►
From YouTube: IETF106-DOTS-20191122-1220
Description
DOTS meeting session at IETF106
2019/11/22 1220
https://datatracker.ietf.org/meeting/106/proceedings/
A
So
shall
we
start
hello,
everybody,
its
dot,
walking
group
session
and
I'm
sure
everybody
is
tired.
It's
the
last
session
of
the
week,
but
let's,
let's
concentrate
so
first
I'm
your
your
speaking
here
today,
because
Frank
worked
so
hard
that
she
caught
it
cold
and
get
most
his
voice,
so
I
think
I
think
he'll
recover.
Wish
you.
A
B
A
B
A
A
So
or
group
draft
status,
so
from
the
last
meeting
we
have
some
progress
on
the
signal
channel
draft.
It
got
stuck
for
quite
a
long
time
with
disgust
from
transport
area
and
director,
but
recently
there
is
some
progress
and
there
were
some
suggestions
from
Carsten
Borman
and
just
they
were
accepted
by
the
draft
authors.
So
I
hope
the
draft
will
be
progress
after
that
and
it
will
be
discussed
today.
A
A
Dirtiest
cases
and
dot
architecture
that
have
already
been
sent
to
ICS
are
waiting
for
our
ID
to
review
it
review
them
and
to
move
them
further.
So,
overall,
there
is
some
good,
a
mountain
of
TVG
in
the
working
group
since
the
last
session,
so
our
agenda
for
today
we
have
several
presentations.
I,
think
that
will
start
the
coding
well
any
button
about
agenda.
Any
suggestions.
C
I'm
kinda
mean
she's
got
from
NTT
communications.
This
weekend,
I
joined
the
IETF
hackathon.
Then
I
did
things
about
the
territory.
Then
the
target
was
territory
draft
written
by
Tyrion,
meadow
and
other
members.
Then
the
target
was
target
target
was
preliminary
implementation
and
POC
of
Daughtery
Matauri.
However,
I
found
at
that
time
that
there,
the
draft
needs
a
lot
of
clarification,
so
I've
tried
it,
but
at
most
the
most
works
at
that
time
was
a
design
review
of
dots.
Telemetry
think
I
just
be
summary
of
design
of
the
parameter
II.
C
That
purpose
is
giving
the
maximum
capability
of
conveying
normal
and
attack
traffic
really
related
metrics
as
a
hint
Roma,
dot,
client,
server
and
server
to
dock
quiet.
So
the
timing
of
geometry
can
be
divided
into
two.
These
two
timings:
first,
one
is
pre
mitigation
and
second
one
is
post
mitigation,
so
other
primitive
Asian.
What
is
the
prim
it
acacia?
So
the
division
of
limitation
telemetry
is
here
limitation.
Resources
are
not
bound
to
any
mediation
request
because
it
is
before
mitigation
any
before,
which
is
a
request.
So
you
are
new.
You
are
a
past.
C
Telemetry
is
defined
in
that
draft.
Then
the
first
2.0
telemetry
config
and
total
metrics
can
be
set
beforehand,
so
it
will
not
be
frequently
updated.
However,
I
found
that
attack
detail
can
be
updated
most
more
frequently
because
it
is
the
update
of
current
status
of
attacks.
So
my
proposal
is
separate
the
URI
path
of
them
into
two,
so
that
update
of
attack
detail
doesn't
always
require
configure
configuration
related
update
so
hit
the
proposal.
You
are
your
thoughts.
C
It
indicates
that
elemetary
config,
so
telemetry
config
includes
the
telemetry
coffee
itself
and
the
total
reacted
metrics,
like
baseline
of
the
traffic
and
capacity
total
capacity
from
viewpoint
of
dot
client,
so
get
delete.
We
work
with
like
this
written,
that's
right,
then.
Theoretically,
it
works
well
with
tcid
time
to
reconfigure
identifier.
