►
From YouTube: IETF106-IPSECME-20191121-1550
Description
IPSECME meeting session at IETF106
2019/11/21 1550
https://datatracker.ietf.org/meeting/106/proceedings/
A
D
C
B
C
Here's
the
note
well
I,
think
everybody
has
noted
dish
already
so
so
we
have
a
blue
seat
somewhere.
We
have
only
one
blue
suit
going
around.
So
if
you,
if
it's
not,
if
it's
a
soft
summer
wave
it
up
and
and
same
people,
can
actually
it's
coming
to
forint
the
other
side.
Now
we
have
a
one
note
taker
also
already
anybody
would
be
willing
to
do
the
other
if
you're
doing
either
part.
So
you
can
actually
just
fill
in
stuff
and
actually
it's
a
very
good
thing
to
go
there
yourself.
C
After
you
have
asked
questions,
you
can
code
fix
that
you
know
what
sore
spot
you
actually
asked
and
who
you
are
that's
quite
often
very
hard,
and
so
when
you
are
going
to
Mike,
please
say
your
name,
so
a
note-taker,
so
dull
and
poor
promise
to
be
a
chopper
scribe.
So
he
can
chop
the
cue
by
adding
some
questions.
C
C
C
Guess
not
so
there
we
go.
First
have
a
draft
at
the
center.
We
have
some
work
items
and
some
other
presentations.
Some
of
the
other
presentations
actually
are
something
that
might
be
the
work
in
the
items
also,
but
they
just
put
a
bit
arbiter
at
the
split
there.
So
the
first
one
is
the
working
group
status
report.
So
we
have
already
published
that
one
of
the
RFC
is
this
split
TNS
was
published
as
an
RFC
that
actually
happened
before
the
previous
meeting.
C
I
think
butter,
and
we
have
one
document,
implicit
IV,
that
is
in
RFC
editor
Q.
Now
we
have
requested
publication
for
quantum
restaurant
hikers
a
to
stuff
I,
don't
know
when
it's
going
to
be
in
tell
us
what
or
when
it's
going
to
be
forward,
but
we
have
finished
working
group
last
roll
call,
a
very
long
one
for
ipv4,
ipv6
codes
and
I
think
it
should
be
ready
for
publication.
We
are
getting
ready
for
the
little
Gator.
We
need
to
have
a
separate
write
up
and
then
then
we
can
post
that
forward.
C
We
have
two
documents
at
a
t'car
Oh.
Actually
one
documented
is
quite
ready.
I
think
they
I
create
an
intermediate.
It
should
be
quite
ready
for
working,
coop,
last
call
and
so
on.
For
the
labels
IPSec
I
heard
there
has
been
some
complications
going
back
and
forth,
and
an
old
or
and
back
again
I
have
a
different
design.
C
Critters
I
think
it's
mostly
because
we
don't
know
what's
a
what
kind
of
a
use
is
for,
it
is
going
to
be
so
it's
very
hard
to
design
a
protocol
when
you
don't
know
how
to
do
it,
and
then
we
have
a
three
new
documents
that
were
stood
up
to
test
work
across.
So
we
have
an
this
IP
traffic
flow
security,
and
then
we
have
a
hybrid
us,
K
and
then
GI
question
to
those
are
still.
You
know,
I
think
there
should
be
quite
ready
for
us.
C
And
let
me
have
a
here's,
our
work
items,
so
we
have
hybrid
USDA
interrupt
stuff.
Then
we
have
IP
traffic
folk
security
and
then
we
have
a
level
IV
that
what
those
IPSec
those
are
the
items
and
then
we
have
other
presentations
in
the
end.
So
I
think
that's
all
we
have
for
that.
So
we
start
with
the
first
presentation,
with
Valerie
with
interrupts
tough.
E
F
F
Was
first
it
strands
one
then,
with
modem
and
with
plus
and
we
tested
well,
all
implementations
have
implemented
Ike
intermediate
draft
and
one
implementation
fully
supported
quiz
key.
The
latest
version
and
two
implementations
put
it
partially,
but
instead
support
real
post
quantum
key
exchange
methods.
So.
F
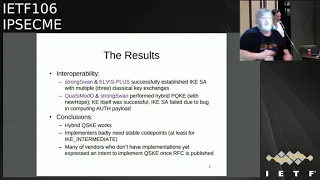
Question
no
Stefan,
no
okay,
so
the
results
we
achieved,
interoperability
with
hybrid
exchange,
but
using
only
classical
method
between
others
plus
since
transform
and
Kojima
dense,
turns
one
also
performed
some
post.
Quantum
key
exchange
method
but
say
wasn't
just
kicks
change
was
successful.
They
say
was
an
established
because
of
the
some.
C
F
And
I
codes
company
accommodation
well,
and
we
also
had
some
discussion
about
all
this
stuff,
and
so
the
conclusion
well,
first
conclusion:
is
that
or
it
works
so
I
agreed,
exchange
works
and
implementers
Bradley
need
stable
codepoints.
We
spent
quite
a
lot
of
time
compiling
our
code
because
we
had
to
set
of
temporary
code.
The
poet's
are
compatible,
of
course,
so
I
feel
that
at
least
for
I
can't
immediate
and
I
think
that
the
draft
is
old
enough.
F
G
Hi
Sean
Turner
D
plan
to
submit
this
implementation
report
to
the
implementation
report,
repository
that
the
isg
maintains
would
button
so
there's
an
ihe
there's
an
int
there's
an
implementation
report.
You
used
to
use
it
back
in
the
day
to
progress
things
from
like
ps2
internet
standard
I.
Don't
know
you
need
to
do
that
anymore,
but
it's
a
place
where
you
wrote
down
all
the
things
you
tested
the
names
of
the
implementations,
you
kind
of
put
it
up
there,
that's
another
place
to
kind
of
like
advertise.
The
fact
that
you
did
get
an
operability.
F
F
C
F
Quite
well
not
completely,
but
quite
a
lot
and
I
sense
some,
and
they
have
some
concerns
about
how
routine
is
specified
in
the
specification.
So
we
had
some
discussion
is
a
sense
that
they
probably
will
sink
a
little
bit
and
if
we
get
rid
of
nonsense
and
they
use
a
dedicated
exchange
type
for
for
follow-up
regime,
they
they
will.
F
Probably
it
is
ok
with
them,
so
I
will
check
with
my
co-authors,
because
well
we
have
some
discussion
with
cause
before
I
achieve
meeting,
but
we
decided
to
postpone
any
change
because
the
draft
was
in
the
adoption
state
and
we
didn't
want
to
compute
to
confuse
people
who
reads
draft
with
some
latest
changes
or
a
new
version.
