►
From YouTube: IETF108-MBONED-20200731-1410
Description
MBONED meeting session at IETF108
2020/07/31 1410
https://datatracker.ietf.org/meeting/108/proceedings/
A
A
C
A
C
A
B
A
B
A
A
A
B
B
B
A
B
A
B
B
B
A
B
A
Let
me
just
say
something
lenny,
because
this
came
up,
hopefully
there's
a
lot
of
overlap
between
people
here
and
those
taking
place
in
writing
area
as
well.
So
you
know
beer
is
some
aggressive
work,
moving
forwards
on
a
whole
different
replicating
model
for
the
for
networks
as
whole,
so
internet
and
in
the
charter.
We
have
a
may
pursue
a
v6
native
option.
What
we've
really
discovered
is
there
is
no
real
native
way
to
do
this.
A
The
question
is:
do
we
need
an
end
cap
in
six
and
we've
got
a
requirements
draft
right
now?
That
is
what
the
working
group
is
focused
on.
Looking
at
what?
What
are
we
trying
to
do?
That's
potentially
unique
in
six
or
is
there
anything
unique?
We
need
to
do
in
six
to
provide
transport
of
beer,
so
please
just
pay
attention.
Look
at
that.
B
A
Oh
yeah,
I
wouldn't
say
a
ways
off
I.
I
know
there
is
hardware
in
labs
right
now
that
operators
are
evaluating,
so
my
expectation
is.
We
will
probably
hear
about
some
real
live
deployments,
possibly
this
year,
but
certainly
next
year
from
there.
Hopefully
we
get
some
bcps.
You
know
some
pressure
put
in
this
group.
Go
hey,
there's
some
things.
We
need
to
do
to
make
sure
we
either.
B
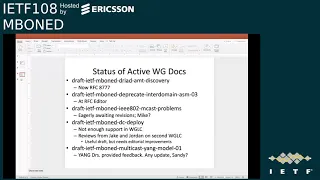
Great
okay,
moving
right
along
here
are
the
active
working
group
docs.
Actually,
the
dryad
draft
is
since
last
meeting
is
now
rfc
8777
congrats
jake,
forgetting
that
moved
along
pretty
quickly.
The
deprecate
asm
draft
is
at
the
rfc
editor
queue.
It's
been
there
a
little
while,
hopefully
we're
getting
close,
but
that
should
be
hopefully
by
ietf
109.
That
will
be
an
rfc
as
well
the
multicast
problems
draft.
B
That
is
still.
We
are
eagerly
awaiting
revisions.
I
think
two
ietfs
ago,
maybe
was
it.
Singapore
there
was
mike
met
with.
I
believe
there
were
some
security
area
concerns
and
mike
was
working
on
revisions
and
getting
out
that
final
revision
based
on
the
final
comments
and
what
was
agreed
to
mike.
I'm
are
you
here.
Are
you
out
there
mike
I'm,
not
seeing
you
in
the
list
yeah
I'm
seeing
the
list
either
warren.
I
believe
you
are
a
co-author
of
that
draft.
E
A
E
E
B
E
B
Okay,
next
was
the
data
center
deploy
draft.
Also
mike
looked
like
mike
was
on
the
lead
on
that
one
and
as
well.
I
guess
we
don't
have
mike
to
talk
about
that
one,
but
basically
that
went
through
last
call
last
year,
not
quite
enough
support
in
the
first
last
call.
We
had
a
second
last
call
and
from
that
jake
a
couple
months
ago,
gave
some
good
some
good
reviews
and
jordan.
B
B
B
B
B
D
F
B
A
B
E
B
B
D
A
D
E
D
Okay,
so
hi,
I'm
jake
I'll,
be
talking
about
the
progress
on
the
multicast
of
the
browser
work
that
we're
doing
the
project
that
we're
doing
this
is
built
on
our
on
the
three
drafts
we
have
active
in
the
working
group.
Now,
primarily
the
dorm
see
back
in
ambi
I'll,
be
touching
on
those,
but
most
of
my
time
will
be
spent
on
the
sort
of
overall
project
status
and
and
where
things
are
so,
I'm
gonna
be
going
over.
