►
From YouTube: IETF106-IDR-20191121-1740
Description
IDR meeting session at IETF106
2019/11/21 1740
https://datatracker.ietf.org/meeting/106/proceedings/
A
A
A
The
the
good
news
is,
if
you
go
back
and
look
at
the
different
drafts
that
were
proposed
and
I,
think
that
you
know
in
various
flavors,
were
you
know
we
got
up
to
at
least
four
of
them,
they're
all
pretty
close
in
terms
of
semantics.
They
all
look
more
or
less
like.
Let's
exchange
the
data
necessary
to
bootstrap
hold
on
just
one
second
to
bootstrap
appearing
and
then
let's
you
know,
move
forward
from
there
AC.
Yes,
please
go
ahead
as
a
simple
reason
for
that
John,
a
selenium
Cisco
Systems.
A
Yeah,
if
anybody
would
like
to
do
Tom
Lehrer
impressions
later,
you
know
at
the
bar-
please
do
okay,
so
so
yeah,
but
we've
got.
There
are
a
number
of
important
differences
between
the
various
approaches
and
things
that
just
haven't
gotten
nailed
so
rather
than
having
you
know
a
whole.
Several
different
teams
of
authors
continue
to
work
on
their
own
drafts
and
then
you
know
debate
about
it
in
the
working
group.
A
A
A
If
you're
have
suggestions
for
how
it
should
operate,
that
means
you
probably
should
also
approach
the
chairs.
You
know
we
would
like
to
do
a
solution
that
is
pragmatic
because
there's
obviously
been
appetite
for
this
for
a
while.
Now,
let's
get
it
done
and
then
we
can
iterate
forward,
so
it
does
not
necessarily
have
to
solve
the
generic
ultimate
protocol
problem.
It
just
has
to
be
useful
for
some
of
the
important
use
cases
that's
about
it
will
keep
the
working
group
updated.
A
A
Think
that
I'm
an
unrealistic
goal:
okay,
well
I'm
famous
for
setting
unrealistic
goals.
We
thank
you
for
the
for
the
feedback.
You're,
probably
right.
If
you
say
that,
because
you've
done
this
more
times
than
I
have
we
will
at
least
have
a
report
out
by
the
next
IETF.
If
it's
an
interim
report,
then
so
be
it
I
mean.
Obviously
the
conclusion
of
the
design
team,
at
least
my
expectation
is
the
design
team
is
not
to
present
the
working
group
with
a
finished
product.
A
D
D
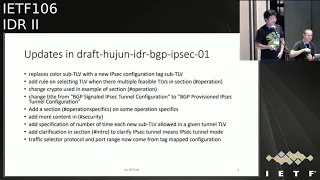
Okay
yeah,
so
the
first
one
is
I've
made
update
for
mark
previous
IDR
BGP
IPSec
a
draft,
so
that
update
is
based
on
the
feedback
feedback
I
received
so
far
since
last
IDF,
the
first
one
I
replaced
the
color
sub-team.
Is
the
new
IP
ii
finishing
tag
sub
TOB,
the
reason
being
that,
instead
of
being
overload,
the
color
sub
TOB,
it's
clear
to
use
a
new
sub
theory
for
such
poppers
next
ones
are
some
text
on
the
selecting
theories
when
there
are
multiple
IP
SEC
theories.
D
What
should
what
system
should
do
in
when
the
tanner
goes
down
or
when
sister
should
agree,
stops
taro
and
also
add
more
content
in
the
Security
section?
Basically,
he
says,
like
I,
agree
to
what
kind
of
mechanism
to
proven
accurate
to
level
dos
attack,
and
so
also
at
specification
and
map
of
time.
Each
of
this
new
sub
theory
could
appear
in
the
give
antenna
theory
and
so
order.
Some
clarification
in
the
intro
to
just
to
clarify
this
draft
is
about
IPSec,
can
a
mode
and
then
last.
Why
is
that?
D
D
Then
I
write
a
new
draft
about
using
the
IPSec
transport
mode
with
any
type
of
IP
said
sorry
any
type
of
IP
tunnel.
So
this
one
is
little
bit
different
from
current.
What
define
in
the
tunneling
cap
draft
current
Alan
capital
can
specifies
how
panel
stack
works
like,
for
example,
tano
X
in
inside
a
kind
of
Y,
but
the
IPSec
trust
model
is
working
it'll
be
different,
because
it's
really
not
a
ton
of
stack.
