►
From YouTube: IETF106-RTGWG-20191120-1330
Description
RTGWG meeting session at IETF106
2019/11/20 1330
https://datatracker.ietf.org/meeting/106/proceedings/
A
A
So
probably
you've
seen
the
note
well
by
this
point,
things
that
you
say,
while
participating
the
working
group
have
certain
consequences.
So
please
pay
attention
to
to
be
note
well
and
read
it
well,
if
you
haven't
already
so
there's
a
sort
of
generic
IETF
policy
about
our
IP,
our
disclosure,
the
routing
area,
working
group,
interpretation
of
that
that
process,
so
that
we,
you
know,
we
got
all
of
our
eyes
and
cross.
Our
T's
is
to
require
that
document.
A
Authors
and
contributors
state
whether
or
not
they're,
aware
of
any
IP,
are
relevant
to
the
document
in
question
that
you
know
it
also.
Others
should
generally
do
it
as
well,
if
you're
participating
in
the
working
group
in
any
in
any
fashion-
and
we
do
it
at
two
stages
in
the
working
group
document
process,
both
when
adopting
individual
dress
and
then
before
working
group
last
call,
so
we
have
engine
doing
the
note-taking.
Do
we
have
a
jabber
scribe,
okay,
you're
on
jabber,
so
that's
good!
The
blue
sheets
are
already
circulating.
A
B
A
A
C
A
The
ATN
bgp
draft
is
expired.
It
would
be
good
to
just
keep
it
current,
even
if
there
aren't
substantive
changes
just
to
keep
it
top
of
mind.
The
the
data
tracker
now
is
a
way
to
show
expired
drafts
as
well
so
I'm
showing
these,
but
it
would
be
good
to
you
know
not
require
that
so
the
VRP
PFD
point-to-point
draft
I
sent
out
an
email
to
the
authors
of
that
and
requesting
that
they
at
a
minimum
do
just
a
bear
update
with
some
sort
of
administrative
changes.
A
On
that
you
know
it
would
be
good
to
get
an
understanding
with
respect
to
that
draft
about
if
anyone's
implementing
it
and
that
kind
of
you
know
when
we
look
at
it
and
see
it's
expired.
What
does
that
mean
exactly?
Does
it
mean
that
it's
stable
and
no
one
you
know,
or
does
it
mean
that
no
one's
implementing
it?
So
it
would
be
good
to
in
terms
of
figuring
out
how
we
proceed
to
get
that
feedback,
but
first
off,
please
just
update
the
draft
so
that
the
administrative
issue
can
be
dealt
with.
A
The
desk
source.
Routing
draft
is
also
showing
expired.
I
guess
David
had
asked
about
adopting
that
we
should
probably
start
a
discussion
about
adopting
or
rather
not
adopting,
but
doing,
working
good
last
call
for
that
draft.
It's
been
in
its
current
state
for
probably
a
year
and
a
half
or
so
so.
The
other
drafts
here
I
think
the
first
two
we're
going
to
hear
about
and
I,
don't
think
we
have
presentations
on
the
other
ones.
Okay,
okay,.
B
E
F
So
the
purpose
of
the
document
I
got
quite
a
few
comments
while
reach
out
to
people
hey.
Can
you
give
some
comments
on
this
draft?
I
got
some
comments.
People
say
why
describe
lots
of
problems
and
what
are
theirs,
for
it's
not
really
for
educational
purposes.
Right
so
I
want
to
make
clear
to
people
that
there
are
lots
and
lots
of
problems
associated
with
cloud
interconnection
and
some
of
the
problems,
not
something
I
think
we
think
IETF
can
do
so.
F
So
the
oh,
the
cloud
public
cloud
data
center
today
is
primarily
between
client
to
the
cloud.
Okay,
you
can
have
different
ways
to
access
the
cloud
and,
however,
if
you
have
some
workload
in
AWS,
if
you
want
to
connect
you
as
your
you
pretty
much
have
to
helping
back
to
your
customer
gateway
to
interconnect
them
together.
So
the
scope
of
this
document
we
call
network
to
cloud,
is
really
to
address
the
net
network
perspective
to
interconnect
them.
F
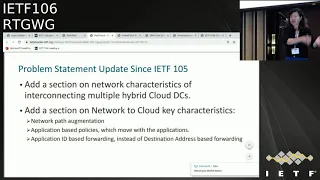
Ok,
so
here's
just
a
brief
summary
of:
what's
added,
we
added
interconnect,
hybrid
cloud,
the
problems
associate
with
them.
We
also
add
a
section
to
talk
about
some
characteristics
of
application
hosting
the
cloud
the
connecting
to
them.
Well,
the
thing
is
like
we
know
the
network
augmentation,
it's
not
just
one
that
were
connecting
to
the
cloud
and
lots
of
times
multiple
ways
and
you
may
have
networks
stitched
together
or
you
may
have
network
magic
multiplex
together.
F
Another
thing
is
application
based
policy.
Those
policies
can
change
based
on
where
the
application
is
so
it's
basic
away
from
the
traditional
we
have
a
firewall
with
defying
our
access
list
or
our
security
policies
on
the
specific
appliances,
and
when
you
have
application
in
the
cloud,
the
the
policies
actually
move
with
the
application.
You
have
to
have
a
way
to
specify
those
policies
are
specifically
for
those
applications.
When
application
moved
from
this
location
to
another
location,
the
policy
has
to
follow
them.
F
Basically,
that's
another
difference
from
the
traditional
networking
and
third
part
is
application
based
forwarding
instead
of
destination
based
forwarding
in
the
network,
for
so
many
decades
has
been
always
using
destination.
As
the
way
to
forward,
but
many
of
the
application
today
is
really
using
application
ID
to
forward
and
different
application,
many
different
topologies.
So
that's
one
some
of
the
key
characteristics
of
connecting
to
cloud
which
is
different
from
traditional
networking.
