►
From YouTube: IETF106-DNSOP-20191121-1330
Description
DNSOP meeting session at IETF106
2019/11/21 1330
https://datatracker.ietf.org/meeting/106/proceedings/
A
B
B
Next,
everybody
is
familiar
with
the
note.
Well
here,
the
blue
sheets.
Please
fill
them
in
because
we
want
well.
We
have
a
very
large
room
now,
but
we
want
to
keep
these
large
rooms.
It's
very
comfortable,
to
hear
the
echo
well.
The
agenda
for
this
afternoon
is
current
working
group
business,
two
presentations,
two
drafts
updates
and
some
new
working
group
business.
B
Our
work,
as
previously
mentioned,
is
on,
of
course,
data
tracker
and
our
github.
So
if
you
want
to
look
at
that
or
we
or
want
to
use
that
use,
github
current
working
group,
business,
TCP
requirements,
Duane
and
the
DNS
server
cookies
by
willem
and
some
five
new
working
group
business
so
of
them
have
been
presented
already
earlier,
but
not
adopted.
Yet
good
I
think
we
can
get
started.
I
want
to
ask
drain
first
to
kick
off
wax
here.
The
generic
slides
for
you.
C
So
I'm
doing
this,
this
is
a
little
update
about
the
DNS
over
TCP
operational
requirements,
draft
that
myself
and
John
Christopher
had
been
working
on
just
a
few
sort
of
minor
updates.
Since
the
last
time
we
talked
about
this
draft,
we
now
mentioned
DNS
over
TLS
in
the
abstract.
So
to
give
it
a
little
more
prominence
there,
we
added
some
some
paragraphs
about
recent
work
on
avoiding
fragmentation
and
and
and
cite
those
references
now
in
the
at
the
end.
C
Instead
of
should
there's
there's
a
couple
paragraphs
in
the
document
about
the
KSK
rollover,
and
since
that
is
happened
quite
a
while
ago,
that
is
all
now
been
updated
to
be
the
past-tense
instead
of
present
present
tense,
and
we
added
section
on
our
addison
text
to
the
privacy
considerations
section.
It's
pretty.
It's
pretty
innocuous,
partly
to
note
that
you
know
DNS
over
TCP
and
UDP
itself
does
not
provide
any
privacy,
but
if
that's
what
you're?
Actually
you
can
use?
You
can
use
TLS
or
DTLS
and
then
generally
updated
some
of
the
references.
So
that's!
C
A
C
C
A
D
This
is
Paul
Hoffman
I
got
the
feeling
that
and
correct
me
if
I'm
wrong,
Duane
that
you
really
stayed
away
from
requirements
and
such
in
this
document.
It
really
was,
if
you
are
doing
this,
don't
forget
about
these
other
things.
In
fact,
don't
hint
don't
wait
until
you've
implemented
to
think
about
these
other
things
think
about
them
ahead
of
time,
so
that
might
be
I
mean
so
Suzanne.
Another
sort
of
way
to
ask
it
is:
has
this
been
useful
to
anybody
reading
through,
as
they
were
doing
their
implementation
to
go?
F
G
B
H
B
B
J
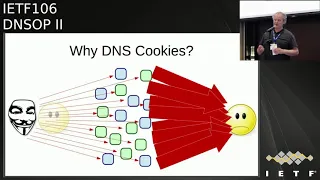
Yes,
sir,
this
is
about
the
draft
that
gives
the
recite
that
for
the
Neshoba
coupe
ish
that
caters
for
other
different
vendors,
so
our
UDP
services
that
reply
with
a
bigger
response
than
they
request
like
it's
possible
readiness.
They
are
susceptible
to
be
misused
for
amplification
denial
of
service
attacks,
and
this
is
the
kind
of
attack.
A
J
Yeah,
that's
better,
so
it's
the
DNS
cookies
are
for
to
protect
against
reflexive
amplification
attacks.
This
is
the
attack
where
the
attackers
pushed
IP
address
of
the
victim
and
sends
a
lot
of
small
DNS
queries,
which
will
be
result
in
a
large
answer
that
which
the
victim
will
be
flooded
and
Dena's.
Cookies
are
a
dienes
native
mechanism
to
deal
with
this
kind
of
text.
J
Now
that
teach
be
the
inner
self
at
HP
would
also
be
a
solution
because
it
has
a
handshake
shock.
Spoofing
is
not
possible,
but
teach
PE
requires
quite
a
lot
of
state
at
server
and
Dena's.
Cookies
are
very
lightweight.
They
do
not
require
a
lot
of
state
that
server
actually
just
a
single
secret
for
all
the
relationships
with
all
the
clients
a
server
has.
So
it
is
like
a
handshake,
though
so
a
client.
This
is
how
it
works.
Clients
that
creates
clients
cookie,
which
is
basically
nonce.
J
The
sheriff
er
generates
the
sheriff
a
cookie
based
on
the
client
cookie
in
the
client
IP
address
and
returns
the
server
cookie
alongside
the
client
cookie
in
the
DNS
response
and
in
subsequent
requests
from
the
client.
The
server
will
recognize
yes,
I'm,
the
only
one
that
could
have
created
the
server
cookie
show.
This
I've
seen
this
client
before
I
will
provide
larger
answers
for
it.
If
it
wants
to
I
will
not
trunky
get
these
answers,
and
also
this
client
does
not
need
to
be
response.
Late
rate
limited
anymore.
J
So
what
was
the
problem?
Our
fee?
Seven,
eight,
seven,
three,
the
DNS
cookies
are:
she
did
a
great
job
at
defining
this
mechanism,
except
that
it
was
sort
of
liberal
in
how
the
server
cookies
would
be
created,
so
the
cookies
were
cooked
by
or
baked
by,
one
vendor
were
not
appetizer
or
well
received
by
another
partner.
J
This
started
to
do
implementation
for
all
the
well-known
Upshaw's
Dina's
vendor
implementations
at
a
hackathon
in
Prague
at
the
ITF
104,
and
that
was
a
big
success.
We
had
a
working,
interoperable
server
cookies
for
those
implementations,
so
we
thought
okay,
we
are
almost
done.
We
just
have
to
do
the
client,
cookie
and
then
interoperable
tests,
each
other's
implementations
had
resolved
us
to
the
authoritative,
etc,
and
then
we
done
this
can
go
to
law
school
and
we
finished
except
that
didn't
happen.
J
So
we
focused
on
the
client
cookies
in
Montreal,
and
we
discovered
that
there's
a
problem
and
to
explain
to
you
why
there's
a
problem
I
have
I've
given
here
the
v-shape
for
client
cookie,
that
we
no
longer
use
it's
no
longer
in
Commonwealth,
but
it
was
based
on
the
clients,
IP
address
the
server
IP
address
and
a
secret,
and
we
need
to
include
the
server
IP
address
for
minimal
authentication,
but
it
needs
to
have
a
different
cookie
for
its
different
relationships
and
clients.
Ip
address
needed
to
be
in
there
for
privacy.
J
So
you
might
ask:
why
is
not
simply
a
if
we
have
a
server
cookie
for
the
server
assented
and
otherwise
create
a
new
client
cookie,
because
that's
obviously
the
more
heavy
operation
here?
That's
because
we
need
to
know
that
client
IP
address
of
to
create
a
client
cookie,
and
if
we
sent
it
an
old
cookie,
then
it
might
have
the
old
might
be
based
on
the
old
client
IP
address,
so
that
so
how
this
works
is
first,
as
you
users
get
shocked,
name
to
get
the
client
IP
address
of
cookie,
creates
new
client
cookie.
J
It's
a
cookie
the
same
as
what
we
had
stored
for
the
server
already.
Then
we
are
fine
if
it
also
has
a
server
cookie.
If
not,
then
we
said
all
the
cookies
are.
New
ones
are
calculated
so
by
the
way,
besides,
not
dealing
with
all
the
error
codes.
This
piece
of
pita
card
has
another
major
flaw.
I
think
some
of
you
might
know
what
it
is
that
are
familiar
with
socket
programming,
so
you
cannot
get
the
client
IP
address
from
a
unconnected,
UDP
sockets
right,
so
get
shocked.
J
Name
doesn't
actually
give
you
the
client
IP
address,
so
there's
a
trick
to
do
this.
