►
From YouTube: IETF108-DNSOP-20200729-1100
Description
DNSOP meeting session at IETF108
2020/07/29 1100
https://datatracker.ietf.org/meeting/108/proceedings/
A
E
C
I
thought
I
already
pushed
all
the
buttons
that
that's
where
in
my
screen.
Sorry
sorry
welcome.
This
is
the
dinosaur
working
group
meeting.
We
have
two
sessions
this
afternoon
for
me
afternoon
for
you
early
morning
or
later
in
the
morning.
This
session
is
one
hour
and
forty
minutes.
We
have
a
packed
agenda.
C
C
C
B
B
B
So
here's
some
document
updates
that
we
have.
If
we
go
to
the
next
slide,
we
have
four
documents
in
the
rfc
editor
queue
there.
We
go
and
they've
been
sitting
there
for
a
while.
So
that's
fairly
good
and
we
finally
got
2845
biz
in
the
same
state.
So
I
think
I'm
pretty
happy
with
that.
The
next
slide
we've
got
a
few
sort
of
updates
on
server
cookies.
B
B
B
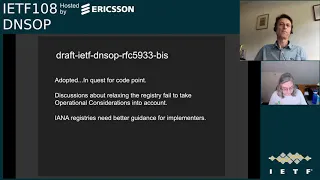
So
on
the
next
slide,
there's
one
that
we
updated.
We
did
adopt
the
5933
biz
that
equally,
everybody
equally
was
unhappy
about
adopting
this
and
we
adopted
it.
As
you
know,
as
well
and
including
the
chairs,
it
was
a
bitter
pill
for
everybody,
but
they
have
a
quest
for
a
code
point
and
that's
part
of
the
whole
process.
B
So
part
of
this
discussion
came
about
also
adopted.
They.
There
was
a
whole
sort
of
threat
about,
oh,
let's
sort
of
relax
the
registry,
but
I
personally
feel
that
fails
to
actually
take
operational
considerations
into
account
to
just
sort
of
add
more
dena
sec
algorithms,
without
sort
of
addressing
any
sort
of
operational
issues,
and
we
are
an
operations
group
and
we
need
to
sort
of
address
those
type
of
issues
and
failing
to
do
so,
I
feel
is
we're
just
laying
down
on
the
job.
B
One
thing
that-
and
I
sort
of
brought
up
a
few
times-
was
the
great
table.
That's
in
86
24
that
paul
and
andre
put
together
about
you
know,
recommendations
using
the
2119
language.
The
problem
is
diana
and
the
ion
registries
don't
really
seem
to
allow
that
sort
of
flexibility,
but
I
feel
that
maybe
the
iana
retrieves
we
have
right
now
need
better
guidance
from
implementers.
B
There's
some
there's
some
ref.
You
know
there's
some
relevant
stuff
in
what
tls
folks
did
in
terms
of
recommending
implementation
versus
not,
and
so
I
that
may
need
a
deeper
dive.
I
I'd
love
to
see
some
folks
sort
of
think
about
that
and
see
how
we
can
do
it
sort
of
go
about
that,
but
to
just
sort
of
you
know,
make
it
easier
to
add
more
algorithms
without
really
sort
of
thinking
of
the
long-term
consequences.
Just
seems
like
that.
B
You
know
like
just
bad
bad
math,
all
the
way
around,
so
just
my
personal
opinion.
So
next
slide
there's!
Oh
yes,
this
one
we've
been
talking
with
with
we
went
through
the
chairs,
went
through
all
the
sort
of
current
drafts
back
in
april
and
and
was
looking
for
sort
of.
We
were
sort
of
thinking
about
this
language
thing
figuring.
This
was
going
to
come
up
and
I
guess
we
were
just
sort
of
lucky.
B
We
were
ahead
of
the
curve
a
little
bit
and
there
are
some
updates
in
84.99
that
we
could
do
to
sort
of
make
that
better.
One
idea
was
to
just
publish
an
update
document
kind
of
like
that
terminology:
tour
thing
that
that
made
those
updates,
but
that
just
seems
like
it's
to
me
that
doesn't
seem
like
it
just
seems
like
it's
it.
B
It
just
seems
weak,
I'm
not
sure
how
how
else
to
say
it,
and
I
would
prefer
we
just
republish
84.99,
with
all
the
changes
we
want
to
make
and
sort
of
clean
that
up,
rather
than
having
people
chase
through
documents
to
find
those
sort
of
to
sort
of
those
updates.