F
At
a
slide,
this
is
actually
primarily
from
earlier
suggestion,
the
key
requirement
so
for
accessing
the
cloud.
While
the
key
thing
is
authentication
authorization
right,
so
you
could
have
a
particular
application
in
the
cloud
and
then,
depending
on
who's
accessing
it.
You
have
different
policy
right
or
you
can
have
policies
on
this
cloud
application
saying
hey.
If
the
traffic
requests
from
the
prams
headquarter
data
center
coming
the
request,
you
can
grant
the
communication
or
processing,
but
if
the
request
traffic
coming
from
a
sure
data
center,
then
you
don't
have
any
communication,
you
drop
it
all.
F
You
may
report,
or
maybe
the
policy
is
changing
like,
for
example,
from
a
certain
time
to
a
certain
time.
You
have
different
authentication
method
and
then,
when
you
have
our
to
cloud
data
center,
when
one
application
need
to
connect
to
another
cap
application,
how
do
you
do
the
authentication?
How
do
you
do
the
authorization?
So
that's
a
big
thing
about
intercloud.
F
F
You
may
have
a
VP
C
for
your
production
environment
and
you
could
have
the
same
application
running
in
different
B
pcs,
but
when
the
traffic
actually
coming
from
this
data
center
or
cloud
data's
in
a
to
your
campus
network,
lots
of
time,
you
can
now
tell
which
VP
see
it's
coming
from,
you
have
an
address,
it
doesn't
attach
with
the
PPC
number
and
similarly,
you
have
ensures
v-net
similar
thing,
the
v-net
and
vp
c.
How
do
I
make
sure
that
they
actually
belong
to
the
same
client
or
same
domain?
F
So
you
may
have
a
subnet
like
we
call
subnet
belong
to
one
particular
group,
but
when
you
assign
something
put
something
into
the
EWS,
they
have
a
VP,
see
you
put
something
else
in
to
the
assure
you
have
v-net.
How
do
we
combine
them
as
well
and
entity
to
show
they
can
actually
communicate
with
each
other?
So
thus
something
has
to
be
addressed
and
that's.
Another
thing
is
about
API
right,
but
this
API
actually
I'm
not
sure.
If
I
can
do
anything
about
it.
It's
basically
different
cloud.
F
G
Maybe
I
don't
understand
what
you're
proposing
Linda,
but
we
keep
talking
about
preparers
proprietary
cloud
designs,
which
are
of
course
entirely
within
the
scope
of
the
provider
to
define
and
modify
the
api's
as
they
want.
We
don't
normally
sort
of
do
interfaces
between
proprietary
systems.
We
only
really
ever
design
standard
solutions,
so
you
could
have
a
sort
of
a
shim
layer
that
we
define
that
they
have
to
map
to,
but
I
don't
think
we
should
be
talking
about
mapping
between
proprietary
systems,
I'm.
F
Not
proposing
that
I'm
just
saying
this,
some
of
the
problems
appearing
and
this
may
be
out
of
the
scope
of
IETF
I,
just
put
it
there.
This
is
one
of
the
problems
facing
by
many
enterprises
when
they
access
multiple
clouds.
That's
all
I'm
doing
here,
I,
don't
think,
that's
something
we
need
to
address.
That's
my
personal
deal.
Okay,.
F
Okay
and
another
problem
requirement
is
the
neck:
how
do
they
do
the
net
different
cloud
provider
has
different
methods
and
how
does
the
network
handling
different
net
methods
and
DNS,
and
also
that
is
any
way
to
like
discover
how
many
cloud
data
centers
this
particular
application
is
connected
to
right.
Those
are
some
of
the
key
requirements
for
the
multi
cloud.
F
For
the
key
problems,
that's
the
focus
of
this
particular
document
is
really
to
address
some
of
the
problems
Enterprise
facing
to
connect
to
the
multiple
cloud.
So
so
the
with
different
cloud
is
basically
like.
We
have
different
access
methods
right,
so
I
I'm,
repeating
myself,
so
that
today
you
have
to
here
ping
back
to
the
campus
network
before
you
can
reach
to
another
cloud.
Make
it
very
difficult.
F
Second
thing
is
as
a
application
self
hiding
inside
the
cloud.
It's
because
the
cloud
allowed
different
ways
of
access
right.
You
can
access
through
public
Internet,
you
can
access
from
IP
sack
you
can
access
from
the
direct
gateway
they
were
connect
and
as
application
themselves
residing
inside
the
cloud
they
can
now
tell
which,
which
entrance
which
gateway
comes
in.
That's
how
it
today's
design,
and
with
that
it's
difficult
to
make
a
consistent
like
performance
measurement
or
maybe
applying
different
policy,
depending
on
which
entrance
you
coming.
F
F
Another
thing
is
the
the
IP
set
itself
right,
so
Abby
set
itself
IP
set
is
point-to-point
right,
so
point-to-point
works
well,
when
you
get
just
have
two
points,
when
you
do
the
configuration
you
configure,
who
are
you?
Who
is
your
remote
end?
And
but
the
problem
is
when
you
have
multiple
sites,
when
you
have
ten
twenty
sites,
and
this
configuration
becomes
very
difficult
and
especially
you,
we
have
two
different
cloud:
data
centers
using
a
preset
becomes
not
not
easily
to
manageable.
F
F
Well,
the
gabilan
analysis
I
just
added
this.
In
the
past,
we've
been
talking
about
using
tunneling
cap
to
carry
the
IPSec
information
to
carry
the
net
information
that
is
in
ID.
Are
they
already
there
already
a
document
proposal
on
how
to
do
that,
and
in
the
best
we
have
a
informational
draft
showing?
How
do
we
use
PGP
to
be
able
to
distribute
the
IPSec
information
to
establish
those
tunnels.
F
F
F
It
could
happen
that
the
application
ID
like
this
read
application
payment
system
and
some
other
application
from
the
same
user
may
have
the
same
address,
and
this
can
create
some
problems.
