►
From YouTube: IETF109-IPSECME-20201117-0900
Description
IPSECME meeting session at IETF109
2020/11/17 0900
https://datatracker.ietf.org/meeting/109/proceedings/
C
Yeah
then
I
find
the
proper
window
to
go
forward.
The
meat
echo
window
doesn't
work
for
moving
next
slide.
So
this
is
the
note
well-
and
everybody
has
probably
seen
this
couple
of
times
already
and
we'll
see
it
a
couple
of
more
times
so
the
first
things
we
don't
need
blue
sheets
because
they
are
taken
automatically,
but
we
brought
with
some
note
takers
and
chopper
scribe.
C
A
C
C
D
E
C
That's
all:
okay,
good,
okay,
so
this
is
our
agenda,
so
we
are
right
on
schedule.
So
we
have
five
minutes
for
the
document
status.
Then
we
have
a
couple
of
work
items.
Actually
the
young
model
for
ip
traffic
flows,
securities
problem
it's
in
the
middle
of
the
work
either
or
the
new
item.
I
don't
know,
and
then
we
have
a
couple
of
new
items,
any
comments
on
the
agenda.
C
If
not,
we
go
forward
so
our
status
report.
So
we
have
one
document
that
is
in
itf
last
call
now
ipv6
ipv4
codes
and
I
think
it's
it
will
be
finishing
in
couple
of
weeks
or
something
like
that.
It's
starts
started,
then
we
have
a
couple
of
documents
that
are
still
in
ongoing.
The
gi
version,
2
is
got
got
to,
I
think,
quite
a
big
right,
but
he
still
hasn't
been
getting
that
much
review.
C
C
F
H
A
G
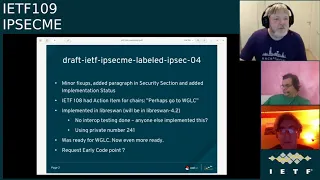
Okay,
so
an
update
on
labeled
ipsec,
there
are
just
a
few
minor
fix.
Ups
in
the
text,
there's
a
little
bit
of
added
text
in
the
security
section
and
we
added
an
implementation
section,
but
currently
only
librisfon
on
linux
has
implemented
this,
so
we
have
implemented
in
librisfon.
It
is
working
with
sc
linux
as
the
the
underlying
security
system
that
transfers
that
uses
the
labels
that
are
transmitted
and
so
for
for
rel
for
red
hat.
G
We
now
have
a
a
path
forward
from
ike
v1
to
ikv2,
which
is
why
why
we
wanted
to
have
this,
so
there's
no
interrupt
testing
done.
If
anyone
else
has
implemented
this.
I
would
like
to
to
interrupt
test
it
that
we
are
using
private
number
241
and
I
think
it's
ready
for
broken
group
last
call.
We
only
had
minor
changes
at
this
point,
maybe
to
an
early
code
point
but
yeah.
That's
it.
C
C
C
Yeah,
okay
yeah,
so
those
are
expert
review
stuff.
So
yeah.
If
you
tickle
the
stable
and
we
can
start
the
last
call,
then
I
think
we
are
going
to
actually
keep
that
because,
as
I
said,
therefore,
there
is
no
official
early
code
point.
We
start
you
starting
to
email
and
or
request
a
code
point
to
be
allocated
and
then
because
it
goes
to
the
expert
review
and
and
so
on
it
actually
goes
directly
to,
and
so
so
you
can
just
start
that
yourself.
H
C
B
B
So
we
published
two
drafts
one
during
the
meeting
after
the
cut
off
the
gate
opened.
The
changes
were
largely
based
on
list
discussions.
One
of
the
additions
was
a
clarification
that
the
fragments
need
to
follow
in
subsequent
sequence
numbers
we
added
a
zero
comp
on
receive
sort
of
feature,
but
this
generate
a
lot
of
discussion.
B
B
So
the
ip
protocol
number
originally
at
108
benjamin
and
said,
do
the
request.
Tarot
said
this
is
too
much
trouble
to
justify
this,
so
we
do
need
to
to
have.
We
don't
always
have
state-based
negotiation
like
ike,
so
we're
going
to
keep
the
payload
type,
but
we're
just
going
to
have
it
be
an
esp
payload
type
and
pick
the
number
five.
This
does
happen
to
correspond
with
ipv5,
which
is
not
actually
deployed
and
used.
So
the
number
wouldn't
actually
conflict
with
anything.
B
B
Zero
comp
received
support,
so
this
this
was
just.
This
is
really
just
about
it's
very
simple
to
implement.
You
can
receive
ipt
fest
frames
and
it's
useful
in
non-like
scenarios.
It's
just
goes
to
one
of
these
things
where
the
more
configuration
you
have
to
get
right,
the
more
chances
of
getting
it
wrong.
B
B
The
primary
changes
are
before
we
had
this
last
sequence
number
and
because
we
were
sending
at
a
fixed
rate,
we
thought
okay,
if,
if
the
sender
you
know
if
the
receiver
sends
back
the
last
sequence
number
that
it
received,
you
could
sort
of
in
inter
interpolate
interpolate
the
time
that
you
sent
it
based
on
the
sequence
number.
This
is
just
this
ended
up
just
being
overly
clever
it
also.
B
The
sender
sends
a
timestamp
which
is
opaque
to
the
receiver.
So
there's
no
synchronization
issues,
it's
just
a
number,
but
you
know
it'll
be
its
clock
when
it
sends
it
and
the
receiver
then
marks
the
time
locally
when
it
receives
it
and
when
it
echoes
that
and
then
it
puts
that
value
in
in
the
echo
field
and
returns
it
along
with
that.
It
sends
the
echo
delay.
