►
From YouTube: IETF105-STIR-20190722-1100
Description
STIR meeting session at IETF105
2019/07/22 1100
https://datatracker.ietf.org/meeting/105/proceedings/
A
A
Being
one
of
the
first
sessions,
you
might
not
have
seen
this
slide
before
all
along
looking
through
the
room
and
I
think
that
I've
seen
all
of
these
phases
before
maybe
I'm
wrong.
If
you're
new
here
come
up
and
introduce
yourself
to
me
at
the
end
of
the
end
of
the
session,
if
you're
not
familiar
with
what
is
on
this
slide,
read
this
leg
carefully
now
understand
the
note
well,
yet
there
are
obligations
in
the
note
well
on
you
on
your
participation
in
this
in
any
session
inside
the
ietf.
A
Here's
our
intended
agenda
we're
going
to
start
off
working
through
the
active
working
group
document.
Cert
delegation
in
our
CD,
then
we'll
get
some
updates
on
things
that
are
being
sent
to
the
isg
out,
abandon,
divert
and
in
any
other
business
team.
If
anyone
who
brings
up
any
does
anybody
have
an
agenda
bash.
D
A
D
Hi,
so
we
are
back
again
with
this
exciting
story
about
delegation,
which
is
a
specification
we
have
here,
which
is
now
a
working
group
item,
as
you
can
see
from
the
fancy
ITF
up
there,
which
basically
sets
out
to
explain
how
delegation
works
Forster.
This
is
something
we
talked
about
in
82,
2682
26
said
you
could
just
kind
of
do.
D
D
We
will
have
some
pain
in
the
way
this
is
being
done
as
it
should
be
in
the
ITF.
We
are
the
few
the
devout
who
are
up
for
the
pain.
So
why
are
we
talking
about
this?
I
mean
there's
really
one
basic
thing
that
is
motivating
the
discussion
about
this
in
the
industry.
This
made
this
so
hot
recently
and
it's
this
prospect
that
sometimes
outbound
calls
just
are
not
going
to
transit
the
authentication
service
of
a
carrier
who
owns
the
calling
party
number-
and
there
are
you-
know
the
the
poster
child
of
this.
D
Is
this
common
case
of
an
enterprise
say
who
requires
tiens
from
one
provider
but
in
fact,
does
least
cost
routing
across
a
number
of
outbound
providers?
And
what,
if
this
call
is
going
to
go
out
through
a
different
out
phone
provider,
then
the
person
they
got
the
numbers
from?
How
are
they
supposed
to
sign
it
and
actually
a
lot
of
the
sort
of
legitimate
spoofing
cases
we
talked
about?
D
Sometimes
these
are
the
cases
where
you
know
the
doctor's
office
right
once
be
able
to
call
from
some
number,
and
there
are
doctors
on
the
road
right
and
they
want
to
be
able
to
attest
this.
These,
the
things
that
are
basically
motivating
getting
delegation
done,
and
it
kind
of
put
the
fire
under
this,
so
we
want
to
do-
is
want
to
be
able
to
push
credentials
from
the
TN
owners.
The
term
TN
service
provider
I
think
is
starting
to
gain
a
little
currency
in
the
industry.
D
As
we
talk
about
this
from
those
TN
source
riders
to
na
s,
that
is
actually
able
to
sign
for
the
call.
Maybe
if
this
is
an
enterprise
as
a
ton
of
SIF
infrastructure
that
could
beat
the
enterprise
itself,
maybe
it
could
be
the
outbound
carrier
itself.
Maybe
there
could
be
a
third
party
service?
That's
doing
it
doesn't
really
matter.
This
entire
architecture
is
agnostic
to
those
sorts
of
questions,
but
the
reason
we
want
to
do
this
is
the
bullet
you
see
at
the
bottom
here.
D
D
You
know
that
kind
of
diminishes
a
lot
of
the
purpose
of
what
we've
been
here
to
try
to
accomplish,
if,
like,
basically
any
carriers,
Camilla
sign
for
any
call,
obviously
there's
a
number
of
great,
extremely
trustworthy
and
responsible
carriers
out
there.
That
will
only
sign
for
appropriate
calls
for
this,
but,
of
course
those
aren't
the
people
that
have
caused
these
massive
problems
with
impersonation
that
have
led
12,
robocalling,
voicemail
hacking
and
the
remainder
of
the
difficulties
that
we
face.
