►
From YouTube: IETF109-LSR-20201116-0500
Description
LSR meeting session at IETF109
2020/11/16 0500
https://datatracker.ietf.org/meeting/109/proceedings/
A
A
B
C
C
C
C
C
B
B
C
B
B
These
are
these
are
good,
as
especially
as
we
spend
a
lot
of
time
on
these.
Those
people
know
that
we
are
involved
in
for
ospf.
It
allows
us
to
get
down
to
much
many
fewer
lsas
for
all
the
different
applications
that
we're
going
to
support.
I
mean
so
this
was
this.
This
is
great
that
these
are
done
next
slide.
B
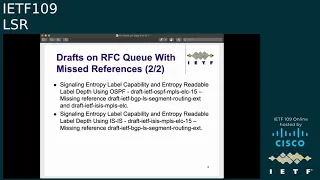
We
have
the
same
drafts
with
missed
references,
the
two
yang
models
ospf
and
isis,
and
the
tunnel
end
caps.
Now
the
tunnel
end
caps
appears
to
me
moving
along
in
idr.
They
got
a
new
editor.
Thank
you,
john
and
it's
hopefully
it'll
be
published
soon
and
that'll
go
now
another
thing
about
these
giraffes.
These
three
drafts-
these
are
the
last
ones
that
don't
have
lsr
in
the
name.
So
after
this
we'll
have
finished
all
the
work
when
we
had
separate
isis
and
ospf
working
groups,
next
slide.
B
B
B
I
think
for
the
ospf
and
isis
segment
routing
the
base,
the
mpls
based
segment.
Routing
yang
models
are
also
ready.
I'm
an
offer
on
that
we'll
we'll
probably
last
call
them
before
the
next
ietf.
Additionally,
the
reverse
metric,
that's
augmentation
to
the
isis
yang
model.
That's
on
the
rcq.
I
think
I
I'll
I'll
working
group
last
call
that
one
probably
with
before
within
the
next
few
weeks
and
extended
lsas.
I
think
this
is
also
ready.
C
Yeah,
I
was
gonna
mention
my
mic
didn't
unmute
last
time,
but
on
the
on
the
prefix
originator,
I'm
shepard
on
that
one
and
it's
it's
ready
to
go
when
it
went
into
work.
In
your
blast
call
there
was
some
contention
over
some
use
cases
being
removed
and
that
got
resolved.
The
use
cases
were
removed.
So
if,
if
anybody
we'll
be
doing
we'll
be
ending
the
last
call
very
soon,
so
if
there
are
any
more
objections,
then
please
post
them.
I
don't
believe
there
are.
B
B
B
C
B
B
We
have
all
the
let's
see.
Is
there
anything
that
was
an
accomplishment?
We
decided
to
go
forward
with
experimental
drafts
for
flooding
reduction
and
we
accepted
three
pieces
of
work,
the
area
proxy,
the
flood
reflection
for
isis
and
the
isis
ttz
we
also
have.
I
probably
shouldn't
have
listed
the
second
one.
This
is
a
mistake:
shouldn't
be
a
new
working
group
document.
It's
been
a
long
time
and
I
need
to
make
sure
I
saw
that
the
offers
re
refreshed
and
make
sure
there's
still
interest
in
this.
It's
pretty
much
just
a
protocol
maintenance.
B
B
B
You
can
see,
I
must
have
thought
that
the
ospf
sr6
extensions
was
important
because
I
listed
it
twice
and
we
just
accepted
isis
rfc
5316
bis.
This
allows
you
to
support
5316
in
ipb6,
only
networks,
the
gm
gmp
os
extensions
in
in
ipv6
only
networks.
Previously
you
required
it
required
the
routers
to
have
the
encodings
required
the
routers
to
have
an
ipv4
address
next
slide.
B
We,
I
think,
all
of
these
we'd,
like
all
the
the
offers
have
asked
for
working
group
adoption.
I
think,
there's
a
good
reason
to
adopt
all
of
them
the
flooding
parameter
advertisement.
I
expect
that
to
generate
working
group
discussion
again,
but
it's
definitely
been
presented
enough
times
and
it's
time
we.
C
F
H
G
G
G
Okay
right
now,
itf
irsa
working
group
have
several
drops
really
related
to
igp
flooding
processing.
So
there
are
two
directions:
one
is
to
reduce
flooding
amount
by
using
flooding
top
logic
and
another
is
to
reduce
transmission
and
speed
ups
flooding.
So
we
try
to
do
some
testing
planning
tests
and
hope
it
can
provide
some
help
to
optimize
igp
flood.
This
is
the
menu
so
the
first
I
introduce
our
motivation
and
the
test
scenario
and
the
test
case.
G
Finally,
it
is
our
conclusion
next
page,
please
so,
let's
test
adjust
adjust
some
lighting
parameters,
try
to
achieve
minimum
flooding
time
and
the
minimum
retransmission
amount,
okay,
what
they
are,
what
we
adjust
at
least
here.
The
first
parameter
is
window.
It
is
similar
with
the
interface
rsp
receiver
window
in
flooding,
speed
draft.
It
is
the
threshold
of
retransmission
queue
and
the
next
one
is
tx
interval.
It
is
to
control
the
transmission
timer.
The
last
one
is
interface
tx
interval.
It
is
rsp
sending
speed.
G
G
So
the
first
is
case
one
we
change
the
tx
interval.
It
is
a
retransmit
interval
in
this
case.
