►
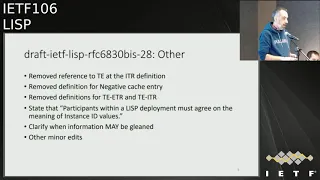
From YouTube: IETF106-LISP-20191119-1000
Description
LISP meeting session at IETF106
2019/11/19 1000
https://datatracker.ietf.org/meeting/106/proceedings/
A
A
B
Yeah,
whatever
you
say
from
now
on
is
a
contribution
to
the
IETF
there.
You
can
see
the
usual
pointers
to
the
chapter,
the
jabber
room,
all
your
three
mythical
and
a
gentle
slides
and
Phrygia
knowledge
all
all
per.
We
are
the
co-chairs
here,
but
mercy
deep
in
the
room.
Is
our
secretary
very
helpful?
Okay,
this
is
the
working
group
status
issue.
B
We
will
quickly
go
over
it.
We
have
sixty
eight
thirty,
four
bits,
it's
a
little
stuck
in
the
sense
that
we
are
waiting,
the
main
specs
to
go
out
to
device
this
document
and
send
it
forward
the
past
last
call,
but
we
have
to
check
that
is
compliant
with
changes
that
we
did.
This
GPE
we
will
have
an
update
later
on.
Introduction
has
done
for
something
like
few
years.
I
can't
read
the
how
many
days
anyway,
but
a
lot
of
time.
B
B
Eighty-One
certain
miss
asked
miss
reference
stuck
in
the
RFC
editor.
We
have
least
sec
now
he
this
document
is
a
slightly
position.
Lucy
has
been
in
working
group
last
call
for
like
three
months
or
so.
Right
reason
is
that
we
went
for.
The
last
call
then
then
jumped
in
with
comments
and
things
to
change.
So
we
waited
for
the
autos
to
change
it.
They
have
done
it
for
a
long
time.
So
I
think
we
did
not
receive
any
more
comments
right,
so
we
will
send
out
an
email
on
the
mailing
list.
B
B
Workgroup
last
call
is
packet
waiting
from
for
the
scheffers,
where
I
dug,
which
is
me,
but
just
we
are
giving
priority
to
the
to
the
main
stack,
okay,
so
agenda
I
will
take
one
minute
to
talk
about
79,
54s,
79,
55,
okay,
and
then
we
will
go
over
the
update
for
the
beast
documents.
This
GPE,
as
I
said
these
are
two
working
group,
the
three
working
the
documents
we
will
discuss
today
and
then
we
have
the
non
working
group
items
list.
Overlays
mark
we
present
dinner
will
give
us
a
demo
about
mobile
node
multicast.
B
B
So
let
me
get
quickly
to
7950
for
that
79-65.
So
these
two
documents
one
was
asking
a
Jana
for
specific
prefix,
ipv6
prefix
to
be
used,
experimentally
for
Lisp,
okay
and
the
other
one
were
the
guidelines:
how
to
manage
this
block.
Okay
and
ripe
NCC
very
kindly
take
over
on
the
management
of
this
block.
Okay,
now
the
experiment
and
the
the
experiment
went
over
for
three
years.
B
Okay,
the
deal
was
in
three
years
in
if
we
don't
have
sufficient
demand
for
the
traffic's
blocks,
and
there
is
no
specific
action
from
the
ETF,
then
we
give
this
block
back
to
Vienna.
So
we
had
few
requests
about
a
ID,
prefix.
Okay,
there
was
no
specific
action,
so
it's
time
to
give
back
this
block
to
Vienna,
which
happened
in
September.
Now.
What
do
we
do?
Is
these
two
RFC's,
okay,
they're,
the
most
reasonable
thing
to
do-
is
to
make
them
store
it.
B
B
Okay,
we
keep
keep
track
of
the
experiment.
Okay,
so
we'll
send
this
this
text
on
the
mailing
list
as
well.
Okay,
if
you
have
any
suggestion
or
collection
to
do
in
the
next
week,
please
send
our
an
email
back.
Otherwise
we
will
use
this
text
to
make
these
two
documents
start.
Okay,
any
comment
on
that
great.
C
C
B
My
perspective,
there
are
two
way
forward
for
this
document,
so
one
is:
do
you
really
need
an
allocation
of
Ramayan,
and
in
this
case
you
may
ask
one
in
the
document
itself.
Otherwise
you
just
can
specify
the
fact
that
maybe
an
operator
should
reserve
a
prefix
to
use
it
from
the
annuity
stuff.
Yeah.
C
B
C
E
Okay,
so
I'm
describing
the
usual
update
on
the
sixteen
thirty
bees
and
six
sixteen
thirty
three
bees.
So
since
last
idea
idea,
if
we
have
posted
two
new
versions-
and
we
have
address
roughly
160,
discussed
and
comments
and
as
far
as
I
know,
we
have
addressed
all
the
comments.
Now,
it's
up
to
the
reviewers
to
to
tell
us
if
you
can
address
them
right
or
not
or
not,
but
all
of
them
have
been
addressed.
So
the
main
changes
on
I
will
discuss.
First,
the
main
changes
in
the
data
plane.
E
The
first
one
is
unlock,
addressed
to
speech.
We
have
fixed
a
behavior
that
occurs
when
a
locator
is
added
or
removed
from
the
locator
set.
Then
when
this
happens,
the
sir
sixty
are
the
one
which
is
setting
up
the
LS.
We
can
no
longer
use
lsv
for
a
timer,
so
it
will
set
up
a
timer
and
it
will
at
the
same
time
send
an
SMR
to
the
destination
xtr,
which
means
the
receiving
site
of
the
laboratories.
E
At
two
speeds,
then
we
receive
inside
of
their
greater
status,
which
will
refresh
the
mapping
and
after
the
timer
expires
the
source
sixth
year.
We'll
be
able
to
set
the
locators
at
those
bits
again
for
us,
so
that
does
describe
on
the
updated
version.
Then
we
have
clarified
also
the
map
versioning
requirements
regarding
synchronization
that
basically
the
DTRS
within
a
lisp
site
needs
to
be
synchronized
within
a
one
minute
window,
which
was
a
requirement
from
the
reviewers.
So
this
paragraph
is
parroting
on
the
spec.
E
Then
there
are
many
many
many
other
minor
edits
and
comments,
and
probably
the
most
important
one
is
that
we
have
removed
references
to
traffic
engineering
on
the
idea
of
definition
because
it
it
was
not
properly
introduced.
We
can
also
remove
the
definition
from
from
form
a
native
map-cache
entry,
all
the
et
R&D
ITR.
