►
From YouTube: IETF108-DRIP-20200730-1410
Description
DRIP meeting session at IETF108
2020/07/30 1410
https://datatracker.ietf.org/meeting/108/proceedings/
A
Yeah,
I
think
we
we
can
start
so
we
will
come
up
for
for
joining
this,
the
drape
working
out
meeting.
So
this
is
the
network,
so
make
sure
you
are
familiar
with
this
with
the
network.
So
if
you
have
any
clarification
questions
you
please
don't
hesitate
to
to
raise
them
the
four
for
the
logistics,
so
we
have
a
shui
who
will
take
care
of
taking
the
minutes.
The
the
pointer
is
there
as
we
are
using
mythical.
A
There
is
a
list
of,
I
would
say
the
the
control
tabs
that
you
you
can
use
to.
I
would
say
to
to
ask
to
put
yourself
on
the
queue
or,
if
you
want
to
to
share
your
dvd
and
so
on.
So
please
yeah
make
sure
that
you
are
following
the
those
ones
the.
As
for
the
objective
of
this
of
the
days
meeting
we
have
at
least
here
so
the
we
have
two
objectives.
A
One
is
for
july.
We
need
to
to
make
to
have,
I
would
say,
an
assessment
from
the
authors,
but
also
from
the
working
participants,
whether
we
are
ready
or
not
yet
for
for
those
ones.
So
these
are
the
two
objectives
we
have
we
have
for
the
meeting.
So
that's
why
we
have,
I
would
say,
the
first
half
of
the
meeting
that
will
be
dedicated
to
the
requirement
and
to
to
the
architecture.
A
So
stewart
will
be
on
the
floor
to
to
present
us
the
the
recent,
I
would
say,
progress
that
was
made
on
this
on
this
third
documents,
and
this
time
we
are
scheduling
the
the
solution
discussions
so
we'll
have.
We
have
four
talks,
the
because
we
will
also
to
to
prepare
to
do
the
working
of
work
on
this
solution
once
that
will
be
for
for
september.
A
A
A
A
C
B
How
about
now
great?
Thank
you.
Okay,
anyway,
a
little
bit
of
a
general
update
on
context
focused
primarily
on
requirements,
which
is
the
more
mature
of
the
two
drafts
and
then
a
little
bit
on
architecture,
which
is
far
less
mature,
and
I
finally
figured
out
just
today
the
conceptual
problem
that
I've
been
having
adapting
to
ietf
culture
on
what
is
architecture
in
in
this
this
context
and
more
more
on
that
in
a
minute.
B
What
we
had
just
adopted
in
the
space
of
the
last
month
is
icaos
international
civil
aviation
organizations
terminology,
but
astm
also
has
a
terminology
document,
so
we
want
to
look
at
that.
Excuse
me
also
from
the
faa.
Now,
admittedly,
this
is
just
u.s
only,
but
it
is,
I
believe,
representative
jay
merkel.
The
executive
director
for
the
u.s
uas
integration
office
in
faa
has
said:
there's
many
areas
where
network
coverage
is
not
available,
and
this
is
why
we've
included
a
broadcast
mode.
B
This
really
confirms,
in
my
opinion,
that
broadcast
rid
authentication
cannot
depend
upon
observers
having
internet
connectivity
in
the
field.
Also,
the
drone
advisory
committee
has
put
out
comments
on
the
utm
conops
version.
2.0
and
they've
basically
suggested
crowdsourced
rid,
although
they
didn't
call
it
that
the
icios
aviation
trust
framework
study
group,
their
prototype
certificate
authority
began
issuing
certificates
and
a
use
case
for
digital
identifiers
for
all
aircraft
has
been
drafted
in
the
trust
reciprocity
operating
needs
working
group
for
consideration
by
the
digital
identity
working
group.
B
These
are
all
ikl
working
groups
and
in
various
memos
from
various
government
agencies
with
limited
distributions.
Surprise
surprise:
having
looked
at
the
regulations
that
are
coming
from
the
civil
aviation
authorities,
they
really
want
to
maximize
their
surveillance
of
other
people
but
minimize
their
surveillance
by
other
people,
and
they
likewise
have
suggested,
but
not
by
our
name
of
crowdsourced
grid,
essentially
crowdsourced
grid.
B
An
outfit
called.
The
att
foundry
recently
published
10
bold
projections
on
the
future
of
drones,
and
I
would
just
like
to
call
your
attention
to
their
first
and
their
10th
prediction
that
drones
will
enable
dynamic
communications
networks
and
secure
internet
of
things.
Platforms
will
catalyze
widespread
adoption
of
drones
all
right.
B
For
me,
we
need
to
get
on
the
use
cases
for
observer
to
pilot
comms
and
the
if
you
will
anti
use
cases
for
observer
to
pilot
comms,
and
we
need
more
help
tracking
what's
going
on,
especially
in
europe,
because
there's
a
lot
of
players
doing
a
lot
of
things
that
affect
this
summary
of
activity
in
the
working
group.
Since
our
last
interim
we've
had
some
promising
discussions
with
domain
registration,
experts
and
michael
will
talk
about
that.
B
The
ansi
roadmap
for
standardization
now
includes
ietf
thanks
to
bob,
and
I
have
addressed
most
of
the
inputs
on
the
requirements
and
architecture
document
from
all
those
folks,
but
not
all
of
it.
Yet.
