►
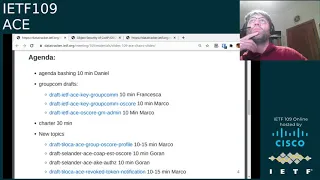
From YouTube: IETF109-ACE-20201118-0500
Description
ACE meeting session at IETF109
2020/11/18 0500
https://datatracker.ietf.org/meeting/109/proceedings/
A
A
A
A
C
He's
been
involved
in
quite
a
lot
of
things
and
of
course
he
predates
me.
I've
only
been
in
the
itf
for
about
eight
years
and
when
I
came
in,
he
was
already
an
old
hand,
but
he
was
definitely
always
willing
to
offer
advice
even
to
young
fresh
faces
like
I
was
at
the
time
I
do
know
his
hands
were
on
many
of
the
foundational
rfcs
for
things
like
cms
or
some
of
the
crypto
algorithms,
and
I
came
to
rely
on
him
for
for
pique's
questions.
C
I'm
still
not
sure
I
got
a
full
view
of
what
he
did
for
the
itf,
because
I'm
sure
there
are
things
that
he
did
that
I
don't
know
about,
but
I
can
definitely
say
that
his
his
efforts
were
not
limited
to
just
the
security
area.
They
were
not
limited
to
a
class
of
technology.
He
really
was
quite
well-rounded.
C
C
He
was
just
so
incredibly
selfless
and
generous
in
his
time
and
his
expertise.
I
certainly
relied
on
him
for
many
things.
I
know
others
did
as
well,
and
you
know
it's
sort
of
strange
to
think
that
he
was
just
so
selfless
and
so
helpful
that
the
only
time
that
he
really
felt
the
need
to
say
no,
I
can't
help
you
right
now
was
actually
at
the
winery
during
the
pressing
season.
C
A
A
A
A
A
A
A
A
Would
say
we
also
have
a
few
bunch
of
documents
waiting
for
ifg
approval
to
be
sent
to
the
rfc
editor
one,
which
is
the
dhl,
is
authorized.
I
I
believe
this
one
is,
is
pretty
much
ready
to
be
sent.
We
had
just
a
yesterday
or
today,
depending
on
time
zone.
The
last
version
of
oauth
earth
drafts
that
addressed
all
the
comments
we've
received.
It
was
in
working
with
last
call
and
we
have
also
the
oauth
param
that
is
being
waiting
for
some
time.
A
A
E
A
A
C
A
A
A
F
So
I
think
people
haven't
really
looked
at
inheritance,
a
lot
and
maybe
people
haven't
implemented
inheritance
yet
in
the
various
protocols.
So
I
think
it
would
be
useful
to
get
some
feedback
about
that.
Of
course,
we
can
finish
this
draft
without
inheritance,
but
it
sounded
like,
like
a
good
way
to
solve
various
problems
that
we
were
having
with
post
actions.
E
A
E
E
For
a
group
member
to
join
a
group
and
it
uses
the
ace
framework
in
the
first
part
of
the
exchange,
documentation,
request,
response
and
a
token
post,
and
then
it
defines
other
operations
between
the
client
and
the
kdc,
which
means
key
distribution
center
to
join
the
group.
So
in
this
in
this
figure,
it's
only
about
the
group
joining
request,
a
response,
but
there
is
more
operations
that
are
defined
yes
and
after
that
the
the
client
can
do
secure
group
communication.
E
E
Since
itf
108,
a
lot
has
happened.
We
have
submitted
version
nine
based
on
a
follow-up
review
from
jim,
which
we
discussed
at
itf
on
108
and
close
24
issues.
If
I'm
not
wrong
and
then
also
christian
gave
us
a
review.
Thank
you
for
that
christian
and
we
have
vanapu
requested
to
be
the
next
version
version
10,
based
on
that,
based
on
that
review,
and
you
can
see
the
details
in
the
github
next
slide.
Please.
E
E
We
try
to
remove
as
much
as
possible
text
that
was
duplicated
from
either
the
ace
framework
or
from
other
sections
of
the
document,
and
then
there
was
some
minor
changes
with
or
yeah
modify
the
error
code.
If
a
client
is
not
a
member
of
the
group
and
is
trying
to
access
resources
that
are
dedicated
members
from
four
zero
zero,
that
quest.
E
E
E
Dealing
two
or
three
possible
solutions,
so
the
first
solution
is
to
solve
this
locally,
so
to
prefix
the
scope
with
a
byte,
and
this
byte
will
indicate
which
application
profile
of
ace
is
being
used
and
to
make
this
effective.