You
create
a
trial.
Socket
then
connect
it
and
sort
of
fake
connected
to
the
server
and
then
get
IP
address
and
in
classifieds.
So
then,
when
we
discovered
that
we
had
to
do
this,
the
implementers
thought
well.
This
is
the
straw
that
breaks
the
camel's
back
right.
J
J
Alongside
the
server
cookie
and
also
its
client
IP
address,
then
the
next
time
the
client
will
connect
to
the
server
it
will
bind,
and
it
has
this
chef
cookie
or
it
connects
to
a
server
which
has
a
server
cookie
as
well
bind
to
the
IP
address
and
which
will
now
cause
failure
if
IP
address
changed,
and
so
it
can
then
create
a
new
client
cookie.
So
this
was
tested.
It's
a
hackathon
and
sort
of
works.
K
J
J
K
L
J
L
J
M
J
F
It
doesn't
have
to
be
changed
often
at
least
one
year
or
something,
but
the
thing
is
that
use
your
best
cryptographic,
knowledge
and
yeah.
If
the
secret
is
not
compromised,
you
don't
have
to
change
it
at
all,
because
unless
the
cryptographic
function
is
compromised,
then
why
change
it?
It
just
got
its
face
and.
J
D
Paul
Hoffman
I'm,
seeing
that
there's
been
a
couple
of
questions,
I
think
your
decision
to
have
the
discussion
happen.
Offline
for
this
change
might
not
have
been
that
great.
So
can
you
bring
things
back
to
the
list
for
this
just
so
that
questions
can
get
resolved
not
just
by
reading
the
document,
but
also
by
seeing
the
logic
and
also
to
Jim
it
does
I
I
just
did
a
quick
search
on
is.
O
D
J
A
J
J
Indeed,
so
the
new
draft
has
been
perfect
to
the
list
on
Monday,
though
so
I
invite
you
all
to
review
it
carefully,
especially
the
security
and
privacy
considerations
and
yeah.
Then,
once
that
settled
them,
we
can
do
a
implementation
or
get
implementation
experience
with
the
software
vendors
and
get
it
over
with
I
suppose
excellent.
A
P
The
mechanism
in
zero
3,
which
we've
updated
recently,
is
pretty
much
the
same
as
a
lot
of
editorial
changes.
Some
clarifications
based
on
discussion
last
time,
implemented
it
more.
There
was
a
bit
of
code
before
it
is
a
bit
more
now
and
deployed
it
on
a
small
set
of
domains
or
mine,
there's
code
there,
it's
a
bunch
of
Python
code
and
some
bash
scripts
to
create
zone
file,
fragments
and
a
bash
script.
P
It's
come
a
wrapper
around
dig
just
to
make
it
look
a
little
bit
less
horrible
and
the
signature
verification
creation
stuff,
which
is
the
most
complicated
bit
of
this,
is
included
in
our
implementation.
Kind
of
works
looks
like
that's,
lovely,
yeah,
I,
think
that
kind
of
has
older
pretty
much
all
the
features
to
the
draft.
Nearly
there's
another
domain
that
uses
a
two
five
five
one
nine
sig
as
well,
and
that's
kind
of
it.
Our
goal,
I
guess,
is
to
progress
a
flavor
of
this.
Q
Oran
Kumari
Google!
No
hats.
Can
you
remind
me
again
what
exactly
the
use
cases
I
mean
I've
shredded
a
few
times,
but
can
I
do
stuff
like?
Can
you
publish
a
record
saying
that
you're
related
domain
is
Apple,
calm
like
it
feels
as
though,
unless
you
have
them
pointing
in
both
directions?
The
semantics
gets
a
little
odd.
This.
P
P
Q
I
P
Q
P
S
P
S
Of
the
same
part
of
the
problem
that
Andrews
SOPA
proposal
attack,
you
me
you
did
it
in
a
different
way,
but
it's
yeah
this
mean
you
can
imagine
just
barely
you
know,
sort
of
papering
the
trees
with
with
parallel
things
which
would
be
you
know,
I
could
write
a
Python
script
to
do
that,
but
it
would
make
things
look
pretty
ugly,
but
I'm.
Just
I
guess:
I
would
like
better
worked
out
examples
that
don't
say,
and
of
course
somehow
you
know
that
the
sub
names
are
the
same,
because
at
this
point
you
don't
okay.
P
T
Tim
and
what,
since
Kenny
speaking
for
myself,
we
actually
do
have
a
real
legitimate
use
case
with
my
employer
trying
to
solve
this
problem
across
organizations
across
domains
across
sort
of
custom
organizations
sort
of
thing.
So
this
is
like
step
one
and
we
have
a
step
two
idea
in
our
head,
but
we
like
to
see
something
like
this
sort
of
start
to
happen.
So
thanks.
P
S
P
S
B
B
You
want
soda,
so
we
yeah
so,
but
that
how
many
people
did
read
the
documents?
Okay,
quite
a
few
excellent
and
I
like
well
as
you
stated
at
the
start
of
your
presentation-
is
what
do
we
do
with
the
document?
Do
we
continue?
Do
we
kill
it
or
something
else
yeah,
so
I
want
to
also
from
the
room
a
little
bit
mixed
in
impression
pro
or
con
I
want
to
take
it
to
the
mailing
list
and
and
I
think
some
people
do
see
the
use
case.
B
D
D
It
is
a
great
example
of
a
different
with
death
of
this
between
this
document
and
John,
Levine's
D
bound
I'll,
be
very
blithe
here
and
say
what
what
is
proposed
in
this
document
are
a
couple
of
things
which
Stephen
has
said
are
extractable
and
he
might
be
happy
with
just
one
of
them.
D
bound,
you
know,
John's
D
bound
is
somewhat
boiling
the
ocean,
but
in
a
way
where
everyone
would
then
be
happy
if
we
could
get
there
so
I'm
a
little
bit
hesitant.
D
If
you
go
to
the
list
and
say,
do
we
to
do
this
because
I
believe
some
people
would
agree
with
what
Stephen
just
said,
which
is
even
a
little
bit.
You
know,
starting
with
just
a
little
bit
of
this
would
be
good
and
there's
a
practical
reason
for
this
one
little
thing.
Other
people
are
course,
are
going
to
be
happy
to
boil
the
ocean.
This
is
DNS
off,
but.
D
P
I
can
make
a
suggestion.
I
mean
I.
Think
there
is
it's
a
valid
point
to
try
and
distinguish
you
know
what
we've
put
in
this
document
versus
the
bigger
problem
mm-hmm.
So
maybe
the
question
would
be:
do
people
want
to
adopt
this
document
or
bit
service
and
try
and
distinguish
that
from
the
bigger
question,
perhaps.
A
R
Not
at
Stough
lest
even
take
the
mic,
so
DNS
SEC
resolvers
operator
recommendations.
So
it's
a
draft
three.
So
a
little
bit
of
history,
we
already
presented
some
version
previous
version
of
that
draft,
but
we
just
handled
it
a
bad
way
so
I
think
now
we
are
achieving
the
initial
goal,
which
is
to
provide
some
recommendations
for
the
operator
and
the
main
thing
is
to
encourage
them
to
deploy
the
in
a
sec:
okay,
oh
okay,
so
the
the
motivations
so
a
little
recap:
how
much
time
do
I
have
20
minutes?
R
Okay,
so
motivation,
the
trust
in
DNS
validation
relies
on
the
signature
and
the
trust
which
is
the
owner
of
the
private
key
associated
to
the
DNS
key
is
the
legitimate
owner
of
the
sign
are
so
you
have
a
trust
anchor
and
then
you
have
a
chain
of
a
chain
of
trust
where
multiple
DNS
key
are
validating
each
each
others
and
each
of
those
keys
can't
be
okay.
Each
of
those
keys
can
rotate
the
over
time.
R
So
the
real
threat
model
for
DNS
SEC
resolver
operator
is
them
to
consider.
Well,
what
should
I
do
and
what
happens
if
there
is
a
malicious
DNS
key
that
is
being
introduced,
so
the
operational
recommendations
we
we
talk,
we're
we
have
are
basically
encouraging
those
dro
to
enable
DNS,
SEC
validations
and
to
provide
them
sufficient
trust
into
the
DNS
SEC
validations
the
rigor.
