►
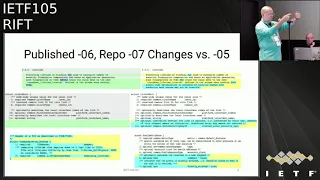
From YouTube: IETF105-RIFT-20190725-1550
Description
RIFT meeting session at IETF105
2019/07/25 1550
https://datatracker.ietf.org/meeting/105/proceedings/
C
C
D
D
E
F
F
Can
you
probably
can't
so
we
published
six
on
the
key
three
points
to
seven
and
doesn't
change
you
since
the
five
and
they
mostly
came
from
Bruno
having
implemented
a
bunch
of
things
and
discovered
that
a
couple
of
things
are
still
unclear
all
right,
so
we
had
this
v4
v6
thingy
going
on.
So
there
was
also
discussion
on
the
lease
rocket
that
would
have
been
brought
up
by
three
or
four
four
different
people
alvaro
originally
as
well,
and
we
had
two
out
two
or
three
clarifications
and
we
had
to
omit
something
from
the
draft
okay.
F
So
first,
when
Bruno
was
sending
v4
v6
right
when
he
switched
off
an
address
family,
he
stopped
sending
it,
but
he
was
still
processing
the
received
frames.
So
it
led
to
an
answer
network
adjacency.
So
we
had
to
add
it
to
the
draft
that
sorry
it
was
the
other
way
around
when
he
switched
off
the
AF
he
stopped
receiving
it,
but
you're
still
sending
it
so.
My
side
I
had
bought
AFS
and
here
on
each
side
and
only
one
AF
support.
So
we
had
to
add
clarification.
F
F
So
it
wasn't
clear
that
you
can
look
behind
the
security
envelope
and
use
the
fields
before
you
validated
the
fingerprint
that
are
enveloping
them
in
protecting
them
subtle
thing.
We
had
to
basically
extend
the
spec
by
saying
that
you
must
not
access
any
value
until
you
validated
the
fingerprint
okay.
F
F
We
added
on
that
when
their
notes
is
wrapping
up
and
you
hit
the
zero
you
automatically
has
to
jump
to
define
value
one
okay,
then
we
had
this
interesting
case
where
we
saying
that
it
on,
unless
you
in
l3,
in
a
threeway
state,
you
must
send
just
zeros,
as
nonces
undefined
I
only
buy
new
in
3-way
State.
You
start
to
mirror
each
other's
nonsense.
Now.
F
The
problem
is
that
if
you
decide
in
a
threeway
state
to
reset
the
adjacency,
the
original
spec
was
saying
that
you
basically
start
to
send
zeros
right,
because
you
must
send
zeros
and
that's
how
the
state
how
the
spec
remains
the
spec
was
correct,
but
it
leads
to
the
fact
that
the
guy
on
the
other
side
has
to
wait
until
he
times
out
because
you're
sending
him
Elwha
one
way
or
two
way
with
all
zeros
which
he
will
ignore,
because
the
spec
says
that's
in
three
way.
You
must
ignore
one
way
into
way
lies.
F
Otherwise
you
could
build
a
very
simple
attack
to
research
essences.
So
as
an
optimization,
we
allow
that
you
may
send
one
one
way
or
two
way
lie
with
the
nonces.
You
know,
because
you're
coming
down
from
three
ways
so
coming
down
for
three
way,
and
you
really
want
to
reset
your
Jess
each
other
on
the
other
side
fast
and
the
only
way
you
manage.
That
is,
if
you
show
the
guy
correct
nonces
on
the
one
way
or
two
way
so
you're
allowed
to
do
that
once
or
twice
we're
basically
says
an
optimization.
F
You
may
do
that
which
will
allow
you
from
a
three
way
to
reset
the
remote
guy,
sending
a
one-way
with
the
correct
Nazis
once
before
you
reset
them
to
zero.
Does
it
sound
need
to
pick
you
well?
That
is
a
full
fledge
interrupt
behind
after
two
people
implemented
without
talking
to
each
other.
All
right,
then
we
had
something
on
the
life
times.
We
softened
up
two
lifetimes.
F
Alright,
so
basically
we
had
this
rounding
up
of
life
times
to
prevent
a
generation
of
fingerprints,
and
we
need
to
talk
through
the
stuff.
We
realize
it
actually
doesn't
buy
you
much
when
the
non
C's
advanced
very
aggressively,
so
we
weaken
it
from
a
shoot
to
an
A.
Okay,
then,
what
we
did
this,
we
added
a
couple
of
optional
things
to
the
schema,
so
the
first
thing
is,
and
that
was
demand
from
a
customer
actually
looking
how
they
would
deploy.
F
That
was
that
we
added
into
this
when
we
sending
out
the
note
ties
with
the
description
of
the
adjacencies
we
added
in
whether
the
essence
is
protected
by
a
key
outer
key,
which
means
the
Llano,
the
the
pairwise
key,
and
the
reason
was
that
the
customer
wanted
to
look
at
the
top
of
the
fabric
where
they
see
the
whole
fabric
right.
You
have
the
topology,
the
full
topology
at
the
top
of
the
of
the
fabric,
and
just
like
we
have
nice
gambling.
They
wanted
to
see
whether
the
fabric
is
secure.
Generally
I
was
very
surprised.
F
Astonish
lehigh
interest
rates,
I
thought
they
will
be
like
one
of
these
thing.
We
must
do
because
we're
like
a
modern
protocol,
but
the
discussion
how
to
secure
fabric
rollover
keys,
is
actually
evoking
a
lot
of
interest
by
a
lot.
I
mean
two.
Three
large
customers
really
wanted
to
know
what
we
want
the
model
is,
and
there
was
a
direct
direct
output.
They
basically
want
to
look
at
the
top
of
the
fabric,
understand
whether
they
have
all
the
links
on
the
fabric
protected
right.