This
needs
to
be
agreed,
of
course,
between
a
resource,
server
and
authorization
server,
and
if
the
same
scope
is
reused
for
several
resource
servers,
they
need
to
sync
this.
This
value
of
this
byte
for
like
for
each
application
profile
with
the
authorization
server.
E
This
has
the
drawback
that
the
this
will
be
longer:
prefix,
local
or
locally
agreed
prefix,
maybe
only
one
byte.
It
depends
on
how
big
of
a
seaboard
tag
we
would
go
for
so
for
now
we
only
can
see
that
we
would
register
a
keyboard
tag
for
only
for
the
ask
group
oscar
profile,
because
this
is
not
the
only
application
profile
we
have
and
but
later
on,
we
would
have
one
for
each
application
profile.
Encoding
and
the
question
is:
is:
is
it
too
much
to
have
one
keyboard
tag
for
each
application
profile?
E
E
E
A
F
F
F
F
E
F
E
E
E
E
E
C
So
I'm
not
sure
if
this
is
exactly
the
question
that
kirsten
was
trying
to
raise.
But
you
know
when
you're
in
the
scenario
where
you
have
some
things
that
are
already
agreed
to
out
of
band
and
then
you're
talking
about.
Do,
I
need
to
add
a
inbound
mechanism
to
disambiguate
something
else
you
have
to
ask
yourself.
C
Is
this
something
else
that
I'm
trying
to
disambiguate
something
that
could
be
agreed
out
of
band
as
well,
because
I
already
have
this
out-of-band
mechanism
and
my
understanding
is
that
the
answer
is
no,
that
we
do
need
an
inband
mechanism
here,
because
the
sort
of
knowing
what
email
means
that
we
say
is
is
out
of
band.
That's
like
a
universal
constant
in
some
sense,
and
the
particular
encoding
used
by
the
different
profiles
is
something
that
can
change
and
you
won't
know
a
priori.
C
E
Yeah
and
daniel,
if
you
could
go
back
one
slide
just
to
go
on
the
slide
on
the
issue
itself,
rather
than
the
solution.
Yeah
that
that's
the.
What
you
said
then,
is
that
this
happens
when
the
client
send
the
post
token
and
the
the
kdc
or
resource
doesn't
have
other
information
about
what
application
profile.
E
F
About
I
need
to
think
about
this,
some
more
because
I'm
not
entirely
sure
what
the
various
uniqueness
requirements
here
are
and
what
what
the
consequence
of
not
achieving
uniqueness
actually
are
and
what
the
attack
vectors
are
and
so
on.
So
I
think
I
have
to
take
this
offline,
but
generally
registering
sibo
takes
is
is
something
that
you
can
easily
do
registering
one
byte
c
bar
takes
well.
There
are
only
so
many
of
them.
E
E
E
E
A
G
E
Case
it's
more
about
what
is
simpler
for
or
what
is
more
convenient
for
implementers
in
some
cases,
as
I
said
in
some
cases,
you
don't
even
need
to
have
an
indication
of
what
scope
you're
using
because
maybe
you're
only
using
one
application
profile.
You
have
already
communicated
with
that
with
the
aes.
A
E
E
And
then
to
the
last
slide
plan
forward,
so
I
guess
the
first
point
should
be
talk
about
more
about
this
scope,
encoding
problem
and
solution.
We
have
some
other
minor
clarification
to
do.
We
want
to
submit
definitely
submit
a
new
version
before
we
can
think
about
moving
forward
to
working
group.
Let's
go.
A
A
B
B
Right
just
as
a
quick
recap
here,
I
know
they're
interested
in
joining
another
group
contacts
and
authorization
server
to
get
an
access
token,
as
an
evidence
of
being
authorized
to
be
a
group
member
with
a
particular
role
or
a
set
of
roles.
The
token
is
posted
and
what
follows
is
joining
request,
joining
response
exchange,
and
especially
the
the
ace
client
here,
gets
in
return.
B
The
key
material
needed
later
on
in
the
group
to
communicate
with
other
group
members,
and
the
focus
is
really
about
that
getting
authorization
to
get
into
the
group
and
get
the
group
key
material.
Other
things
like
communication
in
the
group
or
accessing
resources
of
group
members
or
autoscope
of
this
document,
their
cover
somewhere
else
next
slide.
B
B
This
is
useful
for
verifiers
too,
to
have
an
idea.