So
we
have
a
some
categories,
which
is
we
address
the
provisioning,
the
monitoring
and
the
management
and
I
think.
R
Maybe
an
important
part
of
that
document
is
to
clarify
what
is
the
actually
the
responsibility
of
a
resolver
when,
when
DNS
SEC
is
being
enabled
so
to
demystify
that
is
well,
when
you
ask,
can
you
can
you
enable
DNS,
SEC
validation?
Well,
if
something
goes
wrong
on
the
internet,
I'm
gonna
be
hold
responsible
for
that
and
where
we
would
like
to
go
against
this
myth
and
say:
no,
it's
not
you.
R
So,
even
though
we
have
20
minutes,
I,
don't
think
we're
gonna
explain
it
here.
What
is
a
validator
but
I'm?
We,
the
document,
has
a
clear
I
mean
as
a
recap
of
what's
the
validation
process.
What
are
the
different
modules
that
have
been
involved
into
that?
So
you
have
the
time
the
Crypt
will
capture
graphic
libraries,
you
have
the
DNS
cache
and
then
well
the
DNS,
SEC
validation
and
genes
with
DNS
SEC
message
that
are
also
being
used
to
manage
the
trust
anchors.
R
So
what
are
these
recommendations
intended
to
do
so?
We
first
like
to
minimize
how
those
operators
do
in
to
interact
with
with
evaluations.
The
main
principle
is
to
let
the
NSA
go
on.
We
don't
want
to
to
tweak
the
protocol
note
that
they
require
some
expert
in
DNS
X,
so
they
just
the
expectation
is
that
they
just
be
sufficiently
confident
that
enabling
should
be
sufficient.
R
So
the
categories
we
defined
our
into
three,
you
have
recommendations
for
startup.
So
when
you
start
up
resolver,
you
have
runtime
recommendations.
So
what
should
be
done
on
a
running
resolver
and
there's
some
more
specific
actions
that
are
classified
as
on
demand.
So
in
some
cases
we
expect
that
those
operators
may
want
to
check
some
specific
things.
So
that's
part
of
the
on
demand
so
so
time.
Well
time
is
important
for
the
signature
checks.
N
R
Resolvers
so
I
mean
the
thing
with
time
is
just
to
make
the
difference
between
the
the
categories
of
the
recommendation.
So
startup
run
time
and
on
demand,
then
we
have
a
list
of
recommendations
that
are
based
on
that
are
targeting
the
the
genus
key
record,
so
in
the
I'm
gonna
start
with
the
ta
trust
anchor.
So
we
have
positive
translators
and
we
have
negative
stress
anchors
and
all
of
those
belong
to
a
trust,
anchor
store.
R
Yeah,
so
when
we're
talking
about
management
of
those
trackers
well,
you
should
consider
that
they
are
being
configured.
It's
a
configuration
thing
so
well.
The
Dro
should
be
able
to
have
their
own
configuration
and
to
ensure
that
the
dynastic
resolver
when
it
started
they
start
with
the
appropriate
ta
or
an
ta.
And
when
we
are
thinking
about
ta,
the
TA
with
the
right
value
I
mean
the
up-to-date
value,
then
those
ta
I
mean
there
are
not,
then
they
must
not
be
hard-coded
somewhere,
so
they
should
be
able
to
to
be
updated.
R
R
It's
it's.
It's
quite
pretty
important
to
prevent
that.
The
DNS
SEC
resolver
starts
with
an
old
ta
in
them,
and
so
the
configuration
of
the
TA
is.
It
really
has
to
see
as
a
two-step
process
you
defined,
which
entry
point
you're,
gonna,
trust
and
the
other
thing
that
corresponds
to
the
trust
model.
And
then
what
is
the
actual
value
of
that
TA?
It's
a
it's
it's!
It
does
not
belong
to
the
trust
model,
but
it's
more
related
to
the
configurations.
R
So
the
M
this
theoretical
process
for
configuration,
the
TA,
is
that
the
D
redefines
the
domain
name
is
trust.
So
it
is
really
the
entry
point
and
that's
corresponds
to
the
trust
model
and
it's
expected
not
to
change
over
time
or
I
mean
during
a
long
long
long
time
and
then
once
you
know
which
entry
points.
R
So
if
it's
a
root
zone
or
if
it's
a
some
of
the
TL
DS
or
whatever,
once
you
know
that
you
should
have
a
third
party
mechanisms
that
is
going
to
retrieve
the
appropriate
value
for
HTA,
and
once
you
have
your
TA,
you
can
and
NTA.
You
can
generate
the
configuration
file
so
while
I'm
saying
possibly
young
but
it's
to
have
a
single
process
and
then
once
that's
done,
the
resolver
can
be
configured
and
started
so,
but
it
they
should
not
be
started
without
having
the
step
a
to
be
defined.
R
So
with
that
model
only
the
the
dear
I
mean
only
the
trust
model
is
defined
by
the
D
Rho
and
everything
is
being
automated
and
the
tiara
ta
are
always
being
provisioned
with
the
latest
values.
So
the
the
main
advantage
is
that
you,
by
doing
so,
when
you
reboot
a
machine
when
you
reboot
your
resolver,
you
you
don't
have
to
try
that
the
TA
have
been
recorded
into
the
file
system.
That
is
only
right
only.
That
is
only
read-only,
for
example.
R
R
R
So
now
that
we
have
multiple
steps
to
configure
those
ta,
we
want
them
to
be
deployable
and
realistic.
So
how
possible
way
to
and
I
think
a
simple
way
to
implement
those
recommendations
is
actually
you
have
a
DNS
SEC
resolvers
that
is
already
configured
with
the
right
trust
anchor,
and
so
it's
likely
to
to
fit
the
trust
model
for
99%
of
the
ISPs.
R
So,
in
which
case
I
mean
the
trust
model
is
agreed
by
the
the
provider
of
the
DNS,
the
resolver
software,
and
the
value
is
checked
by
that
software
provider,
and
so
the
only
thing
it
I
mean
an
ISP.
An
operator
has
to
do
is
download
the
up-to-date
code
and
start
to
start
the
code,
and
that
I
mean
that
code
need
to
check
that
it's
the
right
value
with
the
appropriate
mechanisms.
But
that's
fine.
If
you
want
something,
a
trust
model
is
more
complex,
then
yeah
you
may
have.
U
So
is
it
meaningful
to
expose
that
choice
of
how
you
establish,
root
or
bootstrap
trust
to
the
outside
world?
I
mean
the
fact
that
you're,
essentially
relying
on
the
software
signature
key
or
of
the
of
the
distribution
right
or
whatever
software
distribution
you're
using
that's,
essentially
what
you're
saying
right,
yeah.
U
Whether
whether
that
choice,
right
you're
choosing
right,
if
you,
what
you're
saying
is
probably
true
right,
99%
of
the
world,
will
use
sort
of
you
know
trustor
the
the
DBM
signing
key
right
and
can
that
that
signature
is
how
you
anchor
trust
in
the
initial
configuration
right
so
but
others
may
choose
to
do
other
things
to
bootstrap
trust.
So
is
that
choice,
something
you
want
to
expose
if
you're
talking
about
sort
of
making
trust
like
auditable
from
the
outside.
R
U
R
U
R
U
R
R
R
R
R
So
that's
a
one
recommendation
to
keep
an
eye
on
it
and
not
well.
The
reason
we
recommend
this
mechanism
is
that
so
the
the
operator
does
not
open
the
configuration
interface
runtime.
Well,
you
should
regularly.
Maybe
so
it's
a
should.
It's
not
necessary,
but
its
richest
recommended
that
it
checks
the
health
of
the
TA,
and
so
one
important
thing
is
that
it's
only
to
cache
ta.
We
don't
have
to
check
well
did
he
act
when
the
update
has
been
performed.
R
Is
the
update
the
new
the
new
key
actually
stored
into
the
configuration
file
on
the
system,
so
in
case
of
reboots
and
so
and
so
on?
No
because
we
have
a
first
way
to
provision.
I
mean
the
the
resolver
so
and
on
demand.
Recommendation
is
that,
well,
you
should
have
the
tool
to
say:
well:
are
the
key
being
used
by
my
resolvers
so
the
way
I
foresee
that
is
that
when
a
clear
rollover
fail,
the
Dro
should
not
try
to
to
repair
it.