How
do
we
distribute
that
information?
Because
the
application
read
has
to
only
follow
the
point-to-point
topology,
the
tree
topology
to
the
payment
gateway?
They
don't
allow
the
read
application
to
talk
among
each
other.
The
purple
one
is
another
type
of
application
which
is
allowed
to
be
multi-point,
so
one
address
has
to
be
put
on
into
two
different
topologies
I.
Think
that's
something
I'm
not
sure.
F
F
Another
thing
is
the
IPSec
today
is
among
the
client
traffic.
You
create
a
client
traffic
and
you
create
IPSec
tunnel
among
those
clients
that
is
well
between
if
you
just
have
two
nodes,
but
if
you
have
multiple
nodes
and
it
can
be
difficult
so
so
that
it
would
be
good
to
be
able
to
create
some
kind
of
port
days,
IPSec
tunnel,
so
treating
the
IPSec
tunnel
as
a
transport
PI,
so
that
different
traffic
can
be
multiplexed
together
or
be
forwarded.
F
F
Next
step,
so
one
more
review,
I
promise
chair
that
I
know
that
people
are
very
tight
on
time.
You
don't
have
many
times
much
time
to
do.
Everybody
has
lots
of
work.
I
promise
I'll
write
a
very
simple
document
just
along
the
line
I
present
today,
maybe
one
page
two
page,
take
you,
maybe
five
minutes
to
review
it
to
see
if
those
problems
have
been
properly
identified.
H
That's
my
personal
view,
so
my
my
question
is:
should
you
focus
on
cloud
interconnection
and
I?
Think
then
that's
one
option
or
you
should
focus
on
as
the
one
problem
statements
into
working
with
clout
or
something
but
right
now
from
reading
the
document.
Personally,
I
don't
see
where
you
want
to
go
here.
Alright,.
F
That's
a
very
good
suggestions:
we're
going
to
focus
on
the
net
to
cloud
for
the
cloud
interconnection,
so
I'll
take
out
all
the
sd1
mentioning
we're,
focusing
on
primarily
we
use
network
to
connect
to
different
cloud
or
multiple
clouds.
What
are
the
problems
we
have
today?
What
are
the
possible
solution
there
could
be
IT
have
already
had
because.
H
I
J
H
F
B
F
So
what
I
would
do
is
create
a
very
short
draft
just
to
describe
the
problems
with
network
to
cloud
and
then
associate
problems.
I
want
people
to
give
input
just
for
that
specific
domain,
not
not
worrying
about
sty,
oh,
and
he
was
just
talking
about
that
and
if
I
find
some
of
the
material
in
the
document
available,
maybe
I'll
create
another
document.
Ok,
thank
you.
Thank
you
very
much.
Thank
you
for
your
suggestion.
That's
very.
I
K
K
The
other
is
about
the
initial
framework
proposal
and
we
would
like
to
have
your
reviews
and
comments.
Thank
you
and
the
first
about
the
motivations.
That
is
why
we
want
to
propose
the
AP
and
six
as
we
know
that
the
network
operators
have
been
facing
the
challenges
of
providing
better
services
to
their
customers
and
especially
nowadays
as
the
5g
and
the
industry.
K
K
Okay,
sorry
I
thought
it
was,
and
and
also,
moreover,
and
as
the
technologies
involved
and
the
currently
there
online
gaming
live,
reuse,
dreaming
and
also
the
video
conferencing.
Those
applications
are
widely
deployed
and
used
by
the
end
users
by
the
company's
enterprises
and
the
dos
applications
have
even
more
demanding
requirements
and
they
are
the
actual
revenue
producing
applications.
So
the
applet
that
the
network
operators
would
be
good
to
provide
the
the
application
level
SRA
guarantee
fine
granularity
and
as
Eric
guarantee.
K
But,
however,
the
current
network
dodging
doesn't
have
such
capability
of
application
awareness
and
the
network
operator
is
not
aware
of
watch
applications
actually
traversing
the
network
infrastructure
and
to
support
to
guarantee
the
SLA.
Currently,
the
operators
can
only
use
the
light
load
and
sometimes
even
10%,
in
network
utilization,
so
the
network
operators
just
to
keep
investing
in
their
network
structure,
but
they
haven't
counted
the
corresponding
revenue
increases
and
the
actual.
Actually
they
are
losing
the
opportunities
and
to
have
the
new
revenue.
K
So,
fundamentally,
for
us,
the
motivation
is
to
bring
the
application
information
into
the
network
and
to
make
the
network
aware
of
the
applications
and
as
well
as
their
requirements.
So
and
here,
and
we
also,
we
would
like
to
take
advantage
of
the
big
chant
for
now.
That
is
the
ipv6
and
as
our
v6
are
being
widely
deployed
and
and
and
the
programmability
provided
by
ipv6.
That
is
our
basics.
That
is
the
programmable
space
in
there.
K
K
The
first
one
is
the
application
information
conveying
and
that
it
could
be
the
application
itself
or
the
edge
devices
to
add
those
application,
information
and
ways
the
augmentation
of
the
existing
encapsulations
and
just
to
be
noted,
and
that
is
not
a
enforcement
that
is
optional
as
up
to
the
applications
to
decide
whether
to
I
did
or
not.
If
they
don't
add,
the
DOS
information
and
their
packets
will
be
traded
in
the
with
the
traditional
way.
K
Of
course,
they
couldn't
get
the
benefit
of
the
provided
by
18:6,
and
the
second
element
is
a
matching
between
the
application,
information
and
the
network.
So
that
is
like
the
network,
provide
its
capability
towards
the
application
and,
according
to
those
application,
information
and
the
network
could
provide
corresponding
services
like
the
network.
Slicing
deterministic
latency
guarantee
OSF,
see
if
Center
and
the
third
one
is
the
natural
measurement,
and
that
is
to
achieve
the
pattern
or
accurate
matching
for
the
second
element.