But
I'm
you
know
we're
going
to
throw
that
out
and
let
the
and
see
what
the
working
group
feels
about
some
of
that.
What's
the
right
way
to
go
with
that,
so
we'll
you
know
we'll
take
you
guys
anyway.
Next
slide.
B
I
think
that's
the
bulk
of
it.
There's
our
data
tracker
and
stuff
in
our
github.
What
else
we're
working
on
we?
Actually,
since
we
adopted
a
bunch
of
things,
we're
going
to
be
busy
for
a
little
while,
so
I
guess
that's
good,
I
guess
that's
good
also
next
slide
so
for
agenda
in
the
underworld.
Current
group,
mr
ridgewater
science,
going
to
talk
about
the
fragmentation
avoidance,
which
we
hope
we
get
more
people
reading,
because
we
think
it's
getting
pretty
getting
much.
B
You
know
pretty
cleaned
up
and
we
like
to
see
it
move
along
as
well.
The
service
binding
parameter
specification.
That's
the
service
b
draft,
as
you
all
know,
and
they've
been
making
a
lot
of
progress
and
and
and
that's
been
really
great.
What
they're
doing
and,
of
course,
dna
delegation
only
dns
key
flag
and
there's
some
new
working
group
business
on
the
next
slide.
B
These
are
for
the
next
pretty
much
the
end
of
this
session
and
the
second
session,
the
ns2
and
s2t
draft.
I
think
tim's
actually
presented
that
before,
but
we're
coming
back
around
request
to
actually
update
the
resolver
primary
query:
8109
draft
paul's
draft
about
ionic
considerations,
which
I've
sort
of
already
vented
on
a
little
bit.
B
Dns
access,
denied
error
page
and
that
last
one
probably
a
time
permitting
is
on
this
nat
64,
optimization
stuff
you'll
want
to
look
at
the
slides,
it's
it's!
It's
yeah
you'll
want
to
look
at
the
slides.
That's
all
I
can
say
it's.
It's
definitely
people
doing
guinness
and
ways
that
we've
never
actually
thought
about
doing
dns
for
better
or
for
worse.
So
that's
what
we've
got
on
the
agenda
for
today.
F
F
C
G
C
C
F
C
C
A
H
These
are
differences
between
dracula,
georgians,
of
avoiding
fragmentation,
zero,
three
and
drastic
dns
of
avoid
fragmentation;
zero
one,
please,
please
click
this
link
to
show
differences,
main
differences,
changed
was
working
draft
and
added
density.
With
the
countermeasure
in
introduction
and
removed,
section
7.2
dns
packet
size
moved
details
of
minimum
responses
to
appendix
a
and
added
reference
to
directly
hcpwd
datagram.
C
H
C
H
F
F
F
C
E
E
E
If
you
tried
to
separate
all
these
pieces
of
information
out
into
separate
rr
types
and
make
separate
queries
for
them
from
the
client.
Apart
from
requiring
a
lot
of
queries,
there
would
be
no
guarantee
that
you
get
coherent
answers
back,
so
this
ensures
that
you
can
get
a
coherent
bound
set
of
information
out
of
the
dns
to
help
you
connect
to
some
endpoint
next
slide.
C
E
C
E
So
this
is
just
a
one
of
the
motivating
examples
for
this.
There
are
a
lot
of
different
use
cases,
but
one
of
the
key
motivating
examples
is
to
be
able
to
take
a
domain
point
it
at
two
different
cdns
and
have
each
cdn
have
a
bound
set
of
connection
hints
or
metadata
that
are
associated
with
that
specific
cdn.
E
One
of
the
key
reasons
for
this
is
that
that
is
that
this
record
is
the
designated
type
to
deliver
encrypted
client,
hello,
public
keys
for
tls
connections,
and
those
keys
are
only
going
to
work
if
you,
if
they're
bound
to
a
correct
server
pool
if
you
try
to
use
them
with
the
wrong
server
pool
you'll
get
a
fatal
connection.
Error
next
slide.
I
C
E
Is
the
this
was
previous
called
previously
called,
alias
form?
