►
From YouTube: IETF105-6MAN-20190723-1710
Description
6MAN meeting session at IETF105
2019/07/23 1710
https://datatracker.ietf.org/meeting/105/proceedings/
A
C
D
B
B
B
We
have
review
of
the
RFC
8200
fragmentation
errata.
We
have
discovering
prep,
64
and
router
advertisements,
so
we
for
today's
agenda.
We
made
this
may
end
up
going
quicker,
so
we
may
move
some
of
the
other
talks
up,
but
we'll
see
how
it
goes
and
then
we
have
ron's.
Oh
no.
We
have
a
proposal
to
change
RFC
2675
jumbo
grams
to
historic
and
though
he
bronze
sr
v6
+
draft
and
we've
asked
him
to
basically
just
not
get
into
the
details,
but
talk
about
overview
and
motivation.
B
E
Just
want
to
say
is
it.
This
is
really
disappointing,
because
now
I'm
totally
confused
how
we
are
going
to
incrementally
deploy
v6
on
the
networks,
so
I
suggest
people
might
who
were
against
it
might
think
about
the
possible
deployment
model,
because
now,
when
we
decided
that
we
don't
do
not
want
to
have
explicit
signal
in
the
network,
we
might
end
up
with
some
implicit
signal
and
which
is
probably
not
a
good
idea
right.
D
F
A
solution
so
like
Ola
and
I
talked
quite
a
bit
about
this,
like
so
there's
no
consensus
to
advance.
This
doesn't
mean
it's
a
bad
Eddy
or
anything
right.
So
it's
just
that
this,
like
set
of
compromises
to
be
made
because
it's
like
quite
a
bit
of
operator
feedback
saying
this
is
like
actively
harmful
to
them
right
and
there's
like
this
poster
points,
a
negative
points.
D
Course
you
can
appeal
this
decision
right
and
there's
a
process
of
that,
but
you
know
yes,
it
was
certainly
hard
and
I'm,
not
I'm,
not
happy
with
the
outcome
either,
but
that
was
you
know
where
it
seemed
like
the
community
wanted
to
go.
Okay.
Thank
you.
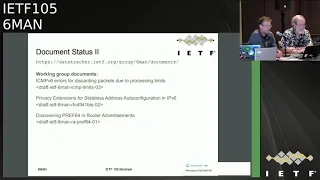
Thanks
for
it
document
status,
we
have
three
working
group
documents.
We
have
the
ICMP
errors,
it's
on
the
agenda.
For
today
we
have
the
privacy
extension
after
date,
that's
in
review.
D
We
have
two
ongoing
reviews
from
other
working
groups.
The
IP
way
one
I
think
we're
pretty
much
done
with
that's
going
on
in
IP
wave,
there's
been
quite
a
lot
of
back
and
forth
on
that,
one
with
regards
to
prefix
lengths
and
so
on
and
from
6lo,
which
we
just
received,
the
our
v6
backbone
reader
document
for
a
review
team.
D
Winters
have
graciously
accepted,
with
a
little
bit
of
nudging,
I
accepted
to
review
that
if
there's
anyone
else
who
like
to
review
that
document,
please
raise
your
hand
or
or
let
the
chairs
know
it's
recently
urgently
so
we'd
like
to
have
a
review
it
in
in
you
know
a
week
or
two
for
that,
one
okay.
So
the
next
topic
is
any
comments
on
the
SRH
based
document.
G
G
So
what
we're
gonna
do
is
just
talk
about
the
issues
that
Suresh
rose
rate
risen
had
had
brought
forward,
like
that's
right
word
and
how
we're
gonna
resolve
those,
and
at
the
end
of
that,
if
anyone
has
comments,
you're
welcome
to
come
on
all
right.
The
first
one
and
I'm
gonna
read
from
down
here
so
TL
views
are
present
when
the
header
extinction
links
exceeds
the
last
entry
element
in
the
segment's
list
and
suresh
points
out.
This
doesn't
doesn't
sound
right.
G
I
think
we
can
fix
this
with
a
bit
of
math
describing
exactly
how
an
implementation
would
be
able
to
identify
when
TLV
czar
presents
so
I'll.
Add
that
in
and
that'll
go
to
the
list
section
2.1,
what's
the
purpose
of
being
able
to
include
an
HTML
TLV
with
the
key
idea
set
to
zero
since
there'll?
Be
no
H
Mac,
that's
been
in
the
draft
for
quite
some
time
and
I'm
gonna
leave
that
as
to
be
determined
because
I
have
to
go
back
and
see
what
the
original
intent
was
around.
That.