K
And
in
the
meadow
point
and
according
to
those
application
information
and
the
some,
we
could
also
do
some
manipulations
to
those
packets
to
guarantee
it
here.
As
our
a
and
the
here
another
highlight
is
that
this
flow
driven
method
could
enable
this
faster
service
for
reasoning,
and
we
have
done
a
lot
of
communications
with
our
customers
and
with
verticals
and
the
industry
here.
So
we
have
identified
some
use
cases
that
could
directly
benefit
from
the
AP
and
six,
and
here
we
have
categorized
into
the
following
five.
K
The
first
one
is
the
fundament
fundamental
one
that
is
a
application
aware.
I
saw
a
guarantee,
that
is
to
enable
the
network
operators
to
provide
differentiated
service
treatment
and
the
fine
granularity
traffic
operations
capability
and,
and
then
the
second
is
the
application
aware
network
slicing.
This
is
for
some
applications
that
they
have
the
specific
requirements
and
in
order
to
guarantee
their
to
satisfy
their
requirements
and
some
levels
of
isolation,
problem
problem,
probably
in
terms
of
the
service
isolation,
our
resources,
isolation,
to
guarantee
their
requirements
so
for
those
locations
they
could
be
steered
into.
K
Certain
networks
lies
and
to
guarantee
their
requirements
there
and
for
the
multiple
different
applications,
and
they
have
errors
that
requirements
they
could
be
steered
into.
Different
networks,
slices
and
and
those
applications
could
be
served
at
the
same
time
and
in
parallel
and
again
and
the
third
one
is
the
application
aware.
Deterministic
networking
for
some
applications
and
the
day
will
require
at
the
deterministic
under
the
latency
guarantee
and
for
such
application
flow.
They
could
be
identified
first
and
steer
into
the
certain
deterministic
path
and,
and
then
is
the
application
of
our
service
function.
Chaining.
K
The
past
the
potential
failure
that
could
arise,
and
here
just
briefly
to
update
with
you
and
what
happened
in
the
last
time
and
we
host
AP
and
six-eyed
meeting
in
105
when
this
is
the
meeting
room
and
we
have
about
50
attendees,
and
we
have
very
good
discussions
there
and
we
roughly
achieve
the
rough
consensus
about
the
value
of
the
work.
That's
why
we
decided
to
continue,
and
this
time
we
have
two
new
drafts
and
together
result
collaborators
and-
and
so
we
want
to
push
forward
and
for
the
Knights
tab.
K
And
we
would
like
to
have
a
meeting
list
for
us
to
continue
our
discussion,
and
now
we
can
only
have
the
separate
discussions
and
and
also
we
are
also
planning
to.
We
are
thinking
to
have
above
for
the
next
meeting
and
here
and
this
time
we
are
presenting
in
the
RT
GWT,
and
we
are
really
sincerely
looking
for
suggestions
related
to
the
chairs
here
and
how
are
we
going
to
move
forward
on
this
work?
So
that's
all.
Thank
you.
E
K
H
K
H
K
L
We
went
a
pseudo
beam
from
hobby,
the
first
one
I
think
that's
the
the
first
one
I
won't
say
it
as
the.
Why
we
discuss
in
rqwg
I
think
the
data
plane
I
use
a
true.
Now
you
saw
open
because
at
the
beginning
we
see
the
ipv6
advantage
you
because
this
the
applications
about
the
ipv6
and
now
this
a
network
aside
also
the
SRA
six-
can
be
combined
through
ipv6
a
similar
seamlessly.
L
That's
at
the
point,
but
I
think
that
usually
truly
can
be
open
to
the
I'm
chars
or
we
axel
I'm,
based
here
it
possible.
The
second
one
I
won't
say
that
the
SFC
I
true
it's
a
higher
some
days
of
the
application
information,
but
from
our
point
of
view,
I
think
I
use
nothing
enough.
On
the
other
hand,
therefore,
the
metadata
I
think
I
use
it,
because
the
metadata
is
another
standard.
Is
the
whale?
That's
a
pond.
H
M
You
know,
RFC
21,
19
may
vs.,
must
it's
a
very
short
step
from
may
to
must
for
some
networks,
and
you
could
end
up
in
a
situation
where
you're
forcing
devices
on
say
a
large
network
in
a
country
to
to
basically
self
DP
their
traffic
and
I.
Think
I,
don't
and
I
know
in
one
of
these
documents
discuss
any
of
these
issues
that
I
could
see
and
I
think
it's
a
huge
problem.
Yes,.
K
We
acknowledge
the
security
and
the
privacy
issue.
That
is
also
noted
in
the
draft
and
actually
post
draft,
and
we
know
we
are.
We
are
aware
of
those
mechanisms
are
needed
and,
for
example,
so
some
automation,
access
control
and
I
also
the
authentication
of
those
IDs
application
information,
son
needed-
and
here
that
would
be
one
topic
for
us
to
explore
there
right.
B
K
B
J
J
Maybe
this
is
some
difficulty
for
the
department
here
Network,
because
you
know
the
application.
There
are
many
many
application
application.
So
if
you
included
the
application
ID
in
the
network
letter
I
think
the
rotor
cannot
keep
so
many
state
for
the
selection
of
the
different
posture.
I
do
not
know
how
you
consider
is
the
accessibility.
K
Yes-
and
that
is
the
so
first
of
all-
and
that
is
depends
on
the
device
capability
and
from
the
camera,
the
scalability
provided
by
the
large
number
of
applications
and,
first
of
all,
it's
not
all
the
applications
for
you
preserve
in
this
way.
That
is
only
for
the
like
the
demanding
applications.
They
have
specific
needs
to
be
satisfied
in
the
network.
They
could
utilize
in
this
way
and.