E
We
have
stated
the
meaning
of
the
instanceid,
just
saying
that
it's
informally
the
participants
analyst
deployment
must
agree
on
the
meaning.
We
have
call
so
clarified
when
information
may
be
cleaned
and
there
are
a
bunch
of
other
edits,
then,
regarding
the
data
plane,
the
control
plane.
Sorry,
we
have
also
clarified
when
the
a
bit
of
relative
it
can
be
set
in
the
map-reply.
E
We
verify
that
we
don't
specify
a
string
meaning
for
the
site,
ID
field
and
informally.
It
provides
an
indication
that
a
group
of
six
years
have
some
relation
admission
if
topologically
or
otherwise.
We
have
also
clarified
and
I
think
that
that's
where
I
could
good
catch
from
been
that
that
integration,
that
is
recomputed
and
verified,
both
in
my
motif
and
members,
if
I
our
Ark
and
we
have
completely
removed
the
section
describing
locators
at
compacting,
because
it's
no
longer
need
because
of
the
first,
a
slight
regarding
locate
residue
fees.
E
We
have
also
remove
any
reference
to
be
hippies,
it
seems,
is
not
consistent
with
the
new
scope
of
double
applicability,
also
reference
to
list
pal,
because
it
it
was
a
sense
of
some
kind
of
privilege.
Mapping
system,
which
is
not
the
control
brain,
can
work
in
any
mapping
system.
We
have
clarified
several
aspect
on
the
second
consideration
and
many
other
minor
edits.
E
F
H
Its
stepper
I
also
thank
you
for
your
work
and
I
encourage
you
try
this
week
to
get
with
Maria
and
Benjamin
to
encourage
them
to
look
at
this,
because
what
will
happen
in
two
weeks,
everybody
will
take
start
taking
the
Christmas
holidays,
New
York
holidays,
especially
your
beans,
go
skiing
and
Maria
will
not
be
on
the
isg
next
year
right.
So
we
got
to
get
this
done.
So
I
really
encourage
it
to
these
next
week,
two
weeks
get
them
busy
with
them.
B
B
B
F
So
these
are
the
changes
I
tracked
since
0
6,
because
there
are
being
a
couple
of
versions.
Did
you
know
where
minor,
but
the
relevant
challenges
are
between
0
six
and
the
current
version?
So
these
are
the
main
changes
we
remove.
Support
for
nonsmoker
sharing
and
LSB
I'll
go
then
through
each
one
of
them.
Okay,
so
I'll
get
back
to
this.
F
F
Hopefully,
a
presentation
of
today
will
clarify
what
is
the
changes
that
we
need
to
do
so
then,
and
a
few
other
reviewers
pointed
out
that
features
like
economy
and
map
versioning
we're
relying
English
GP
on
fields
that
were
even
smaller
than
what
we
had
in
what
we
have
in
the
in
the
list
better.
In
particular,
we
have
only
those
two
bytes
markets
reserved
now,
and
you
know
in
particularly
for
the
nouns
even
from
a
person
in
that
was
complicating
the
the
features
as
well.
F
For
example,
if
one
wanted
to
use
an
ounce
of
64
or
even
under
28
bit,
one
could
do
it
and
the
same
format
versioning
and
the
same
also
for
a
recipe.
So,
rather
than
trying
to
live
with
the
limitation
in
space
that
we
add
in
the
originally
spider
we
will.
We
can
try
to
use
the
the
flexibility
of
GP
to
deploy
a
doc
headers
for
for
those
particular
use
cases.
F
So
this
is
the
new
text
here
and-
and
basically
this
is
what
we
do.
We
got
a
comment
back
from
Ben
saying
that
yeah
this
is
a.
He
agreed
that
this
could
be
a
nice
way
to
move
forward.
So
hopefully
this
will
help
him
to
to
go
into
a
yes
for
for
for
this
document,
she
made
us,
so
the
other
change
was
introduced
it
because
we
realized
that
there
are
some
features
that
can
be
used
and
I
think
this
was
a
comment
from
Miriah
that
started
this
change,
that
it
is
possible.
I
mean
the
list.
F
It
is
possible
for
implementation
to
implement,
of
course,
the
extension
that
are
well
known
at
a
certain
point,
but
it
is
also
possible
to
skip
those
features
that
are
not
known
at
the
moment.
A
particular
other
implementation,
for
example,
or
software
or
matters,
is
defined,
and
this
is
helpful
for
intermediate
nodes,
because
in
this
way
one
can
deploy
incrementally
features
that
we
add
to
list
GP
and
the
intermediate
nodes.
Don't
need
to
be.
You
know
change
because
they
can
just
skip
the
parsing.
F
A
Understand
that
she
matter
better,
we
don't
have
transit
nodes,
the
closest
we
have
is
our
TRS
and
but
but
we
don't
put,
our
TR
is
technically
terminate
a
tunnel
and
start
a
new
tunnel
right.
We
don't
have
any
transit
nodes
right.
I've
noticed
this
coming
up
in
a
number
of
overlay
protocols
where
the
protocol
runs
between
two
endpoints
and
somebody
starts
worrying
about
what
is
the
transit
node
doing?
No,
let's
not
make
any
argument
about
transit,
no
behavior,
please,
okay,
we
don't
have
any
okay.
A
F
F
Maybe
what
we
should
specify
is
that
at
the
tunneling
point
at
the
idea
with
this
structure,
the
implementation
can
pass
in
Hardware.
You
know
all
the
others
that
have
to
be
passed
in
hardware,
and
you
know
for
those
that
were
not
defined
at
the
time
that
the
hardware
was
designed.
You
know
the
packet
can
then
be
patented
in
software
and
those
can
be
taken
care
of
softer,
so
I
agree.
I
can
rephrase
that
and
that's
a
good
joy.
A
F
F
F
Ok,
so
we
will
do
that
thanks
for
the
comment
and
yeah,
and
that
is
it
the
other
aspect
that
may
be
interesting
of
him
at
us
I
think
to
help
hardware
implementation
that
echolocate
some
buffer
for
for
these
particular
features
having
these
adders
in
front
rather
than
at
the
end
help
so
the
she
matters
that
use
a
certain
range
of
the
next
protocol
field.
They
will
be
in
front
them.
F
These
I
think
is
just
a
simplification
for
the
other
implementation
examples,
I
mean
I
have
removed
all
the
normative
reference
to
examples,
but
the
draft
is
actually
you
know
mentioning
that,
for
example,
what
you
could
do,
which
you
made
us,
is
the
find
support
for
GBP
group
based
policies.
Io
am
econ
on
see,
map
versioning
and
LSB,
of
course,
and
there
is
a
sentence
specifically
for
for
nouns
but
versioning
and
locator
set
to
speed,
and
this
is
just
to
provide
the
example
of
what
can
be
done.