That
motivated
this
work
in
the
first
place.
Next
slide.
D
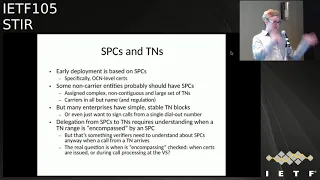
Ok,
so
there
are
hard
edges
on
this
I'm
not
going
to
pretend
that
everything
about
this
is
is
easy
or
obvious.
We
know
that
early
deployment
of
ster,
especially
in
the
shaking
framework,
is
based
on
s,
pcs
and
the
notion
you've
got
in
SPC
these
ocn
level.
Certs
are
something
we
kind
of
bandied
around
in
that
environment,
and
you
know
so.
There's
there's
two
real
ways
to
look
at
a
high
level
at
how
you
do
delegation
from
the
tien
awfulest
object
as
its
defined
in
RC
82
26.
D
You
know
some
of
these
non
carrier
entities
probably
should
have
SP
sees
whether
they
count
as
real
carriers
or
not.
If
you
were
assigned
large,
contiguous
or
non
contiguous,
complicated
blocks
of
five
hundred
thousand
numbers,
you
know
I,
don't
really
want
to
try
to
represent
something
like
that
in
a
TN
awfulest
object
that
would
be
nuts,
and
we
talked
about
some
of
the
alternatives
to
that
in
the
draft
but
yeah
for
some
of
these
entities.
It
might
make
sense
tit
for
them
to
have
an
OC
n
or
a
pseudo
OC
n
of
some
kind.
E
D
Yeah
and
so
and
again,
and
that
that
process
and
what
that's
gonna
mean
as
the
regulatory
framework
or
revolves
around
this
is,
is
interesting.
So
one
important
thing
to
understand
about
this
draft.
This
draft
is
not
saying
don't
do
that.
This
draft
is
saying
there
are
cases
where
you
want
to
do
that.
D
Our
PKI
has
this
idea
that
the
way
that
kind
of
blocks
trickle
down
from
the
Ayana
through
tier
one
carriers
to
you
know
the
various
entities
that
end
up
advertising
these
blocks
on
on
the
Internet
is
that
you
know
each
kind
of
successive
step
needs
to
be
provably
encompassed
by
its
parent
certificate
and
the
scope
of
authority
of
the
parent
certificate,
and
so
there's
a
lot
of
design
questions
in
this.
That
are
interesting
questions,
and
this
is
what
I'd
like
to
talk
about
today.
D
If
people
would
like
to
get
up
and
talk
about
it,
this
is
an
open
issue
in
the
draft.
You
know.
We
all
know
that
at
some
point
the
rubber
meets
the
road
here.
The
verification
services
and
the
terminating
side
of
calls
are
gonna,
get
a
call
assigned
by
a
certificate,
it's
from
a
calling
party
number,
and
they
need
to
make
some
determination.
Should
this
have
been
signed
by
the
entity
that
signed
it,
and
you
know
we.
D
We
need
to
understand
at
least
where
we
think
in
the
architecture
the
right
places
to
perform
that
encompassing
check,
and
there
are
a
couple
of
alternatives
for
this.
You
could
do
it
when
the
certs
are
issued,
for
example,
if
you
are
delegating
from
some
particular
your
carry,
you
want
to
delegate
down
to
a
simple
number
block
like
new
stars.
D
The
alternative
is
to
do
it
like
in
real
time
when
the
call
is
being
set
up-
and
you
know,
on
the
verification
service
side
to
be
able
to
say,
okay
I
need
to
do
some
dip
or
understand.
You
know
that
the
difficulty
with
that
obviously,
is
that
that
could
have
an
impact
on
the
actual
call
set-up
time.
If
you
need
to
wait
for
that
result,
you
know
before
you
start
learning
the
that's
kind
of
a
big
deal.
D
D
I'd
like
to
think
it
is
possible,
at
least
to
push
that
to
the
certification
itself,
to
the
CAS,
to
the
at
least
the
ecosystem
responsible
for
the
issuance
of
certificates,
to
make
sure
somebody
checks
this
encompassing
stuff
and
is
being
like,
audited
and
checked
on
to
make
sure
it's
actually
worked.
