►
From YouTube: IETF106-TEAS-20191119-1710
Description
TEAS meeting session at IETF106
2019/11/19 1710
https://datatracker.ietf.org/meeting/106/proceedings/
A
Welcome
back
there's
the
second
of
the
two
tea
sessions
that
we're
having
today
I'm
powered
by
ROM.
This
is
my
co-chair.
Lew
Berger,
our
secretary
is
remote
Matt
Hartley.
We
did
manage
to
finish
all
our
sessions
slot
sometime
in
the
first
four
in
the
first
session,
so
we
can
jump
straight
to
the
agenda
before
we
do
that.
Quick!
Look
at
the
note!
Well,
if
you
aren't
familiar
eyes
with
this,
yet
please
do
get
yourselves
familiarized,
there's
a
link
at
the
bottom.
That
should
give
you
sufficient
details.
A
We
are
streaming
both
audio
and
video.
So
for
the
benefit
of
folks
who
are
remote,
please
do
use
the
microphones
and
peace
to
state
your
name
before
speaking,
as
always
we're
using
etherpad
for
collective
minute
taking
please
to
join
us
there
and
help
us
take
accurate
minutes,
we're
also
on
jabber
and
for
those
of
you
who
are
remote.
If
you
have
anything
to
add
to
the
conversation,
please
jump
on
the
meter
Kirk
you
with
that.
Let's
jump
to
the
first
presented
first
presenter.
That
would
be.
B
B
The
purpose
is
to
meet
the
requirements
of
the
5g
unnatural
slicing,
and
it
can
also
be
used
in
other
generic
scenarios,
so
can
be
relatively
de
cabo
de
and
generic
in
this
draft.
It
defines
the
layered
architecture
and
also
give
analysis
as
tool
Kennedy
technologies
in
different
planes
and
the
layers,
including
the
enhanced
and
early
data
plane.
B
Several
mechanisms
are
described
which
can
be
used
to
provide
a
different
levels
of
the
SRA
guarantee
and
for
the
in
the
virtual
natural
layer
behind
consider
the
data
playing
encapsulations
and
the
controlling
mechanism
for
the
virtual
network
instantiation
and
for
the
management
plane.
Basically,
young
data
models
can
be
used.
Most
of
the
existing
Llamados
defining
the
ITF
can
be
reused,
with
some
possible
enhancement
to
for
the
creation,
modification
monitoring
and
deletion
of
this
commercial
networks.
This
document
also
have
some
descriptions
about
the
OEM,
resiliency
and
also
telemetry,
etc.
B
Okay,
this
is
picture
shows
the
overall
architecture
for
the
enhance
18
orbiting
PLAs.
This
has
been
shown
several
times
in
the
booking
group,
so
we
will
not
give
details.
We
can
see
that
it
gives
a
layered
architecture,
including
the
enhance
the
data
playing
and
the
virtual
network
layer.
Also,
the
controller
management
for
the
centralized
management
of
this
virtual
networks
and
the
physical
networks
here
are
the
updates
after
last
presentation
in
90f
104
first
is
there
are
some
definitions
polished
in
this
version?
B
First,
there
we
have
some
description
about
the
rope
of
the
transport
network
in
the
ferry
network
slicing
because
the
narrow
slicing
is
considered
as
the
major
motivation
and
the
current
use
case
for
this
enhanced
VPN.
The
end
to
end
in
a
neuro
slice
of
5g
consists
of
the
three
major
types
of
network
segments,
including
the
radio
network
and
their
transport
network
ended
the
core
network
in
the
end-to-end
network.
B
Slice
transport
network
provides
the
required
connectivity
with
the
and
within
and
between
the
ran
and
seeing
our
core
network
parts
of
a
transfer
of
of
an
end-to-end
slice
and
provider.
Specific
performance,
complete
commitment,
and
this
document
also
refines.
The
definition
of
the
transponder
slice,
which
is
a
transponder
slice,
is
a
virtual
or
logical
network,
with
a
particular
network
topology
and
a
set
of
shared
or
dedicating
resources,
and
it
can
be
used
to
provide
a
network
slice
consumer
with
the
required
connectivity
and
appropriate
isolations
and
the
specific
SRA.
B
Another
update
is
about
the
data
plane.
In
this
version
we
reduce
and
refine
the
tape
descriptions
about
the
segment
routing
because
same
routing
is
considered
as
such
as
the
one
candidate
technology
for
this
virtual
network.
Instantiation
and
more
details
about
this
technology
are
described
in
the
spring
draft.
So
in
this
framework
we
just
give
some
analysis
about
the
gaps
in
the
current
racing
routing
and
provided
direction
for
the
possible
enhancements.
We
think
the
currently
the
second
routing
is
mainly
used
to
SIDS
as
the
topological
instructions
and
the
ice
RTE
past.
B
B
Ok,
the
management
plane
in
this
draft
away
clarifies
the
relationship
of
the
existing
data
models
and
their
applicability
to
the
enhanced
Levine
management.
We
also
try
to
map
to
management
architecture
in
the
3gpp
narrow
slicing
to
the
actn
architecture.
It
is
defined
and
available
in
ITF.
Basically,
we
concede
an
interface
and
not
smile
interface
between
them
to
the
network.
Slice
measurement
function
and
another
slice
subnet
imagine
function
for
the
transfer.
B
Network
can
use
the
existing
the
models
defined
in
T
such
a
civilian
model
for
the
service
provisioning
and
for
the
service
delivery,
and
we
can
also
use
M
TLC
to
provision
the
Teton
Ozark
apologies
to
the
next
layer
control
agency
for
the
service
monitoring.
We
also
have
this
kind
of
Hmong
models
for
the
entire
matter:
er
developed
a
little
mushy.
B
Basically,
there
are
two
options
list
here
wise.
We
can
use
VM
to
directly
describe
the
service
requirement.
Another
case
we
can
use
the
leaders
three
or
less
mm
models
to
use
as
the
service
delivery
model
to
the
customer,
and
we
can
use
a
service
mapping
to
map
the
server
layer,
three
layer
to
SM
models
to
the
VM
model
and
further
to
the
tunnel
models
or
topology
models.
B
Some
other
updates,
including
and
descriptions
about
the
telemetry
and
how
we
can
consider
how
to
introduce
telemetry
to
habitat
the
information
collection
for
specific,
are
waiting
past
cannons
and
we
also
improved
the
scalability
consideration
straight
section
and
the
security
consideration
sections.
There
are
also
some
other
editorial
changes
in
this
version.
B
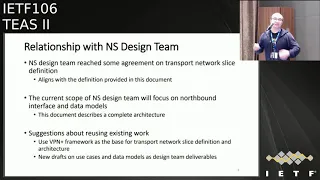
Okay,
this
page
is
a.
We
want
to
talk
about
the
relationship
with
a
narrow
slice,
design
team,
because
we
think
we
have
a
son.
