►
From YouTube: IETF109-IDR-20201120-0900
Description
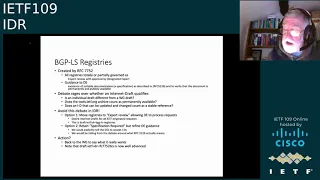
IDR meeting session at IETF109
2020/11/20 0900
https://datatracker.ietf.org/meeting/109/proceedings/
B
A
A
A
A
C
C
So
if
you
have
also
with
virtual
I
gift,
I
would
like
to
make
sure
I
get
all
the
adoption
requests
if
you've
got
an
adoption
request,
please
send
me
a
note
and
a
yang
model
has
received
shares
comments
from
the
young
doctors.
I'd
love
to
know.
If,
if
there's
any
comments,
I
still
have
a
couple
people
to
check
with.
C
Find
it
okay,
where
are
we
well
flow?
Spec
5575,
fists
and
flow
spec
b6
are
very
close
to
publication.
We're
crying
we're
nitpicking
with
some
of
the
isg
members,
but
that's
good.
We
wanted
to
make
sure
this
time.
We
don't
have
to
go
back
and
do
the
the
version
ones
it's
time
to
begin
work
for
people
who
are
interested
in
flow,
spec
version,
2
watch
for
a
call
for
presentations,
and
perhaps
an
interim
I'd
like
to
kick
things
off
on
interims,
because
this
is
a
short
time
sign.
C
The
ipsec
tunnels
are
still
progressing
along
I'll.
Go
through
that
and
bgpls
will
talk
about
streamlining
the
auto
comp
work
is
started,
the
chairs
will
restart
and
I
think
we're
pretty
much
got
one
route
league
protection
document
and
girl
and
idr
are
working
together
next
slide
the
ipsec
tunnels.
This
is
just
a
report
from
someone
who
has
been
trying
to.
C
Work
with
all
three
sets
of
authors,
we
had
two
an
idr
one
and
best.
I
still
see
three
different
use.
Cases
for
these.
My
goal
has
gone
down,
has
as
a
sort
of
shepherd
trying
to
help
them
is
to
see
if
we
can
share
tlbs
if
they're
this
subtleties,
if
they're
the
same
information,
but
the
critical
thing
is
that
they
get
reviewed
by
the
security
area
and
or
security
directed,
so
that
when
we
come
back
to
the
isg
with
them,
we're
not
spending
time
iterating
there.
C
D
That's
interesting,
that's
wrong,
so
they
were
all
all
set
up
as
specification
required
with
a
approval
by
a
designated
expert
and
the
guidance
to
the
de
they're
asked
for
a
stable
document,
as
described
in
rfc
5226,
which
is
now
eight
one.
Eight
one,
seven
four.
I
can't
remember
so.
There's
lots
of
debate
about
whether
an
internet
draft
qualifies
as
a
stable
document
and
alvaro
pointed
out
that
idr's
not
the
place
to
have
this
sort
of
debate.
D
D
D
C
E
E
What
I
want
to
say
is
that
I'm
not
opposed
to
two
documents
or
whatever
you
guys
want.
What
I
did
want
to
point
out
is
that
7370,
which
adrian
mentioned,
is
the
guidance
for
actual
review
for
the
isis
registries,
and
basically,
what
that
says
is
that
it
is
basically
7120
but
handled
by
the
expert
review
handled
by
the
experts.
In
other
words,
drafts
need
to
basically
be
adopted
by
the
working
group
before
anything
gets
adopted.
E
E
With
that
little
caveat
of
maybe
there's
no,
not
enough
clarity,
different
places
about
whether
an
idea
is
accepted
or
not.
That
is
totally
up
to
the
these,
and
I
know
that
it's
not
that's
not
documented
anywhere,
but
you
know
I'm
sure
that
the
current
des,
which
adrian
is
one
and
the
chairs
and
me
and
ayanna,
wouldn't
be
opposed
to
any
of
that.
So
having
said
that,
if
we're
gonna
go
with
seven
three,
seventy
like
expert
instructions-
it
is
pretty
much
the
same
thing
that
you
have
today.