So
you
know
it
didn't
time
stamp
when
it
received
and
when
it
sends
it
back.
B
Additionally,
to
that,
we
added
the
transmit,
delay
and
needed
this,
because
you
can
get
in
situations
where
you're
you
know.
If
you're
you
know,
if
you're
going
from
dc
to
san
francisco
or
new
york
to
london
right
you've
got
a
long
round
trip,
but
if
you're
going
across
a
data
center,
your
round
trip
time
can
be
really
tiny.
B
But
the
actual
logical
round
trip
time
is
based
on
your
send
rates
right
because
you
have
a
transmission
delay
you're
only
sending
packets
every
so
often
to
match
a
certain
bandwidth,
so
the
transmit
delay
is
the
the
sender
of
this
value.
This
is
saying
what
that
value.
You
know
what
that
transmission
delay
is,
and
it
knows
what
that
is,
because
that's
exactly
how
often
it
sends
a
packet,
so
it
just
puts
that
value
in
there.
B
This
can
change
in
congestion
control
because
you
might
be
slowing
down,
so
you
need
to
keep
reporting
it.
So
basically
you
take
you.
Take
these
two
round
trip
times
the
one,
the
actual
one
on
the
wire
and
the
transmit
delay,
which
is
your
train,
your
transmit
delay,
plus
their
transmit
delay,
and
you
pick
the
bigger
one
and
that's
your
actual
round-trip
time
estimate.
B
So
the
open
issues
from
the
last
meeting
was
were
that
job
had
suggested
that
we
should
do
a
transport
review.
I
think
that's
a
good
idea.
I
think
that
the
idea
here
is
that
you
know
everybody
in
this
room
is
an
expert
on
ipsec
and
they
can
understand
the
basic
protocol
here
and
it
all
looks
good,
but
you
know
people
you
know
are
thinking
well,
we
don't
really
know
too
much
about
congestion
control,
so
we
need
to
get
a
transport
review,
so
our
latest
version
is
based
on
implementation
experience.
B
B
A
B
A
C
Most
of
most
of
the
people
when
they
start
to
do
the
review,
they
do
the
latest
version
anyway
for
the
for
the
draft
right,
they
don't
do
that.
We
didn't
request
for
specific
version.
We
asked
for
the
latest
version
so
when
they
start
doing
the
review,
they
usually
take
the
latest
one
but
email
to
the
reviewer,
saying
that
there's
new
version
might
be
a
good
thing
if
they
have
already
started,
but
I
don't
think
people
do
it
very
quickly
when
they
start.
C
B
B
So
we
think
that
moving
forward,
we
think
that
all
the
issues
on
the
you
know
the
base
document
outside
of
the
congestion
control
have
been
addressed.
In
this
current
version,
it
was
really
the
ip
protocol
number
allocation
and
and
that
zero
comp
thing
now
that
I
know
that
the
transport
review
is
happening,
that
that
action
is
going.
So
we
were
going
to
say
is
this?
Can
we
do
this
part
of
the
working
group
last
call,
which
is
pretty
pretty
normal
yeah?
So
that's
the
question.
C
So
for
doing
this,
so
so
for
working
group
last
call,
I
have
to
read
it
myself
before
I
can
actually
see
if
it
actually,
I
would
usually
read
them
before
I
I
could
actually
see
if
it's
ready,
I
mean
when
I
was
actually
reading
it
quickly.
I
realized
that
then
I
wrote
this
this
congress
congestion
control
stuff,
and
then
I
realized
that
I
have
to
ask
for
the
transport
area
for
the
protocol
ip
protocol
number.
As
I
said,
I
don't
think
we.
C
The
reason
I
was
objecting
is.
I
was
saying
that
I
don't
think
we
need
an
early
version
because
we
can
do
our
internal
testing
with
you
know,
just
by
version
two
and
saying.
Okay,
if
you
have
this,
you
know
thing
there.
Then
you
can
do
it,
but
the
I
think
we
can
still
allocate
the
ip
protocol
operating.
That
might
be
better
better
if
you
actually
need
to
have
an
ip
protocol.
Of
course,
I
was
what
I
was
saying.
C
We
could
just
use
zero
or
something
like
that
said
that
ignore
the
ip
protocol
number,
because
we
know
what
is
in
there
I
mean
for
esp
it's
a
transport
mode
or
tunnel
mode,
and
the
protocol
number
is
for
tunnel
mode,
it's
actually
completely
useless.
It
actually
is
never
ever
anything
else
than
the
one
of
this
you
know,
but
for
a
transfer
mortgage
needed.
So
I
was
thinking
about
a
little
bit
similar
kind
of
thing.
B
So
I
I
think
that
that
I
think
that
we
could
do
the
you
know.
Why
don't
we
stick
with
the
value
five?
You
know
as
a
esp
transport
payload
type,
and
you
know
it's
not
really
squatting,
but
no
one's
gonna
use
that
because
it's
allocated
but
unused.
That
was
our
thinking.
Actually
I
think
lou
is
in
the
room
and
he's
co-author
on
ipv5
work.
So
he
was
like
we'll
just
use
that
so.
B
If
that's
okay,
I
mean
we,
we
can
try
to
do
the
ib
protocol
number,
but
I
I
I
don't
want
to
hold
the
work
up
on
on
that
because
it
doesn't
seem
critical
and,
like
you
were
saying,
if
people
do
want
to
use
it
outside,
we
could
always
do
that
work
either
way.
I
think
we
just
we're
just
interested
in
moving
it
forward.
C
Yeah,
but
I
think
the
ip
allocates,
I
don't
remember
what
the
allocation
policy
theory
is
for
for
normal
is
it?