You
know
that
once
the
draft
is
adopted,
I
sends
that
well.
I
think
that
there's
no
big
objection-
and
there
is
a
consensus
month
calls-
is
that
a
new
dedicated
exchange
type
with
pages
in
your
using
information
exchange.
F
F
Rid
of
all
additional
exchanges,
I
chose
it
with
simplify
that's
responses
from
initial
exchange.
Well
after
Zeta,
since
its
transform
agrees
it
it's
it's
a
way
to
go
if
anyway,
well
I
think
the
draft
must
be
discussed
on
saliste,
so
I
solicit
any
review
in
discussion,
because
it
was
not
very
many
comments
on
the
draft
and
unfortunately
so
most
and
most
discussion
among
the
causes.
So
just
if
you
have
some
opinion,
please
bring
to
the
list.
F
H
H
We
did
the
adoption
call
and
recently
for
this
draft,
and
we
also
during
that
same
time
we
also
had
some
suggested
new
charter
text,
because
we
need
to
do
that
to
officially
adopt
the
work
so
that
the
text
seemed
to
be
okay
with
everybody,
and
the
adoption
call
was
issued
to
sort
of
reduce
the
amount
of
process
time
overhead
right
so
just
run
it
in
parallel
and
make
them
contingent
that's
what
the
star
is
about
anyway,
the
the
we
got.
We
had
good
support
and
yeah
so
past
the
adoption
call
we
did
get
some
comments.
H
So
that's
what
this
presentation
is
going
to
be
is
covering
those
comments.
So
one
set
of
comments
we
got
was.
It
was
a
good
starting
point
would
like
to
see
more
analysis
on
fragmentation.
That's
act.
We're
actively
doing
that
right
now,
so
hoping
to
have
something
before
the
next
IETF.
You
know
some
analysis
on
that.
I've
coded
this
with
it.
You
know
even
with
an
option,
to
turn
fragmentation
on
and
off.
You
know
in
configuration,
so
you
know,
there's
real.
You
know
we
plan
to
do
this
analysis.
H
There's
also
some
static
analysis
we
can
do
just
based
on
you
know
what
kind
of
line
utilization
based
on
I
mix
you
know
if
we're
having
to
pad
out
and
rather
than
split
across
payloads,
has
the
effect
of
congestion
control
on
the
tunnel
with
CC
traffic
I
talked
to
David.
Black
and
I
also
went
to
a
side
meeting
this
time
where
this,
the
idea
of
whether
there
is
any
sort
of
feedback
loops
or
oscillations.
H
H
H
That
case
is
not
as
decoupled
as
ours,
so
it's
not
deadly,
but
I,
don't
know
how
good
the
Open
VPN
cases
so,
whatever
we
don't
like
Open
VPN
here,
also
be
aware
of
how
this
lines
with
quick
I
when
I
first
read
this
I
thought
it
was
talking
about
packet,
alignments
and
colleague
of
mine,
Lou
Berger
mentioned
no,
that's
probably
not
what
they
meant.
They
probably
meant
pay
more.
H
You
know
just
pay
attention
to
what's
going
on
and
quick
to
make
sure
that
III
don't
know
so
I
would
like
some
clarification
on
what
what
that
was
particularly
about
moving
forward
okay.
So
the
next
comment
was
a
good
starting
point
and
that
it
was
IP.
Number
allocation
was
scary.
This
was
from
Paul,
but
there
was
a
misunderstanding:
I
thought
we
were
actually
trying
to
replace
ESP,
so
we
were
trying
to
allocate
a
whole
new
IP
payload.
That
isn't
the
case.
It's
just
the
the
scope
of
the
ESP
payload
type.
H
H
That
is,
in
fact
the
case.
If
you
use
the
the
TFS
header,
you
know
you
don't
actually
have
and
we're
we've
written
the
draft
in
a
way
such
that
you
don't
actually
have
to
send
things
at
a
constant
rate.
You
don't
you
could
send
them
on
demand
if
you
want
right,
there's
nothing
that
requires
the
constant
rate
send.
H
So
what
do?
What
do
we
have?
What
are
we
updated?
We've
up?
Where
are
what
are
we
looking
to
update
we're
looking
at
interpet
inter
packet
alignment,
you
know
when
you
have
aggregated
packets
inside
a
payload,
I
coding
this
personally,
you
know
looking
at
some
white
box
code
and
stuff,
there's
a
lot
of
assumptions
about
header
alignment.
H
You
know
because
typically
device
drivers
will
move
the
into
bytes
so
that
the
IP
header
is,
you
know,
32
bit,
aligned
right
and
then
based
on
that
fact,
a
lot
of
code
is
written
so
that
when
it
looks
up
a
length
that
it's
just
grabbing
it
as
you
and
16,
which
of
course
is
going
to
cause
an
exception
on
the
processor,
if
that's
odd,
byte
aligned,
so
you
know
I,
don't
know
if
we
should
be
changing
wire
formats
to
compensate
for
you
know
questionable
code
practices.
But
you
know
it's
worth
thinking
about.
H
Asics,
don't
care
about
this
right,
I
mean
Asics,
they
don't
care,
so
it
you
know.
So
that's
something
that
it's
an
open
issue
to
think
about
and
yeah
and
then
the
only
other
thing
is
that
we
we
do.
We
are
planning
to
open
sources.
We
want
to
get
the
full
implementation
written,
including
the
congestion
control
and
an
IQ
moment
ation
and
then,
as
soon
as
that's
done,
which
you
know
should
be
in
2020.
We're
hoping
early
2020
will
push
this
out
and
we're
totally
open
to
collaborating
and
doing
interoperability
testing.
The
folks.
F
F
H
F
H
We
have
a
sort
of
this
sort
of
analogy
to
like
security
modes
where
we
have,
if
you
think
about
them
like
a
knob
right
like
of
how
secure
things
are
right.
Transport
mode
is
like
the
least
secure
right
and
then
because
you're
giving
away
the
source
and
destination,
then
you
like
turn
the
knob
to
like
one
right
and
that's
tunnel
mode,
we're
now
at
least
you're
hiding
the
source
and
destination.
And
then
then
you
start
talking
about
traffic
analysis
right.
H
F
H
F
H
H
H
I
Benkei
duck
I
guess:
I
have
two
points
now
so
I
mean
I.
Think
an
IP
number
is
like
kind
of
a
big
deal.