E
If
one
of
the
objectives,
which
is
what
I
understood
from
the
draft,
was
to
speed
things
up
and
let
people
request
code
points
without
being
working
group
documents,
then
that
doesn't
necessarily
get
you
there
now
again,
assuming
that
737
is
taken
the
way
it
is,
it
can
still
be
modified.
So
I
just
want
to
point
that.
C
C
Did
you
have
any
other
comments
I
think
alvaro?
I
wasn't
trying
to
say
that
things
were
really
slow,
but
I
agree
that
tunnel
end
caps
took
a
lot
of
time
out
of
both
alvaro
john
and
I
it's
a
good
and
meaty
speck.
I'm
amazed
with
some
stuff
john's
done.
Okay,
adrian
any
more
final
comments.
Otherwise
I'll
go
on
to
some
more
chair.
D
C
A
C
C
Okay,
we
have
the
auto
conf
design
team
and
this
one
I
hope
you
all-
will
take
a
look
at
it.
Sort
of
got
installed
partly
many
things,
but
we're
going
to
give
a
push.
I
have
a
couple
dates
in
december,
8th
and
15th
if
you're
on.
Thank
you,
john
you're,
back
if
you're
on
the
auto
conf
design
team-
and
you
have
strong
feelings
for
a
particular
date
in
december-
please
send
we
will
try
to
get
some
meetings
and
get
an
initial
statement
and
design
document
out.
C
C
The
last
one's
just
a
big
thanks
to
g
he's
done
a
great
job
of
organizing
and
shepherding
things
we
wanted
to
make
sure
to
thank
him.
He
created
our
agenda
and
organized
our
speakers
and
helped
john
and
I
stay
focused
on
the
tunnel
and
caps
back.
Thank
you,
john.
I
think
we
should
go
to
our
first
any
comments.
Folks
on
any
of
the
points
in
the
chair,
slides
or
the
status.
F
F
Just
a
quick
overview
not
going
to
go
to
all
the
details,
so
this
was
presented
a
year
ago
now
and
we
have
had
you
know,
feedback
and
inputs
a
lot
of
discussions
on
their
list
as
well,
and
all
of
those
have
been
updated
or
captured
in
this
update,
quick
point
that
the
the
base
are
the
base
pack
in
spring.
You
know
which,
for
which
the
bgp
extensions
are
covered
here,
is
also
kind
of
getting
ready
for
working
group
last
call
in
spring
next
slide.
F
F
There
was
some
confusion
about
the
policy
name
tlv
that
was
there
existing,
and
you
know
that
was
actually
the
sr
policy
candidate
path,
but
then
based
on
requirements
and
requests.
We
also
added
the
policy
name
again
for
alignment
with
sr
policy,
draft
discussion
about
the
route
origin,
community
and
its
usage
to
indicate
the
originator.
So
we've
added
that
in
the
draft
and
then
we'll
go
about
the
changes
related
to
srv6
in
the
next
slide.
F
But
other
thing
I
would
like
to
flag
quickly
is:
we've
seen
the
tunnel
encaps
draft,
you
know
getting
fixed
up
and
as
part
of
that,
the
ayana
registration
is
happening
there
for
the
color
extended
community.
So
this
draft
has
now
been
updated
to
refer
there,
and
you
know
diana
section
text
has
been
updated.
F
F
We
had
a
check
with
some
of
the
vendors
and
you
know
whether
they
are
deployed
and
used
and
all,
and
we
got
the
indication
that
they
may
not
be
implemented
or
deployed
fully
as
yet,
but
just
to
be
safe.
The
proposal
is,
to
you
know,
deprecate
them.
They
are
kept
in
the
appendix
so
look
forward
to
feedback
from
the
working
group
on
on
this
one
next
slide,
please.
F
So
next
step
is,
I
would
say,
preparing
for
the
working
group
last
call.
The
implementations
have
been
updated
with
two,
but
we're
aware
that
there
are
more
so
I
would
request
to
please
update
and
I
think
it
would
be
good
if
we
can
plan
a
working
group
last
call
for
this,
preferably
after
the
base.
One
is
done
in
spring.
F
G
F
F
So
we
started
around
idea
104
this
thing
to
try
to
fix
them
up,
and
you
know
the
draft
was
presented
at
105
a
little
over
a
year
ago
and
then
it
was
adopted.
