►
From YouTube: IETF105-IPWAVE-20190723-1130
Description
IPWAVE meeting session at IETF105
2019/07/23 1130
https://datatracker.ietf.org/meeting/105/proceedings/
A
B
B
We
have
two
documents
of
progress:
you'll
see
in
a
few
minutes
that
the
number
has
gone
up
since
we
made
these
slides,
but
we're
going
to
talk
about
them
in
this
order.
The
first
one
is
with
the
is
G
and
the
second
one
has
just
been
in
last
call
this
is
the
agenda
we're
going
to
deal
with
the
amount
of
time
necessary
in
this
order,
so
I
hope
we
get
to
everything,
but
we'll
see.
C
Okay,
good
morning,
everybody,
my
name
is
Naveen
amar
I'm,
the
main
Otto,
the
the
first
author
of
the
the
district
after
Alex
left.
The
draft
in
vision,
43,
so
I
will
give
an
update
about
what
have
been
done
in
this
draft
since
version
44
until
15.
Currently
we
are
in
50,
but
we
are
expecting
to
to
to
post
a
new
version
51
after
receiving
some
comments
from
a
romanian
ID,
so
from
44
45.
So
we
have
in
44.
C
We
have
updated
the
author's
list
and
in
45
we
have
updated
the
abstracts
so
that
we
can
give
more
focus
on
the
the
main
scope.
So
we
have
redefined
the
scope,
so
that's
to
animate
any
ambiguity
on
what
we
want
to
do
and
we
want
to
achieve
in
this
draft,
as
suggested
by
the
main
reviewer
at
that
time,
pascal
figure,
so
we
have
added
in
ran
of
one
another
of
I
simply
a
to
do
so.
C
We
are
dealing
with
ranch
and
that
any
other
optimization
are
out
of
scope
in
in
this
draft
from
44
to
46,
we
have
a
new
abstract,
which
is
more
concise,
so
that
we
don't
have
much
details
in
the
abstract
and
we
keep
them
to
the
main
body
of
the
text,
and
we
have
introduced
that
these
drafts
doesn't
make
challenge
in
existing
stack
so
with
minimal
challenge
to
existing
stack
and
also,
we
focus
once
once
out
of
time
that
the
more
complex
scenarios
related
to
vehicular
communication
will
be
covered
in
future.
Work.
C
Also
in
from
45
to
46,
we
have
specifying
the
scope
also
in
the
introduction,
so
we
have
now
in
46
this
new
text.
The
document
describes
the
leading
of
ipv6
networking
on
top
of
the
I
Triple
E
standard,
mock
layer
or
I
Triple,
E,
8
or
2.3
ma
clear,
with
a
frame
translation
underneath,
and
we
have
added
these
centers-
that
the
results
in
stacks
operates
over
80
2.11
ocv
and
provides
at
least
peer
to
peer
connectivity.
C
So
the
term
peer
to
peer
was
not
in
previous
versions
of
the
draft
using
ipv6
in
d
and
link
local
addresses
in
the
extension
and
IP
way
of
optimization
for
vehicular.
Communication
are
not
in
scope
because
we
have
been
dealing
with
Pascal
about
what
kind
of
Indy
what
are
the
the
limits
of
Indy
when
it
comes
to
vehicle
communication,
etc.
C
C
These
comment
was
sent
also
by
from
from
Pascal,
but
we
had
some
other
comments
from
the
80s
when
it
goes
to
the
iesg
that
why
talking
about
mentioning
sand,
if
it's
complex
had
not
deployed-
and
we
replied
that
this
is
the
only
solution
that
we
have
at
that
time.
So
this
is
what
why
we
mention
it
in
this
draft
from
46
to
47.
We
have
changed
the
title
so
now
we
have
this
new
title
of
the
the
draft
basic
support
for
ipv6
over
X
cetera
and
yesterday
I
asked
the
RFC
editor
if
they
can
help.
C
Even
if
it's
not
the
time,
it's
not
an
FCS,
but
if
we
can
gain
some
time
to
if
we
can
receive
some
feedback,
so
they
told
me
that
the
title
is
a
little
bit
long,
so
maybe
we
can,
we
can
think
about
it
in
next
version.
