►
From YouTube: IETF104-I2NSF-20190326-1350
Description
I2NSF meeting session at IETF104
2019/03/26 1350
https://datatracker.ietf.org/meeting/104/proceedings/
B
A
Good
afternoon
is
150
now
and
we
can
get
started,
so
this
is
interface
to
network
security
function.
Just
to
brief.
What
is
this
group
is
for
I.
Think
the
lots
of
people
are
here
before
that
I
saw
some
new
faces
is
really
be
able
to
provide
dynamic
policies
to
network
security
functions,
especially
the
virtualized
functions,
so
that
service
providers
can
do
workload.
Bonded
security
policies,
depending
on
where
you
instantiate
the
network
security
functions.
A
So
here's
some
trivia,
the
Charter,
that's
being
posted
mailing
lists.
So
let's
go
to
the
O,
the
note-taker.
We
need
people
to
help
with
the
etherpad.
Thank
you,
your
name.
We
Penn.
Thank
you.
We
Penn
and
everybody
else.
When
you
ask
questions,
please
go
to
the
etherpad.
To
put
your
questions.
Your
name
affiliation
down
so
that
make
it
easier
for
other
people
to
see
your
questions
and
if
you
see
other
people's
note-taking
incorrect,
please
correct
them.
It's
pretty
simple
and
easy.
Everybody
contribute.
A
Milestone:
okay,
so
we
completed
I've
seized
already
the
terminology,
sorry
framework
and
problem
statement
we
have.
One
document
is
on
the
IES
G's
desk.
Waiting
to
be
reviewed
has
been
there
for
three
months,
and
now
we
have
a
new
ad.
So
hopefully
we
can
goes
through
faster,
there's
the
applicability
and
there's
we
have
a
new
uni
adopted
working
group
draft.
So
together
we
have
those
working
group
drafts,
one
is
on
the
IPSec
flow
policies
and
ones
on
the
capability.
That
document
seems
pretty
stable.
A
Now
and
hopefully,
after
this
meeting,
we
can
call
for
working
group
last
call
and
then
remaining
are
the
data
models
for
different
of
the
interfaces.
One
is
for
the
interface
to
the
security
function.
One
is
the
interface
facing
the
client
and
once
the
interface
facing
the
registration,
those
three
interface
data
model
need
to
be
moved
forward.
Thus
our
deliverable-
and
we
have
this
a
client
interface
requirement.
That
document
has
been
installed
so
we're
looking
for
input
if
people
are
still
interested
in
pushing
this
forward
or
we
can
abandon
that
anything
else.
D
A
So
the
remaining
work
for
this
working
group
is
to
finish
the
capability,
that's
the
information
model
and
then
based
on
that
we
have
several
data
models
which
have
been
becoming
working
group
drafts.
Hopefully
we
can
is
all
converge
and
finish
it,
and
hopefully
this
is
the
last
time
we
need
meaning
to
do
that.
Hopefully,.
E
Friendship
I'm
one
of
the
course
of
the
capability
information
motor
and
the
take
a
motor
I
just
want
to
clarify
some
of
the
reason
that
a
situation
of
this
draft
for
the
capability
information
model.
Actually,
we
don't
bring
a
new,
updated
portion
for
this
meeting.
That's
because
we.
We
also
think
that
current
information
model
is
relatively
made.
Sure
it's
stable
right
now
and
because
it'll,
if
it
is
a
basica
business
motor
information
model
for
a
lot
of
data
motor
based
on
it.
So
and
we
also
have
the
data
model
based
on
it.
E
It
has
been
through
a
lot
of
several
runs
of
Hexham
and
interpret
the
test.
So
I
just
want
to
say
that
maybe
I
want
to
ask
good-looking
group
chair
and
if
we
can
ask
for
work
in
global
aster
Corps
at
this
stage,
because
it's
there's
no
new
thing
for
the
information
motor
shaft
and
the
data
model,
and
we
tend
to
have
the
same
feeling.
Yeah
yeah,.
A
F
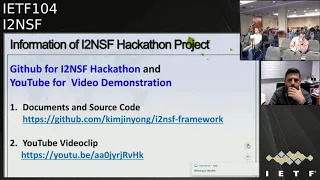
This
hackathon
is
at
the
Ace
accustomed
from
ITF
97
through
this
week
constructively
our
eight
times,
so
the
quarry
that
we
tried
to
verify
our
three
major
on
interfaces,
restoration,
interface
and
consumer-facing
interface
and
also
another
Pro
facing
or
especially
restoration
interface,
is
a
face
on
capability
Susan's
data
young
model,
so
we
verified
that
those
seeing
the
last
eight
yeah
hackathons.
Also
this
time
we
implemented
that
era.
How
was
it
translation?
So?
F
B
F
It
makes
us
like
please
yeah,
okay,
so
this
is
the
frame.
Okay,
I,
believe
you
guys
they
are
familiar
with
this.
So
we
on
top
over
a
Nepali
based
on
the
OpenStack,
we
implemented
the
I
to
an
SMS
system.
Three
interfaces
next
slide.
Okay,
that
is
okay.
So
especially,
we
implemented
a
translator,
such
as
user,
providing
security
policy
and
it
translate,
and
then
it
can
deliver
low-level
policy
into
MSM
facing
interfaces,
and
then
they
can
configure
also
IPSec
stop
case.
F
F
So
this
translator
is
a
very
important
for
our
working
group,
and
this
is
the
structure
my
student
will
explain:
a
young
junior
will
explain
so
I
can
skip
it
so
also
we
can
implement
using
OpenStack,
not
talking
as
I
proceed
for
a
subset
of
function,
chaining
for
services,
so
we
proved
a
proven
concept
and
also
we
designed
translator
or
also
on
the
hair
custom
project
is
open
source
project.
So
this
is
available,
especially
the
translator,
also
available.
F
A
G
F
H
H
We
have
changed
the
name
of
the
cases
we
have
been
discussing
during
the
past
millions
case.
One
is
now
called
Ike
case
and
the
case
to
iCLASS
case
so
remember,
I
case
when
the
Ike
version
2
is
in
the
NSF
and
the
I
to
this
case
when
the
NSF
doesn't
implement
Ike
person
2.
So
far,
we
have
a
description
about
the
case
of
the
hostage
horse
and
gave
way
to
gateway
rod.
War
is
not
concerned
the
current
version,
but
we
have
on
some
question
in
in
the
final
slide
about
the
this
case.
H
H
We
have
divided
the
original
immorality
part
for
better
reading
and,
in
order
to
you
know,
modify
easily
the
different
comments
we
have.