F
F
We
have
a
new
section
section
for
about
implementation
and
deployment
consideration,
so
there
were
a
few
comments
about
congestion
control
how
to
handle
the
UDP
checksum
toss
bit
and
PCP
beats
in
in
the
ethernet
frames
that
were
still
part
of
section
3.
So
actually
there
is
a
RFC
RC
885
that
specify
well
what
are
the
UDP
guidelines
for
tunneling
protocol,
so
what
we
have
done
is
basically
look
at
FC
8086,
that
is
GRE
in
UDP,
encapsulation
and
RFC.
F
A
is
basically
Ferenc,
RFC
885
and
you
know,
following
the
guidelines
or
FC
Alexi
identified,
so
most
no,
not
much,
but
some
of
the
text
that
was
in
our
cat6
could
be.
You
know
basically
easily
ported
in
in
this
case
and
that's
what
we
did
so
we
have
this
section
for
where
we
have
an
applicability
statement.
We
have
comments
about
a
section
about
congestion,
control
functionality,
the
usual
UDP
checksum
and
you
repeat:
zero
checksum
with
ipv6,
and
then
consideration
about
Ethernet,
encapsulation
payloads.
F
So
the
applicability
statement,
I
think,
is
the
most
important
of
this
section
here,
because
according
to
RFC
85,
there
are
two
applicability
scenarios
for
UDP
application.
One
is
when
the
tunneling
protocol
is
a
design
for
general
internet
applications
and
the
other
one
is
when
it's
designed
for
a
controlled
environment
according
to
RFC
885,
the
control
environment
is
what
is
defined.
F
There
is
a
single
minute
of
domain
or
an
edition
set
of
cooperating
domains,
and
you
know
where
a
network
is
in
a
controlled
environment
and
can
be
managed
to
create
under
certain
condition,
they
don't
apply
in
general
to
Internet
the
requirement
for
a
protocol.
A
tunnel
protocol
that
ends
up
in
the
controlled
environment
scenario
are
less
restrictive
than
the
requirement
of
general
internet.
F
Okay-
and
this
is
you
know
the
change,
please
take
a
look
at
section.
4.
Send
your
comments
most
of
the
text,
as
I
said,
is
coming
from
FC
886,
so
it
as
we
stood
the
you
know
the
time
at
least
then
the
last
aspect.
This
was
particularly
complicated
for
some
reason.
I
couldn't
understand
many
of
Luigi's
suggestion,
but
I
think
we
got
it
now.
So.
F
F
So
it
means
that
if
we
wanted
to
refer
to
the
elk
of
type
used
in
ER
c
86
t
these
would
be
a
down
ref
to
an
experimental
RFC,
and
this
is
a
big
no-no,
because
you
know
we
are
defining
li
GP
as
a
proposed
standard
together
with
68
1368
33
B's.
So
the
thing
to
do
is
basically
say:
okay,
let's
take
out
of
scope
of
least
GP
the
detection
of
ETR
capability.
F
B
I
think
I
think
this
is
correct.
Then
you
slide
when
you
say
we
still
deploy
Kobe
before
yeah
here,
because
these
are
controlled
environment
right,
okay
and
if
you
work,
they
are
connected
over
the
public,
Internet
still
connecting
controller
domains.
So
if
the
domains
are
control
it
you
have
a
way
to
know
who's.
F
That's
a
good
comment:
yeah,
okay
and
yeah.
So
next
steps.
So
we
have
a
few
action
items.
The
comments
from
Joyal
section,
5,
1
I,
think
there
are
a
couple
of
I,
have
seen
actually
one
one
typo
in
the
in
the
actual
test.
While
I
was
presenting
the
slides,
so
we
will
address
those
and
we
will
publish
Rev
12
tomorrow
or
the
day
after
tomorrow
and
and
that's
it
and
the
document
will
be
ready
for
for
your
review
and
then
I
guess
and
you
guys
come.
Please
confirm
we
will
send
the
document
back
to
last.
I
F
I
I
I
We
have
also
included
a
couple
of
other
considerations
here,
and
these
are
based
on
on
implementation
aspects
that
we've
seen
while,
while
trying
to
to
put
these
in
practice,
yeah
and
yeah
we've
also
added
some
editorial
comments
and
yeah
I
have
this
ending
that
the
revision
or
two
would
would
be
posted
soon
and
it
just
got
updated,
I
think
Victor
posted
it.
So
you'll
find
these
texts
already
in
the
website,
just
to
recap
with
what
is
the
overlay
draft?
If
you
remember
this
is
a
draft
to
provide
interoperability
as
interoperability
between
site
overlay.
I
These
disparity
can
come
as
as
control,
blame
disparity
or
different
condom
planes
or
different
data
planes,
and
the
basic
proposal
is
or
what
the
draft
tries
to
propose.
These
is
to
structure
these
interpret
interoperability
as
a
hierarchical
structure
where
multiple
sides
are
connected
through
through
these
transit
overlays.
I
This
is
just
a
recap,
but
the
important
thing
is
what
comes
in
this
version
and
and
the
most
important
update?
Is
this
topology
support
discussion?
The
idea
here
is
trying
to
answer.
How
do
we
stitch
together,
multiple
networks,
those
are
running
these
overlays
and
what
the
text
proposes
here
is
this
concept
of
loop
free
topologies.
I
Well,
if
Luffy
topologies
mean
is
that
okay
first
thing,
as
we
said,
right,
overlays
are
proposed
in
this
hierarchical
structure
or
the
idea
to
deploy
overlays
is
to
follow
these
hierarchical
structure,
where
we
have
site
overlay,
site,
overlays
connected
to
or
lace
and
and
these
overlays
could
potentially
be
connected
to
higher-level
overlays.
That
could
provide
these
interconnectivity
between
distant
or
separate
site,
overlays
that
are
connected
to
two
different
overlays
yeah.
But
the
important
thing
in
this
little
loop,
lucrative
ology,
is
this
right
that
we
imposed
to
connectivity
rules
to
this
here.
I
A
key
of
overlays,
where
overlays
that
are
at
the
same
level
should
never
connect
to
each
other
and
and
overlays
of
any
type
should
never
skip
here.
Key
when,
when
connecting
to
to
overlay.
If
we
impose
these
two
rules,
we
guarantee
there
are
no
loops
in
in
this
topology.
So
so
we
are,
we
are
free
from
having
to
to
routing
solutions
to
the
connection
of
I
go
by
the
Ruiz.