It's
really
using
a
same
IP
header
for
the
IPSec
transport
protection.
D
D
So
it
is
it's
like
it's
like
attribute
to
exiting
IP
tunnel,
for
example
in
this.
In
this
figure
it
shows
the
GRU
is
IPSec
transformer
protection,
but
it
could
be
any
type
of
a
piano
like
be
excellent.
Whatever
you
couldn't
apply
this
every
sector
spot
action,
so
the
current
kind
of
ink
up
that
and
really
address
such
a
use
case
so
I.
That's.
Why
I
great
a
new
draft
for
this
I
think
or
it
goes
through
this.
D
So
how
does
it
work
so
in
this
draft
I
introduce
a
new
IPSec
transport
protected
sub
tier
V?
The
value
of
this
theory,
sub
theory,
is
that
it's
an
IPSec
convenient
tag
as
defined
in
the
previous
draft,
when
IPSec
in
capturing
theory
includes
this
new
sub
theory,
it
means
that
the
sizing
router
requires
IPSec
transport
mode
protection
for
the
corresponding
IP
tunnel.
D
So
once
the
receiving
side
receiving
router,
get
this
update
and
and
descend
to
four
packets
to
this
advancing
router.
So
he
will
use
following
a
piece
of
config
to
create
a
try
to
say
so.
Basically,
you
use
transpose
with
ESP
and
then
the
public
probability
instance
would
be
the
same
as
the
packet
to
be
forwarded,
and
the
pier
tunnel
address
would
be
same
as
indicated
in
the
remote
endpoints
of
tier
V.
The
local
traffic
selector
would
be.
The
following.
D
Address
range
would
be
the
Lakota
endpoint
address
the
protocol
and
the
pot
grinch
coming
from
the
IPSec
configured
attack,
mapped
a
value
similar
to
the
motor
traffic.
Selector
address
range
would
be
the
address
in
the
remote
endpoint
security
of
the
selected
tunnel
in
capsule.
In
theory,
the
protocol
and
Poe
range
will
become
from
the
tech,
mapped
value
and
other
transfer
confusion
like
transform
a
lifetime.
Those
ipsec
confusion
also
come
from
the
tech
map
value.
So
this
is
a
quite
straightforward
idea
to
have
this
IPSec
transport
mode
protection
protocol
attano
editor
the
BGP.
D
C
C
E
E
C
C
I
think
the
answer
I
have
a
few
questions
for
him.
I
the
old
IPSec
tunnels
work
slightly
different
in
my
mind,
but
I
may
need
more
clarity.
I,
don't
think
we
should
I
think
they
work
different
is
the
answer,
but
I
may
be
mistaken.
So
before
I
can
do
a
working
group
last
call
or
adoption
call
I've
got
to
figure
out
how
much
overlap
last
time.
My
understanding
from
the
SEC
folks
is
that
they
made
some
suggestions
for
it.
C
A
F
F
D
This
is
just
V,
so
just
the
control
plane
protocol
right,
so
yeah
I
think
I
think
your
point
is
mainly
on
how
do
you
I'll
do
safeguard
BGP
itself
from
like
attacking
attacking
right?
That's
that's
your
point.
Like
there's
a
multiple
mechanisms
in
VG
like
HV
sack
like
outbound
the
future,
you
can
use
those
to
prevent
attacking
okay.
F
All
right,
but
you
have
much
more
information
just
than
a
s
number
I'm
talking
to
my
peers.
You're
talking
about
configuration
or
the
Lexi
have
a
is
in
Singapore
B
is
in
Beijing
or
in
Dallas,
for
example,
and
you're
sending
this
BGP
update
from
Singapore
to
Dallas
through
public
internet,
with
your
configuration
Wow.
D
D
F
D
A
Guys
our
time
is
pretty
tight,
so
if
you've
got
like
specific
questions
about
encodings
and
stuff,
like
that,
I'd
like
to
ask
you
to
keep
that
for
the
mailing
list.
If
you
have
like
fundamental
questions
like
your
first
one
was
more
about
the
security
properties.
I
think
that's
appropriate
for
our
discussion
time
here.
Ok,.
G
Jeff
has-
and
this
is
directed
mostly
to
Linda's
question,
so
everything
in
the
tunnel
encapsulation
attribute
has
this
security
problem
in
the
sense
of
you
know,
the
security
properties
can
get
away
from
where
the
routes
have
been
injected.