It
should
reboot
the
resolver,
that's
basically
the
line
in
in
our
recommendation.
R
R
Anchor
most
of
the
recommendation
is
to
well
to
make
that
feasible
and
to
follow
the
recommendations
in
a
in
another
document
and
so
runtime.
Well,
we
should
monitor
the
failed
signature
associate
to
each
key.
It's
it's
a
shoot.
So
it's
a
nice
thing
to
have,
but
it's
not
necessary
and
maybe,
if
you
want
to
be
able
to
dining
died
well
to
find
out.
Well,
if
ever
something
goes
wrong.
Why
it
goes
wrong,
then
you
may
collect
also
some
status
of
the
key
or
other
informations,
but
that's
really
optional.
R
Yeah
you
should
be
able
to.
If
something
goes
wrong.
I
mean
an
emergency
cash
rollover
key
case
k
roll
over
to
flush,
the
cache.
So
initially
we
were,
I
mean
it
would
be
nice
to
be
able
to
only
flush
the
midi
arse
associate
to
the
case
k
I
mean
suppose
you
have
a
corrupted
KSK
and
you
want
only
flush
the
ours
that
has
been
validated
by
that
case
k
but
I
mean
flushing.
The
food
cache
is
also
something
possible,
pre-field
deprecation.
So
it's
it's.
R
We
want
to
be
able
to
move
the
crypto
and
be
able
to
update
the
crypto
and
not
having
a
software.
That's
carries
all
the
legacy
crypto,
so
we
would
like
that
DeRose
are
confident
to
say
yeah.
This
type
of
crypto
is
never
used,
so
I
can
decently
remove
the
crypto
library
as
associate
to
that
signature
scheme
or
whatever.
So
that's
a
recommendation.
We
recommend
to
check
what
is
actually
being
used
in
the
software
yeah
invalid
recommendation
is
when
something
is
invalid.
R
It
would
be
good
to
have
a
system
to
be
able
to
report
that,
to
the
maybe
to
the
author,
if
thought
of
that,
it's
basically
to
help
to
take
the
right
actions
if
something
goes
wrong,
or
it's
anyway,
an
interesting
information
for
to
share.
So
these
are
basically
the
recommendations,
I
well,
the
the
real
hope
is
so
we
would
like
to
get
feedbacks
and
again
the
real.
The
real
goal
is
that
operators
could
easily
enable
and
feel
confident
to
enable
the
NSA.
V
R
Now
I
guess
we're
pretty
matter
now
there
is.
It
has
been
for
a
long
time
in
the
draft
state,
especially
we
had
issues
to
position
correctly
so,
but
so
we
were
I
mean.
The
previous
versions
are
mostly
at
having
some
mechanisms
mandatory
mechanism
for
the
DNS
resolvers,
which
is
not
the
right
way
to
so
we
figure
out
how
to
do
that,
but
I
think
now
we
we
have
the
right
path
to
and
I'd
like
that
document
to
be
adopted.
That's
okay,.
W
Yes,
Ryanair
from
GPRS
I
I
support
this
document
and
I
have
one
comment
regarding
to
unity.
A
operations.
The
importance
of
MTA
operations
is
to
have
a
deep
contact
with
the
customer
support
center,
because
users
cream
comes
to
the
customer
support
center
so
that
it
operated
have
to
have
channel
with
them
to
know
the
something
strange
happened
and
also
customer
support
serve
to
know
when
the
the
arrow
enables
the
NTA
for
a
certain
domain
name
same
customer
support
center
would
have
claimed
from
the
users.
R
So
but
I
think
what
you're
asking
is
already
in
the
ante
a
document.
So
maybe
we
should
emphasize
on
that
in
the
current
draft
that
we
can
do
but
I
think
the
the
ante.
A
document
is
pretty
clear
that
there
is
an
having
a
another
channel
and
this
is
has
to
be
advertised
through
websites
or
this
kind
of
it,
but
yeah
I'm.
Taking
that
comment.
A
Who
is
more
likely
to
read
it?
Having
seen
the
presentation
today,
good
that
looks
like
a
lot
of
reviewers,
so
I
think
it'd
be
good
to
for
the
folks
that
are
interested
in
doing
this
I
admit
the
sounds
it
useful
to
me.
If
you
are
interested
in
the
topic,
please
go
ahead
and
read
the
document
provide
feedback
to
the
authors
and
we
look
at
the
level
of
interest
in
progress
and
consider
adopting
it.
Okay,.
H
Hello,
I'm,
Cosmo
jihad
and
today
I
will
talk
about
dr.
Jordan.
It's
about
a
boy
who
dimensions
are
the
avoid
augmentation
through
one
avoid
fragmentation
eat
in
deenis?
Again
you
see
80-85
UDP
usage
guidelines,
BCP
145,
published
in
March
2017
section
three
point:
three
messages
are
guidelines
specifies
that
our
application
shouldn't
send
the
UDP
Datagram
dot
resulting
IP
packets
that
exceed
the
maximum
transmission
unit
METU
along
to
along
with
the
pasta,
the
pasta
to
the
destination
and
an
application
should
either
use
the
path.
H
Mtu
information
provided
by
the
IP
layer
or
implement
the
possibility
discovery
PMDD
itself
to
determine
whether
the
pass
to
detonation
will
support
its
desired
missile
sites
without
fragmentation
and
previous
PCP
145
RC
5405
November
2008
in
customer
sites
and
in
casting
UDP
UDP
usage
guidelines
for
application.
Designers
already
have
same
text
then
avoid
fragmentation
in
DNA's.
Avoid
fragmentation
in
UDP
is
effective
after
November,
2008
and
I
checked.
H
Fragmentation
in
DNS
out
of
sheets
and
EDM
sort
of
shades
discussed,
see,
discuss
issues
of
commentation
and
note
that
facility
with
or
without
fermentation
may
be
smaller
than
this
and
our
she
Saudis
3226
Vienna
second
IP
version.
6
alia,
Sabha
is
Reba
message,
size
requirements
or
gain
a
second
IP
version.
6
compliant
entities
must
be
able
to
handle
fragmented,
the
IP
version,
4
and
IP
van
risks,
UDP
packets,
the
master
support,
EDM
syrup
and
other
bottles
message.
H
H
H
H
/
local
policy
and
requested
should
compose
UDP
responses
which
result
in
IP
packet
to
do
not
tow
exceed
the
path
MTU
to
the
request
are
the
maximum
that
the
estimate
is
the
maximum
you
DNS
UDP
parasite
should
be
the
Akshar
or
the
hole
to
maximum
DNS
UDP
payload
size
under
the
body.
Maybe
Jabari
is
equal
to
or
Raja
tongue
320
unders,
smaller
than
or
equal
to
1400
know
maybe
332,
and
the
dong
operator
should
consider
small
responses.
H
Configuration
under
augmented,
DNS
UDP
missile
sites,
Ragna
tds
UDP
messages
may
be
dropped
before
IP
away
assembly
to
avoid
just
poison
attacks,
using
like
the
augmentation
under
how
to
literally
how
to
retrieve
pasyati
body
to
a
destination
is
written
in
manual
page
prissy
get
sock,
get
so
copter
manual
only
knocks
and
I.
Don't
know
how
to
get
value
on
bsd
and
the
mistress
shows
changes
from
0
0
to
0
our.
H
New
cosas
por
bixie
and
the
wrong
because
RFC
80-85,
UDP
UDP,
see
guidelines
and
updated
text
using
EDS.
Certain
terminology,
for
example,
sender,
is
changing
to
request
the
question
respond,
receive
a
responder
and
the
text
about
estimating
the
maximum
gain
CDP
pero
size
under
added
the
operator
should
consider
small
size,
congregation
and
I
did
how
to
retrieve
Posse
annuity
bar
you,
it
laughter,
youth
who
or
under
please
consider
adopting.
F
F
This
working
group
should
adopt
this
work
until
that
work
is
finished
and
I
would
suggest
you
to
because
none
of
the
things
you
talked
about
is
is
Deanna
specific,
it's
UDP
specific,
so
I
don't
think
we
should
add
up
this
work
until
they'd
work
in
the
end
arrives,
finished.
