►
From YouTube: IETF105-ACME-20190722-1000
Description
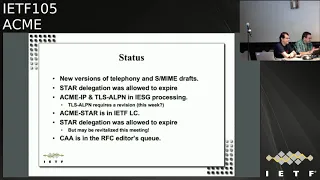
ACME meeting session at IETF105
2019/07/22 1000
https://datatracker.ietf.org/meeting/105/proceedings/
C
Hi
we
need
somebody
to
take
minutes,
just
record
actions
and
somebody
to
be
the
jabber
scribe
for
the
6-8
people
that
are
currently
in
the
jabber
room,
at
least
to
our
remote
any
volunteers.
Obviously
we
can't
start
until
we
get
those
volunteers
and
yo
points
out
that
our
agenda
has
shrunk,
so
we
have
about
20
minutes
free
time,
so
we
can
just
sit
here
waiting
for
two
people
of
our
volunteer
for
nearly
half
an
hour.
If
that's
what
it
takes.
C
C
A
On
the
agenda
today,
obvious
gender
bashing
administrivia,
that's
the
streets
going
around
and
finding
scribes
and
mayor
takers,
and
the
note
well,
which
we
have
already
seen,
then
we're
going
to
do
in
status.
Update
I'm
gonna,
get
update
on
telephony
with
no
slides
from
John,
and
we
had
planned
to
have
a
presentation
about
TLS
LPN.
But
since
neither
Rowland
nor
Jacob
are
in
or
in
Montreal
and
they
haven't
sent
slides
jacob
is
the
jabber
room.
C
A
A
C
E
F
A
E
A
G
G
Last
year,
so
it's
not
like.
We
have
something
particularly
new
to
present
at
this
point.
That's
hardly
because
actually
changes
that
we're
still
contemplating
these
faster
president.
At
this
point,
our
thing
is
that
have
yeah
versions
pendency.
These
are
decisions
that
were
still
kind
of
rolling
over
in
the
storica
group.
I
just
be
an
example
of
one
of
these.
We
have
this
thing:
that's
in
Mersin
TP
from
six,
that's
called
JWT
constraints,
and
this
gets
really
into
no.
We
were
just
up
in
aster
uses
these
certain
and
passports
right,
passports,.
G
It
might
be
handy,
actually
have
the
token
authority
be
able
to
issue
those
constraints.
When
you
know
someone
is
trying
to
get
a
passport
I
trying
to
get
a
certificate
back
mean
so
as
a
consequence
of
that,
we're
still
kind
of
mulling
that
there's
a
particular
use
case
for
it.
That's
associated
with
our
rich
call
display
draft
our
CD,
but
our
CD
is
kind
of
still
in
flux.
G
At
the
moment,
once
I
think
we
know
where
we're
gonna
land
on
that
we'll
be
able
to
decide
whether
we
want
this
JWT
constraints
actually
be
part
of
the
ATC
that
we
have
developed
here
in
the
Acme
working
group
or
not,
and
so
you
know
that
that's
pending
otherwise
I
think
these
graphs
are
in
pretty
good
shape
at
this
point
and
so
yeah.
Well,
we'll
be
back
with
that.
We
may
do
that
like
later
this
week,
just
bang
this
out
and
put
a
new
version
into
the
repository.
G
G
A
H
H
They
use
it
because
thinking
of
the
scenario
of
typical
scenario
of
a
CDN,
the
idea
that
we
split
80
at
the
document
into
to
start,
this
went
on
its
way
and
is
close
to
be
published,
and
the
case
of
the
delegation
was
part
of
another
of
another
document
that
originally
the
group
asked
us
to
to
go
to
sec
dispatch,
to
see
whether
this
is
something
that
belongs
to
what
may
or
it
was
something
that
to
be
considering
another
in
another
group.
They
point
the
conclusion
from
sex
dispatch
was
to
bounce
us
back
here
so
here.
H
Well,
here
we
we
came
some
time
ago.