No
interface
are
sphere,
is
a
window
and
that
the
interface
tx
interval
is
100.
Rsps
per
100
milliseconds
text
interval
is
started
at
5
seconds
3
seconds
and
5
seconds
we
can
find
the
flooding
timer
is
similar.
G
G
So
the
case
tool
we
test
interface
rsv
receive
window.
Now.
This
test
case
is
only
execute
on
the
scenario
y
single
link.
Here
we
have
two
kind
of
read:
default
rate
is
100
rsps
per
100
milliseconds,
the
minimum
rate
is
10
rsps
per
100
milliseconds
interface.
Tx
interval
will
be
set
to
default
rate
in
default
and
the
site
to
minimum
rate.
The
number
of
unacknowledged
rsps
reached
threshold,
the
interface
as
prereceived
window.
G
G
Here
the
interval
is
one
second,
you
can
see
the
number
two
and
the
number
three
the
flooding
timer
improvement
is
obvious
and
number
four.
They
think
the
speed
keep
reaching,
because
the
standing
rsps
have
not
reached
the
series
hot,
so
dynamic,
randomical,
speed
adjustment
based
on
the
static
window,
significantly
reduce
the
rsp
flooding
time
and
the
number
of
re-transmitted
rsps.
G
Based
on
these
three
test
cases,
we
get
some
conclusion
the
first
one
is.
The
sender
should
be
aware
of
the
capability
and
the
processing
status
of
the
receiver
to
control
the
floating
time
under
the
number
of
retransmission,
and
the
second
is
if
only
the
static
window
is
used
to
control
the
retransm
transmit
rate
of
the
sender.
The
number
of
retransmission
can
be
reduced,
but
the
flooding
time
will
be
prolonged
if
the
window
size
reside
is
too
small.
The
flooding
time
would
be
too
long.
G
If
the
window
side
is
too
large,
the
upper
limit
of
the
window
cannot
be
reached
and
the
flooding
speed
on
the
interface
keeps
reaching
until
maximum
adaptive
learning
is
required
to
obtain
an
appropriate
window
site.
Dynamic
adjustment
of
the
flooding
of
the
sanding
speed
based
on
the
appropriate
window,
can
achieve
better
flooding
time
and
better
rsp
transmissions.
G
G
I
C
G
I
G
Okay,
we
need
to
get
get
this
kind
of
control,
so
the
kill
size
and
acknowledge
the
kill
size.
It
is
one
condition
and
how
to
say
that.
Also,
we
also
can
get
some
feedback
from
the
the
the
receiver
side.
All
of
this
is
possible
because
sometimes,
especially
in
ss,
some
scenarios,
no
enough
information
to
control
it.
G
C
K
E
E
G
H
C
N
N
N
N
Okay,
here
are
some
background
about
this
work.
We
introduced
this
term
of
vtn
in
the
draft
itft's
enhanced
vpn.
Basically,
it
is
a
virtual
android
network
with
the
required
topology
and
resource
characteristics,
and
then
we
introduce
the
term
resource
aware
seeds
in
draft
itf
spring
resource,
aware
segments
so
that
src's
can
be
used
to
represent
different
sets
of
resources
allocated
for
the
packet
processing.
N
N
Okay,
this
is
the
mechanism
we
use
in
this
draft.
Basically,
we
reuse
the
flux
algo
id
as
the
control
plane,
identifier
of
a
vgn,
so
that
we
can
use
a
flux,
argon
mechanism
to
describe
the
topology
constraints
of
mvtn,
and
we
can
also
use
the
isis
extension
as
segment
routing
extensions
to
advertise
the
algorithm,
specific
prefixes
or
srv6
locators.
N
Then
we
also
need
some
mechanism
to
advertise.
The
t
attributes
associated
with
hvtn
here
are
the
extensions
we
use.
We
use
the
iss
l2
bundle
with
some
extension
to
advertise.
These
t
attributes
for
each
vtn,
and
we
have
made
some
small
extensions
to
our
the
l2
bundle
to
make
it
applicable
for
both
physical
and
virtual
member
links.
We
introduce
a
new
flag,
we
to
indicate
the
member
link
of
virtual
links,
and
so
that
we
can
associate
the
vtn
with
one
or
more
physical
virtual
member
links
in
a
bundle
interface.
N
N
N
B
N
H
O
N
B
B
M
Okay,
thank
you.
Should
I
stop
right?
Yes,
go
ahead,
okay!
Yes,
this
presentation
about
using
iss,
smart
topology
for
some
ranking
based
vtn
beating
the
hustle
vpn
is
a
enhancement
to
existing
vpn
service
to
support
the
needs
of
new
applications,
so
it
can
be
considered
as
a
revolution
of
traditional
vpn,
but
with
additional
subspecific
commitments
such
as
isolation
and
performance
guarantee,
so
it
may
be
using
using
5g
transport
network
slicing
and
other
genetic
generic
scenarios.
M
M
M
M
M
M
M
It's
also
been
created
specifying
custom
customized
attributes
of
each
product
each
topology,
when
each
vting
has
a
dependent
network
topology,
the
mit
id
could
be
used
as
an
adding
fail
of
beating
the
control
plane
office.
86
67
describes
less
extensions
that
need
to
be
introduced
for
sound
routing
operating
on
mps
data
plane.
M
So
in
order
to
perform
in
order
to
perform
the
constraint
basis,
pass
computation
for
utility
on
the
network,
controller
or
integrated
nucleus
nodes.