We
have
the
same,
go
to
define
and
transfer
now
slice
and
the
architectural
idea-
and
we
kind
of
we
work
together
as
a
member
of
the
design
team
to
provide
the
definitions
and
architecture,
and
we
want
to.
We
also
finalized
to
define
the
scope
of
the
design
team
and
based
on
recent
discussion.
B
B
B
B
Okay,
so
in
the
next
steps
will
continue
to
solve
the
comments
received
on
this
document.
I
work,
together
with
the
design
team
to
polish
the
definition
architecture
means
it's
documents
and
we
will
try
to
make
a
document
already
for
last
call
in
the
following
weeks
or
months.
Okay,
that's
all
for
this
presentation.
D
Thank
you
just
a
question.
This
is
Dave
sénéchaux
from
Erickson.
So
as
I
read
the
introduction
to
the
to
the
draft,
it
talks
about
enhanced
VPN
and
trying
to
work
deterministic
transport
methods
into
the
existing
VPN
mechanisms
that
we've
got
yeah.
If
I
look
at
the
presentation,
you
just
made
your
kind
of
pitching
the
draft
as
an
architecture
for
network
slicing
and
how
transport
interacts
with
network
slicing,
which
is
it
is
it?
Is
it
a
method
of
providing
deterministic
transport
2
VPNs?
Or
is
this
the
new
architecture
for
network
slicing
yep.
B
C
Yeah
I
think
the
presentation
went
a
little
afield
from
the
document.
You
know
we.
We
have
a
working
group
document
that
that's
focused
on
one
thing
and
it's
focused
on
a
particular
solution
and
it
sort
of
drifted
from
that
document
into
the
whole
slicing,
discussion
and
I
think
that's
confused
things.
Okay,
I
would.
B
E
C
F
C
D
D
C
F
B
B
C
C
C
D
Yeah
I
feel
like
I'm,
getting
my
exercise
jumping
back
forth
to
the
mic,
but
this
is
Dave
Schoeneck
rope
Ken.
What
one
of
my
comments
on
the
draft
and
so
far
this
I've
gone
through
the
draft
it
is,
is
it
is
a
little
bit
focused
on
network
to
focused
in
my
network
slicing.
This
would
be
a
good
mechanism,
possibly
for
generic
support
of
deterministic
transport
for
VPNs,
but
it
it
basically
colors.
Everything
is
the
application
being
network.
Slicing
I
think
it's
good
to
emphasize
that
it
is
one.
B
Okay,
so
this
one
is
a
new
draft
which
is
about
controlling
considerations
for
the
enhanced
VPN
beeping
class
first
is
adjuster
described
there.
He
has
with
him
prowl.
He
has
between
framework
in
this
previous
draft,
which
is
a
layered
architecture
which
Canada
technologies
in
the
data,
plane,
control,
plane,
the
management
plane
and
the
use
cases
just
mentioned
that
were
slicing
and
other
generic
scenarios
for
this
document.
B
To
give
some
analysis
about
the
requirements,
functions
and
some
considerations
about
it,
a
control
plane
for
the
between
class,
so
that
it
can
be
used
to
guide
a
design,
the
control,
plane
mechanisms
and
the
extensions
in
the
other
working
groups,
so
some
requirements
on
the
control
plane
first
day.
So
we
need
to
consider
those
supported
isolation,
the
first
days
of
the
data
uplink
isolation.
B
Although
the
data
plane
isolation
is
directly
provided
wasted,
Mac
means
mechanism
means
annual
a
data
plane.
The
control
plane
needs
to
have
to
collect
and
distribute
the
necessary
information
needed
for
the
post,
soft
and
hard
isolation
to
the
to
the
control
plane
to
the
altitude
controllers,
and
the
second
part
of
the
isolation
is
about
the
isolation
of
the
control
plane
itself.
In
this
a
control
plane,
we
already
have
different
mechanisms
which
can
provide
you
different
levels
of
isolationist,
but
with
different
overheads.
For
example,
we
can
use
them.
B
How
do
topology
based
technology
to
give
you
I
saluted
topology
or
the
ribs?
The
multi
instance
can
give
you
further
isolation
with
more
overhead.
A
logical
system
is
another
case
which
give
you
even
further
isolation
in
the
control
plane,
so
for
the
second
requirements
is
to
support
attributes
of
the
we
use
the
transfer
natural
slice,
because
this
is
a
major
case
for
the
trust
fund
address
lies.
We
think
there
are
two
major
types
of
attributes
which
should
be
this
in
the
control
plane.
B
The
first
is
the
topology
attributes
of
this
slice
and
the
resource
information
associated
away
the
slice.
The
third
point
is:
we
need
to
consider
how
to
support
it.
Different
numbers
of
nano
slices
required
in
the
different
phases
and
in
the
scenarios
we
will
face
in
the
future
for
the
deployment
of
them,
not
random,
transport,
narrow
slice.
This
is
a
mainly
relevant
to
the
scalability
considerations.
We
will
discuss
more
detail
in
the
following
slides
and
for
the
control
plane
for
the
controlling
functions.
B
We
think
it
should
be
a
hybrid
of
the
distributed
control
and
the
centralized
the
control
plane
so
for
the
distributed
control
plane.
There
are
two
layers:
typically
the
overlay
and
annually,
but
overlay.
It's
just
the
need
to
work
on
the
distribution
of
the
routing
information
of
the
may
be
impressed
tenants.
This
is
the
traditional
functionality
we
need
to
have
in
the
overlay.
Well,
for
the
annually.
B
The
purpose
the
functionality
is
to
advertise
that
customize,
the
topology
and
the
associated
resources
of
each
natural
slice,
and
we
too
also
need
to
do
the
customize,
the
computation
to
generate
the
routing
and
the
forwarding
entries
for
each
independent
slice
and
for
the
centralized
the
control
plane
within
KT.
The
functionality
is
to
collapse
the
topology
and
resource
as
attributes
of
each
natural
slice
and
to
provide
a
global
computation
and
optimization
of
the
T
passed
within
a
narrow
slice.
B
Here
are
some
considerations
about
the
scalability,
because
we
think
in
the
deployment
we
will
have
different
scenarios,
which
required
for
a
number
of
natural
slices
or
evicting
pass.
So
it's
kind
of
number
can
range
from
tens
to
handers
or
2,000
or
even
more
so.
We
need
to
consider
this
controlling
scalability
from
the
beginning
in
the
design
to
make
it
a
solution
scalable.
So
for
the
scalability
of
the
distributed
control
plane,
we
need
to
consider
several
aspects,
such
as
the
number
of
the
protocol
instances.
B
We
need
to
maintain
on
the
nodes
in
a
number
of
control
sessions
for
each
node.
Another
thing
is
that
the
number
of
browse
to
be
advertised
in
the
network.
This
is
also
need
to
be
considered
because
we
may
have
multiple
virtual
networks
how
we
can
control
this
kind
of
a
number
of
routes
and
the
attributes
for
each
route.