F
It
trusted
the
other
feedback
that
was
from
again
deployment
and
doing
all
kind
of
things
already
like.
How
would
I
hook
up
my
controller
and
do
all
kind
of
funky
stuff
on
the
prefix?
We
have
optional,
see
them
as
flex,
because
the
boolean
one
is
telling
you
whether
the
prefix
is
a
loopback
and
the
other,
whether
it's
directly
attached
to
you
right.
So
that
way
you
can
say
whether
it
shows
up
from
some
funky
place,
but
some
funky
means
injected
by
controller
or
something
simple
stuff:
optional,
didn't
even
increment
the
schema.
F
That's
all.
No.
We
had
more
stuff
all
right
and,
and
there
was
a
discussion
of
the
router
requirements,
so
there
was
one
more
I
didn't
put
on
the
thing,
also
an
optional
element,
but
it
escapes
you,
but
then
we
had
a
discussion
where
we
said
a
rift.
Router
may
support
a
v6,
but
must
support
v4,
oh
yeah,
and
that
that
was
why
the
addition
was
necessary
and-
and
objection
just
to
finally
saw
was
that
before
we
all
pushed
hard
to
obsolete
before
right.
So
that
way
it
will
never
go
away.
F
On
the
other
hand,
the
v6
is
nowhere
close
where
people
will
be
able
everyone
will
run
the
v6
pure
fabric,
good.
A
lot
of
people
do
but
we're
by
far
not
there
yet
so
after
and
the
reasoning
was
the
following
that,
if
a
fabric
does
not
have
any
v4
addresses,
which
is
highly
desirable,
the
only
thing
you
get
on
v6
address
is
nd
coming
up
right.
F
Once
you
have
two
v6
and
you
exchanged,
the
v6
lies
because
you
can
send
v4
lives,
so
no
v4
addresses
if
you
imply
that
you
can
be
for
forward,
which
is
absolutely
possible
right,
because
you
have
to
Gateway
resolution.
Well,
you
don't
need
to
get
or
you
have
to
make
a
trip.
Mac
address
right.
Nd
gives
you
the
binding
the
MEC
binding
to
the
Gateway,
so
you
can
very
fine
forward
before
you
get
a
v4
frame.
F
Yes,
you
don't
have
a
v4
gateway,
but
the
only
thing
is
a
MAC
address,
so
you
just
go
to
the
v6
and
you
just
get
the
Mac
stick
to
Mac
and
forward
works
like
a
charm,
no
tunneling,
no
special
configuration
so
works
beautifully.
But
of
course
you
must
assume
that
the
guys
cable
go
forward
in
v4.
So
you
don't
black
hole.
So
once
you
remove
this
requirement,
that
goes
away.
F
So
what
we
do
on
the
lies
now
on
the
hellos,
you
must
indicate
order
your
support,
v4,
forwarding
and
that
that
way,
I
know
whether
you
will
black
hole.
My
v4
frame
or
not.
The
intention
is,
of
course,
not
to
support
rear
deployments
where
people
will
start
to
build
fabric
partially
forwarding,
v4
and
partially
not
and
computing
partial
SPS.
F
F
So
that's
not
as
convenient
for
the
customer,
but
I
see
how
we
net
cannot
put
out
a
spec
saying
it
must
arouse
running.
This
must
support
v4
and
there
was
a
confusion
for
a
beach
where
people
were
thinking
that.
Thus
that
implies
that
zod
based
on
the
Charter,
we
must
support
both
address
family
and
expect
us
that
any
combination,
so
the
sentence
was
related
to
router
requirements.
If
you
want
to
deploy
such
a
protocol,
so
this
sentence
is
gone
and
we
have
a
new
information
element
indicated
in
ipv4
40.
F
So
it
is
tedious,
but
this
is
no
really
like
grinding
it
to
the
point
where
people
trying
to
switch
the
star
once
a
house
that's
supposed
to
work
and
we
have
to
implementation
really.
You
know
having
stressing
all
kind
of
weird
corner
conditions
on
the
protocol
all
right,
so
we
had
a
full
implementation
of
security
envelope
on
the
open
source
and
my
site,
and
we
had
a
full
interrupt
now
finished.
F
So
that's
result,
so
Bruno
I
have
Bruno's
presentation,
which
is
a
lot
of
interesting
things
that
we
hit,
but
basically
the
Python
reef
has
a
full
implementation
of
the
single
plane
we
have
to
since
a
bit
and
we'll
be
releasing
the
staff
and
already
with
the
0-7
draft
implementation,
which
means
all
the
I'll
talk
about
what
will
come
in
to
zero
sevens.
All
those
changes
plus
some
more
the
security
envelope.
Interoperability
is
finished,
so
we
have
the
done.
B
F
Only
yes,
but
there
is
no
need
on
unless
we
we
would
do
what
preneur
suggests
and
I
rejected,
which
is
protecting
something
like
rift
major,
because
I
see
absolutely
not,
but
then
you
would
look
before
the
fingerprint
right
now.
There
is
nothing
if
you
look
before
fingerprint.
That
makes
any
sense.
Well,
sorry,
nonces!
No.
B
F
So
that
may
still
need
a
small
grind,
because
Brewers
absolutely
correct.
You
can
and
shoot
look
at
the
nonces
before
the
fingerprint,
because
that
you
can
reject
it
without
being
exposed
a
computational
attack,
because
there,
the
fingerprint
computation,
is
an
envelope
where,
if
someone
forces
you
to
compute,
a
lot
of
envelope
damages
basically
have
a
denial-of-service
attack
surface
against
your
computational
resources.
So
Bruna
is
correct.
We
have
that
in
two
minutes:
who's
taking
the
minutes,
because
I
do
not
want
to
miss
that.
Please
Bruna.
G
F
Because
Ted
was
when
I
was
looking
for.
I
was
only
finding
the
7
series,
which
was
all
about
tunneling.
Ok,
excellent,
please
do
poke
me
reference
this
document
absolutely
as
well.