D
Like
this,
is
you
know
if
somebody
happened
in
site
overlay,
one
point
to
a
map
server
in
the
core
overlay
and
it's
against
the
requirements
of
the
draft
I
think
but
I'm
not
sure.
Maybe
you
could
answer
this
is
the
site
ID
that's
being
registered,
could
actually
be
known
in
the
core
uber
lay
and
when
it
registers
to
overlay
one
it
knows
it
can
do
the
loop
detection.
You
might
be
able
to
prevent
this
dynamically
without
any
special
anything
other
than
what
you've
already
specified.
D
I
A
K
I
Think
Silas
can
potentially
help
here
and
we
could
maybe-
and-
and
this
comes
with
the
I
mean
this
relates
to
that
nexus-
light
right.
It's
what
happens
if
we
have
multiple
borders
inter
connecting
multiple
sites
or
or
a
site
and
and
and
overlay,
and
and
here
we
have
another
instance
of
a
loop
in
some
sense
either.
So
the
ABA
we
have
a
border
of
order
said
that
it's
logically
connecting
to
two
sides
and
what
I
think
that
you
might
see
it's
always
weather.
I
Yeah.
The
update
also
brings
a
provision
to
probe
to
solve
this,
and-
and
the
idea
here
is
that
we
need
to
treat
these
groups
of
borders
as
a
border
said
and
implement,
with
horizon
rules
to
the
registration
process.
If
this
could
help
prevent
the
unexpected
configurations
or
in
an
expected,
interconnections
between
overlays
should
reevaluate
a
leave
it,
but
could
we,
but
the
other
proposal
here
is
that
members
of
order
set
need
to
share
the
idea
of
site
of
origin
when
registering
prefixes
and
how
they
do.
These
is
yeah.
I
I
know
that
the
beginning
you
mentioned
that
side.
Iv
is
not
yeah.
It's
it's
been
specified
a
bit
abstract
in
the
in
the
biz
draft,
but
here
we
we
try
to
go
back
and
and
give
a
more
specific
used
to
the
site,
ID
number
and-
and
there
is
that
what
we
these
draft
proposes
is
that
site
ID
identifies
the
origin
from
where
e
is
were
learned.
I
I
A
I
It
so
we
have
border
set.
These
guys.
Are
these?
These
two
guys
are
connecting
these.
These
two
overlays,
let's
say
the
overlay
on
the
side
of
early
now
in
the
overlay,
a
site
ID
will
identify
that
prefixes
come
from
from
side
overlay,
but
this
number
is
only
significant
for
the
two
borders
and
it
must
be
unique
in
the
you
overlay,
but
does
not
need
to
be
unique.
I
A
D
A
D
So
I
have
another
quick
comment
to
me:
it's
a
little
bit
misleading
how
you
have
the
things
going
on
2/3
because
what's
happening
is
the
XT?
Ours
are
registering
to
ms1,
okay
right
and
then,
if
for
some
and
then
the
bx
TRS
are
registering
all
the
e
IDs
from
the
site,
overlay
MS
right.
Yes,
so
you
have
an
arrow
in
number
for
MS
back
to
ex
TR.
What
is
that
supposed?
Is
that
a
message?
It's
not
a
map
register
because
b,
xt
r2
is
not
an
app
server.
D
You
are
you
saying,
ms,
sending
a
map
notifying
message,
xtr
telling
them
about
things
that
have
been
registered
to
it,
which
could
have
came
from
other
site
overlays,
but
could
also
come
from
itself
and
therefore
you
know
you
shouldn't
register
it
re
register
MS
1,
because
xtr
has
registered
it
yeah.
We
could
also
have
partitioning
right
that
I.
I
I
The
idea
with
overlays
and
stitching
together,
site
overlays
is
that
in
deployment
we
assume
that
borders
receive
most
of
the
traffic
following,
for
example,
negative,
mob
replies,
saying:
okay,
prefixes.
In
order
to
prevent
the
an
explosion
of
registrations,
we
may
choose
to
not
register
everything.
I
We
cite
overlays
and
and
kind
of
use
a
default
route
when,
when
accessing
prefixes
that
are
outside
of
the
domain
of
the
site
overlay,
so
these
default
daily
registration
is
just
a
provision
so
that
these
negative
map
replies
can
be
converted
into
complete
mappings
but
and
carry
a
group
of
our
logs
that
correspond
to
the
it's.
It's
just
so
the
basic
idea
that
this
is
registered
as
as
some
other
type
of
Vav
just
so
that
the
map
server
can
continue
computing,
negative
replies
and
yeah
dynamically.
This.
D
D
B
D
D
L
D
So
what
we
are
demoing
is
the
list.
Mobile
node
R
after
f5
on
an
iPhone
and
I,
have
some
RT
R
3,
encapsulating
tunnel
routers
that
are
deployed
in
Google
Cloud
and
the
Lisp
mobile
node
is
going
to
talk
to
list
correspondent
nodes
behind
Nats
and
for
this
demo
the
multicast
sources
and
the
multicast
receivers
are
all
on
the
list
overlay.
So
there's
no
inner
working
per
se.
That's
part
of
the
mobile
phone
demo,
but
the
very
last
slide
is
we're
doing
some
work
with
M
bone
D,
an
interoperability
with
AMT.
D
Okay,
so
in
the
list
mobile
know
what
is
acting
as
a
multicast
receiver,
that
means
it's
a
member
of
a
group.
It's
using
IGMP
to
join
groups.
The
application
that's
running
on
the
phone
will
send
IGMP
reports.
Those
IGMP
reports
are
encapsulated
like
any
other
packet
to
the
RTR
and
then
the
RTR
tract
a
group
membership.
The
RTR
is
then
met,
replicate
multi
kept
multicast
packets.
D
Still,
although
this
mobile
knows
that
our
group
members,
Hedden
replication,
is
head
and
head
is
a
relative
term
here,
it's
the
RTR
that
are
receiving
the
IGMP
reports
from
the
mobile
laws.
When
the
list
mole
note
is
a
multicast
source,
it
sends
multicast
packets,
just
like
any
other
packet
to
the
Artie
ours.
So,
as
you
can
tell
the
list,
mobile
note
does
absolutely
nothing
any
application.
Data
packets
always
get
sent
to
a
an
array
of
our
TRS
or
one
RT
R.
D
It's
been
really
a
great
thing,
so
appreciate
it.
So
the
mobile
node
is
connected
to
Wi-Fi
and
LTE.
Of
course
it's
CID
13,
and
the
idea
here
is
that
we're
going
to
use
those
are
TRS
that
are
sitting
in
the
Internet
underlay.
So
the
GR
TR
is
the
one
in
G
CP
and
there's
three
other
ones
in
AWS
that
were
there
they're
to
be
used.