G
G
G
There's
a
comment
here
saying
that
RFC
82,000
doesn't
actually
talk
about
mutability
and-
and
we
did
talk
about
this
within
the
working
group-
quite
a
bit-
I
think
the
fix
here
is
going
to
be
mentioning
that
well,
RFC
d200
doesn't
explicitly
state
anything
about
mutability
that
it
does
allude
to
it.
In
section,
4.4
and
I
think
that'll
be
our
resolution
to
this
particular
question.
I
know
we
had
a
lot
of
comment
around
this
text
and
a
lot
of
work
on
it
in
the
working
group.
F
I
G
In
section
two,
one
I
think
we
should
also
mention
that
padding
tlvs
are
used
for
alignment
of
tlvs
themselves,
something
along
lines
of
the
new
text
that
was
provided.
This
looks
this
looks
okay
to
me
and
that's.
Obviously,
the
intention
of
like
padding
TLV
uses
two
is
to
align
the
tlvs,
so
that
should
be
good
to
go
section
two
one
two
one
was
this:
one
text
in
the
beginning
is
real
okay.
G
Section
five
point:
for
the
zero:
a
segment
doesn't
seem
very
obvious.
Some
new
text
is
is
suggested
here,
so
we'll
just
take
that
new,
that
new
text
as
is
and
then
on
the
editorial
section,
he's
got
some
suggestions.
Around
segment
routing
could
be
applied
to
the
v6
data
plane
using
a
new
type
of
routing
extension.
Header
he's
got
to
fix
up
there
and
that
text
looks
fine.
G
F
J
K
L
B
K
D
J
K
K
M
You,
okay,
so
there
must
be
a
good
joke
in
there
somewhere,
but
kind
of
late
in
the
day,
so
I
won't
even
try
so
I'm
going
to
talk
a
little
bit.
Hopefully
this
will
be
brief
about
icmpv6
errors
for
discarding
packets.
This
is
a
working
group
draft
a
little
just
a
little
bit
of
overview.
So
the
idea
is
that
we
want
some
ICMP
errors
that
host
in
middle
boxes
can
send
when
they
drop
packets
for
exceeding
limits,
particularly
in
processing
extension
headers.
So
this
defines
for
new
parameter
problem
codes.
M
It
extends
applicability
of
one
parameter
problem
code
and
one
new
destination
unreachable
code,
the
parameter
problem
codes,
one,
the
general
parameter
problem-
is
used
for
middle
boxes
now,
as
opposed
to
just
host.
So
if
middle
box
drops
a
packet
for
next
header
unknown,
that's
like
probably
wrong
for
next
set
are
known.
Then
the
middle
box
connects.
They
send
that
message.
M
Four
five,
six
and
seven
of
the
new
proposed
codes
for
parameter
problems
deal
with
extension,
headers,
so
extension,
header
too
big.
This
can
either
be
a
number
I
think
that's
one's
number
of
bytes
extension
header
chain
too
long.
So
the
sum
total
of
the
and
headers
exceed
some
processing
limit
too
many
options
in
an
extension
header.
This
is
simply
a
limit
of
the
number
of
options
and
options
too
big.
M
So
we
have
some
other
two
other
changes.
As
I
mentioned,
we
extend
the
applicability
of
perimeter
problem
code,
one
under
recognized
header
type,
to
allow
immediate
notes
to
send
and
we
added
new
destination
unreachable
code
parameter
num
number
eight,
which
is
headers
too
long
for
applicability
of
to
apply
to
the
situation
where
the
sum
total
of
headers,
not
just
extension
headers,
may
exceed
the
processing
limit
of
a
device.
F
So
for
the
unrecognized
next
header
type
right
like
are
we
somehow
changing
the
assumption
that
intermediate
nodes?
Don't
look
passing
unrecognized
next
headers,
because
they'd
only
require
to
look
at
a
few?
That's
Tiffin
and
IRC
all
right,
correct
and
any
new
extension
header
types
that
come
after
this,
like
the
intermediates
notes,
have
no
business
looking
at
it,
at
least
from
like
the
specification
point
of
view,
right,
yeah
and
and
I
think
I,
don't
know
like
it's
just
a
point:
I
want
to
bring
it
like.
F
F
M
F
D
M
M
So
we
have
three
drafts
version,
one
I
guess
for
a
truss
version.
One
was
a
working
group
draft
in
version
2
and
version
2
and
3
are
since
last
IETF
version.
Two.
We
added
the
last
option:
option
to
big
or
last
air
code.
I
should
say,
parameter
problem
code,
seven
and
in
version
3.
This
was
mostly
just
clarifications
in
the
security
section
and
some
edits.
