►
From YouTube: IETF106-SPEAKER-20191121-1215
Description
SPEAKER meeting session at IETF106
2019/11/21 1215
https://datatracker.ietf.org/meeting/106/proceedings/
A
Are
you
ready
to
start
or
we
wait
we'll
start
exactly
on
time
for
minutes
or
do
you
want
to
start,
or
you
know,
I
think
most
of
the
people
are
here,
so
we
will
get
it
going.
Is
that
okay
yeah?
So
thanks
all
for
joining
during
lunch,
so
my
name
is
Wayne
Hendrix
and
I
will
be
co-presenting
with
Bryan
and
Risa.
We
will
do
also
a
piece
of
the
talk,
so
the
goal
of
this
presentation
is
mainly
to
talk
about
5g
and
the
impact
on
the
networking
side.
A
So
5g
is
much
bigger
than
what
we
are
going
to
talk
about
in
general,
but
we
try
to
focus
on
this
presentation
on
mainly
the
impact
on
the
networking
side
of
what
5g
is
about,
and
that's
going
to
be.
The
main
focus
of
the
talk,
okay,
just
to
introduce
5g,
because
5g
means
many
things
to
many
people
and
I.
Typically,
the
way
I
try
to
explain
it.
If
you
try
to
summarize
it,
you
see
that
it
can
be
summarized
in
like
three
big
buckets
right.
A
One
is
actually
getting
more
bandwidth
to
end
subscribers
such
that
we
improve
the
band
to
it.
Get
more
speeds
make
sure
that
video
is
consumed
much
faster
onto
the
network.
The
second
thing
is
kind
of
more
connectivity,
so
more
IOT,
more
devices
which
are
getting
connected
to
the
network
and
the
third
elephant
in
the
room
is
kind
of
industry
24.0,
as
we
call
it,
which
is
introducing
new
concept
like
very
low,
latency,
ultra
reliability
and
so
on
and
so
forth,
and
that
has
a
rather
dramatic
impact
on
how
networks
will
be
built
going
forward.
Okay.
A
Now,
if
you
then
look
if
these
are
like
applications
or
like
use
cases
which
are
all
going
to
become
relevant
for
a
set
of
people,
the
second
big
aspect:
what
we
see
is
that
the
way
we
are
implementing
some
of
those
applications
or
devices
which
are
actually
consuming
or
actually
delivering
some
of
these
services.
There
is
also
a
big
shift
right,
so
we
used
to
things
via
physical
devices.
They
were
all
set
together.
It's
an
appliance
all-in-one.
A
If
you
look
going
forward
on
what's
happening
with
NFV
and
virtualization,
you
see
that
we
started
introducing
quite
a
lot
of
virtual
machines,
but
in
the
mean
time
we
talked
about
micro
services.
We
talked
about
containers,
but
we
already
I.
Some
people
are
talking
about
function,
so
it's
no
longer
something
which
you
can
physically
touch
right.
So
as
a
result,
you
see
that
in
order
to
define
and
build
the
network
around
these
things,
you
actually
have
a
very
heterogeneous
environment
to
deal
with
right.
A
So
that's
the
second
big
thing
to
take
into
account
and
then,
of
course,
people
want
to
introduce
things
faster,
wants
to
make
sure
that
things
happen
much
more
quickly,
that
it's
much
more
agile
and
that's.
We
come
into
the
realm
of
programmability
automation,
intent-based,
networking
and
so
on
and
so
forth.
So
we
want
to
make
sure
that
I,
some
of
these
services
get
more
I
delivered
more
quickly
like
basically,
the
big
guys
or
the
the
big
web
guys
are
doing.
A
Is
the
introduced
services
much
more
quickly
and
much
more
faster
into
the
network
and
make
sure
that
I
things
get
consumed
way
faster
than
we
used
to
see
a
going
forward
right?
If
you
put
this
all
together
and
trying
to
build,
let's
say
a
framework
or
an
architecture
around
this,
it's
kind
of
a
big
thing
right,
because
you
see
that
there
is
lots
of
changes,
lots
of
things
are
happening
and
what
we
try
to
do
with
it.
A
Okay,
I,
say:
okay,
if
you
look
at
all
of
this
environment,
how
do
we
deal
with
all
of
that
right
and
I
think
this
is
where
I
template
I
think
they
built
important
concept
from
the
early
days
and
and
if
you
look
at
it,
we
actually
in
order
to
build
like
a
network
infrastructure
to
support
all
of
this.
We
believe
that
is
two
key
principles
which
are
important
to
keep
in
the
back
of
our
minds.
A
It's
important
to
basically
provision
it
at
the
edge
and
leave
the
core
or
the
elements
in
the
middle
untouched
right.
So
we
always
say:
okay,
introduce
the
service
at
the
edge
and
try
to
build,
make
sure
that
the
the
the
elements
in
the
middle
are
not
touched.
When
you
provision
new
services
right
and
as
a
result,
you
actually
get
a
more
easy
way
of
introducing
things.
A
So
we
see
containerization
and
stuff
like
that.
So
you
see
that
the
edge
implementation
in
a
5g
or
in
a
network
going
forward.
It's
know
something
which
you
can
touch
necessarily
right.
So
we
have
I.
Here
are
some
examples.
Like
physical
devices,
we
used
to
have
edge
routers
right,
which
are
routers
built-in,
chesties
or
in
pizza
boxes.
