►
From YouTube: IETF106-DNSSD-20191118-1810
Description
DNSSD meeting session at IETF106
2019/11/18 1810
https://datatracker.ietf.org/meeting/106/proceedings/
A
A
The
two
main
points
that
I
always
highlight
are
your
IPR
requirements.
So
if
you
know
about
patents
relates
to
this
stuff,
there
are
rules
that
you
need
to
follow
and
also
we
will
be
enforcing
the
ITF
code
of
conduct,
which
generally
covers
being
nice
to
one
another.
So
without
further
ado,
Christian.
B
We
have
a
lot
of
time
to
discuss
DNS
SD
privacy
requirement.
In
fact,
we
have
spent
a
lot
of
time
on
that
already.
The
I
started
this
work
and
dannielle
a
case.
I
came
to
work
with
me
a
couple
of
months
after
that
in
March
of
2016,
and
it
went
through
various
iterations
in
the
group
and
eventually
we
decided
cut
off
years
later
to
not
not
really
push
for
solution,
because
we
could
not
get
consensus
on
the
solution,
but
we
excised
from
the
proposal
of
a
solution.
B
The
analysis
part
which
was
basically
the
privacy
requirement
and
the
general
consensus
at
the
time
that
was
in
2018,
was
that
this
requirement
were
useful
because
it
was
interesting
to
be
stuck
in
the
ground
to
a
record
before
saying
hey
when
you
do
discovery,
and
especially
if
you
are
using
a
multicast
protocol,
whatever
it
is,
and
you
have
to
be
concerned
about
requirements
and
if
I
understand
correctly.
The
working
group
last
call
on
this
draft
is
almost
finished.
Our.
A
B
You
still
have
a
couple
of
days
to
explain
why
it's
great
and
we
should
we
publish
it
or
not.
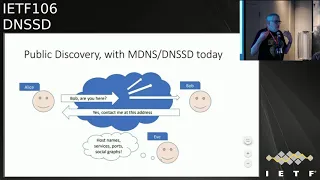
So
what
study
that
effort
is
that
when
mdns
genesis,
the
in
general
but
mdns
in
particular,
is
the
one
so
noisy
and
leaky
protocol,
it
was
done
to
be
in
quakes,
your
configuration,
etc.
But
the
use
of
broadcast
and
the
use
of
identifiers
in
the
broadcast
allows
people
to
track.
Who
is
doing
what
and
when
and
that
generally
a
bad
idea.
C
B
B
The
first
scenario
is
when
you
want
to
find
the
printer
or
when
you
want
to
find
a
fixed
device,
whatever
it
is,
and
in
that
scenario,
basically,
you
don't
care
that
people
discover
that
there
is
a
printer
on
the
network
because
of
course
there
is
a
printer
at
the
network.
But
what
you
do
care
is
that
it'd
be
better
if
you
did
not
identify
who
is
using
the
printer
at
what
time?
And
that's
that's
really.
B
The
requirement
there
to
give
an
example
of
how
mdns,
for
example,
doesn't
completely
meet
that
requirement
mdns
in
order
to
participate.
The
guy
was
doing
the
discovery
as
to
initiate
and
DNS,
and
to
do
that
they
have
to
broadcast
their
host
name
on
the
local
network
and
that
broadcasting
of
the
host
name
is
worth
tracking
you
so
that
it's
easily
fixed.
It's
not
hard
to
do,
but
it's
not
done
yet.
B
As
long
as
you
can
get
the
flow
of
messages
you're
going
to
identify
that
David
here
is
looking
for
stores,
laptop
name
and
and
finding
it
on
the
network
and-
and
you
can
discover
that
so
that
that's
the
kind
of
stuff
we
want
to
not
happen,
and
there
is
the
third
scenario
is
a
variant
of
that
with
wearable
devices.
If
you
have
wearable
devices
and
you
use
this
kind
of
discovery,
scenarios
to
send
broadcast
messages
to
find
them
and
to
initiate
communications.
B
B
And
so
these
are
basically
the
scenarios,
and
the
purpose
of
the
draft
is
just
to
delineate
those
scenarios
delineate
that
we
have
a
problem
and
effectively
get
that
on
the
record
to
commit
ourselves
to
fixing
it
later
or
by
whichever
ways
adequate
and
that's
pretty
much
where
we
are
and
and
basically
my
might
say,
hey
hey.
We
have
been
trying
to
bang
that
message
for
some
time
now.
Are
we
done
yet
I
mean?
Can
we
publish
it
and.
D
A
E
B
A
Yeah,
okay,
so
I
think
we're
gonna.
Let
the
working
group
last
call
go
until
the
end
of
the
week
and
or
I
forget
the
exact
date
that
it's
running
too,
but
so
sometime
I
think
either
end
of
this
week
or
next
week
and
see
if
we
have
any
anyone
speaking
up
before
then,
but
otherwise
I
think
we're
good
to
go
and
ready
to
submit.
This
is
G.
Ok,.
A
F
Daniel
MeeGo
Erickson
I
just
have
a
comment
regarding
the
first
scenario,
so
one
thing
is
concerned
how
we
make
the
discovery,
but
I'm,
looking
at
who's
become
being
connected
to
the
printer
is
another
thing
would
say
there
is
a
DNS
part
as
well,
even
though
you're
using
TLS,
maybe
you
can
sister.
This
IP
is
connected
to
that
one.
Sir.
Well.
B
You
will
know
that
someone
is
doing
a
TLS
connection
to
the
printer
and
hopefully
it's
a
TRS
connection,
and
it
doesn't
give
the
text
of
the
document
in
the
clear
of
it.
Okay,
you
will
know
it
is
a
printer
because
that's
not
a
secret
when
you
are
in
this
hotel
lobby
and
they
have
a
print
of
all
which
you
use
it's
there.
You
know
it's
there,
that's
you're
not
trying
to
hide
the
fact
that
there
is
a
printer.
B
What
you
want
to
not
disclose
is
who
exactly
is
using
the
printer,
so
suppose
that
you
are
using
say
MAC
address
randomization,
so
you
cannot
be
identify
your
MAC
address
or
by
your
IP
address.
You
want
to
not
have.
The
discard
protocol
is
speed,
art
identifiable
information,
racket
like
a
host
name
or
something.
A
All
right,
I
think
we're
then
ready
to
adjourn.
We
heard
may
have
beat
a
record
in
terms
of
shortest
ITF
session,
ever
congratulations,
everyone
and
we
will
hopefully
be
seeing
a
lot
of
you
in
Vancouver,
but,
most
importantly
on
the
list
before
then
for
those
of
you
that
haven't
read
this
draft,
please
find
it
in
your
heart
to
do
so.
Maybe
on
your
plane,
ride
home
and
even
if
your
email
just
says
yes,
this
is
fine.
This
helps
reassure
us
and
the
ADEs
that
this
document
is
ready
to
move
forward.
