►
From YouTube: IETF105-COSE-20190726-1220
Description
COSE meeting session at IETF105
2019/07/26 1220
https://datatracker.ietf.org/meeting/105/proceedings/
A
B
C
B
All
right
welcome
everyone
to
cozy
our
last
session
of
the
last
day
for
those
of
you
paying
attention,
let's
see
so
unless
this
is
your
first
day
here,
I'm
pretty
sure
you've
seen
the
note
well,
but
if
not,
please
please
take
note
of
this.
It
is
important
to
especially
for
the
group
working
on
things
related
to
cryptography
IPR
disclosures
are
very
important
and
very
critical
to
us.
So
please,
please
consult
the
the
relevant
BCPs.
B
B
If,
for
whatever
reason
media
echo
isn't
working
or
is
it
the
inconvenient,
we
have
the
media,
Co
links
and
the
links
to
all
the
materials,
all
the
slides
that
we'll
have
today,
alright,
so
here's
our
agenda,
we've
already
gone
through
most
of
our
administration,
but
we'll
be
covering
this
drafts,
hash,
algorithms,
x.509
from
Jim's
and
then
wrap
up
with
Mike,
Jones
and
web
authentic
to
the
time
we
should
be
out
of
here,
pretty
quick.
So
any
any
bashing
of
this
agenda.
B
B
D
E
E
D
D
We
still
potentially
have
the
down
ref
issue.
We
don't
know
how
fast
is
the
seaboard
based
documents
actually
going
to
get
out?
It
is
not
moving
nearly
as
fast
as
what
this
document
is,
so
we
may
still
end
up
having
to
argue
with
the
IHG
about
that
particular
down
ref,
but
I.
Don't
think
it
should
be
a
big
issue
as
we're
doers
doing
the
most
basic
seaboard
stuff.
D
D
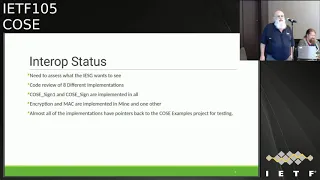
Interestingly
enough,
almost
everybody
does
signing,
and
almost
nobody
does
encryption
I'm
not
really
too
sure
why
that
is
true,
because
when
I
wrote
my
code
I
started
with
encryption,
it
probably
has
to
do
with
what
people
actually
need
in
the
real
world
and
I
basically
just
went
through
in
red
code
in
terms
of
trying
to
figure
out
what
people
were
doing
so
we
may
have.
This
may
actually
change
as
I
find
other
I'm
at.
F
Justin
Richards
just
a
quick
note
that
parallels
the
hoes
a
world
where
I
just
about
everybody
does
Jam
to
the
US.
Most
people
don't
do
jwe
and
even
in
the
classes
that
I
teach
on
a
often
Jose
I
teach
jws
and
say
if
you
want
to
do
JWA,
co-create
or
something
yeah
go.
That's
that's
an
exercise
at
home.
So
this
this
is
not
at
all
surprising
to
me
because
in
the
real
world
that
seems
to
be
where
most
of
the
use
cases
are
dragon
is
signatures.
G
D
G
Think
the
point
of
my
question
actually
to
that
point
is
whether
or
not
users
should
be
specific
or
protocol
users
that
is
should
be
specific
about.
We
accept
sign
one
and
only
sign
one
or
you
should
accept
the
generality
of
both
structures,
which
may
only
be
signed
by
one
for
one
entity
because
there's
a
little
bit
of
subtlety
in
the
clarification
code.
If
it's
that's
there,
if
you
don't
eat
it,
you
don't
have
to
have
it,
but
the
other
hand
of
ending
what
everyone's
implementing
it.
H
I
B
D
Was
planning
to
use
the
wiki
on
the
github,
but
I,
don't
think
it
actually
makes
a
big
difference
in
terms
of
interrupts
testing.
Almost
every
implementation,
I've
seen
actually
pulls
down
the
examples
from
the
example
repository.
So
half
the
job
of
testing
for
interrupts
is
is
probably
already
done.
That
is,
everybody
can
already
verify
stuff
that
I
signed
or
stuff
that
I
encrypted.
It's
just
a
question
making
sure
that
the
other
the
opposite
direction
works
as
well.
D
B
D
Basically,
the
things
that
I
said,
I
was
going
to
do
in
Prague,
I
went
through
and
did
and
I
think
this
document
should
be
ready
to
go
to
working
group
last
call.
There
is
one
interesting
question
which
we
may
want
to
consider
and
I
think
is
a
good
thing
to
consider
during
working
with
last
call,
which
is:
do
we
want
this
document
on
standards
track
or
should
it
be
an
informational
document,
I'm
agnostic
towards
that.
F
F
J
B
J
G
G
See
why
you
wouldn't
it's
just
a
label,
although
everything
else
happens
the
same
way
and
and
is
your,
is
your
it's
some
of
your
reluctance
that
you
believe
that
by
the
time
we
get
to
step
two
that
the
algorithms
will
have
changed?