The
text
is
not
explained
that
now
the
router
requirements
were
kind
making
it
implicit
right,
but
it
would
be
great
to
have
two
five
serious
reference
where
we
basically
don't
even
have
to
explain
how
you
do
it:
okay,
yeah,
because
because
I
refuse
to
put
into
a
respect
like
I'm,
not
here,
to
describe
how
to
build
a
forwarding
path
right
so.
F
Freakin
yeah,
yeah,
okay,
hope
people
can
follow
that
once
implementing
can
do
that
for
sure
all
right,
so
back
to
that.
So
that
will
be
out
in
probably
two
three
weeks
starts
already,
but
as
usual
the
wheels
need
grinding.
Then
we
went
through
the
early
Directorate
reviews
already
got.
You
know
for
three
hours
worth
of
sitting
around
and
cleaning
the
stuff
up.
So,
like
I,
said
the
router
requirements
for
if
discussion
has
been
had
and
we
removed,
the
router
requirements
will
be
gone
completely.
F
F
F
Okay,
alright,
the
usual
location,
Python
reference
implementation
not
associated
when
event
or
no
bribes
accepted
almost
there
all
right.
So
since
104
Bruno
implemented
a
very
good
chunk
of
it,
so
he
implemented
the
positive
disaggregation
he
implemented
and
actually
very
well
debug
the
flood
reduction.
So
he
put
a
very
nice
document
explaining
how
flaw
reduction
works
and
the
properties
is
the
Chiefs
in
rift
good
reading,
generally
very
interested
in
flood
reduction
and
house
during
implementation.
F
F
Actually,
a
very
good
comment
came
in
that
we
are
probably
at
a
sentence
on
the
security
section
specifically
for
the
host
requirements,
because
now
we're
talking
about
protocol
which
can
extend
all
the
way
the
routing
domain
into
the
host,
which
is
about
the
first
time,
something
like
that
is
being
done,
and
the
discussion
was
around
the
fact
that
the
host
is
of
course
much
more
like.
Are
we
talking?
Datacenter
server
is
much
more
likely
to
be
compromised.
What
kind
of
attack
envelope
that
could
present
against
the
fabric?
So
the
output
is
not
nothing
particularly
exciting.
F
You
basically
have
to
own
the
host
either
have
a
very
strict
rate
limiting
how
much
state
you
push
into
the
protocol
or
end
on
the
tour.
You
have
strict
limit
how
much
state
you're
willing
to
take
up
from
a
host
in
terms
of
all
of
us
on
someone
showing
you
a
million
kubernetes
prefixes,
probably
not
a
good
idea
all
right
or
they
try
to
pretend
there's
a
million
people
behind
them,
which,
if
you
deploy
that
with
the
leaf
flag,
is
not
possible.
F
F
Frankly,
there
are
very
few
people
in
the
world
at
large
scale
who
have
the
luxury
to
run
about
a
plane,
but
are
people
who
are
now
multiplying
it
of
the
very
cheap
end
of
the
spectrum?
Surprisingly
enough
so-,
this
application,
east-west
links,
is,
are
not
implemented.
Multi
neighbor
state,
which
is
the
extension
to
the
FSM.
We
did
when
multiple
people
show
up
on
the
same
Ethernet
right,
which
is
a
mystic
8
link,
key
Valley,
which
is
optional,
policy,
be
guided,
which
is
optional.
F
Oh
Brewer
cannot
set
your
bit
clock
comparison,
which
is
the
specific
extension
for
mobility
on
the
fabric.
If
you
want
fast
mobility
on
the
fabric
which,
if
you
don't
support,
is
just
fine,
you
advertise
without
clock
fabric
bandwidth,
balancing,
which
is
the
computation
where
you
bend
with
balance
northbound,
which,
given
that
he's
running
on
Linux
I,
do
not
know
he
well
I.
Do
not
think
that
Linux
is
any
kind
of
support
for
for
next
hops
which
are
unequal,
so
there
is
seeing
people
in
unequal
weight,
but
I
would
have
to
double-check
nor
test
cases.
F
F
So
multicast
is
kind
of
open
discussion.
First
color
probably
talk
about
what
is
stand
with
the
multicast
or
maybe
Jeffrey,
and
no
plan
to
support
engraved
Python
the
end
data
model.
Alright,
so
positive,
dissipation
I,
don't
want
to
explain
necessarily
again
how
positive
desegregation
works,
but
basically,
when.
F
Look
at
this
okay,
so
when
spine
one
loses
a
link
to
a
leaf.
That's
the
simplest
case.
They're.
Basically,
spy,
1/2
and
1/3
have
to
show
the
specifics
of
the
lead
leaf,
1
1,
so
this
guy
doesn't
like
college,
so
they
are
accepted
to
the
default.
The
adds
the
desegregation
of
these
leaf
1:1
routes.
Only
ok.
F
Yeah,
so
that's
basically
the
scenario
1
2
and
1/3
show
amount
specific
and
all
the
traffic
towards
leaf
1
1
is
being
offloaded
or
4
of
the
spine,
1
1,
which
would
black
hole
it
and
that,
as
we
know,
that
it's
non-transitive.
So
if
you
have
a
level
about
the
needs
to
disaggregated,
this
aggregation
does
not
flow
south.
It's
unnecessary
as
a
multiple
levels
and
multiple
parts
of
the
fabric
made
easy
Brigade.
F
So,
as
usual,
well-written
pros
know
very
easily
understandable
narrative.
What
is
all
about
and
how
to
go
into
it
is
reference
implementation
which
can
dump
you
all.
The
states
show
you
what
is
happening.
You
know
it's
excellent,
to
learn
how
the
protocol
works
to
walk
through
these
kind
of
feature
guides.
That
Bruno
is
putting
out.
It's
always
enabled,
and
we
know
the
algorithm.
Is
you
detect
the
black
hole
you
trigger?