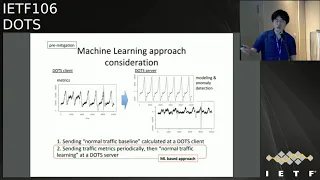
C
So
in
this
spec
I
dropped
the
attack
detail
then
DT.
This
will
be
in
the
separated
URL
path,
but
before
that
I'd
like
to
other
consideration
related
to
machine
learning,
applause,
machine
learning
approach
is
already
written
in
the
territory
draft.
However,
the
specification
current
specification
only
care
about
the
first
point
so
assigning
the
normal
traffic
baseline
status
coracle
created
at
taught
client.
However,
the
second
one
is
more
machine
learning
based
approach,
I
think
and
I
mean
if
you
use
the
Machine
growing
approach,
not
client
need
to
send
the
traffic
metrics
periodically
to
the
dot
server.
C
C
So
as
a
primitive
agent,
you
are
a
path
I
like
to
propose
the
normal
traffic
module.
In
addition
to
otaku
detail,
then
third
and
gate
undelete
will
be
used
for
conveying
the
current
information
of
attack
and
normal
traffic
from
dot
crier
they
now
get
under.
It
is
so
written
here.
However,
here
is
a
note,
so
if
the
agents
and
the
traffic
metrics
I
do
need
to
be
compared
with
other
approaches
like
the
IP
fix,
however,
I
think
those
metrics
is
worth
to
be
conveyed
in
dots
in
each
other
or
they
tutorial
get.
You.
D
If
we
are
relying
on
sending
traffic
metrics
periodically,
I
suggest
we
rely
on
existing
protocols
like
ipv6
IP
fix
and
not
reinvent
something
right.
The
only
reason
why
dot
signal
channel
was
picked
because
it
would
send
the
baseline
behavior,
what's
normal
behavior
of
the
traffic,
that
it
would
see
in
high
low
and
medium
person
profile.
But
what
if
it
is
supposed
to
send
traffic
or
performance
metrics
periodically,
then
we
should
be
using
other
protocols
like
ActiveX,
which
is
already
designed
for
that
purpose,
and
most
of
the
network
devices
support
IP
fix
already
right.
C
D
Yes
through
here,
but
it's
it's,
not
stopping
us
to
use
IP
fix
right,
I
mean
IP
fix,
also
uses
client,
server,
authentication
and
it's
pretty
much
the
the
dots
client
that
Connect
is
a
client
and
send
the
IP
fix
telemetry
back
to
the
zoo,
all
right,
I'm
going
to
say
if
it's
already
use
a
template
for
defining
the
telemetry
attributes,
the
network
attributes
and
the
template
can
be
easily
changed
on
the
fly
right.
Ip
fix
has
various
advantages.
We
should
not
try
to
reinvent
a
new
protocol
for
that.
C
B
C
B
C
My
point
so
thank
you
for
the
comment.
Okay,
then,
from
dadada
to
quiet,
the
doesn't
include
nominal
fee
because
our
tactical
will
be
needed
to
be
conveyed.
Then
I
also
proposed
separated
your
URL
path,
because
these
resources
are
worthy
of
observation
of
the
attack
pin
for
stored
in
the
server
side.
So
it
would
be
and
can
be,
also
used
for
a
synchronous
notification
to
DDOT
client.
C
Okay,
then,
now
here
the
some
scenario
for
you,
because
some
people
might
have
locations
that
why
server
to
client
attack
repo
in
pre
mitigation
stage
is
needed.
So
here's
a
scenario
where
DDoS
attack
happened.
Some
security
operation
center
at
the
but
grass
cry
and
sign
channel
did
something
going
wrong,
but
cannot
figure
out
which
idea
race
is
exactly
attack.
So
what
if
my
solution
is
what,
if
shock
at
the
dot
server
side,
can
convey
attack
details
to
the
dots
quiet,
then?
Finally
described
can
figure
out
which
one
is
attack,
so
then
it
can.
C
C
You
so
pops
past
mitigation.
Here's
a
brief
summary
of
communication.