We've
changed
that
name
to
alias
mode,
to
reflect
the
fact
that
there's
only
one
wire
format
for
this
record
type,
but
there
are
two
different
modes
depending
on
the
indicated
priority,
and
in
this
mode
the
record
acts
a
lot
like
some
variation
on
a
name
or
alias.
It
also
acts
quite
a
bit
like
srv,
it's
essentially
a
simple
indirection.
E
E
So
that
was
all
background
which
I
wanted
to
get
through
as
fast
as
I
could.
These
are
the
really
the
relevant
slides
for
the
meeting,
so
there
have
been
quite
a
few
changes
since
our
last
meeting
we've
gone
through
several
intermediate
drafts,
including
a
name
change
which
caused
the
draft
version
numbers
to
reset.
E
E
We
have
changed
the
ayana
instructions
to
reserve.
The
most
important
change
is
that
half
of
the
key
range
is
now
first
come
first
served.
This
was
requested
by
some
implementers
who
wanted
a
an
easier,
lower
friction
way
to
experiment.
So
the
hope
is
that
this
will
allow
dynamic
experimental
uses
while
ensuring
that
they
can't
exhaust
the
code.
Point
range
since
the
other
half
is
expert
review.
E
The
this
is,
we
argue
that
this
is
safe,
because
clients
normally
ignore
unrecognized
keys.
So
if
somebody
puts
something
strange
in
one
of
these
keys
that
was
allocated
on
a
first
come
first
serve
basis,
most
clients
will
just
ignore
it
unless
they've
specifically
been
configured
to
have
awareness
of
that
key
chain.
Length
limit
is
something
that
we
discussed
in
the
working
group
at
length.
A
previous
draft
said
something
like
eight
question
mark,
which
generated
a
great
deal
of
controversy.
I
E
Are
necessary
in
order
to
use
this
rr?
So
if
you
look
in
the
list
of
mandatory
keys-
and
you
see
a
key
number
so
that
those
are
all
16-bit
type
codes,
if
you
see
a
type
code
that
you
don't
recognize,
then
you
should
just
discard
that
record,
because
you
don't
have
the
information
required
to
use
it.
E
E
E
E
E
Slide
so
the
the
text
still
has
several
to
do's,
which
I
think
we
can
actually
just
remove
at
this
point.
Apart
from
that,
it's
time
for
working
group
last
call
and
interop
testing.
We
actually
have
a
document
now
that
you
may
have
seen
on
the
mailing
list
where
people
have
been
putting
in
notices
of
work
on
implementation
and
I'm
very
happy
to
see
a
number
of
different
major
implementations
coming
online.
There
that's
very
exciting,
so
hopefully
we
can.
We
can
start
to
do
some,
some
more
interrupt
testing.
C
No
questions,
thank
you
ben,
so
so
the
dinosaur
chairs
are
also
thinking.
We're
close
to
working
group
last
call
for
interrupt
testing.
We,
I
think
it's
good
to
have
some
coordination.
Are
you
coordinating
that
or
do
you
want
to
delegate
it
to
the
to
the
chairs?
You
are
in
contact
with
open
source
developers
and
other
developers.
E
C
C
J
Just
that
interop
testing
seems
particularly
important
for
those.
I
think
I
think
it's
it's
an
important
part
of
what
the
working
group
will
be
interested
in
and
not
just
not,
and
quite
possibly,
not
only
danatop.
So
this
does
seem
like
something
where
we
need
to
make
sure.
We've
got
an
adequate
cross
area
review.
I
E
C
E
K
J
K
Great
yeah,
so
just
on
the
topic
of
testing,
so
we
at
apple
have
built
an
implementation
of
this
in
the
next
beta
seed
that
we'll
have
of
ios
and
mac
os.
That
will
be
using
the
official
code
points
so
first,
if
anyone
wants
to
test
out
what
happens
when
clients
are
requesting,
it
should
be
as
simple
as
just
installing
those
on
a
device,
and
so
you
know
please
try
that
out
and
let
us
know
if
you
see
issues
there,
that
particular
version
does
not
the
the
particular
version.
K
Not
play
well
with
new
r
types,
particularly
we've
seen
reports
from
vodafone
italia
that
their
networks
are
seeing
some
level
of
issue
when
they're
receiving
our
types
that
they
don't
recognize
and
it
seems
to
be
affecting
other
dns
queries.
There's
seems
to
be
some
bug
in
their
dns
infrastructure.