I,
think
that
you
should
go
compared
to
do
two
drafts
and
and
provide
a
useful
feedback
to
them
and
and
finish
there,
and
only
then
we
should
have
a
we
might
have
a
draft
in
the
DNS
op.
F
Q
S
I'm
John
Levine
I
think
we
actually
do
have
DNS
specific
stuff.
That
is
useful
to
say
in
a
particular
the
traffic
from
a
resolver
to
an
authoritative
server
like
you
can't
tell
what
network
it's
going
to
go
over,
so
you
need
you.
So
all
this
advice
about
being
conservative
about
what
sort
of
packets
I
to
use
is
relevant.
S
S
I
think
we
should
make
sure
we
don't
contradict
anything
that
the
transport
people
say,
but
I
think
there
are
some
useful
things
to
be
said
like
if
you
know
all
your
clients
are
on
the
same
network,
and
you
know
a
lot
about
that
network,
then
you
can
reasonably
use
sizes
that
are
appropriate
for
that
network.
You
know
and
I
think
that's
actually
a
pretty
common
case.
G
Brian
Dixon
de
GoDaddy,
sorry,
but
you
my
following
up
with
what
the
for
those
non
following
that
other
graft
or
what?
What
exactly
it's
talking
about
I
think
there's
definitely
useful
recommendations.
It
might
need
some
embellishment
and
just
this
draft
I
mean
and
the
recommendations
might
need
to
be
split
out
on
the
recursive
to
off
versus
client
or
recursive,
as
well
as
whether
you
know
more
about
your
immediate
environment
versus
not
in
terms
of
the
selection,
but
have
it
having
a
sensible
default
for
implementations.
G
O
I
am
the
author
of
that,
but
I
was
gonna
head
down
a
subtly
different
direction,
I
think
you're
being
too
prescriptive
and
I
think
you're
jumping
to
a
solution
from
a
minority
case
when
you
actually
start
looking
at
the
survival
mechanisms
for
large,
fragmented
UDP
responses,
they're
actually
higher
than
most
folks
think
they're,
not
100%,
there's
nowhere
near
it.
But
the
problem
really
is
is
that
resolvers
tend
to
rely
on
timeout
to
detect
failure,
because
how
do
you
know
to
go
to
TCP?
O
You
need
a
TC
equals
one
response,
which
means
the
server
has
to
go
hunting
and
we
said
on
Flag
Day.
That's
a
really
bad
idea,
so
you're
jumping
straight
to
a
solution.
You
should
set
the
end
to
you
for
this
and
that
will
solve
all
our
problems.
It
won't
is
probably
the
wrong
approach.
In
general,
now
there
wasn't
piece
of
work
that
was
looked
at
briefly
and
discarded,
which
was
actually
quite
interesting.
O
Davy
song
came
up
with
a
thing
called
ATR
which
sent
back
a
big
UDP
response,
including
fragmentation,
waited
10
milliseconds
and
sent
back
explicit
truncation.
It
set
back
the
query
with
the
truncate
bit
set.
If
you
lost
the
fragmented
UDP,
there
was
a
packet
saying:
try
TCP
immediately,
it
got
rid
of
the
time-out.
O
You
actually
want
to
run
with
quite
high
empty
use
as
high
as
you
can,
because
when
you
go
to
TCP
when
you
finally
get
there,
that's
the
last
resort
and
there
you
need
to
run
with
low
msss
and
you're
kind
of
saying
well
I'm
going
to
solve
the
UDP
problem
and
that's
the
end
of
it.
That's
not
true.
There's
a
much
deeper
set
of
interactions,
and
the
thing
I
think
we
have
to
realize
is
that
if
you
want
that
switch
to
be
fast,
you
actually
have
to
encourage
a
TC
equals
one.
O
Setting
one
way
is
this
muted
flag
day
that
says
no
large
UDP
forever
now,
like
I,
said
that's
kind
of
solving
the
six
to
twelve
percent
problem
for
everyone.
So
we're
all
part
of
the
problem
now,
even
though
large
UDP
packets
make
it
for
a
lot
of
folk.
This
is
a
minority
case
and
it's
sort
of
imposing
the
worst
possible
solution.
Ie,
everyone
goes
small
simply
because
some
folk
don't
make
it
on
the
lifeboat,
so
I
actually
think
deeper
problems
here,
interior
is
looking
at
it
right
now.
There
is
no
hurry
most
of
the
time.
O
G
I've
done
follow-on
research
on
that
I
haven't
published
it
if
I
think
I've
asked
before
if
folks
are
interested
in
that
I
think
that
would
help
justify
one
of
two
recommendations
either
doing
the
smaller
below
MTU.
As
far
as
like
this
draft
is
concerned,
and
the
other
of
which
is
doing
the
the
DNS
cookies
and
one
of
those
two
would
be
adequate
for
addressing
the
cache
poisoning
attack
caused
by
fragmentation
and
I'm.
Not
sure
do
we
want
to
take
that
to
the
list.
A
A
So
it
sounds
like
that
should
go
to
go
ahead
to
the
list
and
sort
of
the
larger
point.
What
I
think
we're
hearing
here
is
that
this
does
record.
This
does
represent
a
significant
amount
of
effort
and
thank
you,
but
there
is
a
related
work
going
on
in
int
area
to
the
general
problem
to
the
general
issues
around
fragmentation.
We
should
wait
and
see
the
status
on
that.
We
should
take
take
a
look
at
what's
going
on
there
and
figure
out
what
of
this
work.
A
That
is
perhaps
still
useful
as
advice
to
dns
implementers
and
its
DNS
specific,
so
I
think
I
think
that
the
what
those?
What
folks
who
are
interested
in
this
work
need
to
do
is
review
what's
going
on
in
int
area
and
then
further
develop.
Perhaps
any
aspect
of
this
that
is
specific
to
DNS
and
the
implementation
of
DNS,
so
that
that
sounds
like
a
reasonable
way
forward
and
I
see
our
jabber
scribe
at
the
mic.
Yes,.
D
D
Okay,
so
Warren
said
that
it
was
just
that
one
documents:
okay,
I'm,
sorry,
okay,
he
thinks
that
it
so
I
think
we
should
check,
because
I
seem
to
remember
that
there
was
work.
That
was
gonna
happen
in
int
area
after
that
finished,
at
which
point
then
we
would
wait
to
be
beyond
all
of
it,
but
if
not
once
some
things
in
the
our
theater
Q,
we
can
read
it
and
then
do
the
determination
you
just
said
of.
Therefore,
what
is
left
okay,
Warren.
A
I
A
X
Perfect,
my
name
is
Ray
Ahrens
I
work
for
I.
Can
all
opinions
expressed
here
on
my
own
and
the
facts
speak
for
themselves,
but
the
opinions
do
not
are
not
necessarily
shared
with
my
employer.
I
wanna
I
want
to
say
that
beforehand
before
I
start
and
the
reason
I
say
this
is
because
this
topic
is
a
little
bit
controversial.
X
So
I
would
like
you
to
keep
an
open
mind
and
I'm
wearing
my
good
shirt.
So
careful
with
the
tomatoes.
I'm
gonna
talk
about
private
space
names
and
the
problem
is:
there
are
no
private
space
names.
There
is
no
such
thing.
There's
no
documents,
no
RFC!
That
tells
you
how
you
can
use
private
names
in
the
DNS
I'm
talking
about
something
similar
to
X
headers
in
mime
types,
SRC,
1918
address
base
except
tech
and
private
use,
language
text,
etc,
etc.
Even
in
the
DNS,
we
have
private
types.
X
So
if
you
then
look
at
the
solution,
space
I
mean,
in
absence
of
a
standard
document
of
how
to
do
things.
People
think
of
their
own
way
of
doing
things,
for
instance,
advice
that
I
sometimes
hear
well.
Why
don't
you
just
register
a
name
and
do
everything
you
want
to
do
under
that
registered
name?
Well,
that's
not
really
private,
there's
not
really
internal
another
one
I
hear
often
is
don't
do
it?
Well,
that's.
That's!
X
Sorry
also
the
author
from
Warren,
and
there
is
dot
local
everywhere
and
got
local
stems
from
an
old
microsoft,
technet
article
it
had
to
be
put
through
RC
67
61
in
order
to
protect
it
and
then,
of
course,
we
have
home
DARPA,
which
is
also
kind
of
a
private
view.