D
D
I
don't
know
how
the
code
review
is
going
to
go
when
that
gets
going,
but
you
know
ideally
that'll
be
that'll,
be
somewhere
before
too
long.
It's
possible
that
it
won't
be
checked
in
still
in
november,
but
one
can
hope
our
internal
poc.
I
guess
it
was
successful,
we're
going
ahead.
Obviously
the
we
had.
We
got
the
webassembly
build
to
run
inside
the
browser
and
produce
video
from
our
product
line.
That
does
video
with
multicast.
D
D
The
cpu
utilization
is
still
not
great,
but
it's
adequate
to
the
task.
For
now
there
will
presumably
be
some
updates
to
to
improve
on
that.
Hopefully,
at
some
point
I
I
would
say
that
that
carries
some
risk
at
this
point
like
we
don't
know
yet
where
the
issues
are,
but
we
think
that
they're
mostly
on
the
transport
between
the
render
and
browser
processes,
so
that
by
putting
that
in
a
shared
memory
transport,
it
should
be
okay.
D
So
there's
just
some
like
engineering
work
to
do
on
that.
But
but
it
looks
tractable.
I
think
I've
spun
up
a
dorm
server,
it's
running
and
discoverable
now,
so
you
should
be
able
to
to
do
the
lookup
as
described
in
the
dorms
draft
and
get
the
srv
record
to
see
where
to
connect
to
it,
and
it
has
cbac
data,
not
yet
any
ambi
config,
but
that
all
that's
using
the
cz
next
check
con
implementation
of
of
rest
conf
and
it's
using.
D
D
I
think
it
was
only
to
ambi
actually
because
the
the
crypto
types
changed,
if
I
remember
right
but
that'll,
be
part
of
the
next
draft
update
we'll
include
the
updated
young
model
for
that,
but
that
all
runs
okay.
That
seems
like
it
does.
What
it's
supposed
to,
and
I
have
a
script
that'll.
You
know,
given
an
sg
will
say
what
c
back
says.
D
D
That
was
a
little
bit
well
that
wasn't
very
much
through
the
ietf
effort,
but
but
with
some
advice
you
know
from
from
a
couple
of
you
guys,
I
went
to
nana
and
presented
there
that
also
led
to
the
apnic
blog
post
that
we
put
up
the
response
on
this
has
been
pretty
good,
so
I
might
continue
doing
a
little
more
on
this
front
just
to
answer
all
the
questions
people
have,
but
that
was
that
was
pretty
successful.
People
are
pretty
interested.
D
D
D
One
of
our
stretch
goals
we're
not
sure
if
it'll
happen,
but
we
would
love
to
be
able
to
try
a
production
delivery
of
some
of
some
actual
traffic
during
an
av
video
test
using
our
our
video
streaming
product,
but
delivering
it
over
an
amt
ingest
path
into
a
willing
network
with
some
willing
content
owner
trying
it
that's
you
know,
that's
we
consider
that
plausible,
but
there
there
are
several
hoops
to
get
through
to
see.
If
we
can
do
that.
D
Most
of
the
time
people
are
on
the
content
owner
side.
You
know
they
see
the
utility
of
this
so
far.
Everyone
we've
talked
to
so
you
know
the
fact
that
we
have
an
sdk
right
now.
Some
people
would
consider
that
they're
not
gonna
do
that,
but
most
of
the
time
they
just
look
at
that
as
a
as
a
minus,
but
one
that
they
could
live
with.
D
If
it
meant
that
we
started
getting
progress
down
this
path
and-
and
you
know
the
the
intent
I
mean
once
the
delivery
is
there,
then
then
it
opens
up
options,
for
you
know
for
more
open
transports
of
it
as
well,
but
we
haven't
made
any.
We
haven't
moved
anywhere
on
on
trying
to
open
our
sdk
yet
or
write
up
the
protocol.
D
They
want
this
to
work,
they
recognize
the
need
and
they
think
that
there's
there's
approaches
that
are
viable.
Probably
that
said,
there
are
some
challenges,
maybe
just
transitional
challenges,
but
but
like
the
way
that
people
use
it
today
and
what
they,
what
their
networks
are
prepared
to
accept,
does
not
necessarily
fit
very
well
with
this
vision
of
of
using
the
global
sg.