Oh
it's
again
about
that
group
with
that
name
and
continue
getting
public
keys
for
verifying
signatures
of
flying
messages,
and
just
as
a
reminder
here,
we
are
considering
scope
as
encoded
building
on
an
aif
data
format
with
a
find
already
in
the
previous
version
right.
B
There
are
also
some
updates
in
the
in
the
main
parameter
of
the
joining
response
transporting
the
the
key
material
to
a
new
joining
member.
We
used
to
have
a
client
id
parameter
borrowed
by
the
oscar
security
context,
object
and
that
parameter
was
removed
from
that
object.
Definition
in
the
last
update
of
your
score
profile,
so
we
simply
have
to
rename
that
parameter
as
group
center
id
now
also
registered
as
a
new
element
of
that
object,
but
all
in
all
keeping
the
same
meaning.
B
B
In
the
group,
of
course,
to
describe
what
algorithms
and
parameters
are
used
when
the
pairwise
mode
has
to
be
used
to
communicate
in
the
group
and
default
values,
just
like
for
other
parameters
are
also
defined
in
the
corresponding
section
and
the
moment
we
have
introduced
these
parameters
explicitly
signaling
the
pairwise
mode
and
how
it
is
supposed
to
work.
We
didn't
need
anymore,
separate
policy
to
tell
that
the
group
can
rely
on
that
mode
as
well.
B
Write
some
clarifications
also
on
on
the
requiem
process.
It
can
happen.
We
say
the
rate
that
the
group
member
can
request
for
a
new
sender
id
from
the
group
manager
for
a
number
of
reasons.
In
that
case,
it's
up
to
the
group
manager
to
decide
what
to
do
exactly.
It
can
just
provide
a
new
sender
id
or
instead
rekey
the
whole
group,
or
do
both
so
the
this
possible
set
of
alternatives
have
been
clarified.
B
Also,
we
we
have
tried
to
align
the
bit
better.
The
group
manager
described
here
with
requirements
and
and
no
reassignment
policies
already
stated
in
the
group
score
document
or
the
non-recycling
of
sender,
ids
and
group
ids,
there's
been
a
discussion
also
earlier
this
week
about
this
exact
point
at
the
core
meeting.
So
something
is
going
to
be
updated
in
the
group
score
document.
B
It
will
be
reflected
here
when
it
comes
to
these
details
and
finally,
we
we
had
a
resource
type
registration
for
this
joining
resource
that
can
be
contacted
by
joining
notes
to
access.
The
group
that
used
to
be
registered
in
another
document
in
in
the
co-working
group
and
the
actual
registration
was
in
fact
moved
here
and
well.
The
resource
type
can,
for
instance,
be
useful
for
the
sake
of
discovering
joining
resources,
just
sending
a
request
to
well
known,
for
instance,
next
slide,
please
yeah.
As
a
next
step.
B
I
expect
at
least
one
more
iteration
to
to
align
this
document
with
with
the
plan
changes
in
ace
giga.com
and
with
some
things.
I
also
mentioned
before
in
the
in
the
group
score
document,
for
instance,
about
no
recycling
policies
of
ids,
we've
been
continuing
working
on
implementation
and
the
whole
interface
of
the
group
manager
is
almost
complete.
I
think
only
only
three
operations
are
missing.
We
plan
to
have
some
tests.
B
B
B
B
Yeah
this
one
yeah,
thank
you
so
yeah.
This
is
another
interface
we
are
describing
at
the
very
same
group
manager.
This
document
was
adopted
following
the
previous
itf
meeting
next
slide.
Please
all
right.
While
in
the
previous
presentation
we
focused
on
the
interface
for
joni
nodes
to
access
the
group
and
get
the
key
material.
B
So,
overall,
for
the
sake
of
this
interface,
the
group
manager
has
one
single
instance
of
a
group
collection
resource
at
the
path
say,
slash
manage
essentially
including
the
the
list
of
existing
oscar
groups
and
then
for
each
existing
oscar
group.
One
group
configuration
resource
in
fact
mentioned
in
that
list
and
each
group
configuration
resource
can
be
accessed
as
at
slash,
manage
slash
well,
the
name
of
the
group,
and
it
includes
the
the
current
configuration
for
the
adult
score
group
here.
B
So
on
the
left,
you
can
see
the
the
possible
operation
on
the
root
single
group
collection
resource.
What
we
have
today
is
a
post,
a
center,
the
group
collision
resource
to
create
a
new
group.
In
fact-
and
already
at
this
point
in
time,
it's
possible
to
provide
a
configuration
for
that
group,
otherwise
default
values
apply
and
when
a
group
is
created,
that
practical
mean
two
things.