Telemetry
Harkins
pick
is
enough
to
convey
those
parameters,
so
there
is
no
update
from
my
site
so
in
the
itraq
to
introduce
two
considerations.
So
first
one
is
about
the
percentile
calculation.
The
percentile
calculation
requires
the
piece
parameters,
so
one
needs
pimpy
period
of
time
and
second,
one
is
time
granularity,
and
so,
if
the
not
quiet
on
the
server
is
not
agreed
on
the
period
of
time
that
they
can
miss
configured,
so
they
should
be.
D
That's
a
good
one,
gonna
be
I,
think
I.
Think
that's
I
think
you
should
raise
a
comment
and
we'll
fix
it
as
an
issue,
and
we
will
look
into
that.
I
think
this
is
gonna,
be
really
useful,
especially
for
flash
drawer
attack
scenarios,
because
flash
Road
happens,
maybe
once
in
any
year
or
twice
and
giving
that
period
of
time
where
the
profile
was
generated
is
gonna,
be
really
useful
for
the
DDoS
mitigation
and
the
granularity
typically
is
probably
for
IP
fix
I.
Believe
it's
around
one
minute
to
five
minutes.
C
C
So
this
is
the
last
point,
so
I'd
like
to
do
a
brief
update
of
Interop.
So
actually
our
eye
on
the
gern
hobby
have
been
conducting
the
continuous
interval
testing,
so
we
found
several
bugs
on
both
sides.
However,
this
is,
must
be
a
good
new
stuff.
There
is
no
significant
issue
or
know
each
other
versions
38
and
the
data
channel
31
except
one.
C
However,
the
issue
found
in
here
was
already
at
the
rest,
so
next
version
we
cover
this
point,
so
there's
no
significant
issue
currently
I
think
then
yeah,
maybe
the
next
or
next
of
next
presentation.
We
may
mention
about
new
dot,
heartbeat
mekinese,
but
it
will
be
introduced
in
the
version
39
of
juvenile
child
rust.
Then
I
on
the
journey
are
waiting
to
test
the
version
39
so
as
possible.
So
it
will
be
a
report
back
to
the
working
group
after
that.
C
B
G
C
C
B
G
This
makes
sense
to
me
and
I
I
think
maybe
the
also
scan
considerately
and
also
do
by
using
the
machine
learning
approaches.
Do
you
have
some
preference
for
I'm
not
familiar
with
this
kind
of
technology,
so
I
don't
know
whether
the
information
need
to
be
trans.
Con
Vedas
is
like
common
or
kind
of
we
can't
standardized
it.
Maybe
you
can
offer
some
information
on
the
mailing
list.
Okay,.
C
G
D
I'm
not
opposed
to
a
machine
learning
approach,
but
what
I'm
trying
to
say
is
that
IP
fix
is
already
used
by
routers
and
DDoS
mitigation
systems
and
he
dose
detectors
for
baselining
and
profiling.
I
think
we
would
want
to
leverage
an
existing
protocol
and
not
reinvent
something,
because
this
has
been
already
done.
There
are
products
in
the
market
which
take
IP,
fixed
data
and
do
analytics
on
that.
I
can
name
few
of
them,
but
our
borders,
your
adware,
does
it
so
most
of
the
reader
education
providers,
who
are
doing
it
for
doing
that.
D
C
D
Hmmm
have
added
explanation
on
multiple
IP
addresses
that
could
be
returned
by
the
DHCP
server
so
that
it
can
act
as
a
both
primary
and
secondary
servers
in
case
if
the
parameter
cannot
be
reached.
Dot
signal
general
already
discusses
happy.I
pulse
mechanism
for
establishing
communication
with
dot
server,
so
the
trap
does
not
go
into
details
on
how
to
establish
communication
with
dots.
D
D
A
D
Yeah
you
think
working
on
this,
for
the
last
I
mean
trying
to
follow
up
with
the
custom,
inform
this
and
bairn
and
others
for
this,
because
we
were
not
sure
what
is
the
alternative
mechanism.
