►
From YouTube: IETF104-OPSAWG-20190328-1610
Description
OPSAWG meeting session at IETF104
2019/03/28 1610
https://datatracker.ietf.org/meeting/104/proceedings/
A
B
C
B
B
B
D
You
one
well
actually,
with
minutes,
we
have
the
etherpad
up
there.
You
see
that,
but
what
I
heard
in
that
mod
I
really
liked
or
what
maybe
it
was
net
comp.
These
are
all
recorded
and
watchable
and
I've
had
some
luck
with
transcribing
stuff,
like
Auto
transcription
service
that
you
just
fix,
so
I
find
that
if
there
is
something
that
you
want
to
record
and
make
sure
it
gets
called
out,
go
to
the
ether
pad,
and
please
put
it
in
the
notes
else.
D
What
what
will
do
is
will
transcribe
this
and
will
put
minutes
up
based
on
that,
since
it's
almost
next
to
impossible
these
days
to
find
a
minute
steak
or
anyway,
and
you
end
up
doing
the
same
amount
of
work
I
find
when
doing
when
creating
the
minutes.
But
if
there
is
something
you
want
to
add
to
notes,
please
do
that
yep,
but
you
are
so
can't
no
take-backs.
D
B
B
And
the
working
global
status
since
last
meeting,
we
published
the
two
RFC's
from
this
working
group.
Congratulations
to
the
authors
and
contributors
and
please
keep
contributing
to
this
working
group.
Now
we
have
three
working
group
documents.
Firstly,
that
affects
b2b
community
document.
We
finish
the
work
and
now
is
in
the
RFC
at
HQ.
D
So
TAC
acts
there
was
quite
a
bit
of
dialogue
on
this
while
it
was
in
while
was
on
the
list.
We've
got
it
to
it,
there's
actually
a
13
version.
Now
that
fixes
a
lot
of
serious
idean
its
problems
with
it
I've
completed
a
shepherd
write-up
that
you
can
go
read,
and
all
of
that
is
public
and
I
kicked
it
up
to
the
iesg.
So
I've
been
talking
to
the
author
as
they
fix
some
things
I.
There
may
be
a
few
outstanding
small
comments
from
someone
on
the
list,
but
we'll
get
those
sorted
out.
D
It
went
through
working
last
call.
It
did
pass
that
we
have
people
did
reply,
that
there
were
implementations,
that
his
vendors
who
implement
tac-x
servers
and
clients
replied
that
those
implementations
correspond
to
the
draft.
That
was
all
noted
in
the
Shepherd
right
up,
so
I'd
like
to
see
that
progress
I'm
not
in
under
any
illusion
that
it
will
be
drama-free
from
this
point
on,
but
it
is
progressing
Ignis.
D
E
D
B
F
Good
Andrew
good
afternoon
everyone,
so
we
all
know
that
everybody
is
talking
about
telemetry.
So
our
goal
is
to
transfer
this
password
to
some
really
meaningful
terms
in
90f,
so
we
can
use
there
to
get
the
standard
and
technology
development
work
here
and
also
help
us
to
clarify
many
misunderstandings
and
to
to
really
learn.
What's
a
scope
of
naturally
telemetry
what
it
is
and
what
it
isn't.
F
We
has
already
went
through
seven
major
revisions
for
this.
For
this
draft
and
on
March
Simmons.
We
start
a
formal
request
for
adoption
to
the
OTS
AWG
and
after
two
weeks
in
during
the
two
weeks,
our
period,
the
majority
of
feedback,
are
positive,
and
so
the
working
group
has
concluded
on
March
11,
no
just
this
Monday
and
formally
adopt
this
as
a
working
group
draft.
So
we
haven't
addressed
the
most
recent.
F
Our
suggestion
are
comments
from
the
email
list,
but
before
this
conference
we
already
submit
another
major
revision
of
nurse'
version:
zero
2
in
this
revision.
Basically,
we
clarify
the
definition
of
the
network
telemetry
and
also
we
move
the
technique,
review
and
survey
to
the
appendix,
because
most
of
this
technology
and
the
protocol
coward
are
still
in
the
draft
state
and
the
not
mature
enough.
F
So,
but
we'll
keep
this
survey
to
help
people
understand
was
our
current
state
a
state
of
art,
but
eventually,
if
we
go
to
the
state
of
RFC
publication,
we
are
removed
on
those
drafts
which
a
note
mature
enough
to
be
included
and
used
in
this
new
revision.
We
also
clarify
the
relationship
between
the
network
telemetry
and
the
network
OAM.
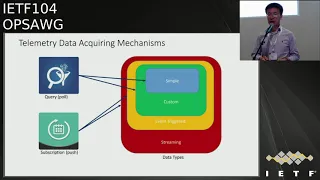
F
We
also
articulate
the
need
to
actually
partition.
The
telemetry
tubes
are
different
in
that
for
planes.
We
are
sure
why
are
in
of
some
later
slides
and
we
add
another
framework
dimension,
which
is
a
data
acquiring
mechanism
to
help
us
to
further
use
another
dimension
to
classify
the
existing
technologies,
and
we
also
add
the
security
regards
discussion
and
some
other
discussions
on
that
for
telemetry
evolution,
so
first,
the
new
dimension
of
to
classify
the
technologies.
F
Basically,
we
have
a
query
and
the
subscription
to
get
telemetry
data.
Our
curry
is
just
another
name
for
the
poor
poor
base.
The
mechanism
and
the
subscription
is
another
name
for
the
push
based
mechanism
and
there
are
basically
four
types:
four
types
of
datas,
the
first
one,
just
simple,
David,
simple
data
which
can
directly
derived
from
the
network
device,
and
the
second
type
is
a
custom
data
which
is
a
more
complex
data
type
which
can
be
aggregated
from
simple
data
or
are
computed
from
simple
data.
So
to
support
custom
data.
F
We
will
need
some
more
complex
mechanism,
such
as
a
programming
and
deploying
the
filters,
and
some
other
other
ways
to
achieve
that,
and
then
the
another
type
event
trigger
data
is
actually
more
capacity
to
type
is
a
build
on
top
of
the
custom
data,
but
is
the
data
only
acquired
through
some
preset
conditions?
The
contagion
condition
can
be
a
very
simple
filter
or
it's
a
very
compressed
must
be
described
with
something
like
a
finite
state
machine
and
lastly,
we
have
this
tree
streaming.
F
F
So
how
we
will
see
in
the
network,
we
actually
have
a
very
different
multi
monitoring
entity
and
objects,
and
we
have
very
different
data
sources
and
the
different
detects
port
location.
Therefore,
we
better
to
petition
the
techniques
or
are
all
the
protocols
in
two
different
planes.
So
in
this
framework
we
partition
it
into
four
different.
F
It
are
planes
the
management,
plane,
control,
plane,
data
plane
and
the
external
data
for
the
management
plane
at
many
deal
with
network
configuration
or
the
operation
status
and
the
data
many
exported
from
the
me
control
board
CPU
for
the
control
plane.
He
do
is
the
PDU,
the
Reeb
deep,
so
the
oldest,
I
relate
to
the
control
protocols
and
data
will
be
exported
from
the
main
control
wars.
If
you
like
her
cpu
or
even
the
directly
from
the
foreign
ship
and
for
the
data
plane,
it
may
do
is
a
user
traffic.
F
So
in
most
cases
the
data
will
be
directly
exported
from
the
Leichhardt
cpu
or
from
the
14
chip,
and
at
last
we
have
the
external
data
can
be
acquired
from
the
terminals
and
the
servers.
There
is
a
social
events
and
the
application
information.
So,
on
the
right
side,
we
list
some
existing
works
for
each
each
plane,
telemetry.
F
With
this
a
petition,
we
have
this
architecture,
so
on
network
size
of
the
west
side,
we
have
a
three
plain
telemetry
and
we
also
have
this
external
data
and
the
UN
telemetry,
all
all
of
them.
Each
each
of
this
has
its
own
interface
to
the
network
operation
operation
applications.
So
the
may.
Our
key
message
for
this
architecture
is
that
we
won't
have
a
one-size-fits-all
solution,
but
on
the
other
hand,
on
the
other
hand,
we
need
to
wire
to
have
a
so
many
different
interfaces.
F
For
each
plane
we
can
further
a
partition,
particularly
partition,
this
the
telemetry
into
five
unique
components,
so
the
first
one
is
on
the
application
side
is
doing
the.
We
call
that
data
analysis
and
storage,
so
each
mini
provides
the
data
requirements
based
on
the
application
and
on
the
other
side,
when
they
de
casa
data,
it
they'll,
do
the
data
sharing
distribution
and
processing
and
in
the
device
side.
F
The
first
component
is
data
subscription
theory
and
the
configuration
it
is
a
about
interface
for
data
requests
and
also
the
data
model
to
define
the
data
and
the
third
component
is
the
data
encode
and
export.
More
true
is
about
the
interface
for
telemetry
data
output,
below
that
is
a
data
generating
and
the
processing
module.
So
it's
too
many
to
the
device
site
data
preparation,
how
to
generate
data
to
satisfy
the
city
request
and
the
finally
is
a
it's
a
data
source,
it's
just
the
raw
data
source,
also
to
identify
where
the
data
can
be
acquired.
F
So
the
next
step
is,
first
of
the
sync
all
the
constructive
reviews
and
the
comments
from
the
working
group
email
list.