A
You
see
going
forward
that
some
of
these
implementations
would
happen
on
the
data
center
switch,
which
is
acting
as
a
top-of-rack
type
of
thing,
or
you
actually
do
it
on
a
peering
type
of
device,
but
an
edge
can
also
be
like
a
virtual
thing
or
in
a
micro
services
architecture.
It
can
be
like
a
user
brain
function
sitting
on
a
server.
It
can
be
a
virtual
switch
implemented
on
a
server
or
it
can
actually
also
be
like
virtual
switch
implemented
on
a
nikkie
going
forward.
A
So
you
see
that
the
environment
which
we
are
having
available
to
us
in
order
to
connect
all
of
these
things
together
is
a
big
I.
There's
there's
quite
a
lot
of
variety
right.
The
second
big
question
is,
and
here
is
there
is
Automation-
is
it's.
Where
is
the
X
right?
We
used
to
build
the
H
in
a
fairly
central
matter,
but
you
see
that
with
this
ultra-low
latency-
and
this
is
of
course
a
use
case,
and
given
that
we
are
a
finished
company,
we
have
to
have
a
finished
example.
A
You
see
that
if
you
distribute
the
application
closer
to
the
user
without
distributing
the
edge
you
actually
don't
achieve.
Anything
you
actually
introduce
bigger
latency
right.
So
you
see
is
that
the
edge
itself
will
vary
depending
on
the
use
case
as
well.
So
it's
no
longer
something
which
is
fairly
central
in
a
typical
deployment.
A
Now,
if
you
look
at
the
typical
network-
and
this
is
what
the
talk
is
all
about-
so
typically
we
segment
I
networks,
but
and-
and
this
is
mainly
a
service
provider
or
an
access
provider-
type
of
use
case
use
you
segment,
the
network
from
I,
typically
access
aggregation
core,
and
then
you
have
like
I
central
data
centers,
which
can
be
let's
say,
localized
data
center
or
private
clouds.
But
you
can
also
see
that
some
people
move
to
public
cloud
type
of
infrastructure,
so
it
can
actually
be
a
very
heterogeneous
environment.
A
Plus
you
see
that
going
forward,
you
see
those
edge
clouds
also
appearing.
So
if
you
look
there,
you
see
that
there
is
much
more
distributed.
Clouds
and
those
are
not
like
a
typical
data
center
going
for,
but
they
are
actually
like
very
small
contained
type
of
server
environments,
which
can
be
deployed
either
on
Prem
or
somewhere
deeper
into
the
network
than
we
used
to
see
right
now.
A
If
you
then
make
a
connotation
of
where
the
edge
is,
you
actually
see
that
it's
all
it's
spread
all
over
the
place
right
and
in
order
to
build
a
network
which
is
delivering,
let's
say,
kpi's
and
delivering
services
and
to
end
with
ultra-low
latency,
but
also
reliability,
where
you
have
to
do
diverse
parts
into
the
network
in
order
to
deliver
such
a
service
or
optimize
for
latency
or
optimize
for
bandwidth
or
optimize
for
whatever
type
of
capability.
You
see
that
this
is
actually
a
very
difficult
space
to
deal
with
right.
A
A
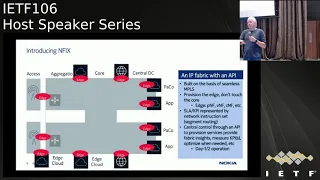
So
when
we
call
this
NFI
X,
which
is
standing
for
network
function,
interconnection
because
we
are
dealing
with
interconnecting
functions
either
distributed
or
central,
but
also
to
connect
them
in
a
way
that
you
can
connect
them
to
devices
which
are
either
physical
elements,
but
also
virtual
elements,
containers
or
functions
right.
So
it
doesn't
really
matter
what
it
is
about.
A
Okay
now,
how
does
it
build
and
we
are
not
going
to
go
to
a
lot
of
detail
given
we
only
have
45
minutes,
but
actually
this
is
built
all
around
ITF,
based
definition,
which
are
actually
here
right.
So,
first
of
all
the
way
we
we
look
at
this
as
we
use
like
multi-protocol
BGP,
for
a
data
plane,
so
we
have
either
a
VPN
or
IP
VPN,
so
we
can
do
both
IP
or
layer,
2
or
layer,
3
services.
We
can.
A
We
would
introduce
segment
routing
for
this
and
which
flavor
depends
on
the
choice
of
the
operator.
So
this
will
work
with
either
an
MPLS
flavor,
either
supporting
over
native
and
pillars
or
with
IP
or
with
as
our
v6
right
so
and
whatever
flavor
comes
available
to
us,
is
actually
capable
to
be
working.
In
that
framework,
we
use
p7
as
a
fee
to
actually
make
sure
that
we
have
capabilities
to
define
as
a
lays
and
KPIs,
depending
on
the
use
cases
which
will
be
supported.
A
So
in
a
nutshell,
before
I
give
it
to
Brian
what
we
are
trying
to
achieve
with
NF
IX
is
building
this
fabric
across
those
different
boundaries
like
aggregation,
core
or
whatever
workload.
We
see
and
give
you
a
single
API,
and
the
goal
of
this
is
to
give
the
same
experience
what
you
get
today
when
you
go
on
to
like
a
Google
or
an
AWS
or
a
Microsoft
or
Alibaba,
where
you
basically
have
a
set
of
api's.