Marian.
E
We
still
have
a
dependency
on
these
existing
identifiers
that
are
selling
the
service
providers
and
that's
very
complicated
right
because
of
number
portability
and
that
sort
of
thing
right
it
gets
so
it's
actually.
If
you
really
wanted
to
check
in
on
the
verification
side,
you
actually
have
to
check
more
than
one
place,
even
sure.
D
D
E
D
Right
right
and
so
yeah
I
mean
I,
think
I'm
much
more
concerned
about
just
architectural
ii-if.
We're
going
to
do
something
like
this.
You
know
where,
where
do
we
want
that
Authority
and
that
responsibility
to
reside
in
the
architecture?
My
preference
would
be
that
it'd
be
something
that
happens.
Offline,
I,
guess
rather
than
happening
during
coal
processing.
E
D
D
F
Christmas
Chris
one
I'm,
not
sure,
I,
agree
that
it's
complex
I
mean
it
should
be
possible.
Matt,
like
you,
can
do
the
lookup,
onler
and
impact,
and
you
know,
there's
a
mapping
there.
That
can
be
checked,
but
that's
just
a
single
comment.
I
think
the
broader
thing
I'd
like
to
see
is
that
we
enable
it
on
both
sides.
You
know
I
can
but
folks
choose
whether
we
should
do
it
on
on
the
front
end
or
if
I
want
to
I
should
be
able
to
verify
it
on
the
back
end
as
well.
Definitely,
pending.
D
F
D
G
D
I
mean
that
is
one
of
the
virtues
of
actually
having
the
telephone
numbers
get
inscribed
themselves
for
these
enterprises,
where
it
does
work.
Writing
it
to
me,
won't
work
in
all
cases,
but
in
cases
where
it
is
a
simple
number
range
having
that
in,
there
does
really
help
verification
service.
That
does
not
ordinarily
interface
with
the
unpack
analog
and
things
like
that.
To
figure
out
whether
or
not
accept
this
call.
H
So,
what's
kind
of
keeping
an
eye
on
like
whether
whether
we're
kind
of
an
engineering
or
ourselves
circle
here,
if
this,
if
these
things
can
only
be
verified
by
doing
a
life
check
at
verifications
on
the
PKI,
is
adding
value,
yeah
yeah
check
it
ready
check,
yep,
so
yeah,
given
that
we
have
the
Sun,
constants
and
DKI
concepts
here,
it
seems
like.
Maybe
we
shouldn't
throw
that
away
and
turn
a
purification.
I
I
D
And
in
hating
again
and
the
the
CA
in
PA
functions
are
kind
of
modularized
out
in
shakin,
and
we
don't
design
shaking
here
and
say
for
the
50th
time,
but
like
you
can
imagine
that
being
the
PAS
job
or
the
cas
job
just
depending
on
how
shaken
wants
to
carve
it
up.
We're
not
gonna
decide
that
there.
I
don't
care.
D
E
F
D
D
D
Money,
it's
drag
so
another
element
of
this,
and
this
goes
to
certification
authorities
and
what
we
mean
by
being
is
a
CA
in
this.
Obviously,
the
way
this
is
specified
in
the
delegation
draft
now
we
are
assuming
that
you'll
be
able
to
get
a
certificate
from
the
CA
if
you're
a
carrier
that
has
this
CA
bit
set
to
true
in
it
to
enable
delegation.
This
is
how
classic
x.509
delegation
works.
D
We
even
bake
that
into
the
acme
ATC
mechanism,
so
that
when
you
go
to
get
an
authority
token
that
you
would
then
present
to
a
CA,
you
can
ask
that
Authority
hey,
give
me
something
that
allows
me
explicitly
to
get
it
a
certificate
that
I
can
delegate
from
myself.
Now
that
has
you
know
this
has
edges
on.
It
means
we're
dealing
with
certificate
chains.
D
Now
you
know,
if
you
know
your,
if
you
have
a
CA
that
is
basically
acting
as
the
CA
for
both
the
care,
your
certificate
and
the
delegate
certificate
in
this
instance,
probably
it's
possible
to
collapse
that
chain.
There
are
a
few
ways
to
do
that,
and
we
may
also
be
able
to
do
some
cross
certification
to
consolidate
credentials
and
permissions
if
you're
an
enterprise,
and
you
get
numbers
from
like
three
different
carriers
who
are
all
delegating
down
to
you.