We
do
inside
the
isg
say:
hey
guys.
We
got
this
draft
that
wants
to
allocate
a
ipv4
number
and
then
like
it's
kind
of
something
that
that
could
be
a
big
deal
in
terms
of
you
know,
people
think
it's
yeah.
H
I
People
heads-up
and
then
the
other
one
was
relating
to
the
alignment
question
which
I
have
to
apologize
for
having
not
worth
the
draft
but
I
think
the
sort
of
general
sense
I
get
from
the
the
general
around
the
ITF
as
a
whole.
Is
that
like,
if
we
have
to
be
adding
new
protocol
machinery
to
our
stuff,
to
like
add
a
variable
length
padding
just
so
we
can
alignment
like
there's,
not
a
whole
lot
of
desire
to
be
able
to
do
that.
I
But
if
it's
just
a
matter
of
well,
do
we
have
an
octave
of
padding
in
here
so
that
all
of
the
fields
have
the
same
alignment
and-
and
it's
not
like
I-
have
one
field:
that's
alignment
once
it
even
and
another
field.
Let's
line
the
odd
and
like
screw,
you
implementers
like
if
we
can
just
make
up
something
very
simple:
yeah.
I
C
Doc,
you
said
for
the
protocol
number
as
we
need
it
only
into
the
ESP
trailer.
We
can
actually
there's
a
couple
of
ways
to
do
without
it.
One
of
the
things
is
that
we
can
I
think
there
is
currently
there's
protocol
number
zero,
which
is
used
for
all
kind
of
weird
purposes,
meaning
no
prophet
are
gonna,
be
actually
using
it
Ike.
We
say
that
there
is
no
protocol,
number
it's
any
and
and
if
you
negotiate
you
know,
protocol
operator
number
is
zero.
It
means
that
there
is
no
practical
number.
It's
any
practical.
C
It's
okay
and
I
think
ipv6
uses
its
first
up
for
some
similar
uses
where
it's
actually
never
in
the
real.
You
know
protocol
field,
but
it's
used
for
internal
purposes,
so
we
could
have
just
say:
okay,
we
don't
have
any
real
protocol
number
there,
because
there
are
these
multiple
pockets
inside
and
then
you
can
have.
C
The
real
protocol
number
is
because
you
have
your
header
there,
it's
half
the
length
of
the
payload
and
you
have
to
have
you
know
it's
it's
pocket
inside
has
to
have
a
you
know
real
protocol
number
anyway,
so
you
could
have.
You
know
just
you
know
you
don't
need
to
have
anything
in
the
trailer.
The
other
option
is
to
use
wrapped
ESP,
which
is
we
haven't
program,
embroidery
for
ESP
for
the
property
PVCs
ESP,
with
four
octet
extra
header
in
the
ESP
before
the
payload,
which
tells
at
least
the
pocket
encrypted.
C
How
long
the
10
trailer
is,
how
long
the
header
is
and
so
on,
and
there's
a
couple
of
research-based
which
we
could
have
just
used,
one
bits
and
say:
oh,
this
is
this
is
pocket
that
has
multiple
pockets
inside,
so
the
format
is
going
to
be
different
and,
of
course
the
third
option
is
to
say
that.
Okay,
because
we
negotiate,
we
always
negotiate
these
use
of
these
in
Ike.
We
can
always
say
that
these
for
this
essay,
the
traffic
is
always
going
to
be.
C
This
kind
of
you
know
multiplex
traffic's,
which
means
that
we
have
we
actually
just
can.
You
know
say
that,
okay,
that
protocol
number,
if
the
first
final
protocol
number,
is
ignored
because
it
doesn't
have
any
meaning.
You
know
we
have
to
anyway.
Code,
true
to
the
protocol
number
is
usually
mean
poor
for
checking
the
police
and
so
on,
and
here
we
don't,
we
actually
have
to
do
policy
checking
for
his
payload.
They
are
not
caring
about
the
applier
stuff.
H
J
C
If
he
put
that,
when
I
would
put
that
as
an
outer,
so
the
real
IP
header
there
would
have
entrapped
ESP
and
if
we
have
actually
you
know
the
extra
you
know,
header
of
the
wrapped,
yet
V
and
if
there's
four
bytes
of
header
in
there,
so
that
would
actually
have
a
bit
saying
that
we
got
actually
shared
one
more
bit
there
saying
that
oh
there's
three
bits
used
on
a
file,
four
bits
well
or
actually
I.
Think
for
you
stand
for
left.
Just
would
one
reserved
bit
to
say
that,
though
this
is
to
this.
C
I'd
like
to
make
a
suggestion,
so
rep
ESB
RFC
actually
has
this.
It
actually
defines
how
to
do.
That's
in
UDP
etiquette,
so
see
what
it
does.
It
actually
used
one
of
the
magic
spi
numbers
so
instead
of
having
all
zeros
like
you
have
like
traffic
or
we
have
a
realized,
VI
number,
it
has
I
think
SP
number
2
means
that,
oh,
it's
a
wrapper
DSP
and
the
next
four
bytes
is
the
header.
So
so
it
actually
ordered
that's.
Actually
one
of
the
things
I
was
think
about
drop
ESP.
C
H
I
mentioned
earlier
coming
up
that
you
know
that
we
so
first
of
all,
IPSec
is
a
pretty
big
deal
right,
so
we
shouldn't
necessarily
be
so
scared
about
asking
for
a
single
IP
number
and
and
also
we
do
have
the
ability
to
once
this.
You
know
once
we
get
the
Charter
text
in
it
and
we
and
we
have
an
official
working
group
document.
We
are
allowed
to
ask
for
early
allocation,
so
we
can
float
a
trial
balloon
here.
Right
I
mean
we're
able
to
go
at
once.
H
J
B
I'm
hearing
in
the
room
is
that
we
should
at
least
investigate
some
options
before
we
we
make
the
allocation
request
zero.
Maybe
it
would
be
useful
if
you
could
send
some
examples
to
the
list
being
a
chair.
That's
stepping
down,
I
can
assign
work
and
then
that
doesn't
come,
but
it
would
be.
It
would
actually
I
think
be
useful
for
that.
Okay,.
B
K
K
K
This
actually
the
second
proposal
already
no
okay,
sorry!
So
no!
This
is
the
first
proposal.
It's
a
it's
a
TS
type,
it's
a
traffic
sector
type
where
we
just
put
in
the
security
label
and
the
length-
and
it
was
very
simple
and
was
a
new
traffic
selector
in
addition
to
the
existing
ones.