The
network
resource
attributes
associated
with
each
btm
needs
to
be
advertised
when
maximum
link
bandwidth
sub
tv
is
carrying
the
mt
as
an
idea
of
topology.
M
M
So
this
document
was
present
in
the
itf
108
me
as
a
working
group
based
on
the
discussion
and
the
suggestion
from
the
working
group.
The
document
type
is
changed
to
informational
and
the
descriptions
about
the
forwarding
plane.
Behavior
is
added
in
new
text
continuous
results,
aware
state
are
used
in
a
data
plane
of
srvtns,
so
the
draft
of
spring
resource
aware
segments
is
added
to
the
reference
section.
M
M
B
B
I
think
this
one's
more
straightforward
than
the
other
one.
I
guess
we
could.
We
could
put
it
in
the
queue
for
adoption.
Myself,
that's
my
opinion,
speaking
as
a
working
group
member,
but
we
can.
I
I
think
we
could
do
it.
The
only
question
would
be
and
would
be
whether
it's
needed-
and
I
think
it's
good
to
have
an
informational
draft
explaining
this.
C
C
C
C
L
L
L
L
C
Okay,
all
right
well
we're
out
of
time
on
this
slot.
Let's
move
to
the
next
one,
so
we
it
sounds
like
we
can
ask
for
adoption
on
the
on
the
list.
It
was
pretty
well
supported
in
the
by
the
call
of
hands
too,
not
necessarily
that'll
get
adopted,
but
you
know
it's
worth
probably
putting
it
out
there
all
right.
Let's,
let's
move
on,
I
think
thank
you.
O
B
Okay,
okay,
you
can
move
forward
I'll
talk
to
this
on
the
next
slide.
Okay,
this
is
a
very
old
draft
that
we
dropped
work
on
the
transport
instance
and
there
were
really
two
motivations
for
reviving
it.
The
first
one
was
there's
the
mechanism,
and
I
applied
the
known
as
the
gen
app
graft
or
the
generic
isis
instance.
Rfc
6823
did
go
forward
and
it
seems
like
a
recurring
theme
now
is
to
advertise
using
the
igps
to
advertise
information.
That's
really
not
related
to
routing,
so
we
revived
it
next
slide.
B
There's
a
number
of
use
cases,
some
of
them
being
present
at
this
ietf
or
past
ietf,
some
that
are
in
the
queue
where
we
want
to
where
people
are
proposing
to
advertise
non-routing
that
information
in
the
in
the
in
ospf,
and
that
would
be
one
use
case.
One
this
is
one
use
case
on
here-
is
the
multi-axis
edge
computing
for
service
discovery
of
servers,
supporting
various
services.
B
Another
one
we've
also
had
some
people
some
discussions
of
running,
putting
more
information
into
lsas,
so
the
information
could
be
exposed
across
areas
now
right
now,
there's
a
number
of
ways:
you
could
do
it,
you
could
run
more
bgpls
sessions,
but
another
way
to
do
it.
You
could
use
the
transport
instance
and
send
this
information
from
other
areas
just
for
bgpls
purposes
in
the
transport
instance
session.
B
B
B
B
Now
one
thing
that's
interesting
about
this:
you
can
support
sparse
topologies.
In
other
words,
you
don't
have
to
have
the
same
ospf
routers
connected
to
one
another.
I
mean
you
don't
have
to
have
the
same
set
of
sessions
for
the
transport
instance
as
your
normal
ospf
instances,
and
you
can
also
support
the
concept
of
a
pre-configured
ospf
neighbor.
That
is
more
than
one
hop
away,
so
you
have
a
remote
neighbor,
which
is
pretty
powerful
because
you
think
about
it.
B
B
B
I
think
this
is
the
last
one.
Here's
just
one
that
we
had
talked
about.
I
talked
about
with
yin
xen
is
for
this
multi-axis
edge
computing
to
identify
the
servers,
and
you
could
put
this
in
no
an
ospf
v2,
opaque
lsa
and
an
ospf
v3.
A
new
lsa
type
you'd
identify
the
servers
by
their
application
address.
That's
the
address
and
you'd
have
have
a
service
id
for
the
type
of
services,
and
then
you'd
have
cpu
usage
and
the
thresholds.
F
I
C
C
K
It
seems
similar
to,
like
I
guess,
like
an
isis
multi
topology,
I
guess
or
let's
say
flat
salary.
Would
it
work?
Let's
say
in
conjunction
with
it
like,
let's
say
the
layering
concept,
where
you
can
do
like
multiple
sparse
instances
and
let's
say
if
you
had
flex
algorithm
as
well,
would
it
could
you
use
it
to
leverage,
I
guess
in
some
way
or
maybe
instead
of
using
a
normal
identification?
I
guess
leverage
flex,
algo
or
I
guess,
use
this
in
conjunction.
I
guess
possibly
request
algorithm.
B
C
H
C
C
R
Hello
christian,
can
you
hear
me,
I
can't
hear
your
voice
christian.
We
can
hear
you
yeah.
Yes,
we
can
hear
you
okay,
yeah.
So
let's
get
started.
Welcome
all
to
the
presentation.
This
is
from
juniper
network
presenting
the
draft
flex
algorithm
in
ip
network.
On
behalf
of
the
authors
next
slide,
please.
R
R
R
Now,
how
do
how
do
we
associate
prefix
with
the
ipflex
algorithm?