D
You
know
if
it
turns
out
that
it
is
onerous
to
have
the
CA
bit
sad.
There
are
alternatives
that
we
can
explore
for
this,
and
the
work
that
I
would
probably
steal
from
from
this
is
this
ITF
TLS
sub
certs
mechanism
and
a
sub
cert
is
basically
a
document
that
is
signed
by
a
normal
and
entity
cert
that
contains
most
of
the
junk.
That
would
be
in
a
cert
to
begin
with,
and
this
is
a
workaround
that
has
been
developed
for
precisely
these
sorts
of
use.
D
Cases
where
you
can
only
get
in
an
entity
cert
at
the
web.
Pki
is
very
ossified
this
way,
and
this
would
be
a
path
we
could
go
down
if,
for
whatever
reason,
if
there
was
enough
administrative
pressure,
people
didn't
want
to
be
able
to
have
the
CA
bit
set.
This
is
direction
that
we
could
take
and
discrete
these
kind
of
pseudo
certs
with
a
narrower
scope.
Yes,.
B
D
So
we're
talking
about
potentially
delegating
CA
issuing
certs
in
you
know
we're
gonna
have
multiple
chains
of
delegation.
There
are
certain
kinds
of
service
writers
who
they
get
numbers
from
a
carrier,
but
they
that
in
turn
are
building
those
numbers
out
to
a
variety
of
customers
right
and
so
for
that
and
since
I
could
imagine
there
being
multiple
levels.
Actually,
these
delegated
certs
ordinarily
I
think
for
typical
operations.
If
you
know
your
carrier
and
you
have
an
enterprise
customer,
you
would
be
giving
them
an
EE
cert
that
they
would
then
be
using.
K
I
I
D
And
I'll
be
very
upfront
about
this,
my
preference
would
be
to
do
classic
x.509
delegation
with
the
CIA
vets
at
it's
just
if
it
turns
out
that
there's
some
artificial
market
constrain
that
that
is
going
to
preclude
that
in
the
short
term,
I
would
be
willing
to
go
build
a
variant
of
sub
certs
that
works
for
stirrer
just
so
we
could
get
like
something
out
there
in
the
interim.
That
would
not
be
my
preference.
L
K
D
L
D
Again,
this
is
exactly
the
session
we're
just
having.
We
want
the
CA
to
tell
you
what
you
need
to
do
to
validate
without
you
having
to
do
some
kind
of
external
check,
or
something
like
that
right
and
so
like,
because,
if
we
hope
to
build
that
into
the
Cir
to
avoid
having
to
do
a
lot
of
verification
service
kind
of
busy
work
during
call
set
up
time,
I
think
that
we
need
something
that
has
a
very
particular
set
of
qualities.
D
D
H
M
K
M
D
N
M
O
H
Again,
I
think
the
expert
90
good
delegations
seems
a
little
bit
cleaner
because
we
have
a
little
bit
more
to
draw
on
with
a
more
machinery
that
kind
of
just
works.
The
substrates
thing
can
obviously
be
made
to
work.
It's
pretty
Greenfield.
We
can
kind
of
make
it
do
what
we
need
it
to
do.
We
would
need
to
add
some
stuff
to
it,
especially
wanted
to
have
multiples
of
delegation
yeah.
D
D
H
H
P
Klem
Wilson
I'd
also
kind
of
lean
towards
back
away
from
Richard,
okay,
move
towards
the
subjects
only
because
it
is
something
that
we've
already
worked
in
Lenny.
It's
it's
much
more
tenable
as
a
solution
permit
from
the
see
a
patient
perspective
or
as
the
xm9
delegation,
as
was
mentioned,
is
kind
of
a
big
no-no,
but
okay,
and
so
it
would
be
harder
to
make
any
structure
that
supports
and.
D
Q
So
the
TLS
sub
six
is
a
little
bit
of
a
misnomer.
It
really
is
a
key
delegation,
not
a
credential
delegation,
but
conceptually
what
it
does
is
is
tailored
Eve,
what's
valid
in
the
certificate
in
narrowing
the
scope,
so
conceptually
is
aligned.
I,
don't
see
any
real
problem
with
making
a
completely
different
variant.