And
then
problems
came
up
because
people
said
well.
This
really
changes
the
core
ahrefs.
You
know
how
we
select
these
these
traffic
selector
types.
K
So
then
Tero
came
up
with
a
brilliant
idea,
like
oh,
let's
just
merge
them
into
new
traffic
selector.
So,
instead
of
adding
one
new
one,
we'll
add
one
new
one:
5pv
401
u1
556
and
if
there's
ever
a
new
type
of
traffic
slack
to
add
one
more
type,
so
you
would
basically
copy
all
the
traffic's
like
the
types
we
have
but
add
ones
with
and
without
the
security
level,
and
so
some
people,
like
it,
some
people
didn't
and
that
change
over
time
as
well.
K
K
So
how
does
this
new
Koshien
really
happen,
and
do
we
really
need
a
traffic
selector?
So
one
of
the
issues
is
also
with
the
narrowing
you
can
do
if
someone
requests
something
and
puts
in
a
traffic
selector
off
a
security
label
and
then
the
other
end
eater
doesn't
support
it
or
the
other
and
doesn't
want
to
use
it.
They'll
return
a
narrow
down
proposal
without
the
traffic
selector,
but
they
have
installed
the
SI
and
now
the
other
end
might
have
say.
Oh
I
actually
really
didn't
like
this,
so
the
initiator
then
goes
like
I.
K
Don't
like
this
narrowed
set.
So
now
I
have
to
send
it
delete
and
then
try
without
the
label
and
maybe
see
if
they
like
that
or
like
so
so
it
really
complicates
how
this
negotiation
is
done,
and
then
we
got
thinking
well,
we
could
we
could
send
and
notify
to
at
least
say:
hey
we'd
like
to
use
this
this
security
label
and
then,
of
course,
next
question
quickly
became
well.
K
If
we're
sending
a
notify,
we
might
as
well
put
the
label
in
and
notify,
not
use
a
traffic
select
and
avoid
all
these
issues,
because
we
also
did
a
quick
check
on
on
the
code
bases
that
we
could
look
at.
Do
people
actually
properly
narrow
down
traffic
slack
too.
So,
if
you
see
an
unknown
on,
do
you
actually
just
drop
it
from
the
from
the
set
and
continue
to
negotiate
the
SI?
Without
that
traffic's,
like
the
type
and
the
answer
is
I,
haven't
seen
a
single
implementation,
a
does.
That's
the
old.
K
K
F
Well,
it
is
mostly
for
this
plus
I
think
that
well,
a
second
object.
Second
bullet
is
definitely
not
an
option,
because
it's
a
well
traffic
selectors
individual
selectors
in
traffic
selectors
interpret
it
as
a
logical
or
so
that,
if
you
knew
these
types
it
will,
it
will
express
only
security
label
it.
You
cannot
combine
this
right.
F
You
know
don't
or
a
new
witch
before
plus
the
Clara,
v6
plastic
label
and
I
think
that
the
third
option
is
most
most
I.
Don't
know
right
from
formal
point
of
view,
from
not
from
practical
but
from
theoretical
point
of
view,
but
from
practical
point
of
view,
I
agree
that
it
leads
to
explosion
of
traffic.
F
You
just
copy
all
the
current
current
selectors
that
are
too
tight
there
before
hundred
six
and
add
them
security
label,
and
if
you
later
want
to
add
some
something
else
we
need
to
multiply
it,
but
so
so
probably
in
unity.
Fiber
load
is
some
kind
of
compromise
in
this
situation,
I
think
it's
probably
way
to
go.
L
L
K
J
Michael
Richardson,
so
I,
I,
I'm
gonna,
say
that
I
don't
haven't,
formed
an
opinion
as
to
which
is
the
the
best
choice
here.
But
my
opinion
would
be
formed
by
considering
two
things
and
I
have
a
question
as
a
result,
which
is
how
would
a
an
implementation
which
doesn't
implement
labeling
respond
to
these
three
things,
and
that
leads
to
my
question,
which
is:
is
it
useful
for
accept
in
a
transition
upgrade
period?
K
J
Failure
and
they
wouldn't
set
up
any
tunnel
correct
right.
So
then
I
would
say
that
it
really
doesn't
matter
that
much
because
the
end
in
the
end
requesting
the
label
is
going
to
have
to
deal
with
whatever
a
failure
comes
back
as
opposed
to
you
know,
saying:
oh
you
picked
the
TS
without
the
label
are
all
to
go
that
way.
J
Then,
if
you
like,
okay
and
and
and
all
I
can
see
the
situation
where
you
might,
you
know,
upgrade
things
incrementally,
and
you
want
to
turn
on
the
policy
and
as
soon
as
it's
all
there,
everyone's
happy
I,
don't
know
if
that,
if
your
use
case
really
supports
that
scenario,
I
think
you
turn
it
on
the
whole
network.
Once
the
network's
ready
you
you
go
to
label
and
until
then
the
network's
not
labeled,
right
right,
yeah,
that's
what
I
think
is
the
case.
J
It's
not
like
you
know,
other
I
think
other
things
where
you
want
to
go.
Oh,
let's
go
for
go
to
aes-256
next
week,
but
you
know
128
will
be
good
enough
for
the
next
week
right,
it's
okay
right.
We
still
want
transmit.
So
that's
my
take
on
it
is
is
what
will
be
easier
for
you
to
determine
if
the
other
end
doesn't
doesn't
agree
and
pick
that
right,
but.
K
C
Both
cases
very
okay,
if
you
have
a
checker,
if
you
propose
something
that
normal
ipv4
and
I
believe
for
PostSecret
label,
that
gives
an
option
for
the
other
and
to
speak,
which
one
of
Anna.
Can
you
allowing
that
for
your
policy?
If
you
only
propose
ipv4,
plus
sec
ylabel?
That
means
that
you
only
allow
that
in
your
policy
and
eat
that
will
actually
be
better
proposed
it.
The
other.
C
One
will
immediately
feel
that
if
he
doesn't
support
actually
say
clay
plus,
because
he
doesn't
have
any
traffic
lights
selector,
it
could
be,
it
would
say,
traction
traffic,
second,
unavailable
or
unacceptable
exotic.
So
so
that
way
actually
gives
you
immediate
error.
Instead
of
you
getting
back
essay
that
you
have
to
immediately
delete
because
it
didn't
have
to
notify.
So
that's
also
I
write
right
this
guy
right,
like
this
kind
of
explicit
you
know
cases
where
you
actually
get
them.