We
have
a
come
on
Mario
that
contains
common
typed
ever
grouping
that
can
be
used
in
both
additional
models.
One
of
them
is
related
with
the
ID
case,
which
is
ID,
fib,
Sakai,
key
Ike
and
then
ID,
fib
cyclase,
so
basically
the
same
original
information
beyond
the
changes
we
have
countless
we
have
received
is
there
but
just
separated
in
this
simply
next.
H
So
the
summary
we
have
the
ipsec
comma,
we
have
defined
type
def
and
groupings
which
are
common
to
both
cases.
I
case
and
eyeglass
case.
So,
for
example,
we
have
defined
their
integrity,
algorithm
encryption
algorithms.
Now
following
the
discussion
in
the
mailing
list,
what
we
have
done
is
true
import,
additional
module,
which
is
cannot
concrete
two
types,
so
we
don't
need
to
specify
one
a
specific
number
if
a
specific
level,
the
algorithms
we
are
going
to
use.
That
was
because
there
was
uncommon
about
what
happen.
If
this
algorithm
may
change.
H
So
in
our
draft,
where
we
are
doing
is
importing
another
module,
which
is
crypto
types
that
has
been
or
is
being
defined
in
networking
guru,
we
have
also
changed
their
lifetime
action.
There
was
a
no
clear
explanation
about
that
when
we
have
defined
these
three
action
related
with
the
lifetime.
The
description
is
in
the
draft
we
have
removed
forward
from
the
IPSec
traffic
direction.
We
have
only
inbound
outbound.
H
We
also
had
the
speedy
mark.
There
was
an
any
conclusion
about
what
to
do
with
that.
So
far,
we
have
removed
that
that
piece
of
information
and
well
regarding
the
lifetime.
For
example,
we
have
used
the
typical
type
engine
which
is
x
term
in
the
selector
grouping.
We
have
now
to
fix
the
lecture.
We
had
a
list
from
I
bleed
Rosanna.
We
have
left
and
right
some
and
then
in
the
processing
info.
H
H
We
have
needed
to
add
PF
group.
We
we
didn't
have
that
at
the
beginning.
Also
from
our
covers,
we
have
defined
another
type
def
about
the
authentication
mechanism
based
on
Fisher
key
or,
if
or
in
general,
the
you
know,
digital
signature
could
be
used,
RSA
or
DSA,
or
or
even
noon,
and
also
using
this
fact
that
we
have
a
container,
which
is
an
out
method
that
include
that
information
using
authentication
based
on
a
prefer,
the
you
know,
digital
signature
in.
F
H
D
H
E
Okay,
now
give
up
comments.
Okay,
a
friendship,
I
I
think
that
it's
a
good
way
that
your
are
just
imported.
Existing
crypto
types,
your
mother
in
the
Netcom,
cooking
or
I-
also
I'm-
also
the
one
of
the
contributor
of
that
right.
But
my
suggestion
is
that
maybe
you
should
just
take
a
look
at
the
current
crypto
diaper
now:
net
coffee
Armando,
because
that's
a
weird
peek,
crypto
times
definitions
there.
We
can't
really
include
episode,
courteous
and
SSH,
so
yeah,
it's
a
big
set
for
all
the
applications.
E
Maybe
you
you
know:
I'm,
not
I,
don't
know
they're
young,
how
to
write
to
your
mother,
but
my
dad
Union.
Maybe
there
are
some
you
can
either
in
your
to
to
support
in
your
your
mother.
Rather,
you
can
just
to
pick
us
a
subset
of
that.
You
know
the
crypto
diaper
yamamoto
identifiers,
just
the
for
use
for
IPSec
right,
because
some
may
be
not
useful
for
you
all
or
you
cannot
use
them.
C
C
For
instance,
people
would
like
to
set
up
a
VPN
between
to
Europe
East
streams
that
actually
are
VX
LAN
IDs,
and
so
you
only
want
is
that
one
specific
vehicle
and
traffic
to
be
carried
so
there's
probably
a
few
more
selectors
that
might
be
useful
to
be
be
added
in
the
future
and
so
and
the
other
thing
is
I'm
still
really
confused
about
the
algorithm
types
and
whether
you
used
other
documents
to
define
them.
I
miss
you
I'm,
not
sure
that
other
draft
and
lists
the
ones
that
are
valid
for
IPSec
or
not.
C
But
my
general
concern
here
is
that
these
types
of
documents
basically
put
a
snapshot
copy
of
the
ini
registry
inside
in
RFC
and
janna
registry
continuously
updates,
and
so,
for
instance,
because
of
this
document.
Actually,
we
started
an
IPSec
working
group
to
to
deprecate
some
of
the
older
ciphers
when
we
saw
that
other
people
were
putting
them
into
their
documents
and
I'm
still
sort
of
concerned
like
isn't
there
a
yang
way
where
you
can
say
the
the
the
valid
values
of
this
keyword
are.
Indecent
is
Ayana
registry
and
I'll.
C
Leave
it
more
because
because
someone
who
implements
whenever
this
becomes
the
RFC
will
have
a
snapshot-
and
you
know
a
year
later,
if
they
start
implementing
it
from
there
they're
missing
the
latest
algorithm
or
they're.
Implementing
obsoleted
algorithms
like
like
I,
would
really
like
to
just
point
to
the
IANA
registry
and
say
you
know
if
all
the
valid
IPSec
encryption
algorithms
look
there.
H
Yeah,
that's
actually
we
did
this,
because
this
is
the
solution
we
take
because
in
the
end
we
understand
is
moving
the
problem
from
our
drive
to
another
drug
that
is
defined
in
other
working
group.
But
actually
we
need
to
investigate
that
so
because,
in
the
end,
you
need
to
define
some
kind
of
I,
don't
know
integral
or
something
to
refer
a
number
saying
this
number
would
be
in
the
beginning.
What
we
have
was
a
type
def
with
several
Adam.
So
actually
the
comment
was:
what
happened
is
something
new,
a
beer
or
something
every
move.
H
E
Can
also
cost
I
think
this
is
a
very
good
question.
I
think
we
need
to
solve
this
kind
of
a
general
problem,
not
only
for
this
distract
I
think
the
better
ways
to
solve
this
problem
in
the
crypt
attack
Emoto
chapter,
because
that's
such
after
that
we
want
to
make
it
a
basically
on
title
mode
or
document
for
a
lot
of
application,
exactly
it's
just
one
of
them.
So
yes,
I
also
hope
so
that
some
young
candy
than
that
we
can
wecan
a
periodically
track,
the
the
the
the
Elgar
a
secure,
crypto
algorithms.