But
in
the
last
few
weeks
we've
made
significant
progress
on
this
thanks
to
all
the
help
from
Karsten,
especially
so
just
a
quick
recap
on
what
happened.
Right
I
mean
the
draft
was
approved
by
all
the
icig
members,
but
the
transport
ad
major
had
an
objection
to
the
way
we
were
using.
D
We
thought
that
this
would
send
back
to
the
client
and
the
reason
we
had
picked
ping,
but
it
was
under
the
full
control
of
the
dots
application
by
both
the
dots,
client
and
server,
and
we
had
a
very
vanilla
behavior
what
the
client
was
acting
as
our
client
and
dot.
So
was
acting
as
a
web
server,
and
our
transport
ad
had
objections
to
that,
and
we
were
not
sure
what
the
alternative
approach
could
be.
Why,
but
the
recent
introduction
with
caution
and
the
co-op
liability
co-op.
D
We
will
be
looking
into
indicated
that
the
dots
client
can
behave
as
a
quiet
light
and
it
can
act
as
both
client
and
server.
Similarly,
the
server
can
also
act
as
a
client
at
servers,
so
it
means
that
the
dots,
so
we
can
now
say
it
refers
back
to
the
client
and
the
client
can
now
respond
to
requests
coming
from
the
server.
So
with
that
in
mind,
it
was
pretty
evident
that
we
could
easily
move
away
from
the
confirmable
co-op
messages
to
dots
level
non
comfortable
messages.
D
So
that's
the
reason
we
picked
put
and
the
other
reason
was.
The
peer
heartbeat
status
is
a
good
way
of
indicating
back
to
the
peer
dots
agent,
whether
a
heartbeat
requests
are
coming
from
the
peer
agent
or
not.
So
that
way,
the
peer
agent
could
basically
change
the
way
change
the
frequency
with
which
it
is
sending
heartbeat
request
to
the
to
its
beer.
D
Medication
request
today
already
follow
the
the
transmission
guidelines
defined
in
RFC
8:08
five.
So
if
the
round-trip
time
is
not
known,
then
medication
requests
are
not
sent
more
than
three
3
seconds
power.
Just
only
one
mitigation
request
is
sent
further
three
seconds
so
with
that
we,
the
dots
medication
requests,
do
not
need
to
follow
the
probing
rate,
and
they
would
continue
to
follow
the
message
transmission
guidelines
given
in
RSA
it's
zero
at
five.
D
But,
however,
for
the
dots
heartbeat
requests,
we
wanted
to
make
sure
that
it
follows
the
probing
rate
that
was
defined
in
the
choir.
So
what
we
have
done
is
we
have
come
up
with
a
couple
of
algorithms
to
define
what
would
be
a
reasonable
probing
rate,
assuming
we
want
to
send
the
probing
rate,
at
least
every
30
seconds,
for
both
liveliness
checks
and
to
keep
the
net
banding
alive.
D
E
Pinkie
luck.
So
can
you
go
back
to
the
previous
slide
please
so
I
just
want
to
double
check
here
we
have
this
new
text
which
is
talking.
You
must
not
apply
other
congestion,
control
checks
and
I.
Think
from
what
you
were
saying
when
you're
talking
about
that
that
you
know
we
have
some
exterior
limit
about,
you
know
you,
you
can't
send
more
than
one
of
these
every
three
seconds
to
certainty
mitigation
requests.
Yes,.
D
E
D
D
And
then,
and
internally
right
beyond
the
way,
the
hardwood
messages
are
exchanged
the
way
or
the
client
and
server
logic
would
be
there
to
make
decisions
with
regard
to
the
heartbeat
missing
number
of
heartbeats
allowed,
or
there
won't
be
any
change
in
that.
So
it's
mostly
a
change
with
regard
to
the
negotiation
of
heart
probing
rate,
but
the
interval
lying
implementation
for
detecting
whether
the
pair
is
alive
or
dead
is
not
changing.