C
You
can
propose
either
with
the
traffic
selector
it
select
with
sick
libel
or
without
or
both
and
you
you
know,
the
other
one
can
decide
what
you
propose
to
tell
us
what
you
want
and
what
the
other
one
responses
tell
us
what
he
wants,
and
there
is,
you
know,
either
get
an
error
or
you
get
an
essay
that
you're
gonna
use
notifies.
The
problem
is
a
feed.
C
We
don't
get
that
C,
so
you're
advertising
for
the
third
options,
though
yeah
the
one
that
we
saw,
I,
believe
four
plus
sec,
ylabel
and
I,
don't
think
we
are
going
to
be
adding
that
many
of
those
new
things
intersect
later.
The
other
things
we
had
earlier
discussion
was
to
how
to
secular
political
to
be
used.
How
is
it
strain?
Is
it
number
or
is
it
software
that
can
be?
K
C
C
C
Yeah,
that's
that's
possible,
yes,
but
you
still
return
actually
the
whole
thing
right,
your
god
franca.
It
says
it's
the
same
thing
with
the
you
know
like
we
have
a
protocol
field
you
have
to
accept.
If
the
protocol
field
is
anything
else
and
zero,
you
have
the
accept
X
that
exact
protocol
number.
You
can't
do
anything
else.
Yeah.
I
You're
good
benkei
doc.
You
have
notes
on
jabber
that
the
notify
payload
could
be
better
because
nobody
has
ever
really
defined
new
traffic
selector
types,
and
we
know
that
implementations
can
handle
unknown
notification
types,
but
they
might
choke
on
an
unknown
traffic.
Electric-Types
right,
that's
true!.
C
E
E
K
B
C
They're,
given
it
I
think
the
bad
idea
about
the
bad
thing
about
the
notifies
is
that
you
get
an
essay
created,
even
if
you
don't
want
it
and
you
have
to
delete
it
and
there's
all
kind
of
race
conditions,
because
oh,
oh
I
have
an
essay
up.
I
have
a
traffic
cone,
oh
no,
no,
no
I
can't
use
that
I
said
even
if
it's
created
I
need
to
delete
it
immediately,
but
I
can
delete
it
before
I
get
response
back
and
you
have
to
block
manually
block.
C
You
know
things
so
that
doesn't
leak
out
in
the
essay
that
it's
not
allowing
it
and
another
thing
in
all
of
the
cases
you
need
to
have
a
new
cone
in
your
traffic
selector.
You
know
code.
If
you
are
going
to
be
implementing
it,
I
mean
everybody
who's
going
to
be
plus
label.
Odd
cycles
are
going
to
be
modifying
their.
You
know,
code
anyway,
so
adding
the
code
for
traffic
selector
support
theories
to
be
smart
is
something
that
you
should
be
doing
anyway,
and
you
shouldn't
be
proposing
these
to
anybody.
Who
is
it
not
really?
B
K
C
J
B
K
N
Day
is
a
quick
recap:
our
purpose
is
to
optimize
unnecessary
pillows
at
every
King
essays,
including
two
or
meet
essay
payloads
at
every
King
I
KSA's,
and
to
omit
essay
mps
pillows
at
a
routine
child
essays.
Why
we
can
do
that
is
because
configurations
may
not
change
a
frequent
frequently
and
the
SI
NTS
pillows
at
every
King
essays
will
be
the
same
and
add
the
ones
that
create
creating
essays.
So
as
the
pillows
are
the
same,
so
we
can
just
use
a
previous
as
ints
pillows,
instead
of
instead
of
sending
them
again
at
a
routine.
N
N
According
to
the
opinions
last
meeting,
we
make
the
draft
the
optimization
some
simple,
simpler.
So
first
we
make
the
IKS
a
working,
optimization
and
the
child
I
say
working
optimization
optional.
It
means
that
it's
up
to
the
implementer,
to
optimize,
IPSS,
routing
or
just
child
I,
say
a
king
or
both
these
cases,
and
if
you
don't
think
I
can
say,
weekends
optimization
is
insane
sure
you
can
just
don't
talk
to
my
debt
and
for
the
optimization
processes.
N
N
Finally,
here
is
a
whole
overview,
our
the
overview
of
our
whole
solution.
First
in
the
negotiate
negotiate
of
the
support
of
this
optimization
between
the
initiator
and
the
responder.
By
sending
the
new
notification
at
a
Keo
message
exchange
after
negotiation,
there
are
two
optional
implementation:
is
the
optimizing,
the
IKS
a
working
and
optimizing
the
child
sa
routines
and
for
each
cases
they
are
all
they
are
all
both
contains
two
sub
cases
and
as
I
just
described
it
it
before.
So
this
is
a
overview
about
the
future
plan.
K
Can
you
go
back
one
slide
because
that's
okay,
everything
right,
so
what
I?
Don't
like
sorry,
pal
I'll,
just
read
it!
What
I
don't
like
about
this
proposal
is
the
part
where
you
initiate
a
consent,
the
unchanged
as
a
notify,
saying
it's
doing
the
one
without
the
traffic
selectors
and
the
responder
can
decide,
based
on
whatever
reasons
that
I,
don't
I,
don't
like.
There's
no
proposal
chosen
because
now
I've
got
a
failed,
Ricky
and
I
would
much
rather
have
to
know
beforehand.
Where
I
can
do
this
proposal
or
not
before
doing
it.
N
Actually,
the
second
you
mean
the
second
case,
why
the
responder
we
are
rejected.
This
optimization
is.
We
think
that
you
are
for
some
products
we
usually
well.
If
the
configuration
changes
on
the
responder
side,
usually
the
responder
will
initiate
the
Rakeem
process
immediately,
but
as
this
is
not
a
mastered
in
the
RFC,
so
for
some
products
they
may
not
do
this
immediately.
They
will
wait
for
the
Rakeem
period
when
the
time
when
the
routine
times
out
they
the
responders
just
initiated
Larry
King.
N
K
K
J
The
case
where
my
clear
so
take
the
case
that
the
initial
policy
on
the
initiator
was
AES,
128
or
AES
256
and
they
agreed
and
the
responders
and
configuration
was
128,
so
they
agreed.
Okay,
life
went
on,
but
now
on.
The
responder
they've
now
changed
the
configuration
to
AES
256,
which
would
still
be
acceptable
to
the
initiator.
J
K
J
K
And,
and
if
you
want
to
split
this
and
say,
I
want
one
for
two
to
show:
support
for
Ike
and
I
won't
want
to
suppose
to
support
the
child.
