►
From YouTube: IETF106-IDR-20191118-1810
Description
IDR meeting session at IETF106
2019/11/18 1810
https://datatracker.ietf.org/meeting/106/proceedings/
A
We're
about
to
start
it's
true,
hello,
everybody!
This
is
IDR
we're
getting
started,
so
please
find
your
seats
or
find
the
door
or
you
know,
stand
up
and
back
at
the
peanut
gallery
or
whatever
su
is
going
to
put
a
note
well
on
the
screen
any
moment
so
that
you
can
have
seen
it.
But
I
bet
some
people
in
here
have
seen
it
but
I
think
yeah.
Here
we
go.
A
It
is
our
note.
Well,
it
is
the
ietf
policy.
You
did
agree
to
this
thing
when
you
registered
to
come
to
the
IETF.
If
you
don't
know
what
it
says,
you
probably
should
acquaint
yourself
with
it
enough
said
we're
gonna
try
to
cut
the
whole
comments
from
the
chairs
thing
well
short,
because
we
would
rather
spend
our
limited
time
on
other
stuff,
especially
because
sue
has
been
doing
a
bang-up
job
of
sending
out
periodic
status
updates.
A
So
it
would
be
kind
of
redundant
to
spend
our
time
here
and
now
sending
out
status
updates,
but
I
realized
I
should
walk
around
and
get
these
blue
sheets
moving,
please
sign
into
the
blue
sheet
and
whenever
they
get
to
the
back
of
the
room,
please
someone
bring
them
forward,
and
so
they
don't
get
lost.
It's
always
a
pain
to
have
to
find
the
blue
sheets
at
the
end
of
the
meeting.
A
Essentially,
I
noticed
that
you
know
I,
guess
I
didn't
just
notice,
but
we
have
a
lot
of
flowspec
related
drafts.
They
continue
to
come
in
every
meeting.
I
think
we've
talked
about
this
before,
but
as
a
reminder,
if
you
go
and
look
at
flowspec
flowspec
does
its
thing
using
NLRA,
the
NLRA
contains
flowspec
components.
Flowspec
components
are
structured
as
type
value
pairs.
They
are
not
structured
as
type
length
values
just
type
value.
A
A
This
isn't
really
good
for
flowspec
extensibility
there's
an
exception,
which
is,
if
you're,
defining
flowspec
over
a
new
a
few
Safi.
That's
fine
because
you've
got
a
demultiplexer
up.
You
know
that
you
do
know
how
to
find
that
either.
You
know
you
either
you
exchange
that
fe
Safi
in
your
MP
bgp
capability,
in
which
case
you'll,
will
know
how
to
parse
the
components
or
you
don't,
in
which
case
you
won't
get
the
component.
So
that's
fine,
but
you
just
get
one
shot.
A
A
Some
years
ago
we
had
a
flow
spec
v2
proposal
that,
among
other
things,
represented
components
as
type
length
values.
So
obviously
they
wouldn't
have
this
problem,
but
instead
we
have
not
worked
on
that
actively
because
we
have
taken,
you
know,
did
the
quick
thing
of
doing
the
bist
document.
First,
with
all
quick
things,
it
wasn't
quick.
A
B
B
Jeff
has
spent
a
lot
of
time
in
the
last
year,
actually
working
on
flowspec
code
and
some
of
the
reason
why
you
have
the
some
of
this
stuff
255,
something
like
this
number
one
piece
F
actually
picked
up
our
format
and
was
going
to
stick
it
in
their
protocol.
They
received
this
morning.
They
did
the
same
thing,
except
for
their
components,
actually
include
link
fields,
so
they
do
not
suffer
from
this
problem,
so
we
have
at
least
one
existence,
proof
of
change.
B
B
C
A
You,
let
seems
like
consensus
in
the
room
so
anyway
we'll
we'll
discuss
it
further
on
the
list,
but
I
think
that
will
be
the
you
know.