This
means
that
you
have
to
worry
about
securing
this
at
your
edges
of
your
network.
C
F
G
Say
that
again,
Linda
is
correct.
That
transport
such
as
MPLS
do
have
the
advantage
that
they're
sort
of
put
scopes
locally
to
a
network,
whereas
this
or
to
take
an
example,
SR
v6,
which
knows
intentionally
supposed
to
be
able
to
go
across
no
things
like
the
Internet.
The
security
considerations
do
change
a
little
bit
and
I
suspect
at
some
point.
This
is
going
to
come
back
and
make
the
security
ADEs
make
doesn't,
has
Carter
questions.
Okay,.
C
E
C
E
F
Okay,
hello,
can
you
hear
me
okay?
So
this
is
the
second
time
we're
presenting
this
and
just
give
an
update
on
what
we
have
done
so
far.
So
the
intention
of
the
draft,
it
is
really
a
informational
draft.
We
have
applied
a
Safi
for
sd-1,
and
here
we
want
to
explain
how
the
sap
is
used.
That's
it
and
we
will
be
glad
to
get
I
would
like
to
get
your
feedback
on
how
we
use
it,
or
maybe
some
suggestions
will
be
even
better.
F
Actually,
we
already
call
some
suggestions
from
some
IPSec
folks,
so
in
this
domain
you
can
see
that
we
have
a
bunch
of
CPEs
located
in
different
locations
and
the
CPE
is
interconnected
by
multiple
types
of
network.
They
can
have
MPLS
Network
and
they
can
also
have
in
Internet
public
Internet
untrusted
and
they
are
in
their
own
administrative
domain
together
with
the
route
reflector.
So
each
of
the
nodes
has
the
secure
channel
to
the
rot.
Reflector
Dave
Corral
had
this
good
term
Confederated
IPSec.
F
So
it's
different
from
the
traditional
peer-to-peer
IPSec
like
if
you
do
traditional
IPSec
as
who
we
drink
just
mention
that
you
need
to
configure
a
lot
more
things,
not
only
need
to
configure
yourself.
You
configure
your
peers
and
you
configure
who
is
attached
on
your
side
and
who
is
attached
on
the
remote
side,
and
you
have
to
set
up
the
tunnel
peer-to-peer
in
this
Confederated
mode.
Each
node
don't
even
know
who
is.
He
is
supposed
to
talk
to
basically
the
security
policy.
The
set
as
ad
is
managed
by
the
reflector,
the
central
controller.
F
This
is
for
the
SD
one
case.
A
node
is
expected
to
be
0
attached
provisioning,
while
he
being
powered
up
supposed
to
be
running
right
away,
so
he
doesn't
even
know
who
he
can
talk
to
so
he's
in
his
own
information
to
the
rot
reflector
to
the
controller
and
then
with
his
own
information
in
the
wrong
reflector.
Decide
who
this
message
is
propagated
to
and
in
this
domain
is
under
the
assumption.
Everybody
trusts
his
own
controller,
because
this
update
is
just
a
small
portion
of
the
entire
scheme
of
things.
Not
only
you
trust.
F
The
controller
tell
you
who
we
are
supposed
to
talk
to.
You
also
have
other
configurations
like
the
tractor
pattern,
who
your
client
is
a
bunch
of
more
information
which
is
complete
out
of
scope
of
BGP
idea,
so
in
in
this
domain,
the
node
himself.
What
do
a
regular
BGP
update
to
basically
propagate
his
attached
routes?
That's
basically
his
VPN
his
attached
routes.
F
So
what
he
does
need
to
do
is
be
able
to
advocate
propagate
the
the
web
port
properties,
including
the
routable
public
routable
address,
because
this
PE
choose
port
to
get
assigned
address
from
isp
like,
for
example,
Verizon
or
China
Telecom,
and
so
he
need
to
tell
them.
Who
am
I
my
identity
and
then
send
a
message
through
a
secure
channel
to
the
route
reflector
and
row.
Reflector
were
propagate
that
information
to
the
remote
notes
were
authorized,
remote
notes
in
them.
F
So
in
the
Li
the
path
attribute,
you
will
give
the
identity
of
the
sport,
the
one
foot
and
in
the
past,
the
tunnel
in
cap
path
attribute,
and
you
need
to
include
the
net
information
you
need
to
include
IPSec
information.
