►
From YouTube: IETF105-SIDROPS-20190723-1520
Description
SIDROPS meeting session at IETF105
2019/07/23 1520
https://datatracker.ietf.org/meeting/105/proceedings/
A
B
A
A
A
G
G
G
G
H
G
The
only
other
half
the
internet
we
care
about.
Yes,
why
don't
we
do
that
as
soon
as
mr.
Bush
is
done
with
his
time?
Fantastic.
Thank
you.
Thank
you
very
much.
Okay.
We
have
these
four
other
presenters
and
mr.
mandersohn
will
be
a
little
squeezed
on
time.
I
think
so
everybody
should
keep
it
short
draft
status
as
it
says
the
documentation.
All
these
slides
by
the
way
are
in
the
meeting
material.
So
you
can
go
down
to
that
and
could
go
to
town.
G
J
Not
smile,
slides,
oh
this
is
my
slits
okay,
my
name
is
a
reason.
Does
enough
work
for
Yandex
and
today
I'm
going
to
provide
you
a
very
short
update
on
his
PA
trots,
so
just
to
quickly
remind
remind
you
what
our
ASP,
so
this
day
is
also
a
system
provider
authorization
so
but
it's
P
is
much
shorter,
so
it's
a
new
application
object--
then
it
can
be
used
to
detect
leaks
and
hijacks,
malicious
and
mistakes.
J
J
J
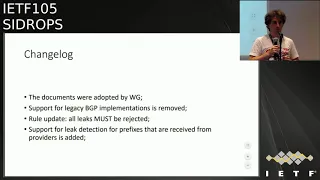
Here
is
the
change
log.
First
of
all,
good
news.
The
drafts
were
adopted
by
these
working
group
and
I
hope
that
it
will
boost
the
process
of
working
on
this
document,
and
it
seems
this.
I
was
right
so
since
recent
discussion,
in
the
main
at
least,
was
quite
fruitful,
and
previously
we
were
stated
that
SBA
can
be
used
to
verify
ice
paths
that
are
received
from
customers
and
peers.
So
now
we
have
extended
the
way
SP
can
be
used,
and
so
you
can
now
also
verify
paths
that
are
received
from
customers.
J
So
there
is
a
some
text
there,
I,
which
I
will
go
over
with
youth,
and
so
it
will
not
look
such
complicated.
So
if
s
speaking
about
the
prefixes
that
I
received
from
customer
or
by
customer
from
provider
or
exam
from
Ike's,
it
may
have
to
subpaths
the
down
the
upstream
part
when
prefix
is
traveling
from
customer
to
provide
and
so
on
so
on
and
downstream
path,
when
prefix
is
traveling
down
from
provider
to
customer
and
so
on,
the
connection
can
be
a
single
autonomous
system
number.
J
It
can
be
appearing
link,
it
can
be
a
transparent
eyes,
but
anyway,
the
first
downstream
link
will
will
have
invalid
outcome
according
to
ASP
a
verification
procedure.
So
in
this
exact
example,
example,
r3
is
leaking
as
one
is
taking.
Transit
from
ice
to
s3,
taking
transit
from
both
eyes
to
and
I
is
for
ice
five
straight,
a
contrasting
from
ice
form,
so
I
hope
it
will
be
clear.
J
So,
according
to
his
be
verification
procedure,
the
outcome
from
verification
of
ice
2
and
R
3
is
invalid.
As
soon
as
we
are
going
through.
First
downstream
link,
all
concern
downstream
leaks.
The
links
that
we
can
find
after
that
in
the
path
will
must
be
also
provided
to
customers.
Otherwise,
it's
a
leak
so
to
verify
this,
but
we
found
that
is
to
in
ice.
J
There
is
a
sequence
which
goes
up
so
it
surrounded
so
I
understand
it
may
sound
a
bit
difficult,
but
in
reality
it's
a
very
easy
to
code
and
I
have
already
already
dropped
a
piece
of
code
in
the
main,
at
least
you
can
take
a
look
at
it,
so
maybe
in
words
it's
harder
to
understand,
then
in
the
piece
of
code.
So
the
second
thing
is
universe
policy
for
anomalies.
J
Previously
we
try
to
treat
different
layer,
hijacks
and
root
leaks.
We
had
good
intent.
We
believed
that
it's
in
some
cases,
root
leaks,
may
pass
by,
because
maybe
it's
a
good
thing,
maybe
it's
the
only
path
to
the
originator,
but
since
we're
talking
not
only
about
mistakes,
we're
also
talking
about
forged
a
cubes
of
the
malicious
activity.
J
The
receiver
cannot
distinguish
if
it
was,
it
is
receiving
a
prefix
that
was
leaked
by
a
mistake
or
if
it's
a
receiving
F
forged
eyes
party,
which
is
a
hijack
but
I
spats.
Most
of
us
modified
to
look
like
a
leak.
So
with
this
in
mind,
we
we
cannot
distinguish
leaks
and
ice
and
hijacks
from
the
receiver
side,
and
the
only
policy
that
can
be
applicable
here
is
draw
all
anomalies
that
can
be
detected
with
ASP.
J
J
E
J
A
good
question:
it's
a
my
question
to
you
to
the
working
group
so
because
it's
for
a
proper
ice
path
of
diversification,
we
cannot
verify
hiset
segments
because
they
are
unordered
and
if
we
want
to
get
rid
of
malicious
activity
that
may
happen
in
BGP,
we
need
to
get
rid
of
Isis
and
that's
why
it's
here
and
that's.
Why
I'm
like
to
another
to
learn,
what's
happening
with
this
draft
and
if
there
is
anybody
willing
to
push
it
forward
to
finally
get
reach
of
the
highest
sets?
B
I
mean
that's
been
sitting
around
for
a
long
time.
That
document
and
mainly
Shri
Rama,
had
been
bumping.