Even
though
I'm
standing
up
here,
I'm
I
do
have
a
chairs
hat
on
right
now,
I
I
think
that's
going
to
be
the
position
of
the
chairs
going
forward.
Is
you
know
you
can
you
can
discuss
your
your
extension
draft,
but
I
think
that
we
are
going
to
want
to
prioritize
the
groups
time
on
getting
the
the
TLV
thing
done
so
that
we
can
actually
roll
out
those
extension
drafts.
A
E
As
the
author
of
the
previous
one,
I,
really
don't
care
just
as
long
as
we
fix
the
TLB
problems,
so
open
proposals
are
are
okay
on
this
we
have
an
a
flow
spec
in
working
group.
Last
call
the
chairs
wanted
to
make
sure
we
knew
what
we,
if
we
had
any
sense
for
the
room
again
we'll
send
more
of
this
out
to
the
mail
list
but
seems
like
it
would
be
a
whole
lot
better
to
fix
it.
E
D
D
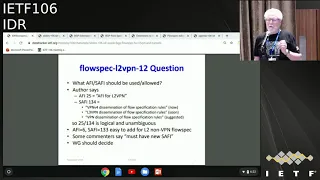
But
the
question
arose
on
the
mailing
list
with
expert
on
whether
this
can
use
Saffy
134.
So
a
fee
25
is
defined
as
the
a
fee
for
l2,
VPN
and
Savi
34.
Currently,
in
the
IANA
registry,
says
VPN
v4
dissemination
of
photo
spec
rules.
The
ipv6
draft
is
going
to
expand
that
to
be
l3,
but
ie,
then
this
staff
proposes
a
change
change
it
to
VPN
dissemination
because
you
can
tell
from
the
a
fee
whether
it's
VPN,
ipv4
or
ipv6
or
lastly,
in
this
case
level,
layer
2.
D
So
why
do
you
need
to
use
a
new
different
Safi
from
134,
because
the
a
fee
tells
you
what's
going
on
and
you
also
might
be
able
want
to
apply?
What's
in
this
draft
to
non
VPN
cases
and
there's
a
convenient
a
fee
for
that
you
can
use
fe6
and
Safie
133
an
ambiguously
from
the
definition
of
that
affiant
a
fee
would
clearly
make
what
case
it
was
appliable
too
obvious
to
anybody
getting
that.
So
that's
the
question
people
can
think
about
it
while
I
go
over
the
other
draft.
D
Is
there
a
good
reason
to
have
another
Safi,
which
I
think
is
a
burns
one
for
no
particularly
good
reason
for
this
ultra
VPM,
so
the
other
draft,
the
file
name,
is
unchanged
and
has
n
vo
3,
but
the
revision
to
the
draft
I've
that's
been
made
from
zero
version.
Zero.
Six
digital
seven
makes
it
really
not
nvo
three
specific,
the
oh
six
focused
there.
It
didn't
really
say
anything
about
sad.
It
wasn't
really
clear:
what's
a
feat
was
being
used
or
anything
it's
a
matter
too
good.
D
A
draft
in
that
regard
was
I
had
lots
of
other
good
stuff
in
it.
It
only
supported
VX
land
and
envy
GRE,
and
it
worked
by
having
a
delimiter
component,
which
marked
boundary,
so
it
sort
of
was
like
adding
a
component
which
is
we
found
least
currently
doesn't
work
at
all
and
may
not
be
the
probably
the
best
way
to
do
it
in
this
case
anyway.
So
the
new
draft
of
the
sex
7
changes
this
quite
a
bit.
It's
really
a
general
tunneling
or
encapsulation
kind
of
flow
spec.
D
It
proposes
to
use
a
new
Safi,
you've
just
TPD,
and
it
has
in
it
details
about
the
ex
lam,
not
just
vehicle
and
env
GRE,
but
also
l2tp,
v3,
IP
@
IP,
jerry
etc,
and
has
a
new
NLRA
structure
which
can
contain
one
or
optionally
also
a
second
flow
spec.