So
many
people
have
have
a
give
a
lot
of
useful
suggestions
to
improve
this
distract.
So
in
the
new
revision,
we
will
consider
all
of
them
and
reflect
this
reviews
in
the
next
revision.
We
also
thank
many
network
operators
and
OTS.
F
D
D
Maybe
even
recommendations,
and
maybe
I'm,
just
speaking
as
a
contributor
at
this
point-
recommendations
on
how
I
as
a
consumer
might
make
better
use
of
telemetry
or
how
I
can
up
up
value
the
telemetry
from
just
raw
data,
so
I
would
say
from
a
chair
standpoint.
I
would
love
to
see
other
stos
participating
in
this
and
giving
feedback
as
a
contributor
I'll
have
other
reviews,
but
I
think
it's
really
around.
How
do
we
get
more
value
out
of
telemetry
yeah
yeah.
H
Okay,
I
sing
with
this
suggestion
is
very
good,
in
fact,
is
from
our
own
wheel.
We
now
dare
to
use
a
community
that
we're
the
China
standard,
Association
and
also
channel
that
they
also
had
Japan.
They
had
the
elementary
working
group,
so
we
also
have
this
one.
We
also
you
try
to
join
this
on
a
gratuitous
concert
as
well.
We've
tried
to
collect
the
more
information
and
later
I
would
like
to
share
this
in
community
okay,
so.
D
D
I
J
Ten
minutes
ten
minutes,
so
this
should
hopefully
be
a
bunch
less
than
ten
minutes.
The
clicker
even
works
so
first
off.
This
is
not
really
a
new
idea.
It's
been
an
idea,
that's
been
kicking
around
for
a
long
time
and
it's
mainly
optimized
for
simplicity.
It's
supposed
to
be
simple,
implement
and
simple.
To
use,
it's
not
supposed
to
be
these
sort
of
shiny
was
all
solves.
J
All
problems
thing
it's
supposed
to
be
a
tactical
solution,
also
I'm
using
the
Cisco
auto
install
type
feature
just
in
examples,
largely
because
it's
something
that
everybody
is
already
familiar
with.
Everybody
knows
it.
This
works
with
anything
with
the
config,
but
again
using
the
Cisco
Auto
config
example
throughout
once
again
doesn't
solve
all
you
can
use
cases
just
a
common
one.
So
what
do
I
actually
want?
J
This,
for
I
would
like
to
be
able
to
buy
a
device
and
ship
it
off
to
an
IXP
or
a
pop,
or
something
and
have
somebody
there
just
plug
it
in
connected
to
my
network
and
have
it
boot,
get
its
config
and
stop
working.
What
I
don't
want
to
have
to
do?
I
don't
want
if
you
ship
a
person
there
I
don't
want
to
have
to
ship
a
thumb.
Drive
I,
don't
want
her
to
shut
my
config
to
the
vendor
and
have
them
put
it
on
the
device
and
then
ship
the
device.
J
J
J
The
router
starts
up
it
realizes
it
doesn't
have
a
config,
it
does
a
DHCP
discover
it
gets
an
IP
address.
It
gets
the
name
of
a
the
next
config
file
to
download
next
boot
server
and
it
connects
to
that
and
it
downloads
a
config
file
and,
as
you
can
see,
the
config
file
has
all
of
my
config
stuff
in
it
right.
It's
got
all
of
my
all
of
my
info
I
mentioned
here.
You
know,
I
show
here
using
TFTP.
Obviously
many
people
use
HTTP,
etc,
but
it's
a
general
sort
of
well
known
concept.
J
So,
what's
the
issue
with
this
well,
an
attacker
can
also
come
along
plug
in
get
an
IP
address
via
DHCP
learn
what
config
files
download
grab
the
config
file,
suck
it
down
and
install
it,
and
it
contains
my
SNMP
community
and
my
tech
X
key
and
my
firewall
config
and
all
of
that
sort
of
stuff.
That
makes
the
attacker
happy
and
it
makes
me
sad
so
what's
the
actual
idea
in
this
document,
when
the
vendor
makes
a
device,
they
make
a
key
pair
for
it
or
when
it
first
boots,
it
generates
its
own
key
pair.
J
J
You
know
sip
server,
vendor
example.com,
something
like
that
when
I
know
order,
advice,
I
call
up
my
bin
and
I
say
P
shipped
me,
one
of
these
and
they
say
sure,
give
me
your
money
I,
give
them
my
money
and
they
say
we're
shipping
you
serial
number
one,
two
three
four
or
in
this
example,
four
to
one
seven
I,
take
that
serial
number
and
then
I
go
and
fetch
that
certificate
from
their
web
server.
You
know
this
is
just
a
web
server
somewhere
anyone
can
go
off
and
fetch
that
certificate.
J
It's
got
a
public
key
in
it.
It's
a
certificate.
Anyone
can
grab
it.
What
I
do
is
I
can
encrypt
my
config
file
to
the
key,
that's
in
the
certificate
and
then
I
followed
the
normal,
auto
install
type
stuff,
a
sticker
on
my
TFTP
server,
FTP
server
whatever,
when
the
device
boots
it
does
the
normal
sort
of
standard
boot
system
it
realizes,
it
doesn't
have
a
config
file.
It
goes
off
and
downloads
this
config
file,
when
it
does
that
it
notices
that
the
config
file
is
basically
just
filled
with
garbage
right.
J
It's
a
big
blob
of
encrypted
stuff.
It
has
look
at
says
this
doesn't
look
like
a
config
file
and
so
it
decrypted
with
its
private
key.
Only
this
device
has
its
private
key,
so
only
it
can
decrypt
it
and
then
it
just
carries
on
booting
as
normal.
Here's
the
example
again.
The
only
thing
that's
changed
here
is
the
config.
You
know
as
the
stuff
and
read
the
config
file
is
now
an
encrypted
config
file
when
the
device
downloads
it
it
figures
out.
This
doesn't
look
like
your
config
and
it
decrypt
it
and
boots
it.
J
The
attack
obviously
can
do
the
same
thing.
He
can
go
from
grab
the
config
file.
He
does
not
have
the
private
key
though,
and
so
he
can't
do
anything
useful
with
it
other
than
kind
of
guess
how
big
my
config
file
is,
which
I
don't
really
care
about.
This
makes
me
happy
and
it
makes
the
attacker
sad.
So
some
serves
obvious
questions.
Why
not
do
draft
IETF,
Netcom
zero-touch
honestly
consider
touch
is
better.
However,
it's
a
fairly
heavyweight
process
or
a
heavier
weight
process.
It
needs
devices
rejected.
J
She
understand
net
conf,
it's
gonna
be
a
while
before
that
comes
about.
This
is
a
simple,
easy
tactical
solution
in
the
meantime,
or
at
least
I
think
it
is
why
not
anima
ACP
and
burski
that's
even
more
complex
and
it's
gonna
be
a
long
time
before
that
happens.
It
also
surve
involves
changing
the
paradigm
of
how
I
run
my
network
might
be
cool
long
way
up.
All
of
the
vendors
I'm
sure
saying
just
buy
my
shiny
new
product.
It'll
do
all
this!
For
you,
sorry,
no
I,
don't
want
your
shiny
in
your
product.
J
Another
question
I've
heard
why
not
use
the
arrow
2.1
ar
I
divide
e
for
those
who
don't
know
the
arrow,
2.1
AR
stuff,
it's
a
new
thing
which
allows
the
device
to
authenticate
itself
to
the
network.
It's
really
cool.
If
your
device
has
this
and
you
have
access
to
the
certificate,
you
can
just
use
that
certificate.
I
mean
it's
already
generated
security.
In
many
cases
the
device
can't
actually
access
the
certificate
separate
subject.
Another
question
here
many
times
is
once
I've
used.
J
This
can
I
delete
the
certificate
or
replace
it
with
my
own
I
think
that's
an
implementation
decision
personally.
I
wouldn't
bother
doing
that
that
way,
if
I
ever
sort
of
sell
the
device
to
someone,
they
can
just
reuse
this
to
bootstrap,
but
implementation
choice
whatever
and
then
the
other
obvious
one
is
I.
Don't
actually
put
my
config
file
on
the
TFTP
server
FTP
server
ever
I
put
a
little
proto
config
on
and
then
I
SSH
in
and
update
it
to
the
real
one.
Yay,
that's
a
really
good
idea.
You
should
do
that.
J
You
can
use
this
to
download
the
proto
config
and
now
you
have
two
layers
of
security.
Is
this
actually
simple
I
think
so
here's
a
quick
example
done
in
you
know
using
open
SSL
make
a
config
file
or
grab
a
certificate,
make
the
config
file
and
the
config
file.
It
ends
up
just
release
the
point
to
work
yep.
It
ends
up
over
there.
You
just
stick
that
on
your
TFTP
server,
FTP
server
whatever
and
now
you
can
use
the
order
of
which
stuff
and
questions
cuz,
I'm
sure
we're
running
low
on
time.
J
K
J
K
J
J
J
J
L
J
D
J
Like
people
to
read
it
and
provide
feedback
poker,
oh
yeah,
my
co-author
is
Colin
Doyle
from
juniper.
Okay
he's
not
here,
unfortunately,
I'd
like
people
to
read
it
and
provide
feedback,
and
then,
if
people
think
it's
interesting
and
worthwhile,
possibly
adopted
by
biopsy
WG,
that
would
be
nice,
but
so.