This
can
be
done
in
via
the
egress
node
procedure,
so
the
loopback
interface
is
associated
with
one
or
more
ip
addresses
right.
So
each
of
this
look
back
address
is
associated
with
the
flex
algo,
so
we
can
associate
one
loopback
address
with
the
ipflexalgo.
R
R
So
one
more
thing
like
association
of
this
address
to
the
ipflex
algorithm
implementation
independent
operator,
is
free,
free
to
choose
existing
mechanism
or
any
new
mechanism
for
the
ip
address
to
the
flexelgo
association.
Now
coming
to
the
advertising
part
of
the
ip
flex
algorithm
each
participating
node
advertise
an
ipv
algorithm
sub
tlv.
This
is
new
subtle.
We
defined
in
the
draft,
so
the
for
the
isis.
This
sub
tlv
will
be
present
in
the
router
capability
tlb
and
for
the
ospf
it
will
go
as
a
router
information
lsa.
R
R
So
advertising
the
flexible
definition,
all
the
router
participating
in
the
ip
flex
algo
must
agree
on
the
flex,
algo
common
flex,
algo
definition,
the
selected
node
within
the
igp
domain
advertise
the
fed,
which
are
agreed
by
the
old
node
and
for
the
ipflex
algorithm.
We
can
leverage
the
fed
protocol
machinery
defined
in
the
internet
draft
ls
reflex
algo
based
on
the
section
5,
6
and
7.
R
So
we
have
set
the
common
ground
by
advertising
the
fed
and
the
ipflex
algorithm
throughout
the
igp
daemon.
Now
we
have
to
associate
the
prefix
with
the
ipflex
algorithm
and
we
have
to
advertise
reachability
throughout
the
igp
so
to
be
able
to
associate
ip
and
ipv6
prefix
with
flex
algorithm
a
new
top
level
tlb
defined
in
the
isis.
R
This
tlv
are
the
ipv4
algorithm,
prefix,
reachability
tlv
and
ipv6
prefix
ipv6
algorithm
prefix,
reachability
tlp.
We
cannot
use
the
existing
prefix
switchability
tlb
because
by
default
it
is
associated
with
the
algo0
in
the
igp
right.
So
we
have
curve
out
two
new
tlv
for
the
sending
the
reachability
of
ip
flex,
algo
tlv.
R
R
R
R
R
So
when
the
ipfx
allowed
to
compute
to
a
node,
it
must
use
the
corresponding
flex,
algorithm
participant
participation,
algo
and
it
compute
the
constraint
based
part
which
is
independent
of
the
underlying
sr
or
srv6
path.
Algo,
if
present,
and
this
iplex
algorithm
can
use
the
lfa
protection
mechanism
which
is
well
defined
in
the
igp,
also
the
s,
the
sr
segment,
routing,
flex,
algo
and
the
ip
flex
and
go
go
parallelly
in
the
network.
If
there
is
a
need
arise,
they
cannot
interfere
each
other
because
they
advertise
different
flex
will
go
okay
next
slide.
Please.
R
B
B
H
B
H
C
K
R
R
P
C
D
D
E
E
R
E
O
Yeah,
I
I
guess
in
theory
one
could
do
that
and
use
the
locator
tlv
without
the
seats
that
is
not
prohibited
at
the
moment.
So
one
can
do
it.
I
don't
well.
I
don't
think
that
would
be
from
the
encoding
perspective.
That
would
really
be
something
that
I
would
prefer,
but
you
know,
theoretically,
you
can
advertise
the
locator
without
any
sid
and
treat
it
as
ipv6
prefix.
O
O
O
O
C
A
R
So
in
the
draft
zero
on
right,
we
have
merged
the
in
earlier
draft.
We
have,
I
mean
we
have
not
counted
the
empty
id.
We
we
have
four
different
top
level
tlv.
Now
we
have
merged
to
the
two
tlv,
the
top
level
tlv
of
the
ip
v4
and
ipv6
header,
which
contain
the
empty
id
of
12
bits
and
some
reserve
bit.
So
with
that
we
can
use
this.
We
can
reduce
the
number
of
top
tlv
to
2
and
which
also
cover
the
mtid
multi
topology
instance.
E
R
O
N
O
R
Very
quick
thing
is
ketan,
talalik
or
cisco.
I
I
actually
support
the
flash.
You
know
new
tlvs
and
encoding
not
to
mix
with
the
existing
reachability
and
even
the
srv6
locator.
I
think
this
is
also
because
for
srv6
the
participation
is
advertised
by
the
sr
algorithm,
whereas
here
we
have
the,
you
know
ip
algorithm.
C
B
C
A
B
B
J
J
Please,
okay,
so
as
specified
in
rsd820
the
hubble
hub
option.
Headers
is
only
examined
and
processed
process
processed
by
nodes
along
a
package
delivery
path
if
they
are
exp
explexity
configured
to
process.
So
in
less
draft
we
considering
to
signaling
the
nodes
capability
to
process
the
hubble
hub
option,
header
so
based
on
the
rfc
specified.
J
We
notice
that
the
nodes
may
be
configured
into
several
options:
the
first
one,
maybe
it's
configured
to
ignore
the
hubble
hub
options,
header
and
second
one
is
job
it
and
another
option
is
assign
the
packet
to
the
slow
processing
path.
So
here
we
see
that
the
problem
is
different.
Devices
can
be
configured
to
process
the
options
header
in
different
ways,
and
we
found
that
there's
a
a
lot
of
service
to
use
this
hubble
hub
options.