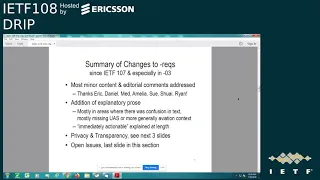
Oh
requirements
summary
of
changes.
There
were
a
lot
of
editorial
comments
and
and
minor
issues
of
content
from
eric
daniel
med,
amelia
sue,
schwei,
ryan
and
most
of
those
have
been
addressed
some
of
them.
I
still
especially
the
editorial
ones.
B
Some
of
the
nits
I
still
need
to
get
to
there's
been
a
considerable
amount
of
explanatory
pros
added,
because
a
lot
of
the
itfers
are
not
deep
into
aviation
in
general
or
unmanned
aircraft
systems
in
particular,
and
so
there
was
a
lot
of
need
for
context
and
in
particular
the
term
immediately
actionable
was
unfamiliar
to
a
number
of
people,
so
that
has
been
explained
at
length
by
immediately
actionable
we're
not
talking
about
the
standards
process.
We're
talking
about
the
information
received
through
unmanned
aircraft
systems,
remote
id.
B
B
The
privacy
and
transparency
considerations
section
is
kind
of
like
an
iana
considerations
or
security
considerations,
and
it
supplements
the
actual
numbered
requirements
about
privacy
which
we'll
talk
about
in
the
next
two
slides.
I'd
like
to
stop
for
just
a
moment
to
ask:
did
anyone
participate
in
the
pidlock
side
meeting
and
is
there
anything
coming
from
that
direction?
That's
going
to
be
in
time
for
us.
E
E
B
Okay,
so
privacy
requirement
two
encrypted
transport.
The
top
paragraph
here
is
the
way
it
is
written
in
revision,
three
of
the
requirements
draft
and
I
apologize.
I
was
guilty
of
solution
space
thinking
in
a
requirements.
Document
bob
has
made
two
suggestions
for
changes.
The
first
one
is
that
we
strike
the
phrase
end
to
end,
which
he
suggested
may
lead
us
down
a
rat
hole
of
defining.
What
are
the
ends?
B
B
What
this
is
all
about
is
the
the
so-called
system
message:
transmits
the
location
of
the
pilot
or
and
the
ground
control
station,
and
that
means
that
in
the
clear
anybody
who's
got,
a
bluetooth
or
wi-fi
receiver
can
find
out
where
a
pilot
is
and
go
harass
them,
which
is
not
desirable.
However,
public
safety
and
security
personnel
need
to
be
able
to
get
that
information.
B
B
B
B
We
got
a
little
bit
outside
the
iatf
swim
lane
here,
but
at
the
same
time
we
wanted
to
encourage
appropriate
behavior.
So
we've
we've
weakened
this
to
drip,
should
facilitate
selective,
strong
encryption
of
private
data
at
rest
in
such
a
manner
that
only
authorized
actors
can
recover
it
and
then,
in
an
explanatory
note,
for
that
number
requirement,
not
the
text
of
the
numbered
requirement
itself.
We've
said
how
the
information
is
actually
stored.
On
the
end
systems
is
out
of
scope,
but
encouraging
privacy
best
practices,
including
end
system
storage.
B
A
E
F
E
Yeah,
I
ordered
this
to
punt
to
a
solution
which
then
does
it
that
it's
this,
the
caa,
which
will
be
setting
policies
and
the
solution
would
have
to
implement
it.
Of
course,
I'm
biased
because
I
do
have
such
a
solution
proposed,
so
I
I
am
coming
from
it
from
that
direction,
so
I
would
like
obviously
like
other
people
to
say
whether
I
got
it
or
not.
With
this.
I
think
this
is
I
I
like
my
wording,
but
we
can
add
a
word
about
safety
in
here,
but
this
is.
B
E
B
A
G
G
A
B
H
H
It's
very
good,
but
now
when
we
talk
broadcast
and
broadcast,
has
a
particular
meaning,
then
it's
difficult
to
define
a
good
encryption
and
I'm
afraid
in
ip
already.
There
is
probably
nothing
in
that,
and
also
in
ip
there
is
no
broadcast
id,
but
it's
multicast
ip,
because
ip
is
of
course
ipv6.
I
consider
and
that
that's
a
very
difficult
question
to
solve.
H
I
also
think
that
the
the
person
jonathan
he
said
something
about
m2
ends,
which
sounds
like
multicast.
I
am
an
end.
I
send
the
packet
to
several
receivers
multicast
and
there
might
be
some
something
possible
there
in
terms
of
encryption.
I'm
not
sure
what
exactly,
but
the
other
thing
that
jonathan
mentioned
ends
to
end.
I
think
at
iatf.
There
is
nothing
about
that
and
I
I
think
there
is
nothing
that
could
be
possible
about
that
or
even
though
I
must
acknowledge,
I
admit,
I
know
nothing
about
hip
and
about
pidlock
and
these
things.
B
H
Yes,
thank
you
presenter
for
this
qualification,
and
this
brings
me
the
other
question.
So
what
kind
of
thing
should
I
mean?
I
am
a
newcomer
here.
I
do
not
know
the
entire
context,
but
what
kind
of
thing
could
itf
do
below
ip
right?
If
you
say
broadcast
below
ip,
maybe
broadcast
at
file
layer
or
broadcast
like
in
tv
broadcast?
B
Think
well,
so,
a
little
bit
more
context.
The
system
as
a
whole
has
plenty
of
components
that
do
use
ip,
but
that
particular
mode
of
doing
remote
identification
over
the
data
link
does
not
use
ip.