The
draft
was
adopted
and
let's
interrupt
a
little
bit
about
the
story,
because
we
will
talk
about
why
it
was
expired.
Basically,
it
rose
about
an
identity
owner
that
receives
a
request
for
delegation,
typically
think
of
a
CDN
node
that
wants
to
use
the
certificate
for
for
the
identity
owner
without
exposing
private
keys
or
whatever.
So
what
the
entity
owner
does
is
precisely
request
for
that
for
a
four
star
certificate,
a
temporaries
at
the
temporary
certificate
using
Acme
and
the
NDC.
H
The
name
delegation
client
pulls
the
certificates,
a
temporary
certificates
and
use
it,
allowing
the
the
identity
owner
to
revoke
them
immediately
without
sending
a
revocation
but
just
stopping
the
the
serving
Yule.
This
is.
This
is
basically
the
the
idea
is
that
well,
there
is
a
request
that
goes
with
the
see
Assad
that
has
to
go
from
the
NDC
up
to
the
I.
Do
that
is
the
one
that
makes
the
request
and,
and
since
he,
at
the
URL,
for
pulling
the
certificates,
the
private
keys
never
left,
never
leave
the
be
NBC.
H
No,
the
any
any
private
material
from
the
identity
on
research
force
is
only
that
the
identity
owner
express
as
willingness
of
via
of
the
certificate
being
generated.
The
reason
this
is
something
that
we
discuss
or
challenges.
Why
is
important?
Just
another
I
say
this
precisely
because
typically
and
NDC
and
an
idea
or
are
living
in
different
domains
and
their
relationships
is
not
precisely,
an
internal
is
not
well
state
goes.
H
G
H
G
Definitely
you
know
we
have
no
real
story
about
how
to
do
like
shortly
stuff
with
anencephaly
I
think
there
is
an
overlap.
I
know
one
constraint
that
is
unusual
for
a
starship
obligation
is
we
want
to
be
able
to
narrow
the
namespace
of
these
locations
was
used,
something
like
yeah,
an
accomplishment
that
you
support,
that
G's.
G
H
H
H
Now
there
are
a
few
things
that
we
have
in
mind:
one
is
about
the
composition
patterns
with
the
other,
how
we
combine
the
flow
for
delegation
with
the
flow
for
the
agree,
star
requirements
once
that
the
ACMA
star
flow
is
skia.
Second,
is
precisely
the
naming
interactions
were
John
was
mentioning
it's
about
how
you
narrow,
or
within
the
weather,
than
the
the
way
in
which
you
interact
with
the
identify
mapping
system.
H
One
is
steel
and
possess,
so
it
is
a
abstraction
from
DNS
in
that
it
would
be
wider
in
terms
of
a
generic
naming
Authority
and
making,
because
star
delegation
considers
DNS
specific
things
that
we
should
have
to
make
optional
or
bring
some
mapping
in
the
case
of
a
CD.
An
idea
is
that
suppose
the
the
is
that
there
is
a
upstream
CDN
that
is
delegating
some
access
to
a
downstream
CDN.
So
it
is.
H
H
I
J
There's
a
couple
of
related
drafts,
so
recapping
cathing
have
drafts
here
and
we
have
had
some
and
these
drafts
cover
client,
enrollment
and
device
one
first,
if
could
use
an
acme,
and
we
have
some
pretty
many
discussions
about
alignment
to
these
three
drafts.
I
went
to
the
site
meeting
scheduled
so
anybody
who's
interested
in
using
acne
for
issuing
client
and
device
certificates.
Please
attend
the
site
meeting,
so
lots
of
them
inserts
for
product
remanded.
J
If
you
read,
if
you
read
the
draft
in
detail,
a
key
mandates
that
the
identifier
in
the
CSR
must
match
it
and
for
in
the
new
order
request
and
the
identifier
and
the
authorization
object
must
be
used
when
fulfilling
HTTP
or
Tina's
challenges,
Arachne
does
not
mandate.