So
that's
something
that
people
should
be
aware
of
as
they're
testing,
and
if
anyone
has
contacts
there,
we
should
let
them
know
that
we
should
make
it
safe
for
these
new
r
types.
L
Hi,
I'm
alison
mankin,
very
nice,
clear,
talk,
ben
and
I'm
I'm
very
impressed
with
the
progress.
I
was
hoping
that
we
could
focus
when
we
get
to
interrupting
on
operators
and
that's
large
dns
operators,
because
it'll
be
really
important
to
see
if
they
to
get
them
used
to
this
very
new
type
of
record,
and
I
I
think
it'll
be
really
valuable
for
adoption
if
it
is
available
from
those
providers.
So
we
deal
with
a
lot
of
vendors
and
we'll
try
at
salesforce
we'll
try
to
encourage
them.
L
F
C
Any
other
questions,
no
okay,
thank
you
so
summarizing
some
interrupt
testing,
also
well
as
tommy
also
mentioned
apple,
is
also
testing.
This,
with
a
new
code
point
interrupt
testing,
including
application
level
and
then
proceed
with
the
process
and
working
group
last
call
is
that
correct.
Did
I
miss
something?
Okay,
please
working
group
have
do
review
the
documents
and
send
feedback
to
the
authors
and
we'll
continue
thanks.
C
C
C
F
D
And
so
just
a
small
reminder:
the
delegation
only
flag
is
a
dns
key
flag
that
you
can
set.
That
basically
indicates
that
you're
only
delegating
in
your
zone,
you
don't
sign
anything
within
your
zone,
and
so
the
idea
is
that
you're
sort
of
yielding
power
that
that
you
have
over
over
your
children,
and
you
commit
this
publicly
in
your
dns
key
flag,
which
means
it's
encoded
in
your
ds
record.
So
so
people
can
can
track
and
monitor
this,
and
this
does.
D
D
So
the
the
main
change
other
than
some
spelling
errors
is
the
the
change
that
talks
about
what
data
is
or
isn't
allowed.
So
we
had
some
confluted
language
saying
if
you're
crossing
a
dot
or
if
you're,
having
a
a
zone
cut,
then
then
those
records
should
only
be
delegation,
records
and
glue
and
should
not
be
signed
and
paul
vixie
contacted
me.
Is
that,
like
you,
you
should
just
talk
about
answers,
because
that's
really
what
you're
talking
about
you
don't
really
care
if
you're
crossing
an
empty
non-terminal,
you
only
care
about
that.
D
Whatever
they're
sending
is
not
an
answer,
but
is
blue
records
and
authority
sector,
so
that
is
really
the
biggest
change,
which
means
that
empty
non-terminals
are
no
longer
an
issue
and
I
think
it
clarifies
the
text.
I
did
add
some
language
into
the
security
considerations,
just
in
case
like
like
sneaky
answer,
section
material
would
end
up
in
the
authority
section
or
the
additional
section,
so
that
should
be
ignored
there.
D
D
F
C
J
L
J
I
C
M
I
F
F
M
M
M
M
M
The
record
can
exist
in
both
places.
It
ideally
would
exist
in
both
places,
but
to
aid
in
rollouts.
It
can
exist
in
the
child,
but
not
the
parent.
It
would
be
signed
in
the
child
zone,
not
in
the
parent
very
similar
to
how
ns
is
done
now
and
it's.
It
has
extra
parameters
which,
if
you
want
more
details
about
exactly
what's
in
it,
there's
a
slide
and
a
couple
more
that
will
show
the
different
values
that
are
currently
allowed.
M
M
The
other
record
type
is
the
ns2t,
which
is
basically
expands
to
the
name
server
to
target
record
type
where
this
would
exist,
where
there's
not
a
zone
cut,
so
you
may
use
the
alias
form
from
one
zone
to
another
and
then
that
zone,
since
it's
not
a
zone
cut.
At
that
point,
you
would
use
the
ns2t
record
and
it's
basically
similar
to
a
c
name
for
a.
M
Very
similarly
to
the
svcp
draft
there
is,
there
can
be
a
chain
of
these.
I
haven't
added
the
language
to
the
draft
yet,
but
the
I
was
going
to
pretty
much
copy
the
the
hop
count,
suggestions
from
the
svcb
draft,
so
that
it's
up
to
the
implementers
of
how
many
hops
to
actually
fall
to
how
many
to
chase
when
resolving
and
then
next
slide
so
going
over.
