have
set.
F
Update
of
intermediate
exchange,
it
was
previously
called
ox
like
ox.
Now
it
is
called
intermediate
so
or
adjust.
If
you
forget
it,
quick
Olivia,
what
is
it
so?
If
transfer
what
you
want
rotated
between
before,
like
else
we
define
a
new
exchange
type,
it
is
called
intermediate
x-bike
ox
and
it
is
continuing.
People
know
that
it
can
be
fragmented,
so
we
turned
have
Alicia's,
who
is
a
large
payload
size
and
IP
fragmentation,
and
so
what
was
changed
from
previous
version,
so
somebody
changing.
F
F
The
other
change
is
more
important.
It
was
changed
the
way
the
exchanging
authenticated.
So
it
was
a
discussion
with
Scott
about
this
particular
issue,
so
in
police
design,
each
party
included
only
he's
a
for
only
intermediate
exchanged
messages
into
its
signature.
So
and
we
have
discussions
some
discussion,
it
is.
G
F
H
H
E
E
H
H
F
I
H
H
F
H
F
F
J
Poly
Apple
so
in
general,
I
think
it's
good
I,
like
the
updates
to
the
document.
I've
sorry
I,
supported
in
that
regard,
I
agree
that
having
Ike
underscore
in
there
would
be
a
little
clearer,
so
don't
really
care
too
much,
but
a
minor
+1
and
then
just
to
clarify,
because
I
looked
up
the
text
around
the
only
thing
that
mentions
Eickhoff
being
packet,
one
it's
so
it's
in
the
part
that
we're
defining
message
IDs
and
it
says
that
the
in
it
is
message
zero
and
then
just
has
like
an
example
sentence
in
which
it
says.
J
F
I
I
K
F
Think
it's
possible,
but
isn't
it
duplicate
smoke
doubles,
so
I
think
that
content.
In
any
case,
you
must
define
a
content
intermediate
exchange,
but
the
current
dropped
serves
a
main
purpose.
It
defines
how
you
authenticate
this
exchange
and
how
it
is
negotiated,
how
error
are
handling
in
case
they
happen,
and
if
you
redefine
it,
it's
error
application
document.
You
need
to
repeat
all
these
texts
and
probably
to
repeat
the
code
I,
don't
know
it
depends
on
implementation.
F
E
Documenting
not
as
a
chair
but
yeah
I
think
it
actually
is
because
if
the
to
integrate
the
exchange
is
really
a
framework,
so
we
could
say
that
okay,
we
don't
have
an
excess
type
for
it
at
all.
We
only
have
said
that
this
is
the
framework.
How
do
you
do
these
things?
This
is
you
know
this
is
how
you
actually
send
the
you
know
stuff,
and
then
all
the
you
know,
documents
that
actually
you
know
use.
E
It
would
then
define
their
own,
which
would
have
a
good
thing
because
we
tend
it
could
actually
have
a
you
know.
Example
like
we
have.
If
we
have
a
like
owls,
we
have
a
create
child
essay.
Then
we
could
have
you
know
USDA,
you
know
exchange
there,
which
has
this
is
using.
You
know
the
framework
of
what
you
have
there,
but
using
completely
different.
E
It
would
allow
you
know
this
kind
of,
and
it
also,
but
of
course
that
would
also
mean
that
we
and
actually
I
think
that's
actually
one
of
things
that
you
know
Nico
says
in
interim
intermediate
is
actually
most
of
the
time
pointless
per
se.
You
are
not
really
negotiating
that
you
are
gonna
use
framework.
You
want
to
negotiate
that
I
want
to
use
this
feature.
That
is
using
the
framework,
which
is,
of
course,
you
know
if
you
are
continuing
to
ska
I
mean,
and
it
requires
intermediate.
E
F
E
Sort
of
thesis
that,
because
we
are
still
want
to
do
that,
we
this
is
you
know,
exchange
we
do
before
I
called
and
it's
not
a
you
know,
gain
Eric.
You
know
this
kind
of
thing.
You
know
you
could
say
that
okay,
this
has
certain
meaning
of
because
of
that,
and
it's
only
meant
to
be
transport.
You
know
stuff
that
is
needed
for
I
cows
or
before
I
like
out.
In
that
case,
it
could
be.
You
know,
say
that.
E
Okay,
we
have
that
the
10
you
could
have
a
negotiation
of
the
you
know
like
intermediate:
it's
actually
lists
what
protocols
can
be
inside
there
like
it's
it
for
you
know
to
so
have
the
notification
of
supported
you
could
have
a
you
know,
feels
they
are
selling
that
we
do
support
this
key,
a
Chiari
mortis
or
this
gear
stays
more
risky.
Xa
Marshall,
but
I
mean
both
of
these
are
actually
done.
I
think
it
would
be
useful
to
think
about
and
see
and
that
but
I
don't
think
yeah.
G
G
L
E
Now
exorcist
yeah,
they
were
sequestered
us
to
velocity.
Do
a
hammer
this
analytic.
Actually,
this
too
early
I
think
this
actually
isn't
anything
that
we
can
actually
start
working
on.
This
manatee
selecting
fruit
crop
so
I
think
it
because
I
mean
I
mean
both
of
these
are
actually
completely
valid.
You
know,
ideas
and
people
has
been
and
I
think
it's
more
like
a
design,
you
notice
kind
of
what
is
nice
and
it
depends
on
source
or
how
many
of
these
things
to
be
happy
record.
E
All
you
have
your
one
cue
sta
is
the
only
one
is
going
to
be
using
they're
so
different
than
if
people
are
seeing
that,
oh,
you
can
have.