Is
it
actually
standardization
required
or
what?
But
I
don't
think
it's
expected.
I
think
it's
higher
bar,
so
so
to
get
it
before
they
actually
go
into
the
publication
requested
and
addressed
the
allocation
is
going
to
be
required
earlier
location.
But
of
course
the
question
is:
if
it's,
if
it's
almost
ready,
then
it's
not
that
far
away
but
yeah
and,
of
course,
with
the
early
allocation
stuff.
I
I
Thing
yeah
yeah,
it's
a
fairly
heavy
bar,
but
we
can
still
request
an
early
allocation
and
with
the
early
allocation.
If
it
is
granted,
then
you
know
after
a
year
we
can
renew
it.
Just
with
the
working
group
chairs,
saying
yeah
we're
still
working
on
this
and
after
you
know
the
second
year,
then
the
isg
has
to
approve
it,
but
we
tend
to
be
happy
to
renew
them.
If
the
draft
is
still
something
that
we
think
is
going
to
happen.
I
C
Yeah,
so
I
I
I
think
there
are
most
of
the
things
I
did
because
I
think,
as
long
as
you're
only
using
it
in
that,
I
still
don't
think
we
actually
need
that,
because
we
can
always
negotiate
like
version
two.
If
we
actually
have
some
other
uses
for
it
outside
like
an
ipsec,
then
I
think
we
need
that
one
definitely
and
then,
but
then
I
actually
would
not
want
to
get.
You
know
more
feedback
from
people
who
are
actually
using
it
somewhere
else
than
in
ipsec,
because
of
course,
there's
nobody
here.
B
Yeah,
that's
so
this
is
our
motivation
for
just
saying:
forget
it
right,
we
just
we.
We
have
people
that
want
to
see
this.
You
know
get
standardized.
So
it's
you
know
it's
just
easier
to
go
the
with
the
flow
here,
and
so
that's
why?
Let's
just
do
the
esp
protocol
payload
type
right
and,
like
you
said,
tarot
it
doesn't,
it
doesn't
actually
have
to
be
an
ip
protocol
number
even
right.
We
because
we
own
the
esp
payload
type
space.
B
So
you
know
we'll
just
pick
five
and
that
way
we're
picking
we're
picking
a
number
no
one's
ever
going
to
allocate
because
it's
already
allocated.
So
if
down
the
road
somebody
wants
to
do
this,
they
can
write
their
draft
that
uses
it
and
then
they
can
do
the
ip
allocation
number.
You
know
they
can
do
the
allocation
request
as
a
part
of
what
they're
doing,
and
I
think
that
matches
what
you're
saying
yeah.
I
C
C
Five,
then
we
say:
okay,
let's
allocate
a
new
one,
how
about
five,
because
we
can
actually
try
that
so
what
we
can
actually
do
at
that
point,
if
we
say
that
the
five
is
actually
never
going
to
be
used,
we
can
actually
then
later
make
an
you
know,
proposal
to
ist
and
say
that,
okay,
how
about
we
actually
repurpose?
This
number
five
to
is
used.
C
C
B
B
So
the
changes
since
108
just
some
reminders,
the
you
know.
The
objective
here
is
just
to
get
a
yang
model
to
support
iptfs
the
approaches
that
we're
going
to
augment
the
only
ip
second
model
that
we
can
find,
which
looks
you
know
done,
which
is
this
sdn
ipsec
flow
protection.
It
actually
works
pretty
well,
there
was.
There
was
an
open
issue
with
it.
It
didn't
actually
work
originally
because
they'd
split
the
essay
database
and
the
policy
database
and
they
put
it
into
iklis.
B
B
So
that
means
somebody,
you
know,
can
use
the
iklas
and
ike
model
together,
even
in
the
ike
case
right
there,
and
they
can
put
that
you
know
they
can
use
the
assay
database
from
the
I-class
model,
so
that
got
us
to
where
we
needed
to
be,
and
so
we
we
updated
the
latest
version
to
refer
to
the
the
to
the
latest
versions
of
of
those.
The
sdn
ipsec
flow
protection
that
one
that
the
version
the
base
document
there
seems
like
it's
moving
forward.
B
B
I
think
I
might
have
yeah,
so
this
is
what
I
just
talked
to
so
it's
they
intentionally
left
the
essay
database
out
and
they're
missing
some
information,
yes
say,
oh,
so
I
should
mention.
Also,
we
put
some
basic
ipsec
counters
into
the
into
the
ike
model
and
the
sa
and
it's
just
rx
packets
and
bytes,
received
our
octets
received
and
transmit,
received
and
drops
next
slide.
B
These
are
the
statistics
that
I
mentioned.
The
the
top
ones
of
the
ipsec
counter
is
very
basic.
Both
of
these
are
also
implemented
as
features,
so
somebody
input
you
know
wanting
to
do
a
minimal
implementation
doesn't
actually
have
to
input
either
of
these.
They
just
have
to
do
the
configuration
next
slide,
please
so
we
we'd
like
to,
and
we
this
is
pretty
straightforward
stuff.
So
we'd
like
to
ask
for
working
group
adoption
on
this,
but
that's
our
last
site.
I.
C
Think,
okay,
I
have,
I
don't
remember
if
this
is
actually
this
probably
isn't
our
charter,
because
I
think
young
models
for
this,
and
so
I
don't
think
we
actually
need
to
do
anything
for
that,
and
but
this
is
quite
new
stuff.
I
don't
think
there
has
been
that
many
people
who
actually
read
this
so
that
I
would
like
to
you
know
we're
gonna
have,
of
course
we
can
actually
start
a
working
group
out
of
sinkhole
and
then
people
will
probably
hopefully
read
it
and
comment
on
it.