If
there's
a
certain
application
can
only
be
talking,
have
certain
topology.
You
may
need
to
indicate
that
as
well.
So
that's,
basically
how
this
new
and
RI
is
used
is
used
for
an
ten
defy
the
web
port.
That's
it.
F
The
tunneling
cap
is
pretty
much
saying
as
before,
so
so
for
the
the
web
port
and
entity,
there
will
be
several
attributes
to
uniquely
identify
this
went
port,
so
there
will
be
port
and
then
the
fire
write
this
port
and
then,
if
I
may
be
locally
significant.
The
note
may
only
know.
Oh,
this
is
meant
number
one
point
number
two
port
numbers
report
and
there's
another
attribute
could
be.
F
Another
one
is
the
routable
address,
meaning
how
can
anybody
else
reach
you
right
see
if,
if
I'm
here
in
Singapore
and
my
peers
in
Dallas-
and
they
had
to
know
how
to
reach
me,
there
has
to
be
a
routable
address.
So
that's
the
note.
Id
address.
Okay,
those
three
attributes
uniquely
identify
the
port
here-
is
the
sub
TOB
for
the
net.
So,
basically
you
need
to
indicate
what
kind
of
a
net
type
it
is.
F
You
need
to
indicate
how
your
panel
associated
property
associate
with
net
here
is
the
information
to
be
carried
minimum
information,
we're
not
talking
about
full
suite
of
information
for
IPSec,
but
minimum
information
that
there's
no
need
to
pass
through
his
route.
His
controller,
actually
I,
took
most
of
the
information
from
Dave
Dave
Corral's
a
draft.
So
basically
you
need
to
include
what
kind
of
weather
is
a
th
or
ESP,
whether
it
is
your
public
key
right.
You
have
to
tell
everybody
a
public
key.
You
have
to
tell
them
the
the
key
counter.
F
This
key
is
the
first
time
or
second
time,
and
you
know
child
tell
the
controller
your
nose
and
you
may
have
another
indicator.
You
probably
want
to
tell
so.
I
have
another
field
that
keys
three
they're,
just
four
additional
field:
that's
that's
it
and
that's
the
minimum
ones,
and
if,
if
this
this
and
note
need
to
establish
like
route
based
IPSec
tunnel,
you
can
also
do
that.
Actually,
you
can
use
footings
draft
to
be
able
to
establish
broad-based,
IPSec
tunnels.
F
A
F
A
A
F
F
F
F
H
Actually,
actually
did
John
made
the
same
point.
I
was
gonna,
make
about
the
information.
I
read
the
draft
on
the
plane
and
I
didn't
even
realize.
I
thought
it
was
standards
track,
okay
and
and
I
didn't
check
to
see
that
the
Safi
was
a
FC
FS
yeah,
I
Anna,
so
I
didn't
know
that
you
wouldn't
need
a
document
to
allocate
one
I
mean
it
wasn't
apparent
to
me,
but
I
understand.
F
H
F
A
C
I
Items
so-so
is
going
to
pick
up
on
from
some
of
the
slides
and
speak
to
them.
So
tremendous
interest
in
trying
to
get
this
done.
The
deprecated
yes
sets
and
yes
can
fred
seitz.
At
least
we
have
been
doing
a
great
deal
of
measurements
and
the
measurements
show
that
out
of
800,000
routes,
less
than
500
have
a
assets
in
them,
so
very
a
minuscule
percentage.
And
if
you
start
looking
at
them
more
closely,
we've
done
a
pretty
detailed
analysis.
The
link
is
at
the
bottom.
I
C
I
G
The
interesting
thing
we're
seeing
in
this
dad's
is
that
roughly
10
percent
of
the
Internet
is
using
a
knob
that
is
resulting
in
aggregation
of
routes,
so
this
is
proving
that
no,
this
is
actually
a
dangerous
thing
for
us
to
be
touching
what
if
we
actually
get
involved
in
the
specs?
This
is
really
my
feedback.
G
That
demonstrated,
you
know.
One
of
the
reasons
we
get
into
this
simple
example
is
that
consider
a
set
of
a
s
set
of
routes
that
have
you
know
in
null
a
s
path.
This
is
strictly
internal
and
then
you
have
similar
set
of
routes
that
have
a
single
a
s
in
there.
If
you
do
aggregation
by
the
current
rules,
you
know
the
longest
common
path
is
0
and
everything
else
gets
tossed
into
us
at
length
of
1.