This
specific
draft
is,
for
you
know,
key
lifetime.
Narrowing.
M
D
Those
were
the
big
questions.
There's
like
a
bunch
of
smaller
questions
that
I
think
we
should
still
work
out.
I
think
was
Richard.
You
pointed
out
like
there
isn't
a
beauty
like
an
x5
C.
We
could
use
as
an
alternative
Dex
flag.
You
and
like
you,
want
as
a
way
to
do
certificate
chains.
You
know
I.
I,
worry,
obviously
that
you
know,
because
passport
has
seen
some
implementation
already,
that
people
just
feel
like
wait.
A
minute.
D
D
F
D
I
mean
it's
just
it's
just
so
the
like
the
jaw
like
header
can
actually
have
you
know
X
5
unit
or
x5c
and
I
mean
it's
just
something
they
defined
for
jaw
and
like
we
can
borrow
ahead
and
use
that,
because
we're
gonna
have
these
pens
certificate
chains.
If
there's
even
one
more
step
in
you
know
the
certificate
management
and
we
have
today.
D
So
I
mean
it's
a
you
know.
We
have
this
PEM
certificate
chain
object.
That
is
gonna,
get
pushed
you
when
you
do
reference
whatever
the
URL
is
it's
in
the
header
and
it
would
technically
be
more
syntactically
accurate
for
us
to
use
an
x5
C
to
point
to
that
chain.
Then
an
x5
Richard.
Yes,
no,
you
there's
your
point
and
you
tell
me:
I
mean
I.
D
D
H
H
E
D
E
D
Okay,
I
mean
I
I,
guess
what
I
probably
say
is
that
we
could
put
in
here.
Let's
allow
either
and
if
whatever
people
want
to
do
is
probably
cool
Lambert.
This
is
all
stuff
that
was
in
82
26
I'm,
just
gonna
like
make
basic
clarifications
around
like
what
how
you
would
actually
do
this
in
practice
and
suddenly
people
are
interested
in
that
we
erect
Barger
and
I
this
morning
had
a
good
discussion
about
this
next
one
about
having
a
good
bit.
D
G
D
G
B
B
D
H
D
D
So
let
me
let
me
run
this
a
little
harder.
I
can
imagine
a
case
where
you're
doing
a
sub
delegation
from
a
TN
range
to
another
TN
range.
Where
you
just
look
at
it
and
you'll
know
nobody.
You
need
to
go
talk
to
an
industry
database
to
figure
that
out.
Right
then
like
so
I
could
imagine
that
that
would
not
require
setting
the
good
bit
for
you
still
to
be
able
to
trust
it
in
a
verifying
side.
H
D
H
D
E
Can
add
to
the
analytics
and
stuff,
because
I
think
about
this?
What
we're
doing
here
is
we're
building
up
information
on
what
we
know
right.
So
this
this
is
another
bit
of
information
that
we
can
add
right,
we're
not
getting
away
from
the
fact
that
there
you've
got
to
run
analytics
and
stuff
to
get
this
right
yeah.
This
isn't
this
isn't
as
deterministic
as
you
might
want
to
be.
H
Like
maybe
I'm
bringing
too
much
of
like
a
traditional,
authoritative
PKI,
it's
sensibility
to
this,
but
usually
you
know
what
wetting
a
thority
signs
a
certificate
to
an
assignment.
You
know
with
the
subordinates
information
there.
It
is
saying
that
I
have
verified
that
this
is
the
case.
The
information
and
certificate
approaches
it
sounds
like
what
is
being
here
is
that
perhaps
in
any
case,
that
statement
is
being
telling
it
has
one
of
a
collection
of
fairies,
not
as
a
single
well.
D
So
so
nari
is
speaking
to
how
the
certificate
itself
is
merely
an
input
to
Mississippi
validation
process.
Then
at
the
turning
side
is
an
input
to
a
broader
analytics
right
that
factors
and
other
things,
then,
what's
in
their
certificate
to
make
decisions
about
whether
or
not
you
should
alert
a
user
or
plox
a
call
or
whatever
right
and
so
I
mean
I
I.
Think
your
message
is
coming
through.
I
would
probably
be
content
to
dispense
with
the
evil
bit
and
just
say
that
are
your
good
bit
and,
like
you
know,
just
just
have
these
certs.