So
what
applies
to
the
outer
header-
and
that
applies
to
the
nested
inner
header,
which
you
would
need
frequently,
but
not
always
so
this
is
what
things
look
like.
This
shows
the
overall
attribute
at
the
higher
level.
D
Is
the
multi-protocol
BGP
attribute
where
it
is
a
naffy
Safi
next
hop
information,
then
there's
the
ml
or
I,
and
it
begins
in
this
draft
with
a
tunnel
type,
so
the
hole
type
actually
acts
sort
of
as
an
additional
thing.
If
you
don't
understand
the
tunnel
type,
you
can
skip
over
the
hole,
the
hole
attribute,
so
we,
you
could
add
things
for
specific
tunneling
headers
later,
even
with
the
same,
a
few
Safi
as
long
as
they
had
a
different
tunnel
type.
D
Okay,
then
there's
some
flags
regarding
discriminator
and
a
second
flow
spec
flag
and
some
reserved
Flags
routing
discriminator
field
and
then
the
then
there's
the
outer
flow
spec,
which
is
always
there.
That's
the
next
to
the
last
box
here
and
that
essentially
parsed
or
whatever,
based
on
the
a
fee,
that's
at
the
top
of
the
attribute,
and
if
the
second
flowspec
flag
is
on,
then
there
is
another
a
fee
and
the
inner
flow
spec
net
inner
a
fee
applies
to
the
inner,
let's
back,
of
course,
so
there's
also
this
Rodney
discriminator
bit.
D
So
if
this
is
the
VPN
case,
you
need
a
routing
discriminator
to
tell
what
VPN
vrf
the
stuff
is
in
that
you're
trying
to
look
for
and
right
it
might
not
be
so
that's
an
optional
thing.
This
way
that
you
only
meet
once
a
fee
rather
than
two
different
Saffy's
for
the
VPN,
an
on
VPN
case.
You
could
do
with
two
Saffy's,
but
it
seems
cheaper
to
use
a
bit
which
determines
whether
the
routing
discriminator
is
present.
So
this
just
blows
up,
the
NLRA
gives
more
detail,
shows
the
link
fields
and
so
forth.
D
This
draft
also
has
more
components
that
defines
because
of
the
other
kinds
of
tunneling
it
covers
previously
only
was
fee
excellent,
NB
GRE
and
only
had
added
the
tunneling
header
components
for
those
it
extends
the
flow
spec
ordering
rules.
So
you
can
tell
what
precedence
is
if
you
have
a
tunneling
and
a
non
tunneling
flowspec
that
both
match
or
something
like
that
includes
validations
based
on
entirely
on
the
outer
flow
spec.
So
whether
the
source
of
the
flow
spec
is
authoritative.
D
So
here's
two
examples.
The
first
one
is
IP
and
IP,
so
you
could
have
in
this
case
you
would
almost
always
have
an
outer
and
inner
flows
back,
because
it's
not
worthwhile
doing
really
for
IP
to
simple
IP
and
IP
intersect,
which
can
match
the
the
inner
IP
address
and
the
outer
one
matches
the
outer
one
and
in
case
of
l2
VPN
there
might
be
Mac
stuff
there,
which
case
you
need
to
use
a
appropriate
a
fee,
and
you
can
have
l2
stuff
as
well.
D
This
is
VX
lamb,
so
this
is
a
little
more
complex,
but
over
at
the
right
side
it
shows
what
would
be
covered
by
the
outer
flow
spec.
They,
let
us
say
the
flow
spec.
That's
always
present.
That
applies
to
the
outer
header
and
what
would
be
out
of
the
inner
flow
spec
so,
but
he
can
either.
One
of
them
can
contain
components
that
match
on
VX,
LAN
content
fields
and
in
both
cases
there
be
a
difference.
The
tunnelling
flow
specs
a
fee
would
be
there,
so
you
could.
You
would
only
get
to
code.
D
So
I
don't
know,
I
go
over
these
different
fields,
but
I'm
not
sure.
There's
too
much
here,
that's
obscure
or
anything.
So
for
once.