We
also
need
to
consider
the
scalability
in
this
case,
and
another
thing
is
the
for
the
computation.
B
Usually,
we
need
to
do
the
routing
computation
like
SPF
on
the
devices,
so
this
number
of
the
SPF
computations
is
also
another
case.
We
need
to
consider
for
the
controlling
scalability.
So
in
in
order
to
meet
at
a
different
levels
of
scalability
requirement,
we
need
to
consider
some
optimizations
for
the
design
in
the
control
plane.
So
here
are
some
suggestions
on
this
controlling
optimizations.
The
first
is:
we
need
to
reduce
the
number
of
control
sessions
so
that
we
can
first
can
show
this
Vlade
and
to
reduce
the
operation
overhead
for
the
control
plane.
B
This
is
can
be
done
with
a
shared
control
plane
to
distribute
the
information
of
multiple
Network
slices.
In
this
case,
we
will
need
to
have
some
identifiers
in
the
control
plane
to
distinguish
the
informations
of
different
advice.
The
second
point
is:
we
can
also
decouple
the
attributes
of
different
type
of
attributes.
We
need
to
advertise
and
process
in
the
control
plane.
B
Another
suggestion
here
is
because
we
have
a
hybrid
control
based
on
the
centralized
controller
and
the
distributed
control
plane.
We
can
divide
as
a
load
between
the
centralized
that
distributed
control
planes
so
that
I
don't
need
to
rely
on
one
of
them
to
do
all
this
works
and
we
can
reduce
a
load
on
each
of
them.
B
C
C
B
B
Think
actually,
post
draft.
They
are
consistent
on
the
control
plane,
but
this
wise
provide
more
details
about
it.
Considerations
we,
which
we
need
to
put
into
consideration
on
the
design
for
the
control
plane
that
one
just
that
describes
the
functionality
is
a
briefly
in
that
one
because
of
the
control,
please
just
one
section
in
the
framework,
but
here
we
want
to
just
put
more
details
so
that
it
can
be
useful
for
the
protocol
design,
okay,
yeah.
I
This
document
that
makes
me
feel
like
there
is
some
confusion,
also
on
the
scope
of
the
document
that
you
have
previously
presented.
So
I
would
like
it
to
rain
for
to
the
statement
that
this
should
be
focusing
on
VPN
Plaza
and
not
just
deterministic
traffic.
In
my
opinion,
it
should
be
covered,
but
also
the
possibility
to
deliver
VPN
traffic
with
given
SLA
is
a
given
kpi's,
not
just
taking
a
deterministic
environment,
but
in
more
generically.
In
a
in
a
now
I
from
layer,
0,
2,
layer,
3,
environment,
Thanks,.
E
So,
besides
what
Allah
sent
when
you
hold
for
centralized
control
a
function,
it
really
looks
like
management
plane.
A
lot
to
me
and
I
read
all
the
and
accompanying
documents.
You
should
really
be
looking
into
an
avoiding
further
pollution.
You
know
bgp
less
some
others
into
management
plan
function
because
a
lot
of
this,
if
really
management,
nothing
to
do
with
control
plane.
Neither
was
distribution
across
network,
it's
kind
of
peer-to-peer
situation
between
northern
question
and
some
business
logic
whatever.
So
maybe
you
just
extend
the
name
to
management
and
control.
B
E
J
J
Of
the
VPN
plus
framework
RFC
was
that
it
is
not
intended
for
the
large
scale,
of
instance,
in
a
network
or
VPN
plus
instance,
although
when
you
explain
here,
you
are
saying
that
the
scale
would
be
much
higher
than
hundreds
of,
although
the
draft
RFC
opposite.
So
how
do
I
interpret
like
these
two
things?
J
J
B
J
B
Because
things
Act
one,
we
actually
talk
about
the
comparison
between
house
wave
here
and
it's
a
tradition,
awake
in
instances.
The
number
of
the
has
BPM
is
considered
small,
much
smaller
than
that
one
and
case,
but
the
still
in
even
following
has
between
itself.
It
has
different
phases
and
scenarios
in
the
deployment
where
considering
we
need
to
meet
this
kind
of
scalability
for
different
phases
in
the
in
the
design,
with
the
protocols
for
what
he
has
with
yourself.
B
F
Okay,
then
Adrian
Farrell
I
agree
with
Jeff
that
the
line
between
control
and
management
has
become
very
muddy
and
we
need
to
sort
it
out
and
I
agree
with
Lou
that
any
other
work
on
control
plane
needs
to
be
consistent
with
the
framework.
There
is
a
section
both
on
management
and
control
plane
in
the
framework
and
it's
about
half
a
page
each,
and
this
is
what
a
10-page
first
draft
and
I'm
wondering
whether
we
should
be
pulling
more
material
into
the
framework
to
describe
control
plane
or
having
it
in
a
separate
place.
A
One
of
the
earlier
versions
of
the
announcer,
a
pn+
document
pre,
could
be
pre-adoption.
It
had
a
control,
plane
conservation,
section,
I,
I
thought
it
got
called
for
a
good
reason,
because
this
is
it
seems,
like
you,
took
most
of
that
text
and
put
this
in
this
new
document.
I
I
wouldn't
be
comfortable,
bringing
it
back
into
the
base
rock.
A
C
C
A
different
reason:
the
I
would
like
to
understand
what
the
control
plane
is
for
VPN
plus
without
seeing
the
word
slice,
because
I
want
to
understand.
Vpn
plus
I,
don't
want
to
understand.
Slicing
I,
don't
want
a
slicing
design
team
I
don't
want
to
do
I,
don't
want.
You
know,
there's
already
other
folks
doing
slicing
if
he
can
floss
to
something
we're
slicing
it
just
one
use
case,
define
it
without.
C
C
You've
seen
me
before
say,
I'm
more
worried
about
the
text
and
what
document
it's
in
I'm
a
fan
of
less
documents
where
appropriate
and
sometimes
but
sometimes
you
need
to
split
things
up.
So
if
we
were
talking
about
text
that
made
sense
to
me,
I
might
have
a
different
opinion
right
now.
I
completely
agree
with
Pavan
I
can
see
combining
this
in
the
other
document,
because
it
doesn't
make
any
sense
to
me.
You
know:
where
do
we
do
VPNs
using
multi
topology
routing
in
the
ITF,
where
that's
what
this
document
says
to
do.
A
Just
one
comment
for
this
discussion:
actually,
my
name
is
Uma
from
feature
ii.
I
think
this
a
lot
of
clarity
will
come.
If
you
separate
overlay
and
underlay,
there
is
a
control
plane
for
underlay.
Maybe
that's
what
you're
talking
about.
If
you
separate
that,
let's
make
it
much
more
easier
to
discuss,
it
was
for
establishing
the
VPN
plus,
you
may
need
a
control
plane
for
underlay
paths.