So
you
know
all
of
the
players
have
got
ip
connectivity
in
some
places
and
at
some
times
and
the
network
remote
id
mode
does
directly
use
ipconnectivity,
but
the
broadcast
grid
is
just
over
a
data
link.
A
I
I
don't
think
personally,
so
I
think
I
would
prefer
to
have
a
discussion.
I
would
say
to
more
inputs
because
yeah,
so
unless
there
is,
I
would
say
the
some
comments
to
to
be
made
here
in
this
session.
I
prefer
that
we
we
discussed
this
further.
You
share
this.
I
would
say
the
the
modification
that
you
have
made
on
the
list
and
then
we
can.
We
can
proceed
on
that
one.
So
may
I
just
call
on
the
participant:
do
you
have
any?
E
A
B
A
D
A
B
B
A
lot
of
these
are
questions
of,
should
I
do
this,
or
should
I
do
that,
because
individual
reviewers
have
had
their
particular
suggestions
and
in
cases
where
it
was
obvious
that
yes,
this?
This
is
what
we
needed
to
do.
I
just
did
it,
but
there
are
a
lot
of
cases
where
you
know
do
we
want
to
take
the
document
this
way
or
we
want
to
take
the
document
that
way,
and
so
I
would
like
to
have
some
discussion
on
the
list,
so
I
will.
B
B
B
And
so
you
know,
for
me,
architecture
always
follows
requirements.
It
does
not
precede
them,
but
I
guess
that's
because
ietf
kind
of
jumps
straight
to
the
technical
requirements
skipping
over
the
operational
and
the
functional,
in
which
case
all
right,
looking
at
architecture
before
requirements,
makes
a
certain
amount
of
sense.
B
But
we
don't
get
to
define
the
overall
architecture,
it's
defined
by
the
regulators
and
by
external
standards,
development
organizations,
and
so
the
architecture
document
that
I
created
is
in
a
sense,
the
wrong
architecture
document,
because
I
guess
what
iatf
really
wanted
is
one
that
described
that
overall
architecture
prior
to
specifying
technical
requirements,
but
that's
already
predefined
and
it
would
be.
It
would
be
pointless
for
us
to
replicate
all
of
the
definition
of
that
architecture.
That
already
exists
in,
in
literally
thousands
of
pages
of
documents
published
by
regulators
and
other
standard
development
organizations.
B
So
I
jumped
directly
to
a
solution,
space
architecture
which
has
led
to
some
confusion
and
some
pushback.
So
there
are
lots
of
open
issues,
many
of
which,
hopefully
can
be
resolved
by
simply
recognizing
that
this
draft
is
in
fact,
for
a
solution,
approach.
Architecture
and
probably
should
be
moved
away
from
the
requirements
and
towards
the
solutions
based
documents,
along
with
what
adam
and
bob
and
and
others
have
been
doing.
So
here
are
the
reviews
that
have
that
I've
received
on
architecture.
B
B
B
I
there's
not
a
common
theme
amongst
all
of
these.
One
thing
that
I
think
I
can
answer
is
this
one
about
asking
the
astm
chair.
My
read
of
the
f3411
document
is
that
for
broadcast
rid,
it
defines
specific
message
formats
for
network
read,
it
defines
only
the
data
dictionary.
The
elements
in
those
dictionary
are
the
same
elements
that
show
up
in
the
specific
message
formats
that
are
used
in
broadcast
id,
but
the
specific
message
formats
themselves
are
not
dictated
for
network
grid.
B
However,
for
confirmation
I
will
ask
the
astm
chair
and
then
there's
some
questions
about
scoping.
You
know
what
really
belongs
in
the
archdocument
and
what
belongs
in
the
other
solution.
Space
documents
and
amelia
did
a
very
thorough
and
very
entertainingly
written
review,
which
I
quite
enjoyed,
and
I've
attempted
to
summarize
here
my
understanding
of
her
points.
B
Some
of
these
I
need
to
go
directly
back
to
amelia
one
to
one
or
on
the
list,
because
I
just
need
to
clarify
some
things.
For
instance,
I
was
not
actually
speculating
on
activities
of
other
sdos,
where
I
said
they
may.
That
was
actually
an
explicit
thing
that
the
regulators
said.
This
is
allowed
and
astm
as
the
primary
sdo
operating
in
this
area
said.
B
Well,
we
have
defined
messages
and
we
have
defined
a
data
dictionary
and
we
have
defined
how
you
transport
them
over
wi-fi
neighbor
awareness,
networking
and
we've
defined
how
you
transport
them
over
bluetooth,
but
if
you
wish
to
transport
them
over,
something
else
have
a
good
time
right.
So
I
was
just.
I
was
just
highlighting
the
fact
that
in
that
the
people
who
defined
the
message
formats
have
said,
yeah
go
ahead
and
carry
them
over
other
things
and
how
you
do
that
is
up
to
you.
B
There
were
additional
points
in
the
thread
that
amalia's
review
launched
and
a
lot
of
it
revolved
around
the
distinction
between
safety
and
security.
Astm
has
said
this
is
a
security
standard,
their
f3411,
which
was
what
we
initially
focused
on
fitting
our
stuff
into
and
augmenting
with
better
trustworthiness.
B
But
now
there
are
other
organizations,
including
euro
k,
who
are
now
stepping
up
and
saying
well
we're
going
to
go
further
and
we're
going
to
do
a
safety
standard.