Now,
what's
sort
of
interesting
for
these
things,
it
is
potentially
possible
in
such
a
case.
G
Maybe
merge
this
into
the
actual
AAS
sequence.
That's
right!
Next
to
it.
In
that
case,
the
length
would
be
preserved
versus
what
we
actually
see
of
the
set
on
there,
but
the
question
really
becomes
whether
this
is
preserving
the
actual
origin
1/10,
especially
since
the
whole
point
of
this
exercise.
Is
people
don't
like
this
because
of
its
impact
on
rpki?
G
So
the
two
observations
here
is
that,
in
the
case
where
you
may
actually
have
in
the
case
of
you
know,
and
a
s
followed
by
a
set
of
the
same,
a
s,
the
merge
operation
has
sort
of
an
optimization
may
make
sense
to
preserve
the
length.
The
other
observation
is
pretty
much
the
brief
style
of
aggregation,
which
has
been
implemented
by
pretty
much
every
implementation
of
each
B
aggregation
since
the
1990s
will
actually
make
this
know
the
correct.
I
So,
even
if
is
for
announces,
the
the
less
specific
to
a
s,
2
s,
2
will
still
be
fine
because
it
installs
the
less
specifics
that
are
necessary
within
the
the
the
more
specifics
that
are
necessary
within
the
less
specifics
s
operation
at
a
s
2,
the
overall
operation
will
be
fine.
Only
problem
arises
when,
if
P
2
stash
24
gets
cut
off,
then
there
is
a
possibility
of
data
packets
looping
for
a
brief
period
of
time,
and
that
goes
away.
I
I
So
one
question
is:
would
the
working
group
like
to
see
that
change
to
must
just
use
the
stronger
language
and
deprecated
without
allowing
any
room
for
use
of
a
assets'
under
any
circumstances,
and
that
would
help
things
like
IP
care,
origin,
validation,
BGP,
SEC
and
Alexander's
ASP
a
great
deal
not
having
assets
in
the
updates.
So
there
are
two
choices
here.
Def
is,
as
you
will
see
in
the
next
few
slides
he
he
thinks
that
it
is
possible
to
just
have
a
BCP
with
the
operational
considerations
clearly
specified.
I
On
the
other
hand,
we
can
do
a
change
to
the
existing
RFC's
that
that
talk
about
a
SaaS
Confed
set,
make
it
as
standards
document
which,
which
updates
these
other
documents,
which
has
a
asset
india's
conferred
set
on
them
in
them,
and
it's
doable
I
have
identified
how
many
mentions
of
these
things
are
there.
We
can
go
and
make
specific
target
recommendations
regarding
wording
changes
so
that
syllable.
C
That
is
one
of
the
projects
that
I'll
send
to
the
working
group.
It
might
be
the
time
to
do
that,
since
we
would
have
to
do
it
anyway
and
I
had
a
lot
of
pieces,
so
this
might
not
be
the
problem
you're
thinking.
That
was
something
we
were
talking
about
in
the
Charter.
If
you
hate
that
idea
do
come,
tell
the
chairs
the
idea,
if
we
do
an
internet
standard,
is
not
new
features
but
to
document
what
is
existing
in
out
there.
Just
so
I.
G
So
the
feedback
I
have
given
is
that
if
we
are
going
to
touch
these
specs,
it
is
deeply
intrusive
and
we
have
to
be
very,
very,
very,
very
careful
about
them
and
a
number
of
us
spent
a
lot
of
time
getting
these
right.
The
alternate
paths,
for
you
know
standardizing
this
or
PC
peeing.
This
is
no
we're
saying
pretty
much.
Every
implementation
does
support
brief
aggregation,
so
no
new
code
is
actually
needed
to
do
the
correct
thing
here:
convincing
your
vendor
that
a
default
knob
no
needs
to
change
his
behavior.
G
That's
a
different
question,
but
in
terms
of
functionality
it
is
already
present
there
isn't
any
need
to
necessarily
change
in
the
RFC's.
6472
came
out
some
time
ago
and
said:
stop
doing
this
well,
they're,
not
gonna.
Stop
doing!
This
is
brief
implementations.
It
is
reasonable
to
ask
the
vendors,
including
the
person-
that's
standing
at
the
microphone
here
to
add
policy
such
that
a
assets
can
be
matched
with
in
the
policy
engine
so
that
you
can
implement
no
drop.