At
te,
topologies
are
whatever
it
is.
B
I
think
you
are
right
that
they
are
overly
and
and
early
for
the
VPN
service
and
actually
for
the
enhance
between
what
we
are
considering
the
integration
of
the
overlay
and
and
early
because
privilege.
Previously
people
think
they
are
separate.
You
can
have
separated
management
and
provisioning
for
each
layer,
but
now
we
are
thinking
for
some
services.
You
need
to
consider
their
mapping
and
the
integration
to
give
that
the
performance
and
the
characteristics
you
required
by
some
services.
So
this
is
a.
We
can
clarify
that,
partly
in
the
document
yeah.
C
C
C
He
had
an
earlier
comment
also,
as
the
confusion
in
this
document
makes
me
feel,
there's
the
same:
confusion,
VPN
+
framework
in
terms
of
scope.
Please
make
sure
this
is
not
another
attempt
to
define
network
slicing,
but
focus
on,
began
+
and,
if
possible,
not
just
the
terminus
VPNs
but
VPNs
that
can
deliver
traffic
with
other
KPIs
and
SLS.
You.
C
K
Okay,
my
name
is
Eric
I'm
here
to
talk
about
network
slicing
design,
team
stages.
Very
basically,
it's
just
starting
up,
so
don't
expect
a
fully
blown
architecture
and
everything,
but
we
have
scoped
out
our
task
a
little
bit
so
I'm
going
to
talk
about
that
the
design
team
set
up.
Basically,
we
were
tasked
by
the
chairs
to
develop
a
framework
for
providing
a
network
slicing
using
IETF
technologies
such
as
MPLS
to
use
to
create
specific,
isolated
and
managed
Network
instances.
And,
as
you
know,
this
is
a
broad
and
diffuse
topic.
K
Slicing
and
many
marketing
words
are
used.
So
our
key
challenge
is
actually
trying
to
focus
on
the
IETF
and
PS
relevant
part
of
this
broader
topic
and,
and
even
the
term
slicing
is
a
little
bit
dangerous
because
it,
you
know,
tends
to
be
used
very
easily
and
you
know
associated
with
you
know,
compatibility
with
5g
and
you
know,
or
many
great
things,
but
at
the
same
time,
some
of
the
terms
aren't
sort
of
fully
defined
and
and
used
in
multiple
different
ways.
K
K
We
have
sixteen
members
initially,
although
other
people
have
also
joined
our
calls.
For
instance,
we
have
open
calls,
you
can
join
them.
We
have
mailing
list
archives
that
are
open
and
any
results
that
we
might
get
will
be
brought
immediately
to
the
working
group
for
your
consideration
and
debate
the
design,
teen
timeline
and
status.
This
was
basically
specified
by
the
chairs
in
the
original
announcement.
That's
this
idea.
We
were
supposed
to
look
at.
You
know
what
our
plans
are,
what
what
scope
we
believe
our
work
should
have.
We've
also
provided
some
individual
contributions
at
this.
K
So
what
is
the
scope
of
the
design
team
and
what
is
our
plan?
So
this
is
basically
about.
You
know
the
item
for
context
that
the
idea
we've
had
a
few
meetings
where
we
discussed
network
slicing
and
it
was
more
or
less
all
over
the
place.
You
know
everything
under
the
Sun
and
was
very
difficult
to
to
focus
so
we're
trying
to
take
back
from
that
or
take
a
lesson
from
that
and
go
back
to
basics
and
just
explain
how
to
use
existing
IT,
EFT
transport
technologies
and
te
technologies.
K
What
we'll
need
is
definitions.
What
are
these
things
that
we
are
trying
to
create
will
lead
a
framework
that
describes
the
overall
set
up
the
system.
You
know
what
interfaces
there
are
and
components,
and
so
on
we'll
need
some
set
of
requirements
that
we
understand.
What
are
we
trying
to
do
and
then
we
actually
want
to
use
existing
ITF
technology
for
the
necessary
components
and
interfaces
that
we
identified
in
the
previous
step.
K
You
know
say,
say
things
that
you
know
we
can
use
this
in
this
manner,
rather
than
build
an
entire
new
thing
and
we're
not
quite
there.
Yet
we
haven't
done
this
analysis,
so
the
results
results
to
be
seen,
but
that's
the
goal
and
sort
of
the
at
this
point.
The
overall
view
is
that
we'll
need
some
kind
of
northbound
interface,
where
some
other
entity
can
requests
these
connections
or
slices
and
they'll
specify
some
set
of
characteristics
that
they
want.
K
This
bandwidth
and
latency
and
whatnot
we'll
need
a
way
to
map
that,
to
particular
IDF
technology,
so
that
requests
that
the
hilar
abstract
level
needs
to
be
mapped
to.
You
know
this
is
how
we
do
it
in
MPLS,
and
then
we
have
obviously
the
underlying
ITF
technology
that
we
can.
We
can
use
as
a
component
here.
You
also
would
like
to
provide
some
use
cases
that
we
can
sort
of
use
as
examples
and
also
verify
that
we
have
sort
of
some
sense,
complete
support
for
some
particular
case,
and
our
plan
is
basically
test.
K
We
did
draw
a
sort
of
a
very
simple
picture
yesterday
about
what's
the
what's
the
model
that
we
have
in
our
minds,
and
there
is
this
northbound
interface
that
perhaps
exists
already
in
the
working
group
existing
documents-
or
maybe
it
needs
it,
so
extend
it
somewhat,
but
but
there's
an
interface
for
requesting
network
slices
or
connections
and
then
there's
some
kind
of
controller
functionality
and
implementation.
A
piece
of
software
that
maps
those
requests
into
existing
technology
in
the
underlying
network
and
sets
up,
for
instance,
a
virtual
network
of
some
sort
in
this
particular
picture.
K
What
we
have
is
three
different
connections
or
slices
that
are
entirely
separate
from
each
other
and
also
using
different
technologies.
In
this
this
case,
there's
obviously
other
cases.
This
just
one
example
in
the
picture,
then,
at
the
top
of
the
picture,
you'll
see
something
else
which
is
a
customer
of
some
sort
or
you
know
higher
level
system.
That
makes
these
requests
and
that's
quite
potent.
So
it's
something
that's
outside
the
scope
of
us
at
the
IETF
or
at
least
outside
this
working
group.
K
You
know
one
example
of
this:
high
level
system
might
be
5g
and,
and
they
would
not
be
able
to
use.
You
know
our
results
for
everything
that
they
need
for
slicing,
but
they
might
use
it
for
a
particular
piece
of
that
they're
functional,
so
they
might
also
end
up
using
other
other
parts
than
the
IETF
technologies,
and
that
was
sort
of
the
positive
way
to
define
that
this
is
what
we
want
to
do,
but
there's
also
a
negative
definition
of
you
know.
This
is
what
we
don't
want
to
do.
K
This
is
not
an
overall
definition
of
all
possible
ideas
under
virtualization.