A
You
define
your
requirements
for
your
applications
and
those
gets
instantiated
into
the
network
and
give
you
a
seamless
experience
using
certain
as
a
lace
kpi's
which
are
relevant
for
that
particular
service
all
right.
So
this
is
kind
of
giving
you
a
bit
of
a
space,
how
we
see
any
Vikes
and
what
it
I.
What
is
a
key
enabler
going
forward
to
build
this
very
heterogeneous
environment
in
in
the
future.
B
All
right
thanks
a
lot
wim
I'm,
going
to
take
a
step
back
now
and
see
what
we're
actually
trying
to
all
service
providers
are
actually
trying
to
achieve
with
5g
from
a
business
driver
perspective.
So
one
of
the
key
things
is
that
5g
is
meant
to
enable
a
whole
bunch
of
new
revenue
lines.
Although
we'd
like
to
focus
on
more
the
technology
piece
here
in
ITF,
this
is
really
the
key
focus.
B
So
when
you
look
towards
how
that
could
be
done
or
where
those
business
drivers
are
coming
from,
you
can
look
to
some
of
these
things
on
the
slide
here.
So,
for
example,
there's
a
huge
amount
of
promise
in
things
such
as
smart
cities,
eHealth
consumer
experience
with
augmented
reality
and
virtual
reality.
B
Public
safety
applications
connected
vehicles
and
critical
automation
and
service
providers
ultimately
want
to
play
a
role
in
the
space,
because,
ultimately,
all
of
these
spaces
are
being
increasingly
digitized
a
huge
proliferation
of
devices
in
each
of
these
applications,
and
so
this
is
a
great
market
for
service
providers
to
expand
into
from
a
pure
technology
perspective.
Ultimately,
we're
talking
about
all
the
different
IOT
devices
here,
all
the
different
connected
devices.
This
can
be
ultimately
made
a
huge
amount
of
additional
endpoints,
but
it's
also
driving
additional
bandwidth,
and
some
of
these
have
very
particular
latency
requirements.
B
Just
to
give
one
particular
example
there
so
I
mentioned
a
bunch
of
industry
vertical
applications.
This
is
just
one
to
illustrate
it.
Port
is
a
huge
and
increasingly
complex
environment.
If
you
look
forward
to
2025,
for
example,
just
looking
at
some
of
our
kind
of
lead
use
cases
here,
you
see
over
18,000-
oh
sorry,
18
million
containers
going
through
these
ports
or
a
given
port
per
year.
You
have
several
10k
trucks.
B
Moving
around
the
environment,
you
have
these
environments,
spanning
across
tens
of
thousands
of
hectares,
so
a
very
large
geographical
space
and
ultimately
they
want
to
bring
an
enormous
amount
of
technology
into
these
ports,
to
increase
the
level
of
automation
and
to
increase
the
order
efficiency
through
these
ports.
So
what
could
this
mean?
This
is
you
know
broadband
connectivity
for
ship-to-shore?
You
were
actually
at
the
port
to
the
ship,
video
surveillance,
all
across
the
port
itself.
B
Asset
tracking
of
every
individual
can
train
er
a
container,
so
we
can
actually
see
its
process
and
its
journey
off
of
the
ship
through
the
container.
You
need
to
have
low
latency
video
feeds
from
key
points
of
the
site
in
the
future.
They
want
to
have
things
such
as
augmented
reality
and
virtual
reality
based
maintenance
of
the
different
aspects
of
the
site,
so
they
can
pull
in
guys
remotely.
They
don't
necessarily
have
to
pull
drive
people
to
every
different
aspect
of
a
site.
B
We
expect
to
have
drones
flying
around
the
site
to
inspect
different
parts
of
the
facility.
You
have
autonomous
vehicles.
Moving
about
all
of
these
require
connectivity
and
there's
a
very
high
value
asset
and
then
also
there
are
people
moving
about
the
site,
so
we
need
to
know
their
exact
location
and
we
need
to
be
able
to
feed
all
the
necessary
information
to
them.
So
this
is
just
one
particular
example.
You
see
there
are
a
couple
of
ways
that
this
could
be
deployed.
B
It
could
be
a
private
5g
environment,
but
the
service
providers
also
look
towards
this
as
being
potentially
something
that
could
be
offered
as
a
network,
slice
or
multiple
network
slices
off
of
their
infrastructure
as
well.
So
just
just
one
illustration
here
to
show
the
the
kind
of
breadth
of
connectivity
required
to
support
such
an
application
or
such
a
use
case.
So
when
we
look
towards
how
we
can
actually
deliver
assure
these
SLA
s
across
a
transport
network,
we
look
towards
this
kind
of
closed-loop
automation
model
inside
Nokia.
We
refer
to
this
as
insight
driven
automation.
B
Ultimately,
what
is
this?
This
is
the
ability
for,
for
you
actually
to
automate
the
instantiation
of
services
in
your
network,
so
whim
spoke
about
this
kind
of
edge
to
edge
provisioning
and
then
the
ability
to
have
kind
of
network
or
application
based
optimization.
We
want
to
have
a
smart
IP
fabric.
This
is
really
based
upon
having
you
know:
segment,
routing,
based
capabilities
and
model,
driven
telemetry
to
be
able
to
program
an
extract
state
from
the
program,
configuration
and
extract
state
from
this
environment,
and
then
on
top
of
that
data
that
were
harvesting
from
the
network.