The
version
number
every
now
and
then
what
we
decided
at
some
point
was,
and
Randy
and
I
had
started
working
on
this
and
then
I
got
sidetracked
again,
but
we'd
started
another
document
which
deprecates
ASX
and
atomic
aggregate
from
BGP
v4.
We
hadn't
hadn't
actually
got
as
far
as
publishing
a
version
of
that,
but
that
seemed
like
would
be
a
much
better
thing
to
actually
do.
It
turns
out
doing
that
requires
all
sorts
of
updates
to
BGP.
B
B
L
J
M
Nothing
else
happens
as
far
as
I
can
tell.
The
interesting
construct
only
occurs
at
the
very
end
of
a
path
you're
speaking
about
this
thing.
No,
no,
no,
no,
no,
no!
The
is
set,
and
the
way
it
usually
is
constructed
is
not
relevant
here
at
all,
and
if
nothing
else
happens,
one
would
need
to
check
that.
Yes,
it
only
can
happen
at
the
end,
and
then
you
could
essentially
just
use
the
regular
path,
for
whatever
is
happening
here.
M
J
M
M
The
complex
asn.1
use
typically
typically
confuses
people
who
don't
need
to
work
with
it,
and
I
think
I
think
that
the
conceptual
data
structure
that
is
transmitted
there
and
what
what
it's
supposed
semantics
are,
could
be
exposed
much
better
and
I
somewhat
assume
actually
the
structure
will,
after
the
will,
the
the
encoding
might
actually
change
to
adapt
it
closer
to
a
concept.
That's
being
that's
being
used,
are
you
speaking
about?
Is
zero,
no
yeah?
Well,
okay,
what
what
is
the
concept
that
is
being
used?
M
J
M
J
J
M
Making
people
understand
what
they
are
supposed
to
do
and
why
things
work
well
kind
of
coding.
Complications
can
be
an
obstacle,
and
yes,
I
also
I
also
have
another
now
unhidden
agenda.
If
we
actually
are
coding
sets
of
a
SS.
That
means
that,
during
the
time
the
standard
is
de
is
being
developed
and
codes.
An
implementation
and
deployment
follows
over
a
couple
of
months.
M
J
M
The
issue
here
is
much
less
the
coding
which
may
be
slightly
easier
or
while,
okay,
it
doesn't
matter
and
I
completely
agree
that,
yes
completely
hand
coding
stuff
is
out
of
the
question,
but
making
making
the
concept
that
is
used
transparent
to
users
actually
actually
is
valuable,
because
ok,
of
course,
with
a
little
bit
of
coding,
the
user
interface
can
also
present
concepts
that
are
kind
of
hidden
in
what's
happening
underneath.
But
that
does
not.
That
does
not
really
help.
J
O
J
We're
speaking
about
protection
against
malicious
activity,
approached
I
said
in
the
middle
of
the
path,
just
nibble
eighths
all
kinds
of
protection,
because
it
will
end
up
that
you
are
able
to
create
a
forged
ice
bath
in
certain
situations.
So
at
the
moment
the
draft
suggests
to
treat
pass
with
ice
set
like
it
sweets,
hijacks
and
leagues.
All.
O
So,
in
my
understanding
the
semantics
here
are
similar
to
what
you
have
an
origin
validation
in
the
sense
that
you
would
argue
to
drop
in
ballots.
So
if
there's
anything
verifiably
invalid,
but
when
things
are
unknown,
that's!
Okay!
Yes,
right!
Okay,
because
the
text
in
the
document
seemed
to
say
something
about
treating
unverifiable
things
with
some
suspicion
and
I'm,
not
sure
that
that's
right.
J
There
is
difference
between
unverifiable
and
unknown,
and
verifiable
is
exactly
introduced
for
Isis.
Well,
unknown
is
for
ice
baths,
so
the
ice
bath
even
returns.
I
think
well,
it's
in
case
of
so
there
is
a
purification.
There
is
three
outcomes
valid
invalid
unknown
for
ice
bath,
verification
procedure.
It
should
be
valid
invalid
and
algorithm,
so
the
unknown
will
be
wedded
right.
Okay,
that
clarifies
thank
you
so
I
think
if
I
come
to,
I
will
check
that
it
is
clearly
stated
and.
O
O
What
I'm
look
for
what
I'm
thinking
of
as
a
missus
a
year?
If
there's
an
SMAS
I
make
a
statement?
Maybe
I
run
one
object
signed
by
a
yes
that
has
everything
in
it
to
ensure
that
I
see
the
complete
policy,
that's
applicable
here
and
not
risk
that
there
are
issues
with
a
bunch
of
objects
where
some
of
them
are
being
published
and
withdrawn,
and
so
that
may
be
something
to
think
about,
because.
O
J
O
So
what
I'm
implying
is
that
as
AAS
who
is
signing
I
could
put
all
those
statements
on
a
single
object.
So
there's
no
risk
that
when
I
publish
things
you
miss
things
because
you
know
it's
still
being
processed
and
it's
partially
published
itself.
So
it's
not
a
big
deal,
but
you
know
maybe
something
to
think
about.
Okay,.
P
P
It's
deprecated,
but
I
actually
don't
even
understand
how,
if
I'm
signing
all
my
adjacencies,
how
I
can
sign
myself
as
adjacent
and
is
set
within
your
construct
and
maybe
that
just
simply
finesses
out
the
entire
issue
of
ASAS,
because
I
can't
be
adjacent
to
one
unless
a
whole
bunch
of
other
work
is
done
to
define
what
I'm
adjacent
to
so,
if
I
sign
all
my
adjacencies
and
you
see
a
park
with
me
adjacent
to
one
of
these,
a
assets
I
think
that's
a
dud.
You
know
straight
away.
Thanks.