The
difference
is
security
in
the
mind
of
the
aviation
community
is
about
stopping
people
from
doing
intentionally
bad
things,
whereas
safety
in
the
aviation
community
is
about
not
having
planes
accidentally
crash.
B
B
B
B
Now
the
next
is
my
whining
and
it
has
to
do
mostly
with
draft
scopes,
and
I
will
caveat
a
lot
of
my
frustration
presumably
comes
from
my
own
failing
to
participate
more
frequently
in
give
and
take
on
the
mailing
list.
So
I
originally
tried
to
write
an
applicability
statement
for
uas
red
got
told
to
split
it
into
requirements
and
architecture.
Fine,
I
did
that,
but
I
did
that
with
my
own
idea
of
what
an
architecture
was
which
is
apparently
not
the.
B
I
etf
concept
of
what
an
architecture
is
the
architecture
into
which
drip
must
fit
is
already
defined.
Any
architecture
that
we
define
is
either
a
redundant
document
or
a
specific
solution
approach,
and
I
did
the
latter,
in
which
case
requirements
should
drive
architecture,
not
vice
versa.
Reviews
have
asked
for
both
more
and
less
context.
At
the
same
time,
a
lot
of
the
confusion
in
people
reading
arch
comes
from
lacking
context
from
requirements
and
now
bob
has
drafted
what
looks
an
awful
lot
like
an
applicability
statement
for
uas
rid.
B
So
I
wonder:
should
we
merge
these
three
drafts?
I
don't
know
that
we
can
decide
that
today,
but
I
want
to
raise
the
question
today
and
then.
Finally,
I
want
to
point
out
that,
even
with
all
that
we
have
been
working
on
in
the
requirements
and
solution
spaces,
there's
nothing
there.
That
would
stop
a
malicious
operator
from
registering
a
harmless
toy,
getting
a
private
key
for
that
harmless
toy
then
provisioning
his
big
weaponized
uas
with
that
same
private
key,
so
that
weaponized
uas
can
spoof
and
pretend
to
be
the
harmless
little
toy.
B
G
B
I
B
J
J
I
Yeah
thanks,
but
is
that
unreasonable?
We
we,
I
mean
for
the
architecture
that
we
assume
that
that
private
key
is
self-generated
by
the
ua
and
that
even
if
it's
not
the
case
now
it's
probably
well.
We
can
hope
is
going
to
be
the
case
later
or
is
it
a
real
problem
that,
because
if
the
private
key
is
believed
to
be
public,
it's
it
makes
things
much
more
harder.
B
For
you
know
the
foreseeable
future
anyway,
cs
rid
itself
is
not
a
fundamental
part
of
drip.
It's
an
option.
I
think
it's
a
very
attractive
option
and
lots
of
other
organizations
have
stumbled
across
similar
ideas
so
anyway,
that
that's
a
discussion
that
we
can
also
take
to
the
list.
I
just
wanted
to.
You
know
open
the
discussion
at
this
point.
K
Just
took
a
while
to
catch
up,
so
I
think
that
one
of
the
things
is
a
tpm
doesn't
even
really
fully
solve
the
problem,
because
often,
even
if
you
can't
get
the
private
key
out
of
the
device,
you
can
still
use
the
device
to
do.
Do
the
encryptions
that
you
need
for
the
protocol
like
you
can
still.
You
know,
fake
the
big
drone
with
it
just
by
calling
the
cheap
tpm
to
go.
Do
what
you
you
need
to
do.
K
So
I
think
this
is
a
semi
unsolvable
problem,
really
because
it's
not
about
the
private
key.
It's
about
the
access
to
use
the
private
key.
That's
the
important
thing!
You
can't
really
block
that,
and
and
most
attempts
to
protect
the
private
key
haven't
gone
very
well
anyway,
you
know
see
the
you
know:
cable
tv
industry,
but
even
if
you
could
solve
that
problem,
it
doesn't
help,
but
I'm
I'm
very
curious
with
this.
K
I
B
K
But
I'm
gonna
write
public
key
crypto
on
stm32.
You
know
you
know
f4
ff7
series,
all
the
time
right,
there's
no
big
deal
doing
on
those
type
of
environments.
So
I'm
I
mean
we
we've
implemented
dtls
on
you
know,
8-bit
processor
says
I
I
just.
I
think
I
think,
if
we're
going
to
go
with
that
assumption,
we
should,
if
that's
an
assumption,
that's
critical
to
us.
B
No,
I
I
grant
your
technical
point
about
the
hardware,
I'm
more
concerned
with,
what's
wrapped
around
it,
that
when
you
go
to
the
store
and
buy
one
of
these
things,
it's
running
an
app
that
is
not
only
a
bare
metal
app,
it's
a
closed
source,
app,
so
of
course
right.
So
so
yes,
this
is.
This
is
a
direction
that
we
could
go,
but
it
will
require
more
manufacturer
cooperation.
K
Okay,
that
really
gets
to
a
good
point,
though
I
think
you
should
say
it
that
way
that
that
you
know,
if
you
require
the
manufacturer
to
change
the
software
on
the
drone,
then
that's
a
that's
a
deployment.
You
know
whatever
that's
a
limitation,
but
you
have
to
decide
whether
you're
doing
it
or
not.
That
that
point
I
understand
thanks.
I
But
what
I'm
I
am
wondering
is
toward.
Are
you
asking?