Is
that
the
identify
new
order
request
matches
to
identifier
in
an
authorization
object?
J
So
what
this
means
for
a
CA
if
I
ca,
implementing
a
controls
to
do
so,
an
acting
server
could
issue
certificates
for
a
subdomain
if
declined
to
only
fulfills
a
challenge
for
the
parent
domain,
so
this
is
actually
technically
allowed
by
the
Acme
draft
of
ran
through.
This
is
Richard
this
way
Richards
on
the
co-authors,
and
we
think
this
is
an
interesting
use
case.
J
If
an
ACME
C
is
willing
to
allow
a
policy
like
this,
and
so
what
that
would
mean
is
that
an
ACME
client
could
prove
ownership,
fulfill
a
challenge
for
a
parent
domain
and
then
issue
a
larger
number
of
client
certificates
or
subdomains
of
that
parent
domain,
which
is
a
nice
optimization.
It
reduces
all
DNS
of
traffic
and
challenges.
J
So
what
this
culture
looks
like
for
supplemental
pre-authorization
and,
on
the
left
hand
side
with
the
standard
floor
for
pre-authorization
of
parent
domain
and
declined
post
the
new
authorization
endpoint,
and
if
you
run
through
the
steps
there,
it's
straight
out,
yacking
standard
and
the
client
just
proves
ownership.
A
for
parents
to
me
in
the
example
that,
given
this
domain
calm
and
there's
nothing,
the
draft
that
precludes
step
two
happening
and
step
two.
J
J
We
think
that
the
teach
standard
is
actually
under
specified
at
the
moment,
and
the
teach
standard
doesn't
really
deal
with
how
the
tip
server
should
react
and
how
the
client
should
react
if
the
tip
server
is
not
able
to
fulfill
that,
because
he
is
10
requests
straight
away.
There's
no
back
off
mechanism,
doesn't
all
the
retry
mechanism,
so
he
believed
the
tip
is
currently
under
specified
and
the
subdomain
proposal
is
a
nice
optimization.
J
It
reduces
to
round
trips
that
would
be
required
if
you're
using
Acme
for
certificate
issuance
sort
of
the
for
client
use
case
is
the
only
one
I've
documented
here
is
the
use
tqi
opinion.
These
culturals
were
taken
straight
from
the
draft
on
the
left-hand
side
to
step
on
the
pre-authorization
of
the
parent
domain.
It's
all
very
standard
than
the
example
of
given
as
pre-authorization
of
domain.com
and
on
the
right
hand,
side
home,
showing
his
de
client
interaction
with
the
east
tra
and
the
client
just
sends
a
standard.
J
The
pre-authorization
involves
an
interaction
with
dns,
but
for
actual
certissue
ins,
there's
no
interaction
with
TS,
there's,
no
authorization
challenges
required
and
for
issuing
a
certificate
should
be
faster
and
should
be
more
scalable
and
once
the
acme
server
is
issued,
the
certificate
to
the
RA
and
after
the
client
that
we
trained
for
this
has
expired.
The
client
should
also
simply
unroll
and
retry,
and
then
the
RA
can
just
issue
the
search
straight
to
the
client.
Then
so
that's
it
really
short
presentation
and
pretty
simply
use
cases
for
interesting
use
cases.
J
So
the
two
main
things
won't
stock.
What,
as
one
is
to
solve
the
menus
case
of
interest
to
acne
series,
and
if
it
is,
is
it
what
formely
documenting
because
it's
currently
allowed
by
the
acme
traffic?
But
it's
not
immediately
obvious
and
our
de
client
and
device
use
cases
of
interest
to
any
other
implementers.
So
a
version
of
this
presentation
is
going
to
be
given
that
amuse
in
you
sessions
as
well,
and
we
have
the
side
meeting
on
Wednesday
mornings,
so
anybody
who's
just
please
come
to
the
second
meeting
mr.
morning.
That's
it!