This
is
well
it's
not
our
role
at
the
ITU
have
to
define
5g
slicing.
They
might
use
our
results
someday,
but
it's
not
our
our
role
to
define
that
particular
system
or
any
other
system
beyond
our
our
own
they're,
not
taking.
Therefore,
the
role
of
any
other
stos,
but
rather
work
together
and
provide
components
for
others.
It's
also
not
about
picking
a
particular
single
implementation
technology.
Like
you
know,
we
will
only
use
you
know
this
technology
to
implement
these
slices.
K
We
have
debated
definitions
for
what
are
we
doing
quite
a
bit,
we're
not
quite
there
yet
so.
There's
some
many
open
areas
here,
but
but
I
think
this
is
useful
for
you
guys
to
understand
where
we
roughly
are
thinking.
So
we
could
call
this
thing
that
we're
trying
to
create
in
this
this
architecture,
a
transport
slice
or
simpler
connection.
K
It
is
an
abstract
need
for
topology
connecting
a
number
of
endpoints
with
an
expected
network
service
specified
as
service
level
objectives,
and,
if
you
note
here-
and
this
is-
you
know,
may
be
similar
to
some
other
things
that
we've
done
in
the
past-
that
that
might
actually
be
great,
you
might
be
able
to
use
those
results
directly.
We're
trying
to
be
generic
in
the
sense
of
this
is
not
just
point-to-point
connections,
but
this
is,
it
also
be
point
to
multi-point
and
so
on
could
be
hierarchical.
Multiple
levels
specified
in
some
fashion.
K
K
We
wanted
to
specify
this
as
a
sliced
connecting
to
only
endpoints
with
you
know,
which
can
be
then,
basically,
whatever
else
there
might
be,
and
if
you
need
to
stitch
different
connections
or
slices
together,
you
can
do
this
through
an
endpoint
and
we
only
cover
transport.
So
this
is
this
is
about
bit
pipes.
So
if
you
need
firewall
functionality,
you
need
a
5g
node
for
some
purpose
and
so
on.
These
are
not
part
of
our
model,
but
a
transport
could
connect.
Potentially
these
entities
together,
and
indeed
this
is
still
work
going
on.
K
I-
also
want
to
briefly
show
a
couple
of
other
pictures.
You
may
have
seen
some
of
these
before
and
other
other
context,
possibly
even
during
this
session
or
me,
and
it
is
just
to
show
that,
like
you
know
this,
the
abstract
thing
that
we're
trying
to
talk
about
how
that
might
map
map
to
some
real
real
world
pictures,
or
at
least
some
people's
perspectives
of
the
real
world
situation.
So
so
this
particular
picture
shows
like
this
5g
example.
K
Where
you
might
have
transport
networks,
slice
part
of
things,
which
is
what
we
would
be
focusing
on,
but
there
might
also
be
other
things
they
like
be
like
a
core
network
slice
functionality
that
you
know
we
here
at
the
IDF
know
nothing
about.
There
might
be
some
radio
network
slicing
aspects
that
again
we
don't
know
anything
about,
we
would
provide.
You
know
the
plumb
being
between
some
of
these.
These
components.
K
Sort
of
another
way
of
looking
at
this
is
that
in
5g
you
have
this
concept
of
end-to-end
network
slice
and,
and
this
picture
tries
to
show
how
you
know.
What's
our
role
in
in
this
and
the
end-to-end
network,
slice
is
a
concept
that
that
is
different
to
what
we're
trying
to
do,
and
it's
defined
by
somebody
else,
and
it
includes
many
other
things,
but
our
transport
slices
might
might
be
part
of
part
of
this
bigger
hole.
K
In
the
presentation
response
pointers
for
further
further
reading
the
announcement,
at
least
the
art
archive,
we
have
notes
from
all
of
our
calls,
except
the
ones
we
held
this
this
week.
Those
notes
are
not
there
yet
and
some
pointers
to
to
documents
that
one
could
look
at
these
are
in
some
cases.
You
know
working
group
accepted
documents
for
some
other
topic.
In
other
cases
there
are
individual
documents
or
with
some
possible
collaboration
with
several
people.
K
You
know
not
only
this
is
a
grid
as
a
component
in
general.
Our
approach
is
that
it,
you
know
we
were
had
previously
discussion
that,
but
you
know,
is
the:
are
these
documents
for
slicing
or
for
some
other
purpose,
and
my
personal
perspective
at
least,
is
that
you
know
define
the
you
know
great
service,
whatever
you're
working
on
and
make
it
clear
what
it
is,
and
then
that
could
be
something
that
we
could
use
us
as
part
of
this,
that
hey,
if
you
need
this,
then
go.
K
Do
that
and
we
don't
do
any
extra
work
here
in
our
team,
so
I
think
that's
about
it
and
I,
don't
if
the
serious
won't
ask
something
or
other
team
members
or
and
I
guess.
The
purpose
of
this
presentation
is
to
for
asked
us
to
listen
to
to
you.
If
you
have
any
thoughts
on
you
know,
this
doesn't
make
any
sense.
Please
direction
or
makes
change
and,
or
you
know,
add
this
or
take
away
that
or
you
know
point
us
to
other
things
that
people
have
done
in
the
past.
L
Hi
Himanshu
from
Siena
I
have
a
clarification
question.
So
are
you
covering
the
soft
slices
or
hard
slices
or
independent
of
that
and
hard
slicing,
meaning
with
ethernet
channels
or
lambdas,
and
all
that
stuff
so
or
I
mean
whether
it's
independent
of
all
that
and
if
it's
not,
then
you
are
determining
whether
this
particular
requirement
or
SLO
requires
hard
slice.
This
one
requires
affinity,
diversity
and
stuff
like
that.
So.
E
M
Well,
being
from
Hawaii,
in
fact
that
they
take
the
role
of
this
of
the
liaison
working
idea
so
because
we
know
that
so
this
had
a
matter
relation
with
the
3gpp.
To
be
honest,
so
they
also
talked
about
the
net
over
slicing,
so
I
think
there
are
some
of
these.
So
the
consideration
on
this
is
the
liaison
or
some
maybe
some
of
the
represent
even
this
team,
or
was
your
plan
on
this
one?
So.
E
Actually,
I
am
the
digital
engine
from
AP,
and
this
technology
is
to
work
on
slices.
It's
not
to
let
this
do
GPP,
it
could
be
never
slice.
5G
networks
lives,
enterprise,
network
slice,
it's
a
network,
slice
that
provides
infrastructure
to
build
it.
We
don't
need
to
engage
with
any
other
is
do
in
particular.
In
order
to
do
this
work
there
are
many
is
DF,
some
others.
So
it's
not
specific
to
do
so.