B
C
One
of
the
question
I
had
actually
is
because
this
actually,
I
have
no
idea
about
the
angle,
but
you
were
having
this
things
here,
saying
that
I
assume
these
ones.
These
configuration
parameters
are
something
that
can
be
changed
on
the
fly,
so
so
somebody
gonna
go
and
say
that
okay,
I
want
to
change
the
bitrate
to
be
something
different,
which
is.
This
has
actually
always
been
problem
with
you
know.
If
people
have
been
trying
to
use
the
traffic
flow
confidence,
they
have
been
okay.
B
C
Yeah,
so
so
the
question
is
that
actually
one
of
the
things
I
actually
had
realized
that
actually
having
you
know,
algorithms,
that
kind
of
things
in
young
also
that
would
also
probably
allow
them
to
be
changed.
Is
there
actually
any
way
to
in
young
say
that
you
can't
modify
this
after
it
has
been
insta
installed.
B
C
Yeah,
because
one
of
the
things
I
realized
that
there's,
I
didn't
see,
that
kind
of
things
into
sdn
stuff
and
I
was
thinking,
but
I
should
probably
actually
comment
and
mark
ask
them.
Actually
somebody
should
go
through
the
model
through
and
check
out
which
of
those
are
something
that
needs
to
be
changed,
but
anyways
that's
actually
a
little
bit
different.
So
anybody
has
any
comments
on
this
document.
C
C
C
A
B
I
C
F
E
F
G
F
F
That
it
will
extract
from
this
and
it
works
well
if,
if,
if
a
message
contains
only
can
contain
only
one
preload
well
in
ixtake
machine,
the
message
contain
only
one
one
payload
of
this
time
in
the
message.
So
it's
true
for
key
exchanging
hours.
It's
a
single
payload,
there's,
no
ambiguity
of
extracting
data
from
them,
and
it's
not
true
for
safety
loads,
because
there
are
multiple,
there
can
be
multiple
set
loads
and
each
with
certificates.
F
If,
if
he
put
a
single
certificate
into
multiple
state
but
set
the
load,
it
would
be
possible
to
to
properly
distinguish
between
several
certificates,
but
it
can
be
workaround,
it's
a
problem,
but
it's
not
not
not
showstopper,
and
so
there
is
a
pro.
Another
problem.
Is
that
all
these
loads,
if
they
appear
in
encrypted
reload,
is
an
encrypted
load
size
won't
fit
into
64
kilobytes.
It's
it's
clear
that
it
will
be
greater.
F
So
it's
it
can
be
also
work
around,
because
the
size
of
encryptable
load
can
be
always
deducted
from
the
size
of
like
message,
because
it's
always
the
last
ballot
and
the
message.
So
it's
the
length
if
you
encrypted
for
load,
it's
useless
is
useless.
It
can
be
set
to
say
zero
or
something
like
that.
It
doesn't
mean
it's
it's
not
needed,
so
it's
not
a
big
deal.
So
next,
please.
E
F
In
the
initiator
request
message
in
the
responder's
response,
the
number
of
these
loads
can
be
different,
so
the
size
is
the
the
size
of
the
key
exchange
in
request
and
response
can
be
different.
That's
very
well
suited
for
encapsulation
exchange
methods
that
is
common
for
what
quantum
cryptography
and
also
in
like
also,
you
can
see
that
we
can
put
several
hours
below
it
and
see
if
signature
doesn't
fit
into
one.
So
next,
please.
F
F
F
Issue
that
not
the
issue,
but
I
think
we
will
will
introduce
a
new
mod
when
ike
will
switch
from
udp
to
tcp
and
esp
will
remain
in
plane
or
edp
encapsulation,
if
it,
if
it
possible,
so
it
will,
it
will
avoid
a
necessity
to
encapsulate
the
ipc
in
gcp
because
for
performance
reasons
it's
not
very
good
idea,
so
either
we
do
all
in
tcp
or
we
do.
I
can
tcp
and
ip
second
udp
on
play,
so
I
think
it
will
address
the
reliability
and
transfer
in
the
religion
that
I
like.
F
C
A
Yeah
hi,
so
I
think
it's
worth
as
an
individual.
I
think
it's
worth
doing.
I
think
we
had
previously
needs
for
larger
payloads
like
where,
with
config
payload,
when
we
wanted
to
send
a
large
amount
of
routes.
Well,
they're,
not
routes,
they're
traffic
selectors
in
the
config
payload,
but
yeah
the
same
thing
and
we
were
limited
by
the
64k
which
was
okay
but
nothing.
F
A
F
Large
balloons,
the
other
case,
is
to
make
like
messages
as
small
as
possible.
Well,
not
not
for
this
particular
large
key
exchange
method,
but
using
ike
for
iot
on
on
on
the
like,
and
we
are
trying
to
make
as
small
as
possible
and
for
this
reason
to
enlarge
a
generic
reload
for
mods
so
that
it
will
take
not
not
not
for
children
not
to
take
provide
but,
for
example,
eight
bytes.
It's
not
very
good
idea.
It
must
at
least
support
both
formats
as
compact
and
large,
and
something
like
that.
C
F
C
I
would
really
like
to
see
a
couple
of
comments
on
people,
and
actually
I
was
really
thinking
about.
We
should
probably
have
a
little
bit
more
discussion
about
what
would
be
the
best
way
of
you
know
having
pros
and
cons
on
different
things
on
on
on,
for
the
actual
you
know,
implementation,
you
know
either
having
you
know,
I
think
three
octaves
is
too
low.
C
That
means
that
we
have
more
than
255
fragments
or
these
kind
of
payloads
that
need
to
combine
together,
which
actually
start
to
get
really
a
little
bit
annoying
already
and
and
that's
actually
it's
one
of
those.