I
say,
and
that's
probably
better
so
that
you
can
decide
what
you
want
to
do.
But
I
don't
like
this
like,
like
you.
Have
this
configuration
and
I
understand,
you're
reloading
the
confirmation
and
you
don't
want
to
kill
a
hundred
thousand
tunnels,
but
but
you
can't
just
like
change
all
the
parameters
and
accept
initiator
to
continue.
F
C
F
Lot
of
optimization,
because
if
you
put,
if
you
do
it,
just
usually
like
a
Saluki
and
put
in
a
safe
below
just
the
same
algorithms
that
are
used
for
I
could
say
it
will
be
a
dozen
of
whites
and
probably
thirty
twenty
bytes,
and
you
replace
this
twenty.
But
who
is
eight
bite
of
a
dental
notification?
So
it's
very
small
wing
and
die
Casa
Liki
happens
very.
F
It's
it's.
It's
not
well,
I,
don't
think
a
big
optimization
for
childís
Araki's.
It's
probably
slightly
different
situation
because
you
need
to
move
the
traffic
selector
and
traffic.
Selector
can
be
quite
complex
and
very
long,
and
if
you
immediately
it
probably
it
will
probably
give
you
some
save
in
size,
but
I
think
that
for
I,
Kosair
kids,
it's
not
worse
to
complicate
so
please
think
was
it's
possible
to
simplify
IQ
drop
just
meet
you
like
a
say,
Ricky,
probably
a
meeting.
F
N
H
I,
you
know
thinking
about
this
it
and
what,
with
the
discussion
that
just
happened,
isn't
it
just
possible
that
this
is
over
engineered
like
you
can
still
get
this
optimization,
but
why?
Why
try
to
make
it
so
fancy
right,
like
it
just
tear
the
essays
down?
If
you
have
a
configuration
change
right
so
then
you
don't
have
to
have
all
these
different
moving
parts.
You
know
the
optimization
if
it's
really
cheap
to
implement,
then
it's
nice
right,
I
mean
you're
talking
about
83
things
a
second
and
in
the
whole
network
right.
So
how
much?
H
K
I
know
the
once
a
thing
just
like
I
said
it
last
time:
I
do
think
for
the
child.
Let's
say
it's
really
useful,
because
not
only
are
you
saving
a
number
of
bytes,
you
also
save
processing
all
the
traffic
slackers,
because
you
have
them
already.
You
don't
have
to
verify
that
the
selectors
are
the
same
as
once
you
had
installed
before
so
actually,
I,
really
like
it
from
the
child's
day
because,
like
we
could
all
use
this
per
default
to
make
our
code
easier.
It's
not
just
on
some
high-performance
server
and
and
I.
C
They're
equivalent
I
don't
like
to
get
because
it
says
options.
This
adds
more
options
that
to
be
doing
and
and
options
are
always
bad
because
we
get
said
if
this
would
have
been
proposed.
When
we
were
making
guy
question
two
we
could
have.
We
could
have
said
in
that
version.
2,
you
never
ever
sent
s
a
pellet
or
traffic
splat
selectors
ever
in
Ricki's,
and
that
would
be
very
simple
and
would
solve
the
problem
now.
I
don't
want
to
have
all
we
have
to
write
this
code
and
we
have
this.
C
You
know
we
stuff
always
say
unchanged.
Oh,
do
we
have
to
do
that
and
if
it's
at
its
new
option,
so
there
has
to
be
tested
and
that's
why
I
mean
we
have
way
too
many
options
already
there
we
have
a
resumption.
We
have
all
kind
of.
We
have
lots
of
things
that
have
text
that
I
just
want
to.
Have
you
know
extra
thing,
especially
even
you
will
say:
oh
it
can
happen
every
20
minutes,
but
it
has.
When
did
that
every
20
minutes
means
it
happens,
every
4
gigabytes.
C
I
N
Yeah
before
after
last,
the
meeting
and
the
IPR
has
disclosed
clammed
on
this
draft
and
I
think
there
are
many
drafts.
Many
are
pcs
in
ITF
that
they
have
the
same
IPR
come
so
I,
don't
think
it's
very
a
big
big
problem
for
considering
IP,
ours
and
but
I,
don't
know
what
people
will
think
about
it.
Yeah
I
mean.
B
G
C
Most
of
the
other
IPRs
we
have
our
actually
don't
require
to
conduct
contact.
They
usually
say
that
we
are
defensively.
If,
if
you
sue
us,
then
we
can
use
this
to
against
you,
but
this
set
where
you
require
them
to
you
know
the
talk
to
the
you
know:
IPR
owners
before
you
can
implement
or
use
it
in
the
code.
That's
actually
is
annoying.
C
First,
for
the
eighties
eighties,
wake
up
so
so
question
is
that
I
think
this
might
be
part
of
our
Charter
or
Mike.
Not
the
question
there
is
that,
because
we
have
in
the
Charter,
we
have
text
saying
that
we
are
doing
optimizations,
for
you
know
something
like
that.
I
think
it's
like
generic
stuff,
and
these
could
be
part
of
that
or
it
could
be
separate.
So
that's
actually
first
I
think
we
need
to
decide
I
remember
last
time
we
were
think
about
this
enemies.
I
C
C
C
K
C
Know
that,
but
we
had
also,
we
have
also
in
the
Charter
texted
saying
that
we
actually
try
to
charge.
We
I
think
we
have
texture
settings
that
we
always
try
to
charter
everything
or
thing
we
actually
do
you
don't
adopt
anything
that
this
is
not
in
charge
but
anyway,
so
so,
but
we
can
actually
do
the
adoption
call
anyway
in
the
we
have
to
do
it
anyway
in
the
working
group
banging
is
so
there
is
no
part
of
200
every.
C
We
will
discuss
about
the
chartering
issues
first,
and
you
know
then
have
the
discussion
later
about
this.
Adopting
this
way.
The
next
presentation
problem
is
that
Paul
again
and
we
are
running
out
of
time
a
little
bit
or
behind
the
schedule
so
try
to
be
first
I
know
you
want
to
talk
about
that
sure.
Fine,
fine
I'll
also
do
only
do
this.
One
slide.
K
K
K
His
documents
so
I've
removed
that
from
the
document
I
let
the
references
to
the
documents
in
everything
we
do
so
if
it
said
something
like
you
know,
we're
obsoleting
this
and
then
it
instructs
Ayana
to
actually
say
to
clarify
whether
this
was
obsolete,
it
or
deprecated,
and
the
existing
RFC's
or
in
this
new.