E
So
you
know
they
are
if
they
are,
if
they
are
still
good
or
if
they
are
duplicated.
According
to
the
angle
and
the
definition,
so,
yes
I
think,
because
that
drafter,
the
Crypt
would
quickly
tap.
Java
is
still
in
progress
and
improving
I.
Think
a
way
I
will
ever
take
a
to
take
care
of
this
problem
and
to
consider
how
to
solve
this
general
program
in
that
just
so
so
that
every
other
document
that
included
that
Java
import
that
traffic
in
tune.
H
E
H
That
was
actually
that
was
actually
our
approach:
I,
meaning,
okay,
this
is
a
problem
that
needs
to
be
solved
and-
and
there
is
some
kind
of
draft
trying
to
compile
of
the
cryptographic,
algorithms,
though
they
will
need
to
update
that.
So
the
only
thing
we
need
to
do
is
to
import
that
that
draft
and
included
in
the
in
our
drive,
okay,.
A
One
more
comment
here:
young
data
model
does
allow
you
to
make
changes,
expand
and
shrink.
So
we
just
need
to
pass
this
to
the
young
doctor
and
have
them
look
into
it.
I
know
that
several
people
I
work
with.
They
actually
work
on
that.
How
do
you
expand
the
data
model,
increase
and
decrease?
So
so
we
I
just
need
to
do
that
if.
I
I
may
interpret
what
Paul
was
saying,
because
I
was
going
to
ask
precisely
for
the
self
of
the
same
thing,
having
the
possibility
of
referencing,
an
Diana
registry
or
any
other
I
mean
because
in
my
proposal
for
going
forward
with
the
models
cause
it
precisely.
The
idea
of
referencing
from
the
gem
model,
another
young
mother,
of
a
piece
of
a
young
model.
I
D
The
obvious,
not
nice
way
of
doing
that
is
the
mean
within
the
NA
three
triple
Gus
is
three
and
ASG
cm
is
twenty,
and
we
can
just
replace
the
enumeration
with
the
number
and
yeah.
Then
the
anything
in
the
and
the
registry
is
okay,
I,
don't
know.
If
that's
what
we
want
to
know
to
do
it,
because
then
our
RFC
becomes
very
unexpressive
just
well.
This
is
a
number
and
go
to
the
end
and
registry
to
see
what
it
means,
but
it
is
future
proof.
C
A
J
H
So
we
have
now
in
the
grouping
like
proposal.
We
have
added
something
related
with
a
lifetime
about
the
I
say:
security
I
mean
I,
say
because
we
didn't
have
any
lifetime.
We
have
defined
hard
and
soft,
and
also
after
a
government
post
comment.
Basically
we
have
defined.
We
haven't
defined,
no
action
related
with
heart.
In
their
sense,
the
action
is
always
terminate.
Okay,
so
that's
also
applicable
to
some
common
about
the
related
with
the
lifetime
of
the
IPSec
s
ad.
H
H
The
different
policy
is
a
list
of
acid
SPD
entries
related
with
that
connection.
So
right
now
in
the
model,
what
happen
is
we
define
a
connection
with
some
between
two
peers
and
then
we
define
the
SPD
entries
for
data
connections.
If
we
define
another
different
connection
and
then
we
are
the
policies
related
with
that
connection,
and
then
we
have
also
a
container
a
list
of
the
child
essays
instead
in
the
sense
that
we
provide
only
information
about
the
different
SP
is
that
the
implementation
has
created,
but
not
additional
information.
H
Now,
our
question
here
in
the
you
know,
slides
we
have
is
if
whether
we
need
actually
more
information
that
only
the
SP
is
or
even
information
about
the
different
IPSec
security
position
that
they
I
lamentation
has
gravity.
It's
a
normal
question.
We
have
in
the
in
the
next
slide,
so
this
next
step.
H
H
We
have
simplified
the
container
I
mean
that
the
model,
so
we
only
have
the
container
for
the
SPD
and
the
container
for
this
ad
and
that's
the
piece
of
information
that
they
control
need
to
configure,
and
then
we
have
a
three
notification:
Dex
file
acquire
and
the
mugs.
Actually,
this
is
an
old
company.
I
know
coming
from
that
all
mentioned
in
the
past.
So
next,
so
we
have
now
two
slides
about
some
open
questions.
We
have
right
now.
H
What
we
have
is
an
SPD
model
with
one
policy,
I
mean
one
engine
SPD
one
policy
with
multiple
traffic
selectors.
Actually,
that
is
fine
and
there
FC
for
300
in
the
implementation.
We
have
film
actually
or
we
have
absurdities.
We
have
one
policy
when
one
traffic
selector,
so
our
question
is:
should
we
simplify
the
speed
model
with
re,
not
just
one
topic
silikal.
H
Another
related
question
is
I.
Think
Paul
mentioned
is,
is:
is
there
any
support
for
multiple
traffic
selector,
the
middle
of
SPD's,
in
a
single
child
essay
right
now
this
is
not
supporting.
The
reason
is
our
assumption.
Is
this?
Child
is
a
should
have
a
traffic
selector
wider
than
the
policies
that
is
associated
with
that
single
child
essay
and
our
download
is
that
is
allowed
in
the
standard.
It
was
our
error
dot
so
so
far
is
not
supported,
but
if
it's
okay
to
re-
but
we
can
do
it
another
question:
should
we
remove
a
h2
board?
H
H
D
With
chair,
cut
off
former
implementer
on
I
would
say
that
a
childís
I
should
have
one
traffic
selector,
because
when
you
try
to
support
more
than
you
get
interoperability
problems
and
yeah,
it's
really
how
about
aah
yeah,
nobody
uses
it
so
yeah
I'm,
very
fine
with
losing
it
is
being
capsulation.
Well.
I'll
leave
the
rest
to
prophetess
here.
I.
C
Thought
so
that
seems
well
going
to
me
and
I
just
wanted
to
make
you
aware
of
another
recent
thing
that
we've
been
doing
is
where
we
are
installing
multiple
ipsec
assays
of
the
exact
same
traffic,
selector
kind,
because
we
are
like
binding
them
to
CPU,
so
we
can
have
like
four
CPUs.
We
bind
four
identical,
IPSec
assays
to
a
single
CPU,
and
then,
if
that
CPU
generates
traffic,
it
goes
over
that
one
IPSec
assay.
So
for
us
it's
a
way
to
to
get
more
and
more
throughput
performance,
so
you
could
actually
have
child
essays.