B
We
want
to
be
able
to
run
data
analytics,
and
we
see
this
closed-loop
automation
as
being
really
critical,
because
it's
not
just
about
provisioning
a
service
in
such
a
way
that
it
satisfies
an
SLA
in
one
moment
in
time.
It's
really
about
ensuring
that
SLA
is
met
throughout
the
entire
lifecycle
of
the
service
or
entire
lifecycle
of
the
application.
So
this
is
a
continual
process,
it's
actually
running,
so
we
can
actually
continue
to
reoptimize
some
react
based
on
the
latest
state
of
the
network.
B
So
just
a
couple
of
examples
of
this,
so
wim
spoke
before
about
the
edge
to
edge
connectivity.
This
is
one
particular
example.
Here
we
show
connectivity
being
created
between
two
data
center
environments
for
4-5
GS.
So
this
is
a
connectivity
between
virtual
RAM
and
virtual
core.
We
can
build
this
up
because
you
know
we
we
can
actually
harvest
and
extract
topology
information
from
the
network
using
things
like
BGP
LS.
We
know
about
end
points
within
a
BGP
based
data
center,
using
things
like
BGP
lu
and
from
a
controller
perspective.
B
We
can
actually
pull
together
at
apology
view
across
each
of
these
distinct
and
disparate
domains
and
between
those
two
end.
Points
in
this
example
actually
create
a
traffic
engineered
segment
erotic
tunnel
to
enable
that
productivity,
so
again
just
that
edge
to
edge
provisioning
and
kind
of
tunneling
within.
So
additionally,
if
there
is
a
if
there's
a
topology
change
there,
we
can
react
to
that
using
the
controller.
We
are
doing
this
in
such
a
way.
It's
actually
going
to
meet
the
the
different
SLA
constraints
of
the
service
right.
B
So
if
you
want
to
have
diversity
path,
diversity
between
these
two
endpoints
and
that's
possible,
or
if
we
move
towards
the
next
example,
you
want
to
move
to
something
a
little
bit
more
complex.
In
this
case,
the
SLA
characteristic
that
we
optimize
around
will
be
latency.
So
in
this
particular
case,
for
example,
we
stay
on
the
red
path
initially,
but
if
there
was
something
like
an
underlying
change
in
the
optical
topology,
maybe
your
optical
transport
network
had
a
reroute.
B
Then
we
observed
that
the
latency
changes,
because
we
harvest
that
information
and
enrich
in
response
to
that
we're
going
to
re
optimize
the
path
from
a
controller
perspective.
So
this
is
the
type
of
like
closed
loop
automation,
I'm,
referring
to
so
such
that
we
can
actually
continue
to
support
these
SLA
s
for
these
different
services
throughout
their
entire
lifecycle
and
at
the
outcome
of
this
we
have
this.
We
have
this
in
fix
fabric
that
wim
described.
B
We
have
a
controller,
that's
actually
enabling
and
securing
SLA
bound
services
on
top
of
it,
which
gives
us
an
ability
to
start
to
satisfy
these
networks,
licensing
requirements
for
each
of
those
different
applications
and
kind
of
business
drivers.
That
I
mentioned
at
the
start,
and
now
I'm
going
to
hand
over
to
Reza
who's,
going
to
talk
a
little
bit
more
from
an
API
perspective
in
network
slicing.
C
Hello,
everyone,
it's
a
good
point
to
go
to
the
networking
I
think
so
far.
We
discussed
how
we
can
create
a
network
which
is
consumable
without
by
Brian
mentioned.
What
is
the
characteristic
of
that
fabric?
What
are
the
use
cases
and
for
the
last
portion
I'm
going
to
tie
this
together
with
how
this
relates
to
network
slicing,
how
it
relates
to
us
or
ATF,
and
how
basically,
that
we
can
use
this
logic
to
create
Network
a
slicing
going
forward.
I
start
with
an
example
to
make
sure
that
at
least
we
are
on
the
same
page.
C
Let's
say:
I
have
an
operator
which
has
transport
it
has
on
the
left.
Side
is
group
of
tenants
or
customers.
It
has
Public
Safety,
Fiat
and
BMW.
These
are
the
customers
and,
on
the
right
hand,
side.
There
are
a
group
of
application
servers
when
we
talk
about
end-to-end
network,
its
loss.
Basically,
we
are
referring
to
the
logically
isolated,
independent
Network
from
left
to
right.
In
this
example,
for
a
take
their
last,
the
public
safety,
video
surveillance
CCTV,
we
are
creating
an
independent
network
from
left
to
the
right.
Each
of
this
network
is
slices.
C
C
Could
your
infotainment
in
the
car
could
be
your
gaming
console
and
on
the
right
side,
is
the
application
that
basically
serves
to
create
each
of
these
and
to
a
network
a
slice
again
I
go
back
to
the
last
one
which
the
CCTV
for
the
customer,
Public
Safety,
let's
say,
I
want
to
create
as
an
operator
I
want
to
create
this
into
a
network,
a
slice.
What
is
needed
to
be
done
in
the
network
from
very
high
level,
we
have
to
create,
ran
a
slice.
C
The
meaning
of
the
rangas
Ronnie's
life
means
simply
I'm
going
to
create
a
context
or
a
personality.
In
my
ran
equipment
to
understand
blue
green
red
Network,
a
slice
if
I
go
to
my
ran
I
will
see
the
resources
in
a
practical
way.
It
means
a
allocation
of
the
radio
interface,
a
scheduling
policy
profiles.