Space,
and
this
is
the
result
of
looking
at
I
thi
data.
X
So
if
you
didn't
think
about
what
the
solution
should
be
and
I
think
personally,
what
would
be
useful?
It's
a
simple
and
concise
BCP,
something
that
says
if
you
want
to
do
this,
do
it
like
this
and
choose
the
label
without
a
semantic
meaning,
and
this
is
actually
the
core
of
my
presentation.
It
does
not
need
to
have
a
semantic
meaning
every
firmly
it
needs
to
be
short.
X
So
what's
the
problem
with
the
semantic
meaning
is
because
internal
is
not
exactly
the
same
as
private,
it's
not
exactly
the
same
as
local
home
that
ARPA
or
neighbor
or
global
or
whatever
string
you
want
to
use
and
all
of
these
strings
are
to
end
or
phonic.
They
don't
work
in
different
languages
and
also,
please
use
a
name
or
it's
very
useful
label
that
is
defined
as
never
to
collide.
X
Now
you
want
to
prevent
collision
with
anything
expected
in
the
future.
So
initially
I
had
a
bullet
point
that
says
maybe
a
one-character,
a
ski
domain.
Well,
I,
that's
never
gonna
happen.
I
can
tell
you
that,
and
that
will
be
a
policy
development,
the
hell,
let
alone
all
the
things
you
need
to
test
in
order
to
get
it
working,
and
so
maybe
you
can
use
a
two-character
a
ski
domain.
Now
this
is
also
a
bit
of
controversial
part
because
the
two-character
a
ski
domains,
sorry
they
are
governed
by
RFC
1591.
X
What
is
RFC
1591
states,
it
says
IANA
is
not
in
the
business
of
deciding
what
is
and
what
is
not
a
country.
The
two
character
codes
are
country
code,
domains
right
and
there's
nothing
the
business
of
deciding
what
is
what
is
not
a
country,
and
so
it
leaves
it
to
the
ISO
three
one.
Six,
if
lists
now
between
you
and
I
ISO
3166,
is
also
not
in
the
business
of
deciding
what
is
the
country
code
or
not?
X
What
they
do
is
they
map
official
country
names
to
two
letter
codes
and
I'll.
Show
you
the
list.
This
is
it
and
there
are
676
or
26
squared
and
and
they
have
colors
now
what
I
mean
is
they
fall
into
categories?
I'll
start
with
them
with
with
a
simple
one,
the
white
background.
Those
are
codes
that
can
be
assigned,
they
haven't
been
designed
yet,
but
it
can
be
in
the
future.
So
that's
a
no-go.
We
can't
use
any
of
those.
The
green
ones
are
those
that
have
been
assigned
like
be4,
Belgium
or
D
for
Germany.
X
Then
we
have
the
yellow
ones,
the
yellow
ones.
They
are
exceptionally
reserves.
Those
are
actually
quite
interesting.
Uk,
for
instance,
is
exceptionally
reserved
and
UK
in
the
context
of
ISO.
3166
does
not
mean
the
United
Kingdom
UK
in
the
context
of
of
366
and
has
been
exceptionally
reserved
for
to
make
sure
it
doesn't
get
allocated
for
any
other
country.
So
the
official
code
for
the
other
Kingdom
and
Great
Britain
and
northern
islands
is
GB,
and
why
is
that?
X
Because
if
you
are
going
to
get
acronyms
or
not
acronyms
initials
for
the
first
two
words
for
the
first
one
worth
of
a
country,
you
quickly
run
out
of
United
of
republics
of
kingdoms
ii
quickly
ran
out
of
urs
in
case.
So
that's
why
they
decided
to
take
this
first,
a
string,
that's
uniquely
identifying
the
country,
in
this
case
great
britain,
sorry
for
the
detour-
and
you
is
another
one,
that's
research!
You
know
what
EU
is
not
a
country
at
all.
X
X
So
I
want
to
talk
about
these.
These
are
the
user
assigned
codes,
they're
42
of
them
AAA
and
zedzee
on
the
top
left
on
the
bottom
right
and
then
qm
2
qs
s
XA
to
exit
now?
What
does
the
iso
3166
standards
say
about
this
range?
You
can
just
do
a
grep
on
the
user
sign
and
then
you
get
these
three
things
and
construction
of
the
alpha-2
code.
How's
it
done.
How
is
it
used?
How
are
these
two
codes
used?
It
says
here:
the
iso
3166
standard
uses
combinations
in
the
range
of
a
b2.
X
If
you
need
a
code
element
to
represent
country
names,
not
included
in
this
part
of
iso
3166,
these
42
are
available
now
I
know
it
says
country
names
here,
we'll
keep
in
mind.
This
is
guidance.
So
how
are
these
code
used
elsewhere
and,
let's
start
with
the
ISO
codes?
I'm
sorry
I
reserved
standards,
3
901,
that's
the
recording
code
equivalent
to
ISBN
it
reserves,
etc,
strands
independent
of
any
country.
Now
the
interesting
one
here
is:
4
1
7,
that's
currency
codes
like
let's
say:
Singapore
dollar
SGD
right.
That's
an
official
currency
codes.
X
The
SG
in
SGD
comes
from
ISO
3166,
Swiss,
franc
CHF,
the
CH
come
from
ISO
3166
GBP,
remember
not
UK,
but
GB
GBP,
the
GB
comes
from
iso
3166.
So
how
are
they
using
these
user
ranges?
If
you
want
to
pay
in
gold
because
you
can
pay
someone
in
gold
and
it's
a
transaction
in
that
includes
gold
right,
you
use
the
code
x
au.
X
If
you
want
to
paint
silver,
it's
XA
g
now
you
can
think
twice
what
what
AG
and
a
you
stand
for.
But
if
you
want
to
pay
in
Bitcoin
this
is
this
is
true.
If
you
want
to
pay
in
Bitcoin,
you
can
use
X,
bTW
I!
Think
it's
pretty
cute,
but
the
X
a
then
refers
to
the
three
one,
six
six
code,
because
it
always
refers
back
to
the
three
one:
six
six
code
for
the
first
two
characters.
So
now
I
can
tell
you
why
EU
is
actually
in
the
ISO
3166
list.
X
Remember
it's
not
a
country
and
his
exceptionally
reserved
it
doesn't
map
through
any
official
name.
The
reason
it's
in
there
is
the
euro
was
introduced
in
99
and
when
the
euro
was
introduced
in
99,
and
you
refer
back
to
ISO
3166,
there
isn't
anything
there
for
EU.
Now,
of
course,
you
might
have
a
risk
in
the
future
that
EU
will
actually
be
assigned
to
an
official
country.
Why
that
may
have
I,
don't
know
rupee
or
ruble,
and
then
you
have
EU
are
so
there's
a
coalition.
So
that's
why
in
ISO
3166
this
is
exceptionally
reserved.
X
That's
where
I
use
them
from.
There
are
a
lot
more
I
quickly
skip
over
them.
International
Civil,
Aviation
Organization
is
that
set
for
you
in
travel
documents,
the
Aeons
I
have
them
scores
XK
for
Kosovo.
You
see,
there's
a
lot
and
wiper
World
Intellectual
Property
Organization.
They
use
these
codes
all
over
the
place.
X
You
and
law
code
used
a
lot
in
a
lot
of
organizations
using
them
and
reserves,
except
for
international
waters.
A
few
more
but
exit
is
for
international
Wars,
I
think
the
kind
of
stands
out.
It's
another
country,
a
World
Bank
exceed
for
the
euro
area.
Actually
you
for
North
America
Interpol
uses
that
when
Interpol
sends
the
document
out
to
all
of
its
agencies
worldwide,
it
can
basically
say
all
this
from
this
country,
because
in
Interpol
is
not
on
the
country
level.
X
It's
an
international
organization
so
when
they
sent
the
document,
there's
a
jet
set
to
all
sets
that
mean
being
from
that
is
so
three
one.
Six
six
list,
a
little
closer
to
home
the
cat
form
right,
there's
difficulty
in
browser
forum.
They
use
xxxx
to
signify
a
country,
that's
not
covered
by
ice
or
three
one.
Six,
six
Unicode
uses
these
things
a
lot
RC
5646.