J
J
P
Just
doesn't
matter
I'm
like
you're,
inside
an
environment
where,
when
maybe
you
get
a
path
until
you
reach
some
gold
and
healthy
and
day,
that's
never
going
to
happen
that
everyone
signs
stuff,
you're
gonna,
have
to
do
partials,
yeah
and
if
you're
doing
partials
no
one's
going
to
be
incorporating.
If
I'm,
if
I
do
my
signing,
I'm
never
adjacent
to
a
set,
the
problem
just
goes
away.
That's
what
I'm
suggesting
Chris
you
can
have
the
time
I'm.
Q
Quick
Chad
much
Akamai
I,
don't
know
how
many
ASI
Jason
sees
I.
Have
it's
actually
an
unknown?
It's
an
unanswerable
question
for
me.
So
I
I,
don't
know.
I
wouldn't
even
have
a
way
to
sign
something
to
say
who
I
chase
it
with
because
I
fear
with
things
like
route
servers,
so
I
have
very
many
unknown
es
adjacencies,
just
for
my
backbone,
a
s
but
how
many
upstream.
J
Not
trying
to
define
complex
business
relations,
the
only
thing
that
a
speii
does
is,
if
you
create
a
record,
you
are
just
be
meeting
what
is
called
provider
to
send
your
prefixes
to
up
streams
or
peers,
and
so
on.
You
are
free,
for
example,
not
to
pay
me
to
one
of
your
providers
to
send
prefixes.
You
can
do
it,
it's
it's
up
to
you.
J
G
R
S
I
would
like
to
present
to
you
our
draft
again.
I
have
been
at
the
last
ITF
meeting
at
Prague,
so
this
time
I
will
give
you
an
update,
and
we
would
like
to
go
for
last
call
soon
to
finish
this
draft.
So
this
is
about
how
to
use
rpki
validation
at
route
servers
and
how
to
forward
the
result
to
the
peers.
S
The
motivation
for
this
draft
was
basically
to
have
something
like
our
C
1897,
which
says
how
to
forward
época
validation
results
in
interior
PGP.
So
at
X
piece
we
have
some
kind
of
similar
situation.
We
run
kind
of
a
more
trusted
environment
to
the
peers
and
it's
natural
for
ex
piece
to
forward
some
information
with
with
routes,
for
example,
where
the
route
has
been
learned
from
how
far
like.
S
So,
just
to
get
a
picture
on
how
it
works.
Some
of
you
already
know
it.
We
get
an
prefix
from,
for
example,
a
SD
that
goes
into
a
route
server.
There
are
servers
doing
all
its
usual
checks.
Also
doing
our
D
check,
see
if
the
prefixes
valid
for
the
a
s.
If
it's
an
is
a
a
set
and
additionally
this
time
it
will
also
do
our
PK
validation.
Then
it
can
have
different
modes.
S
For
example,
it
can
drop
the
prefix
right
away
or
it
can
just
forward
the
prefixes
and
take
the
state
the
result
of
the
state
onto
the
route
to
the
to
the
neighbors,
and
then
it
should
go
to
the
neighbors,
but
the
neighbors
shouldn't
redistribute
this
to
others.
It's
just
the
idea
to
have
this
at
the
domain
of
the
IXP.
S
So
technically
we
now
changed
from
an
extended
community
to
a
large
community,
because
this
has
been
feedback
from
the
last
ITF
meeting
and
it's
now
our
standard.
So
basically
it
would
be.
We
would
have
the
habilitation
status
at
the
last
field,
which
would
be
like
zero
for
if
it's
a
valid
prefix
one,
if
it's
not
found
it's
unknown
or
two.
If
it's
an
invalid
prefix,
we
would
also
have
the
function
of
function.
S
The
first
node
would
be
to
just
tag
the
result
that
routes
of
a
processed
on
to
order
out
and
distributed
to
the
peers.
The
second
mode
of
operation
would
be
to
drop
all
invalid
prefixes
and
just
forward
valid
ones
and
unknowns.
So
this
would
be
now
the
default
mode
of
operation
and
is
basically
like
what
is
done
today
at
severai
expand.
The
third
mode
would
be
to
to
drop
prefixes
with
invalid
and
unknown,
but
basically
do
the
best
path.
Selection,
after
dead
saw
that
valid
routes
would
remain
like
on
top
of
all
errors.
S
Operational
recommendations
in
the
draft
is
that
peers
that
receive
the
result
should
not
redistribute
it
to
a
DA
is
ends.
If
a
route
server
is
receiving
such
a
community
from
from
a
peer,
it
should
strip
it
so
that
it
will
not
redistribute.
Other
checks
then
was
also
common.
Is
that
if
the
very
origin
relation
fails
at
a
route
server,
the
community
should
be
admitted
there
should
be
no
community,
and
then,
if
there's,
multiple
validation
results
for
appear,
if
it
receives
multiple
validation
results,
the
validation
was
art
with
the
highest
values
should
be
should
be
taken.
S
That
would
be
two
for
invalid,
for
example.
So
it's
the
most
secure
way
to
do
it.
So
comments
from
the
last
meeting
have
been
that
we
shouldn't,
or
there
should
be,
a
mechanism
to
a
signal
if
the
validation
could
be
performed
throughout
server,
and
we
have
this
now
and
operational
recommendations
to
admit
the
community
tech
at
the
route
server.
Then
one
comment
was
that
the
draft
has
been
overtaken
by
reality,
which
means
that
now
more
and
more
XP
s
already
drop
in
billets,
but
I
see
it
like
this.
S
You
can't
just
see
that
you
don't
see
it
on
your
router,
but
you
see
that
internally
there
are
servers
already
using
these
communities.
Then
we
had
a
discussion
about
extended
and
large
communities
we
now
resided
in
favor
for
large
communities.
There
was
always
the
concern
of
outsourcing
security.
That
means
that
you
are
giving
like
the
security.