You
know
several
different
other
things
that
would
be
using
that
it's
like
a
little
bit
different,
but
that
so
I
think
this
is
actually
something
we
could
should
go
to
the
list
and
think
about
they're
a
little
bit
more.
But
now
I
want
to
exercise
what
question?
E
Does
anybody
see
any
have
any
objections
to
taking
this
or
working
group
crafts
and
knowing
that
we
can
actually
still
have
a
continue,
working
and
modifying
it
heavily
in
when
it's
working
for
craft
actually
more
easily,
because
we
can
always
changed?
It's
all
terrific
so,
and
we
have
already
discussed
this
in
list
and
I
haven't
seen
anything
anything
in
the
list.
That
would
say
otherwise.
So
I
will
actually
go
and
push
the
button
and
make
it
as
a
feature
of
product.
So
you
can
actually
put
the
next
version.
We
can
prove
an.
G
F
G
F
F
F
G
G
F
E
Alright,
so
more
comment,
I
would
hate
to
see
that
kind
of
happening.
Please
happen,
I
mean
having
seven
to
new
traffic
types
is
bad.
All
of
them,
sharing
the
same,
transform
type
tip
for
is
even
worse
and
because
I
they
are
not
interchangeable.
I
mean
I
mean
that
if
you
human
groups,
we
have
in
transform
tip
type
for
our
groups
for
specificity
for
common
type
of
thing.
These
are
completely
exchanged.
You
know
things
that
don't
have
anything
to
do
with
that
kind
of.
F
E
I
would
really
think
that
they,
if
you
actually
want
to
make
a
new
transport
type,
we
could
we
would
actually
make
a
new
one
and
make
a
crumpet
in
the
register,
for
that
would
only
include
there.
You
know
things
that
are
you
know
in
this
and
I
I,
don't
really
see
that
we
actually
to
have
it
and
the
order,
if
you
actually
want
to
have
an
order
negotiated.
That's
also
something
that
is
said
in
most
of
the
cases
it's
very
fixed.
No,
it
isn't
because,
usually
the
police.
E
You
have
to
say
that
we
do
this
and
dice
and
that
that
those
are
the
only
works.
You
are
a
trust
or
it
might
be
saying
that
they
lease
keep
things
that
we
don't
support
or
the
other
in
such
a
support,
but
usually
tells
okay
week,
I
mean,
for
example,
if
you
think
about
the
multiple
out
indications,
we
have
this
draft
multiple
indicators.
In
that
case,
we
already
left
everything
in
there.
We
don't
actually
negotiate.
You
know
what
out
in
the
cases
you
are
doing
in
the
beginning.
E
It's
just
do
two
different
island
occasions,
and
you
know
they
assume
that
they
are
configurating
in
in
the
both
ends
or
access.
The
recipient
feels
asked
for
something
this
way,
but
anybody
say
dates.
It's
one
by
one
you
do
one
and
then
you
do
a
government
to
do
other
one
under
the
other.
One
is
how
happy
at
fit-
and
it's
saying
that
okay
now
done
and
I
think
similar
kind
of
thing
would
be
here.
F
First
of
all,
from
the
point
of
view,
all
these
quantum
exchange
serves.
The
same
purpose
is
difficult
money,
so
it's
exchange
methods
then
sharing
since
the
register
will
allow
us
to
reuse
to
use
this
post
constantly
exchanging
like
I,
say
I
need
to
so
you
can
just
in
time
for
it.
You
will.
If,
if
the
key
is
not
enough,
so
it's
very
variant
in
the
future,
then
it
would
allow
us
to
use
classic
keep
multiple
classic
exchange.
M
That
we
actually
talking
about
most
of
what
I
was
going
to
say,
but
I
like
to
emphasize
that
one
of
the
things
we
certainly
wanted
to
do
is
allow
well
we'll
do
this.
But
we'll
do
this.
Picard
classical
group
plus
you
to
this
particular
latest
group,
or
that
particular
latest
key
exchange
and
also
will
will
insist
on
a
misogyny
group
disallowed.
This
one
a
construct
allows
that
to
be
done
relatively
straightforward
to.
I
Be
asylum
well,
first
of
all,
I
also
seek
good
reasons
to
use
to
classical
keeps
changes
that
we
have
right
now,
combined
in
a
hybrid
Keith's
change
and
I.
Tell
you
a
key
idea
of
you
know
just
adding
another
layer
of
hierarchy
where
you
can
sort
them
into
groups,
but
I
will
still
put
the
old
ones
in
there
as
diffie-hellman
groups,
so
you
could
still
combine
old
ones.
The
way
you
like
it
and
use.
I
N
I
had
some
of
the
same
comments
about
the
transferrin
types,
but
Martin
cotton,
but
maybe
I,
would
just
ask
question
because
I'm
just
confused
by
something
is
that
in
registrations
that
you
make
in
the
arianna
consideration
section,
do
you
have
seven
of
these
seven
new
ones
right,
I
didn't
see
a
place.
Otherwise
in
the
document
where
it
talks
about
that
limit
that
the
number
seven.
F
F
E
I
mean
we
could
do
this
also,
so
that
I
don't
see
any
reason
why
we
have
to
negotiate
all
of
this
in
the
first
I
for
first
essay
payload
this.
If
he
because
it
in
the
first
essay
panel,
that's
going
to
be
very
difficult
to
her.
If
we
have
any
parameter
still,
you
know
what
what
what
discuss
this
in
early.
You
know
key
a
group
or
something
like
that.