You
know
question
is,
if
you
actually
have
that
big
payload,
then
I
think
you
know,
chasing
the
payload
format
to
be
would
be
either
better,
because
I
mean,
if
you
have
have
to
combine
you
know
hundreds
of
these,
then
it
gets
a
little
bit
annoying.
C
Yeah,
but
we
are
using
yeah
yeah,
of
course,
but
even
in
tcp
you
know
the
yeah.
The
payload
format
is
still.
I
mean
if
you
use
this
method
that
we
have.
You
know
multiple
of
same
payloads
with
maximum
length
of
64
case,
and
we
want
to
send
one
megabyte.
We
still
have
what
we
have.
Let
me
see:
32
sorry,
16
16,
you
know
payloads.
We
have
to
come
by
to
send
one
megabyte.
C
C
All
right,
yeah
yeah,
but
if
you
actually
would
take
this
document,
this
different
approaches
to
the
list
and
we
could
have
started
discussing
on
the
list
about
what
would
be
the
best
of
the
different
approaches
and
what
would
be
the
good
things
and
bad
things
about
those,
because
people
have
different
views
and
different
and,
as
I
said,
they
were
actually
yeah.
One
of
the
things
that
people
also
wanted
to
see
was
actually
transport
and
configuration
payload.
C
They
wanted
to
transport
like
whole
configuration
files
where
you
have
a
text
file
which
has
you
know
the
whole
configuration,
and
that
can
be
actually
quite
big
and
that's
what's
one
of
the
things
that
they
were
saying.
Oh,
we
won't
use
gfk
set
to
set
the
configuration
to
all
of
our
remote
devices
and
then
we'll.
A
F
F
F
F
E
E
F
Has
its
dedicated
attribute
type,
so
it's
it's
like
negotiation
client
includes
all
the
attribute
encrypted
and
it
encrypted
dns
type
it
supports,
and
the
server
returns
back,
one
or
probably
a
few
of
them,
which
it's
also
supported.
It
is
configured
then
as
but
each
attribute
type
each
attribute
can
contain
several
addresses.
F
F
You,
for
example,
would
choose
one
of
the
supported
encrypted
dns
types
and
we
have
the
same
results
in
create.
So
it's
it's
like
like
negotiation.
That's
why
we
decided
to
separate
attribute
title
for
each
indiana
style,
and
next,
please
so
portable
is
included
for
as
a
comment
from
dog
authors
and
it's.
F
F
A
F
F
J
Hello,
can
you
hear
me
yep
great?
Yes,
thank
you
for
presenting
this
moving.
Definitely,
the
document
seems
in
better
shape
than
it
had
before.
I
like
some
of
the
changes
regarding
the
relationship
with
adb,
specifically,
I
actually
would
like
to
urge
us
to
not
necessarily
adopt
or
move
this
work
forward
and
what
more
has
been
done
in
addi,
specifically,
some
of
the
mechanisms
we're
looking
at
there.
J
Details
like
the
alternative
protocols
or
the
ports
could
be
handled
in
a
more
generic
mechanism,
and
that
may
not
be
the
case,
but
it
may
be
the
case,
and
I
don't
think
we
should
jump
the
gun
here
and
end
up
having
a
conflicting
approach.
I
think
in
general
what
we
could
do
in
ike
should
align
with
whatever
we
end
up
putting
into
dhcp
and
ra
for
bootstrapping
trust
in
the
same
way
of
the
encrypted
resolver.
J
A
A
So,
as
mentioned
in
the
job
room,
the
existing
trust
is
different
from
or
trusted
posture.
It's
different
for
dhcp,
as
opposed
to
ike
in,
like
we
already
know
who
the
the
gateway
is.
The
other
batteries,
the
pier,
whereas
in
dcp
we're
just
sending
him
out
of
broadcast
and
waiting
for
some
information
there.
So
the
challenges
are
different.
A
G
If
it's
a
public
one,
then
sure
there
might
be
public
discovery
mechanisms
you
can
use,
but
if
it's
like
a
an
internal
one
and
there's
a
split
vpn
and
so
there's
a
split
dns
as
well
with
an
internal
only
zone
and
the
name
is
internal
only
zone
and
how
you
reach
that
name
without
actually
getting
to
the
name
server.
So
I
think
there's
there's
definitely
an
additional
bootstrap
problem
that
might
need
to
be
resolved
and
that
might
require
actually
sending
some
kind
of
cert
payload
for
the
for
the
tls
connection
or
the
https
connection.
K
K
It's
pretty
much
relying
on
the
work
that's
happening
in
add,
and
we
are
not
defining
any
iq2
extension
for
conveying
that
uhuri
templates.
The
only
reason
why
you
see,
in
addition
to
the
resolver
name,
that
the
ip
addresses
and
port
numbers
are
being
converted
is
to
avoid
any
dns
or
53
lookup,
that
is
to
basically
avoid
a
clear
texting
slot.
K
That
was
the
reason
for
adding
the
portables
and
ip
address,
but
we
can
definitely
wait
for
the
outcome
of
the
discussions
that
I
think
many
of
us,
including
tommy,
and
we're
actively
participating
in.
I
had
working
group.
The
other
one
that
I
wanted
to
bring
up
was
the
comment
that
was
brought
up
with
regard
to
using
private
certificates.
K
It
can
still
have
a
public
certificate
but
use
private
ip
addresses
and
the
vpn
provider
can
still
get
use,
acme
and
other
protocols
to
have
an
public
domain
name
and
get
a
public
certificate,
but
make
sure
that
that
internal
dns
server
is
only
reachable
by
the
vpn
connected
clients
and
not
by
anybody
outside
the
network.