H
K
Ranked
rants
levy
Google,
so
the
value
in
the
subdomain
just
working
is
valuable
in
that
it
aligns
with
public,
see
Asians
I.
Don't
want
to
suggest
that
hacking
is
only
intended
for
public
CAS,
but
it
is
a
nice
side
effect,
which
is
that
a
public
CA
has
to
follow
baseline
requirements
of
recurrence,
and
this
is
an
existing
pattern
that
many
CAS
using
can
use
so
there's
value
in
documenting
it.
K
The
only
caveat
I
throw
out
there
is
that
in
a
world
of
increased
automation,
which
is
a
desirable
world
of
reduced
life
time
for
certificates
across
the
board
in
the
industry
and
again
I'm
only
speaking
about
public
certificates
or
private
ticket.
It's
not
is
this,
maybe
profiled
out
in
a
future
point
rank,
which
is
there
there's
value
in
actually
having
the
domain
authentication
bound
to
the
specific
domain.
So
it's
possible
and
I
say
this
on
the
order
of
many
years.
K
You
know
that
this
gets
profile
out
in
terms
of
public
see
days,
but
I
don't
think
that
precludes
documenting
it.
Now,
as
this
one's
with
public
practice,
this
can
be
used
for
a
number
of
interesting
use
cases
when
you're,
using
acting
with
some
of
these
other
use
cases.
So
that's
just
a
caveat
that
I
put
out
there
is
that
it
may
be
that
in
the
future,
Acme
implementations
being
used
for
public
CAS,
don't
use
this
feature
and
so
any
documentation.
It
would
be
useful
to
at
least
keep
in
mind
that
we
made
profiler
sure.
J
L
Right
this
time,
I
only
updated
one
of
the
documents
which
is
s/mime.
I
think
this
is
getting
closer
to
being
done
next
slide,
so
just
don't
mind
people
what
this
is
trying
to
do.
This
is
basically
to
be
able
to
issue
ex-prime
certificates
for
and
user
for,
email
addresses.
The
way
it
works
is
that
the
challenge
is
sent
in
an
email
in
the
subject
of
email
that
can
be
verified
as
coming
from
their
Akhmatova
email.
L
L
Sort
of
had
a
lot
of
you
know
open
issues
in
the
document
about
how
you
verify
that
email
is
challenging.
Mail
is
coming
from
a
cui
server,
how
you
verified
response,
and
there
was
also
some
questions
about
specific
email,
details
about
format
and
I
was
trying
to
balance
about
between
making
it
very
simple
to
implement
for
email
clients,
but
also
trying
to
make
it
usable
for
wide
variety
of
existing
email
clients
and
existing
libraries.
L
L
Yeah,
basically
because
of
polling
length
limits
in
our
email,
specs,
it's
likely
that
subject
line
is
going
to
be
folded.
It
means
that
encoded-word
specification
has
to
be
used,
so
I
initially
didn't
want
to
use
it,
but
I
think
it's
unavoidable,
so
basically
IRC
twenty
to
thirty
one
needs
to
be
used,
but
this
is
unlimited
to
utf-8
Oh
us
a
sketch
char
sets.
So
we
don't
want
people
to
require
to
implement
various
other
things
and
then
yeah
similar
thing
for
responses
and.
L
Then
basically,
there
was
a
man
in
this
discussion
about
how
do
you
actually
verify
that
email
challenge
is
coming
from
Acme
server
and
tradition?
Two
ways
of
doing
this.
An
email
is
a
the
dekum
signing,
because
the
challenge
itself
in
the
subject.
So
you
want
to
sign
that
it's
coming
from
from
address
associated
with
the
Acme
server
assigned
the
subject
and
few
other
header
fields
or
you
can
use
as
mine,
signing.
L
With
the
responses
is
more
difficult
because
you
don't
want
to
use
s
mine
for
responses,
because
the
whole
point
of
this
is
to
get
a
smile
too
difficult
to
be
able
to
do
that,
among
other
things.