E
How
that
interacts
you
there,
and
so
how
do
so,
so
what
what
I
was
thinking,
but
it
would
be
better
to
do
that
that
they,
actually
you
know,
each
of
these
intermediate
steps
has
said
negotiated.
Okay,
I
want
to
use
one
of
these
for
free.
You
know,
Pierre
says
whether
one
of
them
can't
be
classical
group
for
the
other.
One
could
be,
you
know,
group
type
for
the
other.
One
could
be,
you
know,
type
seven
with
CC
or
whatever
the
number
is
X
number.
This
is
saying
that
we
are
doing
this
kind
of
it.
E
You
know,
first
quantum
you
know
algorithms
and
then
the
other
ones
when
did
receives
that
it
picks
whatever
he
thinks
like
it.
It's
okay
or
actually
there
is
that
if
the
key
extends
you
know,
pillows
are
big,
you
probably
want
to
you
know,
guess
correctly
or
you
want
to
actually
you
know
negotiate
first
and
then
do
the
extra
extra
round
trip
there
to
do
the
negotiation,
but
having
them
to
be.
You
know,
negotiated
in
the
beginning,
all
the
seven
different
algorithms
in
the
order.
E
What
they
are
going
to
be
doing
is
going
to
make
an
essay
payload
huge.
If
you
want
to
support
multiple
different
combinations
of
those,
because
you
have
to
say
okay,
you
can
do
this
first,
this
first,
this
you
know.
Second,
okay,
of
course,
I
also
want
to
make
that
you.
What
you
are
not
going
to
be
selecting
you
know
all
same
has
to
be
one
thousand
pitiful
human
crowd
for,
but
the
we
will.
E
You
will
propose
that
said
that
in
else
possible
places,
because
you
would
say
that
you
can
do
that
phone
in
in
any
place,
but
we
got
seven
powers
in
the
row
is
actually
not
going
to
help
anybody.
So
that's
why
I
was
thinking
about
you
know
doing
this
in
the
beginning,
it's
a
little
bit
bad
devil,
so
I
was
think
about.
It
would
be
balanced,
better
saturated
the
x-ray.
E
F
G
E
E
O
Wanted
to
say
that
I
agree
with
the
principle
of
not
giving
any
special
treatment
to
the
quantum
safe
groups.
I
think
they
should
be
in
the
same
register,
usually
that
if
you
Helmand
groups
do
I
want
there,
the
flexibility
to
be
able
to
take
a
classical
classical,
hybrid
or
quantum
quantum
hybrid,
if
necessary,
having
them
all
in
the
one
place
is
yeah,
helps
to
thing
I.
M
Did
scar
floor
I
like
to
respond
for
bought
product
potato
about
two
things?
What
about
parameters
well,
I
would
like
to
remind
them
that
transforms
can
have
attributes,
and
it's
unclear
at
all.
It's
immediately
unclear
whether
or
not
we'd
make
sense
to
have
attributes
to
key
exchange
transforms,
but
the
possibility
is
there.
In
addition,
he
seems
he's
worried
about
the
size
of
the
SI
proposal.
If
you
have
a
large,
if
it's
rather
complex,
I
believe
that
with
them
with
the
inherent
and
which
is
with
built
into
proposals,
would
be.
F
So
well,
two
more
points
so
in
the
main,
clip
known,
transform
addy
if
any
of
this
exchange-
and
that
means
that
this
exchange,
the
same
number
are
all
optional.
You
doesn't
do
it
and
for
compatibility
with
legacy
implementation,
you
need
to
define
to
unit
in
clip
to
balad
sorry,
two
proposals,
one
of
these
exchange
diamonds,
rather
without
so.
F
C
F
This
is
an
example
of
how
look
if
you
express
your
policy
or
I
want
to
do
is
b-52.
You
know
you
could
say
needs,
then
you
hope,
son,
father's
and
either
are
we
all
done,
is
a
sitcom
and
aromasin.
It's
just
an
example.
Well,
another
stuff
and
the
usual
additional
keeps
changing
policy.
It's
not
an
easy
task,
and
we've
discussed
quite
a
lot
about
it,
and
the
current
proposal
is
to
this
requirement
that
were
take
into
consideration.
Is
that
message
size
too
much
evenly?
F
F
O
E
E
F
F
Confirmed
then,
this
our
creature
of
the
say,
is
a
company
bus
by
some
trailer
into
information
exchanges
it
from
additional
key
exchanges,
and
only
once
all
these
exchanges
are
done.
The
new
si
is
created
so
there's
a
new
notification,
additional
exchange
that
allows
responded
to
link.
It
is
a
four
initiator
to
me.
This
exchanges,
because
she
sends
a
request
receives
response
immediately,
start
new
request.
F
F
Notification
is
needed,
so
it
is
like
okay,
so
it
is
meaningful
only
for
responder.
It
allows
him
to
link
this
exchange
together.
So
next
steps.
So
just
at
notification.
A
lot
of
codification
is
noted,
south
meeting
to
discuss
alternative
stuff,
in
particular
part
a
chalice,
a
and
as
soon
as
the
tapas
sound.
The
message
is
released
so
I
think
he
just
smiles
or
everything
we
discussed
there.
So
the
toughest
we
worked
further,
that's
ink.
It
is
a
woman.
So
any
questions
comments
move
forward.
O
I
G
F
F
F
D
In
the
IETF
we
we
generally
are
adopting
an
approach.
Not
a
specific
draft
I'm,
so
I
would
prefer.
I
would
prefer
that
we
work
out
some
of
the
mechanism
issues
here
before
we
adopt
the
drafts
properly.