So
we
did
not
see
a
reason
for
sending
the
certificate
fingerprint
back
to
the
client
for
authentication
purposes.
C
F
E
F
F
So
this
is
the
first
problem
scenario:
consider
the
network
that
is
very
bad
and
introduces
long
delays
and
high
packet
loss
so
initiated.
First.
Signs,
like
I
say,
need
request,
responder
response
with
cookie.
It
feels
it
only
feels
that
it's
under
attack
and
it
responds
with
a
cookie,
but
this
message
contains
cookie
requests
is
delayed
for
quite
a
long
time,
so
that
initiated
times
out
and
recents
its
initial
request
without
any
cooking.
F
F
F
A
rack
2,
including
this
cookie
into
the
request,
but
this
request
get
lost
in
the
network.
After
some
time,
the
network
initiator
receives
resp
to
response,
and
also
consider
that,
I
can
say,
need
completed
so
at
this
point,
both
initiate
and
responder
things
that
I
can
say
in
it
has
completed,
but
they
have
different
view
on
what
was
the
most
recent
request
message
from
initiator
so
initiator
since
thinks
that
it's
wreck
2
well
responded
since
that,
it's
sorry
respond.
E
F
F
I
can
say
it
is
completed
again
initiate
the
response
has
have
different
views
on
what
was
the
most
recent
request
message
from
the
from
the
initiator,
because
initiate
a
sense
is
that
it
will.
It
contains
cookie
c1,
while
responder
thinks
that
it
contains
cookie,
c2
and
again,
authentication
will
frame.
So
next.
E
F
E
F
E
E
F
E
F
F
And
so
what's
the
proposed
solution,
I
think
that
we
can
work
around
this
situation
by
excluding
cookie
into
from
there.
I
can
say
I
can
say
you
need
request
message
if
it
is
present,
so
every
every
functionality
that
is
tied
to
cookie,
like
in
technology
token,
will
be
retained,
but
it
is
not
fed
into
the
house
followed
compilation,
and
next,
please.
F
So
how
this
can
how
this
can
look
like
the
shelter
sends,
like
I
said
in
each
request
message
a
responder
that
supports
this
revised
cookie
processor
includes
cookie
notification
containing
cookie
and
an
empty,
revised
cookie
notification
just
to
indicate
that
it
supports
this
extension.
If
initiator
doesn't
support
this
extension,
it
will
respond
as
usual.
F
It
will
ignore
a
revised
cookie
and
everything
will
work
or
doesn't
work
as
as
it
currently
happens,
but
if
initiator
also
supports
this
extension,
it
will
place
a
cookie
into
the
revised
cookie
into
the
new
revised
cookie
notification
in
recent
request
message.
So
this
will
indicate
this
one
indication
for
the
responders
that
respond
to
that
initiator
also
support
this
extension.
F
F
E
F
E
F
F
F
F
G
F
I
G
G
F
C
D
F
F
G
Right,
okay,
yeah,
so
I
I
think
I'm
a
little
bit
in
agreement
with
with
joaf
on
on
the
chat
where
he's
like
is
this
case
worth
fixing,
because
you're
already,
assuming
that
there's
so
many
packet
loss
in
such
slow
network.
Even
if
you
get
a
tunnel
up
what
what's
left
to
do
with
it,
it's
going
to
be
unusable.
F
Well,
I
don't
know
again
if
it
depends,
we
encourage,
we
didn't
encounter
this
problem
in
stress
test.
Of
course,
it's
stress
test.
It
was
about
several
thousand
or
ten
thousand
of
eye
connections
that
simultaneously
I
clients,
not
data
type
clients
but
emulated
like
clients
that
simultaneously,
at
the
same
time,
going
to
the
respondent
and.
F
F
E
F
F
So
if
timed
out
is,
is
is
okay,
it's
it's
a
metal
condition,
temperate
message
so
by
the
acme,
but
actually
check
is
also
a
key
samsung
problem
with
network,
but
authentication
free.
It's
something
function,
problem
with
my
certificate,
and
that
is
for
customer.
It
is
very
annoying
and
it's
very
I
don't
know
it's
not
a
good
thing.
C
H
F
E
F
It's
it's
quite
possible
to
receive
several
different
cookies,
because
it's
in
the
draft-
sorry
it's
in
the
rfc,
I
critique
it's
quite
possible
situation
when
initiator
receives
a
first
cookie
request
with
cookie
one
and
then
cookie
request
with
cookie
two
and
it
just
resends
it,
because
it's
a
big
block
for
the
initiative.
It's
just
sent
us
back.
C
Actually,
I
think
in
this
case,
where
we
actually
have
a
cookie
and
you
change
the
secret.
I
think
most
of
the
case
is
actually
the
responder
cookie,
because
if
this
is
the
stateless
thing,
the
responder
spi
are
going
to
be
different,
because
this
is
sending
is
spi,
responded,
spiv,
zero
and
he's
responding
with
some
spi.
E
C
F
C
C
E
C
C
I
C
Then
we
have
to
discuss
about
so
I
will
probably
take
it
to
the
list
and
and
then,
if
the
list
is
agreeing
that
we
should
actually
work
on
this,
then
we
should.
You
know,
start
probably
you
know
working
on
this,
but
I
think
we
want
to
verify
that
on
the
list.
Also,
all
right,
so
the
next
one
is
not
valerie.
F
G
G
G
G
G
How
many
duplicate
ipsec
assays
you
want,
and
then
you
can
put
you
know
one
on
each
cpu
and
keep
them
sticky
on
that
cpu
and
we
have
a
q
info
notify
for
the
qos
case,
where
we
think
that
you
know
some
information
needs
to
be
conveyed
like
this.