M
Since
last
IETF
there
is
an
implementation
against
the
Linux
code.
So,
while
back
in
the
Linux
stack,
we
did
add
limits
per
our
C
80
504
for
extension
headers.
So
we
will
drop.
For
instance,
at
the
number
of
hop
by
hop
options
exceeds
a
limit.
That
limit
happens
to
be
eight
by
default,
so
there's
four
of
these
errors
are
actually
used
in
the
implementation.
So
far,
the
first
two
are
basically
sis
cuddles
and
those
have
to
do
with.
As
I
said,
the
RFC
85
of
four
limits
option.
The
third
case,
they're
extension
header
too
big.
M
So
this
is
flight.
In
two
cases
one
is
a
normal
extension
header
exceeding
a
byte
limit,
but
it's
also
convenient
if
padding
exceeds
the
number
of
pads.
So
our
C
85004,
for
instance,
recommends
that
or
suggests
there
could
be
a
limit
of
seven
consecutive
padding
bytes.
If
that's
exceeded
the
Linux,
a
cat
lease
will
drop
the
packet.
So
now
we
send
the
extension
header
to
a
big
message.
M
So
when
I
posted
this
up
stream,
it
got
some
good
feedback
from
the
net-net
dev
maintainer.
He
commented
that
there
were
other
cases
in
this
particular
block
of
code.
We
were
parsing
extension
headers
where
we
were
dropping
packets
and
not
sending
ICMP
errors.
So
we
filled
that
out,
in
particular
one
of
the
things
that
Linux
does
it.
It
does
check
patent
data
bytes
to
make
sure
there's
zero.
So
if
they're
not
zero,
we
now
send
just
a
normal
header
field
parameter
problem.
M
F
So,
like
one
thing
we
can
do
if
the
chairs,
like
do
a
consensus,
call
on
the
list
asking
for
an
early
allocation.
We
can
actually
go
and
get
an
allocation
right
now
right
and
then
it
it
expires
in
some
amount
of
time
like
I,
know
nine
months
or
like
a
year
or
something
so
you
can
get
the
code
points
lock
them
down
and
put
them
in
the
implementations
and
the
traffic
can
progress
in
parallel.
So
that's
like
a
mechanism
I'm
offering
to
you
like
chairs,
just
at
the
request
knee
okay.
M
D
Don't
all
run
to
microphones,
so
how
many
people
would
be
willing
to
review
this
as
a
part
of
a
working
group
last
call
one
two,
three,
four
five,
six
fantastic
I
didn't
need.
My
fret
shall
plan
after
seven
and
excellently
I
do
remember
you
so
come
back
to
you.
Yes,
I
think
I
think
we're
ready
to
to
last
call
this
and
we'll
send
that
announcement
out
as
soon
as
we
can.
Okay.
Thank
you.
B
We
change
the
option
format
to
include
the
return
value
and
a
recurring
flag,
and
we
I
think
we
talked
about.
We
tried
this
have
in
the
previous
hackathon,
but
we
made
some
we've
moved
over
the
flag
to
the
the
least
low
order
bit
in
the
last
two
bytes
and
we're
no
longer
because
we
have
a
return
value,
we're
no
longer
using
the
ICMP
packet.
Do
big
messages
were
just
you
send
this
in
another
hop-by-hop
option
back
to
the
source,
or
you
know
you
send
your
own.
B
B
You
know,
ipv4
MTU
discovery
had
they
only
known
that
we
wouldn't
be
doing
this
today
and
a
bunch
of
editorial
changes
so
and
here's
the
here's,
the
new
formats
I'm
sure
you've
all
read
the
draft,
but
you
can
see
the
return
flag
at
the
end
and
we
named
the
fields
instead
of
value
one
and
value
two.
So
this
is
what's
in
the
current
draft.
O
So
we
we've
implemented
it
and
we
have
something
in
why
sharklet
works,
but
we
need
to
work
out
if
it
actually
works.
The
internet,
which
seems
like
the
more
important
question,
and
so
we
need
to
do
people
to
do
experiments.
We
planted
your
experiments.
The
first
one
is:
do
hop-by-hop
options
really
work?
We
really
hope
so
what
size
of
empath
interior's
have
actually
supported
and
where
are
the
MTU
bottlenecks?
And
we
don't
know
the
answer
to
this.
O
So
that's
why
we
building
the
tool,
but
we
need
to
have
do
a
bit
of
mapping
for
this
and
what
happens
in
practice
when
we
try
and
do
this
when
we
have
the
crazy,
real
internet
and
well
we're
going
to
do
this
work
and
we
would
love
other
people
to
join
us.