D
If
a
CA
is
issuing
them,
it
should
be
responsible
for
making
sure
the
encompassing
semantics
have
been
validated,
and
you
know
one
handy
fact
as
I
say
here
is
its
auditable
offline
right.
If
you've
got
these
certificate
repositories
and
all
these
certificates
are
being
stored
in
somebody
who
is
responsible
for
the
oversight
of
the
overall
system
could
really
just
go
throughout.
You
go
through
them
like
once
a
day,
there's
not
that
many
certs
right
and
like
just
make
sure
that
actually,
those
encompassing
semantics
apply.
D
D
Yep
we
want
to
be
able
to
check
and
validate
and
verify
as
many
ways
as
we
can.
We
also
want
this
to
be
able
to
work
and
give
you
a
reasonable
assurance
with
as
little
shenanigans
during
call
set
up
time
as
possible.
I
think
it
to
be
a
design
goal,
and
you
know
we
certainly
don't
want
to
close
the
door
and
people
performing
those
checks
if
they
feel
that
they're
necessary
in
the
course
of
call
processing.
So
last
I
know
you
spent
a
lot
of
time
in
this.
D
That's
it
I
think
another
slide.
I,
think
no
side
doesn't
need
to
be
shown,
but
you
can
show
it
I
think
it
just
says.
Next
steps
resolve
issues
continue
work
course,
correction
time,
people
think
this
on
the
right
track.
Anybody
here
thinking
these
are
the
wrong
questions
to
be
asking
they're,
more
fundamental
questions.
Other
things
we're
doing.
C
B
C
You
know
are
feeling
you
know
in
you
know,
in
talking
to
the
vendors
and
actually
even
talking
to
our
customers.
Is
that
they're
they're
not
going
to
be
doing
things
like
this
I
know
for
the
18
giv
flex,
free
servers,
which
is
our
biggest
service.
We
actually
in
our
database,
and
our
app
server
in
the
network
actually
have
a
list
of
numbers
that
our
customers
are
using.
That
are
ATT's
numbers
that
the
customer
is
using
that
come
from
another
carrier
and,
most
recently
we
actually
added
a
feel
for
Blackfoot
that
are
were
vanity
numbers.
C
M
M
I
know
you've
heard
what
you
heard.
I
know:
you've
heard
it
from
a
Cisco
person
but
I'm
trying
to
figure
out
what
what
what
that
is.
It
figured
that
out,
because
I
think
that
I
think
that
there
is
everything
where
who
said
about
who
is
you
say
a
thing
that
there's
people
moving
more
services
to
the
cloud.
P
M
D
Yeah
and
III
just
want
to
harp
on
this.
One
point
here
on
motivation,
push
credentials
from
teen
odors
to
an
AAS
able
to
sign
for
the
call
that
does
not
mean
the
enterprise
necessarily-
and
this
is
something
is
very.
This
architecture
is
not
specific
to
the
notion
that
the
enterprise
is
gonna
end
up
being
the
entity
that
has
these
delegated
certs
these
delegated
certs
are
there?
Maybe
it's
a
cloud
service,
maybe
it's
the
outbound
carrier,
maybe
again
Martin.
D
Maybe
your
service
is
gonna,
get
delegated
credential
from
Verizon
to
sign
for
numbers
that
are
for
Verizon's
customers
and
you're
gonna
be
the
one
using
it.
The
thing
we
want
to
get
back
to
again
is
this
thing
on
the
bottom
of
you
know:
if
what
ends
up
happening
from
this
is
outbound
carrier
signing,
even
though
they
don't
in
the
number
with
credentials
that
have
no
relationship
to
the
ownership.
That
number
you
know,
I
mean
my
greatest
fear.
First
ur
and
shaken
deployment.
D
This
is
this
is
a
way
we
could
get
something
fielded
by
the
end
of
2019
or
into
2020.
That
will
make
people
think
that
stur
accomplish
nothing
and
like
I
just
again
other
than
trace
back.
It
doesn't
evil
trace
back,
but
it
certainly
didn't
able
anything
for
real-time
blocking
or
for
a
real-time
processing,
and
that
is
my
biggest
concern
about
this
overall
project
at
the
moment
and
I
think
we
have
to
get
past
it
Chris.
