►
From YouTube: IETF105-PANRG-20190725-1330
Description
PANRG meeting session at IETF105
2019/07/25 1330
https://datatracker.ietf.org/meeting/105/proceedings/
B
D
C
E
C
C
If
you
have
any
suggestions,
we
have
not
filled
agenda
for
the
next
meeting
here.
So
please
say
your
name
in
the
microphone.
It
was
help
and
yeah.
So
we
have
almost
the
same
list
of
documents
as
the
last
time.
So
we
have
two
active
documents
and
we
going
to
talk
about
both
of
them
today
and
we
have
one
individual
draft
which
Terrell
is
presented
and
we
have
one
individual
draft
which
hasn't
been
updated
since
the
last
meeting
to
keep
it
on
the
slide
so
and
now
I
think
bran.
A
B
More
important
to
be
not
be
from
the
chair
until
I
well
yeah.
Thank
you
very
much.
I
will
do
this
from
the
floor.
Oh
hi,
Brian
Trammell
with
a
question
about
this
document
so
yeah
this
is
my
RTF
energy
questions,
zero.
Two!
Basically
in
Prague
we
discussed
this.
We
went
over
it.
I
decided
actually
not
to
bring
this
back
up
on
slides
because
there
have
been
no
structural
changes
to
the
document.
We
got
good
comments
from
Mohamed
Booker
there
I,
don't
know
if
he's
here
or
not,
we
brought
those
in.
That
was
the
zero
two.
B
As
the
you
know,
the
framework
of
what
it
is
we
do
in
here
or
if
we
wanted
to
go
ahead
and
publish
it
as
a
snapshot
in
time,
and
there
was
kind
of
a
lot
of
discussion
from
the
floor
where
we
said
hey,
yeah
I
know
we
do
actually
want
to
keep
this
open
as
author,
not
as
here
I,
would
push
back
on
that
a
little
bit
in
that.
If
you
want
to
look
here
right
like
so,
there
was
draft
for
my
panarchy
questions
and
then
draft
IRA,
TFP
energy
questions.
B
Living
up
to
our
expectation
is
a
living
document
right
like
so.
A
living
document
that
is
dead
is
an
undead
document
on
draft
I
or
TFP.
An
orgy
zombie
questions,
so
I
would
actually,
as
author,
come
back
and
push
back
on
that
a
little
bit
and
say
hey
if
we
are,
if
we're
not
updating
it
that
quickly,
why
not
just
publish
it
so
not
to
sort
of
like
re,
you
know
relitigate
something
that
we
already
talked
about
if
there
are
not
like.
B
If
there's
not
like,
you
know,
strong
consensus
that
no,
no,
no,
no,
no,
keep
it
open
because
we
might
think
of
something
I
would
say
hey.
Maybe
we
should
just
go
ahead
and
push
this
one
out
so
I
guess
now.
I
would
ask
the
chair
to
open
the
sort
of
questions
or
discussion
about
that.
If
anyone
cares
will
do
it,
if
no
one
care
or
if
anyone
cares,
we
won't
do
it.
If
no
one
cares
we'll
do
it.
B
G
Mr.
Dawkins
so
I
wanted
to
mention
that
I'm
expecting
to
make
references
to
this
document
in
my
second
presentation
today.
So
after
I
do
that
you
might
want
to
decide,
then
whether
you
want
to
whether
you
think
it
makes
more
sense
to
me,
be
for
me
to
be
pointing
to
it
as
a
draft
or
as
something
that
you've
requested
publication
for
cool.
B
B
Okay,
cool
good.
Those
of
you
who
haven't
read
it.
Please
have
and
are
interested
in
this
base
and
are
not
just
sitting
in
here,
because
it's
a
nice
place
to
cool
down.
Please
have
a
look
at
it
and
you
know
give
comments.
You
know
hey.
Yes,
I
think
this
covers
the
questions
that
we
care
about.
Oh
no,
have
you
thought
about
this
question
because,
like
a
lot
of
these
rubs
are
early
on,
you
know
we
actually
did
rather
because
people
are,
do
you
think
about
that?
B
B
Only
think
about
that
I'll
definitely
change
it.
I'll
definitely
make
it
not
like
you
know
open-ended,
because
you're
right
this
sounds
very
open-ended
and
if
we're
going
to
publish
it,
that's
paradoxical
I'm,
not
sure
I
want
to
put
2019
in
the
title,
because
it's
not
my
favorite
year
but
yeah.
So
thank
you
very
much.
H
G
Yeah,
this
is
the
thing
that
always
terrifies
my
kids,
so
I'm
semester
Dawkins
to
talk
about
energy.
The
research
group
draft
of
what
not
to
do
throw
three
provision
now
and
I
want
to
talk
this
time,
mostly
about
what
still
won't
work.
So
here's
what's
happened
since
1
0
0
1,
which
was
the
last
idea
for
vision.
G
If
you
have
meeting
revision
and
I've
gotten
new
comments,
thanks
to
the
people
who
sent
comments,
I'm
getting
careful
reads
but
I'm
not
getting
a
lot
of
new
material,
so
I'm
getting
helpful
suggestions,
I'm
getting
typos
I'm
getting
this
is
unclear,
but
I'm,
not
getting
new
sections
or
you
know,
supporting
new
lessons
learned.
So
we
might
be
finished
with
this.
One
research
group
last
call
question
mark.
We
can
talk
about
that.
G
We
could
certainly,
in
my
opinion,
we
can
certainly
use
0-3
to
guide
our
research
and
to
start
discussing
with
the
IRT
IETF
and
I
actually
mentioned
that
in
a
side
meeting
this
morning.
This
draft
that
the
research
group
had
been
working
on.
So
my
suggestion
is
to
review
the
lessons
learned
and
see
what's
still
true,
because
things
change,
that's
what
I'd
like
to
focus
on
in
this
talk
not
worth
smithing
I'm,
happy
to
wordsmith
and
I've
gotten
pull
requests,
but
we
do
have
a
mailing
list
and
github
for
that.
G
This
is
kind
of
the
out
of
your.
Are
you
out
of
your
mind,
review
by
the
research
group
for
for
Spencer
I
have
blue
boxes.
I
have
suggested
answers
for
whether
each
lesson
learned
is
still
true
in
blue
boxes
like
this
one.
These
are
only
my
opinions.
There
is
a
mic.
There
are
mics
on
both
sides
of
the
room,
I
hope
to
cancer
capture
your
answers
here
and
on
the
mailing
list.
You
know
so
for
revision.
G
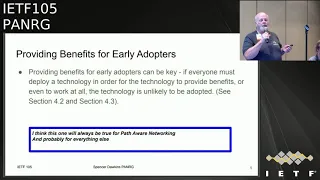
G
I'm,
seeing
thumbs
go
up
and
not
seeing
anybody
diving
for
the
microphones
next,
providing
benefits
for
early
adopters
can
be
key.
I
think
this
one
will
also
be
true
for
path,
aware,
networking
and
probably
for
everything
else
thumbs
up
thumbs
down.
This
could
be
very
Roman:
okay,
I'm
seeing
thumbs
thumbs
up
and
no
thumbs
down.
Yes,
I
should
be
letting
you
call
these
okay,
an
individual
thumb.
Awesome
I
should
actually
probably
be
letting
you
all
call
the
thumbs.
I
can
do
it.
Okay,
cool
whoa!
G
Here
we
go
so
I
think
this
one
is
also
true
for
a
for
networking
and
everything
else.
The
thumbs
have
it
indie
and
mechanisms
may
respond
to
feedback
quickly
enough
that
the
additional
realizable
benefit
from
a
new
path.
Aware
mechanism
may
be
much
more
than
you
thought
it
was
going
to
be
this
one,
in
my
opinion,
is
worth
talking
about
it's
one
of
the
key
debating
points
for
the
loops
buff
that
we
hold
Monday
I.
G
Think
in
this
very
room,
if
I
was
remembering
right,
but
they
all
kind
of
look
alike
and
a
great
deal
has
to
do
with
whether
there
is
more
more
than
one
long
path
segment
in
the
path
thoughts
on
this
one-
and
this
is
not
that
this
is
not
a
thumb
question.
It's
actually
a
brain
question.
Any
thoughts
on
that
or
I
mean
you
could
say
yeah.
We
need
to
think
about
this.
Some
more.
G
G
So
it's
it's
it's!
Basically,
it's
basically
the
classic
discussion
that
we've
had
since
at
least
the
trigger
and
buff
in
the
early
2000s,
which
is
basically
you're,
going
to
add
complexity
to
a
public,
complex
transport
protocol.
In
order
to
improve
performance.
Are
you
going
to
get
enough
new
performance
that
you
know
in
the
quote?
B
B
Property
for
which
you're
going
to
get
a
realizable
benefits.
I'm,
not
this
is
not
were
in
the
chair,
cut
the
the
properties
for
which
you'll
get
a
realizable
benefit
from
path
aware.
Networking
are
qualitatively
different
from
those
to
which
this
question
applies
right.
So
the
this
question
is
about
like
hey.
If
we
get
the
devices
on
the
network
to
tell
us
things
like,
you
know,
queue
occupancy
and
delay
we're
not
going
to
get
data
back
any
faster
than
we
would.
B
If
we
tried
to
measure
it
right
and
that's
true,
and
that
remains
true-
there
are
other
the
set
of
path
properties
for
which
you
get
a
and
immediately
and
end
like
a
scale.
Is
the
wrong
word
for
rich,
for
which
this
really
helps
are
things
that
are
difficult
to
sense
and
change
slowly.