This
new
document
and
I
spoke
to
taro
a
couple
of
days
ago,
so
we
quickly
made
another
change
and
I
submitted.
K
That
yesterday
is
that
we're
actually
formally
asking
to
close
those
two
old
IQ
unrelated
registries,
so
that
no
one
can
ever
do
that
now,
informally,
we've
already,
you
know,
acted
like
this
for
many
years
that
we
don't
add
anything
new
there,
but
if
we're
doing
an
RFC
damn
you
might
as
well.
Officially
close
these
registries.
O
Dan
Harkins
I
noticed
in
the
draft.
It
says
you
know:
I
v1
must
not
be
deployed
and
I'm
not
really
sure
that
we
can
say
that
any
more
than
we
could
say
like
you
know,
you
must
reduce
your
carbon
footprint
or
you.
You
must
not
take
drugs
or
something
like
that.
It,
we
don't
really
have
the
authority
to
well.
We
all
we
can
say.
Is
we
really
don't
like
this
and
which
means
deprecated,
and
it's
already
dead
great.
O
O
O
Have
some
free
text
I
agree
with
all
the
other
stuff
because
it
says
if
you,
if
you
don't
get
rid
of
likely
one
you'll,
have
all
of
these
problems.
That's
exactly
what
we
should
say.
If
you
don't
do
it,
you'll
have
all
of
these
problems,
but
we
can't
mandate
that
somebody
not
deploy
a
protocol.
That's
just
ridiculous
and
furthermore
I'm
not
sure
if
we
well,
maybe
we
can
close
the
registries,
but
there
are
other
standards,
organizations
that
use
the
Ike
v1
registries.
O
C
O
C
O
O
O
C
C
I,
her
statement
was
sent
back
telling
that
the
disease
registry-
that
is
not
for
this
use
and
but
I'd-
really
answer
that.
Oh,
we
can
say
is
our
document
anymore,
because
it's
so
late,
it
was
because
you
could
change
it
and
then,
because
of
that,
you
know,
is
they
allowed
them
to
allocate
this
number
and
then
I,
I
Triple
E
said?
Oh,
oh
good,
it's
we
could
get
the
number,
so
we
don't
need
to
change
the
document.
It's
we
have.
K
O
I
Benedict
as
responsible
ad
totally
right,
we
should
send
liaison
before
we,
just
by
close
the
registries
also
relating
to
Dan's
point
about
you
know.
We
can't
say
you
must
not
use
this
protocol,
it
doesn't
actually
have
binding
force.
I
mean
yes,
that's
true,
but
we
put
that
in
our
documents,
all
the
time
as
I
ATF
and
the
implication
is
sort
of.
If
you
are
adhering
to
this
document
and
you're
complying
to
this
document,
then
you're
not
using
iq1,
but
you
can
ignore
this
document
and
your
own
peril.
E
So
Danny
amigo
Erickson,
it's
it's
really
good
sean
is
behind
me
because
we
had
the
same
kind
of
discussion
in
TLS.
We
said
well,
if
weif,
why
don't
we
duplicate
TLS,
1.2
and
some
argue
is
that
because
1.3
is
obsoleting
in
the
header
today,
that's
1.2.
It
was
not
necessary,
so
I
I'm
not
against
the
draft
but
I,
just
like
we
acquired
with
other
working
group,
maybe
so.
K
So,
to
clarify
that
a
little
bit
so
so,
in
my
view,
is
when
we
say
you
know,
use
Ike
V,
not
Ike
v1.
We
are
technically
talking
to
implementers
like
don't
implement,
Ike
v1
like
we're,
not
saying
don't
run
actually
one,
and
this
RFC
is
more
or
less
saying
it's
been
so
long
now.
You
should
really
also
not
be
running
this
anymore.
G
Hi,
this
is
Sean
Turner,
just
a
minor
word
suggestion
I
think.
Technically
what
we're
trying
to
do
here
is
you're
trying
to
say,
don't
use
it,
but
you're
also
trying
to
add
solution
does
not
make
the
document
historic.
So
what
you
really
want
to
do
is
in
the
words
I
think
it
was
like
must
is
you
this
document
is
been
off
sleet.
It
must
not
be
deployed.
G
B
B
C
B
F
I'll,
be
I,
gotta,
be
quick,
so
it's
an
alternative.
An
alternative
approach
for
most
want
impartiality
in
I,
quit
ooh,
so
bikini
for
a
quitter
defined
in
the
drug
de
Jesus.
Already
in
publication
request
instated
just
online,
so
we
sent
inside
ksanych
we
negotiate.
That
became
is
used
in
the
next
change
and
and
I
quote,
the
PPK
is
barricaded,
identity
is
sent
and
it
begins
used
stilt
into
the
SKG
and
escapee
computation,
so
that
initial
I
guess
I
isn't
protected
by
PPK
wiki.
F
So
the
problem,
the
problem
is
that
now
we
have
group
I
quit
to
GI
Cueto
and
draft
adopted
and
in
GI,
cui
to
the
session
keys,
are
immediately
transferred
from
group
to
group
members
in
the
initial
I.
Guess
a
so
they
these
keys
are
not
practices.
Keys
are
really
sensitive
information
it.
They
are
not
protected
by
both
quantum
shared
key,
so
current
GIP
to
draft
suggests
a
very
long
sequence
of
exchanges
that
can
work
around
this
issue,
so
we
first
the
from
I
guess
I
need.
Then
we
perform
GSA.
F
Også
else
is
equivalent
to
five
cows
for
J
equal
to,
but
in
DC
else
we
don't
transfer
key
stand
with
and
defecation
Araki's
needed.
Some
of
then
group
members
initiate
like
a
sailor
key
initiate
the
registration
exchange,
deletes
initial,
like
saying
so
it's
a
total
of
five
exchanges
and
for
around
tips.
So
an
eternity
of
approach
would
be
to
use
I
continue
to
to
exchange
that
just
becomes
well.
F
There
was
a
popular,
not
popular,
but
it's
that
it
is
implemented,
but
even
some
vendors
and
to
exchange
to
send
appliquéd
entity
in
the
ikat
immediate
exchange.
Even
we
can
even
send
we
can
even
send
several
public
identity.
That
is
not
the
case
with
the
original
approach
I
and
in
this
case
the
I
call
against
and
GSA
always
exchange
will
be
protected
to
respect
the
gate,
because
we
will
still
be
key.
We
were
already
negotiate
which
perfectly
I
did,
which
propagate
to
use.
I
can
will
steer
it
into
the
competition
for
the
SKT
keys.