Header
such
as
the
iom
and
another
one
is
the
alternate
marking
measurement.
J
J
J
So
in
let's
dropped.
We
first
first
defined
the
hobo
options:
header
processing
action.
As
we
see
english,
the
first
figure
we
defined
the
hobart,
hope,
processing
action,
information
forms
of
three
field.
The
first
one
is
the
eight
bit
action
flag
field
and
the
second
one
is
the
8-bit
maximum
extension
header
lens
field
and
the
last
field
is
the
16-bit
service
flag.
J
We
indicate
the
the
length
the
maximum
length
of
the
extension
header
can
be
examined
and
processed
and
the
node
or
link
grand
granularity
and
the
last
field
is
service
flat.
It's
to
indicate
the
supported
services
requires
the
hub
hub
options,
header
here
we
we,
we
defined
two
bits,
the
one
the
the
first
one
is
to
the
ion
tris
option
and
another
bit
is
the
the
alternate
marking
method
and
on
other
beats,
we
will
reserved
for
future
use.
J
So,
based
on
the
definition
of
the
first
processing
action
information-
and
here
we
propose
the
extensions
to
the
isis
protocol
and
we
defined
the
node
processing
action.
Subtrees
sorry
extend
it
to
access
router
and
capability
to
and
another
extension
is
the
link
processing
action
action
sub
theory
and
to
indicate
the
actions
of
the
interface
or
social
associated
with
the
link.
J
So
in
yeah,
in
this
document
we
define
because
we
define
the
node
and
link
processing
action
theories
and
we
we
need
to
mention
that
if
we
all
the
interfaces
or
social
was
associated
with
links
supported
the
same
processing
action.
So
we
we
need.
We
need
just
to
advertise
the
node
capability,
tlvs
yeah
and
the
list
page.
We
shoot
the
signaling
processing
action
using
the
ospf.
J
Similarly,
we
extend
the
nodes,
processing
action
theory
and
the
link
processing
action.
Sub
tube
is
extended
to
the
the
the
os
ospf
router
information
pack
osa
and
for
the
ospf
version
two.
We
defined
the
link
processing
action,
sub
tvs
of
the
extended
link
tov
and
for
the
ospf
version
3.
We
extend
it
to
the
e-router
ls
tv.
J
C
J
Network
thanks
for
your
questions
and
and
thanks
for
your
comments
for
the
I
think
I
dropped
in
the
last
meeting
and
for
this
draft
we
we
want
to
mention
the
motivation
is
to
advertise
the
the
whole
by
hope
processing
action,
not
the
iphat
capability.
So
this
is
not
the
same.
The
problem
we
think
and
because
we're
considering
the
the
nose
or
the
interface
supported
the
processing
action
for
the
callback
hub
header,
it's
may
affect
the
the
past
and
computation.
J
C
Yeah,
no,
I
understand
it
isn't,
but
I
I'm
just
thinking
I'm
putting
to
throw
like
an
operator
hat
on
and
I'm
looking
at
this
and
I'm
wondering
like
you
know,
I
buy
a
bunch
of
routers
and
you
know-
and
I
want
to
do
oam
on
them
and
do
I
really
want
my
traffic
being
determined
by
whether
I've
upgraded
my
line
cards
or
do
I
want
to
just
upload
my
line
cards
and
and
then
use
my
oem
software
right?
I
just
I
you
know,
I'm
not
sure.
C
B
S
B
B
C
N
This
is
jadon
and,
to
my
understanding,
this
documentary
aims
to
advertise
some
generic
attribute
of
the
packet
processing
capability
regarding
the
hub
option.
Headers.
I
think
there
are
also
other
use
cases
in
addition
to
the
iom
or
if
it
functionality
such
as
some
traffic,
which
may
need
to
carry
the
hover
hop
option
header
to
for
some
processing,
behaviors
required
on
each
hop
along
the
path.
N
C
B
C
F
C
F
Yeah
we
so
we
want
to
hear
information.
What
what
do
we
want?
What's
the
proper
one
to
show
you
know,
passive
interface
are
used
commonly
in
the
network.
Here
we
just
list
three
three
scenarios.
The
first
is
in
the
data
center,
so
they
are
used
for
the
villa
interface.
Let's
say
in
the
layer
two
broadcast
domain
and
the
second
scenario
for
the
interest
boundary.
F
They
are
used
to
protect
each
domain
from
igp,
flapping
and
called
by
our
command,
and
the
last
scenario
is
described
in
our
in
one
drop
that
provided
by
linda
for
the
edge
computing
scenario.
I
think
it
is
the
same
as
scenario
as
the
ac
has
just
created,
but
currently
there
is
no
suitable
place
to
advertise
the
pencil
interface
and
their
associated
attribute.
So
we
want
to
find
some
place
to
put
this
information
in
in
the
protocol.
Okay.
Next,
please.
F
F
F
The
type
3
can
be
used
to
flag
the
passive
interface,
but
there
is
no
other
place
to
put
the
interface
attribute
and
ospf
v3
has
removed
the
type
3
link
type.
So,
as
we
said,
it
is
necessary
to
extend
the
opioids
mutual
history
and
iss
to
transfer
the
passive
interface
and
their
related
attitudes.
Okay,
next.
F
Please
so
here
is
the
eq.