So,
for
the
extent
that
we
think
that
there
are
a
large
set
of
those,
then
proper
in
our
being
is
a
great
idea
to
the
extent
that
we
think
that
that
set
is
empty.
B
Flip
this
around
a
little
bit
right
and
basically
rephrase
it
in
terms
of
the
meta
properties
of
the
properties
that
you're
talking
about
pather
TT
is
a
terrible
property
to
use
path.
Aware
networking
for,
if
you're,
actually
talking
about
having
the
path,
tell
you
things
about
path,
RTT,
because
they
don't
know
it
and
it'll
get
to
you
too
slowly.
Yeah.
G
B
Is
a
satellite
link?
Satellite
links
usually
do
not
turn
into
non
satellite
links
on.
You
know
Elon
Musk,
notwithstanding
on
a
very
short
time
scale.
Maybe
you
can
sense
it
probably
you
can
so
I
would
so.
This
is
like
you
know,
question
to
the
research
group
to
think
about,
as
well
as
a
I
think
feedback
on
the
document.
You
know,
if
you
split
that
question
up,
then
the
loops
question
goes
away
and
then
we
have
another
question
that
we
can
dig
in
on.
But
I
don't
know
the
answer
to,
but
okay.
G
G
So
the
first
thing
I'm
thinking
is
that
we
may
end
up
with
the
0
4
that
has
new
subsections
for
some
of
the
lessons
learned,
but
not
all
of
them,
because
you
know
they're
true
for
all
time
and
space,
and
that
that's
where
we
might
put
discussion
about
things
like
that
and
the
second
one
was
being
clear
that
we're
talking
about
relatively
long-lived
and
stable,
but
information
about
the
path
that
isn't
isn't
easy.
This
isn't
easy
to
find
out
and
it's
an
easy
that
you
it
doesn't
change
rapidly.
I
I
G
I
Think
one
of
the
things
that's
confusing
to
me
initially
on
this
is
it
it's
not
really
giving
us
kind
of
the
lesson
learned
is
just
saying
that
this
may
happen
in
there.
So
maybe
can
we
add
some
qualitative
way
of
saying
like
these
particular
mechanisms
that
behave
like
this
end
up.
You
know
being
more
useful
along
this
axis,
so
what
what
is
it
about
it
that
makes
it
better
or
worse
for
this
quality
yeah.
K
Following
up
on
what
Tommy
and
Brian
just
said,
I
am
wonder,
for
example,
if
we
can
say
if
the
endpoint
is
in
the
worst
position
to
learn
about
like
some
RTT
or
some
properties
than
the
path
itself,
then
it
might
be
helpful
or
like
in
what
case?
Might
it
be
helpful?
Well
if
the
path
can
tell
the
endpoint
something
the
endpoint
cannot
measure
by
itself,
for
example.
So
that
would
also
help
me
to
think
about
this
question.
I
think.
G
You'll,
like
my
next
presentation,
the
others
so
I
think
I
know
that
we're
doing
something
with
this
lessons
learned
with
all
of
the
money
I
think
is
always
true
that,
basically,
if
you
can't
you
know,
your
choices
are
basically
either
you
get
a
lot
of
money
from
deploying
this
or
you
get
a
lot
of
benefit
from
doing
this.
At
least
one
of
those
must
be
true
thumbs
up
thumbs
down,
seeing
nothing
heads
seeing
thumbs.
Okay,
cool
operational
practices
can
be
showstoppers.
B
The
operational
practices
might
be,
might
be
an
incentive
I,
don't
know
how
to
counter
capture
that
really
in
the
tone
of
this
section,
but,
for
example,
one
of
the
you
know
looking
at
song
on,
for
example,
as
a
path
aware
architecture,
one
of
the
key
things
that
they
have
heard
and
one
of
the
key
you
know
like
hey
here's,
why
we
think
we
can
actually
get
operators
to
care
about.
This
is
inter-domain
QoS
rate.
It's
like
here.
Look
it
changes
your
practices
and
that
practice
is
here's.
A
new
service
you
can
offer.
B
Will
it
work,
no
idea,
but
does
it
does
it
incentivize
people
to
try?
Yes,
so
I
would
I
would
possibly
I
would
possibly
rephrase
this
one
slightly
to
capture
the
fact
that
this
goes
up
and
down
I,
know
I
just
say:
inter-domain
QoS,
in
a
room
in
a
room
in
a
building
where
the
IETF
is
meeting,
so
I
will
sit
down
now,
cool.
G
Thank
you,
so
that's
the
incredibly
cool
Brian
Hamill
without
the
incredibly
cool
hat.
So
this
this
one
we'll
be
talking
about
some
more
between
now
and
ITF,
106
per
connection
state
again,
I
think
this
one
may
be
worth
discussing,
because
we've
usually
talked
about
this
in
a
please.
Don't
do
this
in
my
core
router
and
serve
texts
in
enough
people
have
scolded
me
saying:
excess
routers
or
enterprise
routers
may
do
just
fine
with
that
to
where
it's
worth
being.
L
L
So
maybe
it's
would
it
be
worth
rephrasing
it
a
little
bit
more
as
saying
here
either
the
kinds
of
things
you
shouldn't
do
or
like
if
you
do
have
per
connection
state
here,
are
the
things
that
seem
fine
to
do
with
it
and
and
kind
of
phrase
it
as
a
like,
not
quite
a
behavior
guideline,
because
that's
not
quite
what
we're
trying
to
come
up
with
here
but
like
something
in
that
area,
as
opposed
to
just
like,
yes
per
connection
state
could
be
a
problem.
It
could
also
not
be
a
problem.
Sharkey.
G
Yeah
and
and
in
trying
again
trying
to
be
measured
about
it,
I
think
that
you
know
this
is
one
of
the
things
where
this
has
been
a
electric.
You
know
a
third
rail
for
a
long
time
and
we
have
a
lot
of
experience
with
it
being
a
problem
and
not
a
lot
of
experience
with
people
trying
it
where
it
might
not
have
been
a
problem.
So
I
think
that
I
think
being
measured
again,
that's
a
good
thing
to
say:
yeah.
M
G
You
so
this
one.
We
need
to
talk
about
a
bit
more
between
now
and
106
in
ban
mechanisms
can
fall
off
the
fast
path
say
the
same
response
here,
I
think,
which
is
basically
there
are
people
that
aren't
as
worried
about
this,
as
the
people
were
worried
about
when
they
started
talking
about
nice,
long,
ipv6,
extension,
headers
or
deep
packet
inspection
on
routers
or
the
other
things
like
that.
So
again,
I
think
this
is
one
that
we'll
be
talking
about
between
now
and
100-106.
B
G
B
Will
point
out
that
I
know
that
right
now
in
sag,
right
over
there
they're
having
a
talk
about
a
potential
discussion
about
reopening
the
internet
threat
model
and
maybe
trying
to
update
it
to
talk
about
stuff?
You
know
we
know
now,
and
this
seems
a
little
bit
like
you
know.
This
is
this:
is
not
the
internet
threat
model?
This
is
new
path,
aware
internet
threat
model,
but
it
seems
like
that
discussion
in
this
discussion
or
maybe
kind
of
the
same
discussion.
So
the
conflict
is
unfortunate.
B
G
N
G
Yes,
thank
you,
and
this
gets
us
to
the
canyon
points,
trust
the
network
path.
So
this
is
the
other
side
of
that
and
that's
got
stuck
on
the
following
slide,
because
the
lesson
learned
was
kind
of
long,
but
my
you
know
again
my
opinion
is
we
absolutely
need
to
talk
about
this,
so
we
need
to
I
think
Brian's
point
as
I
understood
it
was.
We
need
to
figure
out
how
to
talk
about
it,
not
not
not
in
the
middle
of
the
sake,
discussion.
G
Yeah
exactly
yeah
exactly
we
need
to
be
aware
of
the
threat
model
discussions:
cool
is
the.
Can
the
network
provide
actionable
information,
so
this
is
basically
the
distance
in
time
to
time
to
respond
kind
of
kind
of
things.
I
think
that
this
is
actually
even
more
true
now
that
it
was
in
the
cases
where
we've
got
it
in
there,
but
I
think
it's
probably
always
going
to
be
true,
prepare
we're
networking
and
all
everything
else.
Yes,.
B
B
G
K
G
To
the
end,
points
know
what
the
path
needs
to
know.
I
think
this
is
true
for
pet
networking.
That's
where
networking
and
for
everything
else
we
had
yeah.
So
this
is
and
I.
Actually
we
were
in
the
APN
six
side
meeting
this
morning
and
I
was
talking
about
the
you
know,
they're
talking
about
basically
applications
signaling,
the
network
and
I
was
like
I'm,
not
telling
you
need
to
be
in
pen
RG,
but
I'm
telling
you
that
we
have
concerns
about
applications,
knowing
what
they
need
to
tell
the
network
and
being
able
to
tell
the
network.
G
G
Lars
is
in
here
or
not
Laura.
Posted
Lawrence
was
telling
me
that
he's
having
you
know,
he
was
having
trouble
figuring
out
how
to
do
anything
with
ecn
and
rust.
I
mean
you
know
it's
like
so
I
mean
it's
like
things
are
things
may
be
getting
more
broken,
as
people
are
doing
things
that
aren't
necessarily
sockets.
So
assuming
that
this
is
welcome?
Oh,
oh,
so
far,
so
this
is
eight
minutes
into
my
we're
eight
minutes
left
into
my
talk.
G
G
There
are
relevant
questions
and
the
research
questions.