J
You
can
any
way
that
you
could
get
the
config
file
sure
the
issue
with
doing
it
with
getting
it
over
SSL
is
some
people
are
going
to
want
to
do
these
on
their
own
private
network,
and
then
your
device
needs
to
trust
their
certificate,
which
may
or
may
not
be
signed
right,
but
yeah
I
see
no
any
way
that
you
can
get
config
found.
If
you
can
get
it
security
even
better.
I
And
are
you
not
oversimplifying
some
of
the
steps
that
that's
why
they
came
up
with
a
more
complex
solution
and
in
your
diagram,
for
instance,
you
you
fetch
something
from
a
server
but
I.
Think
it's
in
brewskis
cover
that
I
mean
you
can
impersonate
the
server
also,
which
in
York
is
like
maybe
attack
me.
J
Again
so
yeah
I
mean
what
Adam
is
trying
to
do
is
a
much
much
much
much
much
larger
thing
right,
they're
trying
to
build
a
entire
intent
bait
system,
which
requires
a
whole
new
control
plane.
This
I
think
is
simpler
because
it
just
does
a
tiny
small,
narrow
use
case,
and,
yes,
that's
true
an
attacker
who
could
sit
over
there
and
pretend
to
meet
my
TFTP
server
or
wherever
I
fetch
it
from
could
in
fact
serve
me
a
bad
config
file.
J
All
that's
happened
in
as
the
attacker
has
managed
put
his
config
on
my
device
and
right
he's
stolen
my
device.
For
all
intents
and
purposes,
my
particular
use
case
is
mainly
something
like
a
pop
or
an
internet
exchange,
where
my
main
concern
is
smart
hands.
Basically,
stealing
my
config
I'm
shipping,
the
device
to
them.
If
they
want
to
steal
the
router
they
could
put
in
their
trunk
and
drive
off
with
it
so
yeah
a
very
different
use,
case
enema
and
it
confirm
much
larger
solutions.
This
is
just
targeted
tactical
thing.
M
Hello
Cantrell
from
telefónica.
You
know
one
of
the
cases
that
it
was
considered
when
you
were
presenting
this
and
I,
think
that
you
have
hands
are
partially
to
that.
Now
is
that
one
of
the
things
that
the
we
are
facing
is
that,
overall
in
the
outdoor
equipment,
in
some
countries
we
suffer
the
equipment
is
a
stolen.
So
probably
this
mechanism
could
help
somehow
to
also
to
ensure
that
the
kinetics
is
somehow
useful.
My
another
party,
listen
is
not
the
proper
owner
of
these
could
not
work.
M
J
J
A
D
B
O
Hello:
everyone,
my
name-
is
beau
and
I'm
here
to
talk
about
the
TECO's
client
young
data
model,
and
here
is
a
little
background
about
this
dropped.
This
draft
is
initially
defines
a
young
data
model
for
TECO's
client,
TECO's
plus
client
configuration
and
to
allow
centralized
authentication
authorization
and
accounting,
and
in
last
ITF
knee
meeting,
we
received
the
comment
from
the
working
group
that
the
the
original
system-
Triple
A
model,
is
also
need
to
be
extended
to
make
the
device
management
Triple,
A
complete
and
therefore
can
support
a
full
functionality
of
tackles.
O
So
here
is
a
pair
of
updates
since
last
I
kept
meeting
the
first.
Firstly,
we
changed
this
Tycho's
young
structure
to
align
with
radius
client
configuration,
and,
secondly,
we
extend
system
user
authentication
to
make
the
tackles
authentication
method
to
be
enabled
on
a
system
and
the
third
play.
We
add
the
system
user
of
the
addition
and
accounting
method
to
support
additional
device
management,
result
configuration
and
so,
on
the
left
hand
side.
This
is
the
original
IETF
system,
device
management
triple
a
related
configuration
part
and
the
right
hand.
O
O
Triple
A
model
looks
like
after
the
updates,
and
since
we
received
a
comment
from
Ellen
that
hey
thanks
right
now,
the
system
Triple
A
part
Mario,
could
be
tech,
hos,
client,
specific
spaces,
specifics
basic,
so
he
we
we
think,
might
the
system,
Tripoli
extension
could
be,
maybe
like
be
spayed
out
to
be
a
separate
trucked.
So
that's
a
open
issue
for
what
we
like
to
hear
from
the
working
groups.
G
D
I
do
ever
pointed
review
else
into
the
list.
I
thought
it's
good
that
you're
extending
the
system,
just
like
radius,
is
in
there,
but
I
didn't
think
it
was
needed
to
over
overload
this
draft
with
an
a
generic
triple-a
module
I
thought
it
was
good
that
you
were
augmenting
and
fitting
into
where
system
does,
but
it
seemed
kind
of
I
had
to
agree
with
Alan
there.
It
seemed
kind
of
odd
to
also
then
say
we're
going
to
do
more
of
a
broad
triple-a,
because
there
are
things
to
consider.
D
O
D
Who's
read
this
grafter.
This
document
number
of
people,
yeah
number
of
people,
I
honestly
with
the
with
the
Triple
A
in
there
I
I,
don't
think
this
revision
is,
is
ready
for
adoption.
I
would
like
to
see.
If
you
read
this
and
you
you
think
it's
sufficient
to
the
working
group,
you
think
it's
sufficient
to
configure
tax
based
on
how
you
are
using
tax
for
device
administration.
It
would
be
good
to
send
your
comments
to
the
list
to
make
sure
that
it's
covered
correctly
I
think
ultimately
you're
right.
It
does
fit.
D
O
O
Current
sd1
service
attributes
drop
the
specification
and
try
to
make
alignment
this
this
one
and
suggest
us
to
do
the
overlock
or
misalignment
work.
So
we
read
through
the
the
maps
draft
specification,
and
this
figure
is
from
the
max
service.
Oak
Street,
her
reference
architecture
and
since
our
dropped
is
mainly
designed
for
a
managed,
sd1
service
model,
so
we
think
we,
our
draft
and
Neffs
sp1
service
attributes
have
a
lot
of
in
common.
O
That
is
customer
facings
interface.
So
it
will
not
be
used
by
the
like
Estevan
controller,
to
directly
configure
the
underlay
underlying
st-1
devices
such
as
SD
one
edge
or
gateway
in
this
figure,
and
here
is
a
map
that
we
are
doing,
the
matching
between
IETF
as
d1
VPN
service
models
term
and
these
maps
as
divine
service
term
sayings.
O
In
ITF,
we
already
have
the
layer,
2
VPN
service
model
and
layer
3
service
model.
We
would
like
to
follow
the
ITF
service
model
term
terminology.
So
that's
the
reason
we
change
the
the
maps
as
device
service
term
to
the
Ieft
one.
If
someone
have
some
comments
about
this,
we
like
to
hear
from
the
working
group
and
basically
the
sd1
between
service
model
is
quite
similar
right
now
things
we
we
have
the
discussion
this
the
Chou's
before
this
meeting
and
here
is
a
picture
we
borrowed
from
SD
one
service
attributes
from
math
chapter
specification.
O
O
Q
Charles
I
call
and
I
did
read
the
draft
and
we
discussed
the
the
terms
and
I
have
been
active,
are
actually
a
co-chair.
The
activity
group
in
math,
that's
working
on
St,
LAN
and
so
I
think
that
the
timing
is
fantastic
because
the
work
in
math
is
ongoing.
The
work
here
is
is
also
going
on
so
I
think.
There's
there's
really
opportunity
for
us
to
align
this
and
so
I
really
and
very
supportive
of
this
effort.
Q
C
G
O
Q
Yeah,
which
day,
which
one
actually
so
in
math,
we
had
some
I,
think
attempts
at
building
data
model
for
SD
ran
just
kind
of
the
sanity
check.
What
we
were
defining
to
kind
of
see
if
it
was
complete,
but
the
I'd
say
the
consensus
within
meth
is
that
the
right
place
to
define
this
yang
model
would
be
the
ietf
cool.
G
D
About
the
same,
maybe
a
little
more
than
the
tax
draft,
so
it
sounds
to
me,
given
the
Charles
was
the
the
one
who
spoke
up
that
maybe
this
is.
This
is
good.
This
is
proceeding
in
the
right
direction.
I
haven't
seen
a
lot
of
analysts
comments
around
this,
maybe
maybe
I
missed
some
of
them.
I
would
like
to
see
more
before
we
call
for
a
doctrine.
It
sounds
like
there
might
be
some
more
work
to
be
done,
but
but
it
sounds
like.
G
O
Here's
our
thoughts,
because
in
last
night
EF
our
eighty
Ignis
gave
us
the
comment
because
hey
it's
not
that
anak
has
the
sd1
expertise
to
define
the
st1
requirements
because
that's
an
enterprise
community
too,
though
they
have
real
st-1
requirements,
so
they
reach
out
to
the
Steve.
Would
his
his
representing
the
anak
OS
e?
That's
open
service,
open,
sd1
exchange
working
group,
and
actually
they
make
clear
to
me
that
to
us
that
Oneg
is
only
focused
on
enterprise
own
network
and
our
work
is
mailing
about
the
managed
service.
O
Ask
you
a
series,
that's
from
the
that
the
SQL
service
is
provided
by
its
service
provider.