So
it's
been
a
year
now
more
than
a
year.
So
I
would
like
to
thank
everybody
again
for
a
lot
of
feedback
and
input
a
lot
of
it
on
the
list,
but
there
was
also
a
lot
of
off
list
comments.
Next
slide.
F
F
F
F
F
F
F
So
if
I
mean
how
do
we
go
about
this
and
wanted
to
check
here
whether
we
need
to
keep
this
this
document
open?
If,
yes,
for
how
long?
If
no
then,
maybe
next
year,
early
next
year,
we
start
planning
for
a
working
group
last
call
because
I'm
not
sure,
if
helps
just
to
keep
the
document
open,
look
to
inputs
from
the
working
group
chairs
as
well.
C
John
I'll
jump
in
here
real
quick.
I
always
find
that
a
working
group
last
call
knocks
out
documents
when
knocks
out.
Excuse
me
comments
to
documents,
so
I'd
go
for
december
or
january
for
working
group
class.
Call
whenever
you
finish
the
other
things
john,
do
you
have
any
other
comments
about
that.
A
A
I
you
know
we
we
need
to
have
a
proper
working
group
last
call
and
and
know
that
some
people
have
reviewed
it.
But
beyond
that
now,
let's
let's
get
it
done,
I
mean
if
anybody
else
thinks
otherwise,
please
put
yourself
in
the
queue
but
I'd
say
yeah.
What's
you
said,
let's
go
ahead
with
the
last
call
fairly
promptly,
and
I
see
adrian
volunteering
to
review.
Thank
you
adrian.
A
H
So
the
if
the
file
name
for
historic
reasons
has
nvo3
in
it,
but
it
it's
actually
designed
to
cover
flows
for
a
wide
variety
of
tunnel
types
that
are
listed
there.
One's
currently
in
the
draft
will
be
possible
to
add
more,
I
suppose,
but
I
think
it's
got
a
pretty
good
covering
and
it
allows
you
to
match
on
the
actual
tunnel
header
fields
of
various
sorts,
as
well
as
the
various
headers
that
are
just
beyond
the
tunnel
header.
Typically
ip
headers,
just
beyond
the
tunnel.
H
Header
could
be
other
things
and
you
can
as
well
match
on
the
ip
or
whatever
header
in
front
of
it.
There'll
be
examples
and
stuff
in
a
little
bit
later
in
the
presentation-
and
you
indicate
all
this
with
a
happy
safy
pair
using
a
new
safi
that
indicates
it's
a
flow
spec
for
tunnel
traffic
and
the
affi
indicates
what
you're
going
to
match
right
at
the
very
beginning
of
the
packet
or
the
leaning
of
the
packet
inside
the
vpn.
H
If
it's
a
case
where
you're
matching
vpn
traffic,
so,
for
example,
you
might
have
a
ipv4
or
a
fee,
but
the
saffy
says
tunnels.
That
means
you've
matched
an
initial
ipv4
header,
but
then
you
would
be
able
to
match
various
forms
of
following
that
tunnel
header
and
if
you
want
to
go
beyond
that
and
match
the
headers
just
beyond
the
tunnel
header
next
slide.
H
H
So
this
has
been
changed.
The
last
presented
version
was
08,
so
0809
or
changes
in
the
precedence
rules
to
clarify
things.
Obviously,
only
when
a
tunnel
source
back
is
involved,
existing
rules
cover
other
cases
and
various
editorial
improvements
and
typo
fixes,
particularly
the
two
noted
there,
which
occurred
multiple
times
next
slide.
H
And
then
there's
changes
from
09
to
the
currently
posted
10
version.
The
l2
tpv3
flow
spec
in
there
was
extended,
and
previously
it
was
good
for
data
messages,
but
it
didn't
really
cover
control
messages,
so
that
involved
one
fairly
small
addition:
sort
of
expanding
the
capabilities
for
that
particular
tunnel
type.
And
the
second
point
here
is
the
various
fields
which
were
added
for
matching
purposes
to
handle
control
messages
and
for
further
editorial
improvements
next
slide.
H
H
There
are
two
flags.