We
have
also
included
in
the
introduction
that
the
resulting
stuck
in
here
it's
from
ipv6
over
Ethernet,
so
these
lenses
also
some
debates
in
the
mailing
list
and
with
the
ideas
what
we
mean
by
in
heretic
cetera.
C
C
That's
it
yes
for
for
this
version,
and
then
yes-
and
this
was
one
of
the
hot
topics,
hot
debates,
which
is
about
the
the
length
of
the
address
or
the
the
interface
identifier.
So
we
specify
clearly
that
independently
of
the
the
method
used
to
provide
the
even
identifier,
the
left
is
64
bits.
So
if
we
need
any
other,
if
there
is
any
comments
that
should
be
discussed
in
other
working
group,
not
in
IP
wave
from
47
to
48
Mohammed
Boogedy
thanks
to
Mohammed,
he
suggested
he
proofreads
the
whole
document,
and
he
suggests
me
in
private.
C
So
many
correction
were
made
in
this
version:
48
in
from
48
to
14
9.
We
had
some
issues
about
the
references
which
are
normative
and
which
are
informative.
I
think
that
can
be
I
can
happen
in
many
stage
and
hopefully
we
have
solved
this
problem
and
we
fix
it
some
remaining
typos.
In
every
time
we
have
a
lot
of
typos
from
49
to
50,
so
it
was
the
the
ballot.
So
we
got
10
okay.
So
it's
it's
an
okay
for
the
moment,
but
we
still
have
some
three
discuss.
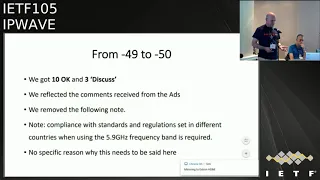
C
We
reflected
the
comments
received
from
the
IDS
we
removed
to
the
following,
not
in
so
in
the
new
version,
which
is
50
compliance
with
standard
and
the
regulation
set
in
different
countries
when
using
the
5.9
gigai
frequency
band
is
required.
We
remove
this
part
because
we
don't
need
to
deal
with
this
detail
in
in
IETF.
No
specific
reason
why
this
needs
to
be
said
here.
So
this
is
why
we
remove
this
part.
I
think
this
is
what
the
so.
This
one
was
one
of
the
main
comment
of
the
of
one
of
the
discuss.
C
So
hopefully
this
discuss
will
turn
on
okay,
the
map
pin
to
the
exit.
So
we
have
this.
Must
that
became
a
shirt
because
one
of
the
ad
is
say
that
must
it's
strong
here
and
is
in
this?
This
idea
deals
with
I
Triple
E,
so
why
we
need
to
force
something
like
that.
So
we
agreed
that
this
must
be.
Should
I
need
to
remind
the
participant
here
that
this
part
of
the
draft
was
sent
us
as
a
review
from
I
Triple
E
802
dogeleven
working
group
based
on
their
review,
a
long
review?
C
C
We
also
reformist
the
Security
section,
because
one
of
the
ATS
suggested
that
an
attacker
may
not
heed
to
legal
limit
for
radio
power
and
can
use
a
very
sensitive
directional
antenna,
so
it
was
okay,
so
I
added
this
sentence.
If
attackers
wish
to
attack
a
given
exchange,
they
don't
necessarily
need
to
be
in
close
physical
proximity,
so
this
detail
was
not
present
in
previous
version.
C
What
remains
to
do
is
to
answer
one
last
comment
in
the
discuss
that
we
have
now
of
Roman,
which
deals
with
pseudonym
handling,
so
I
think
we
have
now
with
the
help
of
Erik.
We
have
now
I
think
a
good
text
that
Roman
will
I
I
hope
will
will
agree
on.
So
that's
it
for
for
these
versions
so
in
equation.
Our
comments
are
welcome.
Thank
you
say:
what
are
you
going
to
say
to
addresses?
C
So
we
are,
we
have
just
sent
few
lines
to
Roman
and
we
can
die
and
we
are
still
waiting
for
his
feedback
just
to
fix
the
the
this
short
paragraph
about
what
is
the
the
the
the
difference
between
what
is
the
impact
of
confidentiality,
because
we
used
the
term
confidentiality
in
the
text.