There
is
a
decision
to
the
route
server,
but
this
is
some
some
trade-off
that
appears
doing
anyway.
S
T
G
T
F
G
Think
that's
I
think
Doug.
Your
point
is
that
as
the
data
and
the
RPI
is
changing
over
time,
I
may
choose
to
validate.
I
may
choose
to
authorize
you
to
do
this
route
today
and
job
tomorrow
and
not
you
tomorrow,
and
if
the
data
at
the
to
different
route
servers
is
in
a
state
where
one
has
the
old
data
you
and
the
other
one
has
the
good
the
new
data
job
I.
Certainly
don't
want
to
accept
the
route
with
you
in
it
anymore.
Can.
U
I
injecting
sense
or
abortionist.
We
made
an
awful
lot
of
tests
last
year
about
that
and
you
can
have
the
following
situation:
let's
assume
you
have
a
route
on
the
East
Coast
and
you
have
a
router
on
the
west
coast
and
they
exchange
their
data
and
they
have
the
same
path.
Those
who
have
two
different
validation,
caches,
I,
don't
know
which
of
the
validation
cache
has
more
up-to-date
data.
It
might
be
that
the
one
that
resorts
a
novella
is
more
up-to-date
than
the
one
that
has
the
other
result.
U
E
You
job
Snyder's
and
CT
in
the
case
of
failure
in
the
original
foundation
process.
For
instance,
how
do
you?
How
do
you
define
failure
of
the
original
foundation
process
because,
for
instance,
if
the
cache
is
empty
policy
will
dictate
that
all
of
them
become
unknown
and
then
omitting?
The
community
is
a
force
signal
in
this
conflict
that
contradicts
with
what
we
understand
that
unknowns
are
or
not
found.
E
So
we
cannot
differentiate,
I,
think
between
a
failure
in
the
urgent
validation
process
or
the
absence
of
a
validation
process.
Yeah
I
see
this
problem
as
well
and
then
a
second
comment.
If
the
default
is
to
reject
invalids,
maybe
you
should
remove
the
well-known
invalids
community
and
then
only
two
communities
are
left
the
unknowns
and
valid,
and
at
that
point
I
kind
of
wonder
what
the
use
case
is
because
I
I
think
it's
not
very
valuable
and
you
should
reconsider
the
words
that
we
can
trust
each
other
at
an
internet
exchange.
K
John
Scudder,
now
that
you
explained
what
the
last
bullet
means,
I
would
like
to
agree
with
rüdiger
that
one
route
has
one
validation
state.
It
doesn't
make
sense
to
talk
about
having
multiple
validation
states
for
a
route
and
as
as
I
understand,
I
have
I
would
need
to
go
and
I
haven't
looked
at
this
version
of
the
draft,
so
I
don't
know
what
the
normative
language
is,
but
it
sounds
to
me
like
that
should
just
be
removed
because
it
doesn't
make
sense
to
say
their
route
has
two
different
validations
days.
V
Randy
push
hi
Jamarcus,
oh
I
have
problems
with
the
trust
nozzle
also,
but
that's
been
beaten
to
death.
Why
you
switched,
which
tomorrow
day,
confuses
me,
we
already
have
a
well,
then
one
and
Burton
Lee,
not
well-known
one,
but
a
well-defined
one,
but
basically,
as
you'll
see
the
real
problem,
that's
expressed
in
the
original
validation
signaling
graph,
which
you'll
get
to
hear
about
boringly
later.
Is
that
saying
the
community
gets
to
my
router,
but
then
what
they're
like
German,
if
it's
invalid?
S
Yeah,
the
community
was
changed
because
of
the
comments
from
the
last
meeting,
so
I
understood
that
this
is
the
right
way
to
go
and
the
default
thing
that
is
also
done
at
route
servers,
so
otherwise
I
understood
that
if
we
want
to
have
extended
communities
like
it's
done
with
the
ibgp
draft,
you
have
to
implement
all
the
policies
and
we
have
to
wait
like
10
years
so
yeah
we
thought.
Is
this
the
way
to
go.
O
Yeah
all
right,
yeah,
Tim
Burgess,
and
on
that
laughs,
I'm
going
to
talk
about
this
graph,
which
is
actually
not
a
last
call
as
far
as
I
know,
but
it
is
on
the
Status
pages.
I
think
that's
because
HDS
intell's
was
in
law
school.
So
it
would
be
nice
to
rectify
that
because
this
is
not
finished
so
goals
still.
This
is
similar
to
the
slide
deck.
O
After
that
it
presented
two
meetings
ago,
where
I
said,
shall
we
call
it
done,
but
still
no
dome
and
I'll
get
back
to
that
in
a
bit
actually,
but
let's
first
look
at
the
goals,
so
we
want
to
allow
for
key
roles
in
the
RPI.
There
are
many
reasons
why,
but
this
might
be
useful.
I
used
to
work
for
write
and
CC
where
I
was
operating
a
trust
anchor
and
we
have
done
the
lock-in
which
regards
to
an
HSM.
So
that's
just
one
of
the
reasons
why
this
might
be
useful
for
relying
parties.
O
It's
important
to
learn
about
these
things.
Currently,
there's
no
way,
except
for
somehow
offline
in
learning
about
a
new
trust,
anchor
locator
and
including
it.
Maybe
when
you
update
or
your
implementation,
you
get
a
new
tell
with
that
update,
but
it's
not
very
well
defined,
so
we
also
want
to
learn
from
experience
in
the
DNS
we
like
to
have
a
way
for
this
to
be
done,
that
you
know,
lands
well
into
the
existing
standards,
so
it
works
well
with,
what's
out
there.
O
Finally,
leave
it's
real
for
our
data
clients.
What
I
mean
by
that
is
that
if
you
have
a
piece
of
software
that
has
aids
for
sync
on
locator
in
its
so
that's,
it
would
be
the
way
your
your
relying
party
tool
finds
the
current
certificate.