These
are
basically
allocated
for
each
of
these
colors.
C
By
the
same
token,
if
I
go
to
my
5g
core
I'm,
going
to
create
a
personality
or
context
for
each
of
these
n
2n
networking
slices
now
I
created,
ran
I
created
core
now,
I
have
to
do
the
connectivity
between
them
and
here
the
transport,
a
slice
come
to
the
picture.
Basically
transfer
a
slice
is
a
group
of
connectivity
with
a
specific
SLA,
slash
SLO,
and
this
is
very
important
to
understand
the
difference
between
they
determine
ology.
Sometimes
this
terminology,
the
is
important
to
be
very
clear.
C
Each
of
this
domain
has
one
controller,
but
I've
run
controller
I,
have
transfer
controller
core
controller
and
at
the
very
top
there
is
an
end
to
an
Orchestrator.
As
the
name
suggests,
Orchestrator
is
basically
orchestrating
a
group
of
actions,
a
group
of
logic
that
should
be
incremented
in
the
network,
the
term
a
slice
here
transferred
the
slice
or
ran
a
slice
or
chorus
slice.
Sometimes
it's
called,
for
example,
transport,
transport,
sub,
a
slice
or
try
for
a
slight
subnet.
All
are
basically
exactly
the
same
different
terminology.
C
C
The
second
observation
here
is
an
end
to
a
network,
a
slice
again
I
pick
on
the
last
one
that
dark
grey
enter
a
network
as
wise
can
have
one
or
more
than
one
transfer
a
slice,
meaning
I
can
have
a
group
of
connections
and
that
one
is
more
than
one.
So
we
want
to
make.
Another
observation
here
is
an
end-to-end
network.
A
slice
depends
on
the
application
here
we
are
talking
about
5g,
but
this
concept
is
well-suited
for
other
type
of
application.
C
For
a
slicing,
for
example,
if
operator
wants
to
share
the
networks-
or
we
want
to
do
the
DC
interconnect
I'm
referring
to
5g
here
as
a
prime
example,
but
keep
in
mind
that
this
logic
that
discussion
could
be
well-suited
for
all
other
applications,
so
I,
referring
to
the
last
word,
another
observation
about
the
number,
the
an
end
to
a
network.
A
slice
can
have
other
slices
here
when
you
say
coton
called
other
in
this
picture.
C
With
other
I
mean
ran
and
core
for
the
other
application
that
might
be
different,
so
in
a
summary
and
Antoinette
regrets,
Lars
has
won
on
many
transfer
slices.
It
might
have
other
slices
in
the
5g
that
other
a
slice
means
run
and
call,
and
the
important
aspect
here
is
the
only
context
for
the
entrant
is
at
the
very
top.
Any
other
context
that
you
see
here
they
are
not
into
it.
I
cannot
expect
transfer
to
be
an
to
I
ran
to
the
entrant
or
core
to
be
into
it.
So
this
is
basically
the
important
aspect.
C
It
should
know
exactly
how
many
Roenick
admit
you
know
it
wants,
because
it
know
that
how
big
the
city
is,
whether
or
not
we
should
create
visual
Network
function
on
the
ran
or
not.
This
is
the
decision
that
the
RAM
controller
make
at
that
point
also
for
the
core.
It
goes
that
do
I
need
to
create
a
core.
How
many
core
I
should
be
created
when
I
said,
could
miss
5g
code?
C
Do
I
need
to
create
any
visual
Network
function,
for
that
all
decision
will
be
made
by
the
correct
controller
and
at
the
end,
when
the
core
and
ran
are
created,
the
transfer
will
be
connected
and
end
to
a
network.
A
slice
for
the
Singapore
public
safety
will
be
created
will
be
exposed
to
that
customer
and
add.
There
is
a
at
the
end
that
a
slice
can
be
used.
The
last
observation
in
this
picture
is
a
tenant
or
customer
can
have
more
than
one
end-to-end
Network
espresso,
you
will
see.
Bmw
has
the
tree
of
them.
C
C
There
is
an
Orchestrator
sitting
at
the
top
again
depends
on
the
application.
If
it
is
not,
5g
is
other
that
could
be
higher
system
other
higher
controller.
But
in
this
context
we
have
end-to-end
there
Orchestrator.
What
does
it
do?
It
does
three
same
three
jobs,
automation,
monitoring
and
optimization
of
the
end-to-end
network
effects.
These
are
very
important
aspect,
because
in
most
cases
we
tend
to
talk
about
only
the
first
one.
C
We
talk
about
automation,
how
to
create
it,
everything
related
to
that,
but
at
the
same
time
we
have
to
be
really
conscious
about
talking
about
monitoring
assurance,
analytic
and
closed-loop,
optimization,
so
the
controller
or
Orchestrator
in
this
case
in
to
analyze
Network
as
West
controller
performing
these
three
jobs.
At
the
same
time,
it
talks
to
left
right
and
middle
controller
ran
core
transfer
controller.
C
To
basically
achieve
the
end-to-end
is
created
for
their
specific
networks
lies.
The
important
aspect
again
here
is
the
top
level.
It
doesn't
know
that
much
about
the
detail
of
the
network.
It
knows
about
the
abstraction
of
the
net
for
some
level
of
knowledge
of
the
network,
but
it
really
delegate
all
the
intelligence
and
everything
to
either
of
those
controller.
It
doesn't
know
how
rent
is
created
or
what
are
the
equivalent
in
the
ran
or
the
transfer
or
core.