B
B
Right
now
we
can
modern
update,
I
should
say,
override
all
together.
The
current
configuration
of
the
group
brutally,
with
a
put
we
have
plans
to
introduce
patch
also
for
a
selective
update
and
issuing
a
delete
to
this
resource.
Instead,
we
just
destroy
the
group,
so
of
course,
there's
no
safe
operations
have
a
side
effect
on
the
group
and
the
group
members
that
we
are
also
describing
in
the
document
next
slide.
Please
right
in
this
particular
update
related
to
what
I
mentioned
before,
also
for
the
other
document.
B
As
I
mentioned,
we
have
also
introduced
the
the
fetch
method
for
the
group
configuration
resources
that
we
are
supporting
already,
both
in
the
sieber
and
in
the
choral
case.
So
this
is
about
retrieving
just
part
of
the
configuration,
so
only
parameters
indicated
in
the
fetch,
payload
and
the
values.
B
B
Please
right.
We
have
also
clarified
this
point
who
take
the
final
decision
on
the
invariant
once
then,
once
established
group
name,
so
we
still
have
the
possibility
for
the
administrator
asking
to
create
a
group
to
specify
an
intended
group
name,
but
then
the
final
decision
remains
on
the
group
manager
that
picks
up
a
final
group
name
also
returned
to
the
administrator
in
the
response,
and
it
seems
to
be
the
best
way
and
as
also
suggested
by
by
christian,
I
think
at
the
discussion
at
the
previous
meeting.
B
B
For
instance,
the
registration
of
the
security
group
in
in
objects
like
resource
directory
so
simplifying
discovery
of
this
security
group
and
links
for
john
8
to
other
nodes.
It
was
also
something
already
suggesting
in
a
discussion
in
core
related
to
coral
and
choral
forms,
but
essentially
makes
the
group
manager
aware
of
the
application
groups
that
are
using
or
are
going
to
use
the
security
group
next
slide.
Please
that
also
clarifies
this
a
bit
more
yeah
following
the
creation
of
a
security
group
here
and
now
that
the
group
manager
has
more
information.
B
The
group
manager
or
the
administrator
can
in
fact
proceed
registering
the
link
to
join
the
security
group.
To
separate
entities
like,
for
instance,
the
the
resource
directory
and
now
it's
much
better
that
the
group
manager
knows
also
the
the
names
of
the
application
groups
involved,
and
they
are
in
fact
used
as,
for
instance,
target
attributes
in
a
particular
approach.
We're
describing
for
for
doing
this
in
another
core
document.
B
We
also
give
overall
guidelines
about
this
process,
and
we
we
do
recommend
that
the
group
manager
really
does
that,
because
it's
it's
the
one
most
likely
to
to
remain
up-to-date
on
possible
changes
related
to
the
oscar
group
or
even
its
own
address
and
uri.
They
would
require
a
refresh
on
what
registered
in
the
resources
directory.
B
Next
and
final
slide.
I
guess
please:
okay,
yeah,
summarize
new
interface
on
the
group
manager
for
administrators
to
create,
configure
and
delete
the
oscar
groups.
We
have
quite
a
good
set
of
operations
already
to
be
continued
and
finalized.
We
have
full
support
already
for
link
format
and
sieber
or
coral
operations
and
messages
as
immediateness
steps.
B
This
would
open
the
way
also
to
allow
some
actions,
not
necessarily
all
of
them,
also
to
other
administrators
coming
in
later
on
also
different
from
the
exact
administrator
that
did
create
the
group
and
also
expanding
on
a
previous
discussion
of
choral
forms
that
I
mentioned.
Also
in
the
previous
slide.
B
We
can
give
some
more
guidelines
when
coral
is
used
in
the
response
to
the
administrator
following
the
registration,
especially
in
case
something
went
wrong
to
guide
the
administrator
on.
What's
the
correct
way
to
proceed
for
correct
group
creation
in
times,
for
instance,
of
message,
format
and
api,
and
that
should
be
all
from
my
side.
Thank
you.
D
I've
seen
in
in
this
document,
but
also
in
many
other
ace
documents,
so
this
might
be
more
general,
a
lot
of
resources
that
are
given
with
in
the
document
with
basically
with
a
path
that
starts
with
slash.
So
how
is
very
generally
best
practice
190
about
uri,
namespace
ownership
and
path
ownership
treat
it
here.
How
is
this
managed
entry
point
supposed
to
be
discovered?
D
B
As
far
as
I
know,
we've
been
following
the
the
wording
already
from
the
ace
framework
about
this
is
a
default
example,
or
not
even
default,
actually
just
an
example.