If
are
you
asking
if
we
should
take
as
an
assumption
that
the
the
private
key
remains
reflecting
the
identity
of
the
I
mean
of
the
eua,
and
I
mean
it's
not
a
is
is
expected
to
be
protected
in
a
way
that
it
can't
be
used
another
as
an
oracle.
Also
or
do
you
are
you
asking
if
we
should
consider
what
is
existing
today.
K
Okay,
so
I
I
think
what
I
was
saying
is:
I
find
the
assertion
that
the
cpus
on
a
drone
that
are
capable
of
keeping
it
in
stable
flight
are
not
capable
of
doing
ace
generating
a
key.
I
find
that.
I
don't
believe
that
that
seems
very
unlikely
to
be
true
to
me
and
that's,
and
it
sounds
like
that's,
not
the
actual-
that
that's
not
probably
the
important
assertion
here.
Probably
the
important
assertion
was
you're,
trying
to
do
an
architecture
that
doesn't
require
changing
any
of
the
software
on
the
drone.
That's
a
very
different
statement
right.
K
So
those
are
two
things
and
then
what's
what
accidentally
got
confounded
with
them
was
a
third
thing,
which
is,
I
don't
really
whatever
you're
doing
with
your
private
keys.
If
you
think
they're
not
going
to
leak
you're
out
of
your
mind,
they
are
going
to
leak.
People
are
going
to
be
able
to
steal
those
private
keys
or
at
least
steal
the
ability
to
use
the
private
keys,
even
if
they
can't
directly
read
the
private
key.
K
I
I
B
So
I
guess
my
instinct
was
to
simply
in
the
basic
drip
documents
to
highlight
the
risks
associated
with
private
key
compromise
leakage,
inappropriate
use
by
the
guy
who
generated
it,
etc.
Right,
but
then,
in
the
you
know,
add-on.
If
you
will
optional
things
that
that
drip
can
do
when
extended
with
something
like
csrid,
that
we
have
mitigation
strategies
available.
F
In
other
words,
you
know
there
will
be
an
time
for
non-compliance
and
warnings
and
stuff,
but
in
in
a
few
years
drones.
If,
if,
if
if
there
is,
if,
if
the
regular
regulatory
authorities
get
it
right,
then
drones
will
create
whatever
key
the
regulators
require
and
if
the
cpu
is
in
those
drones
as
deployed
today,
can't
do
that.
F
With
respect
to
the
technology,
that's
there
I
just
looked
up
quickly
a
topic
king,
a
major
major
distributor,
for
you
know
little
little
drony
things
and
other
things
model
planes
and
whatnot.
You
know
every
of
these
controllers
have
like
32-bit
arm
cores
nowadays
as
a
minimum
yeah.
So
the
times
when,
when
your
stability
control
was
run
by
some
some
eight
big
pid
regulating
thingies,
those
are
long
long
long
gone.
F
B
You
great,
I
mean
a
number
of
you-
have
pretty
much
changed
my
thinking
in
the
last
10
minutes
on
this
point
at
the
at
the
top
level,
though,
a
couple
of
people
have
pointed
out
that
that
keys
will
leak,
and
it
would
be
great
if
we
had
some
strategy
for
dealing
with
the
leakage
of
keys.
Even
if
we,
even
if
we
assume
that
at
some
point
in
the
future,
the
keys
will
be
properly.
B
B
Agreed
yeah,
so
I
I'm
basically
starting
from
the
position
that
somebody
else
stated
about
10
minutes
ago
that
we
we
just
need
to
accept
that
either
private
keys
or
the
ability
to
exercise
the
private
key.
You
know
my
big
weaponized
drone
could
actually
physically
carry
my
toy
on
board
as
part
of
its
payload
right.
B
So
accepting
that
that
can
happen.
What
else
can
we
do?
That
is
not
about
trying
to
prevent
the
leakage
of
the
private
key,
and
it
is
not
even
about
attempting
to
prevent
you
know
carrying
around
the
hardware
that
holds
an
embedded.
You
know
non-leaking
self-generated,
private
key,
and
so
that's
you
know
that's
my
bottom
line
on
the
page
is
can't
we
take
bob's,
crowdsourced
grid
and,
and
look
at
you
know
streaming
video
or
whatever
to
to
do
sanity
checks
on
someone's
assertion
that
they
are
a
harmless
little
toy.
F
I
On
to
the
other
presentation,
I
from
what
I'm
hearing
and
my
perception
of
I
think
this
question
is
a
little
bit
out
of
scope
of
the
architecture
document
and
that
we
should
reasonably
take
that
yeah.
The
journey
is
identified
with
that
public
key
and
not
to
dig
too
much
on
and,
of
course,
it's
gonna
leak.
It's
gonna
that
should
be
put
in
the
security
considerations.
I
L
L
It
should
not
surprise
people
that
know
myself
that,
based
upon
over
20
years
within
the
icann
and
the
main
name
space,
I
am
using
domain
names
as
a
reference
point
for
a
lot
of
what
I
will
be
doing
and
the
approach
that
I
am
taking.
The
basic
building
blocks
in
which
I've
tried
to
engage
in
a
path
forward
here
is
using
existing
protocols,
specifically
epp
and
rdap
in
the
concept
of
epp
with
a
demandroid.
L
I
am
looking
at
coming
up
with
the
equivalent
of
an
aviation
repository
object,
identifier,
and
this
would
be
right
now.