J
You
I
think
the
unfortunate
is
no
IP
network
for
the
SLR
assumes
to
be
often
classified
the
traffic
into
the
several
category,
so
I
think
for
the
number,
the
adult
category.
The
network
can
easily
deployed
the
different
parts,
but
for
the
numerous
applications
requirement,
I
think
it
is
not
possible
to
deploy
these.
J
K
F
N
Dug
Montgomery
I
apologize,
I
haven't,
read
the
drafts,
but
I
had
two
simple
questions.
You
you
said
that
you
clearly
say
in
the
drafts
why
you
can't
achieve
what
you
want
to
achieve
with
existing
virtual
path
and
cost
technologies.
You
you
you
do
that
gap
analysis
of
why
you
can't
achieve
this
with
the
existing
mechanisms.
O
L
N
K
That
is
depends
and
for
the
certain
domain,
and
we
are
thinking
it.
First
of
all,
it
will
be
valid
within
this
is
operational
domains.
It's
it
doesn't
have
to
be
global
for
the
first
stage
and
for
sure
I
think
the
mati
doming.
We
also
acknowledge
the
in
the
tract,
and
that
needs
to
be
considered
because
the
IDE
needs
to
be
delivered
at
corresponding.
F
Linda
Dahmer
from
future
way
of
this
course
I
haven't
read
this
track
before
today's
meeting,
but
just
glancing
through
the
draft
I
find
is
very
useful.
Even
though
people
bring
up
security
concerns,
if
we
can
have
a
mechanism
to
hide
the
user
information
do
some
kind
of
mapping
that
bring
the
application
information
into
the
network
and
that
will
bring
tremendous
value.
This
bring
up
to
the
discussion
which
happening
other
as
deals
in
a
math
in
the
cloud
architecture.
Discussion
customers,
wanting
application
based
forwarding,
is
not
based
on
IP
address
but
based
on
an
application.
F
P
P
So,
first
we
have
a
overview
right
now.
We
have
SR
pass
fast
protection
for
transit
note
here
we
propose
essa,
fast
protection
for
equation
node.
So,
for
example,
we
have
here
we
have
a
as
a
pass
from
p1
ingress
and
then
to
p3
as
a
egress.
So
this
pass
is
a
pass,
carries
the
VPN
traffic
so
in
order
to
provide
protection
for
p3,
which
is,
is
the
egress
of
all
this
as
pass
this
as
a
pass?
So
we
have,
we
will
have
a
PI
cap
equals
node.
P
Here
is
pp4,
so
in
order
to
provide
protection,
we
first
we
configure
on
p4,
which
is
a
biker
believers,
so
the
concrete
configuration
that
which
has
a
configure
bureau
ID,
which
is
to
protect
ps3
and
with
this
kind
of
configuration
and
then
there's
some
actions
going
on.
So
one
action
is
that
the
information
about
this
protection
will
be
distributed
in
the
in
the
network
and
then
at
the
same
time
and
PE
for
which
is
egos
note
a
backup,
accuser,
node,
so
pg4
will
generate
a
map
a
map
in.
P
So
this
mapping
will
map
that
traffic
for
for
a
VPN
traffic
from
when
the
traffic,
when
the
traffic
coke
received
from
backup
has
total
traffic
volume
through
data
mapping
map
into
the
destination
which
is
c2
so
after
configuration
so
on.
The
previous
hope
of
a
equals
node,
for
example,
here
is
p1
and
that
the
p1
will
create
forward
entries
for
protect
the
ps3
here,
for
example,
on
PE
1,
when
1
P
1,
which
is
previous
hope
of
equation.
P
P
is
3
when
P
is
really
fails.
P
P
1,
P
1
will
detect
the
failure
so
P
1.
We
all
seen
the
traffic,
which
is
a
packet
to
PE
3
to
the
bike
hub
equals
note,
which
is
PV
for
through
bike,
a
pass
so
before
sending
those
traffic
to
the
backup
path
to
the
bike.
A
believer's
node
so
p1
well
just
to
modify
party
a
little
bit
just
add
that
mirror
ID
for
the
package.
P
So
we
provided
protections
for
failure
of
us
note
ps3
in
faster
way.
So
regarding
to
the
updates
to
the
previous
version.
So
we
just
the
ad
the
two
sections.
Why
is
the
security
considerations
and
that's?
Why
is
a
ionic
institutions?
And
then
we
updated
the
reference
and
the
third?
Why?
The
some
editorial
changes.
Q
Q
P
R
We
change
from
channel
move
out
at
first
I
think
this
solution
is
a
really
useful,
I
think
because
of
during
4G
China
Mobile
deployed
a
lot
of
a
dual
homing
protection
function,
so
I
think
this
function
can
be
used
in
the
future
and
that
I
have
a
question
about
the
mayor
note.
So
here
you
just
released
the
one
major
note
is
other
possible
configure
more
than
one
mirror
note
right.
P
Now
I
hear
we
have
only
one
backup,
plus
a
backpack,
have
a
eCourse
note,
so
you
mean
we
are
want
so
here
for
the
mural
to
one
load
or
two
dolls,
I
think
in
the
in
this
document.
So
we
can
provide
protections
to
multiple
locators.
So
if
you
use
single
data,
that's
a
marrow
to
Mudville
and
the
marrow
tomato
I.
Don't
know
whether
you
mean
that.
R
E
P
P
R
J
P
Your
so
right
now
it's
a
one-way,
this
or
configuration
so
another
way,
maybe
a
source.
So
this
right
now,
because
we
have
a
central
controller,
you
will
have
a
in
the
controller
environment.
So
those
those
kind
of
configuration
can
be
automatic
through
the
controllers,
so
the
controller
can
do
can
select,
which
one
protocol
which
one
and
then
which
ID
provide
which
locator
and
then
those
can
automatic
mean
that
way.
Yeah.