Is
the
ipsec
safe
for
this
specific
quality
of
service?
G
So
there's
an
implementation
in
linux.
The
draft
has
links
to
it.
This
was
done
by
steven
classer,
and
this
includes
like
where
you
can
do
an
on-demand
acquiring
message
per
cpu.
So
you
can.
If
you
have
16
cpus
you
can,
you
can
say
you
can
do
up
to
16,
but
if
there's
only
two
cpus
sending
traffic
over
the
tunnel,
you
could
just
set
up
two
cpu
to
ipsec
essays.
G
G
G
Some
issues
that
you
know
we
could
use
input
of
the
working
group
for
one
is.
There
was
some
talk
about
how
to
negotiate
the
exact
number
that
you
want
to
do,
because
a
cpu
is
not
a
really
specific
measure
of
computational
power.
So
just
saying
like
I
have
four
cpus
doesn't
really
also
tell
you
how
powerful
they
are.
Maybe
the
other
end
will
only
do
two
and
you
know
versus
the
forum
on
the
smaller
device-
that's
good.
G
G
We're
also
thinking
of
whether
there's
use
in
signaling
on
on
sort
of
a
cpu
id
so
that
both
ends
can
sort
of
keep
sync
about
which
which
cpus
to
to
keep
something
on,
but
that
is
also
conveying
some
internal
state
of
these
machines,
so
so
we're
also
a
little
uncomfortable
doing
that.
So
we're
not
sure
if
there's
value
in
doing
this
or
not
now
for
the
queue
info.
If
it's
only
qos,
then
maybe
we
don't
need
a
subregistry.
G
And
so
then
you
you,
you
run
into
issues
where
one
cpu
is
like
underutilized
and
one
is
over
utilized
and
then
there's
also
issues
with
net
mapping
and
that
mapping
is
it's
the
same
thing
with
rss
you
that
those
gets
those
values
are
hashed.
So
if
the
the
net
route
in
between
changes,
the
mapping
and
changes
the
hash,
then
it
might
also
change
the
affinity
or
the
queue
where
the,
where
this
work
will
end
up
on.
G
So
some
hardware
related
things
that
maybe
we
should
or
should
not
dive
into
in
the
draft.
So
the
assumption
is
that
you
know
the
sender
has
no
issues
to
pick
which
cpu
it
will
use.
It's
only
the
receiver
that
needs
to
distribute
the
load
properly
and
that's
where
that's
where
the
real
hardware
support
is
needed.
So
most
network
cards
these
days
support
rss,
usually
the
only
supporters
for
udp
and
tcp.
G
So
that
would
be
nice
if
it's
available,
but
that's
usually
not
the
case,
and
we
see
that,
like,
like
virtual
nicks,
are
also
starting
to
play
in
this
space
and
trying
to
aggregate
things
and
bind
multiple
virtual
nicks
together
and
so
they're
they're.
Also
playing
in
this
space,
where
we
have
sort
of
you
know
a
virtual
hardware
solutions
and
next
slide.
G
So
so
I
mean
for
us
this
fixes
a
practical
problems
like
we
need
to
bring
up
the
performance
of
you
know
of
a
tunnel
between
two
endpoints.
Where
you
have
like
you
know,
you
don't
have
thousands
of
essays,
but
you
only
have
one
of
them,
so
this
is
one
way
of
of
solving
it,
and
so
the
question
is:
does
the
working
group
think
this
is
a
good
way
of
doing
it?
G
F
F
Requested
to
be
adopted,
and
so
I'm
ready
to
review
it,
and
I
think
we
discussed
with
paul
about
the
generic
general
approach
of
negotiation
of
these
things
in
agriculture
and
I'm
glad
that
so
the
drum
didn't
go
into
too
much
detail
on
the
hardware
and
internals
specifically,
is.
I
think
it's
quite
right,
my
margin
of
not
to
go
into
so
so
that's
why
I'm
against
cpuid?
G
Yeah,
we
would
definitely
like,
like
more
input
from
people
about
the
discussion
of,
like
you
know,
things
like
a
cpu
id
like
like.
Is
there
much
to
be
gained,
or
is
that,
like
local
implementation,
details
that
should
not
be
exposed,
or
that
has
like
little
value
that
I
think
that's
a
good
discussion
to
have
on
the.
C
G
So
no,
this
was
actually
that
it
predates
that
actually
a
number
of
itfs,
so
so
yeah.
Some
of
it
can
solve
similar
problems,
but
we
found
at
least
that
the
the
the
new
esp
work
is
trying
to
do
a
lot
more.
A
lot
of
different
things
is
trying
to
do
multicast
and
a
whole
lot
of
other
issues
that
are
that
we
fear
takes
like
will
take
a
lot
more
time
to
get
into
a
further
stage
than
just
getting
this
out,
and
this
is
like
a
concrete
problem.
G
B
Yeah,
it
definitely
seems
easier
to
get
through.
I
just
as
an
implementation
point,
even
without
like
an
rss
support.
You
know
just
having
been
in
like
vpp
or
whatever
you
know.
If
I'm
rece,
if
I'm
receiving
it,
I
can
fan
out
based
on
the
spi,
even
on
one
cpu
right,
I
can
do
40.
I
can
do
40
gig
on
a
single
core.
If
all
I'm
doing
is
looking
at.
You
know
the
spi
and
then
immediately
handing
it
off
to
another
core
to
do
decrypt
and
all
that
right.
B
B
C
G
C
Yeah,
the
one
of
the
questions
that
I
have
there
are
that
I
would
actually
assume
that
you're
actually
going
to
have.