Your
implementation
can
go
for
something
else,
and
we've
been
trying
to
use
resource
types
to
help
discovery
and
well.
The
framework
two
versions
ago,
I
think,
introduced
also
a
resource
type
for
one
of
its
resources
to
support
discovery.
D
I'll
look
through
the
document
with
with
the
focus
on
this,
but
if,
if
slash,
if
this
is
a
discovered
entry
point,
it's
it's
probably
okay,
so
I
think
there's
a
there's,
a
rough
preference
for
things
that
don't
give
that
static
structure
at
all.
But
if
this
but
kind
of,
if,
if
the
structure
is
given
under
the
an
entry
point,
it's
probably
okay.
D
C
To
jump
in
this
has
been
kirakos
sadie
again.
I
think
the
intent
is
that
in
the
document
we
refer
to
like
a
name
of
the
endpoint,
a
descriptive
name,
and
maybe
the
slides
were
not
as
careful
about
using
the
descriptive
name
instead
of
slash
name,
but
I
think
the
documents
tend
to
be
more
careful
about
that.
A
A
A
G
Hi,
I
was
distracted
by
the
buff
as
well,
but
I'm
reading
this
I
read
it
before
so
the
last
part
about
est
tl
esp
est
co-app.
Well,
so
that's
done
it's
in
the
rfc
editor's
queue
you
could.
I
think,
at
this
point
strike
it
from
the
charter,
except
for
the
question
about
someone
would
like
to
do
cmp
now
and
I
always
thought
it
was
weird
to
do
this
in
this
group
in
the
first
place.
G
I
G
I
So
this
is
your
own.
I
I
I
disagree
with
the
change
here.
I
I
propose
this
paragraph
because
we're
done
with
one
part
of
the
est
profiling,
but
we
are
not
part
done
with
the
other
part,
so
remind
you
about
the
ace
interim.
If
this
was
discussed
on
the
mailing
list,
there
was
an
ace
interim
in
three
years
ago,
where
we
discussed
different
profiles
of
the
est
protocol,
and
one
is
done,
but
the
other
is
not.
So
that's
why
I
proposed
a
charter
text
which
included
both
to
illustrate
that
we
have.
I
G
I
J
A
Okay,
so
I
am
hearing
that
everyone
agrees
with
the
text
now.
The
thing
is
that
I
I
would
like
to,
but
I
mean
this
is
my
personal
opinion
I
would
like
to.
I
mean
the
current
charter
does
not
mention
cmp
and
east
profile,
so
I
am
wondering
I
would
like
to
avoid
to
have
that
discussion
again
and
again.
C
A
C
A
A
B
B
H
B
So
why
are
we
doing
this?
There
are
use
cases
where
you
want
to
have
a
good
communication
and
you
want
to
secure
it,
for
instance
with
a
group
of
score
and
on
the
communication
side
we
are
fine
and
we
have
solution
to
enforce
access
control,
to
access
the
group
and
get
the
key
material
to
use
group
score
in
the
group.
B
That's
essentially
what
we
saw
in
the
previous
presentation
today
we
argued
as
a
separate
domain
to
cover
in
terms
of
us
of
access
control,
though,
if
you,
if
you
use
simply
the
document
we
saw
before
and
you
are
authorized
to
get
into
the
group,
you
do
that
and
you
get
the
key
material
for
very
simple
use
cases.
This
is
just
fine
and
you
don't
need
to
do
anything
more,
in
particular
for
the
sake
of
access
control
once
in
the
group.
B
We
just
argue
that
it's
not
fine
in
general,
where
you
may
want
to
have
different
clients,
authorized
to
do
different
things
at
different
group
members
to
con
to
be
considered
as
resource
servers.
Essentially,
you
have
different
classes
of
access
rights
for
different
clients
and
sure
one
can
try
to
address
this.
Just
creating
several
security
group
groups,
one
for
each
class
of
access
rights,
but
they
would
complicate
management
of
groups
and
key
material
considerably,
especially
in
case
classes
of
access
rights,
change
over
time,
requiring
change
of
group
and
possibly
rekeying.
B
Please
so
just
to
give
examples.
The
first
one
is
really
a
toy
example:
a
simple
home
automation,
application,
for
example,
when
you
may
want
to
have
some
clients,
like
kids,
only
able
to
check
the
status
of
a
lock
while
parents
are
instead
fined
to
both
check
and
change
the
status
of
the
lock
or
or
even
a
more
simple
detail.