Other
questions
draft
that
apply
here
and
we
might
talk
about
how
the
IETF
here's
here's
about
our
lessons
learned,
I,
don't
know
that
we're
ready
to
have
I,
don't
know
that
we're
ready
to
inflict
the
our
wisdom
on
the
IETF
in
any
meaningful
way
yet,
but
but
something
to
think
about,
and
do
you
think
we
need
to
talk
about
that
here?
G
G
B
B
O
G
I
think
what
Spencer
to
think
what
Spencer
is
capable
of
when
he
has
access
to
github
and
no
adult
supervision,
so
I
wanted
to
talk
to
you
all
about
path,
implications,
the
performance,
implications
of
path,
characteristics
and
I
was
interested
in
talking
about
the
pilk
link
characteristics
experience.
This
is
some
information
about
that
and
basically
the
ITF
did
recommendations
for
certain
Network
designers
a
long
time
ago.
We
think
the
Internet
may
have
changed
some
order.
G
In
the
last
50
years
we
had
a
side
meeting
to
gauge
interest
at
104
I
sent
notes
about
that
too
the
penalty
list,
and
we
had
a
side
being
here
to
identify
recommendations.
So
we
were
ready
to
make
the
IETF
about
path
about
path,
awareness,
I,
publicized
that
to
the
pen
orgy
barely
list
with
not
enough
warning
and
that's
okay.
It
may
be
okay,
because
we're
talking
here
trying
to
answer
the
question:
are
there
recommendations
we're
ready
for
the
ITF
to
consider?
And
we
did
this
yesterday
morning-
I
I
have
bad
news.
G
The
good
news
is
that
smart
people
showed
up
to
help
identify
what's
research
now.
Thank
you.
The
people
on
here
I
think
I
got
already
same,
but
thank
you
for
the
people
on
here
who
showed
up
and
if
I
miss
your
name,
please
let
me
know
and
I
can
fix
the
slides
before
they
go
into
the
entombed
proceedings.
G
The
bad
news
is
that
almost
everything
is
still
research.
Oh
noes,
the
question
you
know
somebody
asked
the
question
in
front
of
Juarez.
What
could
we
tell
the
quic
protocol
transport
protocol
designers
and
we
all
kind
of
stared
at
each
other,
so
I'll
be
back
to
talk
about
pipsy
when
we
have
recommendations
for
the
IETF,
but
the
discussion
was
pretty
relevant
to
paint
RG.
G
What
I'm
presenting
now
is
my
take
on
yesterday's
conversation,
Corrections
and
rebuttals
from
the
people
who
are
there
are
welcome,
of
course,
either
here
on
list.
What
I
would
like
to
do
is
do
this
as
a
short
rant,
followed
and
leave
time
for
discussion,
so
we're
on
my
own
time
no
I'm
asking
how
many
minutes.
C
G
Okay,
okay,
okay,
okay,
so
so
I
would
like,
though
I
would
like
to
leave
least
15
minutes
for
for
people
to
say
what
we
should
have
said
yesterday.
Hopefully
it
will
only
take
15
minutes
so
here.
So
what
happened?
What
happened?
What
happens
was
first
question
was
easy:
why
not
do
Pepsi
and
Phe,
and
these
are
recommendations
for
protocol
designers?
If
it's
engineering,
it's
not
research.
So
it's
not
pen
orgy,
these
might
be
BCPs.
G
The
ones
for
pill
see
what
pill
were
BCPs
and
the
only
the
ietf
stream
publishes
BCPs,
but
at
minimum
we'd
like
review
within
the
IETF
before
publishing
them.
So
this
one
was
easy:
they
got
more
complicated.
We
said
that
paths
exist,
but
they
may
change
actually
explaining.
The
idea
of
paths
may
be
helpful
on
its
own.
We
noodled
about
a
bunch
of
things,
but
whether
all
parts
for
path
are
equal,
equally
useful,
less
or
equal
and
trustworthiness
but
keep
reading.
G
G
G
We
recognized
that
there
were
first
hop
networks
that
our
last
hop
networks
for
the
other
host
and
asked
if
information
sharing
was
possible
back
to
I
think
Brian's
point
about.
If
we're
talking
about
really
stable,
difficult
to
discover
properties,
then
maybe
they'll
be
stable
long
enough
long
enough
to
share
and
maybe
they'll
be
useful
enough
to
be
worth
sharing.
I
insert
the
advertisement
for
the
did
I
do
that
right,
yeah
the
path
properties
draft
which
defines
a
lot
of
our
terminology
and
which
has
been
updated.
Yes,
exactly
perfect,
we
talked
about
hints
and
not
directives.
G
We
observed
that
we
do
use
hints
now
like
ecn.
We
did
talk
about.
Are
there
other
hints
that
are
possible?
One
idea
that
came
up
was:
has
anybody
looked
at
IP
TTL
changes
so
that?
Basically,
if
you
know
if
your
TTL
s
were
coming
in
consistently
as
something
like
30
and
they
start
coming
in
at
something
like
to
do-
is
that
likely
to
be
correlated
with
anything
else?
That's
worth
noting.
As
a
as
a
transport
protocol,
I
promised
that
people
like
loops
are
thinking
about
delay
us
a
hint
again.
G
This
is
something
this
is
something
that
doesn't
involve
a
load
of
trust,
but
I
mean
like
we
thought
that
true
hints
are
likely
to
be
less
disastrous
than
directives,
but
we're
not
sure
they're
always
harmless.
No,
actually
we're
pretty
sure.
That's
not
true,
so
telling
path.
Host,
here's
the
path
info
you
should
do.
The
right
thing
seems
like
a
good
thing
for
us
to
do.
G
B
Can
you
given
sort
of
like
how
the
set
of
possible
architectures
that
might
interoperate
with
the
current
internet
architecture
are
built?
Can
you
ever
do
anything
other
than
this?
Our
direct
dues,
so
there's
basically
there's
either
a
type
of
hint
that
says
here
are
the
properties
or
the
path?
Maybe
you
could
use
this
to
do
something
better
and
there's
another
one
that
is
essentially
a
hint
with
a
threat.
Here
are
the
properties
of
the
path?
B
If
you
do
not
assume
this,
then
you're
going
to
have
a
bad
day
because
of
these
other
properties
of
the
path.
That
last
thing
is
as
close
as
you
can
get
to
a
directive
in
you
know,
architectures,
where
you
don't
have
like
sort
of
like
you
know,
integrated
data
control.
Where
you
know
see
me
a
Bitcoin
or
I,
won't
wear
out
of
your
pocket
sort
of
craziness
the
yeah,
so
I
mean
yeah
in
stock
directives.
Could
our
directives
even
possible
I
would
say
no.
G
N
G
I
think
I
think
what
we're
talking,
what
you're
talking
about
is
possibly
attention
in
the
room
yesterday
morning
between
things
that
would
be
interesting
to
research
and
things
that
might
feed
into
a
recommendation
to
the
IETF,
so
I
think
I
think
if
I
understood
what
you
just
said,
that's
probably
really
relevant
to
what
we
might
or
might
not
tell
the
IETF.
But
you
know
researchers
are
curious,
so.
P
Eric
Lloyd
I
can
tell
you
that,
certainly
watching
IB
T
L
IP
TTL
changes
between
on
a
certain
network
behind
walled
gardens
in
Asia.
We
had
1.1.1
that
one
on
port
53
and
on
port
85
three
had
radically
different
IP
t
TLS
one
was
returning
stuff
around
48
and
one
was
turning
stuff
up,
I'd
like
the
high
hundreds
just
under
200.
So
it
was
a
sign
of
interference,
not
necessarily
a
path
characteristic,
but
still
a
worthy
signal
to
have
been
able
to
race.
Cool
I
had
to
find
it
out
with
TCP
dump.
So.
G
Trust
no
one,
literally,
no
one,
some
application
protocol
designers
don't
want
to
trust
anything.
This
is
a
direct
quote
from
a
person
who
I
can't
identify
further,
because
you
would
know
exactly
who
that
was
with
any
with
any
further
description.
Saying:
oh,
you
want
me
to
trust
signals
from
the
network.
You
know
you
want
me
to
give
signals
to
the
network
of
trust
ignores
from
the
network.
How
about
if
I
give
you
no
source
of
destination
addresses.
Does
that
work
for
you,
because
that's
really
what
he
would
like
to
do?
G
The
important
thing
for
us
to
remember
in
penetrate
my
opinion
is
that
we're
providing
transport
services
that
those
protocol
designers
we
have
to
figure.
We
have
to
figure
out
what
we
can
do
and
what
we
can't
do
and
doing
that
in
a
research
group
is
a
whole
lot
less
painful
than
doing
it
doing
some
working
groups
that
have
tried
to
do
that.
G
Speaking
in
service
for
more
responsible,
very
director
we're
using
TLS,
which
is
inherently
two-party
for
a
lot
of
stuff,
we've
talked
about
how
to
make
it
two
and
a
half
party
or
three
party,
and
that
has
been
pretty
consistently
the
wrong
answer
in
the
IETF.
So
for
us
to
think
about
trust,
we
need
to
be
thinking
about
that
really
seriously.
G
G
P
Eric
Cline
I've
been
contemplating
contemplating
a
kind
of
a
hybrid
network
architecture
and
in
this
scenario,
I
I
think
when
used
to
talk
about
trust,
it's
like
what
do
you
trust
and
the
less
you
ask
people
to
trust
the
more
useful
and
generic
a
signal
can
be
right.
Sure
so
I
got
down
to
the
point
where
I
was
thinking.
Let
me
just
not
be
prescriptive
here,
but
for
my
particular
case,
let
me
just
cite
local
multicast
and
basically
some
kind
of
path,
characteristics
of
change.