One
indicates
whether
or
not
there's
a
routing
distinguisher
present,
because
you
want
to
handle
a
vpn
case
and
the
other
is
whether
or
not
there's
an
what
is
called
an
inner
flow
spec
so
moving
down.
Then
there's
the
outer
flow
spec
and
that's
matches
an
outer
header,
which
type
is
determined
by
the
affy
for
the
atheist
fee
that
invoked
this
parsing
and
interpretation.
H
It
could
be
extensive
or
could
be
minimal
depending
on
the
kind
of
tunneling
and
then,
if
you
have
indicated
it's
present,
that
you
can
have
an
optional
inner
flow
spec
and
you
have
to
provide
another
affi
down
there
for
that,
because
you
need
to
indicate
whether
you
want
the
inner
flow
spec
to
match,
for
example,
ipv4
or
ipv6
next
slide,
please
so.
Here's
a
simple
example
where
there
actually
isn't
anything
to
match
in
the
tunnel
header
it's
ip
and
ip.
So
you
have
that's
the
outer
and
an
interflow
spec.
H
H
This
is
a
slightly
more
complicated,
vxlan
case.
In
this
case
there
is
the
vxlan
header,
it
can
match
fields
in
there
and
similarly
there's
an
outer
and
inner
flow
specs,
and
in
this
case
the
interflip
would
be
optional.
You
might
want
to
only
match
outer
and
some
fields
in
the
vxlan
header,
like
the
vni
or
something
and
not
match
anything
on
the
inner
header.
H
J
J
H
H
Say:
okay,
the
the
this
draft
says
that
for
the
matching,
the
headers,
which
is
the
really
new
you
know
substance
to
be
matched
that
there's
a
separate
registry
and
it's.
I
believe
it
says
that
they
are
all
tlv
format,
so
it
doesn't
say
anything
specific
about
what
to
do
about
unknown
types,
for
example.
K
I
H
J
E
H
Yes,
yeah,
essentially,
the
the
fields
being
matched
are
all
either
like
value
fields
or
bit
fields,
or
something
like
that.
So
the
existing
match
operators
and
way
the
value
to
be
matched
is
encoded
and
the
logic
of
having
multiple
of
those
and
the
ending
and
oring
is
sort
of
all
the
same
but
they're,
I
believe,
all
teals.
H
E
C
C
C
What
the
working
group
wants
john-
and
I
specifically
limited
the
first
three
things
to
what
the
operators
told
us,
which
is
5575
bis
v6,
because
the
isgs
strongly
wanted
it,
and
so
did
the
operators
and
the
oid,
because
the
operators
wanted
it.
I
would
love
comments
now.
We
also
can
take
comments.
John,
should
we
take
this
to
the
list
because
of
time
or
shall
we
allow.
A
C
I'd
I'd,
like
some
feedback,
should
we
delay
this
to?
Is
anybody
are
the
opportunities
waiting
for
this
or,
as
I've
announced
it's
time
to
start
v2?
Shall
we
put
this
in
v2
this
document
with
what
donald's
done
starts
to
have
all
the
tlvs?
We
don't
know
if
there's
any
problems,
it's
sort
of
going
toward
that
direction,
feedback
working.
A
J
J
If
the
two
are
intended
to
be
mixed
at
some
point
having
them
as
separate
after
saffies
is
a
little
weird
if
it
really
can
live
as
ships
at
night,
even
if
it's
just
temporary
because
of
a
strong
need
for
the
use
case
to
be
deployed,
nothing
stops
somebody
from
shipping.
You
know
basically
this
version
of
the
draft
to
cover
the
use
case,
and
then
we
end
up
with
spec
v2.
We
end
up
in
the
merged
form.
H
Can
I
make
a
brief
comment?
I
I
just
wanted
to
say
that
I
think
that
a
working
group
last
call
would
cause
greater
working
group
attention
and
review
of
this
document,
and
that
would
perhaps
yield
something
which
clearly
better
expressed
the
need.
What
the
actual
you
know,
requirements
and
an
adequate
mechanism
would
be.
Certainly
the
the
flowspec
needs,
as
indicated
by
this
draft,
should
be
one
of
the
inputs
to
the
v2
effort.
I
would
think
that
was
my.
C
C
A
C
L
L
So
after
we
receive
those
comments
and
then
we
update
the
document
and
then
address.