C
You
do
your
job
if
something
happened,
try
to
resolve
it
to
controller
it
transport
controller,
for
example,
which
says
you
create
this
connectivity
and
it
doesn't
impact.
The
important
aspect
here
is
when
Orchestrator
that
we
just
go
to
the
next
was
the
interfaces
that
we
have
the
3gpp
on
the
left
and
right
in
the
middle.
There
is
no
standard
define
that
interface.
We
have
recently
form
a
new
design
team
in
his
working
group.
C
I'm,
not
encouraging
you
to
go
and
take
a
look,
the
material
that
we
have
their
mandate
and
the
vision
that
we
have
that
interface
and
everything
around
that
transfer
is
voice
controller
and
everything
where
the
logic
for
the
the
receiving
the
request
there
and
fulfilling
that
request
is
basically
will
be
addressed.
One
way
or
another
by
that
design
team
is
real.
Recently
they
have
the
meeting
and
not
everything
is
finalized.
But
this
is
that
my
opinion,
the
right
direction
that
we
go
coming
back
to
that
interface,
that
I
put
idea
that
interface
is
abstract.
C
That
interface
doesn't
tell
from
Orchestrator
to
controller,
go
and
create
a
transfer,
its
life
and
use
RSVP
for
that
tunnel
and
use
l3
VPN.
It
says
just
connect
endpoint
one,
two
three
and,
as
we
mentioned
Connect
age,
1,
2,
3,
2,
H,
4,
&
5,
my
SLA
is
10
Meg
and
I
want
to
have
a
full,
secure,
Network,
for
example,
that
interface
is
defining
the
connectivity.
This
way,
transfer
us
wise
controller
receives.
That
is
that,
for
the
automation,
part
I
have
to
do
something,
and
basically
for
monitoring
and
optimization.
C
I
will
talk
about
that
in
the
next
slide,
but
longer
story
short.
In
this
case
we
have
an
Orchestrator
sitting
at
the
top
and
controllers
and
I'm
encouraging
you
to
think
about.
I
will
give
your
answer
as
we
go.
You
might
think
how
the
hierarchical
controller,
or
whatever
we
do
at
ITF.
You
know
fits
here,
think
about
it.
We
will
get
back
to
the
question
in
a
moment
early,
but
I
just
want
to
make
sure
that
at
least
I
started
with
the
one
question
that
when
we
finished
we
have
the
answer
for
that
now.
C
I
remove
everything
from
this
slide.
I
just
keep
the
transferor
ice
controller
and
every
the
interface
on
top.
This
is
the
picture
that
we
have
if
it
comes.
This
is
the
picture:
I
have
transfer
of
ice
controller
in
the
middle.
Everything
else
is
removed
from
that
picture.
I
have
a
higher
system
again,
I
try
to
be
generalizing
the
concept
I
have
a
higher
system
in
5g.
We
call
it
into
a
network
of
ice
Orchestrator.
The
higher
system
sends
a
request
number
one
to
create
the
connectivity
again.
C
Connectivity
in
this
context
means
connect
age,
1,
2,
3,
2,
H,
4
and
5,
with
SLO,
10,
Meg
or
better.
We
again.
This
is
the
second
question
that
interface
should
not
only
have
this
information,
but
some
information
about
the
request,
which
is
correct,
for
example,
in
the
previous
example
for
this,
the
single
public,
safe,
there's,
a
customer
that
interface
one
has
information
about.
Who
is
the
customer?
What
is
the
service
services?
Cctv
customer
is
Singapore,
Public
Safety
and
some
other
information
about
that
end
to
a
network,
a
slice.
This
is
a
second
question.
C
We
don't
really
need
this
information
for
automation.
Why
we
need
that
one
I
try
to
get
back
to
you
at
the
very
end,
so
number
one
we
receive
a
request.
The
transfer,
a
slice
controller
intelligently,
is
going
to
realize
that
one
in
the
network-
and
this
is
basically
the
whole
idea
of
connecting
this
discussion
to
whatever
Beaman
Brian
mentioned
10
minutes
ago,
we
receive
the
request.
C
If
I
implement
this
connectivity
on
top
of
mantra,
wave
or
Path
number
one
is
do
the
connectivity
between
h1
h2,
h3,
2,
H,
4,
&
5,
so
number
2
basically
tie
together
the
concept
that
we
discussed
so
far,
weed
matting
the
request
to
any
service
tunnel
path
and
fix
will
be
one
of
those
that
we
can
use
and
basically
number
three.
We
realize
that
one
in
the
network
depends
how
we
want
to
do
it.
We
are
using
that
network
as
the
consumable
the
resource,
and
we
basically
we
are
reusing
the
API
to
create
a
connectivity.
C
I.
Ask
you
two
questions.
The
first
question
was
the
what
why
we
need
some
other
information
when
I
want
to
create
a
number
one
it
should
have
in
addition
to
endpoints
and
SLA
and
SLO.
It
should
have
some
other
information.
The
answer
to
that
one
is
number
four.
In
addition
to
creation
or
automation,
we
need
to
do
the
assurance.
We
need
to
do
the
monitoring
and
close
for
those.
We
need
to
have
some
information
that
how
this
transfers
was
basically
the
connect
to
the
end
to
a
network,
a
slice
which
customer
is
requesting
for
that.