P
You
might
begin
reevaluating
now
hint
for
appliances,
applications
and
transfer
protocols
to
start
doing
some
work,
but
but
like
yeah,
the
less
you
ask
got
to
trust.
It
definitely
seems
better
to
me
because
otherwise
your
actually
trust
what
I
have
to
give
it
increasingly
and
specific
information
to
trust,
and
that
seems
to
be
getting
that
seems
to
me
or
going
down
the
path
of
high
prescriptive
kind
of
direction.
P
I
So
I
just
had
another
thought,
I'm
kind
of
trust,
and
you
had
a
point
earlier
about
kind
of
like
having
the
different
parts
of
the
path
and
knowing
are
these
equal
and
Trust
or
how
you
relate
their
trust.
So
got
me
thinking
so
I
actually
wrote
my
comment
in
notes:
I
got
it
myself,
so
you
know
one
of
the
things
I
think
we've
brought
up
in
this
room
before
are
like
provisioning
and
provisioning
domains
telling
you
information
about
the
path.
I
This
is
one
of
the
mechanisms
to
do
that,
and
so
what
we've
been
having
discussions
as
we're
progressing
that
work
and
that
document
about
you
know
what
are
the
guarantees
of
our
trusting
right,
because
this
does
not
make
your
path
safe.
Doesn't
it
does
not
mean
you
can
really
trust
that
the
thing
is
truly
a
captive
portal?
I
It's
truly
giving
you
a
Wi-Fi
or
cellular
uplink
and
one
of
the
few
pieces
that
we
are
able
to
confidently
and
somewhat
confidently
say
we
can
trust,
is
when,
like
the
information
that
is,
you
know,
hopefully
signed
or
written
somehow
can
match
and
essentially
show
that
these
elements
of
the
path
are
associated
or
coordinating
right.
So
we
don't
know
if
they're,
good
or
bad,
or
we
should
trust
them,
but
we
can
see
that
they
are
colluding
or
sharing
properties,
and
that
becomes
a
useful
thing
to
know
right.
I
So
it
means
that
I
can
essentially
transitively
build
out
trust
like
if
I
have
something
that
all
right
I'm
on
the
local
network.
I,
don't
know
how
much
I
can
trust
my
router,
but
I
do
know
that
this
other
thing
has
clearly
coordinated
with
my
router,
because
they
know
the
same
information
and
so
I
can
kind
of
build
out
these
dependencies
of
well.
If
I'm
going
to
use
this
I
may
as
well
use
this
other
thing
as
a
hit,
because
it's
related.
So
maybe
we
can
talk
about
that
type
of
trust.
Building.
G
G
So
what
you
know,
what
could
you
do
to
prevent
that
from
happening?
You
know
to
free
in
the
quote:
was
you're
looking
for
the
talk
on
preventing
time
travel
in
NTP,
there's,
actually
three
drafts
in
the
NBP
working
group
from
the
on
the
same
on
the
same
topic.
So
there's
way
more
detail
than
even
in
the
RTF
talk
and
paper,
but
but
basically
the
thing
was
you
know:
how
do
you,
how
do
you?
G
G
Basically,
if
you
sample
pretty
widely-
and
you
know,
if
you
have
somebody-
that's
attacked,
you
know
yes,
I
think
the
numbers
were
like
a
quarter
of
the
NTP
servers
that
you
might
sample
and
if
you
sample
widely
and
if
you
compare
pretty
closely
to
your
current
thing,
it
would
basically
take
about
in
example,
three
times
every
three
seconds.
I
think
the
numbers
were,
but
the
point
was
that
it
was
like
it
would
take
you.
G
You
know
like
a
century
or
two
to
pull
it,
pull
the
clock
for
200
milliseconds,
so
basically
somebody's
taking
a
protocol,
that's
pretty
trusting
of
what
they
get
back
from
untrusted
endpoints
and
doing
some
exercises
on
it
to
make
it
more
resistant
to
manipulation
from
an
authorized
participant
in
the
protocol
or
30
of
them.
But
I
wanted
to
be
sure
and
mention
that
you
know
they
say
it
was
a
really
good
talk
and
I
talked
with
the
person
who
was
presenting
last
night
for
probably
30
minutes
about
it.
G
We
do
have
various
forms
of
why
what
what
the
transport
encryption
means
or
why
transport
encryption
is
harmful
or
things
like
that
we
had.
You
know
there
are
various
flavors
of
documents
like
that
floating
around,
so
for
us
to
be
seriously
thinking
about
them
and
deciding
stuff
the
pill
working
group,
which
was
kind
of
my
model
for
getting
into
starting
the
whole
conversation
in
the
first
place.
They
did
analysis
and
then
they
worked
on
recommendations.
They
didn't
pop.
G
They
didn't
publish
the
recommendations
until
most
of
the
analysis
was
done
and
published,
so
that
might
be
a
model
for
Panaji
going
forward,
because
penalty
could
certainly
do
the
analysis,
even
if
it
couldn't
write,
BC
piece
and
request
publication
on
them.
Looking
carefully
at
the
chairs
to
see
if
it
sounds
like
a
stupid
thing,
seeing
one
really
cool
head
shaking
side
to
side
now,.
Q
G
We
did
mention
that
we
need
to
remember
api's
because
I
say,
as
I
said
earlier,
Lars
was
in
carrying
languages
like
rest
that
Heidi
CN,
you
know
like
he
doesn't
know
how
to
find
out
whether
ACN
was
said
or
not
in
its
application.
So
for
us
to
think
about
that
and
hearing
other
footsteps
and
I
screwed
up
this
acronym,
it's
AP,
AP,
n
6,
but
T's
and
P
oak.
G
So
here
are
the
people
that
are
trying
to
communicate
between
the
transport
in
the
network,
and
here
the
people
are
trying
to
communicate
between
the
applications
in
the
network,
and
here
are
the
people
that
are
trying
to
communicate
within
the
network,
and
you
know
there's.
This
is
the
comfort
that
it
would
be
a
good
time
to
have
a
I
can
use
this
word
a
deep
dive,
basically
saying
who
all
is
trying
to
who
is
always
trying
to
fix
the
same
problem
and
who
is
always
actually
working
on
different
problems.
You
know
where
are
the
overlaps?
G
B
G
So,
like
I
say
coming
from
my
perspective,
you
know
the
question
was:
is
do.
Can
we
make
recommendations
to
ETF
transport
protocol
designers
now
and
the
answer
is
no,
so
no
so
people
think
that
that's
wrong.
That
would
be
an
interesting
conversation
to
have
either
here
or
on
the
list,
but
I
did
I
didn't
really
have
so.
I
didn't
really
have
questions
after
that.
I
was
just
reporting.
The
12-person
rant
to
energy,
which
seemed
like
it
was
the
most
immediately
affected
bunch
of
folks.
So.
B
That
I
actually,
like
your
last
point
on
your
last
slide,
they're,
not
the
please
discuss,
but
the
communication
is
a
good
thing.
To
some
extent,
this
room
I
think
firstly
and
I
say
this:
is
that
carry
the
research
group
trying
to
occur?
The
research
group
is
a
really
good
place,
how
those
conversations
is
sort
of
like
you
know,
in
addition
to
this
research
program,
where
it's
sort
of
the
interest
group
for
doing
this
sort
of
thing
in
an
IETF
adjacent
space
as
to
whether
a
research
group
can
give
it
advice
to
protocol
designers
neon
etf.
G
So,
actually,
if
you
back
up
to
the
slide
about
I,
think
it's
they've
made
a
previous
slide.
If
the
analogy
the
analysis
here,
then
that's
telling
people,
but
it's
but
it's
here,
but
it's
just
telling
people
what
you're
doing.
If
you
are
making
recommendations,
that's
strongly
encouraging
people
to
do
whatever
and
that
you
know
they
say
and
I
think
I
put
this
early
on
eat
this
eat.
This
at
least
needs
to
be
in
the
IETF
to
get
IETF
review
because
I
RTF
documents
are
not
supposed
to
get
extensive
review
in
the
IETF.
R
B
Vietnam,
the
this
seems
as
good
a
room
as
any
in
which
doctor
take
that
analysis.
Task.
I,
think
that
so,
if
I'm
looking
around
so
I'm
looking
around
today-
and
we
have
a
very
unfortunate
conflict
with
TCP
M,
which
is
so,
we
actually
discussed
this
and
the
outcome
of
that
discussion
was
well.
We
kind
of
screwed
up
and
conflicted
with
everything
in
routing
for
our
first
three
meeting.
B
So
why
not
see
what
happens
when
we
conflict
was
something
in
transport
for
the
next
meeting
and
so
I
would
I
would
not,
as
chair
want
to
look
around
the
room
and
say
well,
you
know
we
have
a
pretty
good
filter
on
this
room
of.
We
have
the
transport
people
who
care
about
this
question
in
here
in
the
transport
people
who
don't
care
about
questioning
in
the
space
out
of
here,
because
anyone
who
cares
about
TCP
is
also
not
here
so.
B
B
So
that
I
don't
think
we
can
answer
that
question
in
this
room
right
now
as
to
whether
this
is
the
right
room,
because
this
is
not
the
right
room,
I
do
as
chair.
This
seems
perfectly
within
the
the
charter
of
the
research
group
and
also
within
sort
of
the
you
know.
Why
are
we
here
right
for
this
communication
is
a
good
thing
and
I
think
this
is
the
right
venue
to
do
it
because,
like
other
transport
area,
working
groups
are
not
the
right
than
you
to
do
this
kind
of
analysis.
I
I
I
J
I
B
Button,
yes,
I
mean
like
yeah
TLDR,
yes,
obviously
as
to
I,
would
actually
have
to
go
back
and
read
the
research
group
charter
because
it's
been
a
while
since
I've
done,
it
I
think
we
might
need
to
add
a
sentence
or
two
there.