C
C
H
H
C
K
C
If
it's
on
your
next
slide
or
not
I,
think
I
convinced
you
to
remove
the
IKE
port
are
being
on
the
source
and
destination
and
I
would
like
to
apologize
and
ask
for
you
to
put
it
back
in,
because
there's
actually
use
cases
where
people
make
bring
kubernetes
containers
that
only
get
a
very
few
UDP
ports,
and
so
they
don't
get
UDP
port
for
Ike.
So
they
get
like
UDP
port
662
680.
And
so
then
you
need
to
pre
configure
the
Ike
port
on
both
the
source
and
destination.
C
J
H
J
H
J
H
A
C
Ditty
sorry
part
is
just
to
clarify
I'm
there's
a
lifetime
of
the
IPSec
assay,
but
there's
also
what
what
value
is
asks
for
an
idle
lifetime
so
that
you
can
say
like
if
this
connection
has
been
idle
for
30
minutes,
just
shut
it
down,
but
all
of
this
happens
in
the
soft
timers.
The
hard
time
is
really
like.
All
your
regular
processing
hasn't
happened,
and
this
is
the
emergency.
We
must
not
do
more
encryption
with
the
key,
so
the
only
action
we
had
is
to
kill
the
SA
and
that's
why
there's
no
action.
H
Yes,
just
the
tree
was
one
yes,
one
common
because
it
stopped
there.
There
was
a
very
common
regarding
removing
a
name
associated
to
the
policy.
We
reflected
that
in
our
model,
because
they
RFC
4301
assess
that,
but
we
are
also
fine
for
removed
in
age,
because
that
cleans,
the
actually
I
think
you
mentioned
Paul.
Mention
mentioned
that
that
name
weird,
but
as
I
said,
is
define
the
data
RFC.
So
we
don't
know
what
to
do.
Who.
H
Maybe
it's
not
useful
to
have
a
name
for
the
policy,
yes,
that
in
a
practical
sense
and
the
final
ballot
each
bullet
is.
The
question
is
up
in
which
should
we
include
road
warrior,
support
or
generate
a
new
ID,
our
idea
in
the
Korean
established
and
considering
all
the
reviews
we
have
received
and
taken
into
account.
We
have
hostile
house
and
gateway
to
anyway.
Maybe
it
would
be
good
to
have
a
separate
internet
back.
That's
our
our
idea!
Well,.
D
I
tend
to
agree
that
this
should
be
in
a
separate
internet
draft.
Well,
for,
if
you
for
know
of
the
reasons
that
we
are
likely
not
controlling
the
road
warriors
machine
with
the
SDN
controller,
it's
usually
a
phone
or
a
laptop
or
something
that's
not
really
under
our
control.
So
in
that
case
we're
just
configuring,
this
sort
of
a
VPN
gateway,
and
then
it's
different
enough
that
it
should
be
something
I.
Think.
H
H
So
that's
another
question
we
have
right.
Now
we
only
provide
the
third
bullet
is
SP
is
a
state
that
related
with
the
ABC
cases
in
there
I
case.
The
question
here
is
whether
I
mean
the
controller
need
to
know.
It's
know
anything
about
the
IP
Sega
says:
yes,
maybe
the
number
I
don't
know
because
after
after
all,
you
send
the
policies
you
want
to
the
I
complement
ation.
The
equation
will
manage
everything
about
the
ABC
cases
and
regarding
their
eyeglass.
Maybe
this
is
related
with
the
previous
discussion
right
now.
H
The
relationship
relationship
between
entries
in
the
SPD
and
the
sa
ID
is
linked
using
traffic
selector.
The
question
is:
if
whether
we
should
have
explicit
pointer
like
something
like
a
reg
ID,
as
you
can
may
know,
in
the
IPSec
kernel,
in
order
to
link
both
entries,
I
mean
the
SPD
and
then
the
there'll
be
second
set,
and
yes
that
I.
D
C
D
H
This
is
a
different
comment
as
this
one
I
we
have
in
this
life,
because
what
we
were
referring
is
if
the
SPD
entry
I
mean
the
policy
des
PD,
and
then
you
have
the
ipsec
essays.
Usually
you,
for
example,
you
have
in
Linux
kernel
you
have
the
Reg
ID
like
you
can
use
that
like
a
pointer
to
to
the
between.
Oh,
oh,
you
see
on
the
Ibis
legacy.
So
the
question
is
we
don't
have
that
kind
of
link
we
had
in
the
past
that
kind
of
thing?
But
right
now
is
okay.
H
This
policy
have
traffic
selector
and
then
you
have
Devi
Sega
say
that
has
traffic
selector,
so
the
relationship
between
the
AV
Sega
say
and
they
in
the
and
the
policy
is
based
on
that
traffic
selector.
The
other
thing
you
mention
is
that
one
inbound
spi
has
a
like
related
outbound
spi,
and
they
we
should
reflect
that
relationship.
Is
that
correct?
Okay,.
D
H
Take
another
look
to
the
draft
in
order
to
see
if
they
are
okay
with
the
changes
or
the
main
changes,
and
then
we
think
the
document
should
be
really
for
they're
working
or
last
call.
We
would
like
to
thank
a
game
to
to
ball
because
he
said
he
did
a
really
amazing
review
of
our
draft
and
we
really
have
to
say
that.
Thank
you.
Okay,.
D
A
D
D
Yeah
right,
good,
so
I
think
we'll
wait
a
week
after
the
meeting
and
then
started
working
up
last
call,
and
hopefully
we
can
get
this
done
by
the
next
ITF,
because
we
are
hearing
a
lot
of
well
a
lot
of
noise
from
the
industry
of
people
who
want
this
buffer
within
the
ITF
and
outside
the
ITF,
because
people
want
to
deploy
IPSec
mainly
because
their
TLS
working
group
is
not
letting
them
break
TLS.
So
they
you
might
as
well
fare
better
with
IPSec.
A
L
So
David
Carol
I
think
it
could
be
complimentary.
I
had
talked
in
the
past
about
trying
to
write
up
a
case.
Three
and
I
have
not
made
the
time
and
done
that,
and
so
it's
not
ready
I
could
bring
something
forward
at
some
other
point
soon,
but
I
don't
know
I.
Think
at
this
point
this
document
seems
ready,
yeah
and
I
wouldn't
want
to
be
holding
it
up.
Okay,
you
know,
I
asked
you,
you
know
thoughts
from
from
you,
but
I
don't
think
holding
it
up
would
make
sense
now,
if
this
isn't
right
so.