It
was
on
big
use
for
him
and
we
changed
it
into
the
identity
of
the
destination
and
making
the
trust,
because
identity
is
not
as
confidentiality
its
to
term
different.
So
we
have
proposed
to
to
change
these
two
terms.
D
C
E
C
F
Hello,
everybody,
this
is
poor,
John
from
SK,
kill
you
so
basically,
this
IP
waive
promise
statement
document
liberated
by
Charlie
pockys
and
three
and
basically
three
kundo,
barely
certified.
With
on
this
television
and
Charlie
Kaiser,
he
looks
like
didn't
finished
and
Libya
yet,
but
I
believe
most
of
his
comments
are
addressed.
F
So
after
last
the
prom
meeting
revised
it
two
times
it
so
right
now
the
version
is
11,
so
so
I
will
explain
to
Orly
be
jealous,
so
the
first
revision
from
9
to
10
so
from
a
chali.
So
the
question
is
the
mortar
linker,
so
Burnette
models.
So
this
is
the
problem
statement.
So
I
remove
a
multi-link,
a
sudden,
a
discussion.
Just
we
specify
characteristic
of
a
virtual
or
linker
model.
Is
it
symmetric
and
so
mobile
attack
and
that
took
property.
F
So
we
just
addressed
and
also
he
mentioned,
the
DNS
motivation,
the
pqy
Deanna's
important,
so
I
explained
it
especially
in
beaker
has
a
lot
of
issue
unit,
so
they
can
be
lester
their
own
domain,
name
or
so
remotely
automotive
services
enter
can
remote
a
monitor
regulator,
so
in
the
case
dns
laceration.
Also,
these
are
resolution
is
important.
So
that's
why
I
added
a
some
text
so
in
appendix
I
added
that
detail
changes.
So
you
can
refer
to
that
so
timing,
issues,
Andy.
F
So
the
you
can
see
the
national
highway
traffic
agencies
as
a
product
service
as
appetizers.
Thank
you.
So
they
mentioned
the
0.25,
the
second
very
important
timing
to
avoid
accident.
So
in
the
case
the
neighbor
discovery
message:
if
used
for
the
safety,
a
message,
0.25
exchanges
required
so
depending
on
tentative
vehicle,
we
can
adjust
the
interval
of
neighbor
discovery
message,
so
I
added
a
tap
text.
F
Next,
the
security
consideration
case,
expanding
the
considered,
neighbor
discovery,
part
and
the
mobility
management
part,
so
I
added
a
some
text
the.
Secondly,
this
you
can
see
documentation
predicts
Charlie,
maybe
some
confused.
Why?
What
is
it
is
so
this
is?
You
can
see
the
documentation
predicts
right
for
the
example.
So
definitely
any
allowed
rubber
IP
version
6
address.
It
can
be
loud
trouble
in
Bennett
and
V
killer,
Edie
vehicle
Annette
on
including
infrastructure,
loader,
RS
use.
Also
the
third
one.
F
In
the
piggy
run
case,
the
separate
vehicle
on
a
dog
netted
panel
can
be
merged
to
using
infrastructure
node.
Over
newly
a
joining
of
vehicles,
so
you
can
see
two
separate:
a
banach
can
link
with
the
infrastructure
loader,
all
the
other
arriving
not
I
mentioned,
and
that
part
and
suggestion
are
how
a
good
a
nose
depress
the
prom,
a
better
nose,
or
so
we
I
added
a
text,
so
certificate
can
be
used
to
authenticate
the
beaker.
So
I
mentioned
the
high
lever.
F
So
our
a
document
again
is
for
problem
Stateville
letter
then
giving
the
solution
so
and
Burton
ten
case
I
reflected
the
chalice.
The
editorial
comment,
so
many
editorial
comments
are
addressed.
Some
several
questions
case
in
the
appendix
that
I
address
the.
What
change
are
ton
and
three
hakuna
volley
case
the
article
she
a
fifty
eighty
five,
zero
five
reference:
this
is
for
the
six
all
of
em
the
address
alliterations
optimization.