I,
don't
think
that
that's
particularly
hard
I
think
we
would
also
need
to
check
with
the
transport
area
directors
as
to
whether
or
not
they
thought
that
was
a
turf
grab,
but
fair
over
in
TCP
M
right
now,
so
we
can't
guess
than
that.
B
When
we're
talking
about
these
sorts
of
things
that
came
out
of
the
Sun
of
built
discussion
yesterday,
so
I
think
that
probably
Spencer,
he
usually
found
one
the
two
of
us
on
the
transport
a
DS,
and
we
should
figure
out
what
that
looks
like
in
terms
of
like
we
and
maybe
Collin
and
figure
out
what
that
looks
like
in
terms
of
charter
changes
for
their
research
group
and
how
we
want
to
scope
that.
So
it's
not
just
like
hey,
if
I
really
don't
want
banner
D
to
be.
B
B
K
So,
of
course
addressing
can
be
on
different
layers,
and
we
talked
a
little
bit
about
layers
in
the
definitions
too,
but
for
the
purpose
of
a
path
we
need
like
hosts
and
routers,
and
the
hosts,
and
in
this
example,
are
the
ones
at
the
very
end
of
the
path
and
the
nodes
are
in
the
middle
and
the
routers
are
in
the
middle
and
both
the
hosts
enter
router
our
nodes
between
nodes.
There
are
links
that
are
connecting
those
nodes
and
that
enable
them
to
exchange
packets.
K
Of
course,
a
link
can
be
between
more
than
two
nodes,
because
we
have
broadcast
medium
and
a
link
can
also
be
virtual,
doesn't
have
to
be
a
physical
link.
So,
for
example,
if
you
have
two
virtual
machines
that
are
running
on
the
same
physical
machine,
there
might
be
a
sort
of
virtual
link
between
those
virtual
machines
right.
So
we
have
nodes
and
we
have
links
now
if
we
string
those
together
if
we
have
a
sequence
of
adjacent
half
elements,
because
both
a
node
and
a
link
or
a
path
element.
K
So
then,
there's
packets,
exchanged
or
I
can
be
packets
exchanged
between
those
entities,
those
nodes
and
we
are
defining
a
flow
as
either
one
or
multiple
packets
which
are
traversing
the
same
sub
path
or
path.
So
it's
not
just
the
classic
definition
of
the
5-tuple
IP
addresses
and
ports
and
transport
protocol,
but
flow
in
our
definition
that
we
use
in
the
current
draft
is.
K
It
can
also
be
all
the
packets
that
are
traversing
the
same
link
between
two
particular
nodes,
for
example,
because
we
want
to
define
a
property
as
either
the
trade
of
a
path
element
or
a
sequence
of
path.
Elements,
and
this
trade
might
be
related
to
a
certain
flow,
such
as
a
packet
or
multiple
packets
that
are
traversing
this
path
or
a
sub
path
or
a
sequence
of
elements.
And
so
we
get
1/2
elements.
K
L
K
This
was
a
question
that
I
me
and
my
co-author
discussed
and
I
first
had
a
sub
path
in
there
and
then
he
said.
Oh,
but
maybe
you
have
like
just
all
the
routers
that
are
sort
of
behind
each
other
on
the
path
a
tenuous
links
between
them.
But
maybe
you
don't
mean
the
links
are
just
the
routers
and
that's
why
it's
a
sequence.
M
K
They
have
turned
on
it.
That's
in
the
definition-
and
you
might
have
I
mean
you
might
have
a
virtual
link
between
two
nodes.
If
there's
no
physical
link
or
even
if
it's
two
processors
on
the
same
machine,
you
could
define
like
the
sort
of
the
pipe
or
whatever
virtual
interface.
There
is
a
virtual
link,
but
we
actually
wanted
to
keep
the
definitions
or
rigorous,
because
otherwise
you
might
get
nonsensical
pass.
M
K
Wait
wait.
Only
a
node
doesn't
have
to
be
on
layer
3,
it
might
be
a
layer,
1
device
or
layer
2
device
right.
So
there's
there's
nodes
that
are
sort
of
hidden.
If
you
look
at
the
path
on
layer
3,
there
might
be
a
switch
somewhere
in
there
and
you
don't
really
look
at
the
switch
but
yeah.
So
we
have
this
layering
thing
in
the
draft
and
we
were
also
discussing
this.
For
example,
if
you,
if
you
have
some
fiber
optics
and
then
there's
passive
splitter
between
them,
then
it's
not
like.
K
P
K
K
K
B
B
Okay,
if
flow
is
an
entity
made
of
packets
to
which
the
traits
of
a
path
or
set
of
sub
paths
may
be
applied
in
a
functional
sense,
I
have
a
flow.
It's
got.
Packets,
the
packets,
are
formless
and
void,
I,
send
them
down
a
path.
That
path
applies
its
treats
to
those
to
the
to
the
packets
in
that
flow,
as
they
go
past
I'm
sure
we
can
find
some
wording
first.
S
B
J
Hi
Aliyah
Atlas,
so
two
questions,
one
is
you're
assuming
the
endpoint
is
always
a
host
and
wondering
if
you're
deliberately
leaving
out
overlays
because
they're
kind
of
everywhere,
and
so
it
even
if
it's
a
subsection,
that's
indicating
this
is
in
this
is
Allen
I
mean
one
of
the
things
that's
very
interesting,
potentially
at
path.
Panner
G
is
being
able
to
think
about
it
and
improve
benefits
for
overlay
networks.
K
We
have
thought
about
overlays
too,
but
okay
in
our
definition
and
overlay
would
be
a
router
not
a
host
potentially,
but
then
we
have
a
sub
path
between
different
overlays
and
is
that
wasted
problem?
I
mean
you
can
still
define
a
property
for
a
sub
path,
or
maybe
we
need
like
a
hierarchy
of
how
involved
is
the
router
in
or
something
yeah.
J
So
there's
different
pieces
when
you
get
traffic
coming
in
better
flow
as
both
into
an
overlay,
but
you
might
be
taking
that
and
putting
it
into
a
specific
micro
flow
which
is
different
from
the
native
flow
that
it
came
in
you
might.
The
router
may
not
may
use
different
properties
to
head
out
the
outgoing
link
like
it
might
use
the
original
micro
flow
as
opposed
to
the
overlay
micro
flow.
You
may
have
less
flexibility
in
terms
of
what
you
can
do
and
you're
probably
not
running.
You
know
they
put
a
little
bit.
J
Tcp
stack
for
each
of
your
connections,
so
I
think
it
does
have
a
number
of
implications
and
I
guess
the
other
since
I'm
up
here.
But
the
other
question
is,
and
we
keep
talk
about
paths
as
if
they're
static
and
they're,
not
because
you
have
hashing
so
I
think
having
some
way
of
discussing
the
time.
Relevance
of
the
path
definition
might
be
interesting
and
also
sort
of
the
aliveness
of
the
path
right.
Cuz.
That's
one
of
the
challenges.
Is
you
send
traffic
down
the
network
and
God
knows
where
it's
going
for
your
lair
leopard
bag?
J
K
To
you,
thank
you
for
your
comments.
I
think
they're
very
useful.
So
the
first
comment
I
think
this
goes
back
to
our
definition
of
node
and
host
of
hosts
and
routers.
Sorry,
because,
like
it's
addressed
to
a
host
okay
on
what
layer
I
mean,
I
said
that
before
so
yeah
I
guess
we
have
to
think
about
encapsulation
and
the
other
part
was
about
oh
yeah
about
the
path.
So
right
now
the
path
is
defined
as
well.
K
It's
there
and
it's
in
theory,
it's
possible
to
send
a
packet
over
that,
and
then
the
packet
gets
sent
and
yeah.
It
will
take
one
of
the
paths
of
we're,
defining
sort
of
all
the
paths,
and
then
we
have
a
property
may
be
related
to
this
path
that
could
be
used
by
a
packet
or
we
define
a
property.
That's
related
to
a
specific
packet
that
is
going
over
a
specific
path.
I.
K
K
E
K
B
I
had
a
question
and
then
I
have
two
observations.
The
question
actually
I
think
you
could
answer
implicitly
you're,
not
making
any
particular
constraint
on
the
layer
at
which
a
link
exists.
Correct
because
you
referred
to
links
that
might
be
virtual
links
that
are
pipes
which
is
later
negative
for
V.
B
B
But
you
know
when
I
use,
IP
fix
flows
and
I
talk
to
people
who
run
routers
now,
I
go
that's
a
micro
flow.
So
and
now
we
have
a
different
definition
of
flow,
which
is
like
the
integral
of
the
application
of
the
function
of
the
path
elements
creates
DT
according
to
rate
yeah,
so
which
is
a
different
definition
of
a
flow
which
might
actually
be
the
superset
definition
of
all
of
the
definitions
of
flows
in
the
IETF,
the
V,
the.
So
all
of
this
stuff
is
really
hard,
but
it
like.
B
So
you
are
trying
to
define
path
properties,
which
is
a
really
really
easy
definition
like
I,
like
this
definition.
As
long
as
you
have
a
definition
of
sequence,
of
path,
elements
and
flow
right,
like
your
property
definition,
depends
on
these
other
definitions,
which
we
have
never
been
able
to
agree
on.
So
your
challenge,
you
should
you
choose
to
accept
it.
B
T
So
I
think
this
is
wonderful.