D
D
You
know,
they're
not
going
to
propagate
it.
To
that
to
that
building
we
asked
whether
this
is
a
sort
of
business
driven
constraint
or
a
technical
constraint,
and
it
was
business
driven.
So
it's
not
like
fixing
the
technical
side
would
address
it.
This
is
like
we're
going
to
have
to
send
it
from
sources
that
are
specific
to
that
network
in
order
to
get
it
transported
across
that
network,
although
they
are
willing
to
transport
the
traffic.
B
D
Well,
they're
not
opposed
to
having
the
source
come
from
outside
is
what
they're
saying
it
sounds
like
they
just
built
a
walled
garden
right
now.
They've
got
a
wild
garden
right
now,
and
they
don't
want
to
change
that.
So
let
me
get
to
what
I'm
thinking
as
a
solution.
Now
I
haven't
written
this
up
as
a
draft,
yet
sorry
about
that,
but
I
wanted
to
get
early
feedback
if
anybody
has
comments
on
it.
D
So
that's
why
I'm
showing
it
here
so
the
the
solution
I
have
in
mind
here
is
essentially
to
let
them
use
their
own.
You
know
let
them
map
it
to
the
the
sg
that
they
want
to
use
within
their
network
right.
So
you
just
build
sort
of
a
translation
layer
at
the
ingest
and
the
at
the
ingress
and
egress,
and
in
this
case,
what
what
pins
it
together
is.
This
I'm
calling
it
a
group
network
address
translation
service
which
is
nats,
and
so
this
would
be
an
http.
D
D
It's
you
know
just
change
it
around,
but
the
the
idea
is
that
when
you're
trying
to
to
join
this
sg,
you
know
that,
oh
because
I'm
in
this
network,
I'm
gonna
talk
to
this
network
associated
nat
service,
the
nat
service
will
tell
me
how
to
map
the
global
sg
to
the
local
sg
that
I
should
use
within
this
network
I'll
issue.
You
know
what
I'll
propagate
as
rpf
is
this
local
join
while
it's
inside
the
network,
whatever
you're
sort
of
topology,
looks
like
through
that
network?
That's
all
unchanged.
D
D
D
So
the
idea
is
just
to
sort
of
wrap
this
up
within
the
network
and
do
that
that
sort
of
at
the
boundary
translate
so
that
the
network
can
do
whatever
they
want
inside
and
they
don't
have
to
change
what
they're
doing
and
and
just
let
that
happen
so
most
likely
I'll
try
to
write
this
up.
Assuming
this,
this
addresses
the
issues
that
they've
raised
and
that
it
becomes
necessary
to
reach
some
networks.
D
B
D
Yeah,
it's
an
interesting
question.
The
I'm
not
sure
I
fully
understand
it,
but
I
do
know
that
the
same
the
same
question
actually
came
up.
I
spent
a
little
bit
of
time
with
dino
trying
to
to
see
his
his
lisp
approach
to
doing
ingest
and-
and
if
you
remember,
I
think
it
was
maybe
singapore.
He
talked
about
pulling
amt
into
into
a
network
over
using
lis.
I
forget
what
it
was
exactly,
but
it
ended
up
re-keying
the
sg
so
that
the
source
was
the
the
was
the.
A
A
C
C
B
C
B
D
D
Well,
no,
you
don't
have
any
local
assigned
group
for
this
and
and
sort
of
handle
that,
but
I
think
that
this
this
approach
is
relatively
simple
and
I'll
probably
be
doing
it
in
at
least
one
of
the
trials
we're
hoping
to
run
so
so
I
wanted
to
give
a
little
heads
up
the
immediate
problems
that
this
can
address
that
I
know
about.
Are
you
know
the
the
their
specific
local
ip
assignments
within
a
network?
There's,
maybe
asm
only
networks.
D
It
occurred
to
me
that
this
also
could
work
to
handle.
If
there's
a
network
that
is
only
transporting
v6,
or
that's
only
transporting
v4
and
you're
trying
to
join
the
opposite
kind
of
group,
then
you
can
do
that
that
translation
at
this
at
the
same
layer
there's
no
reason
that
the
translation
can't
map
between
v6
and
v4,
and
that
the
nat
service
can
maintain
a
population
count
and
perform
the
sort
of
group
assignment
and
and
make
decisions
about
yes
or
no.
