►
From YouTube: IETF109-SUIT-20201120-0730
Description
SUIT meeting session at IETF109
2020/11/20 0730
https://datatracker.ietf.org/meeting/109/proceedings/
A
C
D
C
C
D
C
No,
I
think
we
just
sorted
that
next,
one
okay,
so
this
is
the
agenda
for
today
we
basically
have
two
documents
that
are
out
of
the
working
group,
and
so
we
have
them
on
the
agenda
just
to
discuss
any
issues
that
are
raised
either
by
the
isg
or
the
ietf.
Last
call,
then
we'll
turn
to
the
suit
manifest.
C
C
D
D
B
Yeah,
no,
it's
nothing's
changed
since
then.
Okay
go
for
it
right,
so
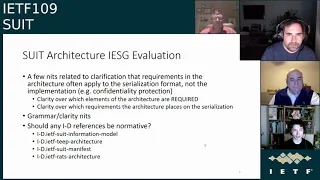
suit
architecture
has
gone
through
iesg
evaluation
and
mostly
we've
got
just
a
relatively
few
number
of
comments.
The
the
ballot
positions
have
all
been.
No
objection,
typically,
no
objection
with
comment.
Mostly.
This
is
a
question
surrounding
questions
around
the
clarity
of
what's
required
in
the
architecture
versus
what
is
a
requirement
of
the
serialization.
B
B
C
D
Be
fine,
so
my
rationale
for
even
the
rats
architecture-
I
so
teep
depends
on
suit
and
rats,
but
I
don't
believe
that
rats,
the
the
suit
depends
on
teep.
It's
the
only
other
direction
and
I
don't
believe
that
suit
depends
on
rats
either
right,
it's
just
indirect,
by
t,
depending
on
both
of
them,
for
example.
So
I
don't
think
there's
anything
that
you
wouldn't
refer
to
for
would
refer
to
rats
in
a
normative
fashion
for
us.
So
I
think
that
they're
all
informative.
C
D
E
E
B
B
We
have
only
received
two
reviews
so
far,
gen
art
said
absolutely
nothing.
Other
than
looks
fine
sector
says
not
ready.
I
think
that
this
is
really
a
contextual
issue.
More
than
anything
else
and
the
reviewer
from
sector
essentially
said
that
he
didn't
look
like
an
information
model
to
him
and
well
fair
enough.
It's
not
it's
an
information
model
and
a
threat
model,
and
I
asked
if
we
changed
the
name
to
that.
B
Sounds
good
to
me:
okay
works
for
me
too.
He
also
drew
out
that
the
order
of
the
sections
is
slightly
confusing.
Now,
of
course,
what's
happened
here
is
that
we
originally
had
threats
and
user
stories
followed
by
requirements
followed
by
elements,
but
then
there
was
the
the
point
that
the
content
that
the
majority
of
people
will
be
looking
for
is
the
element
of
the
manifest,
which
should
then
be
at
the
front.
B
But
we
didn't
then
put
the
requirements
after
the
threats
and
user
stories,
which
means
that
there's
a
kind
of
a
zigzag
in
the
story
of
the
document
as
you
go
through
it
and
that
was
considered
confusing.
So
should
we
reorder
the
sections
to
go
elements,
requirements
and
then
threats
and
user
stories.
F
Hi,
oh
hi
brenton,
so
personally,
I
think
whatever
order
you
choose,
it's
the
wrong
one.
So
that's
first.
I
think
this
is
a
of
course.
So,
but
this
is,
I
think
that
is
correct.
This
is
about
people
want
to
understand
and
implement
this.
So
I
see
the
point
ietf
elements
first,
although
of
course
that
is
a
wrong
order.
F
D
Yeah,
my
personal
preference-
and
I
agree
that
it's
a
matter
of
maybe
it's
preference,
but
I
like
the
order
that
things
are
in
right
now,
which
gives
because
when
we
first
put
the
things
in
that
order,
I
found
that
it
gave
a
natural
flow
right.
That
says:
here's
the
the
things
we're
trying
to
accomplish,
which
then
these
leads
to
these
requirements,
which
then
leads
to
these
solutions.
So
I
thought
that
was
a
fairly
logical
flow.
D
So
hank
said
one
thing
I
was
going
to
say,
which
is:
maybe
the
name
of
the
document
should
be
threat,
model
and
information
model
so
that
it
matches
stuff
and
then
I
might
have
the
table
of
contents
be
organized
such
as
a
section
inside
the
document
that
is
called
threat
model
and
then
a
section
is
called
information
model
after
that.