That's
always
what
particular
would
like
to
have
some
indication
whether
the
working
group
thinks
we
actually
need
to
use
a
brand
new
Safi
for
the
l2
VPM
or
whether
we
can
use
a
fee
25,
just
l2,
VPN
and
Safie
134
for
flowspec,
and
I'm
hoping
to
get
to
early
allocation
of
the
code
points
for
that.
D
But
he
needed
to
resolve
that
question
to
a
more
Reb
of
the
draft
for
the
N
via
3
full
spec,
which
I
could
change
the
name
or
something.
If
people
like
don't
like
that
file
name,
because
it's
no
longer
fully
specific
to
n
vo
3
I'd
like
people
to
look
at
the
latest
version
of
the
draft
and
provide
feedback.
I
do
think
it
needs
another
pass
to
polish
things
and
improve
it,
and
the
goal
is
to
get
Kol
points,
they're
also
on
a
goal.
E
B
Jeff
has
so
one
of
the
reasons
that
a
different
efi
Safiye
pairing
is
a
good
idea,
no
matter
what
is
your
changing
flowspec
precedence
rules,
so
the
problem
would
be
like.
Let's
say
that
you
just
stuck
this
into
what
are
the
existing
efi
Saffy's
as
just
a
new
component
type.
You
want
the
evaluation
to
be
a
different
order
than
what's
actually
in
there
and
that's
the
whole
point
of
an
athlete
Safi.
The
route
selection
is
consistent
across
the
entire
domain.
D
D
Happy
for
that
got
yeah
but
yeah.
My
question
really
is
for
the
for
the
l2
VPN
one
where
I
think
we
can
us
use
134,
25
134
for
a
fee
Safi,
and
it
has
been
asserted
by
at
least
one
person
that
that's
terrible
and
we
have
to
have
a
noose
a
fee.
There
I,
don't
I,
think
that's
unambiguous
and
it's
well
define
so
well.
I
knew
Safi
Ford.
The
tunnel.
Aspec
I
completely
agree
with
you
and.
B
The
only
reason
that
wait
is
sort
of
for
the
reason
that
we
were
talking
about
if
you
stuck
this
into
the
existing
a
fee,
a
fee
type
stuff
regardless,
whether
the
evaluation
is
correct,
a
lot
of
implementations
say:
I,
don't
know
what
this
component
is
and
drop
the
peering
session.
So
your
gated
behind
the
v2
work
or
you
go
with
a
different
Africa's
having
yeah.
A
E
Good
to
me,
okay,
okay,
one
of
the
things
that
again
because
John
presented
at
first
hopefully
you're
thinking
about
is:
should
this
go
in
a
in
a
B
to
fixing
the
type
length
order.
My
suggestion
is
to
give
him
code
points,
even
if
we
make
it
to
v2
decisions
so
that
we
can
get
experimentation
going
as
soon
as
possible,
and
so.
A
Just
to
add
I
think
that,
in
the
case
of
this
pair
of
drafts,
in
fact,
I
had
a
bullet
on
my
my
one
slide
that
but
I
think
covered
your
dress,
which
said
that
if
you're
defining
flowspec
over
a
new
a
piece
a
fee
pair,
you're,
okay,
because
it's
it's
fully
defined
and
I-
think
that's
the
point.
Jeff
was
making
it
the
mic
to
you.
So
I
don't
see
there
any
impediment!
You
know
on
that
basis
to
you
know,
moving
forward
with
these
two
drafts
right.
B
It's
actually
the
pairwise
of
the
Fe
and
the
Safi
together.
That
is
the
important
piece
the
you
know.
You
could
reuse
the
same
magic
number
in
Safiye.
If
the
fe
is
different,
the
code
is
different,
so
that's,
okay.
One
other
thing
I'd
point
out
is
that
looking
at
the
Safi
registry,
241
up
to
like
254
is
reserved
for
private
use.
You
could
just
grab
that
and
start
playing
with
it.
Okay
for
temporarily
Cumbria's
yeah.