So
that's
the
main
difference
of
these
two
work,
but
they're
and
ona
is
also
don't
want
to
touch
the
single
domain
as
divine
service
configuration
because
he
thinks
that's
a
domain-specific
as
the
one
controllers
work
and
they
just
want
to
focus
on
the
inter
domain
configuration
so
and
the
reason
the
that
service
model
is
proposing
a
t.
G
WG,
Singh's,
Steve
Phil,
that's
a
the
working
group
is
in
I
think
one
or
two
meeting.
O
R
G
O
Actually,
I
I
forgot
this
as
a
opening
show,
because
I
think
it's
a
quite
good
question
and
and
I
also
talked
with
Steve.
There's
mainly
have
some
like.
Even
this
is
like
a
one
domain
or
inter
domain.
Maybe
the
application
based
a
policy
could
be
same
so
in
that
way,
some
part
of
the
the
work
may
be
need
to
be
a
lines
together
and
be
I
think
we
should
also
bring
this
requirements
also
to
the
MAF
to
impact
their
service
modeling
and
to
make
this
inter
domain
single
domains.
Work
be
coordinated,
can
I?
Do
you.
Q
I
think
there
there
has
been
nothing
official
there's
not
like
a
liaison
or
an
agreement.
What
there
was
an
agreement
on
was
you
know,
let's
meet
here
and
try
to
hash
some
of
this
out.
One
of
the
promising
things,
though
I
think,
is
that
MF
spec
is
it's
something
that's
being
done
in
phases
and
the
first
phase
just
doesn't
want
to
get
something
out
there.
You
more
kind
of
agile,
hasn't
even
been
published
yet,
and
we
know
there's
going
to
be
subsequent
phases.
Q
So
it's
not
like
it's
something
that's
locked
down
and
if
you
know
we
decide
something
here
in
the
eye
TF
that
we
wouldn't
have
the
chance
to
reflect
it
there,
because
I
think
both
things
are
moving
in
parallel,
so
I
don't
know
about
making
any
formal
pledge.
I
haven't
seen
how
those
work
in
the
past.
How
many
experience
with
that
but
I
would
say
on
the
part
of
the
people
who
are
involved
in
the
work.
They
both
want
to
see
this
happen
and
want
it
to
be
defined
in
ITF.
E
Agnostic
donnas,
so
one
general
comment.
Yes,
you
describe
the
situation
pretty
well
on
why
this
ended
up
in
different
working
groups
and
why
there's
such
a
split
and
I
think
that
is
probably
the
practical
before.
But,
however,
there's
one
concern
with
this,
you
know
now
we
have
multiple
groups,
multiple
interested
groups,
trying
to
define
a
model
for
something
which
seems
to
be
one
common
area,
and
it's
a
big
question
whether
those
solutions
will
eventually
be
would
use
what
comparable
or
compatible
to
me
there's
no
fundamental
difference
from
a
connectivity
perspective.
E
While
we
are
talking
about
enterprise
or
the
service
provider,
the
line
is
quite
blurred.
Yes,
there
are
different
requirements
for
that,
and
maybe
trying
to
separate
that
so
strictly
is
not
the
right
way
forward.
Don't
have
an
answer
for
that
as
such,
and
all
of
this
is
more
in
the
form
of
experimentation,
so
we
have
at
least
you
have
external
entities
which
bring
in
requirements
from
their
side
and
as
that
technology
domain
expertise,
is
he
an
ITF?
This
is
why
this
work
is
being
done
here.
Q
Yeah,
so
Charles
I
call
one
more
thought
that
may
be
helpful
here.
If
you
look
at
the
the
way
these
two
different
services
are
being
defined,
the
one
in
the
service
provider,
space,
yeah
they're
in
for
an
enterprise
and
the
service
provider.
It's
very
important
that,
while
sure
we
we
know
that,
underneath
there
are
these
underlay
networks,
the
way
the
service
is
being
described.
It's
from
the
point
of
view
of
the
customer
to
the
service
provider.
Q
The
customer
is
not
going
to
do
anything
with
the
underlays
going
doubt
really:
no
insights,
how
the
service
provider
is
utilizing
those.
So
it's
a
it's
a
very
high-level
interface,
where
all
the
customer
sees
is
the
overlay
and
describes
what
they
want
it
to
do.
I'm,
not
that
familiar
with,
what's
being
defined
in
a,
but
if
you
think
about
a
Nona,
it's
the
customer
operating
the
the
entire
service
and
I
think
it'd
be
absolutely
necessary
for
them
to
understand
the
underlays
and
how
to
use
them.
Q
S
S
That's
why
we
are
trying
also
to
standardize
it,
and
we
have
a
place
where
it's
being
used,
this
architecture,
the
zero
one
version
was
presented
in
ITF
103
and
the
zero
two
was
updated
to
reflect.
The
comment
that
we
had
in
me
in
the
previous
ITF
and
zero
three
addressed
comments
from
Adrienne
for
the
major
changes
are
that
expects
about
the
motivation,
use
cases
and
changes
to
the
data
model
to
align
with
l3
sm
and
lay
l2
sm.
S
Next
slides
will
describe
these
changes
so
about
the
service.
What
issue
is,
how
is
the
service
model
use
it,
and
we
see
two
ways
by
which
it
can
it
is
being
used.
One
way
is
the
independent
model,
in
which
case
the
it's:
it's
the
network
orchestration
uses
the
compose
repair
model
and
translate
it
to
segment
VPN
for
each
administrative
domain.
So
it's
so
in
terms
of
the
customer
facing
in
this
case,
if
you
will
use,
you
may
use
a
little
three
same
oil
to
them,
but
the
service
car
orchestration.
S
The
network
illustration
will
build
a
composed
VPN
for
each
model.
The
other.
The
other
way
is
that
to
have
it
to
use
by
the
customer
facing
modern
as
input
to
service
orchestration
layer
that
will
translate
to
the
compose
VPN
model.
It's
the
other
way
around
will
transcribe
the
first
one
is
the
okay.
S
Now
the
major
changes.
Other
registers
is
that
we
emphasize
that
it
is
being
used
as
a
single
service
provider
whose
network
is
divided
to
multiple
administrative
domain.
It
may
be
used
by
multiple
service
provider
based
on
peering
agreement,
but
the
current
usage
that
we
have
is
one
service
provider,
the
first
different
administrative
domain.
He
has
the
metro
network
and
the
core
network
and
there
may
be
different.
Each
one
is
its
own
militant
domain
and
the
requirement
is
for
a
single
service
orchestration.
S
Now,
a
composite
EPM
can
be
classified
into
three
categories
based
on
the
domain-specific
VPN
types.
The
interworking
option
may
be
vary
depending
on
the
inter
domain.
Technology
such
as
IP
or
MPLS
forwarding,
so
the
composite
VPN
can
be
could
be
composed
out
of
one
domain
is
layer,
2
VPN,
a
second
domain
in
the
middle
is
a
layer,
2
VPN
and
another
domain
layer,
3
VPN.
Of
course
there
can
be
multiple
domains
in
the
middle.
S
S
We
updated
the
data
model
to
be
inline
with
the
layer,
3
SM
and
layer,
2
SM,
and
the
security
and
core
support
based
on
the
interworking
option,
and
we
took
it
out,
so
it
would
be
the
similar
to
the
ones
that
we
have
in
l3
SML
to
SM.
So
so
these
are
the
the
major
exchanges
we
had
from
the
the
previous
version
of
the
document.
That
means
questions
comments.
S
D
S
D
I
do
appreciate,
based
on
the
comments
you
receive
last
time,
that
you
updated
to
clarify
the
domain.
The
applicability
I
know
that
was
a
serious
concern
that
this
was
talking
about
multiple
service
providers
in
a
way
that
probably
wouldn't
be
implementable,
but
I
would
like
to
see
what
especially
operators
took
to
weigh
in
to
say
that
this
is
valuable,
because
I
think
seeing
that
interest
would
would
say
that
this
work
is
something
that
the
working
group
perceived
in
general.
D
H
This
from
Holly,
because
these
are
related
with
the
VPN,
so
my
suggestion,
we're
heard
that
you,
the
kind
Senate,
is
the
publisher
to
the
some
days
of
the
best
working
group
or
prop
house
is
the
eunha.
You
know
RT
DWG
for
the
presentation,
his
country,
Gore,
Modi's,
caution,
solicitor,
more
comments:
okay,.
G
D
That's
probably
a
fair
comment:
cross
cross
present
this
in
routing
area
to
BES
I
think
you
were
suggesting,
but
where
there
might
be
more
protocol
specific,
so
not
on
may
be
not
only
necessarily
on
the
operational
side,
but
definitely
more
protocol
specific
to
make
sure
that,
from
a
technical
standpoint,
and
maybe
from
an
even
from
a
need
and
a
standpoint
that
their
voices
get
heard.
Alpha.
B
S
B
S
S
B
T
D
C
D
D
U
Good
afternoon
everybody
I'm
just
a
homo
from
NTT
I,
will
talk
about
networks,
rising
provision
Mahler's,
and
this
is
new
draft
and
it's
first
time
to
present
it.
So
I
will
talk
about
background
and
overview
of
contents
or
what
is
draft
and
notice
that
this
draft
is
independent
one
because
the
docs
Rises
we
related
to
several
layers,
not
about
not
only
operation
but
also
a
deadline.