Actually
two
excessive
propeller,
currently
rc
7684
defined
or
fpv2,
extend
the
link
opec
lsa
to
contain
the
additional
link
recipe
of
the
tlv,
and
only
the
extended
link
theory
is
defined,
so
we
propose
defined,
extend
stabling
theory
to
contain
the
subtleties
related
to
the
peso
interface
attribute.
F
F
F
F
Yeah,
this
is
for
the
isis
extension
proto
proposal
for
isis.
As
we
have
discussed
on
the
main
main
list,
we
can
only
define
one
new
top
theory
to
contain
them
to
contain
such
information,
so
they
define
the
theory
at
this
format,
and
the
related,
releasing
subject
can
also
be
included,
is
necessary.
F
C
Okay,
oh
well,
I'm
in
the
queue
I
wanted
to
back
up
just
one.
Second,
the
previous.
My
previous
comments
on
the
other
presentation,
yali
those
were
made
as
a
working
group
member.
I
I'm
supposed
to
say
that
each
time-
and
I
I
sometimes
forget-
so
it
was
just
my
work.
Remember
as
well
as
these
comments
are
as
a
working
group
member.
You
know,
I
I'm
curious
about
some
of
the
use
cases.
C
It
seemed
like
on
the
mailing
list
that
there
was
like
one
use
case
where
it
was
inter,
inter
as
and
that
you
know
there
was
some
discussion
that
that
was
already
covered
by
tlb
and
then
there's
a
reference
to
like
linda
dunbar's
draft,
which
I
went
and
read,
which
was
about
sort
of
like
using
passive
interfaces
to
describe
load
balance,
load
loading
on
servers
with
anycast
addresses,
and
in
that
case
it's
it's
like
you
know.
Why?
Wouldn't
you
just
advertise
the
anycast
as
a
prefix
and
attach
that
you
know
the
attributes
to
that
prefix?
C
F
F
C
B
B
You
know,
because
what
you're
you
know
that
you
have
this
inner
ass
thing.
Why?
Wouldn't
you
just
advertise
this
as
an
inner
as
boundary
or
something
like
that
or
whatever
your
use
case
is,
and
we
can
discuss
this
on
the
list
too.
I
think
this
is
just
when
we
have
nine
minutes
left
and
you
got
one
more
presentation.
B
F
C
K
K
So
the
motivation
behind
so
really
the
main
problem
statement.
I
guess
where
this
draft
can
be
beneficial
is
in
cases
where
you
want
to
have
a
converge.
The
data
plane
so
like
so
instead
of
again
relying
on
control,
plane,
convergence
to
speed
up
the
data,
plane,
convergence
and
one
of
the
really
the
big
use
case
for
this
would
be
for,
and
if
you
have
a
your
bgp
next
top
attribute
convergence.
K
So
let's
say:
if
you
have
external
peers
and
where
you,
where
you're
marking
your
your
your
bgp
next
hop
doing
the
next
hops
self.
So
in
that
particular
case,
and
you
have
a
link
failure
being
able
to
detect
that
link
failure
quickly
with
a
with
a
advertisement
with
the
negative
advertisement
saying
the
link
is
down
and
allowing
your
if
you're
running,
let's
say
bgp
like
pick
core
in
the
core,
your
hierarchical
fib
can
converge
quickly,
noticing
that
data
plane
failure
and
then
you
can
and
you're
able
to
converge
quickly.
K
Another
use
case
for
this
draft
is
with
with
summarization,
where
you
have
a
area,
a
igp
domain.
That's
subdivided
into
multiple
areas,
and
you
want
to
have
you
want
to
be
able
to
switch
the
data
plane,
convergence
from
from
one
a
b
or
your
primary
abr
to
the
secondary
audio,
so
that
that's
another
use
case
and
then
within
a
within
an
area
either
link
or
node
failure,
so
intra
area
link
or
node
failure
and
being
able
to
with
this
negative
advertisement
this
prefix
unreachable
component.
K
K
So
in
that,
in
that
case,
you're
you're
rewriting
the
next
stop
to
the
loopback,
but
the
loopback
is
always
up
so
you're
you're
in
the
core.
Your
core
doesn't
converge
as
quickly
because
you
you've
done
a
rewrite
to
the
loopback.
It's
it's
something!
That's!
It
can
really
exist
at
day,
one
you
know
with
pig
core
and
and
to
work
around
that.
What
you
end
up
doing.
K
Is
you
end
up
having
to
advertise
all
of
your
external
prefixes
into
the
core
which
creates
a
bigger
fib,
so
this
work
around
what
it
does
is
with
this
with
this
negative
advertisement,
it
converges
that
data
plane
quickly.
So
now
you're
doing
this
prefix
unreachable
advertisement
of
that
link.
That's
down
and
you're
able
to
converge
the
core
quickly
onto
that
onto
the
new
path.
K
Now
so
here
in
this
scenario,
this
is
a
an
inter
area
scenario
where
you
have
two
avr.
So
in
the
center
of
the
diagram,
you
have
router
one
and
router
three
router
router,
three
or
router,
two
router
four
and
they're,
both
abrs
or
or
l1
l2
routers,
and
you
have
a
a
link:
failure
when
that
happens
within
the
area
or
node
failure.
In
this
case
we
have
t1,
you
know,
went
down
on
the
left
on
the
right
side,
and
here
we
have
s2
on
the
left
side.
K
So
in
that
case,
what
ends
up
happening?
Is
you
end
up
having
a
summary
advertisement
that
gets
advertised
by
the
adr
so
like
on
the
right
side?