Well,
if
that's
our
data,
it
would
be
very
nice
that
you
can
follow
a
trail
to
the
current
set
up
thrust
anchors
that
should
be
applicable.
O
O
No
yeah,
okay,
great
well
I,
will
go
through
the
phases
here
on
this,
my
deck
as
well
actually,
but
they
try
to
make
the
document
a
bit
more
clear,
but
regards
to
what's
going
on,
I
mean
we're
starting
from
a
situation,
but
none
of
this
is
applicable.
How
do
you
start
use
this,
and
how
do
you
then
do
it
use
it
to
make
a
a
role
in
a
plan
direction?
How
do
you
use
it
to
make
a
role
in
long
blimp
plans
of
direction?
O
That's
it
and,
as
mentioned
back
in
Singapore
as
well,
the
draft
now
uses
distinct
your
eyes
for
where
you
can
retrieve
the
TA
certificates
in
an
attempts
to
help
figure
out
how
many
people
are
actually
learning
about
this
stuff
and
how
many
people
support
the
standard
if
it
becomes
wrong
now
the
objects.
This
is
say
someone.
This
may
be
bit
painful
for
people,
but
essentially
it
says
that
there
has
to
be
one
or
more
current
keys.
O
O
Current
situation,
you
have
none
of
this
right.
You
have
the
trust
and
can
locate
a
faulty,
a
text
file.
It
contains
a
bunch
of
your
eyes
and
the
the
subject
of
key
info
of
a
tracker
certificate.
So
relying
party
uses
that
to
fetch
a
certificate
verifies
it,
and
it
goes
off
a
way
to
introduce
this
in
the
phase.
O
One
let's
say
is
at
a
or
what
we
call
a
tech
foul
to
confuse
tall,
UNTAC,
less
I
suppose
where
a
signed
object
has
a
reference,
a
URI
to
a
location
where
that's
ranked
a
certificate
is
signed
and
the
same
subject:
public
info
now,
when
a
relying
party
two
runs,
they
will
encounter
this
and
the
text
in
the
document.
Can
he
says
or
when
you
learn
about
these
signed
statements,
you
should
use
the
information
in
there
to
replace
what
ya
had
obtained
earlier
from
the
clear
text
value
were
using
now.
O
If
you
used
different
your
eyes
for
both
them
as
an
operator,
you
can
learn
where
people
fetch
things,
so
you
can
also
understand
somehow
how
many
people
would
be
able
to.
You
know,
follow
its
rail,
let's
say
so.
That's
the
more
significant
change,
I
think
in
this
version
of
the
document.
If
you
go
on,
though
o
completeness,
you
can
then
add
a
new
key
have
new
tag
files
as
a
call
referencing,
both
keys.
You
could
have
tell
files
for
both
entry
points.
O
You
can
roll
to
a
third
key
and
revoke
the
first
one
off
all
the
wrongs
in
here
and
I'm,
not
sure
that
I
yeah,
we
can
have
a
discussion
about
this.
You
will
want,
but
I
did
present
this
before.
Let
me
take
away
here
is
that
I
can
revoke
that
first
key
on
the
tech
file
over
the
second
I.
Don't
need
to
do
that
on
the
third,
because
people
who
learn
about
the
third
key
will
have
already
learned
about
the
verification
of
the
first
by
looking
at
a
second,
the
reason:
that's
that
complication
is.
O
O
The
document
actually
distinguishes
two
ways
here:
you
could
say:
okay,
we
want
to
revoke
he
one,
so
a
TA
here
or
you
could
say
well,
actually,
the
one
that
we
just
introduced
is
no
longer
good
and
it
would
technically
look
the
same
from
a
a
blind
party
point
of
view.
Both
current
keys
are
just
treated
equally
as
current,
essentially
and
either
key
can
revoke
all
the
others.
Now
the
documents
actually
allows
for
any
number
of
keys,
and
this
is
another
question
I
think
I
have
for
the
group
as
well.
O
Well,
that
leaves
the
the
makes
a
document
flexible,
I
think
it
also
makes
it
more
complicated
and
strictly
necessary
if
we
could
constrain
this
to
scenarios
where
you
only
have
ever
have
two
keys.
That
might
may
make
things
a
lot
simpler,
so
that
may
be
well
worth
it
now.
Then,
what's
next
well,
well
other
ways
that
I
thought
I
included
something,
but
no
it's
in
my
mind,
actually
wanna
do
real
proof
of
concepts.
O
Work
on
this
and
I
happened
to
do
that
earlier,
but
I
didn't
get
around
to
it,
I'm
still
busy
with
some
other
things
but
arenal
to
get
there
because
I
don't
feel
confident.
You
know
going
asking
for
law
school
on
this.
Unless
I
have
running
code.
That
proves
that
okay,
we
can
do
a
roll.
We
can
do
a
roll
where
we
went
on
with
our
intent.
We
do
overall,
where
we
figured
no
distant
key,
is
no
longer
good
and
I
want
to
verify
that
you
know
following
it.
Phil
actually
works.
O
So,
even
though
it
takes
longer
I
would
rather,
you
know,
do
it
well,
then
rush
it
and
I'm
not
entirely
sure
that
I
can
form
as
when
I'll
get
to
it.
But
you
know
say
it
is
update.
That's
where
I
want
to
go
so
question
to
the
chairs.
I
suppose
would
be
please
get
rid
of
the
status
last
call
because
I
don't
think
it's
there
and
to
anybody
else.
I
mean
if
you
have
comments.
Ideas
concerns,
like
you
know.
O
W
Hey
Eric,
Australia,
coach,
Mason,
University,
so
I
think
this
is
really
good.