That
is
aggregation
as
much
as
you
need
to
prevent
black
holes.
F
You
advertise
the
soft
southbound,
so
the
desegregation
always
go
south
just
as
negative,
if
you
never
desegregate
at
the
top
of
the
fabric
and
you
install
the
most
specific
in
the
table
all
right.
So
here
we
go.
He
looks
at
what
are
the
southbound
adjacencies
and
based
on
all
the
reflection
that
you
get
from
other
people.
You
know
what
you're
not
having
compared
to
the
people
at
the
same
level,
so
people
at
same
level.
These
are
north
urgency.
F
There's
a
suffragist
since
you
realize
okay,
I'm,
missing
the
adjacency
here
and
then
Bruno
has
all
kind
of
you
know
like
interface
states,
where
he
can
tell
you,
you
know,
look
there's
people
who
are
forcing
me
to
be
partially
connected
on
this
interface,
because
this
or
running
actually
not
in
containers,
is
running
on
namespaces
and
then
your
trigger.
You
know
positive
disaggregate,
which
is
this.
F
Then
the
stuff
gets
flooded.
So
this
is
you
see
the
link
state
database
right,
which
direction
do
we
flat?
Who
is
the
originator?
What
is
the
type
is
supposed
to
give
disaggregated
prefix,
because
the
tie
are
all
annotated
and
you
see
what's
inside
and
which
metric-
and
this
will
be
the
SPF
that
you
run
on
it.
So
those
are
results
of
the
SPF
as
far
as
I
remember,
and
it
shows
you
that
it
also
speaking
up
beside
the
defaults
that
go
through
get
the
three
gateways.
F
F
You
see
where
who
installed
the
stuff
and
again
what
are
the
routes
and
you're
only
see
the
gateways
flood
reduction
so
why
flood
reduction
is
because,
obviously,
when
you
flood
in
this
scenario,
every
level
that
floods
up
you
get
an
enormous
amount
of
copies
from
coming
from
the
bottom,
which
is
all
exactly
the
same
information,
and
we
talking
right
now,
easily
64,
128,
256,
fan-out,
so
radix,
which
means
128
down
128
up
something
like
that.
Maybe
64
up
96
down
people
have
different
ratios
right.
So
basically
you
get
overwhelmed
right.
F
You
could
both
overwhelmed
in
terms
of
how
much
you
have
to
replicate
and
you
also
get
overwhelmed,
but
simply
when
the
in
caste
that
you
see
no
matter
how
fast
you're
flat
you
flood
all
right.
So
basically,
what
we
would
like
is
somehow
to
limit
number
of
copies
that
we're
getting
into
some
kind
of
a
safe
number
right
that
will
not
partition
when
we
lose.
Some
links
give
us
a
march
in
safety
but,
on
the
other
hand,
not
burden
us
with
excessive
amount.
So
what
the
rest
construct
is
basically
okay.
So
this
is
an
example.
F
What
happens
when
the
rat
and
the
green
guy
starts
to
flop
when
everything
is
fully
connected,
the
rat
node
would
generate
four
copies.
The
four
copies
will
hit
super
one.
This
leaf
will
do
the
same
thing,
red
and
green
topology,
which
basically
leads
to
four
identical
copies
going
through
the
fabric
and
again
with
four
doesn't
seem
excessive.
F
64
is
nothing
special
right
as
a
radix
year
or
even
1632.
These
things
add
up
very
quickly,
so
what
we
really
want
is
somehow
out
of
this
four
prune
out
to
be
so,
let's
assume
we're
happy
with
two
copies,
which
is
a
good
number
normally,
so,
instead
of
so
of
course,
we
have
to
flock
to
all
those
four
guys,
because
each
of
them
needs
the
information
of
the
road
right
now.
So
there's
nothing
to
reduce
here,
but
from
here
on.
F
What
we
like
is
that
only
two
of
the
spines
and
the
copy
to
the
super
spine
right
and
a
very
subtle
problem
that
starts
to
emerge
is
that
if
everybody
down
here
picks
up
the
two
same
guys,
then
you
have
no
the
problem
that
those
guys
may
get
completely
overrun
with
the
replication
plus.
You
know,
processing
of
the
stuff,
well
absorption
and
then,
of
course,
making
sure
that
the
flooding
went
through.
So
ideally,
we
want
each
of
these
guys
pick
up.
F
Two
different
guys
is,
although
we
load
balanced
and
of
course
we
don't
want
to
synchronize
those
guys
again,
because
we
don't
have
any
reflection.
Beliefs
are
not
even
aware
how
how
many
of
them
are
at
ease
level.
That's
how
you
scale
this
stuff
up
so
non-trivial
to
achieve,
went
through
a
couple
of
iterations
and
solution.
Final
emerging
solution,
largely
based
on
Pascal
thinking,
feature
guide'
again
this
one
I
really
highly
recommend
it
works.
You
very
carefully
again,
we'd,
like
all
the
seal
eyes
and
so
on.
F
I,
don't
know
what
it
will
not
drop
theorizing
into
this.
This
one
will
see,
but
it's
a
nice
English
narrative
explaining
to
you
how
you
achieve
such
a
thing
right
and
what
happens
is
basically
is
that
those
nodes,
running
kind
of
an
election
are
going
distribute
to
the
election
are
great,
so
each
of
them
Peaks
to
write
and
the
algorithm
is
run
in
a
way.
That's
based
on
their
note
ID,
and
these
note
ID
everybody
ends
up
with
a
pretty
nice.
You
know
spreading
it
evenly.
The
story
gets
more
interesting.
F
Of
course,
if
connectivity
is
partial,
because
you
have
to
pick
up
possibly
more
than
two
to
get
a
double
coverage
at
the
top
of
the
fabric
or
the
next
level
up
right,
so
things
get
a
little
bit
more
interesting
very
quickly.