You
have
route
r2
and
r4
they'll
advertise
a
summary
back
towards
area
one
and
on
and
on
and
on
the
left
side
you
have
s2
went
down,
so
you
have
router
one
and
router
three
they're
advertising
a
summary.
So
in
that
particular
case
when,
where
s2
has
gone
down
and
the
prefix
is
no
longer
reachable,
you
still
have
traffic
that
kind
of
heads
back
towards
s2.
K
The
other
caveat
and
part
of
the
problem
statement
is
cases
where
you
have
component
prefixes
that
are
part
of
a
summary
where
you
have
a
false
positive.
That
happens
where
the
components
are
there,
but
then
let's
say
the
component
disappeared
and
there's
no
and
there's
no
component
prefixes,
but
but
the
but
the
summary
route
is
still
advertised.
So
in
that
case
you
made
black
hole
traffic
in
those
cases.
So
this
what
this
does
is
with
this
negative
advertisement.
K
So
so,
in
this
case
this
is
the
inter
area
scenario.
So,
where
you
have
a
node
on
the
right
side,
t2
has
gone,
has
gone
down
and
you
have
a
so.
You
still
have
a
summary
route
advertisement
that
gets
advertised
by
r2
and
r4
into
the
background
area:
zero
and
then
back
over
to
area
one
and
and
then
so.
On
the
left
side,
you
have
the
summary
gets
advertised
back
over,
but
but
now
because
the
link
the
node
t2
is
down,
you
have
traffic
that
will
flow
because
the
summary
is
still
present.
K
K
Let's
say
r4
is
not
reachable,
but
he
was
reachable
for
a
period
of
time,
but
became
unreachable
and
the
component
prefixes
were
present
and
they're
present
on
r2,
but
they're
not
no
longer
present
on
r4
and
if
we're
still
sending
the
summary
route,
you
end
up
having
a
a
situation
where
you
end
up
hole
in
traffic
so
with
this
so
go
go
on
the
next
slide.
So
that's
that's
a
use
case
with
the
node
failure.
I'm
going
to
next.
K
E
K
Unreachable
advertisement:
what
ends
up
what
ends
up
happening
is
when
you
have
that
node
failure
happen
so
like
on
t2.
The
node
failure
happens.
So
now
a
prefix
unreachable
advertisement
is
sent.
You
know
from
from
from
the
abr,
so
r2
on
r4
they
detect
and
they
send
that
the
pua
advertisement
out
towards,
through
the
backbone
over
to
area
one
area.
K
One
sees
that
and
then
the
route
when,
when
it's
flooded
out
to
area
one,
they
install
a
in
the
fib
in
the
data
plane
and
that's
where
the
data
plane,
convergence
happens
and
and
all
zero
to
black
hole,
the
trust
of
the
traffic.
So
no
traffic
is
sent
to
that
route
and
that's
really
for
the
abr.
So
let's
say
if,
for
some
reason,
let's
say,
there's
a
partition
network
r2
is
down
he's
no
longer
reachable.
K
He
doesn't
have
any
component
prefixes,
but
he's
advertising
the
summary
for
for
whatever
reason,
because
there
was
maybe
a
race
condition
or
something
but
he's
advertising.
The
summary
our
four
is
still
up,
but
we
don't
want
any
traffic
to
go
to
our
two.
You
know
black
hole
in
traffic,
so
in
that
case
the
data
plane
it
converges
on
the
left
side
so
like
also
the
routers
on
on
s1,
s4,
s2
and
s3.
They
end
up.
K
K
K
Okay,
so
this
so
with
this
prefix
unreachable
advertisement,
there
is
a
feature
called
maximum
advertisement
which
in
a
case
where
you
have
prefixes-
and
this
is
something
that
you
know-
could
possibly
happen
where
you're
the
number
of
reachable
prefixes
on
unreachable
prefixes,
there
are
more
unreachable
component
prefixes
than
reachable,
so
in
that
case
it
makes
the
pre.
The
summary
advertisement
work
even
more
conditional
that,
typically,
if
you
have
a
single
component
route,
the
pre,
the
summary
is
always
advertised.
K
So
in
this
case
it
would,
there
would
be
there
would
be
a
another
factor
or
another
variable
that
allows
you
to
con.
You
know
would
be
able
to
configure,
so
you
don't
always
advertise
and
you
could
switch
to
only
advertising
longer
matches.
So
it's
just
another
layer
of
condition.
Conditionality,
I
guess
with
the
with
the
summary
route,
so
that's
pretty
much
it
with
for
the
slide
deck.
If
anyone
has
any
questions,
we
can
go
ahead
and
go
to
questions.
C
Well,
something
occurred
to
me,
as
is
being
working.
Remember
when
I
was
thinking
about
this.
A
lot
of
people
seem
to
have
complaints
about
the
mechanism
for
drawing
the
unreachable
and
using
timers
and
whatnot,
and
how
it
was
you
know,
rift
it
was
compared
to
rift
and
how
rift
had
a
more
deterministic
way
to
deal
with
it.
C
It
made
me
think
what
you
know
if
there
was
a
way
to
attach
the
unreachable
to
the
summary
route,
so
that
then
you
would
just
re-advertise
the
summary
route
with
with
or
without
the
unreachable,
the
holes,
basically
right,
and
that
way
you
know,
if
you
don't
have
that
problem
timing
out.
That
was
just
an
idea.
K
Right
so
with
this,
let's
say
when
they
route
the
so
this
these
the
prefix
unreachable
advertisement.