J
I
think
this
is
in
Canada
should
be
a
remand
automatically
in
network,
so
you
know
in
Korea
we
cannot
know
which
node
or
which
link
will
be
broken
down
in
network.
So
you
know
we
I
think.
If,
in
such
a
such
mechanism
become
deployment
automatically
to
India
network,
we
are
either
management
of
the
VPN
protects
them.
Yeah.
P
Yeah
all
right,
I
think
these
draft
is
just
for
a
proposal
based
solution
and
then
based
on
this
basic
solution,
we
can
have
a
very
comprehensive
or
automatic,
and
that
solutions,
because
with
some
notes
or
server
controllers,
have
a
high
level
view
and
then
he
know
which
node
can
provide
for
some
kind
of
protection
for
which
node
and
then
whether
we
have
another
resource
and
link
to
support
this
protection.
Okay,.
S
T
P
Q
U
Louis
Chan
juniper,
one
question
is
that
appear
out
on
p1.
If
we
want
to
protect
the
VPN,
are
we
need
to?
We
need
to
look
into
the
more
packets.
I
mean
dipped
into
the
lipos,
so
that
to
locate
whether
where
there
is
a
protector
or
no
protector,
I
mean.
If
you
want
how
many
labels
you
need
to
mean
I'm
a
release.
X
labeled
in
to
inspect.
Oh,
you
mean
the
okay,
so.
P
I
regarding
to
the
VPN,
so
we,
for
example
here
we
use
a
VPN
SSID
so
because
VPN
we
also
get
more
information.
So
those
are
key
value,
information,
nice
and
easy
in
the
trough.
So
here
we
we
turned
in
this
picture.
We
come
give
details
about
this
total
information,
I
think
basically
for
VPN,
for
example,
of
he
be
honest.
P
So
so
these
are
VAP
here
and
for
one
prefix,
those
Vivian
can
be
associated
by
those
kind
of
or
same
a
VPN
and
the
same
way
of
a
VM,
for
example,
on
the
history
where
I
would
have
Libya
ID
for
the
backup
girls.
We
have
another
VPN
as
ID,
so
because
the
way
I
was,
we
know
this
on
the
same
VPN
and
then
those
we
can
associated
those
one.
So
that's
the
my
opinion
come
from
so
for
for
the
VPN
ID
on
ps3,
that's
different
on
ps4
v
and
E
as
another
one.
P
So
when
P
is
three
files
p1,
we
detect
a
failure
and
in
p1
we
modified
the
package.
Just
a
add
a
mirror
IB
through
the
package
and
then
the
Viviani
on
on
the
ps3
not
changed.
So
when
this
package
is
delivered
to
the
p4
and
then
because
we
have
maro,
we
use
melody
mode
at
a
VPN
ID
on
the
ps3
to
the
local
VP
ID,
which
is
on
a
PG
4
and
then
because
of
those,
even
so
will
have
different
V
Vivian
IDs.
But
those
two
different
one
of
for
same
Vivian.
B
P
B
G
Well,
before
you
ask
for
adoption,
I
think
there's
a
few
technical
problems
you
need
to
solve,
not
the
least
of
which
was
whether
the
anycast
solution
is
a
better
solution
or
not,
and
also
exactly.
We
are
whether
you're
actually
conforming
to
various
architectures
in
the
design,
so
I
think
we're
a
little
way
from
calling
for
a
so
I
really.
B
P
So
this
wise
about
architecture
for
youth,
basically
as
a
central
controller.
So
basically
PGP
is
already
you.
The
controller
is
somewhere
in
somehow,
for
example,
we
ratify
the
SR
policy
and
then
direct
traffic,
and
then
we
have
some
advantages.
We
use
PGP
as
controllers.
We
list
the
number
of
advantages
here.
So
basically
these
are
draft.
We
propose
us
as
three
reference
architectures
for
PGE
as
a
central
controller.
So
why
is
a
single
controller?
And
then
that's?
Why
is
a
controller
cluster
so
which
is
the
middle
middle
one?
P
V
John,
who
is
probably
asking
CGI
chair,
John
scatter
I,
am
NOT
up
here
with
any
chair
hats
on
I,
I
guess.
My
question
is
and
I
think
this
has
been
asked
if
I
remember
right
in
previous
meetings
and
I,
don't
really
know
if
it's
been
answered
or
if
I,
if
it
wasn't
I
forgot,
I'm
sorry,
why
do
we
need
to
work
on
this
in
the
IETF
and
and
I'll?
Give
my
own
answer,
which
is
so
far
I?
V
P
C
Stiffening
of
key
I,
don't
like
that.
You
talk
about
bgp
as
a
controller.
Bgp
is
just
protocols,
so
it
can
be
a
self
interface
of
a
controller,
but
it's
not
a
controller
at
all.
So
you
can
define
a
controller
architecture,
but
it
has
nothing
to
deal
with.
Bgp
bgp
is
just
an
interface
that
the
controller
could
use
to
program
a
path,
but
we
already
have
the
extensions
defined
to
do
so
so
I
don't
really
see
yeah
Sooni.
A
O
O
We
have
to
ask
ourself
a
little
bit
more
and
how
do
we
want
to
continue
getting
you
know
to
the
goals
in
order
to
enable
better
operational
productivity
for
the
network
operators.
The
is
there
a
value
of
splitting
things
up
into
multiple
layers,
splitting
the
decision
making.
Where
should
we
make
some
decisions?
O
O
O
How
can
we
you
know
again?
This
comes
down
to
real-time
actions.
If
there
is
something
happening
that
we
can
react
in
there
that
we
can
enable
an
application
that
detects
that
to
put
the
fast
reaction
without
waiting
for
the
human
network
operator
to
execute
on
the
action,
so
there
are,
you
know,
are
any
of
those
features
useful
and
the
reason
I'm
asking
that
is
that
traditional
traditional
vendors
in
the
past
I'm
not
sure
if
this
still
is
the
presence,
but
in
the
past
day
you
know
they
were
giving
you
some
lackluster
support
for
that.