So
in
this
text
that
we
can
lead
up
them
just
may
be
the
solution
development,
the
page
we
can
consider.
So
we
tell
it
either.
F
E
G
F
E
H
Just
closing
on
the
last
comment,
exactly
I
think
it's
not
touching
on
the
solution.
That's
one
thing
second
thing
is
this
was
the
last
minute
you
know
the
comments
you
know,
but
that
you
are
addressing
were
mostly
based
on
the
reviews
from
Charlie
and
others
right
there.
As
to
some
discussion
randomly,
we
cannot
insert
some
new
sections
without
any
discussion
in
the
mailing
list
right,
so
there's
a
reason
why.
G
So
it
was
scary,
yeah
I
don't
buy
the
last
argument.
If
you
say,
if
you
say:
okay,
that's
not
a
subjective
document.
I
completely
buy
it.
If
you
tell
me
it's
because
we
don't
discuss
enough
well,
let's
discuss
right
now
that
you
can't
just
remove
text.
That's
odd,
because
it's
like,
if
you
say,
okay,
we
have
to
ship
now.
So
whatever
is
discussion
is
pending.
We
don't
take
it.
I
don't
buy!
G
That
I
mean
you
want
a
good
document,
and
if
you
want
a
good
document,
then
you
want
to
make
sure
you
have
settled
on
the
issues
right.
So
if
there
was
a
good
reason
to
mention
it
then,
and
you
remove
it
just
because
you
decided
at
the
last
minute-
that's
not
fair,
either
right
so
so
the
group
must
are
the
consensus
either
way
we
want
to
talk
about
it.
We
don't
want
to
talk
about
it.
It's
the
right
document,
wrong
document,
but
you
can't
just
make
a
decision
like
that
in
a
work
group
document.
G
H
E
E
F
F
We
approved
the
OCB
and
also
one
possible
solution
on
the
big
hill
neighbor
discovery,
the
multi
hub
at
dat,
so
we
proved
concept
and
so
the
basically
we
using
this
multi
hub
at
the
ad
to
lead
years
at
the
ad
arm
delay
or
so
we
can
allow
picker
can
start
the
TCP
connection,
Egyptian
and
possible,
using
the
multi
hub,
adding
network
and
the
impact
on
network.
So
we
extended
the
connectivity,
so
we
probably
using
the
simulation
and
okay,
so
the
appendices
are
explained
and
this
website
can
show
the
video
clip
and
github.
That's
it.
F
G
C
G
Been
working
on
right
because,
because
of
the
bandwidth
that
the
flooding
cost
you
know
the
flooding
well,
each
broadcast
is
that
at
the
slowest
speed
possible-
and
if
you
have
to
flood
it,
that
means
you're,
basically
consuming
all
the
bandwidth
for
everybody
time
you
want
to
form
or
just
check
in
your
dress
and
well,
many
environments
is
just
not
acceptable.
They
can't
see
that
it
would
be
acceptable.
The
CD
I,
don't
just
don't
see
why
it
would
be
acceptable
because
not
you
get
it.
Of
course.
G
The
only
thing
you
will
see
is
that
on
your
network,
there
is
nobody
else
or
anything
else,
not
not
quite
a
good
idea.
So
the
way
six
load
has
that
of
our
multiple
hearts
is
unicast,
so
you
need
to
have
for
a
given
subnet
a
registry,
and
you
just
unicast
check
that
registry.
That's
how
you
avoid
the
flood,
because
the
flood
with
just
one
call
it
looks
great.
Then
you
have
one
thousand
cars.
You
know
nothing
works.
Okay,.
F
E
F
C
Yes,
thank
you
for
pointing
out
to
the
hackathon,
so
we
made
the
two
hackathons
in
the
past,
one
in
Dakar
and
second
one
in
Kampala
last
month
during
the
Africa
internet
summit.
So
we
got
two
good
results
because
we
are
using
not
simulation
but
real
cards
and
to
test
if
there
is
possibility
to
to
connect
and
to
send
pings
and
we
use
in
Wireshark
to
capture
and
to
see
the
the
frame
and
all
fields
and
all
details,
that's
what
we
want
also
to
do
next
time.
Okay,.