With
this
approach
and
and
thanks
to
all
the
feedback
and
the
help
we
got
from
Canada
and
John
I.
D
Think
some
initial
testing
shows
that
this
new
mechanism
is,
you
know,
is
working
and
we
believe
this
issue
is
resolved
and
we
already
sent
a
mail
too
much
already
and
probably
review
from
our
ad
and
chairs
would
help
us
to
progress
this
and
from
the
working
group
as
well
to
quickly
close
this
issue.
Just
codification.
A
A
E
Do
right
so
I
have
been
talking
to
Maria
throughout
this
week
about
you
know
the
proposed
changes
and
how
they
were
looks
I
believe
that
she
should
be
able
to
rebound
soon
and
then
because
we
did
make
some
fairly
big
changes
to
how
things
work
as
a
result
of
the
isg
review.
I
think
it's
probably
a
good
idea
to
do.
Just
like
a
short
one
week.
Working
group
last
called
on
the
changes
you
know,
since
the
the
31
I
think
is
what
we
did.
E
A
A
D
D
So
what
we
have
done
is
we
have
addressed
all
the
comments
received
between
zero
one
zero.
One,
zero
four
actually
addresses
all
the
comments
received
from
the
working
group
and
it
also
integrates
the
integrates
the
work
that
mailing
has
been
doing
in
her
other
draft.
So
we
have
discussed
often
with
her
and
pieces,
which
was
which
we
all
wish.
D
B
A
You
know
from
a
fellow
I:
have
the
Murphy's
the
same?
Don't
well.
My
doubt
is
that
you're
using
signal
channel
for
transferring
additional
information,
but
in
case
enough
of
attack,
signal
channel
will
probably
be
saturated
and
mitigation
requests
is
much
more
important
information.
So,
if
you,
if
you
add
an
additional
bender
ease,
if
you
use
a
signal
channel
for
transferring
more
informations,
are
probably
more
important
request
to
mitigate
an
attack
will
get
lost
so
yeah.
D
So
it
need
not
be
tied
to
the
mitigation
request,
because
that's
the
most
critical
one,
the
bit
the
normal
during
peacetime
I,
think
we
can
send
the
dots,
telemetry
Iser
using
the
signal
or
data
channel.
That's
not
the
problem,
but
during
at
that
time,
when
you
have
lots
of
attack
traffic
coming
and
the
link
is
saturated,
the
only
way
you
can
convey
their
attack
details
is
using
the
signal
channel
and
we
don't
have
an
option
of
using
the
data
Channel.
D
So
this
is
something
that
we
have
updated
to
the
draft
to
discuss.
The
draft
was
previously
focusing
mostly
on
bandwidth,
consuming
attacks,
but
nobody's
we
see
a
large
increase
in
resource
consuming
DDoS
attacks,
so
we
have
added
various
baseline
behavior
with
regard
to
resource
consuming
itaú
attacks
that
the
client
can
signal
to
the
server
it
could
include.
Various
parameters
like
max
number
of
simultaneous
connections
are
allowed
to
the
target
max
number
of
simultaneous
candidate
conditions
allowed
to
the
target
server
per
client
in
case
if
a
client
is
bombarding
the
server
with
various
DDoS
attack
connections.
D
So
this
these
parameters,
just
because
the
max
number
of
requests
allowed
per
second
to
the
target
server
max
number
of
requests
allowed
per
second
to
the
target,
server
per
client
and
the
max
number
of
partial.
It
was
a
lot
per
second
to
the
target
server
and
the
max
number
of
partial
requests
allowed
per
second
to
the
target.
So.
D
Attack.
Details
had
received
several
feedback
from
the
working
group,
especially
with
regard
to
that
add
details
being
signaled
from
the
dot
server
to
client,
which
was
not
there
in
the
original
draft,
and
we
have
updated
to
add
that
with
an
example
on
fight
that
would
happen
just
like
an
app
I
had
explained,
and
we
have
also
updated
the
attack
details
in
very
similar
way
that
products
use
it
today.