So
it's
independent
drafts.
U
U
So,
as
you
know,
an
advertising
is
a
hot
topic
or
topic,
and
several
SEO
are
discussing
so,
and
there
are
several
factors:
for
example,
diversity
of
devices
and
services
based
communication
or
Improvement
network
flexibility
provided
by
network
virtualization
technologies
such
as
an
MV
and
Sdn.
Also
a
net
authorizing
is
a
fundamental
concept
of
5g
and
5g
will
be
launched
as
soon
so
in
5g,
ITU
and
Swiss
VP
defined
three
types:
communications
as
features
of
RG
e
mb,
b,
m
MTC,
and
you
are
AC
and
networks
rises,
appears
on
this
context.
U
Zehra
some
problems
on
the
docks
rising,
as
you
know
how
that
was
rising
is
password
and
the
definition
is
ambiguous.
For
example,
a
sunless
neo
said
rising
as
rice
is
just
with
the
end.
Another
said
rice
is
a
bit
and
starts
churning
also
as
a
range,
whereas
rice
provide
service
is
provided,
it's
not
strict
defined
or
some
possibility.
Ppe
is
discussing
how
to
create
as
Rises
on
the
subsequent
work.
U
Also
how
the
use
case
of
slices
is
unclear
and
it's
I
think
it's
a
program.
For
example,
rice
will
be
used
for
enriching
operators,
subs
France
or
it
is
used
for
providing
dedicated
to
which
come
with
lock
service
Rose
comes
at
4
to
10
amps.
So
we
need
to
clarify
these
definitions
and
use
cases
so
in
the
following.
Two
slides
are
either
talked
about
the
scope
of
this
book
and
purpose
of
this
draft,
so
we
would
like
to
and
to
use
rising,
to
provide
sweet
spot
for
each
services.
U
U
So
in
the
few
slides
I
will
introduce
the
overview
or
contents
of
this
draft,
so
we
verified
resource
types.
We
assume
that
journalist
how
those
types
could
be
categorized
into
three
types
so
network.
Our
first
is
network
or
one
resource
expected
sorry
expressed
of
connectivity
such
as
link,
node
or
displaying
protocols.
Secondly,
is
computing
or
GUI
resources
expressed
as
CPU
memory,
storage,
etcetera
and
Subway's
functionality,
resources,
its
includes
value-added
service
functions
or
optional
control
function.
Also
in
the
network's,
rising
post
of
virtual
and
physical
resources
should
be
integrated
and.
U
And
to
end
networks
instance
will
be
created.
Also
an
assign
may
be
a
multi-level
structure,
so
question
patterns-
it's
it
is
one
of
main
contents
of
this
draft,
so
we
assumed
that
there
are
three
types
of
creation
or
chance
for
this
ready-made
pattern
in
in
this
ready-made
in
the
debate,
so
network
authorized
provider
create
catalogs
in
advance
and
cannot
correct
use
well
well,
which
is
close
to
the
the
demand.
Secondly,
is
a
custom
rate.
U
This
model
is
that
network
service
provider,
design
networks,
wise
catalog
own,
depending
on
requirements
from
tenants
and,
sadly
it's
same
custom
model-
and
this
is
a
hybrid
of
ready-made
and
custom-made.
So
an
NS
provider
create
outline
or
catalogs
and
input
tenants
input
several
parameters
depending
on
their
subsidy
payments
provision
modest.
This
is
also
one
of
many
content
or
batise
draft.
So
we
assume
that
there
are
sweet
motels
on
thrice
provision,
so
first,
it's
a
drive
motor
in
this
model
tenant
will
request
the
request
to
create
slice
on
the
requirement
and
sorry.
U
So
in
this
model,
turnout
can
control
networks.
Life
depends
on
obstructed,
information
for
such
as
connectivity
application
and
there
a
second
days
passed
like
motor
in
this
model.
Tenant
control
networks,
rice
as
bunch
of
resources
like
middle
of
this
figure,
and
surveys
is
Right
model.
In
this
model.
Tenants
can
control
infrastructure
resources
directory.
U
We
assume
that
capability
will
be
acquired
by
tenant,
will
borrow
depending
on
these
models.
This
graph
occasion
will
be
useful.
Only
drops
racing,
so
roster
I
will
talk
about
next
steps
on
this
draft,
so
this
is
new
draft.
So
we
have
very
few
comments
and
leave
you,
so
we
will
welcome
you
all
review
for
it.
Let
you
especially,
we
would
like
to
know
opinion
from
particle
customers
also.
U
D
Questions
so
I
have
one
interesting
read:
where
else
have
you
presented,
this
I
mean
I'm,
not
certain
that
I
could
be
wrong.
I'm,
not
certain
that
opt
area.
Working
group.
The
people
in
here
have
just
like
some
of
the
other
models
have
some
of
the
domain
experience
you
need,
especially
since,
where
you're
looking
for
feedback
and
review,
where
else
of
you
or
where
else
are
you
considering
presenting
this
to
get
more
eyes
more
more
people?
Looking
at
this
more
Commons?
G
V
Questions
the
mic,
yeah
Leon
from
China
Mobile,
I'm
glad
that
you
bring
this
back
to
itself
again,
but
I'm,
not
sure
if
you
know
that
all
of
these
has
been
discussed
two
years
ago
in
crack
and
also
more
recently
in
London
I'm,
just
confused
so
confused,
because
you
know,
if
you're
doing
the
information
model
and
there
is
a
draft
under.
Maybe
it's
expired
something,
but
you
can
find
it,
and
so,
in
a
definition
there.
U
B
I
I
may
try
to
to
KFI
nacho
valium
co-author
of
the
draft
I
think
the
notion
of
model
here
is
provisioning
models,
as
Suki
mention,
which
ready-made
slicing
custom-made
slicing
so
twelve,
a
way
for
a
tenant,
a
customer
to
be
able
to
consume
slices
in
a
very
I
mean
packaged
way.
Some
extent.
This
is
the
aspect
of
provisioning
models
and
I
would
like
to
make
just
to
follow
following.
U
O
I
It's
the
first
time
we
present
this
work
in
this
form
we
thought
ups
was
a
potential
group.
Routine
will
be
a
second
target
and
to
come
back,
maybe
to
the
previous
question
and
the
I
think
that
is
my
view
for
for
this
work,
why
we
think,
maybe
in
ops
it
will
be
relevant,
is
there
have
been
several
draft
on
layer
to
service
model
layer,
free
service
models,
also
some
service
automation,
draft
trying
to
combine
different
use
of
young
models
at
different
layers
or
levels.
I
I
think
this
is
a
bit
in
the
same
spirit
trying
to
come
with
a
request
customer
or
they
won't
like
to
consume
a
service
or
slice
package
as
a
service
and
what
will
be
required
in
terms
of
how
you
are
you
bring
the
different
things
together
at
the
different
and
underlying
levels,
so
a
bit
similar
to
l2
l3
service
model,
but
like
a
slice
service
model
to
be
consumed.
This
is
my
partial
view,
partial
understanding,
but
may
be
to
put
some.
U
V
Again
leon
from
china
mobile
just
to
run
remind
you
that
the
previous
bath
was
held
in
ops
area.
I
would
like
this
work
to
be
done
in
IETF,
but
we
have
a
pre
conclusion
that
this
is
not
the
right
work
to
do
here,
but
I
would
it
the
first
person
to
rise
my
hand
here
to
continue
this
work,
but
here's
our
ad.
E
E
The
initially
formulated
problem
of
network
slicing
was
not
a
problem
for
ATF
to
solve.
Itf
has
taken
certain
fragments
of
that,
especially
in
a
data
plane.
Vpn
plus
you
have
some
other
derivatives
of
that
and
that
work
happily
continues
in
the
routing
area.
Now
I
actually
have
read
this
document,
and
my
interpretation
of
that
is
that
your
intentions
are
more
of.
How
do
you
take
the
components
which
are
already
existing
somewhere,
which
you
can
call
what
builds
Network
slicing
out
of
way
out
of
what
network
sizing
is
implemented?
V
Well,
personally,
I
think
there
are
some
work
in
terms
of
cross
room
and
VPN.
We
can
call
it
cross
room
and
VPN
or
slice.
Slicing
is
a
commercialized
word.
You
know,
I
mean
slicing.
Is
it's
slicing,
so
yeah?
If
it
is
I
I
would
like
to
see
more.
You
know
usable
tools
being
developer
models.
Help
here
in
is
therefore
Crossman
VPNs.
That
would
be
very
helpful.
I,
don't
care,
it's
called
network
slicing
or
not.
That's
that's
basically,
for
me
and.
I
D
My
opinion
Jenna
and
my
thing
differently,
given
that
it
seems
like
there
were
very
few
people
who
read
it.
Some
comments
very
few
comments.
I
would
say
very
much
like
the
previous
presentation.
There
is
probably
more
eyes
to
be
looked
at,
maybe
in
routing
and
maybe
after
more
comments,
more
people
look
at
this
there
and
more
to
the
I.
D
B
I
T
Hello
could
have
no
I
Wednesday,
switching
from
Huawei
I'm
here
actually
discuss
a
framework
for
automation,
automated
service
and
management
was
young
actually
in
lunch
host
the
speech.