Okay,
and
so
that
means
that
the
title
would
be
threat
model
information
model.
The
table
of
contents
would
be
structured
like
threat
model
and
then
after
that
would
be
the
information
model
section.
D
And
then
the
elements
are
in
the
information
model,
section
right,
and
so,
if
you
only
care
about
that,
you
jump
to
the
information
model
section,
but
I
think
that
would
be
less
work
than
trying
to
reflow
the
texts
to
make.
You
know
backwards,
reference
stitches
to
terms
and
things
like
that
you
have
to
fix
up,
and
so
I,
like.
B
D
D
B
E
E
F
D
B
B
So
essentially,
what's
going
on
here
is
that
the
information
model
is
saying
that
a
the
support
for
a
particular
information
element
must
exist
in
a
in
any
given
serialization
format,
but
that
it
is
optional
to
use
in
any
given
manifest.
So
you
have
a
strange
completion
of
required
and
optional
in
the
same
element,
and
there
were
a
couple
of
places
that
that
cropped
up
and
the
reviewer
felt
that
it
would
be
helpful
to
clarify
exactly
what
was
required
and
what
was
optional.
D
B
D
If
it
would
have
helped
so
microsoft
has
the
ability
to
create
short
links
like
aka
dot,
ms
slash
whatever
the
well.
Maybe
it's
called
an
fw
link.
So
there's
a
number
of
things
that
when
microsoft
publishes
references
to
its
own
msdn
things,
it
uses
something
that
it
can
redirect
if
msdn
ever
changes
that
structure.
So
if
it
would
help.
E
D
B
D
A
G
G
D
G
B
B
Right
shall
we
so
we
started
yeah
okay,
so
there
are
a
few
technical
changes,
but
they
are
relatively
minor,
there's
only
one
that
might
be
considered
breaking
and
that
is
separating
the
digest
out
from
cozy
sign
and
cozy
mac.
Previously,
that
was
the
payload
of
the
cozy
object
or
cozy
structure.
I
mean
the
rest
of
these
are
additions
and
they
are
hopefully
relatively
straightforward.
B
So,
let's
move
on
next
slide,
please
yeah.
There
we
go
so
first
off
private
enterprise
number.
There
was
some
discussion
in
ietf
108
about
using
private
enterprise
numbers
rather
than
the
uuid
based
vendor
ids.
So
what
I've
done
is
looked
at
what
options
we
have
for
encoding,
a
private
enterprise
number
now,
since
private
enterprise
numbers
are
actually
oids
that
are
relative
to
the
the
ietf
private
enterprise
number
oid,
it
seemed
like
the
best
thing
to
do
was
retain
those
semantics.
B
Now,
what
I've
done
is
I've
gone
one
step
further
than
that,
and
I
have
asked
the
authors
of
that
draft
to
also
include
a
specific
tag
for
a
pen.
So
what
that
is
is
semantics
that
are
almost
identical
to
the
relative
oid,
but
because
they
are
understood
to
be
relative
to
the
private
enterprise
number
oid.
They
actually
resolve
to
a
full
oid,
because
we
already
know
what
that
prefix
is
so
now
we
have
a
way
to
encode,
not
just
the
numeric
pen,
but
the
any
sub-assignments
that
might
show
up
as
well.
B
B
B
D
D
B
So
we
also
discussed
at
ietf
108
the
idea
of
removing
the
suit
digest
from
the
cozy
payload
and
making
it
the
first
element
in
the
the
suit
off
list
now.
The
reason
for
this
is
that
it
could
show
up
multiple
times
if
the
cozy
sign
one
or
cosy
mac.
Zero
objects
are
used
and
there's
more
than
one
signature.
B
B
What
this
does
mean
is
that
it
enforces
that
each
manifest
can
have
only
a
single
canonical
digest
with
a
single
choice
for
what
the
what
type
of
digest
it
is.
So
that
means
that
you
can't
refer
to
a
given
manifest
with
both
a
sha-256
and
a
that
would
be
invalid,
because
the
mana,
the
the
digest
that
shows
up
in
that
manifest,
would
be
one
or
the
other.
Not
both.
B
However,
what
it
does
mean
is
that
if
you
have
two
recipients
that
don't
support
the
same
digest,
parameters,
there's
no
way
to
send
an
identical
manifest
to
both
of
them.
I
think
that's
a
bit
of
a
corner
case.