If
you
consider
partial
connectivity
so
wrist,
Python
exams,
annex
implements
an
example
algorithm,
and
the
funny
thing
is
that
if
you
three
think
farther,
each
of
these
nodes
can
actually
pick
a
different
algorithm
if
they
choose
without
the
endangering
the
whole
thing
very
much.
So
that's
a
surprising
property.
So
he
implements.
F
We
gave
a
nice
algorithm
that
has
a
lot
of
entropy.
If
everybody
runs
it,
it
will
spread
nicely,
but
it
is
a
very,
very
resilient
if
you
trying
to
do
something
slightly
funky
and
you
do
other
choices
unless
everybody's
really
stupid
and
picked
the
first
in
the
second
then
like
well,
okay,
right,
you
have
no
entropy,
you
know
the
ID
has
to
somehow
get
into
the
entropy.
F
So
this
whole
show
comments
is
on
his
implementation.
Okay,
so
he
even
included
something.
So
when
you
look
at
the
flood
reduction,
what
you
find
is
you
have
an
interface
and
you're
talking
to
someone.
Obviously
that's
the
system
ID
on
some
interface,
and
you
know
how
many
grandparents
he
has
because
that's
what
you
get
on
his
node
tie.
You
see
that
even
if
yourself,
all
the
adjustments
are
included-
and
you
know
which
is
north
or
south,
so
you
know
he
has
four
grandparents
and
here
is
their
normally
right.
F
This
guy
has
one
which
means
that
he
lost
three
links,
so
you
have
to
account
for
that.
This
I
will
never
not
even
talk
about.
We
basically
put
this
thing
into
equivalence
group,
so
we
say
all
those
three
guys
are
actually
equally
good.
When
you
choose
them,
and
then
we
mix
them
up,
we
run
like
a
mixer,
so
those
are
gonna
code.
Hash
groups
I
forgot
what
we
call
them.
F
It's
used
for
the
Fisher,
Fisher
Yates
type
of
hashes
and
what
happens
at
the
end
after
they
are
ordered
in
these
equivalent
and
movement
and
meshed
up.
You
basically
start
to
pick
them
and
you
assign
them
as
a
flat
repeater,
which
means
we
signal
to
them.
If
you
see
my
originator
tie
to,
please
repeat
to
a
level
above
I
did
you
say,
Falls
means
I'm
sending
in
my
information.
Please
do
not
keep
repeating
it.
F
The
whole
thing
is
actually
vaguely
similar
to
money,
flood
reduction
right,
which
worked
very
well,
but
we
couldn't
use
directly
because
they
take
advantage
as
far
as
I
remember,
very
heavily
from
the
fact
that
their
wireless
medium
is
broadcast,
which
we
don't
have
right.
Our
our
medium
is
the
opposite
of
broadcast.
F
Actually,
we
have
link
to
link
everywhere,
okay,
so
then
what
you
can
also
see
from
Bruno's
cody's
when
you
look
at
the
grandparents,
which
means
top
the
parents,
but
the
grandparents,
you
can
actually
see
whether
they've
redundantly
covered,
which
means
do
they
have
at
least
a
degree
of
over
off
of
replication
right.
So
one
link
and
I'll
break
it,
and
then
you
have
to
you
know,
figure
everything
out
and
wait
until
you
figure
out
the
front
row
reduction
and
then
go
flat
until
you
have
everything
everywhere.
F
F
Let's
probably
look
from
the
other
side,
where
you
see
whether
you
are
the
flood
repeater
for
the
guy
on
the
other
side
tons
of
stuff.
You
see,
that's
basically
digesting
these
metrics
right
watch
the
neighbor
state
are
you
which
direction
is
the
neighbor?
What's
his
system,
ID
interface,
which
is
we
think
that
people
appreciate
a
lot
when
they
debug
those
fun
fabrics
and
it's
like
trivial
thing,
but
it's
very
hard
to
do
a
traditional
protocols,
it's
very
easy
to
see
whom
you're
talking
to
on
the
other
side.
F
So
you
have
to
name
off
the
guy
right.
You
know
who
it
is,
but
not
only
this
you,
you
see
his
interface
name,
it's
very
easy
to
go
right
over
okay,
I
hook
up
into
this
guide
on
this
port.
So
that's
what
ref
gives
you
right?
You
always
know
when
I'm
going
out
and
who
MIDI
I
hook
up
on
which
interface
when
I'm
cabling
alright,
so
you
can
disable
that,
of
course
you
know,
but
it's
enabled
by
default
and
I.
F
Think
Brunel
allows
you
to
play
with
a
redundancy
factor,
and
the
similarity
factor
is
that's
how
you
balance,
depending
on
how
many
edges
the
guy
said,
not
wrong,
because
you
can
have
different
strategies
when
you
pick.
Who
is
repeating
for
you
right,
you
can
pick
up
the
guy
with
most
of
this
is
not
found
because
he
gives
you
the
highest
coverage.
You
can
just
do
the
opposite.
You
can
pick
up
one
with
the
least
right
because
he
will
repeat
the
fastest
right
or
the
guy
who
has
the
most
CP
or
whatever.
Not
it
really
doesn't.
F
Like
I
said
it's
highly
resilient.
As
long
as
you
put,
you
knows,
ID
essential
P
into
the
whole
algorithm,
the
staff
will
spread.
You
know
depending
how
it
really
doesn't
matter.
It's
bloody
resilient
as
long
as
you
put
a
little
bit,
entropy
the
stuff,
just
slow
balances,
all
right,
all
right
security.
So
now
here
comes
the
most
delicate
part
of
the
work
or
what
happened?
Ok!
F
So
again,
here
comes
Bruno,
nothing
until
it's
like
in
beautiful
English
write
down,
everybody
can
follow
and
learn
from
so
truly
a
reference
implementation
in
the
in
to
really
the
best
sense
of
the
work.
So
we
have
two
outer
keys
per
interface
right.
Protect
are
not
showing
in
the
law
where
we
protect
twice.