I,
really
like
the
approach
you've
taken
and
also
the
fact
that
you're
highlighting
a
problem
that
I
think
exists
in
DNS
SEC,
among
other
places,
where
understanding
what
a
key
role
is
is
proving
to
be
very
difficult,
because
it
wasn't
very
clear
when
the
protocol
is
designed.
That
key
role
is
a
really
a
big
thing.
It's
more
than
just
sticking
a
key
out
there
using
it
and
then
seeking
a
new
key
out
there
and
using
it.
W
You
know
they
actually
wind
up
having
a
relationship
to
each
other
after
they've
been
cycled
out
and
whether
they're
still
valid
they
become
replay,
vulnerabilities,
I.
Think
there's
a
lot
of
like
thinking
through.
Are
you
rolling
forward
or
you're
rolling
backward?
And
how
do
you
actually
represent
that
that
I
think
you
I,
like
the
fact
that
you're
going
to
do
a
lot
of
analysis?
W
V
X
X
Bravo
Stein
arcus
to
your
question
about
without
you
can
simplify
but
getting
rid
of
some
of
those
infinite
light
sequences
given
you're
talking
about
prototyping
at
first,
which
I
think
is
a
highly
advisable
thing
li,
but
it's
open-ended
sequences
for
now
and
if
it
turns
out
you
don't
actually
need
all
those
slots,
then
you
turn
them
because
we've
been
seeing
all
kinds
of
entertaining
things
lately
with
people's
pushing
things
that
were
not
envisioned
as
more
than
three
entries
up
to
ten
thousand.
Let's
see
what
happens.
Y
Marcin
iris
and
she
she,
the
dutch
one-
that's
so
you
just
talked
about
keys
being
able
to
revoke
other
keys
and
what
that's
your
security
conservation
says
that
currently
any
key
can
revoke
any
other
key.
So
I
was
thinking
about
this
too,
and
I'm
wondering
if
you
want
to
roll
a
key,
because
you
are
not
sure
that
it's
safe
anymore,
for
example,
that's
the
property
you're
looking
for,
and
I
don't
know
what
the
property
is,
that
you're
looking
for
but
yeah.
This
basically
made
me
question
how
that
that
works.
Y
So
in
the
I
noted
in
the
last
working
group
that
they
tried
to
get
some
of
the
academic,
formal
proof
groups,
look
at
some
parts
of
the
protocol,
I'm
wondering
if
that's
useful,
to
be
trying
to
do
here
with
the
the
P
key
a
bit
to
try
and
understand
if
the
property
here
looking
for
are
provided
by
the
functionality,
you're,
modeling
and
I'm,
not
sure,
if,
if
anyone's
willing
and
able
to
do
that,
but
I
guess
it's.
This
is
a
time
where
you
can
easily
fix
oversight.
O
O
O
You
know
own
one
of
these
keys
to
wreak
havoc
and
clearly
that
that
can
introduce
you
know,
bigger
security
risks,
so
I
think
there's
a
trade-off
here
and
you
know
I'm
not
sure
that
I
have
only
all
the
answers
but
I'm,
hoping
that
the
use
of
hsn's
will
actually
help
in
this
regard
and
strong
processes,
but
I
don't
think
having
this
is
enough.
You
need,
you
need
to
have
all
kinds
of
our
know,
especially
processors.
I.
Think
your.
Y
Your
slide
sparked
my
thought,
because
you
mentioned
just
now
that
you
didn't
want
to
revoke
key
one
with
keep
with
package
two
and
three,
so
that
made
me
think
about
this.
So
if
you
don't
want
like
the
newest
key
to
revoke,
then
maybe
it
doesn't
have
to
be
able
to
or
well
so
you
think
about
that
kind
of
property.
O
Well,
if
you
referring
to
the
one
where
I
said
only
key
to
needs
to
revoke
key
one,
that
was
mainly
because
you
and
only
need
to
learn
about
key
ones,
revocation
ones,
and
so
that
was
an
attempt
to
stop.
You
know
the
object
from
becoming
really
huge.
If
you,
you
know,
theoretically,
to
do
dozens
of
these
roles.
C
Murphy
Parsons
I'm
standing
at
the
far
mic,
because
I'm
asking
a
question
from
a
position
of
ignorance
and
in
case
you
want
to
throw
things.
I
have
been
impressed
at
the
amount
of
effort
it
took
to
do
the
DNS
SEC
key
role.
So
this
is
a
really
good
idea
to
get
an
early
start
on
considering
here,
and
so
thank
you
very
much
for
starting
the
work.
I
also
remember
the
difficulties
that
there
was
in
the
site
of
working
group
to
define
the
algorithm
change
documents
from
very
long
ago.
F
X
X
John's
was
intending
with
the
RC
5011
for
DNS
SEC
was
the
ability
to
pre
publish
keys
before
really
using
them,
and
that's
basically
because
no
one
really
knows
how
to
do
an
emergency
key
role,
an
emergency
key
role
for
real
and
unplanned
one
he's
basically
burned
it
to
the
ground
and
start
over
which
kind
of
sucks.
So
what
you
do
instead
is
an
accelerated
schedule
planned
key
role,
which
kind
of
requires
you
get
the
the
four
to
work.
Well,
you
need
to
get
the
next
key
out
there
early
part.
C
V
So,
as
was
kind
of
mentioned
in
a
previous
talk,
there
was
RFC
1897
with
an
extended
community
for
origin
validation.
Signaling,
it
kind
of
looked
like
this,
and
how
does
the
receiver
drop
in
balance?
Yeah
I
got
the
message.
I
gave
you
a
prefix,
you
wrote
back
and
you
said
it
sucked.
What
do
I
do
cry?
Okay,
so
I
want
to
drop
in
balance
as
if
I
had
detected
it
myself
running
origin,
validation,
okay,
that
should
be
the
effect
kind
of,
in
fact,
even
slightly
more
strongly.