D
I
don't
see
any
reason
that
you
couldn't
do
a
beer
encapsulation
this
way
as
well
or
to
do
it
to
integrate
with
the
the
layer
one
sort
of
rf
channels
for
this.
So
if
you're
gonna
be
sending
something
you
know,
I
think
that
a
lot
of
these
devices
have
some
support
for
mapping
specific
groups
into
an
rf
channel
already.
D
But
I
don't
know
if
there's
going
to
be
any
applicability
to
being
able
to
assign
a
sort
of
you
know
couple
that
inside
the
nats
service,
but
I
think
that's
all
like
tbd
and-
and
I
would
hope
only
to
leave
that
open
as
an
extension
path
not
to
put
that
into
the
first
version
of
the
of
the
service.
So.
B
I'm
wondering
if
I
mean
one
that
can
help
with
the
bgp
free
core,
maybe
because
you
can
get,
though
it
wouldn't
help
your
rpf
problems.
Underneath
you
know,
if
the
next
hop
isn't
it
was
an
lsp
though
there
are
apple.
There
are
implementations
that
do
support
that
I
mean
there's
a
so
there's,
there's
a
there's,
a
thing
called
gtm
which
enables
you
to
do.
D
D
Fortunately,
we're
all
engineers,
so
if
you've
got
a
suggestion
on
a
different
name,
that's
fine
I'd
love
to
have
it,
but
the
the
yeah
any
any
feedback
you've
got.
Please
please!
You
know
think
it
over.
Send
it
to
me,
because
I'm
probably
going
to
write
this.
If
I
don't
have
a
better
idea
just
to
make
it
so
that
you
know
all
the
operators
that
are
interested
have
a
good
path
to
to
participate.
B
D
D
D
The
rough
plan
is
to
use
the
multicast
ingest
platform.
That's
the
same
one
I
presented
back
when
I
started
working
on
the
dryad
stuff
or
right
before
that,
I
think
and
to
add
a
see
back
capability
to
it
so
that
it
would
be
using
the
the
global
you
know,
the
globally
discoverable
dorm
server
and
making
making
choices
about
bandwidth
allocation.
D
At
the
ingest
point
we
would
like
to
to
integrate
with
some
of
the
actual
operator
devices
as
well,
so
that
you
know
they'll,
ideally
we're
hoping
to
get
somebody
who's
willing
to
kind
of
take
that
that
seeback
code
and
port
it
into
driving
their
routers
api
to
to.
We
think
it's
possible
to
do
this
by
just
managing
the
acl
in
the
router,
so
that
see
back
can
cut
off
if
you're
over
can
cut
things
off.
D
If
you're
oversubscribed,
just
by
pushing
an
acl
thing,
we'll
see
if
that
works
out,
we
don't
really
know,
but
that's
kind
of
the
direction
we're
aiming
to
head
at
least
one
of
the
trials
assuming
we
we
do
get
by
n
would
probably
include
a
prototype
of
the
of
the
nats
or
mnat
service
that
we,
we
think
will
do.
I
may
or
may
not
have
to
write
that
before
I
write
the
spec
for
it,
but
you
know
at
some
point
if
that
does
seem
like
it,
it
makes
it
more.
D
B
Well,
just
one
bigger
question
have
have
you
gotten
feedback?
I
mean,
I
think,
the
the
three
drafts
nbc
back
and
dorms.
The
goal
is
to
you
know,
make
multicast
safe
for
the
browser
and
get
past
the
gateway
or
the
gatekeepers.
Have
you
gotten
feedback
thus
far
that
this
is
good
enough?
If
you
know
with
this,
yes,
they
will
allow
multicast
into
their
precious
browsers.
D
Nothing
quite
so
firm
the
the
authentication
story.
I
mean
that
was
all
the
browser.
Folks,
I've
talked
to
that's
the
first
question:
it's
like
how
do
you
authenticate
this
and
when
I
told
them
the
scheme
that
we're
using
in
mb
and
and
tried
to
just
honestly
describe
it
that
was
they
said
that
that
that
would
work
for
authentication
the
you
know.