C
From
that
aspect,
you
know
using
this
information,
basically
helping
us
to
do
that,
the
assurance
and
the
monitoring
and
optimization
of
the
transfer
slices
if
I'd
recap,
whatever
you
put
here,
we
have
at
the
bottom.
We
have
a
consumable
network
resource
now.
The
application
that
we
built
on
top
basically
is
going
to
use
that
resources,
and
basically
this
is
the
way
that
we
see
the
IETF
can
fit
here.
C
Number
three
is
exactly
whatever
IETF
has
lots
of
history
on
that
and
doing
number
one
and
two
and
number
four
is
basically
leveraging
everything
that
is
already
here
and
another
question
that
might
be
relevant
here.
Sometimes
there's
a
there's,
some
question
of
how
we
do
the
for
example,
surface
slicing
versus
how
the
fly
see
how
we
can
make
sure
the
resources
is
in
the
network.
C
All
is
related
to
number
three,
the
realization
do
we
need
any
specific
new
protocol
or
technology
to
achieve
number
three
at
this
point,
the
most
likely
answer
is
NIST
is
no,
but
as
we
go
forward,
this
is
basically
one
of
the
items
that
we
can
think
and
we
can
you
know,
address
going
forward.
So
this
is
end
of
the
presentation
for
us.
I
give
the
stage
to
we
to
basically
wrap
it
up,
and
we
have
I
guess
10
15
minutes
to
go
through
a
question
and
answer.
Thank
you
very
much.
A
A
But
we
are
trying
to
do
here
is
what,
if
you
own
an
infrastructure,
and
you
want
to
build
certain
KPIs
and
deliver
ubiquitous
services
across
those
heterogeneous
environment.
That
is
what
we
are
trying
to
achieve
within
fix
all
right.
The
third
bullet,
which
I,
which
I'm
saying
is
that
it's
built
on
all
ITF
standards,
which
are
actually
happening
here,
the
challenge
which
we
have
sometimes
it's
actually
people
I,
don't
really
know
which
pieces
fit
together
right.
So
we
decided
that
we
are
going
to
write
a
draft.
A
It
will
be
an
informational
draft,
so
if
people
are
interested
in
contributing
I
would
welcome
them.
So
please
contact
us
after
this
talk
or
something
like
that,
because
I
think
it's
important
that
it's
sometimes
I
important,
that
we
fit
the
pieces
together,
because
we
are
using
many
building
blocks
which
are
built
here
right,
so
we're
using
things
from
bears.
We
are
using
things
from
spraying
we're
using
things
from
net
mod
with
all
the
yang
definition,
models
which
are
delivered
or
being
built
in
different
working
groups.
A
If
you
see
how
easy
it
is
consumable,
their
networks
is
consumable.
This
is
where
we
should
go
towards
right,
so
we
should
basically,
with
a
few
point
and
clicks,
be
able
to
instantiate
those
capabilities
which
are
your
customers
demanding
and
doing
that
in
a
seamless
way
over
that
heterogeneous
environment,
and
this
is
kind
of
how
we
see
the
implications
of
5g
and
how
networks
should
be
built
or
the
capabilities
that
should
be
delivered
going
forward
to
achieve
and
to
deliver
those
type
of
use.
C
D
A
What
I
so
the
way
we
I
said?
The
question
is,
is
about
how
we
get
requires
from
operators
and
in
this
community.
So
right.
So
what
we
do?
I,
from
a
Nokia
point
of
view,
is
all
the
different
requirements
we
get
from
operators
we
try
to.
So
that's
how
we
contribute
to
draft
an
IETF,
and
so,
if
we
see
that
there
are
third
missing
pieces,
like
Raisa
mentioned
for
transport
slicing,
we
believe
that
is
a
missing
piece
for
a
service
abstraction
to
give
you
that
slice
and
transport
slice
controller.
A
We
build
a
contribution
into
the
various
working
group
in
order
to
contribute
and
make
sure
that
we
built
this
open
framework
to
support
this
type
of
thing.
So,
basically,
the
requirements
which
we
see
from
customers
we
bring
back
to
IDF
and
we
try
to
contribute
and
try
to
make
those
things
adoptable
or
change
depending
on
the
use
or
how
IDF
sees
this
adopt.
Based
on
the
the
feedback
of
the
working
group.
Here,
okay,
I.
E
Saw
on
the
slide
about
how
these
slices,
let
you
do
more
than
one
thing
at
the
same
time
on
the
network
or
different
comes
like
Fiat
and
BMW
could
both
use
the
same
network
and
what
I'm
struck
by
is
already
when
I'm
at
home
I
can
watch
Netflix
while
at
the
same
time
my
Tesla's
doing
a
firmware
update
because
I
have
an
internet
connection.
I
didn't
see
any
mention
of
the
Internet
in
this
presentation.
Is
this
a
totally
new
thing
to
replace
the
Internet
No.
A
So
this
is
actually
I
saw
ok.
So
this
is
a
good
good
question.
Actually,
if
the
Internet
is
good
enough
for
that
service,
we
use
the
internet
as
a
so
we
use
basically
the
Internet
connectivity
right.
So
it's
only
when
you
have
specific
requirements
which
cannot
be
met
or
which
are
like
certain
latency
requirements
and
stuff
like
that,
on
your
service,
delivered
on
X
wires
that
you
actually
do
or
change
things.
So
we
have
the
capability
to
influence
based
on
your
needs
of
that
specific
use
case.