You
know
to
prefer
to
be
like
three
times
what
you
have
a
cpus,
especially
because
I
mean
that
will
actually
solve
lots
of
the
other
cases.
It
solves
the
corner
cases,
it
doesn't
matter.
If
you
have,
you
know
eight
or
nine,
if,
if
your
limit
is
24
and
25
and
it
solves
the
problem
of
hashing,
because
if
you
have
lots
of
those
randomly
has,
they
will
spread
out
with
all
the
tpus.
C
Otherwise
you
have
to
have
a
certain
problem
that
you
have
to
allocate
cspi
so
that
they
actually
hash
into
the
certain
you
know
cpu,
which
might
make
it
very
difficult.
If
you
don't
know
how
the
hashing
is
done
in
the
hardware,
so
I
I
think
it
would
be
much
more
interesting
to
just
say
that
okay
use
the
big
enough
number.
C
The
question
is
the
queue
info
qr
info-
I
I
don't
under
I
mean
if
it
if
it
needs
a
super
registered,
then
it
probably
needs
to
have
a
standardization
way
of
putting
something
in
there.
If
it's
just
opaque,
they
stop
for
the
implementation
for
two
implementers
that
know
each
other,
then
I
don't
think
we
actually
need
a
super
extra,
but
if
you
need
to
have
a
super
extend,
we
probably
also
want
to
specify,
what's
in
there
like,
what's
really
in
there.
G
So
so
so
right
now
the
only
the
only
use
we
have
for
it
is
qos.
So
we
could,
we
could
tailor
it
to
qrs
only
and
have
it
specifically
for
that,
but
we're
wondering
maybe
other
people
have
other
bits
of
information
that
is
useful
for
them
to
to
to
inform
the
peers
of
for
for
this.
So
if
nobody
comes
up
with
anything
new,
maybe
we
will
just
reduce
it
and
say
like
we'll:
just
do
a
specific
qrs
one
and
no
no,
so
then
it
would
be
like
you
know,
qos
info
specifically.
G
F
So
this
draft
is
concerned
with
high
performance
issues
for
pck
and
actually,
if
you
send
very
small
packets,
like
yp
packets
with
high
rate,
then
I
our
head-
that
esp
implies
is
very
high.
And
even
if
network
is
fast,
you
will
lose
a
quite
noticeable
percentage
of
its
performance
and
so
that
I
think
that
iptfs.
F
G
Yeah,
that's
true,
and
we
had
a
two
on
our
list
of
of
you
know
similar
workouts
being
done
right
now,
so
so
yeah.
If,
if,
if
the
new
esp
could
do
something
as
well,
where
it
can
like
sort
of
group
a
number
of
small
packets
together
into
one
and
do
that
based
on
like
you
know,
similarly
to
how
how
modern,
kernels
or
nic
cards
do
this
gso
or
other
other
features
that
would
be
great
to
have.
But
that
would
be
a
much
more
substantial,
substantive
change
than
than
doing
this.
A
A
G
A
G
G
B
G
Sorry,
I
was
probably
muted.
We
don't
want
to.
We
don't
want
to
go
into
the
the
implementation
itself,
like
it's
just
to
negotiate
and
say
like
this
is
the
the
quality
of
service.
You
know
voip
super
important
and
how
you
deal
with
that.
On
the
other
hand,
it's
up
to
the
other
end,
but
like
like
at
least
you
have
two
different
ipsec
essays
to
encrypt.
Like
you
know
your
bulk
unimportant
stuff
and
your
super
important
stuff.
B
G
C
All
right,
so
I
think
that's
it
for
that
one,
and
then
we
move
to
the
I
question
one
graveyard,
which
is
not
our
working
group
item,
because
it's
not
it's
I'm
talking
about.
I
question
one,
even
if
I
original
first
version
of
the
agenda,
I
was
talking
like
version
2
graveyard
by
mistake,
but
that
was
fixed,
so
fall.
G
Yeah
so
funny
enough,
even
though
so
next
slide
yeah
for
enough,
even
though
it
has
not
been
adopted.
Yet
if
you
look
at
the
ietf
108
action
items
for
the
chairs,
that
says
perhaps
go
to
working
group
last
call.
So
apparently
the
chairs
were
jumping
to
make
this
happen
anyway.
So
only
a
very
few
small
changes
made
us,
mostly
the
text
from
sean
turner,
to
make
sure
that
we
were
not
seeing
anything
that
either
ayanna
or
isg
couldn't
couldn't
be
instructed
to
do
so.
G
All
the
work
has
really
been
done,
and
I
think
it
we
should
just
get
it
done
or
we
should
just
drop
it,
but
but,
like
it,
clarifies
the
anna
registries,
it
adds
a
deprecated
column.
It
I
think
it.
You
know
it
will
make
sure
that
people
who
are
implementing
gang
won't
start
implementing
all
this
old
stuff
anymore,
because
it's
clearly
deprecated
and
and
think
it's
very
useful
to
do.
It's
also
just
really
nice
to
have
an
rfc
number,
where
you
can
point
to
people
and
say,
like
don't
use
ikv
one.
C
I
C
Left,
I
don't
see
anybody
jumping
onto
the
queue
or
going
to
the
jobber
or
anything
like
that.
So
I
think
that's
it.
So
thank
you
for
the
presentations
I
I
will
try
to.
As
I
wasn't
able
to
collect
all
the
you
know,
the
action
items
that
I
was
supposed
to
do.
So,
if
anybody
has
any
action
items
I
should
be
doing
send
me
an
email
after
this
meeting
remind
me
that
this
was
something
that
we
agreed
on,
because
I
I
most
likely
forgot
most
of
the
things
that
we
agreed
on
here.