F
F
Have
direct
access
to
telephone
numbers
and
1's
Ellucian?
We
have
wholesale
customers
that
have
directly
asked
us.
The
question
then,
are
supportive
of
this
work
and
then
the
other
one
is
not
really
the
enterprise
but
more
like
outbound
call
centers
and
things
like
that
where
they
really
do
want
to
control.
What
is
you
know,
and
this
sort
of
correlates
with
our
CD
a
little
bit
which.
F
Where
they
want
to
control,
you
know
how
they
want
to
assign
the
call
they
want
to
sign
what's
being
shown
to
the
customer,
and
they
want
to
be
able
to
control
the
experience
for
the
customer.
So
I
think
those
are
the
sort
of
the
two
top
of
mind
things
from
our
perspective,
part
of
our
most
important
here.
B
Yes,
Eric
Kruger
I
would
offer
the
last
two
statements
are
dead
wrong.
Dead
incorrect
and
delegated
Sturtz
could
make
things
better
right.
How
what
could
make
things
better,
but
I
would
say
it
is
saying
that
allowing
like,
when
18th
years
were
saying,
I'm
going
to
give
a
attestation
to
fidelity.
That
is
enough
for
real-time
authorization
blockade
it's
enough
for
penalizing
them.
If
they're
lying
it's
enough
for
finding
the
bad
guys
so
making
statements
that
you
know
18
P
is
going
to
break
of.
D
Course
I
didn't
say
that
I
said
it's
great:
if
AT&T
does
it
for
fidelity,
it's
not
so
great
if
some
other
carriers
who
have
different
policies,
but
you
know
again,
we
have
a.
We
have
a
goose
and
gander
problem
in
this
and
like,
if
you're
just
saying
about,
if
what
do
I
need
to
do
to
sign
from
a
goose
perspective,
I
I,
don't
want
to
have
to
do
a
lot
of
I.
Just
want
to
sign.
Things
is
very
simple.
D
B
D
Well,
I
mean
it.
The
attestation
of
those
are
a
factor
but
I'm
just
much
more
concerned
about
the
fact
there
is
a
class
of
carriers
before
any
of
this
forsaken
stuff
came
along
right.
Who
apparently
are
willing
to
you:
send
numbers
calling
party
numbers
out
into
the
telephone
network
that
are
not
legitimate,
that
are
responsible
for
all
the
impersonation,
all
the
voicemail
hacking,
all
the
Robo
calling
stuff
that
we've
talked
about
here
and
I,
see
no
reason
why,
if
we
open
the
door,
hey
it's
okay
for
carries
a
sign
for
whatever
number
they
want.
D
If
it's,
even
if
we
do
that,
with
the
best
intention
of
having
a
set
of
carriers
who
are
very
reliable,
like
have
an
easy
life.
The
unfortunate
consequence
of
that,
if
that's
the
policy
of
the
network,
is
that
it
is
not
going
to
change
the
fact
that
these
actors,
who
have
not
been
as
responsible
in
the
past,
are
going
to
leverage
that
to
continue
to
impersonate,
except
now
it
will
be
with
stir
shaken
and
we've
accomplished.
Nothing.
B
D
B
D
B
D
B
B
B
B
H
D
D
R
R
D
Got
it
yeah
which
isn't
which
isn't
terribly
quickly,
but
that
much
said
there
are
a
lot
of
them
out
there,
and
so
you
you
know,
there's
some
people
may
have
opportunity
to
cycle
through
them
rapidly,
but
it's
a
relatively
constrained
resource,
they're
relatively
difficult
to
get
I.
Imagine
there
could
be
analytics
I
could
let
you
make
correlations,
but
it's
tricky.
R
D
R
R
D
Match
once
this
is
very
common
in
its
in
and
there's
further
wrinkles
in
this,
like
if
you're
using
like
pseudo
OC
ends
like
SPC's,
that
are
not
quite
us
yen's,
those
could
have
very
different
properties
in
terms
of
how
could
they
acquire
them
and
how
quickly
they
can
be
correlated.
And
so
you
know,
there's
there's
a
lot
of
edges
in
this.
We'd
need
to
analyze,
but
I
I
really
was
not
trying
to
pick
too
much
of
a
fight
with
this
and
I
apologize
that
those
were
like
kind
of
divisive.