So
it's
a
plea
for
other
people
to
say
this
is
fun.
Oh.
B
And
so
we
did
do
we
hit
a
smaller
hackathon
project.
Olli
worked
on
his
VPP
radical
notation
and
I
learned
how
to
actually,
instead
of
doing
a
Lua
plug-in
I
learned
with
a
lot
of
help,
how
to
actually
modify
Wireshark.
You
know
change
the
packet,
ipv6
dot,
C
file
and
with
some
other
help.
We
finally
have
it
working
as
you
can
maybe
read
this,
but
it
now
shows
the
option
and
and
more
importantly,
with
the
thing
we
couldn't
do
with
the
Lua
plug-in.
B
P
Hi,
my
name
is
Tim
Shepherd
this
sometimes
the
IMP
eat
into
you
bottleneck
is
in
a
box
that
does
not
look
at
the
IP
header
and
in
which
case
the
box
that
is
looking
at
the
IP
header
and
the
extension
headers
might
not
even
know
about
an
MTU
bottleneck
between
it
and
its
next
hop,
IP
layer
thing,
and
so
that
I
mean
so
just
as
long
as
you
all
understand
the
limitation
of
this.
This
easy
answer
to
this.
Yes,.
O
But
and
okay,
so
there's
two
places
we
could
you
use
this
one
was
in
an
area
where
you're,
actually
configuring
equipment
and
you
intend
it
all
to
work,
and
you
just
got
different
time
to
use.
Then
it
probably
will
work
in
the
big
bad
internet.
Maybe
you
to
couple
it
with
something
magic
like
DPL,
PMT,
UD
or
PM
tud,
or
something
to
discover
all
these
other
facets.
It
still
helps
yeah.
B
I,
just
add
to
that
I
mean
we're
not
expecting
this
to
be
the
magic
bullet
that
makes
this
perfect.
We
think
this
is
we're
trying
to
figure
out
if
this
is
a
useful
tool
that
will
help
you
know
the
transport
will
need
to
fall
back
to
whatever
information
it
can
obtain,
whether
it's
stuff
that
figures
out
or
whether
it
gets
feedback
like
this
or
you
know,
nodes
that
don't
support.
This
may
still
do
you
know,
send
ICMP
packet
to
big
messages.
All
of
that
feedback
needs
to
be
dealt
with.
M
Tell
Herbert
so
I
really
love
the
kind
of
hidden
bullet
point
there
that
we
were
going
to
do
some
experiments
to
see.
If
extension,
headers
work
over
the
intranet
again
be
fantastic.
If
we
could
have
fresher
data
than
RFC
I
think
it's
78
72,
and
not
only
that
if
you
do
this
experiment
and
I
certainly
would
volunteer
to
help.
Can
we
make
this
kind
of
ongoing
to
measure
the
progression
of
the
deployment
of
extension?
Headers
is,
hopefully
the
situation's
improving,
but
right
now
without
data
obvious,
they
were
in
the
dark
on
it.
Yeah.
O
I
E
Jenning
call
someone
who
actually
promised
to
get
you
dating
I'm
working
on
it
I'm
in
the
middle
of
the
experiment,
so
you
won't
get
some
additional
measurements
on
extension,
headers
and
so
I
like
this
again,
how
useful
it
is
we'll
see
after
we
do
some
measurements
right.
It's
really
early
to
say,
if
you,
if
you
actually
can
do
it
internet
scale,
yeah,
but
I
support
this
idea
and
I
think
here
we
need
to
run
internet
wide
like
actually
get
in
I,
don't
know
Robert
here.
Could
you
get
there?
When
we
get
the
option?
E
I
Julia
Glee
yeah,
so
I
I,
like
the
idea
of
experimentation.
I
would
like
to
see
if,
in
fact,
there
are
some
places
on
the
internet
that
you
can
pass
hop-by-hop
options
through
I
know
in
the
case
of
my
network
that,
because
those
actually
have
to
be
sent
up
to
the
control
plane,
I
will
never
see
them
because
I
can't
process
them.
So
I
know
how
that
experiment
is
going
to
go.
But
you
know
maybe
it's
possible
to
build
a
router
architecture
that
can
actually
do
that.
K
B
I
Q
We
did
this
a
few
hundred
million
times
remember.
Last
year
the
a
crate
was
bad
we're
getting
a
failure
rate
of
these
kind
of
packets
between
30
and
36
percent.
So
it's
it's!
The
it's
pretty
gloomy
out.