O
You
know
they
were
I
mentioned
here
too.
That
I
was
part
of
it.
You
know,
I
know
about
it,
but
like
another
one,
but
it
was
proprietary
interfaces.
It
wasn't
the
friendliest.
You
know
environment,
to
develop
to
the
third
parties.
You
have
to
adopt
many
vendor
development
policies
in
order
to
be
able
to
do
that,
and
they
were
never
too
happy
to
do
it
or
to
expand
it.
If
you
were
asking
me
I
want
this
I
want
that
Bob.
O
We
will
be
just
bolting
on
more
and
more
things
onto
that,
and
we
did
that.
We
were
saying:
oh,
we
need
more
and
more
things
to
execute
on
the
network
and
at
the
same
time
we
were
running
into
a
problem
with
the
CPU,
and
you
know
in
the
memory
and
we
were
trying
to
build
bigger
systems,
but
there
was
more
more
software
and
more
shared
infrastructure.
O
O
In
my
opinion,
we
should
really
abandon
the
controller
agent
architecture
because
it
it
is
ending
up
being
a
mess,
and
then
you
have
controllers
on
the
controller.
Hierarchical
controllers,
you
are,
you
know,
getting
in
a
way
lost
in
different
controllers.
What
each
one
is
doing-
and
you
are
hiding
too
much-
Network
information
behind
multiple
agents
and
controllers,
one
of
the
thing
which
I
really
liked
about
the
Aitu
RS.
It
was
the
initial
services
focused
on
the
services
they
included
and
they
said
hey.
O
You
know
what
we
would
like
to
manipulate
these
services,
this
application
as
well.
You
know,
as
the
rib
in
this
focus
on
this
you
know,
applications
is
something
that
I
find
attractive
and
that
we
are
touching
upon
in
different
areas
of
the
ITF.
But
at
least
to
me
it
looks
you
know
a
little
bit
of
unstructured
and
I
would
like
to
see
more
proper
layers,
because
if
you
look
at
any
network
element,
we
can
say
we
have
the
forwarding
and
hardware
abstractions.
O
We
have
the
shared
infrastructure
in
the
data
and
then
we
have
the
applications
on
top
of
that.
Now,
if
we
look,
what
is
where
and
saying
hey
look.
What
is
the
forwarding
and
the
hardware
abstractions?
We
have
people
who
know
packet
by
plants.
We
have
people
here
in
the
ITF
community
who
are
building
and
working
with
them
to
provide
us
a
you
know.
O
What
here
are
the
here
are
the
models:
here's,
what
we
can
support
visiting,
what
we
can
provide
as
a
high-level
model
and
decide
what
to
I'm,
not
saying
what
should
be
the
transport
for
that
I'm.
Just
saying:
here's
the
model.
What
that
hard
work
can
do.
It
can
be
vendor
specific.
But
as
long
we
can
agree
on
the
common
semantics
and
the
common
syntax.
We
can
make
a
big
you
know,
step
forward
in
having
some.
You
know
common
model
that
everybody
will
understand.
I
love
to
go
back
to
the
ACL
example.
O
O
So
with
that,
if
we
can
decide
for
each
one
of
those
layers
to
have
a
common
naming
convention
with
the
common
models
with
the
minimum
functionality,
we
can
either
move
forward
and
say:
look
if
we
decide
that
we
can
layer
that,
in
you
know
such
examples
where
we
would
be
X
for
each
application
for
each
in
a
shared
infrastructure.
A
framework
that
we
will
be
saying
here
are
the
models.
Here.
Are
the
frameworks
that
we
would
you
know
like
to
work
on
and
support.
O
O
You
can
get
the
photo
buffs,
you
can,
you
know
change
it
model
it,
but
do
we
want
to
adopt
that
or
do
we
want
to
see
and
make
sure
that
it
can
work
for
a
much
wider
community
and
for
much?
Why
the
use
cases
then,
for
just
a
certain
type
of
use,
cases
that
that
has
been
the
proposed
and
done
and
I
would
say
you
know
with
all
of
this-
is
rip
2i
Torres.
It
should
rest
in
peace.
It
was
a
useful
exercise,
but
the
outcome
of
that
wasn't
very
useful.
O
The
architecture
wasn't
there
I
liked.
Ok,
here
are
the
services
that
we
should
focus
on.
This
is
what
you
would
like
to
be
able
to
manipulate.
Let's
find
what
would
be
the
right
way
to
get
them.
You
know
at
each
correct
layer
the
actions
that
we
will
provide
to
the
users
in
different
ways,
because
I
don't
want
to
address
a
protocol
through
a
controller
I,
don't
want
to
add
another
layer
of
abstractions
between
it.
I
would
like
to
be
able
to
talk
directly
to
the
protocol.
O
Daemon,
you
know,
get
the
actual
state
from
the
protocol
daemon
compared
to
the
state
on
the
on
the
wire
and
no.
What
is
this
situation
between
and
on
my
intended
and
Maxwell's
day,
if
I
going
through
anything
in
between
that
I'm,
you
know,
I,
don't
know
how
much
information
they
sent
them
from
me.
What
you
know,
what
I
can
really
actually
what
I
can
change?
What
I
cannot
change
and
simplifying
such
actions
would
move
us
forward
in
again
achieving
better
program
ability
of
the
overall
network.
O
Now,
do
you
want
to
do
some
work
like
that
I'm,
not
sure,
because
we
have
some
of
our
own.
You
know
employer
restrictions,
we
have.
You
know
some
of
our
own
ideas,
but
I
said
it's
a
thought:
experiments
that
each
one
of
us
can
do
and
I
just
want
you
to
give
you
some
food
for
thought
and
say:
maybe
we
can,
you
know,
propose
something
else
and
see
if
it
can
be
useful
or
not.
Thank
you.