We
talked
about
this
essentially
past
definition
and,
for
example,
given
that
is
the
I,
our
research
group
and
oftentimes
I,
guess
fundamentally,
when
first
city's
definition
of
a
past
very
likely,
it
comes
from
graph
theory
right
and
somehow
a
lot
of
debate
in
graphs.
The
oven
time
is.
Do
I
define
bypass
occupy
if
I'm,
by
flow
now
here
the
flow
but
fully
in
context
about
their
busy?
Often
time
is
one
meter
from
we?
Were
you
formulate
a
lot
of
problems
using
path?
T
Is
you
have
a
problem
of
enumerating
exponential
number
of
paths,
for
example?
Look
what
one
example
suppose
here
you
have
one
two
three
four
five
nodes
and
imagine
between
any
two
nodes.
You
don't
have
single
Inklings.
So
therefore,
suppose
you
have
n
nodes.
You're
gonna
have
a
code
of
2
to
n
number
path.
It's
best
explanation,
and
often
time
when
we
dissolve
is
a
problem
time
for
exam.
You
say:
I'm
VI,
I
do
is
I
I'm,
not
a
new
one,
every
single
path
because
exponential
and
then
I
will
use
for
exam
equal
split,
your
hash.
T
Whatever
you
been
told,
it
is
I.
Don't
really
know
Marin
all
expendable
at
this,
and
Airport
really
might
make
my
problem
to
be
essentially
scalable
making
my
measurement
to
be
scalable,
make
my
information
discovery
to
be
scalable
and
so
on.
So
what
I'd
really
be
in
school,
for
example,
that
a
case?
How
do
you
begin
to
model
a
particular
case,
ecmp
and,
for
example,
exponential
number
paths
using
hashes?
So
therefore
you
don't
enumerate
passes
and
essentially
you
make
the
implicit.
Maybe
that's
the
way
you
can
go.
Q
Will
be
a
very
quick
coming,
it's
the
crack
used
again
Union
again
and
I
think
it
was
mentioned
in
the
draft.
Things
are
considered
are
directional,
but
in
our
third
rate
use
case
we
have
huge
asymmetry
between
what
we
receive
and
what
we
send.
There
are
huge
different
characteristics,
so
you
may
want
either
to
say
that
links
are
unidirectional
and
there
may
be
two
links
between
two
nodes
or
clear.
That
is
video
channel.
K
B
Despite
the
fact
that
we
need
work
on
the
definitions,
do
we
want
to
adopt
this
document
with
the
idea
that
it's
essentially
on
track
to
become
the
document
that
we
want,
or
do
we
want
to
basically
send
it
back
and
say,
keep
going
I
mean
I
I.
Think
that
get
the
you
know
get
it
completely
right
before
we
adopt
that.
This
is
a
thing
that
I
actually
do
in
my
working
group.
G
Spencer
mr.
Dawkins
I
would
like
to
see
you
do
a
call
for
adoption.
I
think
one
of
the
things
that
would
make
it
easier
for
Teresa
to
move
forward
on
the
document
is
to
having
more
people
looking
at
it,
which
you
know
when
the
thing
becomes.
A
research
group
document
that
becomes
our
collective
responsibility.
I
think
you
know
one
problem
you
may
be
dealing
with
is
that
you
know
what
you
mean
and
having
more
people.
Look
at
it
that
don't
know
what
you
mean
would
be
a
lot
of
help.
G
Adrian
Farrell
has
the
bring
me
a
rock
of
problem,
which
is
basically
you
say,
bring
me
a
rock
and
I
bring
you
a
rock,
and
you
say:
that's
not
the
right,
Rock
bring
you
another
rock
and
yeah
I.
Think
that
adopting
it
would
get
you
out
of
the
bring
me
a
rock
theory
and
basically
say
you
know
what
you
know.
This
is
the
kind
of
rock
that
we've
got.
This
is
the
kind
of
rock
we're
looking
for
and
it
would
make
it
easier
for
you
to
bring
the
right
rock
back
next
time.
Spencer.
B
J
G
As
soon
as
it
as
soon
as
the
time,
but
you
know
as
soon
as
a
day
but
someday
I-
think
we're
gonna
be
happier
that
we've
got
definitions,
that
we
can
show
people
rather
than
having
them
say.
I,
kinda
kinda
know
it
a
hand-waving
level
what
your
research
results
mean
and
now
I'm
gonna
go
off
an
engineer
based
on
that.
The
ietf.
L
Eric
Kinnear
Apple,
so
I
would
echo
much
of
what
Spencer
was
saying
in
the
sense
that
our
ability
to
communicate
with
other
people
is
going
to
be
much
enhanced
by
having
these
things
defined
and
I.
Think
we've
seen
that
if
you
show
us
something
we
can,
we
can
think
about
it
and
talk
about
it
and
having
it
be.
A
working
group
document
would
help
that
a
lot
and
I
think
it
fits
a
natural
place
in
what
we're
trying
to
do.
This
is
a
research
group.
I
guess
sorry,
pardon
me
you're
right.
L
U
U
What's
on
your
slide,
Teresa
and
and
so
I'm,
you
know
that's
the
engineering
side
of
our
happy
week
here,
I'm
I,
guess:
I'm
wondering
what
value
the
draft
on
terminology
here
in
research
brings,
and
maybe
there
maybe
a
broader
perspective
and
I'd,
encourage
you
to
emphasize
that
as
you
as
you
go
forward,
what
we're
kind
of
bound
in
the
old
world
of
tuples
and
flows
and
stuff,
like
that,
that's
what
our
flow
definition
looks
like.
Maybe
there's
something
more
that
that
you
can
bring
to
the
table
there.
U
B
V
I
can
probably
do
this
in
15
minutes,
so
that's,
okay,
hi
I'm
new
here
I'm,
my
name
is
Tom
cougar,
it's
my
first
ITF
and
so
my
contributions
might
be
maybe
trivial
to
many
people
here
and
also
during
the
past
few
days.
I
had
a
lot
of
fun
and
I
really
enjoyed
the
discussion
culture
here,
but
it
also
caused
me
to
really
completely
rework
this
rework
this
set
of
slides
and
focus
it
a
different
focus.
That's
the
first
disclaimer.
V
The
second
disclaimer
is
that
I'm
sort
of
involved
with
a
scion
project
that
Brian
was
also
involved
in
and
this
might
color
my
perception
of
what
hathaway,
networking
or
hide
might
look,
and
so
I
might
have
some
implicit
assumptions
that
might
not
be
generally
applicable,
but
here
I.
Just
let
me
continue.
I
had
looked
at
the
questions
draft
and
in
particular
the
questions
2.7
and
2.8,
which
I
would
like
to
paraphrase
so.
A
question.
V
2.7
is
how
can
a
pathway
network
reconcile
the
apparent
conflicts
of
intent
between
and
between
endpoints
and
the
network
instead
of
fair
summary
of
that
paragraph?
Would
you
say:
okay
and
the
question
2.8?
How
would
we,
in
the
interest
of
the
network
operators
just
render
path,
selection
or
authority
to
the
endpoints?
So
when
we
are
given
the
endpoints
the
opportunity
to
decide
what
they
would
like
to
what
past
I
would
like
to
take,
then
the
networks
can
then
go
ahead
and
not
respect
this
decision.
V
At
least
this
is
how
it's,
how
Scion
is
designed
where
actually
the
networks
can't
really
change
anything,
but
might
not
be
that
clear-cut
in
general,
so
I
asked
myself,
doesn't
don't
these
two
questions
all
relate
to
the
question
of
how
paths
election
in
particular
is
to
be
implemented
on
the
endpoints?
What
kind
of
behavior
do
the
endpoints
actually
should
they
use
them
right
now?
It's
sort
of
to
my
mind.
V
It's
kind
of
glossed
over
and
the
endpoints
will
do
the
right
thing
or
the
thing
that
is
in
the
interest
using
this
information
that
they
get
but
and
I
found
in
it.
You
just
draft
I
found
the
following
yeah
requirement
that
says
an
endpoints
path.
Selection
algorithm
should
aim
to
not
perform
worse
than
the
default
case.
Okay,
that
you
can't
might
construe
this
as
a
sort
of
requirement
for
the
endpoint
as
a
Coralie.
I
would
also
say
that
possibility
should
not
be
to
the
detriment
of
the
network
in
the
default
case.
V
So
and
I
would
sort
of
I
hope.
Everyone
knows
this.
Guy
Americans,
who
said
so
I
could
only
according
to
that
Maxim,
whereby
you
can
at
the
same
time,
will
that
it
should
become
a
universal
law.
It
was
kind
of
mouthful,
but
maybe
we
should
the
path.
Selection
behavior
still
needs
to
work
when
a
significant
number
of
endpoints
use
the
exact
same
behavior,
and
thereby
it
must
account
for
the
fact
that
it
might
be
in
ubiquitous
use
and
might
thereby
have
effect
effects
on
the
network
itself.
V
In
being
able
to
cheer
for
the
next
goal,
and
it's
sort
of
two
myths
here-
that
naive
strategies
fall
on
their
faces
right,
they
are
likely
to
lead
to
wild
oscillations
and
I've,
build
a
test
bed
where
I
had
a
toy
path.
Where
network,
where
I
could
actually
demonstrate
that
using
these
naive
approaches,
I
could
show
that.
V
Actually
you
get
these
problems
with
oscillations
where,
when
everyone
in
the
network
is
using
the
same
strategy
to
act
on
those
path
properties,
the
changes
that
they
caused
in
them
on
the
paths
lead
to
feedback
loops
that
are
kind
of
hard
to
dampen.
Actually,
so,
even
when
you
introduce
a
dampening
factor
and
say,
okay,
I
only
switch
away
with
a
very
low
probability
when
I
find
out
that,
there's
that
the
other
path
looks
better,
you
still
get
these.