G
This
prefix,
if
you
so
chose
and
somewhat
in
the
absence
of
no
people,
actually
no
doing
any
of
these
things.
Rpki
filtering
is
becoming
more
and
more
common
if
people
don't
clean
up
their
own
act
in
their
own
self-interest,
they're,
just
something
I
get
their
routes
filtered
anyway.
You
know
this
is
a
self-correcting
problem.
G
My
sort
of
recommendation
is
that
we
take
this
opportunity
and
you
know
clean
it,
use
the
operational
considerations
section
here
and
cover
the
facts
of
what
happens,
but
you
know
what
was
sets
actually
there
for
it.
What
does
it
actually
prevent
you
in
terms
of
receiving
routes
within
your
network
and
receiving
your
own
forwarding?
G
So
you
know
that
the
behaviors
that
we
need
that
we
see
that
are
known
that
are
called
out
in
the
RFC,
but
aren't
necessarily
something
you
think
through
unless
you're
an
operator
aggregators,
you
know
the
person,
that's
actually
doing
that
needs
to
supply
the
more
specifics
to
the
contributing
a
s's.
You
know,
that's
that's
the
behavior
that
was
expected
out
of
this
when
you're
doing
proxy
aggregation.
It's
not
documented
anywhere
the
entity.
That's
doing.
G
That's
capable
of
doing
that,
you
know
is
a
tricky
thing,
I'm
aware
of
from
at
least
one
that,
when
a
service
provider
that
they
have
a
practice
of
taking
their
own
address
space
and
basically
nailing
up
a
black
hole
route
internally
for
all
of
their
own
space,
and
this
keeps
traffic
knowing
in
the
case,
you
actually
do
get
some
sort
of
a
great
route
internetwork
from
leaving
the
network.
This
again
is
not
written
down
anywhere,
and
this
is
not
a
bad
place.
To
put
it.
J
K
C
C
L
Think
I
want
to
echo
Jared.
This
is
a
thank
you.
This
is
going
to
be
a
lot
of
hard
work,
but
it's
needed
to
be
done
we
couple
of
years,
so
you
go
gosh
and
skip
Verizon
media
Yahoo
a
couple
years
ago,
like
eight
or
so,
we
went
through
a
painful
process
of
changing
every
single
announcement
that
we
had.
That
was
using
aggregation
a
assets
to
do
atomic
aggregate,
so
I'd
like
to
echo
Jared.
Can
you
give
people
a
knob
that
just
says,
convert
AS
sets
to
atomic
aggregate.
L
G
L
G
L
L
M
Just
a
short
remark:
I'll
try
seeing
seeing
discussion
about
cleaning
up
certain
historic,
artifacts
and
deprecating,
some
of
them
I
would
suggest.
We
probably
should
be
also
considering
to
clean
up
as
far
as
possible
the
a
that
you
bite,
a
SS
showing
up
just
I
I
got
the
idea.
We
should
be
thinking
about
it
after
once
more
this
week
having
to
comment
that
well,
okay,
figure,
well,
okay,
creating
complexity
in
new
BGP
stuff
to
take
care
of
the
of
implementations
that
actually
don't
do
to
be
don't
do
for
by
it
is
that's!
G
So
comments
the
chairs.
Basically,
what
we
have
is
no,
we,
the
original
draft,
which
says,
let's
perceive
a
deprecation
I'm,
offering
an
alternate
path.
That's
basically,
here's
ways
to
take
it
forward
as
a
clean
up
thing,
the
Britain
group
will
need
to
figure
out
which
way
wants
to
go.
I
can
contribute
text
either
right.
Thank.
A
N
So
this
very
quick
get
ontological
Cisco.
So
we
have
this
working
group
draft.
It's
about
SR
policy
Safi
for
signaling
of
SR
policies
from
controllers
to
head
ends
by
a
BGP.
Now
it's
been
there
for
quite
some
time
and
we
are
preparing
for
working
group
last
call
it's
a
companion
draft
of
the
SR
policy
architecture
draft
which
is
in
spring
and
also
close
to
working
group.
N
Last
call
implementations
are
around
even
deployments,
so
what
we
have
done
in
this
recent
updates
is
taken
care
of
some
things
to
make
this
last
called
smoother
and
go
faster,
so
I'm
not
going
to
go
into
all
of
these,
because
there
has
been
some
disk
on
the
thread
and
we
are
running
short
of
time.