So
maybe
we
can
resolve
the
the
mechanism
discussion
on
the
list
and
then
do
a
quick
adoption
call.
Then,
okay.
E
Q
F
I
To
be
a
spider,
that's
an
implement
us
view
in
the
hybrid
quantum
key
exchange
and
I'm
the
inferno.
So
that's
what
all
the
fuss
is
about.
Those
are
the
17
key
exchange.
Canada's
stood
on
NIST
competition
right
now
for
post
front
and
Keith's
changes.
We
see
it
as
three
big
categories,
lattices
codes
as
or
Chinese,
and
all
of
them
are
quite
dead.
Do
you
have
disadvantages
compared
to
what
we're
using
now?
So
they
do
have
bigger
keys.
They
might
be
a
lot
less
fast
and
we
don't
know
how
secure
they
are
overall.
I
So
we
actually
want
to
do
a
hybrid
key
exchange
because
we
don't
really
trust
them,
so
we
want
to
have
a
fallback
which
is
our
classical
key
exchange.
So
what
we
do
is
we
combine
a
classical
heat
exchange
and
when,
if
there's
new
methods-
and
that
is
here's-
a
simple
method
of
doing
it-
like
the
most
simple
method,
you
could
do
just
to
find
any
a
group
call
it
streamlined
and
2
prime
plus
65
5
online
Kakao
tonight
the
keys
and
put
them
in
e
ke
payload.
I
I
That's
a
problem
might
be
a
problem
and
also
you
can't
use
fragmentation
so
talking
about
fragmentation
using
did
588
ipv6
fragmentation
threshold,
that's
what
you
still
can
use
if
she
cannot
fragment
and
it's
even
worse
for
ipv4
there's
only
two
things
left
that
you
could
use.
So
that
is
not
just
the
right
solution
to
that
problem.
Actually,
so
my
next
implementation
is
placed
on
and
Valerie's
draft
or
ask
the
what
Valerie
just
presented.
I
I
It
looks
great,
so
this
is
the
same
as
before,
just
using
knee
approach.
Now
this
also
challenges,
that's
the
V
key
and
it
looks
complicated
and
it
is
complicated
and
it
has
a
lot
of
problems
we
we
have
to
keep
state.
We
have
this
additional
and
notify
using
that
link
cookie,
because
actually
the
transmission
window
might
be
bigger
than
one.
I
So
if
you
can't
fragment
decree,
try
to
say
we
can
just
put
it
all
in
there,
so
we
would
do
an
educated
guess
on
what
the
responders,
probably
accepting,
because
we
don't
know
yet
well
I-
think
that's
no
problem,
just
put
it
all
in
there
and
she's
gonna
accept
it
or
not.
Otherwise,
it's
just
handled
the
usual
way
using
invalid
K
payload.
I
So
now,
finally,
if
guarded
we
we
can
do
fragmentation.
We
it's
a
fully
functional,
hybrid
key
exchange.
We
can
be
most
random
if
there's
methods
are
actually
secure
right,
not
yet
there's
two
more
that
we
do
not
support
yet
and
why
don't
we
support
them?
So
I
made
a
plot
on
the
y-axis.
We've
got
the
public
key
size
and
megabyte
on
the
x-axis.
Is
the
encryption
speed
speed
of
these
mechanisms
and
that
red
line
down
there?
That's
the
64
kilobyte,
which
is
the
size
limitation
of
caplet
substructures?
I
Actually
because
pay,
let's
go
to
16-bit
size
field.
We
can
put
those
in
a
ke
payload
and
release
is
actually
quite
special
because
it's
it's
quite
popular
among
the
cryptographers,
because
it's
been
around
for
several
years
like
1978,
I,
guess
and
it
hasn't
been
broken
and
just
it
has
gotten
review.
So
if
you
want
to
do
post
quantum
keeps
changed
today,
you
probably
would
want
to
use
that
one
and
that's
an
unresolved
problem.
We've
talked
about
it
yesterday,
actually,
but
there's
no
documented
solution
to
it.
So
conclusion,
I
would
like
this
draft.
I
She
reduced
the
complexity
overall,
especially
the
wreaking.
We
should
find
a
way
to
support
mekinese
keys,
and
this
draft
does
not
contain
any
first
quantum
kicks
and
transforms
so
either
put
them
in
there
or
real
label
it
to
hybrid
key
exchange,
because
that's
what
it
is
right
now.
Otherwise
it
is
functional.
We
can
do
hybrid,
post,
quantum,
key
exchange
and
I
guess
just
no
security
problems
there.
So
Bobby.
F
Of
us
least
and
I
think
that
Coach
I'll
to
say
is
a
little
bit
challenging
to
implement,
but
otherwise
the
proposal
to
put
all
the
exchange
belong
to
the
same
message,
has
significant
drawbacks.
So
that
message
would
become
extremely
large,
quite
extremely
rich
and
we
don't
want
the
press
call
to
lose.
F
F
Before
there's
a
mailing
list,
it
is
quite
possible
if
people
don't
want
to
use
this
geese,
so
we
can,
we
can
do
it
well,
it
is
not
it
in
sub-optimally
we
can
break
these
huge
public
keys
into
several
key
exchange,
broad
adjacent
exchange
below
and
just
put
them
into
the
single
message.
It
is
not
a
good,
it
is
not
optimal
way,
but
it
will.
It
is
workable,
at
least
so.
Just
thank.
I
You
very
so
yeah,
actually
I
made
these
slides
before
I've
talked
to
yesterday.