F
I'm
going
to
talk
about
the
BGP
yang
model
to
begin
with,
if
we
have
a
new
author
edition
and
Jeff
has
a
agreed
to
join
it
and
be
an
author
on
the
draft
and
for
thanks
for
his
contributions,
I'm
not
going
to
go
through
the
status
you
can
go
through
it
look
at
it.
The
tips
are,
of
course
there.
If
you
have
any
questions,
feel
free
to
post
on
the
mailing
list.
F
So
I'm
going
to
talk
about
five
issues
that
we
are
tracking
they're
being
tracked
and
github
at
that
particular
location,
feel
free
to
comment
on
any
of
the
issues
there.
If
you
or
on
the
mailing
list
either
one
is
fine,
I'm
gonna
go
through
each
one
of
them
and
if
I
don't
hear
any
objections
and
by
also
posting
on
the
mailing
list,
if
I
don't
hear
any
objections,
I'm
going
to
zoom
it's
okay
to
proceed
and
implement
them
all
right,
so
the
first
is:
should
Confederation
be
a
peer
type.
F
B
As
the
question
from
Randy
Bushwood
to
differentiate
it,
yes,
so
the
motivation
is
hearing
sessions
are
internal
and
external,
and
are
you
appearing
with
your
Confederation,
yes
or
no
from
upstate?
You
know,
we've
always
shown
its
internal
or
external,
and
we
need
the
show
if
it's
Confederation,
because
the
rules
differ,
but.
G
B
H
H
F
F
I
J
A
B
F
The
third
issue
that
we're
tracking
is
the
a
spat,
Lent
container
ill
ill,
contain
the
calculated
s
padlet,
four
routes
per
42,
seven
rules-
and
this
is
mainly
for
the
user
to
see
the
number
that
serves
as
input
to
the
BGP
route
selection
are
in
odd
state.
Yes,
okay,
comments,
support
for
authentication,
so
currently
we
are
tracking
supporting
authentication
either
over
IPSec
TCP
md5
and
TCP
AO,
with
the
idea
that
we'll
probably
try
to
achieve
this
using
IDF
keychain
model
that
they
see
and
others
have
locked
on.
Ac
is
this
work
for
you.
F
J
J
B
H
J
B
J
F
E
B
K
Ok,
quick
North
capital
R
cos
the
the
King
mechanism
that
is
described
here
that
sees
his
trough
supports
us,
as
he
said,
for
md5
nao
for
IPSec.
You
probably
want
to
look
at
something
which
was
discussed
in
carp
working
group-
that's
close,
but
you
need
a
king
mechanism
or
a
key
material
to
be
exchanged.
E
Is
this
is
where
the
chair
I
take
off
my
co-author
hat
and
put
on
the
chair
had
this
is
essentially
in
order
to
get
to
be
effective
within
the
yang
committee.
We
need
to
actually
define
these
so
we'll
need
to
put
together
a
description.
There
are
two
option
in
a
chair
model,
separate
draft
or
this
draft.
My
suggestion
is
to
make
that
clear
and
and
easy
for
everybody
to
debate
on.
J
E
L
Have
a
question
now
for
the
model:
how
to
arise
to
implemented
for
multi
public
instance?
Not
for
we
are
all
behind
for
I
mean
that
if
I
have
money
for
PDP
incidence,
both
wrong,
we
came
before
or
other
adjust
by
then
I
have
some
way
of
instance.
It's
also
wrong
P
P
for
P
to
ze,
but
L
1,
for
example.
1
we
have
1
I
want
to
use
the
PDP
instance
the
one
to
advertise
beginning
for
roles
and
the
reacted
to
I
have
a
for
another
excellent.
E
A
L
B
F
E
M
E
M
That's
that's
fine,
so
the
observations
that
ever
make
is
that
we
know
how
long
the
process
can
take
for
each
one
of
these
documents
and
if
it's
not
one,
if
it's
multiple
one,
six
right,
maybe
consider
if
there
are
features
that
you
can
define
in
there
I
don't
know
advertising
active
routes.