A
M
L
Of
them
it's
different
than
both
its
you're
not
doing
an
IKE,
but
it's
not
ike.
Well,
it
cyclist,
but
it's
not
the
same
as
the
I
close.
Okay,
it's
still
doing
you
know,
there's
there's
different
messages
that
need
to
be
sent
back
and
forth
some
of
it
some
some
of
the
things
that
the
SPD
and
the
and
the
pad
are
a
little
more
similar
to
what's
done
in
ike,
but
it's
not
the
same.
Okay,.
A
A
E
Good
night,
okay,
III
have
another
question
about
to
this
document,
and
maybe
the
option
three
kind
of
document
is
about
the
many
about
the
configuration.
Are
you
on
data
model
for
the
IKEA
and
a
keyless
case
and
I'm
not
sure
whether
the
the
another
solution
I
think
that's
that
resolutions
contender
is
mainly
about
t-distribution,
McKenna
de
for
the
sta
or
Sdn
controller,
our
scenario?
So
is
it
also
if
it
also
includes
some
data,
how
to
configure
the
the
the
pointer
to
achieve
this
tricky
treat
key
distribution,
so
I
mean
so
I?
E
H
Solutions
here
are
very
simple:
in
the
eye
case,
you
send
credentials
for
to
allow
the
icon
sent
occasion
and
in
the
case
of
the
eyeglass
you
are
sending
the
IP
sagesse,
so
the
interlocutors
usual
you're
sending
the
cryptography
material
and
algorithms.
You
need
to
establish
the
IPSec
assay,
so
I
don't
see
any
conflict.
Actually
he
said
young
model
could
be
extensible,
but
I
don't
see
any
conflict
actually
in,
as
I
said,
the
idea
behind
this
drug
is
firmly
simple.
You
configure
IPSec
assay,
then
you
send
all
the
parameters.
H
You
need
to
come
for
your
debbie's
baby,
sega
say
in
the
case
of
the
iCLASS
case,
and
when
you
have
to
perform
Ike,
then
you
send
credentials
about
authentication
in
Ike
and
in
the
first
phase
phase
one
or
the
authentication
of
the
I
say
so
I
don't
see
any
particular
if
I
understood
the
question
of
course.
Yes,.
E
C
It
so
I'll
try
to
sync
up
there.
It
is
so
what
I
think
is
the
case
is
that
in
the
distributed
eye
cases
where
you,
you
still
do
an
IKE
exchange
between
two
two
security
controllers,
but
then
some
of
the
values
are
only
transported
in
a
sort
of
similar
to
IQs
case
to
the
nodes
that
actually
use
it,
and
in
this
case
it
means
that
the
nodes
actually
only
know
the
private
key
and
not
security
controller.
C
H
F
Hello,
this
is
a
porridge
young,
so
at
least
documentary
is
about
the
applicability
of
I
to
NSF
in
the
real
world.
So
after
are
working
on
raw
score,
the
error,
detector
array,
La
Scala,
are
gave
a
three
major
comment.
The
first
one
is,
it
is
insecure.
If
we
allow
TMS
developer
management,
the
system
accesses
the
its
own
on
that
really
functions
their
time.
So
so
our
document
clearly
measure
the
TMS
is
not
allowed
to
access
NSF
online.
F
The
only
access
is
allowed
by
critic
on
Salama.
Secondly,
the
XML
example
required
for
concrete
example,
so
we
are
provided
the
time
based
our
fiber,
so
we
provided
the
code.
The
third
one
is
so
we
clarify
how
to
tell
if
a
given
software
element
in
an
aqua
blue
in
vironment,
such
as
an
MSF
learning,
on
top
of
what
we
adapt
or
just
virtual,
by
50,
such
as
the
STR
switch.
F
So
we
have
of
lien
upon
boarding
system
in
a
memo
system,
so
we
can
easily
clarify
using
the
description
of
a
capability
of
a
PMF,
so
we
can
easily
resolve
it.
So
those
are
three
things
are
addressed
in
the
libyan,
so
we
believe
this
is
related
to
some
committee
solution
to
ISSG,
so
hopefully,
working
out
of
chairs
can
move
it
forward.
Okay,
thank
you,
baby,
you
ready
who
is
it?
Okay,
eighty,
okay,
okay,
okay,
so
yeah
we
are
just
yet
commented.
You
can
yet
yeah
move
forward.
Okay,
okay,
thank
you,
yeah!
F
So
this
slider
includes
a
five.
There
are
young
model,
the
first
one
in
the
students
are
capability.
There
are
young
model.
This
is
the
debate
basis
for
the
other
young
models,
and
also
we
have
three
a
major
or
NSF
interface
and
consumer
interface,
laceration
interface.
So
also
we
have
a
monetary
interface
to
regulate
NSF.
F
F
F
Ops
are
working
group,
some
person
or
providing
a
valuable
comment.
The
first
one
is
Lee
vision
over
our
Tara
long
model
according
to
the
young
Caroline
such
as
RFC
sixty
eighty
seven,
so
we
synchronized
among
five
young
model,
especially
we
added
this
time.
Three
examples:
XML
file,
one
is
dr.
security,
such
as
a
fire
and
time-based.
If
I
were
the
secondly
content,
security,
such
as
a
reflector
vo,
IP
appeal,
I
people,
your
LT
security,
the
last
one
is
attack.
Mitigation
such
as
HTTP
or
HTTPS.
F
Firstly,
capability
a
terror
model,
so
we
devised
and
structured
tourneys
are
no
major
some
changes
in
content.
So
we
followed
the
guideline
for
young,
so
60
87.
So
we
follow
that
ease,
Qaeda
lines,
the
secondly
NSF
of
facing
interface
or
the
error
model.
Also,
we
be
structured
original
content.
The
major
change
apart,
we
added
four
or
three
scenario
for
personally
the
Web
Filter
during
work
time.
Secondly,
malicious
who
you
IP
buyo
lt-col
and
certainly
mitigation
of
HTTP
and
HTTPS
flood
attack.
F
So
you
can
see
this
I
just
to
show
a
time-based
fiber,
so
time-based
case
we
specify
during
what
time
such
as
you
are
employee,
so
you
cannot
access
Facebook
and
over
some
YouTube
during
your
work
time
right.
So,
in
that
case,
we
specify
time
range
and
also
this
is
the
SNS
IP
address
and
such
as
a
Google,
YouTube
and
Facebook,
something
like
that
that
we
can
find
out
otherwise
discrete
associated
web
filter.
So
we
providing
a
source
function,
training
so,
firstly,
the
fiber.