K
E
K
That
that
X,
exactly
right
and
and
to
sort
of
emphasize
that
even
a
little
bit
more
like
we're
trying
to
provide
a
useful
function
once
we
had
to
find
a
useful
function,
then
it
may
be
more
relevant
to
talk
to
others,
we're
not
redefining
what
5g
or
3gpp
guys
are
doing
with
with
slicing.
They
might
use
our
results,
but
before
we
have
any
results,
then
there
isn't
much
the
point.
Of
course
they
some
of
those
people
and-
and
they
also
interact
here
at
the
ITF-
might
come
with
some
requirements.
N
Eeling
Holly,
when
you're
defining
the
transpose
lies
my
suggestions.
If
we
can
do
that,
this
question
about
the
relationship
and
these
differences
between
transport
slice
and
those
about
VPN,
enhanced,
VPN
and
virtual
network
and
nagas
obsession,
etc.
That
would
be
much
clearer
for
the
for
the
English,
a
yeah
technology.
E
O
My
name
is
Reza
from
Nokia
I'm
part
of
the
design
team.
Maybe
I
just
give
a
clarification
about
a
few
question
that
I
heard
there
our
concept
of
the
transverse
slice
concept
and
implementation.
All
this
discussion
that
we
have
here,
for
example,
vpm
plus
harder
slice
office
like
all
these
are
implementation
of
a
transversal
s.
For
example,
you
want
to
connect
two
nodes
together
at
the
end
of
the
day
it
doesn't
from
the
customer
perspective.
It
doesn't
really
matter
how
it
is
implemented
in
networks.
O
As
long
as
the
SLA
or
SLO
are
satisfied,
you
want
to
connect
from
the
customer.
They
just
ask
connectivity,
they
do
they
don't
ask
you
to
connect
something
and,
by
the
way,
use
VPN
or
use
the
segment,
routing,
RSVP
or
harder
harder
slice
of
service
like
they
just
give
you
a
requirement.
I
need
this
transport.
This
connectivity
to
be
fully
secure
when
I
receive
it
as
an
operator
I
translate
that
to
be
harder
slice,
meaning
I
have
to
have
a
specific
node
for
that
implementation,
maybe
from
other
operator
that
means
something
else.
O
Different
example
different
technology,
and
we
give
some
Riku
some
recommendation
that
if
you
want
to
implement
it
this
way,
so
this
is
a
basically
the
best
practice
that
you
can
do,
but
this
is
basically
the
whole
idea
of
the
implementation,
which
is
very
important,
but
at
the
same
time
they
are
completely
independent
from
the
definition
that
we
have,
but
we
have
to
make
them
separate.
Otherwise,
if
we
mix
them
together,
we
come
up
with.
You
know
something:
that's
not
really
manageable.
Thanks.
C
N
So
here
the
presentation
is
about
transport
network
slicing.
This
is
part
of
the
network,
sizing
design
team
I've
heard,
but
this
draft
is
the
individual
draft,
not
a
design
team
draft
so
not
great
with
the
by
everyone
in
the
design
team.
Yet
so
even
the
terminology
here,
I
put
here,
the
transport
network
slice
will
be
aligned
to
what
I
was.
The
consensus
we
reached
could
be
transpose
last
little.
N
Idea,
and
also
the
tactic
here
is
to
reuse
as
much
as
possible.
The
existing
IETF
work
and
this
especially
T's
work
so
currently
were
derived
Network
Authority
models
a
whole
bunch
of
them.
We
have
paste
apology,
model
RC,
it
is
345
and
based
on
that,
we
derived
a
whole
bunch
of
different
models:
OD
n
2
or
3
T
to
party.
So
how
do
we
deal
with
the
slicing
and
we
add
another
or
completion
at
the
same
level?
N
So
the
way
we
do
that
we
argument
at
the
pace:
RFC,
satis,
354
or
4045
based
party
model,
so
that
we
have
independent,
separate
type
between
night
and
also
using
the
multiple
inheritance
table
based
version
model
feature
can
make
the
slice
model
either
without
te
AO
with
te.
So
here,
if
we
have
the
sliced
type
and
also
T
type,
then
we
got
a
chance
per
slice
with
T
and
then
you
can
even
have
more
types
here.
So
we
have
a
theory.
N
We
have
packet
extensions,
then
we've
got
layer,
three,
the
project
with
slicing
and
also
we
may
have
even
have
a
service
function,
a
word
to
party
under,
and
we
also
have
a
city
and
a
set
of
models
here,
and
many
of
those
models
are
topology
based
models,
so
they
are
based
on
the
based
poetry
model
RCS.
That
is
345.
So
once
we
argument
the
base
model
here
effectively,
we
augment
the
city
model,
making
it
slicing
capable.
N
N
The
blue
piece
and
the
table
will
form
a
slice
of
the
network
which
here
would
be
customized
partly
provided
to
the
pool,
and
similarly
we
got
another
piece
for
red.
They
are
all
physically
isolated,
then,
in
another
place,
if
the
requests
are
coming
from,
the
customer
is
darker
soft
isolation.
It's
a
virtual
resources.
Isolation
in
that
case
that
the
provider
here
they
have
like
four
node
resources,
topology
here
so
I
went
at
to
us.
N
We
are
for
an
r5
the
way
the
provider
to
achieve
this
is
to
build
some
Kitano
in
their
native
topology,
and
on
top
of
that,
we'll
have
a
overlay
which
is
a
and
in
the
middle
of
the
picture.
Then
we
have
a
virtual
network
there
and
take
one
piece
for
blue
another
piece
for
right,
so
we
called
to
size.
Is
there
the
way,
the
link,
the
relationship
here
like
so
with,
based
on
the
that
the
green
arrow
here?
N
Okay,
here's
a
model-
and
this
is
argumentation-
we
see
how
much
we
I
didn't
and
we
have
the
example
JSON
encoding,
so
the
base
native
to
party,
nothing
widow,
slice
the
next
four
times
empty
and
the
now
we
have
the
network
type
required
and
the
slacks
and
the
resi
at
the
node
level.
We
need
the
higher
the
physical
separation
and
the
the
topology
leveling
in
the
physical
separation.
Also,
the
link
level
is
also
physical
network
isolation
and
the
node
is
memory
isolation.
N
Once
we
have
that
another
possible
for
that
te
case,
the
differences
here
we
have
how
the
virtual
resources,
isolation
of
the
the
the
different
kind
of
who
we
have
ope
already
in
the
model.
So
this
will
achieve
the
soft
isolation
and
provides
to
the
client,
so
the
inner
drive
that
we
have
a
full
JSON
encoding
for
the
two
examples.
O
O
O
C
P
P
P
There
are
tool
granularity
of
traffic
adjustment,
look
until
the
pants
levels.
Negril,
the
asking
controller
will
optimize
the
traffic
information
he
ought
to
bypass
the
congest.
A
congested
link
implies
flow
level,
the
pants
information.
It's
cut,
the
interest
note
only
optimizes,
the
man
team
return,
pants
and
flows
in
Cirrus.
The
granularity
is
finer
and
the
network-related.