So
I
do
know
your
position,
and
this
and
I
see
now
the
problems
you
try
to
solve.
I
still
think
this
is
not
the
optimal
solution,
so
maybe
put
it
all
into
a
singer.
Other
additional
key
exchange,
don't
use
informational.
I
So
I
didn't
like
the
use
of
information
that
you
would
have
to
you,
know
parse
context-sensitive
and
see
where
you
are
and
if
this
information
actually
contains
two
key
shares
and
so
on,
and
maybe
put
it
all
into
one
additional
I,
don't
know.
I
I
cannot
offer
any
solution
or
I
see
a
problem
there
and
having.
I
P
I
E
G
So
yeah
I'm,
Leone,
pocket
and
I
will
say
a
few
words
about
hybrid
Ike
in
strongswan,
so
I
think
you
are
all
aware
that
highly
sensitive
data
needs
to
be
protected
with
most
quantum
cryptography
very
soon
and,
however
considerable
time
is
required
for
standardizing
algorithms,
implementing
and
testing
and
so
on.
So
and
that's
why
we'd
like
to
have
a
standard
soon
and
to
explicitly
support
adoption
of
these
two
documents.
G
A
payload
and
the
key
shares
can
be
transported
by
are
the
odds
or
intermediate
exchange,
but
they
can
also
be
transported
in
create
child
as
aid
to
allow
for
wreaking
and
multiple
child
as
a
sand
in
case
in
case
Keisha
is
sent
which
is
not
supported
by
the
responder.
We
use
an
invalid
qsq,
a
payload
to
indicate
support
for
another
post
quantum
algorithm
and
for
post
quantum
algorithms.
Currently,
lib
oqs
library
is
used,
which
provides
some
of
the
round
one
candidates
of
the
nist
standardization
process
and
yeah.
L
R
E
L
Okay,
hello,
so
Tobias
here,
I'm,
not
talking
about
post
quantum
I'm
for
sure,
so
we
have
done
with
this
topic.
This
presentation
is
about
the
ESP
header
compression
and
the
presentation
is
because
lasts
ITF.
We
had
this
discussion.
Why
is
this
document
so
complicated
and
I
would
like
to
explain
why
it
is
like
that
and
I'm
trying
to
make
it
short.
L
L
So
I
keep
this
short
I
just
run
through
a
few
ideas
and
you
can
use
it
for
basically
anything
you
do
with
IOT
and
the
basic
thing
about
IOT
is
they
want
an
IP
stick
and
my
or
our
thing
is
if
we
want
to
if
we
want
to
have
an
IP
stack
and
we
should
allow
people
to
use
IPSec
in
IOT.
That's
my
basic
comment
about
that,
and
there
are
many
use
cases.
For
example,
my
favorite
one
is
multicast
because
it's
naturally
for
IP
a
sec,
but
that's
just
the
person
thing.
L
L
L
So
there
are
many
reasons,
but
I
want
to
go
to
one
which
is
to
wonder
draft
addresses
it's
about
compression
and
the
problem
is
the
packet
size
in
this
kind
of
scenarios
and
wireless
networks
is
a
problem
not
only
because
of
energy,
but
it's
two
major
issue
and
the
problem
is.
You
would
like
to
send
your
data
if
you
can,
in
one
single
radio
frame
and
I
put
a
few
payloads
here
which
are
typical
for
IOT
scenarios.
So
802.15.4
is
basically
the
upper
line.
L
There
are
stuff
like
Laura,
which
I
got
thought
lost
this
week,
that
we
can
actually
go
as
low
as
12
bytes
for
a
payload.
Bluetooth
is
also
can
also
be
quite
minimal.
So
whenever
you
have
an
IP
stack
on
that,
you
want
to
minimize
that,
and
there
are
many
ideas
on
how
to
do
that.
The
one
favorite
or
one
famous
solution
is
a
stateless
solution
which
is
called
6lowpan.
It
compressed
just
information
within
the
packet.
L
So
basically,
the
red
thing
here
is
the
IP
UDP
header,
and
with
this
it's
actually
three
bytes,
you
can
transport
all
the
information
you
have
in
this
huge
ipv6,
UDP
header
there
isn't
you
can
do
it
like
that
there
is
no
information
left,
it's
only
the
payload.
Another
ideas
which
is
older
and
younger
is
a
stateful
compression.
L
So,
if
that
you
have
actually
have
a
compression
state
between
the
two
peers,
which
are
communicating
the
older
one,
is
robust
header
compression,
where
you
have
a
separate
channel
to
agree
on
a
compression
context,
the
newer
idea
is,
and
that's
the
one
which
comes
from
IOT
is
that
you
have
a
static
context.
So
you
just
compile
a
contact
or
reflash
a
context
on
a
certain
device
and
how
does
basically
it
works?
Is
you
have
like
rules
and
functions
with
the
context,
so
you
can,
for
example,
say:
rule
bonds
means
delete
the
UDP
destination
port.
L
L
This
compression
usually
takes
place
between
layer
three
and
two
and
three
so
after
the
IP
stack
problem
is
ESP
is
everything
we
can
compress
this
already
encrypted
and
I
mean
you
can
you
can
compress
encrypted
payload?
But
then
you
maybe
don't
want
to
encrypt
it,
so
the
only
thing
we
can
do
and
which
is
actually
kind
of
done
already.
You
can
compress
the
ESP
header,
because
this
is
this-
is
the
information
with
just
in
plain
text
there
nothing
else.
L
The
good
news
was
easy
header
compression.