So,
for
responses
is
probably
just
Hakeem
signing
and
make
sure
that
SPF
and
de
mark
and
various
other
things
in
use
work
right
next
slide.
L
Yeah
I
got
a
couple
of
questions.
Last
week,
I'm
sorry
I
didn't
reply
to
email
all
those
later.
Hopefully,
today
one
question
was
the
document
currently
says:
the
responses
need
to
use
re
colon
space,
prefix
and
suggestion
was
to
allow
any
prefix,
not
a
big
deal.
I
the
way,
purist
and
me
says
the
only
client
that
generates
non
re,
prefixes
old
version
of
Outlook
that
should
be
banished
from
the
surface
of
the
earth
if
there
are
other
clients
doing
this
I'm
curious
to
know.
L
L
Was
struggling
a
bit
with
you
know
how
simple
the
structure
of
challenge
and
response
e-mails
can
be
original.
I
just
said:
it's
it's
to
explain
messages
where
for
the
challenge,
the
challenge
itself
is
on
the
subject
of
email.
So
text
plan
is
just
explanatory
note,
for
response
is
risk
response
itself
actually
contains
the
response
part.
L
So
I
was
trying
to
balance
whether
you
know
do
you
want
to
require
Acme
clients
to
be
full
email,
clients?
You
know
to
allow
multi-part
mix
or
maybe
allow
you
know
nice
HTML
text
to
be
included
explaining
what
you
do
with
this
challenge,
how
you
can
handle
it
manually?
If
you,
your
client,
doesn't
support
like
me
as
my
automatically,
but
you
know
the
user
can
be
instructed
how
to
do
this
still
open
to
suggestions.
L
One
suggestion
was
also
to
use
spam
like
encoding
inside,
to
explain
so
like
sort
of
for
certificates
and
various
other
objects
yeah
again,
depending
on
your
API
in
your
client,
libraries
that
might
be
convenient.
I
personally
prefer
to
tag
challenges
and
responses,
and
you
as
extra
media
types
which
allows
to
invoke
external
applications
automatically
and
it's
slightly
easier
for
email
clients
to
to
key
off
to
do
automatic
action.
But
again,
this
is
the
grand
scheme
of
things
it
doesn't
matter,
but
we
just
need
to
make
a
choice
and
move
on
think
next
slide.
L
So
this
is
a
list
of
mal
standing
issues.
I
dealt
with
challenge.
Verification
I
need
to
do
a
bit
more
work
on
response,
verification
and
again
there
is
still
a
little
bit
of
open
issue
about
structure
of
their
challenges
and
responses.
So
more
feedback
from
the
mailing
list
would
be
useful,
I
think
probably
one
more
revision
and
this
can
go
to
Alice
Cole
and
then
we
can
I
can
try
to
ping
various
people
who
who
can
provide
more
feedback
on.
You
know
the
structure
of
the
message
and.
M
C
M
N
D
D
Okay,
so
from
the
last
meeting,
I
split
out
the
the
one
draft
I
had
into
two.
So
the
basis
of
this
one
is
just
to
set
a
few
new
challenge,
types
for
user
authentication
focus
and
that
could
be
for
code
signing
certificates
operating
within
a
process
where
you
establish
an
account
first
with
the
CA,
and
then
you
get
credentials
to
use
for
that
pre-authorization
challenge
and
so
I'm
proposing
one
time
password.
D
D
So
I
did
get
some
email
and
private
conversations
after
the
last
talk
and
not
what
not
I
think
crickets
on
the
list
right,
but
I
did
get
a
bunch
in
private,
so
I
don't
know
if
people
are
ready
to
do
this
yet
or
if
they
like
or
so
so.
This
is
the
first
time
I
have
these
three.
In
there
last
I
was
just
trying
to
see
who
is
interested,
so
I
actually
did
get
some
interest.
Is
anyone
in
the
room
here
interested
in
adding
these
challenge
types?