There
there's
an
awful
lot
of
dropping
of
extension,
headers
I've,
no
idea
why
we
are
looking
at
doing
this
on
an
ongoing
basis
for
both
UDP
for
the
DNS
and
TCP
and
we'll
put
up
a
page
or
something
and
sort
of
publish
it
more
regularly.
But
you
know
the
base
level
data
is
for
whatever
reason
deployed.
R
Detailer,
so
let's
a
assume
for
the
sake
of
argument
right
now
that
you
have
a
path
that
does
not
drop
packets
with
how
high
up
options
thanks
both
rewrite
my
understanding
of
what
your
draft
talks
about.
Is
that
if
you
don't
understand
it,
you
just
pass
it
on
right,
and
so
this
actually
does
not
discover
the
path
MTU.
This
discovers
an
upper
bound
on
it
right
because
the
hidden
node
may
have
something
lower
right.
So
it
gives
you
an
upper
bound
on
the
path,
MTU
correct
it
only
works
and
yeah.
R
It
it
provides
the
a
hint
at
the
path
MTU
in
the
same
sense
as
your
local
view,
of
your
current
link
into
you
does
right,
which
is
it's
an
upper
bound
right
now
you
observe
at
the
beginning
that
PMT
UD
has
problems
across
the
internet
and
yeah.
You
can
get
this
information.
What
are
you
gonna
use
it
for
we.
O
R
S
B
S
D
D
D
I
T
These
districts
actually
triggered
by
work
at
I,
like
your
wife,
working
with
the
IPF
guy
guys
as
int
dear
reviewer
and
IOT
trul
I
realized
that
we,
we
kind
of
needed
a
common
framework
to
understanding
to
understand
how
we
could
map
ipv6,
all
radios,
so
that
people
coming
in
with
a
particular
radio
could
actually
refer
to
that,
because
there
was
a
lot
of
ingenuity
in
in
the
way
they
approach
the
problem,
so
I
thought
I
could
write
paper
just
specific
to
IP.
Why?
T
If
I
could
just
try
to
see
if,
if
6-0
can
agree
on
on
the
various
models
that
we
could
apply
to
25gb
six
of
our
wireless,
so
I
need
to
put
this
draft
okay.
So
a
lot
of
much
time,
I
presented
that
at
six
know
many
more
slides,
so
I
just
picked
three:
that's
the
chairs
required,
and
so
it's
three
different
angles
of
the
first
bra
or
the
same
prom.
This
slide
is
all
about
the
expectation
that
people
doing
wireless
would
have
found
on
the
night
six
naval,
discovery
method
and
well.
T
There
is
quite
a
mismatch.
So
the
first
point
which
we
hurts
is
that
usually
for
most
radios,
the
medium
is
not
transitive.
It
is
usually
reflexive
do
not
necessarily
like.
If
I
can
talk
to
be.
Usually
we
can
talk
to
I.
It's
not
necessarily
true
right.
You
have
difference
of
power.
You
get
interference
on
one
side.
You've
got
lots
of
effects
that
make
me
may
make
it,
so
it's
not
reflexive,
but
most
of
the
time
it
is
what
it
is
not
is
transitive
like.
T
If
you
have
ABC
in
this
picture,
you
get
the
broadcast
domain
of
ABC.
I
can
talk
to
B,
we
can
talk
to
C,
but
I
cannot
talk
to
C.
So
if
there
is
a
dad
message,
I'll
look
up
and
it's
just
broadcasted
by
a
on
his
broadcast
domain,
then
C
will
not
be
able
to
respond.
So
that's
that's
the
basic
thing
which
appears
that
most
of
the
radios
around
with
the
exception
of
Wi-Fi,
because
Wi-Fi,
provides
a
mat
level
emulation
of
a
broadcast
domain
by
using
the
broadcast
domain
of
the
AP
as
the
reference.
T
But
even
if
you're
there
ng
again
fails
to
be
feeling
all
its
promises
and
in
particular
it
hurts
a
lot
because
of
the
the
broadcast
that
it
generates.
We've
we've
done
measures
recently.
There
was
the
Cisco
live
like
a
month
ago,
and
there
was
this
big
room
for
the
keynote.
It
was
very
well
attended.
T
Thank
you,
and
we
kind
of
measured
the
network
for
the
hour
and
a
half
of
the
keynote
and
found
that
ipv6
and
degenerated
300
messages
per
second
during
the
whole
show
averaged
300
message
per
second
broadcast
about
the
whole
thing
during
one
hour
and
a
half
think
about
the
battery
of
your
device
during
that
time.
Okay
and
that
could
have
been
completely
avoided.
If
we
add
the
method
that
we
have
deployed
at
six
low
by
the
way,
and
then
there
are
a
number
of
other
mismatches
that
appear.