You
may
want
locks
to
to
act,
only
resource
servers
and
not
to
start
opening
and
closing
each
other.
B
B
B
B
We
also
saw
today
the
second
domain
that
we
argue
should
be
addressed
separately
instead
in
general,
is
about
ones
in
the
group
having
authorized
access
with
fine
grain
access
control
at
the
recesses
of
other
group
members
and,
of
course,
one
can
think
of
using
ace
and
the
access
tokens
for
that.
So
you
need
a
profile.
Well,
the
current
profiles
around
don't
cover
access
control
with
secure
group
communication
in
in
the
domain.
I
I'm
really
addressing
here.
B
The
closest
thing
we
can
have
is
the
score
profile,
but
of
course
it
considers
the
oscore
protocol,
not
group
of
scores,
so
it
doesn't
really
target
a
group
communication,
so
it
seems
we
are
missing
a
transport
profile
with
fine
grain
access
control
and
supporting
secure
communication
practically
with
the
group
score
protocol
next
slide.
Please.
B
And
that's
essentially
the
proposal
of
this
document,
so
it
describes
a
new
transport
profile
using
grouposcore
a
security
protocol
between
the
client
and
resource
servers,
as
already
members
of
the
group
and
I'll
come
back
to
this
point,
but
we
have
try
to
clarify
in
as
best
as
possible
the
timeline
here
in
the
document.
So
the
client
and
resource
servers
consider
here
are
already
group
members.
The
joining
happened
first
for
both
of
them,
according
to
the
approach
of
the
document
presented
earlier
today.
B
B
The
resource
server
can
can
achieve
proof
of
group
membership,
so
to
say
so,
it
can
actually
check
that
the
client
is
indeed
a
member
of
that
oscar
group
and
there's
also
mutual
authentication.
That
is,
of
course,
achieved
only
when
a
full
exchange
is
completed
liking
the
escort
profile
by
the
way
next
slide.
Please
so.
B
Updates,
mostly,
I
would
say,
okay
cool
thanks.
Please
continue
yeah
yeah,
a
number
of
dates
updates
have
been
included
in
this
latest
version.
As
I
mentioned,
we
clarified
the
timeline
that
was
mostly
requested
by
ben
actually
in
the
singapore
meeting
last
year.
So
this
is
really
about
something
for
nodes
that
are
already
group
members.
The
join
have
to
have
to
has
to
happen
first,
then,
we
have
considerably
simplified
the
the
profile
and
the
workflow
of
the
protocol
itself,
thanks
to
input
from
joran.
B
Still
we
added
an
appendix,
including
what
used
to
be
the
original
version
of
this
profile
and
considering
both
oscor
and
group
score
and
security
protocol.
So,
in
addition
to
that,
you
would
also
have
the
possibility
to
establish
a
pairwise
or
security
context
between
a
client
and
the
resource
server.
B
C
B
But
this
is
the
core
of
the
proposal,
essentially
so
so
checking
this
at
a
high
level.
A
client
is
interested
to
to
access
with
fine
grain
access
control
resources
at
two
group
members
rs1.
There
is
two
here:
it
gets
a
token
for
rs1.
Just
some
of
the
new
informations
I
did
here
are
also
in
the
slide.
So
first
token
is
received
and
posted
and
confirmed
next
slide.
Please
yeah
the
same
happens
to
get
a
token
for
rstu,
also
posted
to
rsdu
next
slide.
B
Please
yeah
and
following
that,
the
client
can
send
a
request
in
group
score
in
this
example,
over
multicast
and
in
group
mode
received
by
the
two
resource
servers.
They
each
reply
with
one
response
in
group
score
that
can
be
either
groupon
or
payouts
mode,
and
I
said
before,
for
either
mode
proof
of
possession
is
achieved
at
the
resource
server,
either
by
directly
verifying
a
counter
signature
or
decrypting.
The
message
in
the
first
place,
using
a
pairwise
key
derived
out
of
the
asymmetric
keys
of
the
two
nodes.
B
Next
slide,
please
yeah.
It's
a
new
transfer
profile
base
to
bring
fingering
access
control
as
per
ace
security
protocol,
and
we
still
have
an
appendix
describing
an
old
version
with
both
all
scoring
group
score
and
security
protocol.
So
these
changes
incorporated
mostly
comments
from
from
ben
and
joran
and
as
next
step,
we
would
like
to
give
guidelines
on
how
even
the
main
mode
with
the
group
of
score
only
the
client
can
possibly
go
separately
for
an
execution
of
the
oscar
profile,
as
is
in
case.