Actually,
we
already
hear
the
telemetry
discussion
and
there
is
a
more
about
actually
photo
app
approach
here.
What
I,
like
Lucas
can
see
is
top-down.
T
So
what
a
problem
problem
we
really
are
like
a
solved
lab
today.
Today
we
see
large
number
of
young
beta
motor
has
to
be
developed
or
on
the
develop
idea.
For
recently,
we
see
many
of
them
get
published
made
sure
enough.
So
how
can
we
piece
these
model
together?
Put
the
model
together
together
to
complete
the
device
cradle
service?
It's
not
a
clear
to
everybody.
T
Certainly,
when
operate
her
began
to
deploy
some
of
the
model,
the
big
challenges
faced
by
the
operator
is:
how
do
we
select
the
idea
of
define
a
model
to
fit
their
use?
Cases
currently,
I
define
a
model
actually
distributing
different
protocol.
Working
GUI
is
hard
to
take
chatter,
with
the
maturity
of
the
I.t
I.t
final
model.
So
this
is
some
issue.
We
really
want
to
attack
her,
and
so
here
we,
the
goal.
This
work
is
to
define
a
framework
to
tell
the
developer,
implementer
and
operator
how
to
implement
the
ITF,
define
the
models.
T
Give
some
guidance,
provide
some
reference
framework
for
identifying
motorists
and
to
to
to
instruct
how
how
to
to
use
idea
different
model.
If
we
have
time
we
want
to,
actually
it
will
want
to
use
Kaiser
to
explain
how
do
you
leverage
the
company
with
defining
a
firm
Walker,
automated
Network
and
automated
a
service
management
and.
T
Actually,
before
we
get
to
the
start
of
the
idea
to
find
a
model,
we
want
to
introduce
two
concept.
The
first
is
paid
model
layering
and
secondary
state
model
representation
data
modern
living.
Actually
we
can,
you
know
abstracting
network
infrastructure
from
the
bottom.
Also
we
can
abstract
the
business
needs
or
service
economy
from
the
top.
So
we
can,
you
know,
submit
the
young
data
model
into
service
model
and
animal
motto.
T
Service
model
will
focus
on
the
you
know,
define
what
a
service
is,
what
a
customer
needs
is
and
for
Neto
an
animal
model
Lincoln,
you
know,
can
be
used
to
get
a
net
was
set
up
a
program,
the
network
to
realize
their
service.
So,
but
here
in
this
work
that
we
really
actually
induce
another
layer,
we
call
the
natural
resource
model.
T
Typical
example
is
network
topology
model
tunnel
model
and,
to
make
a
lot
of
analogy
to
to
explain
that
the
data
model
representation,
we
make
a
analogy
to
the
house
building
process
actually
for
the
customer,
the
out
of
the
house.
Actually,
they
may
order
a
house
with
Sweden
when
living
room
1001
pitching.
T
Actually
they
may
want
to
have
a
living
room
with
three
window,
and
all
of
these
problems
can
be
reflected
into
the
house
building
blueprints
this
house
building
blueprint
as
you
can
be
compared
to
the
service
model,
so
the
service
model
can
be
used
by
the
customer
to
communicate
that
their
requirements,
the
artisans
needs
and
when
the
customer,
actually
you
know
the
the
the
proofing
that
get
approved
by
the
customer
or
authority,
as
it
has
already
the
can
put
into
the
production
they
can
actually
clear
the
side.
We
can
step
sure
the
trench.
T
If,
for
the
water
supply
that
supply
and
this
water
supply,
electricity
block
can
be
compared
these
in
Africa
resource
model.
So
we
think
that
is
the
Nano
resource
model
is
very
crucial,
because
really,
you
can
schedule
results
to
meet
the
customer
needs.
In
addition,
you
can
schedule
results
to
you,
know,
attitudes
and
network
changes
for
the
house.
Building
you
can
nail
the
foundation,
you
can
build
a
different
room
in
a
house.
All
of
these
building
block
can
be
compared
to
the
device
model.
T
So
actually
one
opposition
we
we
have
here
is
we
sync
idea
to
find
many
policy
related
model
like
a
CEO
like
a
routing
policy,
but
the
for
some
generic
reports
or
some
other
policy.
It
seems
to
make
very
slow
progress,
but
we
think
of
the
policy
model
is
very
crucial
because
they
conclude
even
a
model
together,
whether
it
is
a
service
layer
or
an
animal
layer
or
device
layer,
they
can
really
automate
a
networker.
T
So
here
is
the
status
update
of
the
IDF
network
of
young
work
actually
stands
for
the
design
team
set
up
by
the
different
protocol,
working
GU,
young
doctor
team
and
young
calab
team
and
young
coordination
team,
and
we
already
make
a
good
progress
right
now.
We
have
referenced
Atticus
and
may
be
subject
to
change.
Here
we
have
more
than
50
of
so
you
gotta
publish
that
we
have
more
than
80
working
with
young
working
in
progress.
We
still
have
another,
maybe
80
individually.
T
Actually,
that
need
to
be
proceeded,
and
we
also
see
actually
for
managing
name
protocol
like
a
non
congress.
Comp
young
push
and
MDA
recently
also
make
a
very
good
progress.
So
this
is
actually
benefited
from
open
sources
of
community
like
open
configure.
They
have
lot
of
imported
their
innovation,
actually
really
inspired
here
for
to
try
to
stand
as
this
kind
of
worker.
So
we
think
that
this
should
be
signatures
and
should
continue
to
do
also.
T
We
CIT
r
had
already
have
some
good
crab
fishing
with
as
sto
like
a
3
D
BT
PBF
HIV,
and
we
have
many
different
layer
models.
Maybe
they're
still,
you
know
some
problem
with
in
Sao
Paulo.
We
think
we
should
encourage
a
more
coordination
between
the
spo2
and
I
wish.
Well,
I'm
saying
we
build
a
difference.
I
know
that
that
will
make
us
miss.
T
So
this
is
a
WI
TF
define
a
model.
We
have
service
layer
model,
we
have
network,
never
a
model,
we
call
the
nettle
resource
model.
This
actually
is
a
common
building
block.
You
can
phenomenal
risk
topology
model
or
tunnel
model
you.
Actually
you
can
leverage
you
IDF
defined
mechanism
like
a
scheme,
among
actually
compose
this
model
to
help
you
automate
a
network
management,
so
it's
very
crucial
for
device
in
their
model.
It
actually
have
fully
coverages
different
technology.
T
Like
a
transport
technology,
routing
technology,
om
technology
performance,
amendment
technology,
so
here
we
also
have
some
observation
actually
to
you
know,
deliver
some
surveys.
Actually
you
really
need
to
extend
eyes
like
a
P,
GB
model,
VPN
model
and
the
Libby
model
I
mean
here
trace
in
that
element,
the
peer
model,
but
we
we
sink
sink
actually
for
some
reason,
process,
issue
or
human
resource
issue.
T
Actually
they
make
a
very
slow
progress
so
that
actually
make
a
no
cat
risk
and
you
know
to
to
really
how
do
you
know
for
up
literally
builds
our
project
based
on
use
cases
actually,
for
some
more
model
is
not
ready.
Actually,
that's
a
big
issue,
so
we
will
call
them
to
the
IETF
people.
Our
model
could
be
the
use
case
driven
and
we
can
keep
track
of
this
idea.
Define
a
model,
maturity
actually
I.
Think
a
young
Carlo
is
a
good
talk
good
to
us
actually
right
now.
T
We
here
also
make
a
very
cool
progress.
Young
hello
has
all
be
migrated
to
the
ITA
repository
for
maintenance,
so
this
could
be
very
powerful
tour,
but
I
think
is
that
it's
not
enough
here.
Actually,
I
wanna,
you
know,
compare
the
difference
between
the
traditional
subsidiary
and
multi
trillion
service
delivery
for
the
traditional
service
delivery.
You
know
the
big
problem
is:
actually
you
the
OSS.
Yes,
you
know
they
control
the
surface,
diminishing
with
how
the
service
is
realized.
Is
that
actually
cause?
T
T
Also,
you
know
for
some
protocol
operation.
The
create
delayed
out,
modify
this
process,
we're
repeating
in
many,
whereas
different
process
so
torturous.
We
can
introduce
a
motor-driven
approach
actually
to
urgency.
We
can
define
a
standard
interface
than
the
model.
We
can
use
the
service
model
to
describe
the
service
requirements.
So
so
so
my
idea
for
the
model
driven
approach,
you
really
need
to
decouple
the
service
technician
from
the
house
of
its
is
realized,
so
the
management
system
can
be
really
into
two
system.
One
is
recall
the
activation
provision
system.
The
second
is
service
enforcement
system.
T
Now
will
you
know,
allow
you
to
do
the
most
obvious
innovation,
you
introduce
a
new
service,
but
the
the
service
enforcement's
system
doesn't
need
to
be
change.
It.
Doesn't
it
be
Apple
crater?
You
just
need
to
actually
upgrade
the
service
activation
provision
system.
So
that's
where,
however,
to
try
more
service
innovation
to
to
support
service
agility.
T
So
what
is
the
management
automation,
so
we
can
actually
introduce
a
two
layer
management
automation.
We
have
service
layer
management,
automation.
Actually,
we
can
use
my
guy
l3
VPN
service
model.
We
call
the
top-down
superior
model
to
describe
the
customer
needs
several
comments
to
cut
and
then
we'll
set
up.