T
For
instance,
there
was
a
great
effort
at
a
to
2.11
called
feels
a
totally
divine
AI,
which
is
kind
of
the
Tokyo
Station
use
case
where
you
get
200
people
or
going
out
of
trying
the
station.
They
want
instant
connectivity
and
there
was
a
lot
of
effort
at
dogeleven
to
give
them
the
almost
instant
connectivity
love
them
all
at
cetera,
give
them
access,
and
then
you
know
the
Jen's
draft.
T
T
So
that's
that's
one
angle
applying
just
ND
to
most
of
the
radios
around
now.
This
draft
is
not
specifically
about
end.
It's
about
more,
like
what
kind
of
models
we
want
to
apply
was
the
link
was
some
network
can
have
subnet?
Do
you
want
to
be
out?
Is
the
subnet
bigger
than
the
link
is
the
link
bigger
than
the
certain
nodes
it
amount
links
and
that
all
those
games?
So
we
try
to
model
that
and
provoke?
You
know
just
give
a
name
to
the
different
approaches.
An
interesting
one
is:
what
is
your
link
right?
T
A
previous
six
is
the
link
is
the
medium
for
communication
between
two
devices.
Well,
that's!
Fine!
What
do
you
mean
by
medium
is
layer,
two
major
military
of
one
medium.
If
you
look
at
your
layer,
one
medium,
that's
my
broadcast
domain
on
my
broadcast
domain.
I
can
talk,
but
I
mean
who
can
I
talk
to?
Can
I
stablish
of
point-to-point
link
right
if
I
do
that?
T
If
I
start
my
radio
in
the
morning
and
I
do
that
on
an
ipv6
link,
local
twice,
if
I
walk
all
day
with
my
radio
on,
do
I
consider
that
the
dad
I
did
in
the
morning
is
still
valid
two
hours
later,
when
I
crossed
off
of
the
world?
Probably
not
so.
He
realized
that
a
demand
on
which
I
can
assert
the
uniqueness
of
my
link.
T
Local
choice
is
probably
appear
that
I'm
talking
to
a
Deming
Claire,
meaning
that
a
link
is
probably
a
pair
of
devices,
communicating
with
one
another
that
when
they
start
assert
that
it
should
also
dress,
is
unique
from
each
other's
perspective
and
that's
how
6lo
modeled.
Actually,
the
radio
domain
doesn't
mean
that
the
subnet
is
that,
for
instance,
here
I
just
have
one
of
the
possible
model
which
is
hub
and
spoke
well
by.
T
The
router
in
the
middle
can
use
same
prefix
to
talk
prefix
be
64
can
be
used
for
a
and
C
2
for
matrices,
and
they
can
all
talk
together
as
long
as
B
exposes
the
prefix
as
not
a
link
and
realized
by
CAD
between
a
and
C.
So
the
model
that
you
are
used
to
in
in
BSS,
which
is
Wi-Fi
current
of
this,
can
completely
apply
in
the
X
news,
unfortunately
or
three.
If
you
don't
have
a
layer
to
BSS,
we
can
do
it
at
layer
3.
T
T
Last
but
not
least,
angle
of
this
discussion
is:
can
we
do
everything
that
we
want
already
with
the
method
we
have
at
layer?
3
not
exactly?
There
are
even
for
IP
wife,
even
based
on
everything
we
have
at
6lo.
There
are
still
things
which
could
be
improved,
6lo,
mostly
country,
considered
devices
that
don't
remove
a
lot
and
well.
T
So
if
you,
if
your
mobile
and
and
you
don't
even-
have
a
link
layer
method
to
detect
the
routers
you
have
around,
which
is
the
case
of
a
CB
4.11,
then
you
probably
want
to
have
new
things
that
you
do.
Income,
including
matching
the
address
with
the
router
I,
get
this
Pio
from
that
router
I'm,
using
this
source
address
I'm
using
that
router,
it's
unusual
for
Andy!
It's
not
the
right
thing.
Maybe
in
some
environments
it's
it's
pretty
much.
T
But
this
was
a
router,
speaks
every
minute,
but
I
just
heard
about
it
so
which
one
should
I
use
the
one
that
speaks
every
minute,
but
I
just
heard
all
the
one
that
tells
me
is
going
to
beacon
every
100
milliseconds,
that's
a
sort
of
logic
that
you
have
to
invent.
As
you
go
and
I
did
my
own,
like
you
know
alright
as
long
ago
when
I
did
those
experiments,
but
there
is
no
standard
for
doing
this
and
probably
the
wrong
saying
it
appear
to
work.