They
would
only
be
present
when
a
component
is
down.
So
when
that
component
comes
up
the
unreachable,
like
you
know,
it
stops
immediately.
So
it's
it
wouldn't
stay,
but
it
would
help
it
would
help
for
you
know
propagation,
but
when
that
when
the
summary
is
advertised,
it
would
be
the
summary
plus
this
this
component,
so
it
would
be
attached
to
the
summary
route.
K
So,
when
the
the
the
receivers-
I
guess
on
the
other
side,
when
they
let's
say
on
the
left
side,
let's
say
when
they
receive
the
the
summary.
The
summary
they'll
see
the
routes,
the
components
that
are
down
and
it
will
automatically
program
it
in,
but
let's
say
program
into
the
fib
to
stop.
You
know
to
drop
traffic
and
not
send
any
traffic
to
that.
To
that
summary
route
right.
C
B
B
Cases
in
your
slides
and
the
interaction
with
with
the
rib
is
going
to
be
quite
complic,
complicated
that
if
you
should
describe
what
you'd
expect
to
be
installed
in
these
cases
and
how
it's
going
to
work,
because
I
I
look
at
it
and
I
said:
oh,
I
yeah
you
know
I
can
kind
of
wave
my
hands
and
say
how
it
works.
I
think
that
needs
to
be
specified.
K
Yeah,
I
mean,
I
think
I
think,
that
piece
of
it
with
the
convergence-
and
let's
say
I-
you
know
if
you
have
a
false,
positive,
false
negative,
I
think
with
timers,
because
you're
impacting
the
data
plane
it's
supposed
to
make
the
convergence
better
not
worse.
So
we
want
to
make
sure
that
whatever
timers
that
we
make
sure
that
the
that,
when
services
come
back
that-
and
it
would
be
a
flood
that
it
would
be
part
of
the
summary
so
when,
when
the
when
the
service
comes
back
up,
it's
immediately
flooded
and
removed.
K
So
you
you
converge
immediately
as
soon
as
and
it
would
be
part
of
the
same
summary
advertisement
same
sub
tlv.
So
when
when
when,
when
the
service
is
back,
it
comes
back
when
it
goes
down.
Data
plane
converges
immediately
on
that
component.
That
goes
down
so
just
and
it's
for
a
link
or
a
node
failure,
but
really
improving
the
data
plane
convergence.
K
We
actually
have
multiple
areas,
but
if
you
had
a
single
area
and
that
issue
with
the
next
top
self
on
your
tie
to
let's
say
you
know
other
you
know
customer
yes's,
where
you
know
because
you're
doing
that
next
top
rewrite
your
your
your
your
bgp,
like
prefix,
independent
convergence,
your
your
your
core
pick
core,
because
that
that
hierarchical
fib
that
now
it's
dependent
on
the
loopback
doesn't
go
down.
So
that
kind
of
impact
and
that's
something-
that's
always
existed
for
a
long
time.
K
So
this
this
thing
would
make
the
that
next
hop
reachability
that
the
next
hop.
You
know
where
that
when
that
that
pec
links
goes
down
now,
you're
converged
immediately,
and
I
think
that
would
be
like
a
huge
gain
and
it
would
be
really
for
any
service
provider
operator
that
that
you
have
where
you
have
that
tie.
But
now
now
you
actually
converge
that
data
plane
quickly.
When
that,
when
that
next
top
goes
down,
so
I
mean
I
would
say
overall,
that's
probably
the
biggest
one
I
mean.
K
It
would
be
immediately
flooded
as
soon
as
the
service
comes
up
boom,
that
black
hole
route
is
gone,
the
unreachable's
gone
as
soon
as
the
component.
You
know
as
soon
as
the
component
is
down,
you
know
as
soon
as
it's
down
like
the
next
stop
goes
away,
then
immediately
the
data
plane
converges
as
soon
as
that.
Next
out
comes
up,
then
immediately
the
it's
withdrawn.
K
Basically,
the
poa
has
to
be
withdrawn,
so
it
would
really
have
to
be
immediate,
you
know,
and
it
it
would
you
it
can't
be
that
that
it's
lingering
and
or
any
case
of
a
false,
positive
or
false
negative
happening.
I
mean
that's
really
the
critical
one,
because
we
don't
want
to
make
things
worse.
We
want
to
make
it
better
and
improve
conversions.
K
C
K
C
B
N
K
Right,
no,
it
is,
I
mean,
I
think,
there's
some
stuff.
I
think
we
have
to
really
you
know,
clarify
and
just
kind
of
you
know
clean
up
some
of
the
verbiage
in
the
draft,
but
I
agree
the
mix
there
are.
There
is
a
mix
of
use
cases
with
the
areas
at
you
know,
convergence
and
all,
but
I
think
some
of
that
will
we
have
to
work
on
cleaning
that
up.
You
know
in
the.
A
K
Even
though
you're
just
let's
say
you
have
a
thousand
component
prefixes,
but
as
long
as
one
component
is
up,
you
always
advertise
it
and
that's
something
that
you
could
change.
You
could
say
well
make
it
like
50.
If
you
have
50
of
your,
your
components
are
down.
Really,
you
know
you
shouldn't
be
sending
out
the
you
know
summary.
Maybe
at
that
point
you
know,
send
out
your
components
because
they're
there
there's
a
lot
of
downstream
failures,
but
it
would
be
something
that
would
be
user
configurable.