The
current
best
thinking
is
that
this
identifier
would
be
associated
with
the
airframe
and
right
now,
based
upon
some
of
the
discussions
that
I've
been
having
with
sallow
and
bob
stu
and
some
of
the
other
people
within
the
community.
L
L
L
L
I
F
I
I
E
Okay,
so
let's
go
into
screen
mode
here,
slide
percent
slide
mode.
Okay,
let's
go
here
in
the
charter
which
says
drip's
goal
is
to
specify
how
remote
id
can
be
made
trustworthy
and
available
in
both
internet
and
local
only
connected
scenarios
so,
and
there
are
some
design
goals
that
are
limiting
us
from
technology
or
from
other
standards,
one
we
are
limited
to
an
id
which
is
20
characters
maximum,
and
that's
because
this
has
to
work
over
bluetooth,
4
inside
a
single
broadcast
frame.
E
We
want
deterministically
globally
unique
with
distributed
registry
services
such
that
this
id
is
related
to
this
device
and
not
some
others.
We
also
want
non-spoofable
approval
ownership
without
internet
lookup
in
200
bytes,
which
it
would
fit
within
the
chained,
bluetooth,
4
frame
or
into
bluetooth,
5
frame
and
much
less
for
better
performance,
which
probably
will
require
some
internet
lookup.
E
So
those
were
the
design
goals
that
I
was
I've
been
looking
at
since
I
started
this
and
let's
see,
did
I
get
okay?
Fine,
so
I
had
some
design
considerations
and
is
a
registered
string
non-spoofable
and
the
answer
is
no.
It's
not
non-spoofable
whether
I
look
at
the
proposed
standard
for
you
for
ui
ur
uas's,
the
ansi
cta
serial
number,
or
look
at
a
classic
registered
string,
rfid
epc.
E
E
So
what
about
digital
certificates
are
they
non-spoofable
certificates
themselves
are
not
are
non-spoofable,
but
the
name
is
spoofable.
The
subject
ought
name
can
occur
in
multiple
routes,
who's.
We
trusted
on
a
name
and
again,
we've
had
some
really
classic
issues
here
in
the
web
of
somebody
registering
an
important
fqdn
in
another
pki.
E
You
know
the
ca,
causing
trust
issues
and
what,
if
there's
a
simultaneous
registration
of
of
a
name
in
in
multiple
places
who
wins
how
to
do
the
management
across
multiple
independently
operated
certificate
systems,
so
those
were
design
considerations
which
I've,
which
I
looked
at
and
to
be
trusted.
Non-Spoofable
identity
means
to
be
self-asserting.
E
This
is
my
particular
claim,
and,
and
the
only
way
to
do
a
that,
I've
able
to
find
learn
to
do
a
a
self-asserting
identity
is
that
the
identity
is
derived
from
trustable
information.
That
is
a
public
key
and
there's
an
algorithm
that
this
trust
information
yields,
identity,
hash
of
the
public
keys,
identify
fixed
length
results
is
best
because
of
that's
what
protocols
like
so
worked
on
this
as
design
considerations.
E
What
was
thinking
about
a
year
ago,
when
I
was
first
brought
to
this
problem
space
and
the
globally
unique
list
implies
an
assigning
hierarchy.
Statistical
uniqueness
of
just
hashing,
a
public
key
is
not
sufficient.
Even
the
prior
probability
is
small.
You
will
get
collisions
so
include
a
hierarchy
into
the
identity,
and
you
need
to
include
that
hierarchy
in
the
hashing
for
a
non-spoofable
hierarchy.
E
E
It
has
a
loose
hierarchy
in
the
ipv6
prefix,
which
is
actually
then
hard
to
limit
and
control
for
remote
id.
If
I
did
try
to
work
this
with
cgas,
I
was
not
satisfied
with
the
result.
Maybe
that's
my
bias,
and
so
I
chose
to
take
the
the
the
hit
and
add
hierarchy
to
it
and
that
you'll
see
my
hypercall
hit
draft
as
an
open
discussion
where
there's
a
better
way
of
defining
the
96-bit
partitioning
and
and
I'm
open
to.
E
I
have
changed
that
from
the
original
draft
to
what,
where
it
currently
is,
and
we
can
debate
the
choice
of
vddsa
2459
with
c-shake
128
sweet
choice,
but
the
edd
sa
gives
us
a
public
key
in
32
bytes
without
patent
issues,
which
I
feel
is
is
important.
Unlike
p256
and
seed.
Shake
is
neat
and
it
does
give
me
some.
E
I
put
out
a
a
draft
used
on
how
to
register
article
hits
within
hip,
but
evp
that
michael
was
presenting
is
probably
a
better
choice.
I'm
willing
to
concede
that
and
look
at
how
we
can
use
evp
for
the
provisioning
and
get
the
global
uniqueness.
That
way.
Look
up
by
dns
since
hierarchical
hits
are
valid.
E
E
So
that
gives
some
of
the
design
and
and
and
direction
I
had.
I
feel
that
the
solution
I've
come
up
with
meets
a
number
of
the
requirements
in
our
requirement
drafts.
It
provides
approval
ownership
in
and
of
itself.
If
you
read
the
draft
and
the
security
considerations,
the
the
the
harco
hit
as
remote
id
does
not
provide
proof
of
ownership.
It's
the
tool
to
to
get
the
approval
ownership
if
that
tool
provides
the
binding
and
the
registration.
E
E
It
provides
uniqueness
and
through
using
the
private
key,
provides
announcement
of
ability
and
in
registry
one
and
two
through
dns
lookup
you
can
get
with
the
information
is
publicly
available
and
going
to
the
registry.