W
W
Fine,
so
the
the
presentation
has
a
lot
of
excellent
points:
I
Taurus
in
all
no
objective
criteria
for
what
was
supposed
to
have
accomplished
failed.
We
ended
up
with
models.
We
ended
up
with
no
the
vestiges
of
a
mechanism
that
supposedly
used
that
comp
to
actually
do
that.
Work
and
people
are
not
deploying
it.
So
from
that
could
stand
point,
it
is
a
failure,
but
over
the
time
that
the
working
group
existed
and
that
the
models
got
worked
on,
you
know
we
helped
the
net
modern
epitaph
groups
changed.
The
protocol
changed
their
mechanisms.
W
You
know
the
current
data
store
model
is
largely
influenced
by
the
ITRs
work.
A
lot
of
the
Dynamis
adeno
that
we
had
in
terms
of
things
in
Metcalfe
was
pushed
partially
by
hrs
back
in
the
day,
a
lot
of
the
components
that
we
actually
talked
to
the
RHIB
model
that
we
have
an
IETF
got
a
big
upgrade
because
the
hrs
people
were
looking
at.
W
You
know
the
contents
of
things
with
great
scrutiny,
so
there's
a
lot
of
inputs
that
this
failed
experiment
had
in
terms
of
pushing
on
the
rest,
the
ietf
ecosystem,
to
develop
good
stuff
and,
to
a
large
extent,
about
your
components,
no
we're
we're
looking
at
to
some
extent
the
result
of
the
failure
that
was
projected,
which
is,
if
we
don't
actually
solve
the
problem
in
IETF.
We're
going
to
see
is
that
vendors
are
going
to.
You
know,
fork
off
and
do
their
own
things,
and
you
know
the
most
successful
of
those.
W
Obviously
is
the
work
from
Google
for
doji
ribbing
company
and
are
the
problem?
Is
the
work
is
not
done
here?
We
don't
get
a
lot
of
no
say
in
the
matter.
It's
you
know
walking
dead
of
SNMP
returned
in
many
respects,
so
we
get
all
the
sins
from
that.
But
people
are
solving
exactly
the
problem.
Spaces
we
knew
were
need
to
get
to
be
solved
and
I
dress
people
are
doing
rip
programming.
Some
people
are
doing
fib
programming
with
different
models,
we're
getting
telemetry
via
very
various
streaming
things
and
lots
of
different
faces.
W
The
one
success
that
we
got
out
of
a
lot
of
that
is,
regardless
of
the
transport,
whether
it's
you
know,
thrift,
whether
it's
protobufs,
whether
it's
something
else
a
lot
of
people
have
actually
gone
down.
The
road
that
we
sort
of
pushed
them
to
which
is
gang
is
the
high
level
modeling
language
this
stuff
gets
done
in
so
that,
at
the
very
least,
the
models
can
you,
interchange,.
O
So,
with
most
of
your
comments,
you
know
I
agree
I
put
back
this
slide
on,
because
this
is
what
they
see.
What
was
the
value
coming
out
of
the
ITRs
I
still
see.
There's
you
know
a
lot
of
controller
agent
coming
forward
and
I
would
like
to
say:
let's
try
to
remove
that,
put
in
proper
software
layering
in
between
it
and
decide
whichever
framework
we
want
to
support
on
or
whichever
one
will
be,
the
juror
at
that
moment
that
can
be
easily
you
know
plugged.
On
top
of
that,
so.
W
X
Robinson
Cisco,
actually
going
back
on
Jeff's
point
I.
Think
in
terms
of
where
we
got
in
net
mod
with
Andy
and
MDA
architecture
was
we
almost
got
to
the
point
of
defining
what
you'd
need
for
ITRs?
And
then
we
didn't
do
this,
the
small
bit
at
the
very
end,
and
so
the
architecture
talks
about
how
you
would
do
a
dynamic
datastore,
but
doesn't
define
us
have
but
actually
defining
one
and
ideally
saying
how
does
the
data
merge
in
with
the
existing
one?
X
B
O
We
have
developed
bunch
of
models
that
people
will
not
implement
it
because
they
are
too
complex
and
too
big.
There
are
parts
of
the
models
that
are
being
implemented
and
are
being
used,
but
it's
a
very
minor.
You
know
part
of
some
of
the
models
that
are
being
used
and
it
is
the
idea
to
instead
of
trying
to
model
everything
under
the
Sun
trying
to
see
what
are
the
you
know
to
come
to
your
common
semantics
and
syntax
for
the
key
functions
and
services
and
say
here's
the
model.
O
O
O
You
know
so
there
I
have
to
know
too
many
rib
too
many
rib
models
and
then
too
many
fit
models
from
all
the
different
vendors
and
then
I
can
you
know
and
have
the
access
to
all
of
that
in
order
to
be
able
to
start
doing
things
like
that,
which
gives
me
a
much
better
overview
and
much
faster
ory.
What
is
actually
really
on
the
wire
versus
you
know
what
some
of
the
other
groups
are
doing?
O
I'm
also
a
little
bit
worried
that
we
are
so
pushing
forward
and
that
a
20
year
old
technology,
which
was
first
proposed
in
November
2002.
So
we
are
now
coming
to
the
70th
anniversary
of
a
saint
Iran
of
you
know
of
a
10th
year
of
technology
is
becoming
the
main
network
management
technology,
and
is
it
is
not
the
friendliest
programming
tool
we
have
moved
forward
and
I
would
like
to
see
us
being
more
flexible
to
those
new
tools
and
new
frameworks.
I've
been
saying
a
long
time.
B
O
So
I'm
just
trying
to
finish
something
with
regards
to
work
for
the
previous
presentation
and
for
the
dis
presentation,
I'm
planning
to
write
up
a
draft,
you
know
set
of
requirements
and
action
items
and
release.
It
know
before
the
next
ITF
meeting.
That
would
be
great
and
thank
you
for
presentation.