D
One
of
the
important
parameters
that
was
added
is
whether
the
top
duck
that
is
a
spoofed
IP
address
or
not.
If
it's
a
spoofed
IP
address,
you
cannot
put
an
ACL
rule
and
block
the
traffic,
because
that
would
penalize
legitimate
traffic
right.
Imagine
somebody
using
a
tornado
date
to
send
Tina
spoof
responses.
D
D
One
of
the
major
questions
I'm
in
the
comments
that
has
that
we
have
not
yet
addressed
is
where
do
we
draw
the
line?
Basically
right,
especially
during
the
attack
time.
We
know
certain
attributes
can
only
be
set
using
tor
signal
channels,
but
now,
during
the
piece
time,
do
you
want
to
use
the
dot
signal
channel
or
do
you
want
to
use
the
dot
status
channel
right?
D
We
just
picked
on
the
dot
signal
channel,
because
tor
signal
channel
also
are
those
confirmable
messages
and
co-op
is
also
used
nowadays
for
configuration
purposes.
So
whether
we
want
to
use
dots
signal
channel
during
the
piece
time
for
sending
the
dots
telemetry
is
a
question
for
the
working
group
and
I
think
both
the
protocols
can
do
the
job
here.
G
B
A
F
Thank
you,
I
mean
you
hear
her.
She
from
entity,
so
I
will
show
a
use
case
of
the
state
tournament.
We
use
case
name
it
if
she
use
of
DMS
based
on
track
boundaries.
This
is
somebody
of
presentation.
We
carried
out
Pio,
she
about
efficient
use
of
DMS
based
on
bandwidth,
and
we
assess
that
adopts
enemy.
Terrific,
especially
yeah
mojo
created
a
top
talker
and
bad
Willis
I
can
be
applied
in
the
use
case.
F
I
want
to
explain
this
scenario.
Orchestrator
carries
out
some
process
a
fast
receiving
attack
report,
unchecking
the
duplication
and
register
the
boundaries
of
two
double
floats
and
check
available
available
capacity
of
DMS
and
a
check
mixer.
This
IP
is
the
email
service
subscribers
wrong
and
then
okay,
sorry,
the
direct
attack
row,
two
DMS.
If
so,
DMS
available
capacity
is
more
than
at
this
IP
broadband
with
Alvida
Orchestrator
redirects.
All
of
this
IP
road
to
a
better
with
TMS.
On
the
other
hand,
demon
cerebral
capacity
is
destined
at
this
type
across
boundaries.
F
Orchestrator
dialect
to
topple
rows
of
top
talker
preferentially
and
network
operator
can
use
available
capacity
of
demons
in
T.
By
using
this
scenario,
and
we
assist
that
kind
of
traumatic
can
be
applied
to
the
use
case,
lift
figure
is
shows.
This
region
shows
that
I
am
Mojo
related
to
top
topper
on
path.
Wheels
on
the
right,
one
is
a
low
Robo.
Orchestrator
assertively
is
a
young
module
related.
The
top
talker
and
panelists
can
be
applied
to
the
use
case.
C
From
NTT
communications,
one
clarification
question,
so
you
need
the
bandwidth
information
of
couple
of
th,
IP
and
source
IP
rights
address
right.
So
sorry,
back
to
the
previous
yeah
that
one.
So
in
order
to
convey
that
information,
you
will
use
the
pre-initiation
module
because
it
only
includes
a
target
IP
source
IP
address.
Subject
right,
so
yes,
that's
right,
yeah,
so
attack
detail
is
not
enough
because
it
only
includes
Disney
IP
address,
also
your
source
IP
address.
Yes,
thank
you.
D
C
C
E
Benkei
doc,
so
I
me
on
the
slide.
It
talks
about
the
tuple
of
the
source
and
destination
IP
addresses
and
then
Konami
was
just
talking
about.
Maybe
you
have
the
source
prefixes.