F
F
Suddenly,
a
consumer
facing
in
to
pace
the
consumer
face
interface
is
providing
to
I
to
MSB
users
such
as
the
security
of
the
Mitchell
writer
specify
high
level
scripted
policy
such
as
during
what
time
employee
cannot
access
as
soon
as
our
site,
that
kind
of
high
level
policy
at
liberty
to
security,
our
controller,
secure
controller
which
translate
to
using
our
translator
and
then
a
Massa
facing
interfaces.
It
can
be
used
to
deliver
that
so
previous
slide,
I
showed
the
fire
a
repeater
scenario.
F
So
this
time
we
changed
as
follows:
detailed
description
for
each
more
object
in
data
model,
and
also
we
use
the
crew
Fein
to
reduce
the
petition
over
the
common
part,
and
also
we
provided
a
more
generic
yeah
data
young
motor.
So
this
is
an
example,
so
you
can
see
the
metadata
IP
address.
The
metadata
has
a
name
and
also
take
that
one
is
just
has
a
mnemonic
name
meta
and
that
this
one
can
be
used
rather
than
the
Terra
is
many
places
require
data
to
this
one,
so
we
can
accrue
practice
also
IP
address
case.
F
Also
we
can
exact
exact
matching.
Overland
matching
can
be
provided
using
this
grouping
feature
so
also
generic
a
data
model.
So
the
PI
word
did
that
our
security
videos
are
take
it
in
the
attack
mitigation,
other
custom
condition,
threat
conditions,
wreck
condition,
especially
is
from
the
Oasis
the
standard,
e-series
and
the
body.
They
are
working
for
structured,
the
threat
information
from
it.
So
we
also
take
advantage
of
that
file
type
and
a
signature
information
for
content
security.
F
F
Detected
by
this
fiber
vnf
SNF,
so
you
can
see
this
website.
It
can
be
leased
up
like
this,
so
we
can
easily
specify
how
high-level
policy
and
then
fourthly,
restoration,
interface,
registration,
interface
cases
this
time
week,
just
focus
on
the
last
meeting.
Thiago
mentioned
lifecycle
management
is
out
of
scope,
so
we
need
of
them
and
just
focus
on
restoration
and
the
second
rate,
the
quarry
certain
cases,
some
helmet
policies
given
to
secure
security,
control
law,
432
no
registered
NSF
in
that
time,
secure
control
law
or
contact
contact.
F
The
developer
manuals
term
to
ask
whether
such
as
NSF
exists
on
that,
so
that
kind
of
quarry
is
provided.
So
we
devised
a
structure
and
also
we
added
a
some
description
for
young
tree
diagram.
Also,
we
also
provided
the
XML
exam
flows,
so
one
example
is
a
general
or
five
words.
So
fire
case
you
can
see
the
protocol
address
photo
number
and
also
we
specify
the
possible
actions.
This
is
a
fire
feature
and
also
we
can
providing
the
performance,
yeah
cry
tears,
criteria
and
also
access
implemented.
F
This
NSF,
if
I,
were
I
to
address
the
ears
right
there
and
photo
number
is
right
here.
So
security
control
lock
can
have
this
information
to
provide
security
service
for
users
so
and
then,
fifthly
and
I
said
for
monitoring
in
tera
models,
so
we
merge
the
information
model
in
the
data
model
and
also
we
in
structured
according
to
Caroline
for
young
terremoto,
and
also
we
replace
the
enumeration
type
with
the
identify
for
scalable
components.
F
So,
okay,
that
is
the
summary
of
changes
of
five
tarae-hyung
model
from
now.
I
briefly
describe
the
discussion
with
Diego
and
Frank,
as
though
Tiago
will
explain
in
detail
last
of
of
this
recession,
so
he
is
playing
so
but
I
pre-plea
explain
why
we
do
we.
Why
need
this
kind
of
terror,
motor
compulsion?
So
she's,
such
as
I
said
we
just
discussed?
The
lava
is
flamed
right.
So,
in
the
case,
certain
you
or
Tara
model
is
is
required
so
how
to
accommodate
in
our
Tara
model.
F
So
the
approach
is
that
we
can
use
like
for
us
to
that
concrete
Tara,
young
mothers,
so
especially
the
Ike
and
the
I
key,
IPSec,
I
or
I
could
list
cases
we
can
easily
specified
using
one
identity
are
left
reference
variable
so
for
young
for
so
new
yeah
you
can
see.
So
this
is
a
cop
ability.
There
are
models.
F
So
when
the
develop
management
system
register
fiber
into
the
security
control
law,
we
can
specify
this
kind
of
IPSec
Macerata
such
as
is
a
case
or
I,
detect
ELISA
cases
and
the
Leicester
racial
interface
can
specify
concretely.
So
such
this
intersect
for
support,
I
could
list
cases
so
we
can
easily
and
then
we
can
provide
it
on
this
kind
of
selection
of
Michael
is
the
script
controller
can
tell
the
security
NSF's
of
a
face
interface,
which
kind
of
like
master
diesel
used
for
NSF.
F
So
next
steps.
So
we
believe
last
eight
hackathon
project,
those
especially
the
Suzanne's
capability
data
model
and
three
major
interface-
is
a
young
go.
There
are
primo
mature,
so
we
believe
we
can
last
score
those
for
data
young
model
trapped
and
then
monitoring
cases.
Still
we
needed.
Two
more
or
some
airports,
so
next
accustomed
we
implement
and
that
we
can
prove
the
concept.
Okay,
that's
all
okay!
Thank
you.
N
O
O
I
I
That
doesn't
make
sense,
if
you
think
about
it,
because
is
that
difficult
that
many
of
the
functions
that
are
already
available
will
be
start
building
translators
from
capabilities
down
to
to
the
configuration
all
the
other
thing
is
is
a
translator
that
is
almighty.
That
knows
everything
that
can
translate
capabilities
into
all
the
different
kinds
of
mobiles
that
network
security
function
could
follow
for
its
falafels
for
many
being
managed
and
well
something
that
held
at
least
myself
in
understanding.
The
problem
is
when
it
comes
to
this
precisely
the
ipsec
controlling
model
that
is
brand
new.
I
I
So
there
is
that
that,
with
each
capability,
whenever
the
function
declares
a
capability
registers,
a
capability
being
used
to
say
well,
this
capability
is
associated
with
this
particular
model,
ideally
not
not
with
the
whole
mobile,
but
with
the
fragment
or
even,
if
you
like,
with
a
particular
barrier
variable
inside
that
particular
model.