A
A
I
I
I
Now
we
already
mentioned
today
cms
and
cmc,
which
jim
shard
worked
on,
and
we
have
the
enrollment
of
secure
transport
and
then
the
draft
which
is
soon
for
publication,
the
esd
co-op
s,
draft,
protecting
esd
payloads
over
dtls
and
co-op,
and
this
draft
is
closely
following
that
draft,
but
replacing
dtls
with
that
hopkins
low
score.
Next,
like
this.
I
E
I
It's
section
by
section
copying
stuff
from
from
ust
or
referencing
the
corpus
profile
of
sd
yeah.
You
see
here,
discovery
the
functions,
the
payload
formats,
measured
findings,
response
codes
and
the
delayed
responses
which
is
defined
in
that
draft
introduced
in
that
graph,
and
then
fragmentation
next
slide.
I
So
you
need
to
proxy
the
enrollment
request
and
with
the
use
of
oscore
you
don't
need
to
do
anything
est
related
in
the
proxy,
so
you
could
actually
just
just
pass
it
on
and
then
you
could
get
end-to-end
security
and
that's
the
next
slide
last
slide
is
next
steps.
We
need
to
complete
the
additions
on
on
the
the
new
est
function,
submit
a
new
version.
I
A
A
I
I
A
I
I
I
I
I
This
presentation,
so
here
here,
is
a
slide
showing
how
different
different
components
can
be
different
drafts
can
be
used
to
make
this
more
efficient.
In
the
we
see,
we
see
the
ad
hoc
exchange,
the
blue
messages,
and
we
see
the
enrollment,
the
black
box
and
the
black
messages.
That
was,
that
was
previous
draft,
and
this
described
here
in
this
session.
I
I
I
I
I
We
do
have
a
trust
relationship
between
the
device
and
the
trusted
third
party.
That's
exactly
what
we're
using
here:
authorization
server!
It
could
be
in
the
brewski
case.
It's
the
manufacturer,
authorization
service,
or
it
could
be
some
other
some
other
trusted
third
party
and
v,
and
w
only
have
sort
of
a
web-based
trust
so
that
they
could
look
up
and
have
some
implicit
trust
anchors
and
they
could
verify
their
yes
certificates.
I
I
G
I
I
I
I
So
if
you
compare
the
if
we
map
the
authenticator
to
the
client,
the
device
to
the
constrain
device
to
the
resource
server
and
the
authorization
server
to
the
authorization
server,
we
get
something
like
this.
And
if
you
look
at
the
assumptions
it
seems
to
to
match
what
the
assumptions
are
are
for
ace.
I
The
rs
provides
information
about
location
of
the
aes
to
c
that's
the
as
request
creation
hints
the
rs
and
the
as,
on
the
other
hand,
they
have
a
strong
cross
relationship
in
this
case,
sharing
by
the
rs
having
the
public
key
of
aes
and
the
as
can
can
can
look
up
information
about
the
rs
and
provide
that
to
the
client,
whereas
the
relationship
between
the
client
and
the
authorization
server
is
is
not
strictly
specified
in
in
the
ace
framework
and
the
one
way
of
resolving.
That
is
some
sort
of
web-based
trust.
I
I
I
So
I'm
wrapping
up
this
two
more
slides.
This
is
just
so.
There
was
a
lot
of
arrows
in
the
in
the
previous
pictures.
The
actual
content
of
the
draft,
which
is
it's
of
course,
work
in
progress,
still,
is
that
we
we
produce
two
new
auxiliary
data
types
for
ad
hoc,
which
contains
this
information
that
needs
to
be
carried
between
client
and
and
authenticator
between
device
and
authenticator.
Sorry-
and
there
is
what
michael
called
an
ultra-constrained
voucher
matching
the
brisket
terminology,
which
is
just
a
mac
of
this.
I
This
data
that
comes
from
from
the
authentication,
server
authorization
service,
sorry
and
then
with
the
exchange
of
data
between
the
authenticator
and
authorization
server,
which
is
independent
of
transport.
But
there
is
an
ace
map
being
described
in
this
draft
and
then
some
security
processing
next
slide.
I
There
are
plans
definitely
to
implement.
I
don't
know
if
michael
want
to
say
more
what
what
exists
and
what
does
not
exist
and
ben
also
commented
that
rfc
yeah,
the
voucher
rfc
can
be
useful
for
more
than
just
versky,
and
if
someone
wants
to
say
anything
about
that,
that
would
be
great.
Maybe
michael
is
the
right
person
here
bear
in
mind
now,
michael
that
I've
already
taken
all
the
time
for
this
presentation.