So
do
you
have
a
sense
for
how
much
coalescing
there
is
between
source
IP
addresses
of
the
attack
into
having
just
a
source
prefix?
Because
if
we
need
to
always
send
the
source
IP
address,
then
it
might
be
a
very
large
amount
of
information.
That's.
F
D
If
it's
a
large
scale,
II
decided
it
would
be
a
group
of
source
prefixes
that
would
be
launching
and
they
would
be
the
top
talkers,
it's
very
difficult
to
identify
just
10
top
talkers,
who
could
basically
bring
down
a
large.
So
basically,
so
it
has
to
be
a
group
of
thousands
of
malware
which
are
coordinating
America
and
of
an
attacker,
and
that
would
be
a
prefix
range
coming
from
a
specific
geography,
because
malware
is
typically
start
with
a
specific
geography
and
then
they
move
across
to
other
geographies.
So.
F
G
I
want
to
say
that
the
use
case
for
is
a
taught
elementary.
Such
work
is
very
useful
and
to
validate
whether
that
ultimate
Elementary's
are
needed,
or
complete
and
I'd
like
to
raise
another
discuss
or
use
case
about
how
telemetric
can
be
used
for
imaging.
We
discussed
the
way
that
you
use
a
signal
channel
at
for
telemetry
at
the
attack
time.
So
at
the
attack
time,
the
both
signal
channel
and
a
channel
may
first,
a
channel
won't
work
as
we
designed
it,
and
the
signal
Channel
may
or
may
also
can
not
be
useful.
B
D
If
you
see
the
telemetry
right,
telemetry
can
be
stills,
and
during
the
peacetime,
for
example,
the
baseline
and
the
capacity
one
like
we
discussed
in
the
raft
can
be
sent
during
the
plea
statement
as
a
recommendation.
If
the
text
is
not,
there
definitely
add
that,
but
the
recommendation
is
to
threaten
the
baseline.
Do
your
traffic
and
the
capabilities
of
the
dots
over
like
how
many
connections
it
can
and
all
that
can
be
sent
during
the
peace
trip.
D
G
F
B
Actually,
as
a
chair,
yes,
it's
a
good
good
thing
to
do
when
card
you,
you
sorry,
but
if
you
really
want
to
propose
use
case,
please
be
quick
because
we're
already
on
the
dock
on
the
track
on
the
solution
draft
and
actually
they
are
also
included
some
use
cases
in
the
a
solution
draft
so
we'd
like
to
see.
Is
there
any
differently?
Okay,
you,
your
scales
for
your
side
or
you
have
the
same
concern
with
the
current
solution.
So
if
more
quickly
is
better
okay,
yeah.
D
Till
here,
I
agree:
I
think
we
need
it.
We
need
to
list
all
the
possible
use
cases
so
that
we
can
basically
go
back
and
check
if
the
dots
telemetry
is
meeting
those
use
cases
or
not,
and
unfortunately
the
original
dots
use
cases
does
not
talk
about
perimetry.
So
we
definitely
need
a
dots
use
case
for
telemetry.
Well,
as.
A
A
chair
since
that
it's
probably
was
to
st.
if
to
include
use
cases
in
the
telemetry
dropped,
because
it's
always
easy
for
reading
it
to
first
look
at
these
cases
and
then
look
at
the
solution.
It
depends
on
the
number
of
use
cases.
Probably
we
need
to
judge
whether
we
need
a
separate
document
or
just
include
an
additional
introduction
sector
section
describing
common
use
cases
for
the
tonight
rain.
Yeah.
A
A
A
E
Benkei
dock
yeah,
so
I
was
actually
looking
at
the
Charter
yesterday
or
the
day
before.
Thinking
about
the
new
milestones
and
I
agree
that
we
should
have
a
little
bit
more
clarity
in
the
Charter
about
what
we're
working
on
right
now,
it's
a
little
bit
ambiguous,
so
I
think
it's
probably
worth
going
forward
with
the
recharter.