Let's
start
all
over
again
or
is
your
reluctance,
bigger
architectural
IETF.
G
G
Okay,
to
be
honest,
you
could
probably
look
it
up
in
the
thing,
but
under
something
you're,
probably
not
familiar
with
that,
but
but
we
extended
must
and
should
and
stop
to
have,
must
plus
and
must
and
should,
plus
and
should,
and
that
basically
means
these
are
algorithms
which
we're
thinking
about
deprecating
if
they
have
as
they're
going
on
the
way
down
and
if
they
have
pluses
they're
going
on
the
way
out,
you
should
think
about
they're
becoming
mandatory
and
and
I.
Think.
G
G
D
G
D
Exactly
we
did
exactly
the
same
thing
with
the
S
minus
specifications
and
I've
never
thought
about
trying
to
progress.
Those
about
to
fall
stands
because
we,
since
they
got
algorithm
recommendations
in
them,
we
Rev
them
on
a
you
know
every
year
basis,
but
you
know
in
the
last
20
years,
I
think
we're
now
on
the
fifth
or
sixth
version
right.
G
D
The
algorithm
in
that
is
is
to
be
done
or
actually
I'm,
not
too
sure.
If
it's
about
how
we
actually,
if
Modi
in
a
charter
for
new
algorithms,
so
far,
we've
had
one
only
one
person
has
actually
said:
I
really
want.
If
this
algorithm,
if
it's
only
one
hey
I,
can
do
that
really
I
can
do
that
by
Singapore
in
him
we
can
be
been
finished
if
other
people
really
want
us
to
put
in
other
algorithms.
I
really
want
to
hear
about
it.
D
Basically,
everything
that
we
talked
about
at
the
last
meeting-
most
of
it
basically
is
after
I
thought
about
it
for
a
while
I,
don't
think
we
need
to
do
it
so
I
didn't
write
it
into
any
of
the
documents
we
have
had.
One
person
asked
for
an
early
assignment
of
the
curb
points
for
this.
This
because
they're
actually
going
to
start
doing
some
interrupts
testing
in
about
three
weeks
and
then,
if
we
actually
have
real
numbers,
that
would
prefer
to
use
real
numbers
than
to
use
made-up
numbers.
D
That
purpose
I
actually
intended
to
push
examples
for
this
up
to
the
to
the
repository
and
I
ended
up
with
problems
with
open
SSL
in
terms
of
trying
to
generate
certificates
for
things
like
x2
55.9,
because
of
course
you
can't
actually
create
a
CSR
with
it.
So
they
have
some
funky
language
for
command
switches,
which
I
haven't
managed
to
figure
out
how
to
get
to
work.
Actually,
I
need
to
actually
like
synced
up
my
version
of
open,
SSL
and
rebuild
it
in
debug
mode
and
try
to
figure
out
what
I'm
doing
wrong.
D
One
of
the
big
issues
that
I
talked
about
was
defining
a
new
cozy
key
type
I.
Actually,
in
my
codebase
said
no
I'm,
just
gonna
have
a
parameter
which
says:
how
do
you
create
it?
Create
a
cozy
key
from
this
public
key
and
I've
found
that
to
be
sufficient,
so
I
don't
think
we
actually
need
to
carry
them
separately.
D
M
M
D
I'd
like
to
have
sure
we
have
at
least
a
day
idea
of
what
I'd
use
it
for,
and
there
are
content
types
defined
for
just
a
bearer
I
mean
it
would
make
sense,
potentially
to
define
a
content
type
for
bare
x.509
certificate,
but
not
for
what
not
for
one
of
you
not
for
a
barrier
certificates,
maybe,
but
we
would
wanted
to
find
the
content
types
that
match
up
to
the
current
contents
that
exist
like
that.
At
one
point,
you
were
planning
to
do
a
drop
at.
M
D
B
D
B
D
B
C
Okay,
there
we
go
so
this
specification.
As
you
may
recall,
the
purpose
of
it
is
to
register
some
existing
algorithms
that
are
used
by
the
web
application
specification,
both
in
the
cozy
algorithms
registry
and
to
make
corresponding
registrations
if
they're
not
already
present
in
the
Hosea
registry
and
the
draft
fulfills
a
charter
point.
C
So
what's
happened.
Since
we
last
met
our
heroes,
we
had
working
group
adoption
of
an
individual
draft.
We
changed
the
title,
as
requested
by
the
working
group
address,
review
comments,
some
of
which
were
substantive
from
John
Matson,
Matt,
Palmer
and
Jim
shod,
and
we
did
make
normative
changes.
The
primary
change
was
to
change
the
Jose
curve,
identifier
from
P
256k,
which
had
been
made
up
and
was
in
use
by
some
early
implementations
to
sect
P
256,
K
1,
and
that
was
discussed
on
the
list.
I
won't
repeat
the
rationale
here.