That
sounds
like
a
true
sentence
thing
that
you,
where
you
can
describe
what
that
is.
Maybe
that
is
something
you
could
just
put
in
the
draft
right,
this.
It's
not
normative
or
anywhere
else.
Maybe
something
you
want
to
do.
E
J
N
N
So
in
this
draft
I,
we
addressed
all
the
comments.
So
it's
basically
the
first
one,
the
first
of
the
important
one.
So
some
people
don't
like
this
kind
of
extension
to
PGP
lr
s
for
s
ID,
so
we
just
get
a
raved
get
rid
of
that
one.
And
then
we
use
the
suggestions.
So
we
use
ur
new
at
the
NS,
a
v4
s
ID
as
suggested,
and
then
for
those
are
other
comments.
For
example,
people
says
why
you
use
a
BGP.
Why
not?
It
is
a
young
and
then
those
are
stuff.
N
So
we
give
more
detailed
explanations
for
those.
Why
and
why
not
in
the
draft,
and
also
some
people
mentioned,
that
we're
missing
something
we
straw
if
we
want
to
withdraw
these
SIDS
and
we
need
to
put
something
so
we
also
addressed
of
the
one
in
addition
to
that,
we
ad
the
cap
with
the
negotiations,
so
any
other
comments
regarding
for
this
new
version,
I.
E
E
N
N
N
So
basically
we
the
fact
that
the
format
of
this
one
this
is
similar
to
the
existing
rules
back,
so
each
one
will
contain
at
least
of
all
OP
and
values.
So
these
at
least
will
define
the
match
conditions.
So
has
this
much
condition
are
satisfied,
so
action
will
happen,
so
both
axes
are
at
same
as
the
existing
one.
N
E
We
recently
improved
the
v6
flowspec
by
releasing
it
and
making
it,
and
this
thing
had
co-author
on
the
v6.
Have
you
taken
a
look
at
it?
I
realize
we
just
made
the
deadline,
so
maybe
you
didn't
it
might
if
you
haven't,
if
you
I
forgot
to
mention
that
yesterday,
that
if
you're
looking
for
the
v6,
if
you're
only
SR,
v6.
E
E
E
J
Easy
later,
I
just
have
a
comment
on
all
these
flow
specs
and
the
idea
of
getting
a
flow
spec
for
every
end
cap
is
the
ID.
Is
there
a
framework
for
what
you're
gonna
do?
If
this
is,
it
seems
like
you're
doing
open
flow
with
flowspec
right
is
our?
Is
there
some
document
that
describes
the
requirement
and
what
you're
doing
of
this?
Or
is
it
just
just
because
if
there's
an
MP
and
that
end
cap
exists,
we'll
do
a
flowspec.
E
Okay,
see
John's
first
slide.
Our
first
thing
is,
we
think
we
oughta
as
chairs
again
chair
hat
on.
We
have
to
go
back
and
fix
the
basics
of
TLV
then
as
to
the
rest,
that
would
be
an
appropriate
time
to
say
what,
if
you
think,
we
should
narrow
our
scope.
At
the
original
definition
of
flowspec,
there
was
a
very
targeted
audience
and
a
very
targeted
focus.
The
addition
requests
have
indicated
that
the
same
denial
of
service
attack
work
is
concerned.
E
We
haven't
done
when
I
presented,
the
original
v2
I
had
called
for
a
thought.
Your
exact
question
of
harmonization,
the
working
group
asked
to
put
it
off
till
we
got
the
Bissau.
So
your
comment
is
germane
and
I
think
the
working
group
should
reconsider
all
these
things.
The
reason
I
asked
about
the
SR
v6.
This
is
a
new
type
of
caring
planter
that
seems
to
take
the
v6
control
plane.
I,
don't
know
enough
personally
as
to
the
deployment.
So
that
was
a
question.
I
guess:
yeah.
J
A
K
B
Jeffires,
as
far
as
the
applicability
goes,
the
motivation
that
all
these
different
authors
have
for
trying
to
drill
into
the
contents
of
various
tunneled
packets.