We
do
origin
protection,
which
means
when
I'm
originating
information
I
am
putting
my
key
signature
around
that,
which
means
the
content
cannot
be
changed,
but
then,
when
I
break
up
an
adjacency
I
have
the
option.
It's
all
optional.
F
I
know
everyone
without
keys.
Fine
I
have
the
option
to
only
accept
adjacency
if
we
agree
on
fingerprint
of
a
key
non
acceptable
key
and
in
every
packet,
when
it's
a
tyent's
in
a
protect
that
gets
wrapped
into
the
outer
one
right
on
every
adjacency,
we
have
an
outer
key,
which
is
suggesting
specific
if
you
want,
and
we
have
the
inner
key,
which
is
really
signed
by
the
originator
of
the
information
which
is
really
only
of
interest.
F
If
you
write,
if
you,
if
you
do
a
less
piece,
theis
lsas
right
the
stuff
that
slots
all
over
the
place
so
right,
so
we
call
them
inner
keys.
Bruno
tried
to
pushed
into
Thai
origin
keys,
but
actually
we
can
protect
more
stuff
like
PS
and
PS
right
tire
kites
also
with
this
key.
So
it's
not
clear
what
will
happens.
I
prefer
to
call
them
inner
key
right.
F
It's
the
originator,
protection,
of
course
multiple
algorithms,
because
we
show
the
key
and
then
we
show
what
is
the
fingerprint
length
that
we
use
right
now
we
are
running
off,
run
or
correct.
Me
I.
Think
char
to
256,
which
looked
to
me,
like
the
sweet
spot
I
think
there
was
some
discussion
on
the
list.
F
F
So
we
have
this
mo
file
which
describes
it
Apollo
you
use
to
interact,
because
we
both
bring
up
his
virtual
topologies
writing.
We
can
read
the
same
format
to
see
the
topology
description
without
running
a
lot
of
virtual
machines
or
whatever
or
not.
So
we
added
all
kind
of
things
where
you
have
to
describe
the
keys
and
each
note
can
say
right.
So
what
is
the
my
origin
authentication
key
that
I'm
using
which
one
will
I
accept,
and
what
am
I
running
pay
interface?
F
What
is
my
active
dedication
key
on
the
interface
and
what
is
the
accepted
keys
on
this
interface?
I
have
more
staff
which
Bruno
does
not
support,
which
is
all
kind
of
strategies.
What
I'll
do
with
the
key
if
it
shows
up,
which
is
in
in
practical
deployment,
very
useful,
there's,
no
or
kind
of
lose
permissive
thing
which
says
like
if
you
don't
have
the
keys?
Okay,
if
you
have
a
key,
are
verified
otherwise,
I'm.
F
F
But
if
you
have
one
metric,
you
probably
wants
to
mesh
something
up,
which
is
a
mixture
of
your
administrative
metric,
Plus,
available
bandwidth
and
you
can
provide
all
kind
of
knobs
and
things
right
as
the
spec
gives
you
one
example
and
suggest
how
to
do
something
like
that,
but
again
it's
highly
resilient.
So
to
debug
the
security.
You
have
a
lot
of
things
which
are
mostly
same
zero
and
those
are
the
reason
why
you
wouldn't
not
process
the
packets,
father
right
so
there's
may
envelope.
Maybe
me
saying
you
don't
accept
the
key
ID.
F
That's
exaggerated,
but
anyway
it
good
good
amount
of
discussion
about
all
the
performance
right
I
mean
would
will
be
the
throughput,
because
rift
flats
at
depends
on
what
we
implemented,
but
something
like
having
you
know,
20
or
30
thousand
information
element
coming
into
the
database
per
second,
so
we're
not
even
talking
flooding
rates.
That
means
that
is
the
consolidated
flooding
rate
on
all
the
interface
you're
running
is
nothing
special
right,
so
the
interface
is
makeup.
Cumulative
at
one
hundred
two
hundred
thousand
packets
I,
don't
know
widget
almost
interested.
F
How
fast
is
the
dye
to
depth
item
data
base
sucking
up
and,
of
course,
at
those
rates
we
were
very
interested.
You
know
we'll
the
encryption
even
hold
up
and
no
problem
at
all.
On
the
generic
CPU
I
mean
you
can
crank
insane
numbers
once
you
move
into
like
1024
204
a
territory.
It
starts
to
get
tricky,
so
Bruno
put
out
actually
I
think
an
email
on
the
list
where
he
measured
the
stuff.
F
F
Alright,
so
interrupt
testing
security
was
the
focus
we
fully
automate.
The
whole
thing
right.
The
whole
thing
get
chucked
on
the
usual
continuous
integration,
things
no
manual
like
pushing
and
kicking
things.
No
one
has
time
for
that.
We
are
also
to
easy
report.
Everything
is
passing
at
this
point
in
time.
So
that's
that's
a
no
custom
image
I
through
pre-release
package
on
Bruno,
because
we
were
iterating
back
and
forth.
He
found
one
thing
on
my
side:
they
found
a
thing
on
his
side.
So
so
what
did
we
learn?
F
So
the
fingerprints
per
said
is
the
envelope
parsing
and
the
one
was
not
a
problem
at
all,
so
like
accepting
the
key
and
parsing
and
I'll
parsing
the
key
and
and
going
after
fingerprint
that
basically
just
flipped
it
on
lawns
reflection.
So
here
Bruno
belief
didn't
believe
me
when
I
relaxed
the
norms
is
right
and
I
was
very
specific,
that
you
have
to
be
fairly
leisurely.
How
you
push
the
knowns
is
up
and
how
you.
F
F
So
there's
nothing
to
attack
it
boots
empty
knows
that
you
can
attack
or
store
the
stake
and
then
no
matter
what
they're
trying
to
attack
within
the
session
or
after
reboot
a
new
session
comes
out.
You
try
to
attack.