You
can
then
use
as
a
key
to
get
the
private
lookup.
So
I
feel
that
it
is
the
entry
point
to
all
of
these
requirements.
E
And
so
I
would
like
to
bet
that
the
draft
be
called
to
the
adopted
by
the
work
group.
It
can't
be
I've
been
told
by
our
chairs,
not
at
this
this
session.
I
want
people
to
please
read
the
draft.
Please
comment
to
me
directly
comment
on
the
list
so
that
in
the
august
interim
we
can
make
this
as
a
call
for
work
group
adoption
that
covers
my
slides
kind
of
covered
it
fast,
but
that
is
that
is
it
and
I'm
open
to
questions.
I
I
I
M
E
E
I
I
Yeah,
currently
I
have
to
talk
with
my
co-chair.
What's
the
plan,
I
I
I
really
want
to
to
have
the
the
to
the
requirement
and
architecture
document
to
be
sent
before
we
all
focused
on
the
next.
I
mean
the
solution
drafts,
but
we
should
not
also
wait
maybe
too
much
time
for
that.
So
it's
gonna
come
soon.
I
don't
know
when
I
have
to
to
talk
to
my
co-chair.
E
I
I
will
say
that
this
is
the
first
thing
technical
solution
piece
we
need.
We
need
to
agree
on
what
is
remote
id
so
then
we
have
something
to
build
all
the
rest
on
and
what
our
basic
points
are,
and
also
to
the
larger
aviation
community
and
regulatory
community
saying
that
we're
bringing
something
to
the
table,
and
so
that
is
why
I
personally
want
work
group
adoption
soon
rather
than
later.
So,
when
I'm
in
these
iko
meetings,
when
I'm
in
the
the
other
meetings,
I
say
I
can
point
to
that.
E
E
L
L
L
L
I
think
this
is
self-explanatory
as
far
as
the
hierarchical
nature
of
what
I'm
proposing
and
how
this
is
largely
modeled
after
the
domain
name
marketplace.
This
following
diagram
here
is
a
a
diagram
which
bob
and
stu
had
pre
had
presented
to
the
registry.
Icann
registry
operator
working
group
a
couple
of
months
ago,
which
shows
the
utm
architect
and
the
reason
I've
used.
This
document
here
is
I'd
like
to
show
you
where
the
proposed
hierarchy
or
registry
would
fit.
L
All
193
member
states,
which
are
signatories
to
the
iko
avia
treaty,
final
point
here
again
just
trying
to
wrap
this
up.
I
am
going
to
continue
to
engage
in
outreach
just
this
week
since
the
original
submission
I've
had
some
discussions
about
the
existing
identifiers
for
both
drones
as
well
as
aircraft
and
how
that
could
easily
be
interfaced
into
the
registry.
Again,
we
are
not
looking
to
reinvent
the
wheel,
we're
trying
to
use
existing
naming
schemes
with
existing
protocols
within
the
domain
name
space.
L
I
I
L
No,
we
it's
not
questioning
the
use.
Rdap
will
be
used.
So
if
you
look
at
a
lot
of
the
debate
that
is
going
on
within
the
icann
community
right
now,
as
far
as
how
what
third
parties
can
get
access
to
the
underlying
pii
or
non-public,
who
is
data
as
a
result
of
gdpr
the
scenarios
map?
I
almost
identically,
you
know
the
ability
for
law
enforcement
or
first
responders
to
get
quick
timely.
L
B
I
B
I
L
L
Yeah,
so
let
let
me
keep
this
real
real
short
and
again
I'll.
Just
follow
up
on
the
list
to
explain
this
in
more
detail.
I
I
believe
that
our
debt
can
be
used
to
provide
the
differentiated
access
to
the
underlying
data
subjects
for
the
data
subjects
or
the
machines,
and
that
could
be
automated
or
perhaps
manually
reviewed
based
upon
the
data
privacy
requirements
of
the
individual
member
states.
I
B
Steve
yeah,
if
I
may,
even
as
the
editor
and
primary
author
of
architecture,
I
do
not
believe
it
to
be
ready
for
working
group
last
call,
although
I
will
continue
to
work
on
it
and
and
try
to
move
it
in
that
direction
as
rapidly
as
possible.
The
requirements
document,
I
believe,
needs
one
more
round
of
minor
changes
as
long
as
we
get
confirmation
on
the
list
that
the
language
proposed
today
to
address
those
issues
is
acceptable.
I
E
E
We
have
the
requirements
we
can
work
on
that
we
have
enough
of
the
architecture
there
that
we
know
we
do
need
to
do
on
that.
I've
seen
many
work
groups
that
the
architecture
has
gone
on
for
a
long
time
in
in
in
holding
that
down.
So
let's
set
the
required:
let's
get
the
requirements
into
working
class,
call
and
and
and
wrap
that
up
and
let's
do
it,
and
I
continue
to
beat
on
architecture.
I
N
Slides,
can
you
guys
see
my
slides
and
hear
me?
Yes,
awesome.
Okay,
sorry,
I
was
tabbed
out
all
right,
so
I'm
going
to
talk
about
the
authentication
formats
today.
This
is
the
drip
off
trap
version.
Three,
I'm
gonna
start
off
with
some
of
the
fun
stuff.
We
are
actually
flying
drip
drafts.
These
are
just
a
collection
of
some
photos.
N
N
N
So
this
is
the
same
slide
from
bob's
draft.