D
F
C
D
O
O
D
D
M
D
I
split
out
these
two
drafts
after
a
message
from
Richard
Barnes
and
some
conversations
with
Owen,
and
we
have
to
sort
out
like
what
we
should
do
with
all
of
these
drafts.
I
just
want
to
go
to
the
next
slide.
So
when
I
talk
about
this
work,
people
just
see
the
let's
encrypt
work
and
the
RFC
eight
five
five
five
and
they
get
lots
of
I've
gotten
lots
of
questions.
That
of
things.
I.
D
Think
Owen
head
said
this
things
that
you
can
do
with
acne,
but
it's
not
clear
from
the
draft
and
then
people
are
hesitant
to
go
forward
because
they
think
it
has
to
fit
in
with
the
realm
of
what
let's
encrypt
does
so
this
would
be
informational,
I
think
we
have
to
sort
out,
maybe
in
the
Wednesday
meeting,
what
Doc's
go
where
or
here
ideally,
but
what's
useful,
are
there
other
questions
that
need
to
be
answered
that
other
people
are
getting
like
I
get
ones
like
okay?
Where
can
you
store
the
keys
and
it's
orthogonal
right?
D
So
you
could
use
pkcs
11,
but
it
doesn't
say
it
anywhere.
In
RFC
a
five
five
five
I
know
I
know
John
John's
face
yeah,
yes,
it
should
be
obvious,
but
apparently
it's
not
right,
and
then
there
was
long
mailing
list
discussions
on
things
like
comparing
it
to
esthe,
but
that
wasn't
captured
and
you
have
to
go
back
and
read
a
mailing
list.
So
I've
gotten
lots
of
questions
on
that
and
then
being
able
to
use
a
challenge
type
for
a
different
type
of
certificate.
D
You
know
you
just
have
to
change
the
the
CSR
and
it
has
a
different
cert
type,
but
that's
not
obvious
either
so
yeah.
Some
of
this
might
be
silly.
Is
it
worth
documenting
and
improving
this
or
as
an
informational
draft
or
not?
What
do
people
think
I'm
happy,
but
this
I
didn't
put
a
lot
of
time
into
yet
I
there.
So
it
can
be
much
improved,
but.
M
I
Yeah
I
mean
this
is
like
interesting,
material
I
think
rc--
seems
like
an
odd
way
to
do
it.
They're
gonna
have
an
import
questions
that
people
are
going
to
have.
It's
like
a
fax
kind
of
it's
more
needed
here.
Also
remember
what
a
little
sort
of
sad
about
the
material
in
here
this
you're
like.
Why
not
ask
that
seems
like,
like
I,
think
you
did
what
he
sidestepped
those
questions.
I
D
P
I've
read
the
draft
segment,
there's
some
useful
stuff
in
here
some
stuff
that
yeah,
maybe
history,
but
I-
don't
see
why
this
needs
to
be
an
emergency
it
all
it
doesn't
need.
The
consensus
is
the
IETF.
It
doesn't
need
permanent
archive
ability.
I
think
this
would
make
a
fine
blog
post
or
a
series
of
blog
posts
that
doesn't
okay.
D
D
A
Q
D
Q
And
I
personally
think
about
the
question
of
whether
it's
to
the
PRC
or
the
kind
of
way
to
publish
it,
I
think
because
I
think
that
maybe
this
drafter
you
have
talked
about
or
you
described
about
something
about
how
to
use
eme
and
together
with
the
Brisky.
Oh
yes,
the
other
kind
of
technology
to
provide
a
whole
process
of
the
device
or
the
of
the
users
auto
provision
right.
So.
Q
D
Q
D
So
I
was
aiming
it
at
informational
I.
You
think
from
the
feedback
I'm
getting
I'm
happy
to
aerate
this
again
as
a
draft,
even
if
it's
not
a
working
group
draft
and
we
can
figure
out
where
it
gets
published
as
it
iterates.
So
if
you
want
to
help
add
that
information
please
share
and
and
we'll
get
it
incorporated
and
we'll
see
how
this
develops.