They
were
there
for
the
unicast
demo,
but
we're
not
going
to
use
them
for
the
multicast.
Don't
know.
D
We
can,
though,
with
some
issues
that
I'll
talk
about
so
the
first,
the
first
demo
or
there's
two
streams.
We're
going
to
do
we're
going
to
show
that
the
the
25
is
going
to
be
a
multicast
or
sending
to
group
2
24,
1,
1
1,
and
it's
going
to
be
running
VLC
as
the
application,
video
streamers.
And
then
we
have
a
copy
of
VLC.
D
That's
on
the
iPhone,
that's
running
and
it's
going
to
be
joined
to
2,
24,
1,
1,
1
and
then
the
second
demos
we're
going
to
have
the
phone
be
the
source
and
it's
just
going
to
be
sending
pings
at
24
2
and
we're
going
to
show
that
the
two
containers
are
doing
to
that
group.
Ok,
clear
fire
up
this
demo,
I'm
I'm,
not
a
film
expert!
So
there's
a
little
bit
of
touchy
filming.
M
J
A
D
I'll
keep
the
pointer
up
there
and
while
describing
it
just
just
do
this
a
couple
times,
so
the
screen
stays
refreshed.
Okay,
it's
only
a
three
minutes:
video,
but
okay,
now
Rebecca
reviewer.
So
what's
going
to
happen
here
is
we're
going
to
pain,
to
24
2
as
I'm,
showing
there
with
the
arrow.
If
you
can
see
it
from
back
there
I'm
not
sure,
and
then
these
are
the
two
containers
in
this
window
window.
So
once
the
ping
starts,
these
guys
are
joined
to
the
group.
D
D
Then,
when
you
come
here,
I'm
refreshing
the
display
to
show
you
the
packet
count
going
through
the
RT
R,
so
it's
replicating
the
two
containers.
This
is
happening.
The
containers,
the
receivers
and
the
source
are
both
at
my
house
using
my
Comcast
connection,
so
they're
actually
going
all
the
way
to
GCP
and
coming
back,
but
and
so
there's
a
lot
of
delay.
So
the
RT
R
is
really
there's
really
a
lot
of
hair,
pretty
going
on
now.
What
I'm
doing
I
was
on
Wi-Fi?
D
D
D
Now
it's
interesting
here,
because
it's
acting
as
a
source,
the
gleaning
of
the
source
here,
is
not
really
that
important,
because
there's
really
no
packets
going
back
to
the
cell
phone.
This
is
really
a
unidirectional
multicast
well
from
from
I,
had
I
had
my
iPad
as
a
camera
on
an
easel
and
I
knocked
it
off
so
and
I
was
quick
enough
to
put
it
back
up
where
you
hopefully
didn't
see
it.
D
So
that's
about
the
tepid
and
there's
the
stream
is
sending
a
waterfall
video
image
from
this
container
and
there
you
see
it
on
the
phone,
okay
and
then
I
think
I'm,
going
to
show
you
the
RTI.
Now
now
like
you're
gonna,
see,
is
two
twenty
four
one.
When
one
is
joined
by
the
phone
and
you
notice
it's
sending
into
the
166
address,
which
is
over
LTE
and
then
I'm
refreshing
the
screen
to
show
you
that
the
count
when
the
counters
are
duck
green.
That
means
a
packets.
D
D
Okay,
so
some
observations,
the
glean
links
he
does
not
exist
as
it
does
for
unicast.
So
the
idea
is
is
when
the
phone
sends
a
packet
to
the
RTR
and
it
cleans
the
are
look
information
via
the
NAT
through
than
that.
That
information
is
glean
and
has
to
be
set
up
in
a
map
cache
entry,
because
when
a
return
packet
comes
back,
it
uses
it.
But
since
we
have
a
unidirectional
multicast
flow
here,
we're
really
not
sending
a
unicast
packets
back
for
so
for
sender,
only
nose.
You
really
don't
have
to
glean
for
receiver
nodes.
D
You
have
to
glean,
but
the
gleaning
happens
at
the
control
plane,
not
when
you
need
the
data,
so
the
IGMP
report
that
is
sent
from
the
phone
to
the
RTR
that
the
gleaning
is
done
there
and
there's
no
way
that
the
receiver
can
receive
the
traffic
until
the
IGMP
reports.
So
it's
great
the
reporting
the
group
join,
the
group
membership
join
and
the
glean
happened
exactly
at
the
same
time.
So
this
is
kind
of
nice.
This
is
where
multicast
is
your
head
upside
down.
D
We
were
able
to
take
advantage
of
this
receiver
oriented,
so
there
is
an
interesting
issue.
If
the
members
are
spread
across
our
TRS,
then
the
listener
will
know
needs
to
send
to
all
our
TRS,
which
means
the
list
mobile
node
to
replicate.
This
is
probably
not
good
because
of
spectrum
usage
and
stuff.
D
D
If
a
source
is
sending
it
could
send
to
a
single
our
Tiaras,
a
mobile
phone
could
do
the
same,
and
since
these
guys,
these
two
iPhones
RIT
MP
reporting
to
a
different
RTR
that
these
phones
are
configured
with
different
RT
RS.
They
join
up
separately.
So
what
we
do
is
rather
than
replicate
for
replications
happening
at
the
source
or
for
replications
happening
here.
D
D
A
D
So
the
trick
there
is:
where
will
the
application
sends
the
IGMP
reports
if
it's
multi-home
that
they're
both
active?
It's
a
unique?
This
works
just
great
because
you
could
load
split
on
how
bound
and
your
and
who's
in
cap
slating.
You
can
load
split
Unruh
sieve,
so
you
know
I
mean
that's
just
basically.
The
original
Lisp
problem
statement
was
doing
multihoming,
service-provider
multihoming,
so
unicast
not
a
problem
in
in
the
multicast.
D
It
depends
on
where
the
application
is
going
to
send
the
IGMP
report,
and
today
most
implementations,
I've
see
ITP
reports
aren't
sent
on
multiple
interfaces,
the
same
thing,
because
if
it
is
there's
a
good
chance,
duplicates
will
come
down.
So
you
want
to
avoid
that.
So
that's
kind
of
TBD
still
researchy.
Well,
we
don't
know
what
the
implementations
do.
Should
we
specify
it
good
question.
There's.
A
Also,
the
ways
they're
talking
about
using
multiple
interfaces
may
make
it
transparent
to
you,
because
if
it's
all
under
the
same
I
forget
what
G,
node
B
or
something
then
it'll
take
care
of
it
and
it'll
look
like
one
to
you,
but
there
is
definite
support
for
even
splitting,
but
simultaneously
Soph,
Wi-Fi
and
5g.