D
There's
often
some
further
discussion
about
encryption
and
privacy
is
a
sort
of
unknown
still
because
there
is
some
privacy
what
they
call
it:
a
there's,
a
fingerprinting
footprint
to
to
the
the
joining
of
flows
from
a
browser
like
from
a
web
page.
So
this
is
a
concern
that
we're
not
really
so,
I
would
say,
there's
some
risk
on
that
front
as
well.
That's
that's
not
even
technical
risk,
but
sort
of
you
know
policy
risk.
D
D
You
know
if
what
it
might
end
up
being
is
more
like
you
know,
the
browser
will
have
to
ask
permission
in
order
to
join
in
order
to
enable
the
joining
of
multicast
flows
and
have
a
sort
of
you
know
like
the
way
cookies
are
where
you'd
have
a
sort
of
thing
that
pops
up
that
says
hey
this
browser
wants
to
join
some
flows.
This
could
expose
information,
learn
more
here
right.
D
D
B
So
should
we
be,
you
know,
is
there
a
formal,
you
know
request
for
review,
or
can
we
get?
You
know
those
folks
to
review
these
drafts?
I
guess
you
know
my
my
concern
would
be
you
know
we
go
through
this
process.
We
come
up
with
these
drafts
and
docs
and
we
think
they're
good
and
then
you
know
the
whole
purpose
is
so
that
we
can
get
into
the
browser
party
and
then
the
person
at
the
front
door
of
the
browser
says
no,
that's
not
good
enough.
D
That's
a
good
question,
so
there
is
for
me,
certainly
so
there's
a
sort
of
in
w3c
there's
a
tag
process
like
maybe
maybe
we
should
reach
out
to
a
w3c
liaison
and
ask
for
advice.
That
would
be
a
reasonable,
a
reasonable
idea.
I
think
you
know
I've
been
sort
of
like
there's
this
whole
reasonably
well
documented
path
for
how
individuals
are
supposed
to
try
to
get
things
adopted
by
by
w3c.
But
you
know
I
I
don't
know
if
it's
any
different.
B
E
Because
I
don't
participate
in
w3c,
but
I
could
probably
break
around
and
find
someone,
but
it
kind
of
sounds
like
proposed.
While
they've
got
an
infinite,
mirror
thing
proposed
idea
of
yeah,
I
don't
know,
but
okay
yeah
I
mean
it
seems
like
people
who
really
participate
in
w3c
should
make
better.
Just
ask
nicely
like
this
is
how
an
individual
does
it?
Do
you
give
any
special
priority
to
the
ietf
or
a
working
group?
I
believe
we
do
have
a
liaison
with
the
w3c.
E
B
D
D
Attention
so
the
the
question
at
this
point
is
more.
Like
you
know,
I,
I
guess
what
I
I'm
not
sure
I
haven't
done
as
much
with
the
w3c
engagement
process,
as
maybe
maybe
what
we
should
do
is
in
november
have
a
have
a
action
plan
for
making
sure
it
gets
on
the
on
their
list
on
the
tag
list
of
of
things
to
consider
for
real,
you
know,
and
maybe
that
would
include
updates
to
the
drafts
to
make
sure
they're
in
in
good
enough
shape.
D
D
I
feel
like
right
now:
the
barriers
are
more
technical,
there's
still
some
skepticism
as
to
well
this
will
this
actually
work
and
I'm
hoping
that
the
trials
will
address
part
of
that
you
know,
I.
I
don't
think
we're
going
to
get
away
from
the
risk
that
that
people
won't
likely,
but
that's
no
different
than
you
know.
Multicast
was
in
the
first
place.
B
B
Okay,
well,
I
would
say
first
of
all,
we
had
awesome
attendance
for
the
last
meeting
on
the
last
day.
I
don't.
I
think
this
is
in
20-something
years
of
going
to
ietfs.
This
is
the
first
time
I've
ever
been
in
a
working
group
meeting
at
the
end
of
on
the
last
on
on
friday
afternoon.
So
maybe
there
are
some
benefits
to
being
virtual
you're
being
you're
going
to
be
stuck
on
a
with
friday
on
the
friday
agenda.
I
guess
it's
good
to
be
a
virtual
friday
agenda.