Some
of
the
changes
between
the
zero
zero
and
the
zero
one,
the
main
ones
where
the
ds
information
has
been
removed
from
the
record.
M
So
that
can
be
signed.
And
then
the
ipv
four
and
six
hints
has
been
removed
from
the
allowed
parameter
keys,
because
that's
basically
just
the
glue.
That
would
also
exist
in
the
parent.
At
the
same
time,
which
leaves
the
next
slide
as
the
service
parameter
keys
that
are
defined
for
these
record
types.
M
I
don't
remember
if
it
was
on
the
list
or
in
private
conversations,
but
there
was
some
talk
about
something
similar
to
the
cdns
key
record
type,
but
that
currently
putting
that
out
of
scope
for
this
draft
and
then
a
clarity,
piece
of
ns2
and
ns2t
should
not
exist
for
the
same
name
in
the
same
zone
and
the
final
slide
are
there's
a
few
open
questions.
Thanks
to
ben
schwartz,
I
thought
I
had
replied
your
email.
I
guess
I
haven't.
I
will
do
that
later
today.
M
G
Please
go
ahead.
You
have
the
microphone.
This
is
paul
hoffman.
The
question
I
had
was
exactly
what
you
brought
up
at
the
end,
which
is
where
should
this
be
done,
deprive
which
is
meeting
later
in
the
week,
has
a
very
different
draft,
with
a
very
different
set
of
parameters,
a
very
different
use
case,
which
is
narrower
and
such
it's
not
been
adopted
by
deprived,
but
I
I
actually
prefer
this.
G
I
J
C
E
E
C
I
N
M
N
M
J
F
Q
Q
Q
C
E
To
clarify
my
previous
comment
to
say,
I
don't
think
that
we
necessarily
need
to
reduce
this
down
to
one
draft.
I
think
that
there
are
a
lot
of
pieces
here,
and
maybe
it
is
too
much
for
one
draft
and
we
have
a
lot
of
authors
who
might
have
separate
areas
of
expertise,
but
I'd
like
to
find
a
constellation
of
drafts
that
work
together.
G
G
G
I
think
what
ben
was
about
to
say,
but
was
too
polite,
which
was
that
the
different
authors
really
want
their
own
use
cases
pushed
forward
and,
quite
frankly,
there
are
drafts
that
have
not
even
been
written
that
could
be
in
this
space
because
we
were
waiting
on
dpriv
and
you
know
on
on
the
previous
work
in
deprive
to
set
up
the
use
cases
and
that
that
just
sort
of
got
lost.
I
went
when
when
this
discussion
happens
instead
of
saying.
Oh
look,
we've
got
a
bunch
of
drafts.
G
G
I
again
this
draft
to
me
is
a
lot
cleaner
than
the
one.
That's
being
discussed
in
deprived-
and
I
to
me
that's
that
is
an
advantage,
but
the
folks
in
the
peter
van
dyke
and
folks
in
deprived
have
a
very
specific
use
case
that
this
would
not
follow.
So
please
don't
look
at
you
know
please
chairs
and
that's
the
chairs
here
and
and
the
chairs
everywhere.
It
seems
like.
Please
don't
look
at
these
as
drafts,
but
as
use
cases.
Thank
you.
C
C
G
Sure,
if
you
want
to
do
video,
that's
fine
with
me.
I
sort
of
believe
in
since
none
of
us
are
seeing
each
other
in
the
hallway
in
in
spain
right
now
sort
of
nice
to
have
humans
around
and
given.
I
can't
tell
if
medico
is
showing
my
my
lovely
face
or
not,
but
it
doesn't
really
matter
as
long
as
you
can
hear.
G
G
So
rfc
8109
is
about
priming.
It
was
published
just
just
a
couple
years
ago
by
the
standards
of
this
working
group
and
it
explains
how
to
do
priming.
You
know
for
dns
for
with
the
root,
so
the
working
group
worked
on
it.
We
got
an
okay
amount
of
input
during
the
pub
you
know
during
the
discussion
we
published
it
and
then
a
bunch
of
people
asked
questions
after
it
was
published.
So
this.
If
it
was
one
question
I
might
say:
okay
well,
maybe
we'll
just
do
a
little.