X
These
are
the
text
for
identifying
languages,
and
you
can
have
your
own
user
code
in
there,
your
own
user
sign
code
in
there
and
as
an
example,
here's
a
here's
Kosovo
again
and
there's
sq
dash
XK.
This
for
the
Albanian
language
in
Kosovo
or
SR,
Cyril
XK,
that's
the
Serbian
language
in
Cyrillic
scripts
in
Kosovo
I
mean
these
are
currently
on
your
laptop's
right
in
some
libraries
somewhere
and
even
closer
to
home
and
I.
Think
this
is
this.
X
X
It's
a
little
bit
of
secure
to
find,
but
it's
there,
it
says
the
following
steps
will
be
used
to
select
the
two
character
code,
and
here
is
that
is
three
one:
six
six
mesh
again:
is
they
actually
using
18
of
the
42
coats?
But
it
literally
says
here
and
I
think
this
is
important
to
mention
the
use
of
ISO
3166.
X
These
codes
are
used
as
intended
in
various
standards,
not
just
our
C's,
but
also
ISO
standards
itself
uses
these,
so
we
also
know
that
these
will
then
never
be
assigned
or
reserved
by
the
IHL
if
they
would
do
so,
and
all
of
these
standards
that
uses
these
private
code
need
to
be
changed.
So
it's
highly
unlikely
that
that
will
happen.
X
We
also
don't
know
that
these
UA
coats
are
collision-free
because
you
will
never
be
delegated.
And,
lastly,
one
important
point
and
the
you
a
codes
user
assigned
codes,
they
have
no
semantic
meaning
great,
that's
five
out
of
five,
so
in
fact
you
can
have
different
code
for
different
uses.
Remember
your
42
codes,
I'm,
not
suggesting
you
just
do
whatever
you
like,
you're
gonna,
get
that
same
message
and
they
need
some
procedure
around
it.
But
I
had
a
conversation
with
a
colleague
the
other
night,
and
this
person
basically
said.
X
If
this
was
done
10
years
ago,
then
maybe
as
an
example,
we
could
have
zest
set
for
private
use,
names
or
X
age
for
homeless
names
or
XM
for
M
DNS
names.
Now
I
kind
of
kind
of
put
this
quickly
under
here
in
slides
just
an
example
I'm
not
suggesting
we
should
use
it
that
way.
But
if
we've
known
this
10
years
ago,
this
would
have
been
a
possibility.
X
So
then
there's
the
question:
if
this
should
be
delegated
or
not
now,
personally
I
think
it
shouldn't
be,
and
if
you
delegate
it
so
if
you
don't
delegate,
is
an
evaluator
behind
a
resolver
and
will
validate
that
these
things
do
not
exist.
That
road
negates
any
inserted
private
private
space
data
and
so
a
validating,
stub
resolver
now
needs
a
negative
trust
anchor
for
these
to
work.
So
that's
a
whole
lot
of
configuration.
X
So,
on
the
other
side,
if
it's
delegated
as
an
unsigned
delegation-
and
you
avoid
configuring,
each
individual
stub
validates
with
a
negative
trust,
anchor
plus
a
negative
side.
You
basically
allow
anyone
in
the
world
and
to
insert
this
private
data
in
your
device.
Id,
keep
in
mind.
You've
done
everything
you
can
on
a
stub
resolver
right
under
stop
validate
it's
secure
as
possible.
Your
SSH
is
on
the
latest
version.
X
Your
certificates
have
been
carefully
selected,
etc,
etc,
and
now,
without
your
knowledge,
people
can
use,
can
insert
private
space
data
so
a
way
around
that
is
to
actually
have
a
positive
trust
anchor
for
a
sign
to
private
space
top-level
domain.
But
anyway
that's
that's.
That's
a
there's
got
to
be
an
interesting
discussion,
I'm
sure
and
so
just
to
paint
the
back
shed
a
little
bit.
I'm
gonna
use
suggest
set
set
for
private
use
names.
It
can
be
any
of
these
42,
but
I
thought
that
set
was
the
cutest.
X
X
X
Finish
this
one
up
is
my
last
slide,
so
let's
move
the
discussion
if
it's
takes
too
long
to
be
e
to
the
mailing
list
and
if,
but
only
if
there
are
sufficient
interest
and
then
hopefully
by
the
next
ITF
I
I
can
ask
the
working
group
chairs
because
that's
that's
the
process.
I'll
actually
work
working
your
chairs
to
see,
if
there's
enough
consensus,
to
adopt
this
as
a
working
group
item
and
if
that's
the
case,
if
it's
a
working
group
item,
then
the
real
work
starts.
X
Q
Warren
so
Warren
Kumari
Google
I've
got
lots
of
thoughts
on
this
I'll
try
and
keep
them
short,
so
I,
definitely
I'm
just
I'm
half-deaf
sure,
there's
something
in
the
back
here.
Sure
I'll
try
to
talk
better,
yes,
so
I
mean
I,
definitely
understand
and
agree
that
we
need
some
sort
of
internal
namespace,
a
way
to
carve
a
foot
set
of
name
space
enough
that
back
in
2017
I
wrote
a
document
suggesting
we
do
something
like
this
and
I
called
it.
Q
Taut
internal,
the
I,
brought
along
two
DNS
up
and
DNS
up
largely
stood
up
and
said,
sounds
like
a
finite,
but
this
is
my
recollection
sounds
like
a
fine
idea.
Don't
do
it
here.
This
is
not
a
special
use
domain
name,
it
does
not
require
special
use
handling.
This
should
go
to
I
can
and
so
I
took
it
to
I.
Can
not
it
hasn't,
really
progressed
progressed
there
yet.
But
you
know
the
last
time
this
came
up.
Dns
table
said
sounds
interesting.
Not
here.
I'm
gonna,.
H
X
Right
otherwise,
I
need
to
remember
all
the
point,
so
I'm
I'm
I'm,
very
well
aware
of
of
the
dolls
internal
documents
and
them
and
I'm
in
favor,
of
having
something
private
spacey
that
then
there's
a
fundamental
difference
right
and
be,
and
that's
what
I'm
trying
to
make
here
is.
The
fundamental
difference
is
the
semantic
meaning
in
a
very
long
internal
plus.
The
other
thing
is
I
think
the
document
requires
currently
to
have
it
delegate
it
and
I'm,
not
sure,
and
this
sure
this
is
slightly.
Q
Different
but
go
ahead
next
point
yeah
on
the
specific
string.
I
think
that
a
semantically
meaningful
string
is
sadly
important.
You
know
it
doesn't
really
matter
what
the
semantics
string
is
maybe
actually
having
a
couple,
but
the
reason
that
people
have
chosen,
whatever
names
they
have
chosen
is
because
they
want
it
to
be
somewhat
descriptive.
Q
Okay,
I
think
that
that's
a
place
where
we're
going
to
disagree
yeah
if
people
would
use
you
know
the
reason
people
have
used
blah
blah
blah
Corp
is
because
they
wanted
to
describe
something
blah,
blah
blah,
Zizi
I.
Think
it's
just
going
to
be
confusing
to
the
average
user.
I
also
think
that
this
does
require
a
in
some
sort
of
delegation
and
it
needs
to
be
an
insecure
delegation.
We
can
have
a
long,
a
discussion
on
the
mailing
list
about
why
basically
I
want
something
to
go
forward.
Q
A
As
far
as
the
chairs
are
concerned,
the
IETF
does
not
have
the
ability
to
declare
what
will
or
will
not
go
into
the
root
zone
and
any
further
discussion
of
this
document
and
its
purpose
in
the
IETF
has
to
take
into
account
the
fact
that
the
IETF
does
not
decide
what
goes
into
or
does
not
go
into
the
root
zone
so
that
division
of
I
think
I
think
what
is
saying
what
is
hung
us
up
before
on
the
point
that
Warren
just
made
about.
Where
do
you
talk
and
where
do
you
do
these
things?
A
B
Z
Z
Icann
has
made
decisions
about
what
goes
in
the
root
zone,
specifically
following
ISO
3166,
which
means
that
these
two
letter
codes
will
never
go
in
the
root
zone.
Now,
if
we
can
have
a
discussion
with
ICANN
and
clarify
that,
that
really
is
the
position
I
can
hold,
then
that
creates
some
to
letter
codes
that
we
know
will
not
cause
a
conflict,
and
that
is
a
wonderful
observation
and
and
would
avoid,
would
have
avoided
not
a
lot
of
fighting.