If
it
develops
into
you
know
something
more
or
not,
maybe
gets
published
a
different
way,
but
I'll
iterate
it
in
a
draft.
For
now
the
drafts
are
cheap.
O
O
D
L
Alexei
Melnikov
I
suggest
the
Working
Girl.
If
there
is
enough
interest
adopters
as
a
work
item
with
understanding,
it
might
not
be
published
as
an
arty
and
just
do
it
as
a
working
your
process,
and
then
you
figure
out
what
to
do
with
it
later
on
whether
it's
you
know,
wiki
blog
post,
you
know,
RFC
or
not.
You
know
content
so.
D
E
C
D
C
A
Tomorrow,
yeah,
so
I,
don't
see
really
a
good
case
for
asking
whether
people
want
to
want
to
adopt
this
now
so
encourage
people
to
read
this
and
perhaps
next
time
or
on
the
mailing
list.
We
can
decide
whether
this
ought
to
be
a
the
workman
draft,
that's
discussed
in
the
working
group
or
an
individual
drugs
that
is
discussed
in
the
working
group,
so
either
way,
I,
don't
think,
there's
any
decision
that
were
that
we
can
make
right
now,
all.
A
He
doesn't
come
to
the
meetings
and
the
question
is:
do
we
really
need
a
working
group
to
do
that?
I
mean?
Is
this
either?
Is
there
any
advantage
of
having
an
active
working
group
when
what
we're
doing
here
isn't
of
interest
to
the
people
in
the
room
to
the
people
on
the
mailing
list,
except
for
that
one
or
two
people
coming
from
another
group
to
do
some
acting
work
for
their
group?
A
So
the
question
is:
do
we
want
to
be
always
be
closing
this
working
group
or
doing
one
team,
or
do
you
think
that
there's
any
actual
work
that
the
working
group
is
going
to
do
rather
than
just
sitting
here
reading
our
email?
Well,
somebody
from
another
group
comes
to
the
mic
and
tell
us
what
what
they
need.
So
this
really
has
to
go
in
the
mic.
P
D
P
Seems
to
be
reaching
a
natural,
ending
point,
I.
Think:
there's
not
there
shouldn't
be
a
real
great
need
for
this
group
to
stay
open
long
term
unless
he
needs
to
make
tweaks
to
acne,
I.
Think
defining
you,
identifier,
testify
challenge
types
can
be
done
in
different
groups
and
extended
by
the
IRS.
Jews
need
to
find.
D
A
So
I'm
sure
that
anything
that
we've
already
accepted
should
move
forward
and
we
done
that.
But
we
could
go
into
the
kind
of
closing
State
where
we're
not
taking
any
new
stuff.
Because
as
long
as
we
stay
open,
people
are
going
to
come
and
have
this
new
little
extension
that
they
want
to
we're.
Never
gonna
we're
gonna,
be
like
the
old
pickax.
E
We
have
some
drafts
in
flight
that
are
adopted.
We
have
some
drafts
that
are
not
yet
adopted.
What
we've
talked
about.
Is
there
any
body
of
work
that
has
not
come
a
draft
warm
to
the
working
group
that
we
would
want
to
put
in
the
table
that
would
necessitate
us
continuing
the
work,
so
I
guess
I'm
asking
another
evening.
Is
everything
it's
or
all
the
traps
that
we
would
think
about
kind
of
advancing
they
all
the
tables?
There's
something
else.
I
said.
N
Hi,
this
is
entrenar
own
from
my
historical
perspective,
and
you
mentioned
pickax
like
it
took
like
18
years
to
close
it.
If
you
have
something,
that's
open,
it's
about
PKI,
it
will
stay
open
into
the
closest.
So
if
you've
got
things
and
you
think
you're
good
to
go
and
close,
it
start
on
another
working
group.
It
doesn't
take
that
much
time,
so
we
charter
do
whatever
I
mean
there's
all
kinds
of
ways
to
do.
This
I
think
you're
things
that
me
are
good.