So
this
is
something
they're
all
looking
at,
but
it's
all
ongoing
now.
D
E
Commenting
what
you
said
the
problem,
typically
with
mobile
phones,
is
that
although
multi
coming
might
be
available
at
the
kernel
level,
they
typically
hide
this
kind
of
functionality
and
make
it
transparent
to
the
application
level,
which
means
that
it's
very
hard
to
be
right.
To
take
advantage
of
that.
D
Mean
I,
don't
know
if
that
helps
the
problem.
Right
I
mean
you
can
certainly
okay.
So
let's
entertain
that
thought.
It's
a
great
idea
mark
if,
if
we
put
a
map
register
functionality
on
the
phone
and
it
registered
its
CID
enjoying
the
group
because
of
what
it's
doing,
it's
not
only
registering
it's
the
ID
that
has
two
interfaces.
It's
also
registering
to
24
one
one
one
when
it
does
that
it
can
put
in
our
look
set
in
that
register.
Saying
I
have
two
interfaces
and
two
the
replicator.
D
It
looks
like
two
different
places
where
in
fact
it's
the
same,
but
you'll
have
to
do
duplicate
detection
on
the
receiving
end
now
I've
been
getting
requests
from
from
customers
contracts
or
whatever
that
it's
nice
to
send
packets
both
ways,
and
if
we
can
use
the
nonce
in
the
list
patter
to
detect,
duplicates
and
have
a
small
cache,
then
on
receipt
we
could
drop
the
packets,
that's
subject
for
another
topic:
another
IETF
yeah,
that's
for
you,
so
bring
it
up
on
email
for
you.
Wanna
do
yeah.
D
Okay,
interesting,
okay,
multicast
to-do
lists
list,
my
ok
on
time
and
we
have
a
couple.
Okay,
this
mobile
node
must
send
okay.
So
this
was
interesting
in
this
demo.
If
we
ran
it
long
enough,
the
video
stream
would
stop
it's
because
the
IGMP
reports
are
not
said
being
sent
periodically
from
the
phone
and
the
reason
is
is
because
IGMP
reports
are
only
sent
in
response
to
IGMP
queries.
Well,
the
RTR
is
not
sending
IGMP
queries
periodically,
so
they,
the
reports,
can't
come
so
I
did
send.
D
D
We
think
that
the
kernel
on
iOS
could
support
IGMP
queries,
but
the
queries
are
coming
and
they
have
to
be
associated
with
the
loopback
interface
versus
any
physical
interface.
So
that's
some
work
we
have
to
do.
We
want
to
keep
the
stream
going
in
my
applications.
I
just
send
on
the
containers.
I
send
IGMP
reports
periodically,
so
I
don't
need
a
query
or
happening,
and
I
would
like
to
avoid
a
query
because
that's
less
messages
that
have
to
go
to
the
phone.
D
So
we
would
have
to
write
functionality
in
oor
that
once
an
application
on
a
socket
joins
a
group
that
something
in
the
background
or
adjacent
a
sidecar
whatever.
This
is
a
popular
new
term.
I
guess
is,
would
have
to
send
period
but
we'll
take
that
offline.
But
that's
a
to-do
list
thing
same
with
MLD
for
ipv6,
so
yeah
multicast
support
for
ipv6
is
not
part
of
this
I.
Don't
know
the
current
status,
but
we
can
certainly
do
ipv6.
Cid
is
in
group
joining
over
v4.
D
D
However,
so
the
guys
at
juniper
and
the
M
bode
working
group
are
playing
around
with
AMT
and
AMT
is
a
tunneling
mechanism
only
supported
for
multicast,
and
all
this
infrastructure
on
the
bottom
here
from
the
yellow
down
is
what
they're
testing,
so
they
have
a
multicast
native
mbone,
where
multicast
is
native
using
juniper
and
cisco
boxes,
and
the
AMT
relay
is
kind
of
a
head
end
that
replicates
packets
to
a
MT
gateways
which
are
usually
on
mobile
devices
or
or
any
sort
of
devices.
So
what
we
try
doing
is
we.
D
They
said
if
you
can
source
some
data
from
a
phone
from
Lisp
over
on
the
left-hand
side.
Can
we
actually
connect
these
infrastructures
together,
and
this
is
work
in
progress
that
we're
starting?
We
just
started
it
last
week
and
we're
gonna
play
with
a
little
bit
this
week,
but
the
idea
here
is
for
13
to
send
multicast
2
to
24
2
to
3,
and
it
gets
replicated
to
the
two
containers,
as
well
as
an
e
TR
that
joins
to
24
2,
to
3.
D
D
The
problem
is
Serhant
RPF
213,
because
it's
not
in
the
core
routing
tables
so
and
this
dot
here
we
do
list
net
and
what
list
net
does
is
translates
the
source
address
from
an
eID
to
the
address
on
that
interface,
and
so
all
these
routers
here
to
this,
which
will
naturally
work
right
and
so
the
MT
relay
will
accept
the
pappas
because,
assuming
he
defaults
or
has
a
specific
address
to
that
thing
and
then
sends
it
to
the
receivers.
So
what
we
have
working
right.
H
D
D
N
Okay,
so
this
is
a
good
follow-up
to
the
multicast,
because
this
is
an
edge
network
mobility
edge
network
that
actually
leverages
the
mobile,
not
multicast
significantly
so
discuss
is
the
least
Draft.
Next
agon
will
do
a
quick
recap
just
to
baseline.
What's
going
on,
what
is
this
network
updates
to
the
draft
since
last
ITF
105
I'm
gonna?
N
Just
summarize
the
value
of
this
list
edge
network,
so
it
builds
on
the
stability
of
the
base
and
these
mechanisms
and
makes
use
of
Lisp
in
edge
in
a
time
where
mobile
edge
is
very
hot
and
needs
these
capabilities.
That
I'll
show
how
and
then,
given
the
stability
of
the
base
protocol,
a
will
ask
that
we'll
make
that
special
educator
but
fairly
generic.
A
working
group
draft.
N
N
But
it
needs
to
be
organized,
there's
so
many
things
patrolling
so
many
machines,
cars
dash,
cams
and
negative
cams
traffic
light
cams
out
there.
You
need
to
somehow
compile
this
thing
so
that
it
can
be
consumed
and
the
approach
we
lie
to
do.
That
is
just
just
to
snap
what
you
enumerate
to
a
formal
grid
of
the
earth.
N
You
can
choose
multiple
grades.
We
chose
h3
because
of
its
hierarchical
nature
and
exergonic
all
tiling
very
elegant,
and
this
is
addressable
by
lispy
IDs
and
we're
going
to
show
why
this
is
useful.