F
F
Further
for
I
could
say
for
like
we
do
not
4G
I
quit
you
just
for
tradition
like
we.
There
is
a
more
mixed
situation,
because
we
need
three
exchanges,
a
stand
of
two,
but
if
you
psyche
intermediate
of
for
some
other
purposes,
we
can
piggyback
replicate
identity
into
each.
So
it's
probably
not.
We
may
not
lose
it
something
in
the
middle
and
it's
still
less
complication
for
ICO's.
If
you
need
protection
for
for
for.
C
F
F
E
C
F
C
C
B
E
Hi,
so
this
draft
is
basically
explaining
how
introducing
a
method
to
negotiate
multiple
I
tried.
They
say
at
one
one
time
so
next
slide,
oh
yeah,
so,
as
I
mentioned
before,
usually
the
create
charges
that
result
in
creating
only
one
try,
let's
say,
and
what
we'd
like
is
to
improve
that
from
one
to
n.
So
this
requires.
Basically,
you
propose
a
number
and
you
provide
another
number
saying:
I
will
not
go
above
this
number
and
you
provide
some
arguments
so
that
you
can
generate
all
the
necessary
parameters
for
that.
E
In
this
case,
that's
going
to
be
the
SPI
nones.
That's
going
to
be
used
to
generate
the
different
SP
is
for
each
child,
let's
say,
and
you
have
a
response
with
the
same
parameters,
but
in
here
the
end
child
s,
a
is
the
number
agreed
max
charlie,
say,
is
sort
of
useless.
It's
just
repeating
the
previous
one,
and
s
PR
announced
is
just
a
hint
to
derive
all
the
different
SBI's.
E
C
Turki
Vanessa
says:
I:
don't
think
you
actually
can
do
that
with
SPI
numbers,
because
they
see
our
numbers
need
to
be
unique
and
now,
if
using
hashing,
there
is
no,
of
course.
Yes,
you
could
generate
non-si
so
long
that
you
actually
get
all
their.
You
know.
Spi
numbers
you
generate
are
going
to
be
unique,
but
it's
got
to
be
a
little
bit
annoying.
We
had
this
feature
in
a
person,
one
Mike
or
someone.
You
would
actually
propose
multiple
I
say
you
send.
C
You
know
multiple
SPI
numbers
and
no
credit
and
I
think
we
were
the
only
implementers
ever
who
implemented
it
and
in
our
case
we
implemented
it,
but
they
were
no
way
to
configure
it.
So
I
think
it's
actually
a
little
bit.
You
know.
I
would
really
invite
like
to
see
first
that
people
who
actually,
what
is
the
use
case
for
this
before
we
actually
want
to
implement
it
so.
E
The
use
case
so
well,
one
question
is
about
the
SPI,
so
you
can
extend
this
as
long
as
you
wish.
So
maybe
there
are
other
ways
to
do,
but
I'm
you
can
choose
the
nodes
so
that
you
don't
have
collisions.
The
use
case
is
clearly
when
you
have
multiple
calls
it's
better
to
to
have
multiple
si
at
least
one
per
core
or
and
to
avoid
to
avoid
that
you
have
some
switches
on
contact,
switching
and
some
essays
that
are
shared
between
the
multiple
calls.
So
that's
the
the
main
motivations.
B
C
F
Our
F
plus
king
material,
because
there
is
a
counter-
and
it
is
a
one
point
counter,
so
you
can't
iterate
pair
F
plus
more
than
255
times.
So
if
so,
you
can't
generate
more
than
well.
It
depends
on
the
on
the
size
of
the
key
for
the
childís,
a
that
is
needed,
but
there
is
some
limit
on
the
number
of
assays
that
you
can
generate
just
it's
hard
coded
limit
in
the
equity
space
because
of
the
definition
of
error,
f+
and
I
think
that
well
I
agree
the
historicity.
F
E
C
E
But
well,
it's
going
to
be
made
basically
a
restriction
on
them,
but
we
can
work
on
that
scheme.
That's
so
about
the
complexity
and
I
think
you're,
referring
to
how
the
sps
have
been
generated.
Yeah
but
I
I,
sort
of
don't
understand
where
the
complexity.
It
is
because
I
think
you
can
turn
really
announce
and
you
can
see
if
you
have
any
collisions
with
your
SPI
well
at.
E
F
E
To
use
those
those
that
are
I
mean
you
say,
I'm
gonna
do
an
exchange,
so
I'm
taking
ounce.
Okay,
these
are
free,
know
what
there
is
a
collision.
I
take
another
one:
okay,
fine
I'm,
sending
it,
and
if
those
the
other
choose,
how
much
si
is
is
willing
to
generate
is
the
same
thing
and
but
when
is
suppose
he's
taking
less
or
he's
not
taking
that
exact
number
or
is
saying
no
I'm,
not
using
those
multiple
choice.
A
then
I
received
that
ID
allocate
those
so
understand
it,
but
we
have
two
minutes
left.
K
K
The
second
use
case
was
if
he,
if
you
do
this
per
CPU,
so
we're
we're
working
with
a
few
other
people
with
Strong's
on
the
Linux
kernel
to
be
able
to
do
more
processing,
because
currently
there's
a
limitation
on
on
CPU
versus
Nick
receive
cues.
So
we
cannot
use
the
full
amount
of
traffic,
so
we
want
to
install
multiple
of
the
same
essays
on
different
CPUs
and
the
use
guys
there
was
brought
up.
You
can
actually
do
this
on
demand
whenever
another
CPUs
it.
K
So
if
you
have
64
CPUs,
you
don't
have
to
set
up
64
children.
You
can
just
set
as
soon
as
a
new
CPU
generates
a
packet.
It
will
acquire
and
a
new
sort
of
fake
acquire
message,
and
you
will
set
up
the
the
the
essays
on
demand.
So
so
you
should
have
spreading
a
load
arrazolo.
The
third
one
is
similar
to
the
second
one.
This
was
for
the
Equality
of
servers,
different
essays,
where
you're
also
thinking
maybe
need
to
set
up
64
essays
at
once,
and
a
similar
thing
applies
there.
K
If
you
only
set
up
the
ones
on
demand
based
on
the
quality
of
service
bits,
you're,
actually
not
setting
up
many
of
them,
you're,
probably
only
setting
up
two
or
three.
So
then
it
doesn't
really
become
a
much
of
an
issue
anymore.
So
I
think
this.
This
optimization
is
not
really
needed.
Based
on
the
use
cases
that
I
know.