The
utilization
is
better
and
the
less
impact
on
the
existing
current
network.
P
P
What
caused
this
problem
there
is
two
technical
services.
Well
is
interactive
business
such
as
mobile
in
China
from
a
Nevada,
which
is
the
online
shopping
application.
The
peak
to
average
ratio
is
about
86
with
the
continuous
interaction
of
new
interactive
services.
The
peak
to
average
ratio
of
the
network
traffic
will
become
more
and
more
serious.
P
The
iconic
architecture
is
a
proposed.
This
architecture
can
be
divided
to
expect
you
to
understand.
On
the
one
hand,
it's
the
centralized
mode
and
the
distribute
more
elaborate,
as
in
controller,
is
responsible,
optimizing
pass
information
to
bypass
the
congest,
the
link,
ingress,
node
and
rigorous
node
I
response
for
optimize
the
mapping,
return
path
and
flows.
On
the
other
hand,
the
pants
quality
monitoring
and
flow
recognition,
standest
a
context,
mapping,
return
flow
and
manse
are
all
wrong
in
disciplining
other
to
two
ways:
microburst.
P
Health
quality
assessment
assessment
is
a
key
technology
to
I.
Can
the
method
the
method
uses
them
in
periodic
environment,
for
example,
ingress
ingress
router
will
insert
the
monument
message
to
the
traffic
and
the
ingress
ingress
router
will
fit
a
bank.
The
moment
result
result
result
to
the
ingress
router
in
the
same
interview.
P
P
The
method
also
consider
the
flow
passing
switching.
We
give
the
comparison
beetle
before
switching
and
after
switching
okay,
this
mess
of
the
concealers
are
the
Panthalassa
assurance
influences
vici.
Okay,
the
pull
the
paper
only
for
did
plan
using
icon.
We
prove
it
as
a
network
throughput
by
around
30%
I
per.
We
believe
that
icon
is
a
kind
of
traffic
engineering
architecture.
C
C
E
Absolutely
I
would,
I
would
provide
you
this
time
to
present,
but
in
general
it
feels
like
a
didgeridoo
going
back
to
their
zoo,
going
back
to
fashion
and
bacon
and
similar
technologies.
I
think
very
significantly.
You're
mixing
throughput
with
good
food
and
they're,
not
the
same
thing
and
congestion.
We
can
introduce
tcp
something
built-in,
like
quick
influences,
your
good
put
much
more
than
quality
of
the
past.
Otherwise
it
just
blurted
shall
exercise,
and
I
think
I've
seen
this
at
least
15
times
in
my
life.
E
H
N
You
chess
and
we
need
to
present
the
as,
if
he's
extension,
to
support
proactive
protection,
and
this
is
the
new
job,
and
the
background
is
that
we
know
that
there
is
some
always
some
indications
before
a
physical
failure
happens
in
a
network.
If
we
can
catch
up
with
this
kind
of
event,
we
can
do
a
tradition
before
the
the
real
failure
happens,
and
one
of
the
typical
example
is
that
we
know
that
in
the
optical
transport
network,
most
of
the
failure
is
because
of
fiber
cut.
N
And
if
we
look
at
a
fiber,
the
fiber
is
is
quite
sensitive
to
the
pressures
or
stretch
and
say
if
we
have.
If
we
have
a
digger
coming
nearby
and
dig
in
the
dig
in
the
ground,
the
fiber
will
the
some
of
the
parameters
of
the
fiber
will
changed
a
lot.
So
if
we
can
catch
up
with
this
change,
we
can
do
the
prediction
when
the
fiber
will
be
cut
top.
N
So
so
the
main
idea
of
the
job
is
to
if
we
can
have
a
this
kind
of
video
protection
function
and
we
can
create
a
protection
pass
after
receive
the
protect
prediction
event
and
before
the
real
happen,
the
real
failure
happens.
So
we
made
a
extension
to
that
to
the
icdbg
protocols
to
support
these
kind
of
functions
and
because
the
tradition
is
quite
physical
technology
related,
but
the
protocol
extension
is
really
generic,
so
we
are
not
sure
to
push
in
see
Camp
Ortiz
so
to
be
safe.
N
N
So,
ok,
so
here
the
reason
why
we
introduced
to
missing
the
protection
object
is
to
indicate
the
intermedia
know
that
was
that
prediction
function.
Okay,
so
the
proto
is
tension
is
quite
simple.
We
add
these
two
B's
and
which
is
used
to
indicate
the
to
ask.
The
middle
note
took
notice
that
the
protection
function,
sorry,
the
prediction
function
and
okay,
this
is
for
the
segment
protection
is
very
similar
and
another
is
dangerous
to
the
notified
message.
We
may
need
a
new
sub
error
code
that
who
notified
the
note
does
not
about
the
prediction.
N
Failure
event
so
and
also
we
may
indicate
the
term
of
the
predation
and
if
the
failure
did
not
happen
until
t6,
then
we
can
consider
that
is
safe
is
safe
enough
to
tear
down
the
protozoan
path
to
save
the
resource.
That's
the
extension
and
next
step.
I
see
Chester,
have
answered
the
question.
We
can
continue
this
work
in
the
kiss
Nazi
camp
and
because
it's
not
new
jobs,
so
we
are
encourage
the
audience
to
help
comments
and
vote
for
us.
Thank
you.
E
E
Why
don't
you
look
into
creating
local
state
on
pillars
or
not?
That
is
attached
directly
to
failure,
and
at
least
you
reduce
the
blast
radius.
So
if
something
happens
or
you
predict
something's
going
to
happen,
DLR
might
create
some
state
and
throughout
the
traffic.
However,
in
your
case,
you
are
creating
state
across
whole
network
for
something
that
might
or
should
never
happen.
Right.
Error
CP
doesn't
seem
like
we're
a
suitable
vehicle
to
me.
C
E
G
G
Q
C
We
were
out
of
time
on
this,
but
just
quick
read
of
the
room.
How
many
think
that
this
is
an
interesting
topic
to
keep
discussing?
You
know
it's
a
very
early
draft,
obviously,
but
should
we
be
hearing
about
it
more
or
talking
about
it?
More
yes,
interested
so
there's
some
reasonable
number.
How
many
are
completely
uninterested,
just
Jeff?
Okay?
Now
we
got
a
cup,
we
have
a
couple,
but
you
know
there
was
clearly
some
interests
of
keep
talking
about
it,
but
dude.
C
R
Hi
guys
this
is
vodka
from
Hawaii,
and
today,
I
want
to
introduce
a
on
date,
mother
for
service
performance,
monitoring,
okay,
as
way
no
way
I
can
for
the
fund
set
of
technologies
to
support
as
a
perform
network,
performance,
monitoring
and
population
said
how
far
see,
but
this
walks.
This
mechanism
can
only
cannot
be
used
as
a
data
source
to
merriments
weapon
level,
alter
new
levels,
network
performance,
so
two
addresses
issues
away,
propose
a
documented
to
define
the
young
date
module.