This
specific
map,
you
can
actually
go
play
with
it.
I'll
send
you.
The
URL
is
live
New,
York,
City
right
now,
including
images
and
enumerations.
Okay,.
N
D
D
A
N
All
right,
so
what
is
the
structure
of
the
draft
at
the
core?
Is
a
lisp
network
able
to
route
these
specially
IDs,
and
especially
IDs
re
IDs
for
the
earth?
Styles
and
Eydie
is
for
clients
that
protect
their
privacy,
meaning
the
objects
in
the
network
which
are
addressable
routable,
don't
need
to
know
who
is
it
specifically
that
is
interested
in
that
piece
of
the
earth
meaning
disclose
their
geo
privacy?
They
just
need
to
know
that
they're
authenticated
and
authorized
okay
and
they
have
their
credentials,
but
not
exactly
what
is
their
IP.
N
N
Quickly,
what
we
did
on
the
right
that
side,
which
is
your,
is
a
triple
a
mechanism
to
get
on
to
the
network.
So
what
we
do,
he
you
is
make
use
of
diameter,
which
is
very
common
in
mobile
network.
Typically,
typically
in
non
overlay,
you
will
do
something
to
the
gateway,
the
P
gateway
and
it
will
generate
a
diameter
propagation.
Since
this
is
an
overlay,
you
have
an
IP
address.
N
N
Are
your
ATP's
and
there
the
temporary
ID
allocated
for
you,
based
on
your
credentials
before
you
get
it
back,
along
with
the
arlok
that
you're
going
to
use
for
the
RTR
your
edge
router,
its
first
cleared
with
that
edge
RTR,
meaning,
is
gonna,
expect
you,
okay
or
multiple.
If
you
want
a
multi-home
okay
and
then
you
get
a
reply
back,
which
is
this-
is
your
ID
for
using
the
mobility
network
using
this
hour
lock
of
your
RTR
okay.
N
N
These
pictures
are
the
unicast
and
multicast
the
publish
and
what
you
get
when
you
subscribed
it's
basically
source
test,
so
e
ID
source,
CID
desk
or
Eskimo
G
in
multicast,
and
then
some
flags
and
then
the
tuples,
where
what?
Where
what
key
value
key
body
there
is
one
flag
which
is
proven
to
be
extremely
useful,
which
is
to
zip
the
kbk
V,
because
the
IDS
of
the
tiles
are
usually
in
the
same
area,
so
they
zip
very
nicely
the
values
in
case
of
an
area.
Somebody
breached
a
red
light.
N
The
danger
covers
a
lot
of
area,
okay,
but
it's
the
same
status.
Staying
man,
a
enumeration
and
also
in
these
situations.
Many
times
were
some
neural
networks
will
just
be
looking
for
one
thing:
just
portholes,
okay,
so
whatever
the
report
is
going
to
be
consistent,
so
the
object
IDs
HIDs
are
very
kind
distant
and
the
state
is
also
fairly
consistent.
Our
typical
zipping
is
7080
percent.
N
Alright,
what
another
thing
that
happened
since
last
idea
is
we
have
a
package
on
github
I,
think
you
still
need
our
permission,
so
we
are
giving
it.
So
if
you
want
you
can
get
it,
it
still
doesn't
use
or
because
the
list
but
the
client,
if
you
want
to
build
a
client,
it's
still
fairly
hard,
the
way
of
using
Lisp
and
since
all
the
addressing
here
is
algorithmic
so,
which
makes
is
very
scalable
based
on
where
you
are.
You
know
the
Eid.
You
don't
need
to
so
at
this
point.
N
This
is
a
you
know,
pretty
simple,
but
in
addition
the
Triple
A
packets,
the
diameter
packets,
are
all
encoded
in
there.
You
can
get
permissions.
That's
for
the
the
part
of
this
we
use
in
the
client,
which
is
control
plane,
free
as
Dino
described
until
the
RT
R.
Is
there
and
you
go?
You
also
get
the
full
edge
as
all-in-one
just
to
debug
your
client.
N
If
you
want
to
start
using
your
gonna
get,
if
you
want
to
do
a
navigation
app,
that
knows
what's
behind
the
corner
or
knows
more
things
than
the
typical
navigation
app
does
or
you
want
to
play
with
it
and
see.
Potholes
see
the
traffic
signs
which
you
can't
see,
because
the
tree
hides
things
like
that.
You
can
use
that
kit.
N
Ok,
so
let
me
just
capture
the
value
of
this
special
list.
Edge
network-
it
has
a
broad
value,
is
worth
a
stake.
It
on
I
think
I,
hope
the
value
to
immunise
and
Department
of
Transportation
s--
government
highway
authorities
is
a
it's
a
cheaper,
fresher
way
to
survey.
What's
going
on,
usually
very
costly
done,
every
few
years,
not
up
to
date
all
the
time
and
it's
budgeted
its
has
economic
value
per
meter.
N
But
this
is
a
way
to
just
let
the
network
gather
the
information
to
edge
objects
that
the
objects
compiled
the
multiple
sources,
the
multiple
passes,
the
multiple
directions
and
give
you
like
a
survey
of
signs
on
the
street.
What's
deemed
went
away,
you
need
to
repaint
a
traffic
signs,
the
side
of
the
road.
You
know
these
teenager
rooms,
where
they
have
the
stop
signs
they're
taking
from
somewhere.
N
Construction
zones
Muniz
love
that,
because
they
love
to
give
tickets
to
people
who
break
their
permits
in
time
and
span.
But
this
is
really
good
for
commuters
as
well,
an
alert
for
for
drivers
and
OEM
companies.
Oems
would
like
to
make
money
as
they
drive
they're
looking
for
that
source.
So
it's
a
the
recent
economy
of
data
trade,
so
we
can
facilitate
with
an
Interpol
protocol
parking
assist.
This
is
one
of
the
major
challenges
of
the
auto
industry.
There
no
parking
people
are
hesitant
to
buy
cars.
N
Blockages
slowdowns
in
the
highway
you'll
see
dashcam
footage
last
winter
of
these
pile
ups,
which
are
completely
needless
a
heartbreak
situation.
In
short
turn,
let
extends
them
the
sensor
of
a
car
beyond
its
line
of
sight
using
the
network
using
the
list
purge
in
Pleiades
enterprises
like
ups
and
are
really
interested
in
curbside
conditions.
Where
can
they
stop
working
out?
So
what
our
truck
routes,
pedestrian
vehicle
density?
How
many
people
are
in
the
street?
N
Google
Maps
wants
that
Apple
Maps
wants
that
and
we
can
offer
a
standard
interface
to
subscribe
to
that
the
5g
edge
is
very
appealing
and
make
it
very
relevant.