V
I
should
withdraw
all
the
announcements
where
I
actually
sent
out
the
garbage
right
so
think
about
reflector
with
lazy
clients,
the
clients
don't
run
origin
validation,
but
it
would
be
nice
if
they
understood
this
community
and
actually
knew
how
to
act
on
it.
And
this
isn't
policy.
This
is
actual
behavior
change,
I'm
getting
a
scowl
from
John
and
that's
why?
Because
it
sounds
like
work.
V
Okay,
I
mean
it's
not
just
the
route
reflect
your
situation,
but
here
in
this
draft
we
specifically
talked
about
trust
boundary.
Okay,
it's
only
within
a
pop.
It's
not
outsourcing!
It
okay
do
not
share
your
needles
with
customers
or
friends;
okay,
so
here's
where
we
kind
of
differ
with
the
route
server
issue:
okay,
no,
okay,
as
well
of
origin
validation,
ploys.
We
really
want
to
do
something
like
this.
It
would
be
a
bit
of
an
accelerator,
make
it
easy
for
some
people.
Let's
set
her
okay
and
we'd
like
to
request
w/g
adoption.
V
K
K
V
V
E
E
N
No
about
some
baby
care
can
see
the
route
reflector
when
it
receives
routes
from
its
clients
will
run
a
best
spot
and
will
announce
the
best
spot
a
best
spot
when
it
does
the
community
tags
on
top
of
it
to
say
what
is
wrong
with
it.
Now
the
route
reflector
could
say
part
one
is
the
best
but
part
four
that
I
just
received
had
a
bad
community,
so
it
could
do
ad
parts
in
piggyback
part.
Four
and
say
this
is
wrong.
N
V
Q
N
What
Randy
is
trying
to
say
and
I'm
channeling
him?
So
keep
me
honest
when
it
receives
an
extended
when
edge
router
receives
an
extended
community
for
that,
given
prefix
on
an
edge
router
for
all
the
paths,
it
will
go
and
loop
and
say
wherever
you
find
a
spot,
which
is
incorrect,
mark
that
path,
ineligible
for
best
path,
reading
the
best
path
and
then
announced
that
new
best
path
back
to
the
route
reflector,
so
that,
if
someone
does
a
router
refresh
in
again,
you
always
always
send
out
the
right
path.
Does
that
make
sense.
V
E
V
My
personal
instinct,
of
course,
but
there
are
others
who
said
otherwise
they
want
to
have
more
centralized
control
at
that
level,
just
as
they
have
single
or
you
know,
paired
validators
in
a
pop
Ruettiger,
I'm,
sorry
to
be
rude,
I
have
another
present
day.
How
am
I
doing
for
time?
For
the
second
presentation,
can
we
move
along?
Please
sorry,
gentlemen:.
V
V
V
V
Because
I
can
lunge
the
path
change.
The
effect
of
origin
I
could
have
a
selection
of
a
SS
on
this
router
and
I'm
the
originator
and
then
I
choose
which
one
of
I'm
gonna
tag,
etc.
So
I
want
to
be
able
to
apply
origin
validation
to
what
I
am
about
to
announce,
because
I
don't
want
to
hear
from
warrants.
Knock
well.
I've
got
bad
breath.
V
K
H
Thank
you
for
your
your
time,
so
my
name
is
Terry
I'm
a
route
server
operator
I'll
be
very
clear
that
I
only
speak
for
myself
as
a
root
server
operator
and
for
the
root
server
that
I
operate.
I
will
not
speak
for
any
other
root
server
operator.
I
want
to
draw
your
attention
I'm
talking
about
DNS
and
there's
a
reason.
I'm
talking
about
DNS
I'll
get
to
it
in
a
minute.
H
So
there's
a
lot
of
a
lot
of
push
to
do.
Rpki
because
you
know
you'll,
look
better
you'll,
you'll
grow
your
hair
back
and
you
know
you'll
be
more
attractive
to
the
opposite,
sex,
all
those
sorts
of
things
and
that's
fantastic.
There
are
two
documents.
I
would
like
to
draw
your
attention
to
just
slightly.
You
may
not
understand
where
they
come
from,
but
you
can
google
them
and
find
them.
There's
something
called
Rs
sac.
0:21
are
a
sec.
Is
the
root
server
system.
Advisory
Committee
and
our
sector.
H
A21
essentially
says
that
the
failure
of
one
root
server
operator
is
not
critical
to
the
operation
of
the
entire
internet
and
that's
good.
There's
a
second
document.
Our
sex
0
for
2,
which
says
things
about
the
independence
of
root
cellar
operators
and
one
of
those
things
that
it
discusses,
is
that
root
server
operators
will
be
diverse
in
their
operations
and
their
network
operations
and
infrastructures.
H
So
now
I
think
about
this,
and
this
is
my
perspective.
Only
no
one
else's,
someone
might
share
it,
but
this
is
my
observation.
Is
that
if
the
root
server
operators
all
do
rpki,
they
are
then
impacted?
Should
one
of
the
five
TAS
have
an
a
situation
more
so
right
now,
if
one
particular
operator
ta
operator,
rpki
operator
has
an
issue,
it
will
affect
nine
root.
Server
operators
discuss.
L
AA
H
Matter
who
it
is
it's
arbitrary?
Well,
whether
there's
there's
12
organizations
that
operate
root,
servers,
there's
only
five
organizations
that
currently
do
the
in
this
current
model,
like
I'm,
not
trying
to
propose
any
solutions.
That's
not
my
job.
My
job
is
just
to
highlight
that
I
see
there
that
there
is
a
diversity
issue.
I
was.
AA
AA
H
E
G
H
H
E
I
My
name
is
Carlos
I
work
for
Lange,
Nick
notify,
or
else
we
would
happily
welcome
you
guys
I
mean
we
can
recover
policies
that
allow
us
to
assign
prefixes
for
critical
infrastructure
that
can
be
used
outside
of
our
region
and
I.