We
already
have
this
kind
of
channel
to
agree
on
a
state
which
is
or
IQ
to
group
IP.
We
can
do
it
static.
We
even
have
a
static
State,
which
is
our
security
Association,
and
this
state
already
includes
some
information
we
can
use
for
compression.
So
basically
the
traffic
selectors.
If
you
do
them
uniquely,
you
can.
You
have
the
IP
addresses
theory
of
ports
there
and
much
more,
and
actually,
we've
done
this
before
Rock
over
rock
over
IPSec
is
already
there.
L
The
problem
is,
we
need
to
define
how
to
make
use
of
this
context
and
one
thing
which
turned
out
like
the
last
I
think
two
or
three
years,
especially
in
the
six
loop
and
this
lo
pan,
a
community
which
are
developing
this
static
context,
hello
compression
that
rock
is
too
hard.
6Lowpan
is
too
hard.
So
we
need
to
do
something
different
and
the
problem
is
this
required
specification?
L
So
we
need
to
define
what
to
do
with
an
every
single
header
of
the
protocols
we
want
to
compress,
and
this
is
unfortunately
why
this
draft
is
kind
of
long,
but
I
will
try
to
go
quickly
through
what
our
idea
is.
It's
very
close
to
what
the
people
in
the
ship
work
and
the
lp1
working
group
do
and
they
actually
liked
the
idea
quite
a
lot.
L
So
we
kind
of
split
the
ESP
stack
in
four
layers,
so
we
have
a
pre
ESP,
so
basically
been
so
the
input
of
the
ESP
stack
where
you
could
compress
the
IP
UDP
TCP.
Whatever
you
have
in
plain
text
for
the
payload,
then
we
have
clear
text
ESP.
So
once
you
have
to
use
P
packet
build,
then
you
can
compress,
for
example,
the
ESP
trailer
we
have
to
encryption
phase.
L
This
is
not
part
of
this
draft.
This
is,
for
example,
done
by
implicit
IV
that
you
can
just
kind
of
compress
the
information
you
need
for
encryption,
and
you
can
do
something
after
the
ESP
is
properly
processed.
You
can
do
you
can
compress
the
ESP
header
or
which
is
also
not
parked.
For
after
don't
worry,
you
could
do
something
as
the
ICD,
but
it
could
be
that
there
is
some
sort
of
short,
shorter
ICV
calculation
for
IOT
scenarios.
L
So
the
way
we
do
it
and
I
said
it's
very
close
to
what
the
people
in
the
LP
bond
working
group
do.
We
defined
functions
and
the
functions
basically
just
says
what
happens
on
the
compression
side
and
one
dirty
cop
inside
so,
for
example,
scent
value
just
means,
don't
compress
anything
which
is
if
there
are
like
variable
options
in
ipv4
or
TCP
or
whatever
elite.
It
means
there
is
a
context
available
which
allows
you
to
just
delete
this
specific
field.
L
So,
for
example,
I
have
an
IP
address
in
the
traffic
selector
just
deleted
and
decompresses
on
the
receiver.
Then
we
can
do
something
like
for
sequence:
numbers
like
basically
a
reverse
idea
of
extended
sequence.
Number
second
mechanism:
we
can
compute
values
from
lower
layers.
So,
for
example,
you
can
calculate
the
UTP
lengths
from
the
alter,
IP
lengths
and
I'll
checksum
is
easy
and
yeah
padding
is
something
you
can
also
do.
That's
just
the
functions
used
for
compression
and
what
you
then
do.
You
define
the
rule?
What
happens
on
a
specific
field
off
the
header?
L
So
I
go
back
to
the
example
before,
for
example,
the
IP
address,
we
have
a
rule
which
says
compress
ipv6
source
the
field
it
it
affects
the
source
address
of
the
ipv6
header.
The
action
is
needed,
so
it's
removed
and
the
parameters
or
the
value
you
use
is
the
IP
6
address
with
just
to
be
negotiated
during
the
peers
and
we
defined
roles
and
rules
for
all
headers
within
ESP.
We
could
imagine
and
that's
why
this
document
is
so
long.
So
currently
we
use
ESP
ipv6
a
p40
UDP
you.
L
E
L
And
then
we
have
the
context
which
basically
just
says
which
values
are
there
and
that's
also
something
which
has
to
be
defined
in
those
documents
and
how
to
make
use
of
it
again.
For
example,
our
IP
addresses
the
problem
remains.
We
have
so
many
header
fields
which
can
be
part
of
the
ESP
payload
I
calculated
and
like
even
you.
If
you
say
layer,
four
port
is
one
one
field
so
which
can
be
used
for
TCP
UDP
UDP
light.
You
come
up
with
4444
header
fields.
L
L
E
H
Ok,
so
history,
geologists
assume
that
people
sort
of
noticed
we've
labeled,
IPSec
I'll,
skip
that
there's
an
example.
Is
this
the
s
P
silicon
kernel?
You
see
that
there's
additional
labels
to
select
burden
on
the
package
should
be
encrypted
or
not
so
the
original
proposal
vd8
was
we
added
the
traffic's
like
about
a
security
label.
H
Would
those
be
clear
that
you
would
pick
one
of
them,
but
then,
when
we
start
adding
new
traffic
selector
types,
it
becomes
unclear
whether
you
have
to
pick
a
v4
and
v6
one
and
other
ones,
or
rather
or
how
you
would
combine
them.
So
after
some
pressure
of
the
Honourable
chair,
it
was
decided
to
basically
copy
the
existing
traffic.