So
key
points
is
error.
Handling
things
have
been
consolidated
in
in
one
section,
just
to
make
it
easier.
N
Iana
considerations
has
been
updated
to
catch,
something
which
was
missed
out
from
the
color
extended
community
and
some
minor
changes
to
the
allocation
process.
We
welcome
feedback,
so
this
is
really
more
of
a
heads
up
to
the
working
group
to
review
provide
inputs.
Implementation
reports
have
been
updated
with
two
implementations,
so
hopefully
by
when
cooler,
maybe
we
can
get
it
the
next
one
is
the
BGP,
also
working
group
document
for
BGP
LS
applications,
specific
attributes.
This
will
be
even
faster
hope,
so
just
want
to
update
the
progression.
N
The
key
thing
which
I
wanted
to
point
out
here
is
that
underlying
IGP
specs
have
are
in
the
review,
is
de
review
and
as
they
have
been
updated
based
on
feedback,
we
have
updated
this
spec
to
be
aligned
with
them.
So
again,
I'm
not
going
to
go
into
the
details,
but
at
a
high
level.
That's
all
about
what
the
changes
to
this
draft
is.
So
we
are
requesting
for
review
and
once
the
IDP
drafts
go
past
the
work
there
is
d
reviews.
C
H
O
So
in
the
inter
demand,
sigma
routing,
we
are
seeing
more
and
more
cases
where
you
know,
network
attributes
and
natural
resources
are
assigned
colors
and
colors
used
together
with
BGP
next
hop
to
map
a
prefix.
You
know
a
service
prefix
or
pelo
prefix
to
transport
a
nose.
So
in
this
case
here
we
have
pedal
prefix
with
BGP
next
sub
N
and
color
red,
and
we
map
it
to
a
red
tunnel
to
n.
There
are
two
reason
behind
that.
O
O
Second
reason
is
that
you
know
color
encoded,
as
BGP
community
can
be
conveniently
signaled
across
the
main
boundaries
and
can
be
signal
from
controller
to
routers.
So
if
we
can
assign
colors
to
network
attributes
or
animal
resources,
we'll
be
able
to
create
the
color
tunnels
and
color
the
panel
prefixes,
the
kind
of
tunnel
would
be
the
color
of
the
network
attribute
that
based
on
which
the
tunnel
is
established
and
the
color
of
the
payload
prefix
will
be
the
color
of
the.
O
You
know
that
the
color
of
the
type
of
the
tunnel
that
the
prefix
desires,
so
on
top
of
that,
if
we
can
do
color
based
Tunnel
selection,
will
have
a
very
general
service
map
in
the
chasm
it
can
work
in.
You
know,
inter
domain
environment
and
controller
driven
environments,
so
red
you
know,
red
color
panel
prefix
mapping
to
a
retino
is
the
most
basic
mapping
mode.
In
many
cases
we
would
like
to
have
much
more
flexibility
flexibility.
O
O
Each
scheme
consists
of
a
sequence
of
extended
modes
in
in
a
fallback
order,
meaning
that
you
know
you
select
your
title
based
on
the
first
mode.
If
it's
unsuccessful
you,
you
know,
move
on
to
your
second
mode
and
a
third
mode
so
on
so
in
this
example,
we
have
pelo
prefix
with
next
op
n
and
color
red
and
that
the
user
may
define
a
scheme
and
attach
to
that
pelo
prefix.
There
are
three
modes
in
this
scheme:
the
first
ones
are
color
IP
card
with
a
fallback,
blue
and
green.
O
O
O
We
comfort
a
configure
the
scheme,
the
egress,
router
and
I
will
use
BGP
to
signal
the
scheme
with
the
payload
prefix
to
two
ingress
routers,
and
here
we
are
using
a
new
path,
attribute
called
the
flexible
color
tunnel
exit
path
attribute
and
then
on
the
each
ingress
router.
We,
you
know,
apply
the
scheme
to
the
associate
pelo
prefixes.
O
O
This
shows
the
encoding
of
the
new
path
attribute.
It
consists
of
a
sequence
of
extended
mapping
mode
T
RVs.
Each
t
RV
has
a
mode
value
and
it
may
optionally
have
a
list
of
four
for
bad
colors.
So
this
Lisa
for
bad
colors
applied
to
the
some
some
mode,
not
all
the
modes.