We
have
protection,
football
Brewer
thought
that
he'll
go
Baron
and
the
spec
and
he
was
advancing.
His
knowns
is
very,
very
aggressively
or
pretty
much
any
packets
anywhere.
F
F
Brune
asked
me
why
you
would
even
accept
something
that
is
higher,
that
you
announced
so
I
walked
him
through
implications
of
heavily
paralyzed
implementation
of
routing
protocols,
where
you
may
have
multiple
clocks
advancing
India
implementation
at
different
rates.
So
it
may
happen
that,
on
an
interest
that
you
will
find
yourself
receiving
something
which
is
ahead
of
what
you
think
where
you
are
yes,.
F
H
F
Yes,
so
there's
the
security
review,
I
didn't
see
there
I'm,
not
sure
what
he's
talking
about
with
the
publishing
okay,
so
Bruno
was
advancing
the
stuff
so
fast
that
when
the
FSM
was
like
revving
up
and
already
doing
some
kind
of
flooding
stuff,
he
would
be
falling
out
five-window
right.
So
he
was
resetting
the
session,
so
he
had
to
back
off
and
do
pretty
much
what
the
spec
suggests
and
then
everything
went
went
up
nicely
and
even
despite
he
was
slightly
concerned
that
he's
a
little
bit
more
Asian
leisurely.
F
F
What
draft
was
changed
to
because
what
emerged
out
of
that
trying
to
reset
this
FSM
and
so
on,
I
think
it
was
Bruno's
input.
We
decided
to
send
the
remote
nonce
is
zero
in
both
one
and
two
ways,
because
I
think
I
was
more
relaxed
there.
That
was
the
result,
so
you
cannot
do
because
we
couldn't
negotiate
the
keys
early
enough.
Always
so
the
two-way
will
be
already
nonce
protected.
F
Details
gave
me
it
will
be
in
his
report.
Ok,
so
he
said
already,
there
is
a
very
detailed
review
report.
He
updated
on
the
second
version
so
that
talks
about
all
possible
attack
vectors.
What
we
saw
you
know
the
finesse
of
the
whole
thing.
Any
questions.
I
know
there
was
comprehensive,
but
his
bony
term
were
basically
jump
up
and
down.
We
got
an
early
review
from
the
security
one
of
director.
Eight,
we
addressed
all
the
staff
good
while
ago
implemented
interrupt
what
we
got
was.
F
We
have
been
granted
the
exception
by
the
ad
to
actually
keep
the
security
section
within
the
spec,
rather
than
published
in
our
security
consideration
draft
which,
in
my
opinion,
which
makes
much
more
sense
just
like
keeping
the
requirements
and
the
security
on
the
spec,
rather
than
slamming
them
around
no
questions.
So
the
only
real
discussion
I
saw
what
is
router
requirements
that
was
floating
around.
F
D
I
I
So
it's
a
key
problem
here
to
be
sold
and
then
the
second
points
is
that
the
leaf
node
has
the
same
data
base
with
other
node
in
the
network
because
of
the
IDP
filter,
and
we
know
that
we
always
use
OSPF
or
he
sees
in
these
fabrics,
but
every
node
in
the
network
will
maintain
the
same
database.
So
the
leaf
node
will
have
the
same
database
with
other
nodes.
It's
a
it
brings
great
burden
to
the
leaf
nodes.
I
I
We
know
that
rift
is
a
new
dynamic
routing
protocol
for
the
cross
and
factory
approaches,
because
the
key
feature
of
rift
is
that
you
see
it
uses
a
different
advertisement
for
different
directions.
It's
more
like
a
link,
Stata
protocol,
whereupon
knows,
and
it's
more
like
a
path
vector
protocol
well
point
source
and
the
rift
protocol
is
fully
automated
construction
based
on
detection
of
link.
So
it
can
support
CTP
the
demons.
Zero
touch
permission,
so
it
can
greet,
reduce
the
burden
of
the
network
administrator.
I
I
According
to
these
key
features,
the
sub
optimal
ranking
and
the
black
holding
can
be
avoided
and
also
Rifkin
supports
a
rift,
allows,
trafficker,
steering
and
rerouting
policies,
because
good
extension,
and
also
it
allows
loop
of
three
non
SNP
verdict
and
it
can
support
it,
can
automatically
support
the
balance
of
trafficker
towards
the
spine
based
on
the
panelists
were
available
and
also
it
can
provide
the
mechanisms
to
synchronize
immediately
in
value
and
he
readily
restore
that
can
be
used.
Avatar
protocol
convergence
so
from
it.
I
D
B
E
E
Now
that
you
mention
it
working
your
production,
I
wanted
to
mention
that
what
sure
says
is
that
we
wanna
release
stating
it
it
talks
about
how
employee
and
configure
drift
policies
well,
I
think
this
Nachman
does.
Is
it
basically
summarizes
the
features,
and
then
it
says,
oh
because
it
has
those
features,
recognition
powers
as.
I
I
E
Didn't
read
it
all,
but
it
looks
like
there's,
maybe
one
or
two
paragraphs
for
each
of
the
ears
cases.
No
I,
don't
know
that.
That's
a
lot
I,
don't
think.
That's
a
lot
and
I.
Don't
think
that
in
one
of
the
two
paragraphs
you
can
talk
about
how
to
employ
and
configure
for
each
one
of
these
cases.
So
again
with
the
grain
of
salt,
I
haven't
read
the
whole
thing,
but
but
it
seems
to
me
that
this
draft
in
the
correct
form,
is
not
what
we
want
to
meet
the
Charter.
E
This
sounds
more
and
don't
take
this
the
wrong
way,
but
this
sounds
more
like
a
marketing,
sorry.
This
is
all
the
great
things
well
correct,
which
is
great,
but
it
doesn't
tell
me
if
I
need
to
apply
rift
to
a
fabric
for
this
excited.
For
example,
what
considerations
should
I
take
like
a
figure
of
the
point?