F
So
in
your
ignorance,
one
of
the
slides,
you
showed
the
round
slice
and
transport
slice
and
the
cost
slice.
Yes,
then
you
said
essentially
the
leftmost
either
ends
or
mostly
from
3gpp
3G.
Does
the
run,
slice
and
da,
and
that
may
be
on
the
core
side.
Then
the
transport
slice
you
said
IDF
can
stand,
I
start
what
exactly
IDF
can
sterilized.
Is
it
just
the
provisioning
of
the
slice
or
what?
What
is
the
standardization?
That's
left
here,
whatever.
C
We
plan
to
do
idea
if
it's
I
encourage
you
to
take
a
look
at
their
outcome
and
the
result
that
we
have
on
their
teaser
in
troupe
for
the
network
is
slicing
in
the
summaries.
We
do
want
to
first
of
all
define
transversal
eyes.
What
is
the
consensus,
the
definition
of
that,
how
it
relates
to
network
a
slice?
This
is
the
first
thing.
C
The
second
one
is
study,
a
framework
to
make
sure
that
we
know
all
the
component
that
we
have
to
do,
whether
or
not
there
should
be
a,
for
example,
a
new
NB
I
to
be
build.
This
could
be
one
of
the
outcome
of
that
discussion
and,
last
but
not
least,
to
their
address
the
mapping
that
I
mentioned.
If
I
wanna
map
that
abstract
interface
to
a
specific
technology,
we
are
going
to
have
a
few
use
cases
and
we
basically
they
show
how
the
mapping
might
work
in
the
real
world.
C
So
these
are
the
the
tree,
the
most
important
aspect
that
we
want
to
cover
there
as
we
go
forward.
Definitely
we
need
a
contribution
from
everybody
and
whether
or
not
there
are
some
other
thing
needed
to
be
done
it.
This
is
for
the
future,
but
at
this
time
we
wanted
to
make
sure
we
are
really
focused
on
couple
of
saying
we
are
not
basically
boiling
the
ocean
at
the
same
time,
how
relevant
that
work
is
to
ITF
is
a
prime,
the
example
of
whatever
we
do,
and
it's
very
important
to
consider
that.
F
C
C
What
service
is
that?
So
these
are
very
high-level
the
detail
of
that.
Obviously,
we
have
to
go
through
it
to
make
sure
that
we
are
addressing
it
in
a
very
logical
way
and
whether
or
not
we
need
to
add
other
attributed
A's
or
you
know
remove
it.
This
is
the
we
have
to
go
through
the
process.
Okay,
thank
you.
Okay,
no
problem.
Okay,.
G
This
is
a
important
from
SK
key
you.
So
a
very
nice
talk.
I
have
a
one
question,
one
comment,
so
you
basically
you
propose
intended
based
and
that
talking
will
be
useful
for
our
net
optimizing.
Is
it
correct?
Yes,
so,
basically,
you
can
see
a
high-level
some
policy
service
level
will
be
translated
into
metal
label
or
device
Allegra
right,
so
I
believe
it.
One
of
our
core
functions
is
translation.
So
are
you
considering
how
to
translate
sub
survival
policy
into
low-level
policy?
Are
you
considering,
or
are
you
working
for
that.
G
C
A
You
do
see
is
that
the
vendors
have
not
all
implemented
that
uniformly
yet
right.
So
what
you
need
to
do
is
basically,
even
if
we
say
about
intent
based
networking.
What
you
stiff
typically
still
see
is
that
you
need
a
device
model
which
is
specific
for
a
specific
vendor.
So
as
such,
what
we
are
doing
is
we
like
these
abstract
service
models,
which
are
being
defined
like,
for
example,
even
in
IDF
EF
l2,
as
an
all
3sm
being
defined
alright
as
a
service
model?
A
But
what
you
see
is,
if
you
have
to
implement
that
to
the
specific
device,
you
sometimes
need
a
translation
layer,
so
we
have
like
device
abstraction
capabilities
which
are
actually
mediating
towards
a
specific
device
implementing
that
particular
use
case
in
order
to
translate
for
the
specific
models
which
that
device
actually
has
implemented,
and
but
so
we
have
this,
that
is
a
abstract
service
layer,
and
then
there
is
a
device
type
of
model
which
is
actually
then
implemented
into
the
device,
depending
on
the
capabilities
that
device
has
enabled.
Then.
B
G
A
closely
collimation
opener
yeah,
basically
the
IDF
developer,
many
young,
the
era,
models,
high-level
and
low-level.
The
problem
is
the
link
to
each
other.
The
translation
is
missing
line
now,
so
many
people
constantly
working
with
it.
Basically
the
I
to
and
i7
data
security,
a
function
working
alone
about
a
member,
so
we
are
basically
implemented.
The
policy
translator
to
link
high-level
policy
into
low
level,
so
I
believe
Network
slicing
case
I.
Think
we
can
elaborate.
The
previous
our
work
I
mean.
G
Other
our
question
is
a
some,
a
collaboration
with
the
other
standard.
Apart,
for
example,
the
I
to
honest
F
we
are
facing
the
problem
is
we
are
using
in
security,
NATO
spirit
function
with
the
Sdn,
for
example.
The
problem
is
ITF
I
to
an
ACEF
and
Sdn.
The
interface
should
be
specified.
The
problem
is
how
to
collaborate
with
other
area
standard
body.
So
your
cases,
the
3gpp
and
airier,
some
standardization
and
I'd-
have
some.