His
flowspec
is
being
used
for
two
big
cases
right
now,
the
first
one
for
dealing
with
standard,
DDoS
type
things
at
various
number
gauges
which
may
be
under
some
types
of
tunnels.
As
an
example,
you
know
if,
for
example,
if
I
would
pick
a
topic
near
and
you're
like
Linda's
heart
fit,
so
that's
the
UN
type
of
implementation.
B
You
may
need
to
be
able
to
do
a
flowspec
filter,
targeting
a
specific
port
for
a
specific
encapsulation
and
still
do
all
the
firewall
type
things
that
flow
spec
is
good
for.
So
that's
one
motivation.
The
second
motivation
and
I
suspect
from
some
of
the
people
in
the
participants
is
that
they're
using
the
flowspec
filters
to
be
able
to
be
used
for
traffic
engineering
purposes,.
E
N
One
Mia
is
about
a
extension
to
BGP
for
SR
pass
ingress
protection.
So
right
now
we
already
have
SR
policy
draft
is
invoking,
is
walking
walking
with
document.
So
as
our
policy
well
sender,
s
are
passed
to
the
ingress
node
of
data
pass
and
English,
not
West
set
up
that
pass,
but
when
that
humid
in
Lhasa
fails
so
in
order
to
prove
in
order
to
provide
protection
for
the
failure
of
that
English
node,
so
we
needed
to
also
send
up
another
by
car,
pass
through
a
backpack,
Harper
English
note.
N
So
basically,
in
the
previous
version,
we
already
talked
about
these
kind
of
extensions,
so
the
extension
is
the
first
small
and
then
we
just
made
stop.
At
least
this
opportunity
contains
the
information
for
the
protections
and
then,
in
this
version
we
just
make
made
a
little
bit
change
a
damn
war
description
as
a
subsidiary
which
described
the
traffic
that
a
backup
as
well
well
we'll
transport.
E
So,
on
all
of
this
a
couple
of
times,
I've
queried
these
bring
chairs
on
some
of
the
policy.
I
also
ask
if
you're
working
toward
using
this
spring
policy,
that
you
at
least
give
me
a
heads
up
operationally
what
what
this
is
being
used
for
on
the
are
pd
acceptance
as
a
draft.
I
also
call
for
operator
input.
P
Hi,
andrew
here
from
liquid
telecom,
we
are
using
s
or
policy
a
fair
amount
of
it
primarily
for
steering
traffic
around
places
that
how
do
I
put
this
certain
customers
do
not
want
to
root
over
certain
locations
of
a
certain
hardware,
etc,
etc,
and
so
we
give
them
the
option
to
steer
around
far
away
patch.
That
is
all
done
with
s
or
policy
injection,
and
it's
a
big
deal
for
us.
P
Looking
at
this
I
I
will
admit
that
I
have
not
read
the
drafts.
This
proposal
before
this
meeting
my
bad,
but
my
question
here
would
be,
if
I'm
going
to
send
a
backup
off
at
the
moment
over
the
SR
stuff.
Why
am
I
not
just
going
to
send
two
separate
paths
using
two
separate
communities
to
dictate
which
route
or
accepts
them
and
send
it
like
that?
P
Rather
than
complexified,
my
policy
saying
to
the
Ruta
create
another
part
when
I
can
simply
inject
the
two
paths:
do
all
the
calculations
on
the
back
end
and
then
set
the
communities
to
determine
which
route
or
accepts
to
me.
That
seems
like
a
lot
simpler
option
and
it
leaves
the
control,
in
my
controller,
to
calculate
all
of
those
paths.
That
would
be
my
comment
on
this
I.
E
A
R
Q
The
topic
at
hand
is
bgp
maximum
prefix
limits,
HB
maximum
prefix
limits
are
a
very
popular
mechanism
in
the
operator
world
to
dampen
the
negative
effects
of
mostly
full
table
route
leaks.