But
this
is
not
enough.
In
some
cases,
you
also
need
to.
You
know,
provide
a
service
assurance
service
monitoring.
So
what
do
you
can
do
actually
to
leverage
a
young
push
notification?
T
The
telemetry
mechanism
to
actually
you
know
reporter
the
network
performance
information
to
the
customer
operator.
So
one
way
you
you
should
do
actually
to
buy
another
service
with
a
network
topology
or
tunnel,
and
you
can
report
a
ton
of
performance
or
network
topology,
partner,
performance
or
team
performance
to
the
customer
or
to
the
operator.
We
can
manipulate
these
kind
of
performance
better.
They
can
reorganize
the
network,
so
you
really
can
build
a
closed-loop
service
and
management
so
for
the
network,
management
is
very
similar.
Actually
you
can
also
leverage
is
a
yum
pushing
notification.
T
You
can
subscribe
the
data.
You
are
interesting
and
allow
the
device
this
through
the
data
in
real-time
or
continuously
actually,
and
also
we
really
want
to
have
the
like
an
policy
engine.
They
can
use
like
a
meadow
policy
model.
Actually
they
can
glue
the
telemetry
data
with
the
provision
data.
So
you
also
computers
a
closed
loop
management
automation.
T
So
so
we
have
the
service
management
automation.
We
also
have
nanomedicine
automation,
so
we
really
need
to
hook
them
together.
So
how
do
you
hook
them
in
together?
We
can
introduce
his
service
mapping
in
RPE
service
scenario.
Actually,
we
can
map
as
a
service
requirement
to
define
the
VPN
into
the
BGP
converging
parameter.
M
POS
parameter
that
can
enable
the
that
can
configure
P,
enable
the
big
ETA
say
or
queues,
and
also
we
have
some
other
scenario.
We
have
T's
and
Eric.
T
T
So,
okay,
so
hey
take
away
here.
Actually
I
think
the
kernel
problem
is
not
here,
for
you
know,
process
so
for
summer
model,
you
know
we
really,
you
know
we
need
him,
compete
more
attention
to
some
of
the
model
like
a
PCB
model
or
policy
reading
model.
Q7
Amada
I
think
it's
crucial
to
help
to
deliver
that
we
can
return
surveys
so
the
second,
naturally,
we
think
of
the
kernel
idea,
define
model
is
not
a
you
know,
is
a
distributing
given
protocol
working
with
hard
to
keep
track
of
their
maturity.
T
So
we
really
want
to
leverage
some
of
the
tools
like
a
young
catalog.
Also,
it
would
be
great
actually
to
get
Orbiter
together,
establish
the
operator
community
or
design
team
to
really
have
achievement
to
help
to
review
this
idea.
De
pano
model
identifies
some
packs
or
an
implementation
issue
feedback
to
the
ITF.
That
will
be
really
have
idea
for
to
make
this
a
younger
model
you
more
useful.
So
what
we
will
add
92
is
should
be
the
young
idea
for
young
mothers
generation
should
be
the
use
case
driven
or
projective.
T
Even
we
can,
you
know,
provide
prioritize.
Some
of
these
model
that
I
can
fit
is
a
customer
needs,
and
you
know
teaching
we
think
in
this
walk
up
to
we
define
a
framework,
we
call
the
table
town,
so
the
service
delivery
that
can
be.
You
know,
leverages
that
the
model
define
the
ITF.
Actually,
we
can
provide
a
reference
framework
for
operator
for
developer
implementer
and
to
see
how
to
implement
idea,
define
a
model.
So
last
we
want
to
cover
operator
to
helper,
deploy
this
model
implement
this
model,
and
that's
that's
what
I
wanna
hear.
H
Convene
from
hobby,
in
fact
the
ISIL
remember
I,
forget
about
the
two
or
three
years
ago.
I
Eunice
talked
about
this
with
the
progress
of
this
of
the
yamato
unite.
Have
so
that
time
I
propose
several
days
the
proposal.
I
think
this
was
a
presentation.
To
some
extent
a
usual
aya
is
aligned
with
this
proposal.
I
wonder
the
know
some
days
I
wanna
know
some
answers
about
certain
question.
The
first
one
I
wonder
mainly
suited
for
the
young
model
used
to
do
you
can
list
or
not.
T
Now
young
lady
turned
him
in
voting.
Era
has
already
closed
down
and
young
coronation
having
already
closed
down
and
about
for
some
Yamada
I
think
they
actually
go
back
to
the
normal
process.
They
already
have
many
needs
in
different
protocol
working
goal.
So
really
we
hold
each
on
these
work
with
just
the
you
know,
uses
and
the
many
seen
different
a
protocol
work
working
go
to
each
of
this,
and
we
don't
have
dedicated
young
many
young
design,
team
or
young
men
in
a
system
right
now.
Okay,.
H
From
my
point
of
view,
icing
icing,
the
coordination
worker
use.
Do
you
use
necessary,
because
here
we
try
to
use
of
cases
that
who
indicate
what
in
your
model
should
be?
What
are
the
sauce
on?
Your
model
should
be
necessary
to
be
to
be
defined
as
early
as
possible.
So,
but
this
is
the
Yamato
for
specific
surface
may
be
distributed
in
the
different
working
group.
So
I
suggest
your
possible.
We
can
initiate.
Has
some
this.
The
coordination,
meaning
is
the
Archaea,
try
to
utilize
the
UTA
Ahava
to
coordinate
this
with
a
walk?
That's
my
suggestion.
H
T
H
I
think
that's
the
is
a
very
useful
and,
and
also
that's
I,
wonder
that,
because
I
noted
review
this,
the
draft
because
of
here
I
show
some
of
the
picture
about
this
is
earlier
Sasori
model
and
also
you
have
some
the
future
so
show
the
show
so
at
least
offer
this
as
a
model
for
specific
and
surveys.
I
know
sure
I
thought
you
hated.
H
D
D
D
W
Hi
everyone-
this
is
único
from
Hawaii,
so
today,
I'm
going
to
discuss
that
draft
that
identifies
the
use
cases
for
control
plan
telemetry.
So
here
I
will
use
term
network
wide
protocol
monitoring
to
refer
to
the
control
plan:
geometry,
okay,
so
similar
control
parameters
similar
to
management
plan
and
data
plan.
What
it
does
is
it
monitors
and
analyze
data
that
collects
from
different
plans,
but
there
are
also
differences
and
the
major
difference
relies
on
specific
use
cases
and
for
the
control
plan.
W
There
are
basically
two
type
of
applications
or
use
cases
that
we
think
are
useful.
First
one
is
that
work
travel.
So
here's
a
a
statistic
figure
that
shows
a
very
large
percent
of
the
network.
Issues
are
caused
by
product
failures,
so
having
at
the
protocol,
monitoring
and
analysis
will
be
benefit
for
the
work
troubleshooting
and
the
second
category
is
network
planning.
W
So,
for
example,
you
want
to
optimize
a
rope
pass
or
you
want
to
set
up
a
new
tunnel
and
then
with
some
detailed
route
information
you
can
have
better,
centralized
or
distributed
calculations
and
then
also,
if
also
oh,
there's,
a
very
hot
I,
think
very
hot
concern
or
topic
that
rise
from
operators
and
also
ot
T's.
They
are
concerned
about
policy
validation,
and
so
it's
just
not
a
simply
monitoring
of
the
route
policy.
W
The
separation
of
group
policy
processing
from
the
route
attributes
does
not
solve
the
validation
problem,
so
we
need
more
information
and
and
analysis
to
do
a
church
achieve
that
and
finally,
for
some
long-term
or
short-term
network
design,
optimization
there
requires
or
the
requires,
the
what-if
simulation
works
so
to
the
best
of
my
knowledge.
Currently,
most
simulation
works
are
based
on
the
profile
or
the
configuration
profiles
collected
from
devices.
W
Some
some
applications
requires
data
just
from
like
single
devices,
but
some
others
require
narrow,
wide
monitoring
and
then
once
we
have
the
data
we'll
discuss
the
data
modelling
encapsulation
Theory,
Theory,
whatever
and
also
our
subscription.
Ok,
so
here
are
the
the
data.
Processing
efficiency
will
be
considered,
and
then
that
comes
to
data
transportation.
W
W
Finally
comes
to
the
data
analysis,
this
is
most
connected
to
the
use
cases
so
well
for
different
applications.
The
the
requirement
of
data
synchronization
and
the
data
path.
Efficiency
are
different,
so
well
as
a
whole
picture.
These
problems
are
discussed
in
this
drafts,
and
so
next,
let's
look
at
to.
W
So
at
this
time
you
will
need
to
do
the
comparison
between
the
local
else,
DB
and
also
the
receive
doors
and
I
think
them
received
an
an
unsent
errors
piece
to
localize,
where
exactly
the
issue
lies
and
and
and
and
then
do
further
analysis.
Okay.
So
the
second
use
case
here
is
the
ro
policy
validation.
W
So,
whatever
we
can
have
a
high-performance
control
plan,
snapshot
that
recovers
the
ongoing
network,
then
the
simulation
results
will
be
more
accurate
and
effective.
Okay,
so
more
use
cases
can
be
fine
in
the
draft,
and
here
are
two
general
requirements
that
we
are
summarized
from.