G
G
I
look
at
the
the
priming
list,
such
as
the
one
from
iana,
and
it
has
domain
names
in
it,
but
that's
not,
you
know
actually
covered
in
rfc8109,
and
so
we
we
actually
need
to
say
to
people
what
is
what
is
used
in
a
configuration
list
and
then,
of
course,
one
of
the
favorite
topics
of
this
working
group
was
what
about
the
tc
bit
and
in
specific.
If
you
send
a
priming
query
to
root
servers
and
you
are
not
using
edns0,
so
you
have
a
512
byte
limit.
G
The
answers
that
come
back
do
not
have
the
tc
bits
set
on
which
shocks
some
people
and
is
completely
the
correct
thing
for
others.
So
something
needs
to
be
discussed
about
that
and
then
someone
asked
and-
and
I
I
should
have
anticipated
this-
what
if
I'm
on
a
private
network?
What
you
know
like
what
should
I
do
about
priming
so
next
slide.
G
So
the
purpose
of
the
draft
here
is
to
make
small
updates
just
to
answer
these
questions.
That
is,
keep
the
vast
you
know,
keep
the
text
as
we
have
it
put
in
little
additions
for
each
of
these
questions,
plus
maybe
folks
in
the
working
group,
will
ask
the
questions
that
would
have
come
up
after
we
publish
this
now
but
again,
so
the
idea
is,
keep
8109
and
add
sentences
and
paragraphs
here
and
there
we
can
take
advantage
of
this.
G
Also
to
do
something
rsac
published
a
document
recently
on
terminology,
or
it
republished
that
also
as
a
dis
where,
in
that
document
they
actually
have
much
clearer
wording
for
things
that
are
in
you
know
about
the
root
zone.
So
right
now,
8109
talks
about
the
root
name,
server
name,
which
is
a
bit
confusing
rsac
itself.
G
I'm
sorry
for
those
of
you
aren't
familiar
with
with
all
the
icannes
rsac
is
the
root
server
system
advisory
committee,
which
is
a
formal
group
within
icann
that
advises
the
icann
board
on
root
server
stuff,
but
it's
it's
comprised
of
all
the
root
server
operators,
so
their
terminology
document
now
has
a
a
single
name
that
they
use
for
this,
which
is
called
the
root
server
identifier.
So
we
might
as
well
throw
that
in
to
clarify
here
so
next
in
the
last
slide.
G
So
if
this
is
adopted,
I
think
it
can
move
quickly.
I
don't
want
it
to
move
so
quickly
that
people
have
questions
after
we've
published
the
next
rfc,
but
it
I
don't
believe
that
there's
anything
controversial
here
other
than
additions
for
what
we've
had
already,
and
that's
it
for
this.
If
people
have
questions
or
comments.
C
C
F
C
G
C
C
C
I
C
C
R
Yeah
I
was
just
going
to
comment
that
I
think
a
couple
people
were
saying
you
know.
Maybe,
since
you
have
the
time,
perhaps
you
do
take
a
hum
to
see
if
there's
actual
interest
in
130
people
who
are
on
here
about
doing
something.
With
this
last
draft
and
paul
yep,
just
the
suggestion,
there
are
a
couple
of.
R
C
C
J
I
J
We
will
go
ahead
and
and
ask
a
question
and
see
what
happens.
We've
had
discussion,
we've
had
this
presentation
of
this
new
draft
from
from
paul
hoffman,
and
the
question
is
whether
we
want
one
of
the
sufficient
interests
to
adopt
it,
review
it
and
eventually
publish
it.
We
will
start
the
hum
now
we
get
35
seconds
and
you
should
be
able
to
see
a
little
menu.
C
J
C
J
J
S
J
Yeah,
it's
very
hard
to
there,
there's
nothing
here.
That
shows
me
and,
and
frankly,
I
don't
want
to
know
how
many,
but
if,
if
what
you're
saying
is
true,
that's
that's
that's
good
to
know.
Frankly,
I
wouldn't
take
this
as
anything
except
an
experiment,
but
at
least
now
we
know
how
to
use
the
tool.
So
thanks
for
every
thanks,
everybody
that
stuck
around-
and
we
will
be
back
shortly
for
the
final
three
draft
discussions
for
dinosaur
ietf108
see
you.