R
It
can
help
to
do
the
network,
performance,
monitoring
and
weapons,
erased,
monitoring
and
also
can
help
to
use
a
monitoring
and
management.
The
network
performance
on
the
topology
at
higher
layer,
all
at
a
service
authority
between
VP,
incite.
This
drafter
is
present
in
last
year
in
Bangkok
and
in
bathroom
working
group.
There
are
many
people
are
interested
in
this
topic
and
so
working
who
has
visited
it
in
conferred
option
and
our
queue
here
is
some
snails.
R
If
we
want
to
choose
wrote
an
open-source
monetary,
we
can
Marin
two
products
first
step.
We
can
merriment
protein
Network
performance
in
under
layer
Network
and
using
this
you
know
that
previous
discussions
are
pieces
are
another
mechanisms
and
then
a
report
use
a
controller
and
the
controlled
came
on
chirper
tano's
performance
and
the
user
can
use
subscribe
notification
master
to
retrieve
this
data.
All
just
use
only
demand
RPC,
just
drive
Caterpie
spell
command
to
Travis's
module
to
drive
this
mode
teacher.
R
If
we
can
cut
this
data
so
we
can
optimize
the
network
census
data
here
are
two
works
need
to
do
the
first
say
the
way
you
took
your
animal.
Do
we
need
to
augment
network
topology
to
provide
this
information
on
network
level
and
also
need
to
provide
this
as
a
performance
data
in
data?
Well,
all
you
know
driver
all
link
level.
We
also
need
to
establish
relationship
between
under
layer,
topology,
the
service
layer,
topology.
R
R
Libyans
performs
monetary
and
we,
if
and
you
can
predict
how
only
one
didn't
us
receive
the
notification
from
the
device.
All
we
can
use
just
to
use
it
a
get
to
drive
this.
You
know
this
daters,
ok,
a
way
how
one
open
issue
in
email
discussion-
and
we
there
are-
we
talk
about-
we
receive
some
comments.
It's
a
hard
talk
about
should
way
a
design
like
linked
hard
to
indicate
different
channels
to
technologies
and
we
print
in
way
we
bring
in
the
advertising
mail
list.
R
The
party
didn't
receive
a
free
park,
but
currently
rate
is
a
starts
okay.
So
it's
a
way
forward.
We
have
received
a
good
number
support
in
past
session,
but
cheers
may
not
have
decided
it
should
be
done
in
pass
so
a
way
presence
document
in
here,
because
the
feel
relevant
Jeff,
the
proquest
in
this
working
group.
So
we
want
to
hear,
is
it
is
chairs
otherwise
I.
C
S
Hello
final,
one
almost
done
so
this
is
how
me
I'm
from
Harley
and
I'm,
presenting
the
young
data
model
for
client
to
signal
a
performance
monitoring.
This
is
a
new
draft
and
we
will
present
here
and
together
in
C
camp
as
well.
So
this
is
a
new
model
and
the
first
question
would
always
be
why
we
need
this
model
and
we
we
have
so
far
completed
the
configuration
of
the
Ethernet
service
and
the
transport
signs
signals
over
the
let's
say
the
T
panels,
or
more
specifically,
GNP,
are
supporting
technolon
O's.
S
So
the
operator
would
need
the
kind
of
performance
to
be
more
than
her
service
or
client
signal
configured
on
the
C
part.
So
basically,
this
kind
of
performance
monitoring
is
done
by
its
configured
by
the
controller
and
also
on
the
customer
edge,
and
this
is
also
to
be
kicked
off
between
the
controller
and
these
upper
hierarchies.
S
So
this
is
the
more
network
side
rather
than
the
server
side,
and
the
other
is
the
previous
topic
in
the
agenda
talking
about
the
VPN
stuff,
and
that
is
we
peon
service,
which
it's
different
from
this
two.
So
we
believe
currently
is
a
boundary
between
the
scope
of
those
three
works
are
clear
so
far
and
what
has
been
done?
Okay,
this
is
the
capture
of
the
subset
of
the
tree.
So
what
has
been
done
so
currently?
S
We
only
use
the
latency
as
a
as
an
example
for
how
to
do
the
performance
monitoring
and
we
can
configure
okay,
how
you,
how
you
monitor
the
latency
and
how
you
read
the
latency
from
the
using
the
models
and
the
same.
We
list
we
provide
a
table
and
are
playing
the
performance
candidates.
Performance
parameters
may
include
the
bit
error
rate
packet,
loss,
cheater,
bandwidth
and
so
also
first,
so
it
may
be
used
from
the
year
0
to
layer,
2
networking,
but
some
of
them
more
specific
of
more
layer
specific.
S
So
we
presently
here
and
to
make
sure
that
we
are
doing
the
right
thing
whether
this
thing
is
generic
or
technology
specific
and
from
the
perspective
of
the
other.
So
we
believe
this
was
quite
technology
specific,
because
we
we
have
layer,
specific
performance
and
we
like
to
do
it
through
a
very
specific
configuration
model
as
well
and
to
move
forward.
We
need
to
make
sure
that
we
coordinate
with
other
performance
monitoring
models
and
continue
to
to
make
the
parameters
in
the
plan
table
to
be
incorporated
into
the
model.
T
Dieter
bell
or
nokia.
I
suppose
that
this
document
is
not
specifying
any
new
performance
monitoring
capabilities
that
have
to
be
implemented
in
the
device.
I
guess
it's
probably
referring
to
existing
mechanisms,
and
I
think
it
would
be
good
to
have
references
to
those
standards
or
specifications
that
define
those
mechanisms
like
I
understood
that
the
latency
measurement
is,
for
example,
used
as
an
example
a
or
there's
the
first
example
also
there.
I
think
it
would
be
good
to
add
a
reference
how
a
latency
is
determined
yeah.
S
C
S
C
S
Q
Who's
it
from
oh
I,
speak
I.
Think
if
you
are
all
maintaining
technology,
specific
modules
is
difficult
to
do
that
in
a
generic
module.
Maybe
what
we
can
have
is
some
generic
types,
because
maybe
lattice
is
the
same
for
every
technology,
so
we
can
assign
generic
types
and
import
those
types
into
this
technology.
Specific
combination,
you
can.
C
See
at
least
should
try
I
mean,
for
example,
IP
and
Ethernet.
What
I
just
saw
that
list?
There
would
share
an
awful
lot
of
things
yeah,
the
other.
The
other
thing
is
is
that
there
are
is
other
Ethernet
performance,
pram
performance
monitoring,
related
work,
notably
in
the
I
Triple
E,
and
we
might
be
able
to
just
leverage
off
of
that,
which
of
course,
ends
up.
You
know
countering
my
own
argument
is
that
becomes
technology,
specific
yeah,
I
think
a
little
more
work
needs
to
be
done
here
to
understand
different.