H
Well,
we
cannot
do
this
solution
because
now
we're
going
to
get
a
combinatorial
explosion
of
all
the
things
that
people
might
want
or
not
want
to
do
so
that
basically
brought
me
to
the
problem
of
like.
Is
this
really
the
way
forward?
I
think?
Actually
it
might
be
better
that
we
clarify
you
must
pick
a
v4
v6
original
traffic
selector
and
of
all
the
other
traffic
selectors
types
that
are
sent,
and
you
must
pick
one
of
them.
E
E
H
I
give
run
graduate,
so
this
got
triggered
by
the
I
to
NSF
working
group.
I
did
some
drafts
on
putting
some
of
the
IPSec
modeling
into
there
in
today
yang
models
and
then
recently
started
seeing
all
these
obsoleted
old
things
that
they
put
in,
because
they're
unfortunately
actually
might
have
heard
me
say
on
the
plenary
and
they're
they're
trying
to
put
inr
registries
snapshots
into
RFC
documents,
which
is
kind
of
terrible,
and
suddenly
I
see
these
options
like
oh
we're
going
to
support
one
des
an
actually.
H
It's
not
even
one
set
that
we've
already
said
not
to
use
it's
like
cast
an
idea,
and
and
and
all
these
sort
of
algorithms
that
we
haven't
deprecated,
because
we
weren't
weaker,
we
didn't
find
any
attack
for
them,
but
we
kind
of
linger
them
in
from
Ike
v1
error
times,
and
so
what
we
really
needed,
apart
from
the
regular
algorithm
cycle,
update
very
very
give
implementation
recommendations.
We
should
do
something
with
all
of
these
collected
may
and
trees
that
we
have
left
and
sort
of
write.
E
H
S
Implement
dan
Harkins
yeah,
this
kind
of
reminds
me
of
HL
Mencken's
comment
about
Puritanism,
where
he
said
that
it's
a
haunting
fear
that
someone
somewhere
might
be
having
fun,
and
this
seems
to
be
like
a
hunting-
fear
that
someone
somewhere
might
be
doing
Icke
v1
and
you
know
not
sure,
really
why
we
care
regarding
using
Ayane
as
a
way
to
kill
off
a
deprecated
protocol.
I,
don't
think
that's
really
the
point
of
Vienna
registries.
I
I
do
agree
that
things
like
tiger
and
caste.
We
might
want
to
deprecated,
but
I.
Think
the.
H
S
H
H
H
S
F
So
for
this
plus
two
points,
first
of
all,
art
supported.
You
need
to
well
duplicate
multiplicate.
Well,
they
died.
I
could
one
already
removed
it
from
our
product
just
last
year,
which
is
not
implemented
what
they
wanted,
and
the
other
point
is:
please
save
H
for
now
it's
probably
uses,
but
it
is
at
least
harmless
and
comparisons
like
your
on,
so
please
keep
aged
for
now.
Just
for
the
reason,
because
it
provides
some
the
probabilities,
nobody
use
it,
but
it
is.
H
R
H
Away
of,
and
not
just
like,
killed
we're
really
talking
about
things
we
forgot
like
cast
like
there
was
no
reason
to
say:
don't
use
casts
insecure,
but
because
it's
not
but
but
then
again
nobody
has
researchers
for
20
years
either.
So
do
we
really
know
that
it's
not
insecure
either?
At
this
point
all
right,
yeah,
thank
you.
So
then
we
have
one
final.
K
So
this
is
a
some
new
work
to
improve
IPSec
traffic
flow
confidentiality,
I
think
probably
a
lot
of
people
who
are
more
familiar
with
this,
but
basically
this
is
why
do
we
want
this
is
to
protect
against
traffic
analysis,
which
is
the
act
of
extracting
information
from
the
size
and
rate
of
data?
That's.
G
K
And
the
point
is
you:
can
you
can
encrypt
your
payload,
but
you
can
still
get
information.
You
know
from
from
the
what
I
just
said,
there's
actually
a
presentation:
they
use
next
2017,
where
they're
picking
they
can
determine
which
movie
you're
watching
they
show
picking
which
movie
you're
watching,
even
though
the
stream
is
encrypted.
That's
one
example.
K
K
This
has
suboptimal
performance
increases
latency
and
it
has
a
very
low
bandwidth.
So
our
proposed
solution
is
fairly
simple:
it's
to
continue
to
use
IPSec
ESP,
but
we
have
a
new.
We
use
a
new
payload
and
inside
the
payload
we
fragment
and
aggregate
the
IP
stream.
This
creates
minimal
latency
and
gives
us
a
constant
high
bandwidth.
So
we
have
a
graph
here
showing
that
these
results,
so
the
top
three
constant
lines
are
those
new
solution.
K
Ip
DFS,
the
numbers
are
the
MTU,
so
that's
a
nine
thousand
fifteen
hundred
and
576,
and
we
also
you
can
see
that
we
have
in
the
middle.
You
have
either
just
pure
Ethernet,
so
that's
not
a
fixed
size
and
ESP
pure
ESP.
That's
also
enough
excite
so
PFC
going
on
there
there's
no
confidentiality
and
then
the
bottom
represents
the
currently
available
option
right.
So
it's
because
it's
very.
K
For
bandwidth
utilization,
let's
see
what
time
do
I
get?
Okay,
so
that's
sort
before
there's
a
sales
slide
since
I
don't
have
I,
have
30
slides
I'm,
never
going
to
present
all
those
so
I'm
gonna
skip
through
some
the
key
design
points.
It's
we
use
a
fixed
size
and
caps
elating
packets.
We
sell
them
at
a
constant
rate.