But
this
is
something
this
is
one
of
the
things
that
we
would
like
to
ask
the
giant
doctors,
because
I'm
not
sure
that
can
be.
I
I
This
association,
the
natural
way,
is
that
we
we
keep
the
capability
model
without
without
being
touched,
and
what
we
do
is
that
we
make
this
association
whenever
there
is
a
registration,
so
the
developer
vendo,
who
knows
about
they,
they
say
well,
I,
implement
capability,
X
and
to
activate
a
man
and
control
capability
X.
You
should
use
this
piece
of
the
of
this
model,
so
it
should
be
an
extension
to
registration
interface
and
both
translate
into
a
ratio
of
models
that
are
applicable
for
the
set
of
capabilities
that
the
controller
knows
about
well.
I
That
implies
that
the
security
controller
both
have
to
keep
a
registry
of
models
and
associations
is
a
database
anyway,
should
have
to
keep
array
a
database
of
the
capabilities.
So
it's
extending
the
capability
later
is
and
rely
on
this
registry
for
Policy
translations.
What
means
makes
recent
proposal
that
Paul
made
precisely
about
the
policy
translator,
so
it
will
be
part
of
the
security
controller
and
what
probably
they
in
the
draft
about
the
policy
translator,
there
should
be
a
reference
to
the
capability
register.
I
The
means
well
basically,
I
mean
this-
is
something
that
since
well,
I
must
say
this
is
an
idea
while
flying
here
this
is
an
idiot
a
little
bit
with
Paul
and
Frank
during
the
during
the
hackathon.
So
probably
there
are
a
lot
of
problems
inside,
but
the
idea
is
that
we
should
send
the
registration
interface.
I
mean
the
registration
data
mobile
to
make
it
to
put
a
mechanism
to
announce
these.
These
reference
to
the
air
to
the
management
mobile.
I
We
have
to
decide
what
to
do
with
the
NS
NSF
facing
interface,
because
if
we
transform
the
NSF
phasing
interface
to
a
way
of
using
Jan
to
modify
the
functions
using
the
registry
either,
we
think
that
is
a
wrapper,
and
that
inside
is
the
data
model
operating
without
me.
They'd
be
data
model
at
all,
because
we
are
going
to
use
the
reference
ones.
This
is
something
that
we
have
to
think
and
again
it's
more
about
the
tooling
using
jiying
than
anything
else.
I
Well
that
we
need
to
refine
this
essentially
and
well.
Yes,
I
know
this
is
a
very
rough
idea.
Let
me
see
what
they
think
is
important.
I
mean
for
making
this
advance
and
make
it
this
advanced
as
fast
as
we
can,
because
otherwise
we
are
risking
to
get
stuck
in
a
situation
in
which
we
have
the
the
IPSec
graph
moving
it.
Let's
say
in
the
wild,
not
allowing
with
the
capability
movin
over
lag
and,
as
you
have
said
it,
there
is
a
demand
for
it.
I
E
Thank
you,
Iago
and
Peter
complained
about.
It
is
a
new
idea,
but
I
I
think
about
it,
and
we
discuss
it.
I
think
that
that's
a
way
to
achieve
the
consistency
about
the
current,
so
so
many
data
models
to
reach
your
consistency
between
them,
because
we
have
a
long
time.
We
have
a
consensus
in
working
group
that
capability
data
murder
and
that
information
more.
The
capability
is
a
very
key
terminology
or
the
basic
block
for
the
whole
extended
attack
interface
data
model.
E
So
we
mastered
a
figure
a
way
to
to
make
Oda
statement
or
to
be
in
a
consistent
way.
So
this
is
a
good
solution.
Is
a
good
way
to
to
achieve
this
or
Cantonese
and
I
also
say.
I.
Also
think
that
this
is
a
also
our
flexible
way,
because
a
country
we
have
a
visa
is
example
that
IPSec
statement
or
how
to
comply.
E
How
to
a
language
that
is
not
debilitated
moaner
and
maybe
in
the
future
they
are
allowed
or
a
statement
of
policy
motor
for
the
all
security
function,
management,
so
I
think
we
should
as
soon
as
possible.
We
find
our
way
to
to
provide
it.
Is
the
kind
of
flexibility
to
add
the
future
new
data
model
in
our
the
general
model?
So
this
is
a
very
good
way,
so
the
only
problem
is
that
a
theater
will
bring
a
big
influence
or
changes
to
our
coordinate
data
model.
E
I
Reflection
thanks
Frank,
my
only
what
do
we
have
to
do
as
well
is
to
talk
with
Aldo
and
young
about
this
because
they
are
not
here.
This
is
something
that
we
have
and
well
we
have
to
share
this
with
them.
I
hope
they
will
be
I
think
this
will
be
acceptable
for
them
because
doesn't
affect
that
the
capability
model
at
the
end,
it
doesn't
change
the
principles
so.
F
This
is
a
Porto
from
sa
Kiki.
You
so
yeah
I
think
a
Diego
point
out
a
very
important
issue.
So
during
a
cousin
project,
Diego
prank
and
I
discussed
this
one
also
I
discussed
it
with
my
student
how
to
implement
this
new
or
suggestion
into
the
error
model.
So
my
group
are
disgusted
during
we
can
and
then
my
previous
presentation
we
can
conclude
the
identity
identity
left
can
be
used
because
the
ana
space
in
case
we
can
have
as
an
additional
variable
for
identity
in
laugh
and
that
we
can
easily
import
the
Nahas
ipsec.
F
A
I
I
Is
this
one
and
you
put
other
reference
we
have
to
discuss,
or
we
have
to
find
whether
this
how
this
reference
can
be
constructed
in
the
best
possible
way
in
terms
of
referencing
being
able
to
verify
etc,
but
is
a
reference
to
say:
AI
is
a
little
bit,
and
this
is
what
I
was
asking
before
is
a
little
bit.
What
Paul
was
asking
about
the
Yana
registries,
something
similar
as
to
say
is
to
say
look
here:
I
want
to
use
that
thing.
Basically,
so.
F
P
I
There
is
only
one
I
mean
that
well,
there
are
two
later
models
that
I
mean
the
capability
model
is
not
going
to
be
touched
at
all
the,
and
this
is
one
of
the
things
that
we
were
trying
to
find
a
way
of
solving
this
race,
because
a
capability
model
I,
don't
know
we
do
have
gone
through
the
document.
That
is
heavy,
something
that
is
difficult
to
deal
with,
and
so
the
capability
model
is
not
to
be
touched.
I
The
registration
interface
should
not
go
for
La
Scala,
because
we
need
to
make
this
modification
and
we
have
to
open
a
reflection
time
for
the
NSF
facing
interface.