It's
our
goal
of
making
trustworthy
and
available
on
both
local
and
connected
scenarios
and
we're
using
the
solution.
So
a
lot
of
the
pieces
from
this
draft
are
using
other
pieces,
so
we
use
the
hierarchical
hit
from
the
uas
draft
that
bob
just
talked
about
because
we're
using
the
hierarchical
hit.
N
We
have
the
small
key
signatures
of
ed
dsa25519,
which
gives
us
64
byte
signatures,
and
we
all
we
need
to
do
is
really
pension,
the
astm
to
increase
the
auth
page
limit
from
5
pages
to
10
pages.
We
have
gone
to
them.
They
are
receptive
of
the
change
for
the
next
revision
of
the
astm
standard,
so
we
would
have
224
bytes
of
authentication
data
to
play
with
to
add
to
our
solution.
We
would
add
forward
error
correction
for
bluetooth,
4
and
the
certificates
for
local
only
connected
scenarios.
N
N
The
identity
is
in
one
message:
the
position
is
in
another
message
and
then
authentication
is
a
completely
different
message,
which
is
also
paged
on
bluetooth
4..
So
we
get
a
lot
of
fragmentation
of
data,
and
this
creates
a
lack
of
trust
in
the
messages.
Bluetooth,
4,
especially
bluetooth.
5,
is
a
little
less
susceptible
to
this.
N
So
the
question
was
raised
very
early
on
in
our
boss.
Why
so
small?
Why
are
we
stuck
with
24,
bytes
or
20
bytes
for
the
identifier?
This
is
what
a
bluetooth
4
frame
looks
like.
We
only
have
25
bytes
of
data,
and
one
of
them
is
already
taken,
leaving
only
24,
that's
excluding
any
other
extra
headers
that
astm
defines
for
authentication,
specifically,
that
leaves
only
109
bytes
total
for
authentication
data
to
be
used
into
five
pages.
N
So
just
some
high
level
draft
changes
from
version
zero,
zero,
we're
at
version
zero.
Three.
Now
I
can't
type-
and
I
can't
spell
I
am
upset-
we
have
new
auth
formatting,
which
I
will
go
into
detail
in
the
next
couple.
Slides
and
the
entire
draft
covers
three
requirements:
gen
one
gen
two
engine,
three
3.
certificates
address
gen,
1
and
3,
which
are
provable
ownership
and
registration
and
the
auth
types
that
I
will
present
cover
the
provable
binding
or
gen
2..
N
F
N
N
N
It
allows
us
to
have
an
independent
fec
flag
gives
us
128
possible
drip
types
which
currently,
we
only
have
nine
defined,
and
the
seven
bit
space
is
broken
into
the
five
areas
that
you
can
see
on
the
bottom
picture,
and
I
have
a
question
to
the
working
group
which
I'll
raise
on
to
the
list
of.
Is
this
the
best
way
to
carve
up
this
single
byte?
This
is
what
intuitively
to
me
seems
like
the
best
way
to
do
it,
but
I
am
open
to
suggestions.
N
N
I
can't
really
get
into
that
much
detail
and
I'll
raise
this
up
onto
the
list
in
more
detail
but
effectively.
There
are
multiple
different
types
of
timestamps
being
used
in
the
general
ecosystem
and
right
now
we're
kind
of
doing
a
mix
of
them,
and
the
question
to
the
working
group
is:
what
one
should
we
adopt?
N
N
The
messages
must
be
in
much
as
type
order
and
they
fill
the
payload
of
the
wrapper
frame.
The
special
case
is
type
5.
If
you
have
five
messages,
you
can't
do
fec
and
bluetooth
4,
but
the
entire
authentication
message
now
acts
as
a
pseudo
message
pack,
which
the
message
pack
is
a
bluetooth
five
only
thing
from
astm,
which
uses
the
255
byte
payload
formatting
of
bluetooth.
N
N
N
The
final
format
for
bluetooth
4
is
the
certificate
registry
on
aircraft.
The
certificate
is
defined,
much
more
detail
in
the
identity
claims
draft.
So
I
encourage
people
to
go.
Look
at
that,
but
effectively
the
200
bytes
fit
snugly
within
the
general
frame
and
give
us
23
bytes
of
fec
so
on
to
bluetooth,
5.
The
bluetooth
5
is
a
little
bit
easier
because
it
is
all
within
one
bluetooth
frame.
N
The
final
bluetooth
5
message
is
a
zero
wrapped,
astm
messages.
This
is
a
special
one
where
the
we
virtually
fill
the
auth
data
of
the
wrapper
frame
and
sign,
and
the
data
is
actually
outside
of
the
authentication
message
and
is
all
the
data
around
it
in
the
message
pack
there's
a
question
of.
We
can
maybe
name
this
something
slightly
better
than
zero
wrapped
astm
messages.
N
Here's
the
entire
auth
type
tree
to
give
you
guys
an
idea
of
the
layout
and,
as
you
can
see,
ascm
authentication
data
general
frame
fits
within
that
and
then
the
wrapper
frame
fits
within
the
drip
authentication
data
and
then
the
payload
has
a
multitude
of
different
formats
that
can
fit
within
that,
and
with
that
I
am
done.
I
blazed
through
this
in
record
time,
so
I
will
take
questions,
comments
or
concerns
on
this
either
here
or
in
the
mailing
list.
I'll
leave
that
up
to
the
chairs.
If
we
have
time.