The
unidirectional
thing
is
more
about.
The
idea
was
that
you
could
do
TFS
in
one
direction.
You
didn't
have
to
do
it
in
both.
We
had
that
as
a
goal
in
the
design.
K
K
K
We
also,
you
know,
aren't
married
to
any
particular
solution
here.
So
we
just
need
to
get
the
drop
reports
back
to
the
sender.
So
this
is
just
a
starting
point
right,
so
the
non
congestion
control
mode
is
obvious,
but
we
we
also
allow
for
sending
the
congestion
information
in
case
you
want
to
implement
something
like
circuit
breakers,
so
we'll
skip
that.
So
the
basic
good
thing.
So
this
is
just
some.
You
know
basic
packet
formats,
you,
our
header,
is
basically
in
more
solid
lines
there.
K
So
in
you
know,
the
ESP
header
followed
by
a
block
offset
and
that
allows
us
to
pack
IP
packets
together.
What
that
looks
like
is
each
data
block.
Looks
we
basically
use
the
first
nibble,
so
you
we're
not
using
any
bites,
actually
specify
the
data
block
header.
We
just
look
into
that.
First,
four
bits,
so
ipv4
it'll
be
four
b6o
v6
and
padding
would
be
zero.
K
So
the
the
congestion
control
info
will
be
sent
on
an
interval,
but
again
I,
don't
really
want
to
talk
about
how
we're
gonna
send
it.
Since
you
know
it's
sort
of
in
flux
right
now
this
this
is
just
the
introduction
of
this
work
right.
We
we
imagine,
discussions
on
the
list
and
coming
to
the
best
sort
of
solution
for
how
to
sunset
formation
I.
Also,
you
know
it
was
brought
up
that
we
could
do
I.
Think
Valerie.
You
said
you
know
why
don't
send
an
end
band
and
I
was
like
well
it's
unidirectional.
K
If
we
can,
in
fact,
you
know
if
we
had
just
pure
IP
ESP
coming
back,
you
know
through
the
the
paired
si
if
we
could
do
a
next
header
to
attach
it
there.
That
might
be
a
solution
to
that.
Somebody
mentioned
to
me
actually
anyway,
so
this
is
stuff.
We
could
do
an
arrest
since
I
don't
have
tons
of
time
the
data
right
now.
This
actually
is
also
in
flux.
K
K
K
So
you
can
see
it's
quite
large
and
if
we
go
to
the
next
one,
it's
this
is
same
numbers
by
percent.
So
you
can
see
that
for
the
TFS
solution,
it's
a
fixed
percent
and
it's
very
small,
obviously
there's
some
outliers
there
for
the
prefer.
The
currently
available
solution-
22,000
percent,
it's
horrible
they're,
not
all
that
bad,
but
they're,
all
pretty
bad.
K
K
You
can
go
a
lot
deeper
into
this
right,
because
if
you
start
looking
at
queues,
you
can
imagine
if
you're,
if
you're
patting
40
byte
TCP
packets
into
1,500,
byte
ESP
right
and
then
you
have
ten
of
those
in
a
queue
right.
That's
a
huge
amount
of
latency
you're
adding
to
that
last
40
byte
packet.
So
we
there's
some
related
work.
That's
going
on
in
the
I
Triple
E.
With
regards
to
this.
They
just
met
recently
and
it
looked
really
promising.
K
There's
gonna
be
there's
progress
on
this,
and
it's
anticipated
in
upcoming
meetings
well
and
I
also
wrote
some
code
that's
available
at
that
link.
Now
this
is
just
proof
of
concept
code.
It
doesn't
actually
it's
not
actually
an
ESP
because
that's
hard
to
sort
of
whip
together
quickly,
so
I
used
UDP.
But
basically
what
this
is
proving
is
the
is
the
framing
the
packing
and
the
the
you
know,
fragmenting
and
aggregating
of
the
payload
packets,
as
well
as
being
able
to
adjust
to
congestion.
K
F
F
K
F
H
Quick
because
we're
over
time,
yeah,
okay,
poets,
so
I
think
that
that
discussin
should
be
doing
two
things.
One
of
them
is
sort
of
providing
privacy
in
the
other.
One
is
sort
of
compressing,
very
small
packets
into
bigger
packets
and
saying
those
are
two
very
different
goals
and
for
the
first
gold
of
privacy
that
the
RFC
you
quote
about
ESP
allows
you
to
not
only
do
padding,
but
also
some
dummy
packets,
so
so
from
a
privacy
point
of
view.
H
The
existing
RFC
already
covers
everything
you
would
want
to
make
a
stream
look
like
you
know,
a
similar
mana,
monotone
stream,
so
I
think
like
then,
maybe
clarify
bit
why
you
want
to
do
these
other
things
that
are
like
additionally
complicated
because
I
think
that's
foot,
but
we
had
a
real
work
in
this
track
for
years.
Sure.
K
U
K
U
My
understanding
is
from
implementations
that
have
actually
tried
to
do
the
existing
RFC.
It
basically
isn't
deployable
that
it
translates
into
what
looks
like
a
variable
lost
link
because
of
the
expansion.
You
know,
if
you
think
about
a
normal
packet
distribution.
Well,
we
used
to
be
bimodal
really
trimodal.
Most
of
the
bandwidth
is
in
big
packets,
but
most
of
the
packets
are
little
small
ones
and
we
end
up
just
destroying
the
available
bandwidth
because
of
the
expansion.
So
well
he's
not
listening,
but
but
you
know
the
existing
RFC,
it
doesn't
work.