As
you
can
see,
you
have
an
aggregation
at
the
edge
that
leverages
the
new
5g
technology
and
then
a
after
processing.
The
consumption
makes
it
available
over
any
internet
or
back
to
the
edge.
N
The
capabilities
in
5g.
The
new
ones
are
a
massive
bandwidth,
which
means
you
can
put
all
a
I
in
the
edge.
You
can
really
low
cost
the
dash
cams
and
other
sources
of
information,
even
Street
cams,
because
it
can.
But
then
you
have
to
put
that
ad
object
at
the
edge
if
you
wanna
put
it
in
Amazon,
it's
just
not
gonna
work
and
then
auto,
reliable
or
latency,
which
is
the
public
channels.
N
We
don't
miss
any
packets,
even
if
we
have
multihoming
and
we're
gonna
receive
it
twice
or
three
times
we
still
don't
wanna
miss
any
packet,
because
if
there
is
a
red
light
bridge
and
within
I
want
to
get
that
packet
within
one
hundredth
of
a
second,
so
I
can
can
hear
a
sound
I
can
lift
my
eyes
because
otherwise
it's
dangerous
and
that's
a
demo.
We
need
in
AT&T.
N
The
value
of
the
Lisp
as
an
edge
network,
as
you
can
see,
is
that
really
what
happens
is
that
the
privacy,
the
security,
the
latency
control
the
subscription,
the
sharding
of
the
processing,
is
all
throughly
sprouting
so
having
a
stable
standard
to
do
that,
having
off-the-shelf
routers
and
multiple
stacks
to
control
that
and
best
practices
to
control?
That
is
really
helpful.
N
You
can
see
in
a
note
that
was
sent
to
the
list
by
AT&T
without
this
layer,
three
option
really
there
AT&T
was
facing
two
options:
to
extremes:
build
the
dedicated
infrastructure.
Just
for
that
or
have
proprietary
backends.
They
need
to
integrate
forever
for
every
feature
for
every
vendor
for
every
type
of
client
and
we
offer
something
different.
N
One
last
value
point
that
I
scooped
for
Marco
in
DMM
is
that
we
need
to
realize
that
between
the
edge,
the
mobile
edge
and
aggregation,
the
edge
routers
and
the
mobile
clients
there's
a
whole
3gpp
network
and
for
anything
to
leverage
5g,
there's
a
bunch
of
provisioning
that
has
to
happen.
There's
slicing,
there's
a
quality
of
service.
N
There's
there
is
provisioning
that
happened,
and
if
we
want
that
a
provisioning
to
be
efficient,
we
allow
that
we
facilitate
better,
because
it's
all
done
based
on
Eid
parsing
and
all
done
from
edge
routers
to
the
to
the
EPC.
We
don't
have
to
mess
with
application-specific
backends.
The
fact
that
we
put
it
on
list
should
make
it
a
lot
simpler
and
there's
a
lot
that
you
can
do,
for
example,
in
baby,
if
I'm,
Russia
or
me
town
I,
don't
want
to
receive
that
corner
all
the
time.
It's
really
important,
so
I
can
slice
it.
A
O
N
So
you
have
an
IP,
you
have
IP
connectivity
and
you
want
to
use
specific
mobility
network.
Okay.
What
you
do
is
you
ask
for
authorization
from
the
you
first
ask
DNS
what
is
my
a
triple
a
server
for
this
mobility
in
the
next
second
Mobility
network?
You
will
get
an
IP
address,
okay,
and
then
you
ask
you
get
you.
That
is
a
diameter
server
in
which
you
give
it
your
credentials,
user,
password,
vendor
blah
blah,
and
after
some
back
end,
you
will
get
back
an
e
ID,
which
is
your
overlay
address.
N
O
A
A
O
K
N
D
And
could
you
go
back
to
slides
where
you
have
a
nice
diagram
of
the
h3
tiles
I,
don't
know
if
you
thought
about
that.
Yeah
that'll
work
right
there
that
so
you
have
these
solid
lines
around
7
yeah
right,
perfect!
Thank
you.
You
have
a
hexagon
Accra
across
2
4,
6,
7
hexagons,
and
so
what
I'm
thinking
is?
Have
you
put
much
thought
about
how
to
join
multicast
groups
when
they're
per
each
h3
tile,
for
instance,
that
on
the
bottom
right
hand
corner?
D
If
you
look
at
a
node,
that's
right
in
the
very
center
it
would
actually
join
a
group
that
would
be
for
that
tile.
That's
it
right
in
the
center
should
that
guy
join
that
group,
as
well
as
all
the
six
groups
around
it
or
should
a
join
to
the
one
group
which
is
the
aggregate
of
all
of
them
and
what
I've
noticed
with
the
resolutions?
They
don't
map
exactly
and
fit.
N
Here's
the
thing,
so
what
you
use
is
a
specific
resolution
for
multicast,
which
is
resolution,
nine,
which
is
like
a
few
blocks.
Okay,
let's
say
this
ruffle
City
and
this
holds
all
the
tiles
that's
AI,
D
addressable
and
the
the
tiles
are
not
when
you
hierarchy.
There
is
leftovers,
that's
correct,
and
this
is
the
price
you
pay
for
having
a
polygon
which
is
both
approximation
of
a
circle
but
ties
in
hierarchy.
N
N
D
You
realize
we
might
have
joined
latency
as
your
I
remember.
When
I
worked
at
Cisco,
we
did
this
on
battlefield
grids
and
leaving
one
square
of
a
grid
going
the
other.
You
have
to
leave
to
stop
receiving
data
enjoying
the
next
one,
and
this
has
the
same
problem.
It's
a
joint
latency
data
and
state
trade-off
core,
and
we,
you
know,
see.
N
Similar
to
Hannover
I
mean
you
may
join
a
few
just
to
make
sure
that
you
covered
and
that's
okay
for
the
same
reason,
why
it's?
Okay
for
you
to
receive
multi-home,
it's
all
contained
so
you'll,
just
get
more,
doesn't
mean
that
they
are.
The
application
will
alert
the
driver
graphically
or
no
or
soundly
on
everything
may
use
judgment,
but
it
will
receive
a
look
ahead.
D
Yeah
I
understand,
and
it
depends
how
soon
you
start
joining,
because
there
is
joy
latency
there,
since
the
joint
message
is
the
red
map.
Registers
are
UDP
messages
that
can
be
dropped.
Yes,
and
will
you
get?
Will
you
get
the
information
soon
enough?
Do
you
have
to
plan
multiple
tiles
ahead
of
you
say,
says.