T
If
we
want
to
enable
model
things
like
the
scores
of
our
CV,
then
we'll
have
to
reconsider
those
things.
So
the
era
interval
that
we
have
in
mobile
IP
is
the
beginning
of
that
story
that
emulates
the
beacon,
but
then
how
you
manage
your
care
of
address
and
match
it
with
the
router.
This
is
not
described
anywhere,
so
that's
pretty
much
what
I
had
on
this
slide?
So
if
you
want
more
slides,
I
present
any
6lo,
just
download
them
from
6lo.
T
If
you
want
more
time
next
time,
I
can
go
all
the
subnet
models
and
discuss
that.
Otherwise,
there's
a
draft,
but
the
question
to
the
room
is:
is
there
interest
in
six-man
to
document
all
those
possibilities
and
those
stakes
all
right?
The
draft
is
published,
I
can
leave
it
like
that.
I
can
extend
it
tons
of
things.
I
could
write
in.
There
is
an
interest
I.
D
T
One
is
this:
one
is
more,
it's
not
on
a
track.
It's
more
informational,
like
your
things
right
you
know
here
is
how
you
could
play
with
your
radio.
Here
is
how
you
could
map
ng
with
with
traditional
ng.
You
can
do
this
with
6lowpan
ng.
You
can
do
that,
and
here
is
what
you
still
cannot
do
kind
of
it's
it's
more
this
level.
If
you
want
to
solve
anything,
I,
don't
expect
it
to
be
this
draft
right.
H
This
draft
is
sort
of
like
not
even
almost
about
restarting
work,
I
think
it's
there's
a
good
summary
of
things
that
have
been
done
in
the
past
and
then
different
link
layers
and
and
what
the
underlying
semantics
of
the
links
are
and
what
you
can
do
with
them.
It's
it's
heavily
biased
towards
what
was
done
already,
and
it's
sort
of
a
little
bit
biased
against,
like
classic,
can
be
there's
a
few
sort
of
like
we
recommend
this
and
we
recommend
that
which
doesn't
really
belong
in
informational,
but
I.
H
Think
as
a
document
itself
is
actually
useful
too,
because
it
presents
its
relatively
neutral
and
it
presents
like
a
lot
of
the
trade-offs
that
were
made,
but
it
I
don't
know
that.
It's
something
that,
though
we
need
to
work
on
it's
sort
of
like
it's
almost
complete,
as
is
right,
I,
wonder
if
it
just
should
be.
H
T
T
This
one
is
not
a
six-month
rush,
but
they
don't
know
where
it
should
it
should
live.
Actually
we
asked
the
question
at
six
low
on
the
the
sense
of
the
room
and
of
the
ad,
if
I
thought,
if
I
remember
well,
was
that
it
would
be
better
at
six
at
six
men
and
six
low.
So
this
is
the
logical
continuation
of
the
world
that
happened
at
six
low.
The
world
that
happen
at
six
low
was
really
looking
at
the
world
side
trying
to
optimize
the
multicast.
T
But
we
realized
that
probably
are
some
of
those
aspect
that
we
could
actually
port
it
to
a
more
general
news
age.
So
what
do
we
try
to
address
here?
The
first
thing
we
try
to
address
is
the
scalability
of
a
ninety
six
subnet
and
if
you
rely
on
multi-level
emulation
of
a
broadcast
domain
of
our
large
fabric,
well
that
that's
fine
on
the
limited
Ethernet
switch
fabric.
If
you
have
a
lot
of
wireless
edge,
it's
already
starts
to
work.
T
If
you
distribute
your
layer
to
fabric
of
a
layer,
three
multiple
data
centers
that
really
hurts
a
lot.
What
we
do
in
those
networks
is
we
build
overlays
and
we
want
to
resolve
the
other
hand
of
the
tunnel.
We
don't
want
to
have
to
broadcast
anything.
It
happens
that
today,
with
outcome
fabric,
we
still
do
have
to
do
broadcast
because
our
cases
where
we
don't
resolve
the
tree
hurts.
T
So
what
we
would
like
to
do
is
do
our
solution
through
a
mapping
server,
most
of
them
in
pure
unicast
and
avoid
the
the
broadcast
so
today,
my
cup
initial
solution
based
on
Lisp,
to
do
that.
So
we
have
this
map
server.
My
preserver
and
you
can
create
with
Lisp,
and
if
you
do
that,
then
you
can
save
a
lookup.
You
can
save
the
broadcast
on
your
fabric,
but
what
we
don't
have
is
a
generic
way
of
doing
that
through
the
most
logical
way,
which
is
neighbor
discovery.
T
So
the
idea
behind
this
draft
is
pretty
much
to
say
a.