Believe
the
other
four
have
similar
policies.
My
my
comment
is
that
I,
don't
think
that's
a
problem
for
us
to
solve
I
mean
as
cider
ups
I.
I
Think
if
you
have
nine
prefixes
within
a
single
IRR,
you
guys
are
a
bit
weak
on
the
diversity
aspect
that
you
apparently
are
defending
and
other
documents
I,
don't
know
what
the
solution
is.
I
mean
you
could
roll
a
piece
in
some
of
the
root
servers
distributed
among
their
areas.
You
could
get
a
new
space
from
us.
You
could
transfer
like
yourself.
There
are
a
bunch
of
ways.
You
could
actually
create
more
diversity
in
that
aspect
of
their
roots
or
reparations.
I
I
H
M
G
Don't
make
a
magazine
anymore,
I
think
the
depth
I
guess
what
I
was
trying
to
go.
Is
you?
There
are
some
things
that
are
sort
of
hot-button
topics,
and
maybe
the
issue
is
not
necessarily
a
roots
or
a
problem.
This
is
in
general
network
operations
problem
if
I
operate,
something
a
large
resource
of
the
Internet.
G
G
AB
H
AB
AB
Numbers
and
stuff
as
well,
six
five
second
statement:
we
went
through
the
scenarios
over
lunch
and
I'm
happy
to
talk
to
you
or
anyone
who
is
interested
or
we
can
form
some
kind
of
committee
whatever.
But
the
end
result
of
the
discussion
was
that
no
operator
can
be
worse
off
than
today.
If
they
also
have
Roseanne
rpki,
they
may
be
better
off,
but
they
will
not
be
worse
off
in
case
of
attacks
and
so
on.
Okay,
it's
not
just
every
day,
but
if
hits
the
fan,
I'm
happy
to
talk
about
it,
as
I
said.
AB
The
third
statement
is
that
it's
a
bit
tongue-in-cheek,
but
brute
operators
already
synchronize
on
protocols
and
everything
they
do.
You
all
run
ipv4
ipv6,
bgp
blah
blah
blah.
So
you
might
want
to
you
know.
If
you
want
to
diversify,
then
you
might
want
to
do
write,
P,
X
or
something
yeah.
It's
pretty
much
tongue
in
cheek.
T
H
H
T
V
V
V
X
X
H
X
Other
thing,
though,
I
think
you
need
to
make
a
distinction
between
reliability
and
availability
and
the
two
services
you're
talking
about
here.
The
fetching
and
caching
behavior
of
DNS
is
very
different
from
the
fetching
and
caching
behavior
of
the
rpki.
You
can
probably
survive
an
outage
of
no
new
stuff
being
published
in
the
rpki
for
a
while
I
mean
eventually
they'll
start
to
have
problems.
X
You
know,
CR
ELLs
get
stale
bla
bla
bla
bla
bla,
but
if
people
aren't
using
stupidly
short
expiration
times,
you
can
last
a
few
days
right
a
few
days
if
a
root
server
being
out
would
probably
be
more
noticeable,
so
you
may
need
to
do
the
numbers
on
how
long
of
an
outage
is
acceptable.
That
sort
of
thing-
and
you
know
getting
good.
X
F
P
P
P
P
I
think
the
politeness
is
more
than
a
sec
might
circle
around
either.
The
group
will
one
or
two
of
the
group
and
get
some
more
data
as
they
do
their
investigation
and
that's
great
and
it's
great
that
it's
forewarning
as
I
said
it's
a
bit
tough
to
say
to
us
solve
it
because,
like
I,
said
wrong
place
wrong
time,
I'm
not
ask
you
to
solve
it
on
actually
think.
H
P
Like
many
things
about
the
root
server
system,
it's
about
assurance
to
the
community
that
the
you
know
we're
doing
as
well
as
we
can
do
state-of-the-art.
Is
there
and
you
know
I-
think
our
sac
is
perfectly
capable
of
getting
to
that
kind
of
advice
without
necessarily
committing
myself
there
doing
any
work
at
all.
Just.
AC
With
little
markers
just
one
general
remark:
it's
a
common
thing
that
the
when
you
are
implements
are
mechanism
to
cope
the
summer,
the
attacks,
then
you
will
have
additional
failures
connected
with
a
possible
failure
of
that
mechanism.
It's
obvious!
You
should
leave
that.
The
problem
is
whether
gains
from
implementing
that
measure
mechanism
over
weights,
where
possible,
drawbacks
from
these
mechanism
being
broken.
So
you
just
brought
the
common
general
question
so
who
is
it
worth
to
implement
mechanism
yeah?
Just
the
drawbacks
will
alway
to
gains
so
so
everyone
should
decide
by
himself.
So.
T
H
E
M
H
My
next
steps,
and
one
had
already
planned,
is
to
raise
it
at
at
our
sect
bit
of
information
is
that
I
am
also
a
representative
at
our
sac
and
I'm.
Also,
a
member
of
the
asset
caucus.
The
asset
caucus
is
the
thing
that
does
the
work
for
our
sac,
so
it
will
be
raised
in
our
sac
that
may
also
spin
off
into
other
requests
into
other
parts
of
the
the
I
can't
ecosystem,
including
something
called
s
SEC
which
I
do
know.
H
Jeff
is
also
a
member
of,
and
some
others
here
in
this
room,
perhaps
as
well.
So
yes,
there's
additional
stuff
coming
through
and
I
think
Jeff's
right,
I
think
those
groups
will
circle
back
here,
but
I
think
it
was
good
to
just
raise
it,
and
so
you
have
some
awareness
of
issues,
some
operational
issues
that
are
caused
by
this
particular
corner
case
and,
as
Chris
pointed
out,
possibly
by
other
organizations
who
might
think
the
same
way
are.