Okay
and
the
segment
routing
policy,
draft
and
ID
are
same
routing.
Policy
draft
defines
two
so
called
color
only
a
bits
in
the
color
extending
community
and
defines
three
four
back
modes.
O
C
Have
just
a
few
questions
for
you
number
one:
have
you
shown
this
particular
scheme
to
the
spring
folks
who
are
working
on
the
other
dress
with
policy?
We
have
not
okay.
That
might
be
at
least
why,
since
you
refer
to
that,
secondly,
can
you
compare
and
contrast
it
with
the
use
that
other
than
the
IPSec
portion,
that
June
was
using
for
his
color?
The.
A
Actually,
I'm
sorry
can
I
ask
you
to
take
it
offline
because
we're
we're
actually
out
of
session
time.
We
have
one
more
thing
on
the
agenda.
I
will
ask
people
if
you
can,
if
you
have
five
minutes,
please
give
us
five
more
minutes.
Please
we
did
have
go
ahead.
I'm
just
as
you're
setting
up
I'm
gonna
make
one
other
announcement,
which
was
we
had
one
extra
talk
that
came
in
late.
We
put
it
on
if
time
allows
time
is
not
going
to
allow
I'm.
Sorry
Louis.
P
I'm
hiper
wall
from
Holly
a
noun
well
introduce
a
definition.
A
tRNA
is
filter
for
TPA
flows
back
because
now
frostback
is
used
for
a
judge
traffic
or
more
and
more.
Some.
Some
operators
give
me
some
requirements
outside.
You
want
to
adjust
a
trafficker
from
four
special
is
from
one
side
to
another
side,
such
as
the
front.
P
They
want
to
adjust
the
traffic
from
r2
to
r3
in
current
method,
or
we
can
we
also
care
into
each,
but
we
must
generate
several
multiple
across
the
back
roads,
understanding
the
true
the
rotor
we
must
use
for
sewing
room.
You
will
use
s
IP
and
the
IP
and
multiple
to
do
this,
but
we
probably
mostly
sell
so
we
use
one
road
to
instead
of
multiple,
we
use
a
destination
IP
or
aeneas
route
to
instead
of
multi
port
kasnia
IP
address.
P
We
now
use
a
new
component
type
40s
and
we
for
this
common
highway
suggest
method
to
to
realize
it
to
look
up
or
to
knock
out
fit
then
catch
the
t,
IPS
or
me
ears
and
then
use
a
TS
to
match
the
distro.
Also,
you
may
have
another
two
options:
you
to
expand
that
he
asked
for
to
multiple
the
IP
based
arose
under
the
there
is
a
location
and
the
evolution
gotcha
we
may
come
back
combined.
P
This
leg
z
combines
a
new
component
which
exists
for
us
back
common
answer
for
shark
man
matching
the
way
combined
with
the
money
touched
and
also
more
new
types.
So
we
want
to
introduce
such
as
a
society
or
nes
and
destination
IP,
community
or
society
community
and
the
others,
and
we
also
have
will
receive
some
comments.
There
are
two
about
too
many
considered.
One
is
the
security
consideration.
P
P
Also,
women,
you
know
the
target
to
country
to
control
well,
which
rotor
that
can
receive
this
new
component
type
and
now
another
question
Natalie
whether
we
will
use
a
new
Safi
for
this
common
type,
because
now
the
new
covenant
I
will
also
provides
a
match
criteria
under
a
fruit,
spec
architecture
north
of
the
component
type
of
menu
together
with
existing
common
type.
So
we
don't
want
to
use
a
new
Safiye
later
on.
We
may
welcome
to
or
for
comments.
Thank
you.
G
Jeff
Alice
I'm,
going
to
just
make
the
point
that
my
this
comments
stand.
Please
review
the
comments
on
the
list
for
context,
but
you
have
mischaracterize
my
objection.
My
objection
is
that
flowspec
operates
and
firewall
rules.
You
are
reaching
across
the
boundary
between
the
firewall
and
the
red
I.
H
Q
E
R
S
A
S
B
A
We're
five
minutes
over.
Thank
you,
everybody
for
sticking
it
out
sorry
for
running
over
our
time
twice
in
one
week,
we'll
try
to
do
better
next
time.
Hope
to
see
you
all
there
please
I
know:
we've
had
to
cut
off
several
conversations,
I
hope
you
continue
them
on
the
list
or
out
in
the
hallway.
Thanks
again.