We
already
have
this
in
six
low,
the
software
registrar,
where
we
list
all
the
addresses
in
the
in
the
network
that
were
registered.
That's
how
we
do
that
over
multiple
routers
in
a
big
fabric.
Why
don't
we
just
look
at
this
thing
using
the
same
ng
methods,
so
you
could
use
to
the
draft
purposes.
Just
then,
let's
look
up,
but
you
send
it
unique
as
to
this
guy.
T
It's
the
first
thing
you
can
do
or
if,
if
it's
actually
not
on
your
broadcast
link
like
if
you're
on
a
wireless
Wi-Fi-
and
we
do
this
backbone,
router
game
and
the
proxy
which
is
actually
recommended
by
Wi-Fi,
then
you
will
have
make
a
packet.
That
goes
multiple
hops,
because
you
have
to
go
to
the
router
or
it's
different
links.
You
have
a
backbone
link
which
is
represented
on
the
right
here
by
this
Ethernet
backbone,
and
you
have
the
wireless
link
and
there
are
two
different
links
like
it's:
an
S
and
literally
news,
multi-link
subnet.
T
So
if
you
live
in
a
world
like
this,
then
the
database
is
not
on
your
link.
It's
on
on
the
broadcast
domain
on
the
ethernet,
meaning
that
you
need
a
packet
which
goes
multiple
hops,
which
is
what
six
laws
provided
anyway.
So
what
the
drafters
mostly
is
take
the
six
low
signaling,
which
can
go
multiple
hop,
which
is
called
dag
duplicate.
That
was
request.
If
you
get
address
confirm-
and
this
tended
to
do
a
lookup.
So
now
we
have
a
new
code
same
ICMP
code
right,
we
don't
serve
as
a
p-type.
T
We
don't
go
beyond
the
user
new
ICMP
type,
but
we
have
code
and
sub
code
in
there,
and
so
we
just
take
in
that
space
and
allow
this
multi-hop
message
to
be
a
lookup,
as
opposed
to
just
that
request.
That's
pretty
much
what
the
message
says:
ten
minutes!
Okay,
one
one
on
this
slide!
Wouldn't
next!
So
this
is
just
giving
you
an
example.
So
all
the
six
low
drafts,
basically,
which
talk
about
the
backbone,
are
really
meant
to
coexist.
T
It
doesn't
mean
that
you
have
to
have
either
the
broadcast
games,
the
old
ng
or
six
low
nd.
You
can
have
both
at
the
same
time
it's
romantic
coexist.
There
is
what
would
happen
in
the
fields
use
case,
no
a
to
deliver
the
I,
where
all
those
hundreds
of
people
jump
out
of
the
Train,
so
any
of
those
guys
would
basically
send
an
arrest
to
locate
the
router.
It's
it's
supposed
to
be
a
multicast.
T
But
since
the
access
point
is
a
router
and
the
access
point
is
the
one
that
that's
a
real
broadcast
it
to
just
will
not
do
that
because
it's
a
router,
so
it
will
just
intercept
the
errors
and
the
rest
will
never
be
broadcasted
on
the
otherwise
network.
Then
it
will
answer.
Unicast
arise,
that's
immediate,
and
even
so
the
now
the
6ln
cannot
take
off
from
the
truss
as
many
as
it
likes
and
it
registers
them
to
the
6lb
arm,
which
means
that
we
pre
populate
the
nd
cache.
T
T
The
register
writes
it
down
on
the
central
registry,
and
now
we
can
do
optimistic
that
pretty
much
that's
what's
happening
here,
so
the
the
whole
sent
well
also
on
the
articles
as
a
proxy
centenares
to
the
router
without
a
sale
ago,
because
that's
what
add,
the
router
looks
wants
to
outside
unicast,
so
it
sends
an
S
and
I
and
and
that's
how
the
router
gets
populated
and
now
in
optimistic
mode,
the
ipv6
packets
can
start
right
over.
So
you
don't
have
any
deal,
I,
just
a
few
exchanges,
and
then
you
go.
T
You
can
start
exchanging
your
data
so
that
that's
pretty
much
what
we
can
do
in
ipv6.
To
finish
what
the
Dutch
Levin
AI
group
does
grow
started
at
a
to
that
sea
level,
and
that's
pretty
much
my
talk.
So
we
put
the
central
registrar
that
we
already
have.
Anyway,
we
give
an
NG
interface
to
it
so
that
any
host
can
register
to
it
and
the
most
most
host
register
to
it.
The
last
podcast
you'll
get
doing.
Okay,
that's
pretty
much!
What
you
have
super.