V
Is
always
beneficial,
so
maybe
there
should
be
guidelines
for
path.
Selection,
behaviors
and
I
would
like
I
would
like
to
post
a
question
to
the
audience.
Maybe
we
need
to
is
this
might
be
part
of
the
become
part
of
the
questions
draft
that
the
actual
behavior
for
for
path
selection
should
not
be
out
of
scope
for
us
or
I
mean
the
the
other
question
that
we
might
have
to
ask
when
we
say
okay,
we
don't
want
to
specify
this.
We
don't
want
to
constrain
path,
selection
itself.
V
We
want
people
to
to
be
able
to
do
what
they
want,
but
then
we
have
to
ask
should
be
okay
for
networks
to
misrepresent
the
path
properties
depending
on
who's
asking.
So
this
is
in
a
world
where
the
networks
are
communicating
the
path
packages
and
I,
don't
measure
them
or
any
way.
So
I
can
query
the
network
for
properties,
but
when
I'm
not
being
smart
with
this
these
properties,
then
it's
in
the
interest
of
the
network's
to
maybe
you
start
lying
about
them
so
and
I
would
like
to
posts.
Question
should
path
properties
should.
V
K
J
K
I
just
wanted
to
say
this
is
probably
related
to
question
2.3
as
well.
How
can
an
endpoint
select
path
to
use
in
a
way
that
can
be
trusted
by
both
the
network
and
the
endpoint?
As
what
I
wrote
down
for
question
2.3,
there
might
be
an
addition
to
a
question
two
point
three
in
the
questions
draft
in
there
and
there
might
be
potential
thinking
about
answers.
K
V
J
O
Historical
that
we
can
do
is
that
in
car,
true,
only
in
car
traffic
and
variation
of
five
percent
generates
a
traffic
jam
and
this
the
issue
you
bring
and
the
consequences
are
really
similar
to,
for
example,
if
we
change
the
routing
path.
So,
yes,
yes,
yes,
definitely
any
functionality
allowing
to
change
a
path
from
the
end
points
should
be
moderated.
There
should
be
a
moderation
function
that
with
all
those
histories,
thresholding
and
stuff,
like
that.
Definitely,
yes,.
B
My
brand
Dremel
individual,
thank
you
very
much
for
giving
me
a
chance
to
cite
Kant
in
art
and
an
internet
draft
I.
Think
I
will
actually
add
this
categorical
imperative
thing
to
one
of
the
questions.
I
think
the
two
point
three
is
probably
to
collect
one
one
question
that
I
would
have
for
you
I
think
this
is
this
Avella
velan
valuable
contribution?
Thank
you
very
much
for
bringing
it
I'm,
not
sure
what
the
ask
is
I
mean.
Do
you
do
you
want
to
turn
this
into
a
draft
and
and
run
it
here?
B
B
Loop
problems
different
in
a
path
aware
network
compared
to
a
current
network
where
this
information
comes
from
measurement
great
and
that's
actually
I
think
the
question
that
we
need
to
distill
your
questions
down
into
and
that's
a
question
that
we
need
to
address
because
I
think
a
lot
of
the
the
things
raising
of
like
naive
strategies
with
with
bad
feedback.
Our
questions
who
run
into
an
engineering
in
the
transport
area
before
right.
B
B
Hey
this
is
a
new
thing.
It
really
isn't
and
it
looks
a
lot
like
you
know,
so
the
graphs
that
you
showed,
if
you
like,
take
off
the
X&Y
label
axes
and
the
labels
at
the
top
I've
seen
those
graphs
before
in
in
Isis
your
G,
for
example,
right
like
so
where
you
get
these
things
are
doing
naive
things
with
that
feedback.
Then
they
do
this.
It's
exactly
the
same
thing.
So
I
think
it
would
encourage
you
to
take
a
little
bit
more
into
what's
what
the
specialness
of
path
aware
networking
is
there.
W
I
Right
to
the
question
so
I
think
the
second
question,
while
it's
interesting
I'm,
not
ready
for
that
one
yet
because
actually
going
back
to
the
first
question
of
what
we're
talking
about
here
like
shoe,
we
be
doing
this
I.
Think
that's
you
know,
so
something
that's
very
interesting
and
I
totally
agree
with
what
Brian
said.
I
came
up
here
to
say,
like
oh,
this
looks
very
similar
to
the
graphs
we
would
see
in
ICC,
RG
and
like
this
could
be.
I
Selection
on
these
and
kind
of
that
extra
dimension
of
that,
so
I
think
figuring
out
a
way
to
make
this
more
rigorous
and
maybe
to
the
point
of
getting
advice
and
stuff
from
other
groups.
Well,
we
have
other
groups
that
are
doing
explicit
path.
Selection,
let's
say
MPT
CP
doing
work,
especially
if
we
start
doing
PVD
stuff
and
multiple
up
links
on
the
same
local
network,
where
we
are
starting
to
do
more
explicit
path.
Selection
have
that
work
could
be
demonstrated
here
and
also
do
more
experiments
in
conjunction
with
that.
M
M
The
question
is:
is
this
a
right
method,
you're
working
on,
or
should
you
have
some
kind
of
derived
metric
that
you
can
be
honest
about
and
I
think
this
is
one
of
the
core
questions
we
have
what
are
the
right
metrics
and
if
the
right
metrics
from
an
observation
or
measurement
point
of
view
lead
to
oscillation
to
control?
Is
it
the
right
metric
to
decide
upon
or
do
we
need
some
derived
metric
or
something
completely
different
to
act
upon
at
therefore
not
lying
pleased
but
being
honest
and
finding
out
whether
that's
useful
yeah.
X
R
Okay,
my
name's
John
border
I'm
actually
got
to
go
through
the
early
slides
about
how
the
test
is
set
up.
Quick,
cuz
I
want
to
get
to
the
path,
a
where
question
that,
towards
the
end
of
my
presentation
and
spends
time,
I
reread
the
questions
document
last
night
which
raised
the
question
in
my
mind
whether
this
fits
and
also
some
comments
about
RTT
rates.
Question
in
my
mind
about
where
this
fits.
R
So,
basically,
you
know
we're
what
we're
trying
to
do
is
you
know
we
have
split
CCP
pep.
We
can't
do
that
anymore,
it's
quick,
so
we
need
to
be
quick
to
perform
well
without
the
solution.
So
why
now
we
were
doing
some
tests
to
see?
Well,
what's
the
disparity,
what
can
we
do?
Fsk
pepco
versus
what
it's
quickly
right
now,
so
I'm
not
gonna,
really
go
over
this
slide.
This
is
just
a
test
setup.
We
have
it's
in
the
slides.
R
R
So
you
know
we
did
what
1.1
hb2
with
TCP
spoofed
and
then
of
course,
quick
and
then
we
also
did
without
TC
v
spoof,
and
we
have
a
one
gig
connection
to
the
Internet,
so
we're
trying
to
test
high-end
stuff.
How
fast
can
we
go
not
with
real
plans
in
place
and
that's
one
of
the
reason
we're
using
a
day,
delay
box?
We
have
our
own
network,
but
if
we
did,
we
would
be
limited
to
planned
rates
and
we're
not
trying
to
do
that
right
now
and
then
we
also
are
interested
in
packet
loss
rates.
R
So
here's
some
preliminary
results
so
with
you
know,
with
TCP
spoofing
stays
our
we're
way
over
200
megabits.
Okay,
we
could
do
that
pretty
easily,
but
we
switched.
We
did
the
1.1
2.0
because
we
discovered
that
2.0
has
flow
control
inside
of
it.
So
we
actually
did
that
first
and
wonder
why
we
couldn't
get
part
200
megabits,
and
so
that's
what
we
have
results
for
both
when
you
run
direct
you
can
see
when
there
is
no
pet
there.
R
R
Talk
about
the
part
of
it,
so
what
we
are
interested
in
is
we
want
quick
over
satellite
to
be
just
as
fast
as
we
can
spoof
things
today.
You
need
a
very
large
window,
that's
part
of
getting
to
the
high
speed,
but
you
also
need
some
kind
of
optimized
packet
loss
recovery.
So
an
FEC
solution
or
something
some
kind
of
local
thing
you
know,
but
the
problem
is,
if
you
tune
quick
for
those
properties.
R
R
What
I
was
reading
the
draft
and
talking
about
are
cutie
what
I'm
really
trying
to
do
with
what
I'm
saying
here
is
I'd
like
to
know
and
before
I,
even
get
my
first
connection,
that
I'm
in
this
environment
and
be
aware
and
bring
up
so
I
could
come
up
and
be
great
performance
from
the
start.
One
option
is
I,
can
learn
and
remember,
and
certainly
that's
another
path
that
I
think
has
to
be
explored,
but
that
doesn't
you
know,
learning
and
remember
thing
isn't
really
fit
in
was
I.
R
Think
the
the
general
questions
of
path,
awareness
as
I
understand
them
now.
I
still
think
it's
important
work,
but
it's
not
clear
to
me
whether
how
well
that
fits
in
here
there
was
a
section
on
their
early
questions
about
being
aware
of
the
this
kind
of
stuff.
But
so
it's
not
really
clear
to
me
but
we're
that
is
that
the
only
other
thing
is
yeah
we're
doing
for
collaborating
with
other
people.
R
On
this
testing,
you
really
would
like
to
find
somebody
who
has
a
high-speed
connection
to
a
quick
enabled
server
on
the
internet
so
that
we
could
have
better
control
test
with
the
congestion
control
part
of
it.