Why.
E
G
F
E
Algorithm
elevate,
so
there's
nothing
wrong
with
life.
There's
nothing
wrong
with
seven,
there's,
probably
nothing
wrong
with
white,
so
what
we
want,
or
what
I
thought
we
had
weed
from
the
beginning
of
the
Charter
with
Satan
is
to
say:
okay
now
here
we
have
the
Peugeot
specification.
This
is
how
you
use
it
now.
You
just
have
something
interesting
which
is
well.
This
is
so
easy
to
just
cook
your
regular
them.
So
maybe
there
aren't
that
many
considerations.
E
The
science
of
breath
dilemmas,
that
is
to
say
that
that
below
just
like
security,
you
could
have
a
session
in
here
in
the
big
document,
which
is
already
a
hundred
40
pages.
To
say
these
are
those
employment
considerations,
there's
an
RFC
that
I
forget,
which
one
it
is
in
the
5000
series,
I'm
going
to
say
51:43.
E
But
where
was
the
fetish
checker?
You
check
their
talks
about
deployment
that
manage
malicious
iterations,
and
so
it
talks
about
if
I,
really
a
new
protocol.
What
kinds
of
things
going
to
think
if
I
mean
yeah,
something
that
that's
the
type
of
thing
they
want
to
see?
It
may
be
that
you
know
the
program
is
so
simple.
F
F
Narsing
like
that,
so
thanks
for
this
reference,
yes
required
reading,
where
we
had
deployment
consideration
was
basically
miss
Kay
plate
right.
That's
where
the
stuff
pops
up
on
the
security
this
stuff
I
saw
it.
Bruna
was
more
implementation.
Considerations
with
where
he
had
to
loosen
up.
He
stopped
otherwise
keys
are
keys
where
we
can
put
something
in
like
urea
stores,
Pyo
science,
key
management,
same
thing,
I
mean
if
that
contributes
anything,
and
we
had
the
configuration
which
is
just
embarrassing,
Li.
F
L
G
L
In
DC
fabrics,
if
you
want
to
do,
though,
hamid
costs
and
keep
them
out
of
route
and
say
it's
small
okay,
there
is
an
RFC
how
to
do
out
in
in
DC
using
bgp,
but
it
comes
through
there
really
really
difficult
to
most
minimize
state
and
the
door.
Holland,
for
example,
because
it
essentially
requires
the
condition
of
desegregation
base
it
on
normal
or
confirmation
very
difficult
to
do
this
out.
A
lot
of
additional
logic.
D
M
F
Here's
a
question
ad
bound,
so
do
we
have
to
last
call
everything
as
a
package?
What's
the
deal
also
with
LSD
our
because
at
this
point
in
time
the
protocol
spec
is
very
thoroughly
cooked
with
two
implementations
and
I?
Have
people
ask
me
where
the
world
I
have
authority
for
the
RFPs
and
their
life,
so
Eastern
policy
here
or
what
can
we
go
to
the
last
call
of
the
protocol
spec
one?
All
the
stuff,
of
course,
is
absolutely
necessary
and
committed
to
end
the
one
interlock.
E
E
M
Better
friendly
suggestion,
mostly
at
the
chairs,
Jeffrey
I,
think
what
I
heard
while
I
wasn't
reading
my
email,
which
of
course
wasn't
doing
the
turn.
The
discussion
of
the
applicability
draft
was
like
presumably
applicability
a
draft,
and
then
there
were,
you
know
some
criticisms
of
it
whatever
and
then
you
say:
well,
maybe
it's
not
ready
for
adoption
yet
and
God.
M
So
it
sounds
to
me,
like
the
working
group
is
discussing
a
draft
that
the
working
group
is
chartered
to
produce,
which
sounds
to
me
exactly
like
what
a
working
group
is
supposed
to
adopt
a
graph
to
do
like.
Normally,
you
don't,
you
know,
wait
until
a
draft
is
perfect
before
adopting
it,
you
adopt
it
when
you're
like
yeah.
This
is
kind
of
what
we're
supposed
to
be
working
on
and
then
you
insist
it
to
be
perfect
at
last
call
time,
but
it's
your
group
I
mean
run
it
the
way
you
want
to
so.
D
D
So
as
when
you're
understand
now
the
zero
six
revision
has
been
posted,
we
did
the
wrote
interrupter
directory
renew
by
Ross
Thank
You
Russ,
and
the
authors
in
Ross
had
extensive
discussions
in
the
last
two
days
and
the
or
they
agreed
on
that
the
changes
they
need
to
happen
and
the
zero
seven
radiation
will
be
out
soon.
The
pen
is
to
issue
the
working
group
last
call
right
up,
sir.
Does
your
server
0-7
revision
and-
and
this
does
not
have
to
wait
until
we
go.
D
We
peppered
the
previous
statements
on
to
be
ready,
and
so
originally
we
thought
we
would
call
for
that
option
for
the
applicability
statements.
I
think
well
wait
for
the
next
revision
and
the
yes
back.
He
was
adopted
the
last
time.
There
still
must
a
minor
updated.
They
need
to
be
done
issued
last
last
call
after
after
that
multicast
wraps
we
taught,
but
we
discussed
the
multicast
ideas
and
at
last
IETF
meeting
and
we
put
out
the
zero
zero
radiation
initial
craft.
D
E
D
D
G
If
some
people
dig
down
the
year
or
discussions
we
had,
we
are
topics
like
very
mobile
and
devices.
We
don't
want
to
12
state
in
the
intermediate
layers.
You
just
want
to
put
the
state
to
satisfy
them
turn
off
from
the
spine
to
the
leaf
Adam,
very
mobile
carriers.
So
we
are
things
like
that:
optimize
very
special
cases.
We
coverage
it's
useful,
so
yes,
the
I
just
floating
in
here,
and
we
are
ready
to
realize
that
ready
time
zombies
it
have
immediate
right.