I
A
B
Yes,
thank
you
again,
final
presentation.
This
work
was
presented
last
time
at
the
june
interim
we
had.
I
think
the
problem
we
are
addressing
is
that
access
tokens
can
be
revoked
before
their
intended
expiration
time
for
a
number
of
reasons,
clients
and
resource
service
compromised.
The
policies
of
their
outcome
have
changed
or
da's
profile
to
use
with.
B
So,
for
example,
a
client
can
get
only
this
kind
of
information
for
the
tokens
it
has
received
in
the
first
place,
and
this
complement
the
already
available,
of
course
token
introspection,
editorization
server
and
it
doesn't
require
at
all
any
new
endpoint
on
the
client
or
there
is
a
server
next
slide.
Please.
B
B
Really,
the
client
and
resource
server
will
get
the
exact
url
to
that
trl
resource
at
the
authorization
server
and
then,
as
I
said,
they
can
send
requests
for
the
pertaining
portion
of
that
list
or
observe
it
for
for
changes,
but
we
are
actually
admitting
a
special
requester
like
an
administrator
that
can
in
fact
get
back
the
full
content
of
that
list.
So
right
now
we
have
two
different
modes
of
operations
in
in
full
query
mode.
You
can
get
back.
B
In
fact,
all
the
pertaining
portion
of
the
list
and
and
the
related
token
ash
is
included
there
in
this
query
mode.
You
can
instead
get
back
a
set
of
most
recent
updates
that
happened
to
that
part
of
the
list
pertaining
to
you,
and
we
have
recently
improved
that
based
on
feedback.
We
got
next
slide.
Please.
B
So
since
version
one
that
that
was
presented,
in
fact
in
the
june
interim
now,
we
are
in
in
version
three.
The
the
latest
version
especially
addresses
review
comments
from
from
karsten
posted
on
the
list
after
the
interim
and
comments
we
got
from
from
bain.
Also
during
that
same
interim,
so
we
clarified
even
better
providing
examples.
B
B
So
now
we
have
a
single
query,
parameter
that
specifies
the
number
of
requested,
most
recent
updates
in
the
response
and
the
response
payload
that
used
to
to
be
based
on
zebra
maps
and
now
is
essentially
an
array.
So
so
the
the
outer
payload,
the
overall
payload
is
an
array,
including
the
different
updates
happen
to
the
list
as
individual
elements
that
are
in
turns
array
and
then
for
each
update.
We
specify
which
token
ashes
have
been
added
or
removed,
especially
for
that
for
that
update
next
slide.
Please.
B
So
other
than
that,
following
a
recommendation
from
men
when
the
registration,
the
initial
registration
happened
at
the
authorization
server
what's
returned,
is
not
only
the
exact
url
to
this
list
resource,
but
also
the
identifier
of
the
exact
hash
algorithm
used
and
we've
also
added
more
interaction.
Examples
we
used
to
have
only
one
in
full
query
mode.
We
we
added
two
in
diff,
query
mode,
also
using
observation.
In
fact,
we
also
added
two
big
appendices.
B
The
first
one
follows
carson's
review
where
he
was
suggesting
to
check
the
series
transfer
pattern
and
well,
it
was
right.
There
was
also
inspiring
and
in
appendix
a
we
described.
How
yeah
the
diff
query
mode
proposed
here
is,
in
fact
an
instance,
an
example
of
usage
of
that
series
transfer
pattern
and
we
define
the
the
alignment
more
in
detail.
B
We
we
have
the
interface
defined,
also
considering
all
observation
as
initial
intention
for
unsolicited
information
of
revoked
tokens,
and
this
latest
version,
as
I
mentioned,
included
especially
review
from
carson
comments
from
ben,
but
further
builds
on
an
earlier
review
on
the
list,
from
trevi
spencer
and
comments
and
discussion
from
jim.
As
immediate
next
step,
we
would
like
to
try
to
move
that
appendix
p
to
the
document
body
as
an
actual
third
mode
of
operation
like
an
enhanced
query
mode
and
all
considering
the
the
current
status
and
the
previous
reviewed.
B
A
A
I
mean
we
should
start
focusing
on
finalizing
the
work
that
is
being
in
progress,
so
I
I'm
I
have
in
mind
the
current
working
group
documents
and
the
the
other
track
for
us
is
to
recharge
as
soon
as
possible.
So
I'm
gonna
send
the
the
charter
on
the
mailing
list
and
then
I
think
that's
gonna
be
on
ben's
spot
to
move
that
to
the
isg.