I
don't
think
I'm
overly
worried
about
that
particular
problem.
So
I
think
this
is
probably
fine.
B
G
G
C
B
B
Now
that
said,
we
have
a
structure,
that's
usually
around
300
bytes,
including
signature.
So
quibbling
over
a
two
byte
tag,
I
think,
is
probably
unnecessary
and
I
would
be
happy
with
a
three
byte
tag,
so
we
could
probably
go
over
the
256
boundary
without
really
much
noticeable
cost
and
knowing
that
many
of
these
tags
are
in
short
supply.
I
I
don't
see
a
problem
with
that.
So
maybe
we
should
change
that
if,
if
anyone
has
a
particular
idea
on
on
what
tag
value,
we
should
look
for.
B
B
B
All
right:
well,
let's,
let's
move
on
in
any
case,
we've
also
added
index
lists.
Now
this
is
just
an
extension
of
the
original
index
equals
true
semantics.
So
the
idea
being
that
when
index,
when
the
the
in
either
the
dependency
index
or
the
component
index
was
set
to
true,
then
it
would
apply
to
all
components
or
dependencies
respectively
or
each
each
individual
command
would
reply
would
apply
like
that.
So
this
adds
a
new
semantic
which
says
that
you
can
provide
a
list
of
indices
to
which
all
subsequent
commands
apply.
B
So
if
you
have
two
components
that
need
to
be
loaded
into
ram,
you
want
to
be
able
to
say
load
my
two
components
into
ram,
not
load
component,
a
load
component
b
and
the
difficulty
with
the
index
equals
true
semantics
is
that
the
destinations
of
those
loads
would
not
themselves
be
loadable
and
the
commands
would
not
apply
to
them.
So
what
this
does
is
gives
you
the
opportunity
to
say
load
component,
one
load
component,
two,
but
don't
load
three
and
four,
because
that's
where
the
loads
are
gonna
wind
up.
B
This
required
a
little
bit
of
thinking
through
what
it
means
for
the
try,
each
and
run
sequence
commands
and,
and
what
that
essentially
means
is
that
we
had
to
properly
document
exactly
what
the
semantics
are.
When
you
use
one
of
these
multi-component
indices
on
one
of
those
command
sequences
and
what
what
it
means
is
that
they
shouldn't
actually
know
that
that's
what's
going
on
the
content
of
the
command
should
not
be
aware
of
this.
B
Instead,
the
command
as
a
whole
should
be
run
once
with
each
possible
index,
regardless
of
whether
that's
the
index
equals
true
semantics
or
the
index
equals
list
semantics,
they
should
only
ever
get
the
numeric
indices,
so
that's
now
been
clearly
defined
in
the
document,
which
should
lead
to
less
implementation
errors.
I
hope
next
slide.
Please.
B
And
we
have
removed
suit
report
and
it's
been
factored
into
its
own
draft,
which
I
think
we're
coming
to
very
shortly,
so
that
was
just
yeah.
Okay,
fine,
all
I
was
gonna
say
was
that
it
didn't
have
a
lot
of
bearing
on
the
content
of
the
suit
manifest
itself
and,
and
so
it
needed
to
be
in
its
own
draft.
B
Dave
thaler
gave
us
a
really
substantial
review,
which
I
don't
know
how
much
time
you
spent
on
it,
but
I
tell
you
going
through
it
and
putting
those
changes
in
sure
took
me
a
while
that,
so
that
that's
that
was
good
review
and
I
think
that
the
document's
substantially
better
for
it.
One
of
my
my
remaining
frustrations
with
this
document
is
that
it
is
enormous
and
it
this
is.
This
is
frustrating
because
it
is
a
relatively
simple
concept.
B
B
B
One
of
the
things
I've
done
to
try
and
aid
clarity
in
the
examples
is
remove
text
printing
of
byte
string,
wrapped
c
bore
so
now
there
isn't
an
enormous
quantity
of
just
hex
printed
noise
in
the
examples
anywhere
that
that
would
have
been
has
been
replaced
with
an
explicit
b
string,
dot
seaborg
as
a
as
a
reference
back
to
the
cddl
that
shows
the
decoded
sebor
inside
it
with
no
hex
printing
around
it
next
slide,
please,
I
think
that
might
be
the
end
of
it.
Is
that
the
end
yeah?
That's
the
end.
D
Okay,
then
I'll
go
ahead,
so
I
just
want
to
report
out
to
the
rest
of
the
working
group
that
there
was
a
first
that
there
was
a
topic
that
came
up
in
teep.