All
the
rest
I
mean
that
we
took
it
to
documents
that
say
we
need
to
reconsider.
The
rest
are
ready
for
as
far
as
I
can,
as
we
can
tell,
because
it's
something
that.
A
A
P
I
I
A
H
Q
A
Q
H
A
R
R
Then
curious.
Here
is
the
two
types
of
sentence.
The
first
one
is
the
policy
for
I
to
nesaf
users
and
second,
one
is
policy
for
NSS
so
and
I
turn
us
a
future
case.
They
can
easily
generate
the
first
sentence,
but
because
it's
usual
kindly,
but
second
one
isn't
when
I
turn
as
a
user
doesn't
have
any
expert
knowledge
of
security.
R
However,
in
NSF
case
and
as
NSF
cannot
recognize
the
first
first
one
because
the
data
of
that
first,
the
first
sentence
is
really
abstracted.
So
even
if
I
turn
SF
user
gives
the
first
high-level
policy,
then
I
turn
SF
system
needs
to
automatically
translate
it
into
the
low
level
policy
yeah.
So
actually
for
translating
the
XML
based
policy.
Actually
Excel
silty
is
popular
method
for
doing
that.
So
in
sis
ripple,
for
example,
sis
ripple
is
for
implementing
the
using
the
net-net
comp
server
yeah,
but
it's
really
popular,
but
it
has
some
limitation.
R
So
we
propose
the
automata
based
policy
translation,
so
we
can
solve
the
two
kinds
of
limitations,
so
here
translation
architecture.
So
our
purpose
is
when
I
to
an
ACEF
users,
then
a
high-level
policy
geo
are
as
the
critical
controller.
Then
we
can
select
the
proper
target
NSF's
automatically
and
translate
the
high
dollar
policy
into
the
low
level
policy
and
send
it
via
the
network
security
function
based
interface.
R
Then
we
can.
We
should
specify
the
abstracted
data,
because
NSF
cannot
recognize
the
abstracted
data
and
also
we
should
find
the
proper
NSF
automatically.
So
we
extract
the
unique
capability
for
each
NSF.
So
when
the
policy
data
has
some
unique
capability,
then
we
can
select
the
appropriate
NSF
automatically
like
that.
R
So
the
previous
draft
was
the
version
2.
So
actually,
the
explanation
have
been
added
or
explaining
the
NSF
data
based
components
and
also
implementation.
Consideration
section
is
added
for
providing
the
great
guideline
for
developer,
so
security
policy
translation
is
the
core
function
for
I
to
Anessa
implementation
in
the
real
world.
So
for
emphasizing
these
draft,
so
I
will
introduce
one
draft
RFC
documents,
its
RFC,
eight
7:5.
It's
about
the
mapping,
implementation
between
HTTP
clients
and
web
server.
R
That
purpose
of
that
purpose
of
that
draft
was
just
attaching
the
HTTP
client
and
clap
server
for
exactly
IOT
IOT
network,
so
that
that
was
a
really
necessary
function
in
their
work
and
they
gave
the
cat
guideline
for
mapping
constructing
environments
and
yeah
such
the
other
things
for
implementation
and
its
success
it
to
be
the
RS
RFC
documents
for
that
case.
So
this
draft
can
provide
the
I
to
NSF
developers
with
the
great
guideline
to
implement
and
mapping
and
constructing
the
security
controller.
R
F
Yeah
can
I
share
my
opinion,
so
I
am
paul
john
kasich
iike
you,
I
am
also
the
court
is
prepped,
so,
as
you
may
observe,
the
translation
is
very
important,
especially
the
la
paz
IPSec
that
high
labor
some
policy
given
to
the
security
controller
from
I
turn
a
polluter.
So
our
translator
also
tells
with
that
kind
of
policy,
which
means
I
core
I
could
list
case
is
translate
and
then
easily
impressed
into
NSF
and
also
security
policy
for
security
functions
such
as
our
recruiter
and
other
videos
attack
mitigation
case.
F
The
policy
is
a
delivered
to
security
controller
from
I
to
another
user
or
the
oedometer
writer,
so
we
can
easily
translate
to
using
these
framework.
So
this
document
is
a
more
likely
architecture
and
also
those
on
procedure
letter
than
some
implementation
detail.
Even
though
we
have
a
guideline
for
implementation
for
a
developer,
but
we
aim
at
informational
atmosphere
like
the
core
core
working
group.
Has
the
ad
875
is
a
mapping
from
HTTP
to
coop,
so
in
the
same
way,
I
believe
it
is
documented,
very
usable
from
our
working
group
work
in
the
industry.
A
F
A
E
Francha
and
I
think
yeah,
I
agree
that
this
document
has
some
value
that
it
came
to
right.
The
guidance
for
the
working
group
to
do
the
translation
functions,
engineering,
the
security
controller,
a20
securing
that
is
value,
but
based
on
the
example
you
show
here,
I
I
think
my
personal
feeling
that
you
may
miss
understand
the
the
risk
at
the
the
latest
are
security
functions,
implementation
for
example,
right
now,
our
a
lot
of
network
firewall
devices
we
whatever
work,
we
we
call
it.
Maybe
we
can
call
it
our
next-generation
firewall
right.
E
A
lot
of
these
kind
of
security
devices
has
already
provided
a
lot
of
application.
They
are
information
to
manage
them
to
directory.
For
example,
we
can
you
put
in
director
configure
then
by
using
the
user
information,
the
user
group
and
the
application
name
or
the
service
name.
So
that's
that's.
So
that
means
that
so
those
work
to
not
need
to
provider
by
the
to
be
provided
by
the
network
security
controller
security
controller.
E
So
if
all
of
your
content
in
this
document
is
about
to
translate
from
this
a
fall
for
this
kind
of
information,
I,
don't
think,
is
very
useful.
For
current
we're
more
than
a
security
device,
so
if
you
otherwise,
if
your
provider
are
very
high
level
architecture
to,
please
spend
how
to
do
these,
abstract
translation
functions
and
what
is
architecture?
What
is
a
general
mens
order?
I
think
they
are
helpful.
R
I
I
want
to
take
some
more
time
before
you
go
for
coffee
Sibley.
Is
that
well
I
at
the
beginning,
when
I
first
saw
these
these
proposed,
this
document
I
thought
it
was
that
sort
we
are
to
have
in
the
in
the
group
right
now.
Taking
it
again,
the
reason
proposed
all
about
the
registration
interface
and
other
like
is
something
that
it
makes
much
more
sense.