So,
if
anybody's
interested
in
doing
helping
us
do
some
of
these
tests,
you
know
please
come
and
contact
me.
So
I
went
kind
of
fast,
because
I
wanted
also
leave
time
for
Nicolas
to
have
more
time
he's
got
more
details
than
I
do.
But
if
anybody
has
any
questions.
K
K
R
This
picture
shortest
can
show
me
the
link
between
the
hughster
Monteux
at
the
top
and
that
other
guy
is
generally
gonna,
be
Wi-Fi.
Well,
loops
doesn't
go
to
the
end
host,
so
I
have
no
way
to
recover
that
link,
and
that's
actually,
where
most
of
my
packet
loss
is
these
days
and
that's
what
the
pep
is
doing
for
me
is
this:
give
me
that
local
recovery,
when
I,
throw
quick
into
the
path?
It's
not
there
anymore.
R
K
R
I
talked
to
them
about
that
and
it's
sort
of
a
later
phase,
but
you
know
it's
definitely
I'm
looking
at
the
tool
toolbox,
and
so
that's
definitely
on
my
radar
look
like
I'm.
Also
looking
at
you
thinks
we
can
do
inside
a
quick
and
be
you
know
at
least
the
learning
part
of
it
and
figure
out
you're
there
and
then
do
something,
but
I
still
have
that
the
packet
loss
thing
is
the
one
that
concerns
me
the
most
because
of
that,
in
the
end
time
it
takes
to
recover
from
packets
packet
loss.
W
I
Colin
Perkins
as
as
an
individual
I,
mean
I
kind
of
want
to
take
your
theories.
I
just
said
you
know
hey,
it
would
be
better
if
quick
could
solve
this
problem
without
needing
things
like
loops,
but
suddenly
from
talking
to
the
loops
people.
It
does
seem
that
that
they're
open
to
considering
this
use
case.
P
B
P
R
J
Y
J
Y
J
R
Y
P
B
You
very
much
for
this.
Thank
you.
I
will
note
that,
because
of
our
unfortunate
conflict
that
most
of
the
people,
who
would
be
able
to
answer
your
question
about
getting
you
access
to
quick
end
points
are
probably
not
here
so
I
would
take
that
to
the
the
maybe
the
quick
and
the
TSB
aerialists,
as
well
as
the
apparent
well
or
even
just
awesome
at
energy.
Let's
do
the
same.
B
L
B
Q
Q
We
all
have
these
trendy
information
about
anonymous,
trying
to
sound
to
send
thousands
of
satellites,
but
today's
is
high.
Broad
bond.
Do
constellations
are
not
really
operating
today.
What
we
see
what
we
use
today
for
city
internet
access
is
mostly
geo
based
satellites.
We
have
large
cooperation
delay
and
come
again
which,
against
which
we
can
do
much,
and
we
have
I
lost
weight
when
you
are
moving
in
the
tree
or
when
you
are
behind
the
Wi-Fi.
But
this
point
I
want
to
make
here
we,
unless
you're
in
India-
and
it
rains
a
lot.
Q
We
don't
have
losses
on
the
satellite
link.
Losses
comes
after
from
the
satellite
terminal
to
the
end
user.
So
that
is
why
I'm
here
we
have
and
also
a
point
I
wanted
to
make
on
asymmetry
I
made
earlier
on
our
link
for
various
metrics,
both
systems
of
capacity
on
the
GTA
on
the
link.
So
that's
we
have
these
strange
things
and
if
you
are
interested,
I
had
a
look
at
these
old
air
Fe
from
the
Pips
working
group
and
most
of
the
descriptions
on
today,
things
you
can
find
it
there
in
still
Elevens.
Q
So
if
you
have
more,
if
you
want
more
info
on
satellite
links
here,
you
have
so
we'll
go
quickly
on
that
satellite
systems
is
a
point-to-point
link
or
mostly
used
for
TV
broadcast
as
well
and
the
problem
is
we
see
a
lot
of
trends
in
the
market
in
doing
backhaul,
and
so
we
have
lots
of
different
IP
networks
which
are
back
old
with
satellite
accesses.
So
the
satellite
IP
network
is
only
one
part
of
the
end-to-end
path,
and
so
the
problem
is
we
have
this
long
delay
link
low.
Q
We
don't
have
losses,
we
have
a
long
delay,
but
then
we
have
to
interconnect
it.
We
just
with
networks
which
have
very
different
characteristics
and
I
think.
This
is
why
this
use
case
is
interesting
for
this
group,
because
this
is
somehow
a
corner
case
for
the
internet
access,
but
for
our
users
this
is
very
important,
so
we
have
been
seeking
on
what
we
can
do
to
improve
quick
for
SATCOM.
That
is
something
we
have
been
starting
to.
Q
Think
of,
we
didn't
make
any
publicity
for
that,
because
we
wait
for
quick,
v1
and
proper
quick
implementations
to
make
clear
best
curing
practices.
We
are
not
there
yet
so
just
from
our
brainstorming
ideas.
We
have
here
at
the
moment
and
I
will
show
you
some
results
on
how
we
can
actually
tune
parameters
on
what
we
have
done.
Adamant.
Q
I
liked
the
point
on
discussions
being.
We
are
open
for
discussion.
If
you
want
to
discuss
with
us,
we
are
open.
We
have
github
issues
everything,
so
if
you
want
to
join
the
party,
please
welcome.
We
have
things
flying
in
the
sky
that
very
funny
to
play.
With
first
thing
we
always
think
of
is
initial
window.
So
I
will
we
have
two
different.
Q
We
have
been
using
quick,
go
implementation
and
all
the
version
I
don't
have
the
number
in
my
head
at
the
moment,
and
so
basically
we
have
the
default
parent
revision
and
we
have
changed
lots
of
things
and
mostly
is
a
maximum
congestion
window
and
and
also
the
initial
condition
window.
So
the
first
point
here
is
to
speak
about
the
initial
condition
window
and
we
have
done
some
tests.
So
these
are
the
traffic
patterns.
Q
I
don't
have
time
to
go
deep
into
that,
but
we
have
short
files,
medium
files,
large
ones,
and
we
play
with
mix
of
them
and
the
main
point
I
want
to
make.
Is
we
have
the
attitude
of
600
milliseconds
on
the
left
and
if
you
look
at
the
results
on
the
and
here
medically,
when
you
have
large
files,
we
have
lots
of,
we
might
adapting
and
tuning
the
quick
stack.
We
have
lots
of
games
and
also
what
is
funny
to
see
that
this
parameterization
does
not.
Q
We
do
not
have
an
impact
on
the
lower
DTE
case,
so
we
think
trying
to
think
of
our
pro
use
case
when
doing
evaluations
in
quick
may
be
relevant
for
everyone,
and
indeed
we
can
see
that
increasing
the
initial
condition
window
helps
in
reducing
the
doubling
time
of
an
object.
But
people
don't
like
high
initial
condition
window
because
they
say
we
are
sending
bursts
of
packets
in
the
network,
and
that
is
bad.
We
agree
with
that.
Q
So
that's
something
work
that
is
going
on.
We
we
wait
for
the
quick,
though
we
want
to
provide
based
on
parties
on
at
least
make
people
aware
of
our
use
case
when
you
do
quick,
parameterization
in
your
CDN
centers,
and
if
I'm
here
is
to
speak
to
you
about
the
losses
on
satellite
terminal
we
have
so
this
is
a
real
satellite
gateway.
We
have
a
real
satellite
in
the
in
the
sky
and
satellite
terminal
and
we
connect
to
computers.
We
don't
have
TCP
split
solutions.
Q
We
have
an
two
megabytes
transfer
and
we
just
induce
one
percent
losses
between
these
two,
the
terminal
and
the
end
user,
and
what
we
see
from
our
result
on
the
left.
You
have
the
CDF
of
the
page
loading
time
of
these
two
megabyte
subjects
and
on
the
right
we
have
losses,
one
percent
classes,
and
we
can
see
that
in
our
case,
when
you
have
in
sequence,
networks
with
very
different
characteristics
that
are
not
communicated
to
the
favor
and
not
meeting
server,
do
not
provide
any
things
to
mitigate
these
problems.
Q
To
be
fair,
we
have
also
considered
congestion
losses,
because
we
know
that
they're
not
only
loss
losses
that
are
due
to
the
wireless
part,
but
also
losses
due
to
congestion
in
the
network,
and
so
to
be
fair.
We
wanted
to
see
the
impact
of
congestion
on
these
results,
and
what
we
have
seen
is
that
we
have
an
increase
in
the
demand
in
time
when
you
have
congestion,
but
it's
a
very
less
important
magnitude
and
the
Wi-Fi
losses.
Q
So,
in
short,
this
is
an
early
work
on
quick
paralyzation.
We
have
the
draft
collaboration
use
welcome
if
you
want
to
help
us,
we
think
that,
maybe
for
the
moment,
we
want
to
focus
on
the
satellite
use
case,
but
if
you
we
think
that,
having
based
on
parties
on
how
you
parameterize,
quick
or
wider
internet
is
very
relevant,
so
we
still
need
further
indications
and
that's
just
ongoing
work
and
to
go
back
to
one
of
the
things
we
can
do
to
mitigate
these
Wi-Fi
losses.
Q
We
often
mention
the
fact
we
know
lots
of
people,
don't
like
fake.
So
that's
why
we
have
been
also
following
what
has
been
done
in
masks
this
morning
when
we
think
that
when
submission
can
occur
between
satellite
communities,
any
other,
we
don't
know
actually
how
all
the
implications
on
that,
because
I'm
not
a
mask
specialists
vola.
We
are
looking
at
ways
of
improving
this
use
case.