That
brennan
was
there
for,
and
just
wanted
to
summarize,
that
it
had
to
do
with
the
use
of
component
ids
and
there's
another
message
on
the
list
after
the
meeting
that
brandon
and
I
and
hannah
and
folks
are
in
and
the
remember,
teep
uses
suit
and
uses
rats.
D
D
Should
we
have
just
one
of
those
as
mandatory
more
like
the
suit
manifest
does,
and
if
we
think
that
say
the
component
id
path
is
the
mandatory
one
and
coswood
is
optional,
then
it
might
behoove
the
rats
working
group
to
take
that
into
account
when
doing
eating
coding.
So
that
was
the
summary
of
that
issue.
Right.
B
E
B
E
D
F
F
I
am
not
entirely
sure
it
has
if
it
has
to
go
into
the
car
each
draft
it
could,
but
it
would
a
little
bit
split
one
item
out
and
single
it
out,
and
that
was
a
little
bit
confusing
to
the
context.
Maybe
actually
I'm
not
really
worried
about
that.
We
can
reference
it
here,
instead
of
defining
it
here
same
same,
so
it's
on
the
radar.
I
don't
think
that
is
a
issue
actually.
D
D
D
I
thought
that
one
of
the
use
cases
was.
If
I
have
a
set
of
temperature
settings
each
taken
over.
You
know
10
second
period
over
the
last
hour,
then
I
can
express
them
all
in
a
sentimental
format
and
send
them
off
in
one
message.
That
type
of
thing,
I
think,
is
an
example
of
a
use
case
and
again
yeah.
I
agree
with
you.
I
don't
see
the
overlap
with
suits
so.
D
D
B
That's
that's
a
fair
comment.
That's
going
to
require
a
little
bit
of
of
thinking
through
so
just
to
to
explain
where
the
problem
lies
here.
Essentially,
the
the
issue
that
I
see
is
that
there's
a
dramatically
different
behavior,
depending
on
whether
you've
got
an
execute
in
place
or
or
raw
flash
type
device,
or
whether
you've
got
a
file
system
device
and
and
they
act
very
very
differently.
B
The
other
thing
is
that
you
might
not
actually
want
to
allow
a
particular
manifest
to
delete
a
payload
of
a
previous
version
of
itself,
because
that
would
that
would
open
the
door
to
a
number
of
reliability
problems.
So
so
that
seems
to
me,
like
the
the
tpu's
case,
is
actually
orthogonal
to
the
to
the
reliable
unattended
iot
device
use
case
and
that
we,
this
is
going
to
take
some
very
careful
handling
to
make
sure
that
we
don't
get
it
wrong.
D
Yeah,
I
think
that
the
use
case
can
come
up
any
time
that
you
can
have
multiple
independent
things
installed.
So
like
multiple
apps
installed,
for
example
right,
it
can
come
up
not
just
in
a
tp
use
case,
but
any
time
that
you
can
install
multiple
things
supposed
to
say
one
piece
of
firmware
that
you're
always
overriding.
You
have
to
have
a
piece
of
firmware
at
a
boot
right
anytime,.
D
Things
on
top
of
that,
this
problem
can
come
up
an
example
of
a
complexity
and
t.
That's
very
deep
specific
is
antique.
We
used
to
have
this
notion
of
security
domains
right,
and
we
said
well
that
was
pushed
down
to
the
suit
manifest
if
you
need
to
create
a
security
domain
at
the
time
that
you
add
a
an
app
that
would
depend
on
it.
Well,
what
about?
If
you
delete
that
app,
you
delete
the
security
domain
or
not,
and
you
might
imagine
that
you
want
that
to
be
configurable
somehow
and
so
exactly.
D
B
Yup,
I
see
the
I
see
the
challenge
there.
I
I
understand
the
use
case
I'll
I'll
have
to
I.
I
suspect
that
the
answer
is
that
much
like
we've
got
a
way
to
fetch
something
and
to
copy
something
we
need
an
explicit
delete.
I
suspect
that
that's
the
answer
and
there's
a
couple
of
reasons
that
that's
important,
but
the
thing
that
we
definitely
need
to
clarify
is
what
is
the
behavior
if
you
have
multiple
copies
of
something.
B
The
thing-
and
maybe
that's
true
in
the
teep
use
case,
but
that's
not
true
for
all
suit
devices.
It's
fine
for
me
to
say
the
tls
library
and
then
have
that
selected
based
on
which
one's
most
recent
and
valid
and
its
manifest
works.