So
first,
let
me
thank
you
for
that.
Z
One,
quick
terminology
suggestion
where
you
talk
about
private
DNS,
there's
a
lot
of
talk
here
at
ITF
about
DNS
privacy
DNS
over
TLS
DNS
over
HTTPS,
the
term
private
DNS
has
kind
of
got
overloaded
to
mean
that
so
I
would
say
internal
DNS.
For
what
your
talk
might
we're
a
school
or
university
or
company
has
an
internal
name.
Server
I
try
to
call
that
internal
DNS
to
distinguish
it
from
private
DNS.
Z
So
that's
just
a
terminology
thing
to
avoid
confusion,
moving
forwards,
and
then
the
final
comment
I'll
make
is
where
it's
tempting,
when
you
think
about
declaring
something
for
internal
use.
Like
RFC
1918
addresses
that
you
say
you
are
free
to
do
whatever
you
want
with
this,
but
the
U
in
that
sentence
is
not
defined.
Z
So
so
it's
not
that
anybody
can
do
what
they
want.
It
is
that
the
banking
industry
is
free
to
define
their
own
standards
for
those
codes
means,
and
the
analog
he
wrote
is
that
the
IETF
has
the
responsibility
for
giving
meaning
to
those
values,
not
to
say
that
it's
a
free-for-all
and
because
saying
do
what
you
want
and
I'll
give
one
final
example
of
this
draft
I've
been
working
on
with
Warren
ipv4
only
to
Harper.
If
you
send
that
over
your
dns
over
TLS
connection
to
quad
8,
it
doesn't
know
your
local
networks,
nat64
prefix.
Z
M
I
think
the
whole
thing
could
get
very,
very
horrible
very
very
quickly,
and
we
can
also,
in
the
same
situation,
think
very,
very
horrible,
very,
very
quickly
about
whether
this
name
or
shouldn't
be
delegated,
whether
it
should
or
shouldn't
be
signed
and
I.
Think
all
those
problems
will
just
come
back
and
recur
over
and
over
again.
If
this
is
to
go
forward,
I
think
the
most
simplest
thing.
The
simplest
thing
to
do
with
this
is
Venus.
M
Unless
these
are
some
country
codes,
perhaps
not
even
less
than
we
see,
there
is
a
set
of
codes
in
the
ISO
3166
list
which
are
set
aside
for
sort
of
private
use.
If
you
want
to
use
a
private
use,
label
for
DNS
purposes,
go
to
that
list
and
pick
one,
and
then
you
piece
of
consequence
of
that
yourself.
If
you
want
to
say
that
you
figure
out
the
trust.
Thank
you
for
it.
M
If
you're
then
going
to
plug
your
network
into
somebody
else's
network,
there's
a
chance
that
both
of
those
networks
are
using
the
same
internal
private
use
label,
in
which
case
tough
I,
think
something
like
that
is
poor.
The
best
we
can
do
but
trying
to
come
up
to
see
an
informational
document
or
even
watch
the
stand.
Abstract
document
this
year,
I
think,
is
ultimately
going
to
have
the
same
problems
we
had
before
and
we're
gonna
go
further
forward.
I
think
also
make
a
reference
and
see
to
the
3166
thing.
AA
AA
Okay,
so
Terry
Madison
and
god
I
have
no
idea
what
had
to
wear
on
this.
So
let's
say
no
hats,
as
the
the
the
person
in
the
hot
seat
around
the
dot
home.
Skirmish.
I
really
like
this.
This
this
is
a
void
and
I.
When
you
introduce
this,
you
said
this
might
be
a
sensitive
political
topic.
I
actually
think
this
is
really
good
because
it
actually
avoids
political
skirmishes.
I
think
this
is
great.
It
is
pragmatic
thinking
it
is
inherently
pragmatic
and
I
love
it.
AA
X
Y
I
Okay,
first
comment
from
Peter
spot-check:
it's
not
correct
to
claim
that
there's
no
risk
of
no
risk
of
collision
collisions
will
happen
when
two
organizations
using
dot
that
set
are
being
merged
with
each
other
similar
to
RFC.
1918
main
way
of
this
document
is
documenting.
What
terrible
things
will
happen
if
you
use
dot.
X
Right
I
want
to
respond
to
them.
First
of
all,
if
there's
two
organizations
that
both
use
that
says
they're-
probably
two
organizations
that
have
to
have
an
HR
department,
two
organizations
that
have
a
financial
department,
they
will
merge
and
they
will
figure
this
out.
I
think
when
they
do
that
a
internal
top-level
domain,
like
said
that
is
the
least
of
their
problems.
So
sorry
to
be
blunt,
but
I
don't
think
that's!
That's
that's
a
real
problems
and
the
whole
idea
is
that
these
are
locally
unique
but
globally,
not
unique.
That's
that's
the
whole
point.
X
It's
the
same
way
with
RC
1918
address
space.
If
you
use
in
one
organization
and
in
the
other
organization,
you
merge
the
organization's,
you
have
that
problem,
but
thank
you
for
your
comments.
John
Clemson.
Thank
you
for
your
for
your
response,
looking
forward
to
to
engage
with
you
off
list,
but
would
work
with
very
much
your
engagement
on
the
working
Lister's
working
group
list
as
well.
Thank
you.
E
Hi
Sanjeev
Gupta.
First,
thank
you
for
a
very
well-written,
readable
draft.
It
clarifies
lots
of
issues
and
covers
the
background.
My
concern
is
actually
who
would,
since
enterprise
users
have
shown
an
unwillingness
to
use
dot
local
and,
as
you
have
shown,
this
a
lot
of
fragmentation,
dot
home
dot
private?
Who
would
actually
use
this
since
most
enterprise,
administrators,
I,
know
and
I
come
from
an
end-user
organization?
Don't
wait?
Don't
care
and
further
Microsoft's,
which
is
the
largest
deployed
Enterprise
after
Microsoft's
own
guidance
on
whether
to
use
dot,
local
and
not
to
use
dot.
E
X
First,
off
the
reason
that
people
use
different
things
now
is
because
there's
never
been
a
standard
that
explains
how
to
use.
This
does
never
be
the
best
current
practice
that
says
how
to
use
this
now.
The
only
thing
that
we
can
do
going
forward
if
there
is
such
a
documents
is
appoint
a
listening
ear
to
this
new
documents
and
we
will
see
what
the
future
brings,
but
at
least
when
people
make
their
own
things
and
basically
say
there
is
no
other
thing
now
we
would
have
of
in
the
future.
X
We
would
have
this
document,
so
that
would
be
my
point.
I,
don't
think.
There's
any
value
in
trying
to
trying
to
force
people
to
move
over
I
think
that's
impossible,
not
necessary.
Eventually,
using
this,
you
kind
of
have
some
guarantees
about
less
collisions,
for
instance,
dot
Corp,
for
instance,
dot
home.
We
all
know
that
these
have
a
few
collisions
in
the
ICANN
G&S.
Oh
sorry,
I
can
new
gTLD
space
or
a
couple
of
organizations
I've
applied
for
these.
X
Z
Into
the
microphone,
because
I
wanted
to
have
a
good
answering
that
question,
as
things
evolve
in
DNS
like
DNS,
over
TLS
Android
provides
a
setting
that
you
can
turn
on
strict
DNS
over
TLS,
and
if
the
user
enters
quad
8
as
that
DNS
server,
and
you
look
at
your
company
mail,
server,
mail,
dot,
internal,
you
fail
because
quad
8
doesn't
know
your
internal
address
of
your
internal
mail
server.
If
we
have
an
RFC
that
says
names
ending
indoors
easy,
do
not
go
over
your
TLS
public
resolver.
Z
They
have
to
go
to
the
resolver
that
you
learned
via
DHCP
or
I
six
router
advertisements.
Then
your
mail
server
does
work,
so
the
incentive
for
corporations
to
use
these
names
is
because
these
names
work
and
picking
a
random
thing
and
sending
it
to
quad.
8
doesn't
work,
so
they
all
find
out
pretty
quickly
the
benefit
of
using
something
that
has
a
document
that
defines
how
it
works
thanks.
Everyone.