The
use
cases
we
listed
the
first
one
is
that
we
need
to
have
a
tunnel
this
tunnel
is,
should
be
able
to
guarantee
the
performance
of
data
generation
from
generation
to
two
to
exploitation,
two
to
be
able
to
meet
different
applications,
and
the
second
thing
is
the
data.
W
The
data
types
should
be
sufficient
to
meet
various
applications.
Okay,
so
well,
and
this
is
of
course,
informational
draft
and
what
we
want
to
do
as
a
first
step
is
to
identify
the
use
cases
that
operators
so
disease.
They
truly
concern
about,
and
so
please
provide
your
comments
if
these
use
cases
are
useful
or
not,
and
if
you
have
other
more
valuable
use
cases,
please
give
us
feedbacks
and,
and
then
once
we
have
refined
the
use
cases,
we
can
work
hard
at
analysis
and
and
and
and
another
set
our
disease.
D
You
you
know
any
comments,
please,
since
we're
running
I'd,
really
appreciate
you
finishing
in
exactly
ten
minutes.
That
was
great
any
comments
list
I
do
have
a
review
that
I
will
I'll
send
out
the
list.
I
really
appreciate
the
presentation.
Thank
you,
Shawn
can
you
take
us
home
and
this
again
is
I
hate,
I'm,
sorry,
Warren
and
Ignis
to
kind
of
do
this,
but
this
is
ops
area.
Starting
now
we
have
our
ABS
against
McDonough's,
Warren,
Kumari
and
I'm
going
fullscreen
and
giving
Shawn
control.
X
Hi,
my
name
hi
testing,
Justin
heated,
alright
and
my
name
is
Shawn
Turner.
This
presentation
is
not
like
the
others.
The
high
level
bits
here
ours.
This
is
a
myth
and
I'm,
not
gonna.
Ask
for
working
group
adoption,
I'm
gonna
sitting
here,
looking
at
Ben,
why
he
was
my
co
et
at
the
time.
Yahng
yahng
yahng,
nip
okay,
and
thank
you
very
much.
Thank
you
very
much
for
allowing
me
to
stay
and
talk
here.
Cuz
I
sent
this
presentation
at
like
noon
and
thank
you
for
staying
late.
X
I'll
go
quick
because
between
you
and
dinner,
why
am
I
here
so
the
first
time
I
ever
came,
I
talked
about
this
I
think
was
actually
in
Prague
the
last
time
and
so
I
remember
walking
up
to
Warren
and
some
others
insane.
So
I
got
this
min
and
they
all
said.
Well,
you
gotta
go
gang
and
I'm
like
okay.
Well,
we'll
see
how
that
goes,
but
it's
still
a
man,
it's
not
yang,
which
is
why
I
think
wouldn't
really
fly
here
in
the
ITF.
It's
gonna
be
informational.
X
The
reason
why
it
says
standard
shotgun
in
the
tools
thing
and
on
the
github
repo
is
cuz.
That's
the
one
I
you,
the
format,
template
I'll
use,
so
I'm
gonna
change
it.
The
oeid
that
I'm
gonna
end
up
using
in
the
mill
actually
aren't
the
SMI
oils,
which
of
the
oils
that
are
used
at
a
guy.
You
know
the
ietf
arc,
I'm
gonna
use
some
mids
from
some
oils
from
some
other
crazy
thing
and
it's
for
cryptographic
modules.
X
So
it's
got
all
kinds
of
things
in
there
that,
like
don't,
really
apply
the
ietf,
so
we
do
have
some
asymmetric
key
and
symmetric
key
stuff.
That's
pretty
common
to
use
and
some
just
anchor
stuff,
but
the
trust
anchor
protocol,
that's
defined
that
this
thing
is
getting
Kim,
can
manage
and
really
used
anywhere.
There's
firmware
stuff.
X
There
is
firmware,
but
it's
based
on
RFC
4108,
which
probably
really
isn't
gonna,
get
used
and
there's
all
kinds
of
things
like
security
policies,
which
you
know,
classification
levels
and
things
which
really
pretty
much
aren't
used
anywhere
else
in
the
IETF.
Generally
again
did
I
mention
it's
not
yang.
It's
also
got
some
pretty
modern
concepts.
We're
in
the
ops
area,
one
of
the
things
is
2-0
eyes.
You
have
a
box,
you
don't
want
somebody
to
have
it
because
you
maybe
think
you've
lost
control.
So
what
do
you
do
you
brick
it?
X
So
they
can't
walk
off
with
it.
It
does
nothing.
It's
a
great
concept,
doesn't
really
fly
with
ops,
security
policies
or
classifications
security
world.
They
have
tried
and
tried.
They
got
it
in
the
IP
protocol
and
nobody,
not
many
people,
use
it
and
getting
it
to
be
used
anywhere
else
and
messaging,
and
that
kind
of
stuff
doesn't
really
fly.
It's
got
some
specialized
stuff
for
like
compromised
keyless,
because
you
know
CR
else,
they're,
just
too
large
I
would
just
list
the
keys.
X
Now
in
Kent,
Kent
Watson
has
a
giraffe,
it's
a
net
comp
which
is
for
like
like
certs
right
and
that's
great,
but
you
know
why
stop
there
there's
hundreds
of
knobs.
You
can
turn
on
a
certificate
path.
So,
let's
list
them
all.
Oh
yeah
did
I
mention.
This
move
is
123
pages,
there's
six
or
seven
different
modules.
X
There's
this
pal
thing,
which
you
know
it's
kind
of
new
from
this
est
extension
things
I
mentioned
firmware:
it's
RFC
4108,
the
nobody
really
uses
the
stress
tanker
management
protocol,
which
is
about
done
in
the
security
world
and
pretty
much
not
a
lot
of
people
implement
and
I
can
actually
go
on.
So
what
am
I
hoping
for?
Well
since
warns
up
here?
X
So
what
I
want
to
go
to
the
ISC
I'm
gonna
be
full.
You
know
open
kimono,
truth
in
advertising
that,
like
this
is
an
internet
internet
draft,
it's
gonna
be
informational.
It's
gonna
go
through
the
ISEE
they'll.
Probably
make
me
put
some
other
kind
of
disclaimers
on
the
front
of
it
than
the
whole
nine
yards
I
will
talk
to
Kent
and
make
sure
I'm
not
ruffling
his
feathers,
because
I
already
did
and
so
I'm,
basically
hoping
for
no
one
to
get
to
the
microphone
and
say
I
absolutely
want
this
working
group
to
adopt
this
draft.
J
X
I
wish
it
worked
on
it
here:
yeah
cuz,
if
you've
never
gone
to
the
ISC
one
of
the
questions
he
asked
this
so
who?
Where
do
you
talk
about
this?
And
so
you
tell
him
and
if
you
say
no,
where
and
he's
concerned,
there's
gonna
be
an
end
run
because
there's
this
thing
called
an
RFC
57:42
review,
which
the
area
directors
will
do.
Maybe
him
maybe
the
security
guys
which
I'll
talk
to
too
I.
Guess
that's
the
other
part
I
should
add.
X
You
know,
there's
MIBs
and
there's
yang
modules
and
I
know
you
guys
have
tried
to
get
them
to
write
you
a
modules
and
mid
modules
for
security
protocols
forever
and
you
get
ignored.
I'd
get
ignored
too,
because
they've
been
laughing.
They
had
been
laughing
at
me
for
two
years
over,
so
my
hope
basically
is
to
just
quietly
move
into
the
night,
and
that's
really
it
right.
Nobody
is
objecting.
So
please
take
this
work
elsewhere.
J
You
I'll,
let
you
drive,
so
this
is
largely
oh
yeah.
We
gave
the
observer
gave
a
bunch
of
our
time.
Click
on
the
button.
There
we
go
so
yeah.
The
ops
area
basically
gave
most
of
our
time
to
ops
AWG,
because
we
didn't
have
much
that
we
thought
needed
to
be
on
the
agenda.
So
this
is
going
to
be
the
very
very,
very,
very
short,
ops,
AWG
part,
mainly
open
mics,
that
people
can
come
along
and
shout
at
us
if
you
would
like
to
we're
perfectly
fine.
J
E
And
we
actually
have
two
topics
on
the
agenda.
One
is
some
news
from
external
area
on
registration
procedures
for
interface
types
and
then
the
open
mic,
so
interior
have
asked
us
to
simply
share
some
information
with
the
community
on
one
of
the
documents
which
is
being
progressed
there.
It
will
be
a
responsive
document,
but
it
is
being
worked
on
and
discussed
in
the
interior.
It's
about
the
procedure
of
unprocess
how
to
request
the
interface
type
if
you're
working
on
new
fancy
tunneling
mechanism,
which
you
think
it
deserves
a
new
name
for
the
tunnel
interface.
E
This
is
where
you
need
to
look
at
and
the
overall.
Why
why
this
has
surfaced?
There
was
no
such
process
before
young
days
and
now
interior
claims
that
the
large
portion
of
requests
for
interface
types
comes
from
op
Syria.
Therefore,
they
would
like
to
educate
us
a
little
bit
on
what
the
process
will
look
like
the
process
overall
is
very
simple.
This
is
a
registry
if
you
want
to
name
your
interface
and
the
name
already
appears
in
the
registry.
Well,
you're
out
of
luck.
If
the
name
is
not
taken,
there's
pros
procedure
to
be
followed.