So
it's
a
very
crude
mechanism
or
it
helps
against
very
common
occurrence
that
we
see
in
internet
in
the
internet
routing
system.
Q
Q
Now
this
is
what
happens.
Pre
policy
well
can
occur
if
a
maximum
prefix
limit
is
applied.
Post
policy
is
that
between
an
e
BGP,
prefix
based
filter,
that
derive
from
say,
IR
data
or
or
in
case
RPI
based
HP
origin
validation
is
applied
that
so
many
parts
are
rejected
in
the
policy
that
the
amount
of
routes
that
make
it
through
the
policy
does
not
exceed
the
trash
hold,
in
which
case,
even
though
you
have
a
full
routing,
League
full
table
route
leak.
Q
Q
The
illustration
here
is
that
that
both
use
cases
exist
in
a
world
and
I
think
they're.
There
they're
valid
use
cases.
Now,
if
we
go
take
a
look
at
what
is
available
to
operators
these
days,
it
appears
there's
a
wealth
myriad
of
interpretations
of
the
particular
sections
of
the
core
BGP
spec
on
how
to
do
maximum
prefix
limits,
specifically
on
iOS
XR
+
XE.
The
concept
of
pre
policy
limits
does
not
exist
at
all
and
then
on
other
platforms,
for
instance,
OpenBSD
is
open.
Q
Q
So
this
the
concept
of
maximum
of
outbound
maximum
prefix
limits
serves
to
to
facilitate
situations
where
maybe
the
peer
did
not
configure
any
limits,
but
we
have
expectations
of
what
we
expect
to
announce
to
the
specific
adjacent
network
and
that
we
can
opt
to
shoot
ourselves
in
the
head.
Should
we
shoot
certain
high-water
marks
be
reached
now
only
birth
as
an
implementation
supports
this
today
and
I.
If
a
battle
of
open
Beach
PD
to
to
consider
for
testing
I
am
aware
that
there
are
a
number
of
complexities
related
to
this
feature.
Q
Q
Should
be
applied
if
maximum
prefix
limits
are
met,
reasoning
from
the
perspective
of
internet
routing,
we're
tearing
down
the
session
is
a
more
desirable
state
of
being
compared
to
keeping
the
session
up,
but
stopping
stop
accepting
new
advertisements.
However,
upon
rereading
the
core
BGP
specification,
it
became
clear
to
me
that
already
today,
in
the
course
back,
we
have
two
options
of
dealing
with
hitting
the
maximum
prefix
limits.
One
is
keep
the
session
of
block
new
extra
announcements.
Q
I
want
us
to
go
through
the
motions
of
tearing
out
the
session,
so
we
will
need
to
rework
the
draft
to
provide
compatibility
with
what
already
exists,
even
though,
as
an
internet
operator,
it
is
not
my
favorite
option.
I
do
not
wish
to
alter
that
part.
I
want
to
my
goal
is
to
to
revise
and
clarify
and
not
take
things
away.
Q
Sue
has
been
very
kind
in
providing
a
extensive
review
of
our
first
step
at
this
draft
and
she
also
provided
the
primary
notes
fish
and
who
moved
the
word
from
grow
to
idea,
as
she
was
able
to
articulate
with
some
patience
to
us
that
these
things
can
only
materialize.
If
we
do
this
as
a
update
to
for
2001
in
doing
so,
I've
come
to
realize
that
there
is
a
fair
bit
of
spaghetti
to
untangle,
because
the
concept
of
maximum
prefix
limits
is
mentioned
in
numerous
sections
and
well.
Q
Q
A
You
I
would
like
to
say:
let's
not
have
questions
at
the
mic
because
we're
at
two
minutes
over
our
three
minutes
over
so
now
we're
five
minutes
over
and
I,
don't
you
know
I've
seen
people
filtering
out
so
I
think
it's.
You
know,
sort
of.
Let's
respect
the
group's
time,
if
you
have
points
to
make
by
all
means,
please
make
them
on
the
list
or
you
know
where
to
find
job.