And
then,
if
something
fails-
and
I
need
to
do
a
rollback-
I
pick
the
previous
tls
library
and
and
for
that
to
work
they
have
to
have
the
same
component
id.
So
that
becomes
a
challenge
when
I
now
say
delete
the
tls
library,
which
one
do
I
delete.
D
Well,
the
same
thing
comes
up.
I
should
say
that
in
teep,
when
the
tip
has
to
be
able
to
express
the
list
of
things
that
are
installed
and
right
now
in
the
discussion,
the
teep
we
said
we
want
to
do
that
by
component
id
now.
I
think
that
does
force
teeth
to
always
have
unique
ones
and
never
have
the
collisions
based
on
that.
D
Up,
I
did
post
it
to
the
list
yesterday,
but
most
people
haven't
seen
it,
but
I
my
belief
is,
unless
somebody
tells
me
otherwise
in
this
meeting.
My
belief
is,
we
don't
have
to
have
the
answer
right
now.
We
just
have
to
agree
that
the
answer
should
be
in
the
suit
manifest
document
before
we
ship
it
to
isg.
B
A
C
B
B
So
what
you
need
to
know
to
be
able
to
work
out
exactly
what
your
manifest
processor
did
is
the
digest
of
the
root
manifest.
So
you've
got
something
to
refer
to
the
canonical
uri,
so
you
can
fetch
the
full
set
of
the
manifest,
regardless,
if
anything
of
whether
or
not
something's
been
stripped
on
the
end
node
the
and
then
for
each
condition.
Failure
you
need
to
know
which
manifest
it
was
processing
the
section
that
it
was
in
how
far
into
that
section
it
was
the
current
manifest.
B
B
There
are
a
couple
open
issues
with
this
now,
specifically
there's
the
the
question
as
to
what
happens
when
you've
got
strict
order
set
to
false
and
a
condition
fails.
That's
not
exactly
clear
at
the
moment
so
need
to
work
through
that
one
and
then
there's
a
question
of
whether
we
should
add
an
anti-replay
mechanism
to
it.
So
that's
really
it
and
I
believe
the
answer
to
the
anti-replay
mechanism
is
yes.
It
should
contain
some
kind
of
unique
number,
however,
that
works
whatever.
B
D
Yeah,
so
I
believe
as
chairs
this
is
a
question
to
dave
and
russ.
Should
we
ask
for
a
call
for
adoption
at
this
point
as
a
data
point
for
the
working
group,
the
teep
working
group
in
the
past
version
of
the
suit
manifest
document
that
has
reports
in
it?
The
teat
protocol
took
a
dependency
on
the
suit
reports
and
referred
to
that,
and
since
it
was
split
out,
the
t
protocol
now
refers
to
this
document,
which
is
not
a
working
group
document.
D
D
C
E
C
B
So,
just
as
background
we've
already
talked
about
the
mud,
one
in
ietf
108,
so
there's
not
anything
new
to
report
on
it,
though
this
is
just
a
very
quick
overview,
and
hopefully
that
is
helpful.
So
the
idea
here
is
that
we
want
to
deliver
some
mud
info
and
suit,
and
to
do
that
we
need
some
new
data
in
suit
manifests
and
some
new
data
in
eat.
B
B
C
D
C
A
A
D
D
D
A
D
Yeah,
I
see
it
yeah,
I
think,
there's
multiple
possible
books.
This
one
looks
fine
to
me
if
this
is
one
that
people
are
familiar
with.
It's
a
wylie
and
a
dr
dobbs
jolt
award
finalist
sure
this
one
looks
like
a
fine
reference
to
me.
So
then
I
will
not
do
my
action
unless
somebody
tells
me
otherwise,
if
that's
going
to
be
our
default
answer,
so
I
mean
separately,
I
will
still
go
and
get
a
stable
link
for
it,
but
I
don't
think
we
need
to
use
it
in
the
suit
manifest
document.
B
B
D
E
B
D
D
D
B
D
Okay,
so
it
only
matters
well,
not
only,
but
it
matters
to
the
teep
working
group,
because
they'll
have
a
normative
dependency
on
the
suit
report,
which
means
t
protocol
can't
go
to
rfc
any
sooner
than
the
suit
report
does
yeah,
and
if
it's
blocked
behind
a
recharger
effort,
then
that
adds
delays
in
the
suit
into
the
tea
protocol,
which
may
or
may
not
be
an
issue.
So
well.
This.