I
think
we
think-
and
we
address
the
those
comments,
so
those
comments
can
be
classified
three
three
groups.
One
group
is
that
we
already
have
configurations
we
can
for
dynamic,
adjuster
traffic.
We
can
do
this
job
through
configurations,
so
why
do
we
need
rpd
for
dynamic
traffic
adjustment?
So
that's
the
one
group
of
comments,
so
another
group
of
comments
is
that
so
in
in
the
older
document,
so
it
looks
like
that
the
rpd
route
is
distributed
through
p2p
or
p2mp.
L
L
L
So
in
order
to
adjust
the
traffic
dynamically
as
soon
as
we
want
to
adjust
the
traffic,
then
we
need
put
or
push
some
configurations
to
sum
to
those
some
of
the
loads
in
the
network,
because
this
adjust
of
traffic
is
dynamic,
so
we,
the
frequency,
may
be
sometimes
high
and
then
so.
This
kind
of
configuration
change
and
some
of
the
nodes
of
the
network
will
be
very
sometimes
frequent
and
then
sometimes
maybe
it's
not
that
frequent.
L
So
with
this
kind
of
operation,
so
change
configuration
on
some
of
those
and
then
delete
the
configuration
of
something
nodes
for
dynamic.
Adjust
traffic
will
have
some
issues.
For
example,
this
kind
of
operation
is
very
complex
and
error-prone.
In
addition
to
that,
this
kind
of
dynamic
we
have
a
stable
configuration
and
then
we
have
the
name.
Calculation
keep
changing.
So
this
is
hard
for
for
operator
for
operators
to
maintain
this
kind
of
things
so
with
the
rpd
ross
and
then
this
issues
or
problems
is
well
is
so
is
resolved.
L
So
I
us
so
another
group
of
comments
from
the
logical
is
that
of
people
say
that
this
kind
of
rpd
wrong
distribution
is
a
p2p
and
even
though
they
can
be
a
p2mp,
so
we
just
disk
this
one.
So
we
through
updates
document
with
more
details
and
then
through
this
update.
So
we
can
see
that
rp
raw
distribution
is
p2.
L
Mp
is
about
a
p2p,
so
here
we
show
a
typical
application
scenarios.
So
in
this
network
we
have
a
1s
s1
and
then
we
have
another
two
as
s2
and
s3.
So
here
we
we
have
a
controller
and
that
controller
is
is
connected
to
a
router
reflector.
So
this
rolls
reflector
is
connected
to
all
the
other
nodes.
So
here
we
just
show
the
nodes
a
b
and
c,
so
you
want
to
adjust
traffic
dynamically.
L
L
So
after
each
of
the
routers
receive
these
rpd
routes,
so
it
will
apply
the
policy
included
in
this
rp
route
to
to
to
the
to
the
routers
or
or
according
to
the
peers
or,
for
example,
we
can
apply
those
policies
controlled
by
the
pip
address.
So
if
a
pip
address
is
zero,
then
that
means
we
will
apply
the
policy
to
order
all
the
ps.
So
if
this
p
address
is
a
determined
is
not
zero.
That
means
we
just
apply
that
policy
to
data
to
that
ps.
L
L
So
the
last
of
the
group
issue
is
about
about
failures,
so
so
the
thing
is,
we
can
classify
different
types.
One
type
is
that
the
failure
is
a
because
of
bach,
for
example,
failure.
The
route
is
fair
if
we
cannot
of
a
route
fails
to
install
the
routes
in
the
folding
table,
so
this
is
out
of
our
control.
This
is
the
box,
so
we
need
to
fix
this
bug,
so
this
is
a
fairly
easy
to
qualify.
This
video
is
out
of
of
the
this
document,
so
another
thing
is
that
we
can
have
controller
failure.
L
We
can
have
a
failure
of
illustrations
between
the
controller
and
the
router
reflector.
So
for
these
kind
of
failures,
so
we
can
use
existing
gr,
so
we
can
use
the
basic
jr
so
in
this
case
either
controller
failure
or
session
failure,
and
then
those
of
the
routes
for
use
for
adjustment
traffic
can
stay
there
for
some
time.
So
if
we
use,
we
think
that
this
time
it's
not
a
long
enough,
so
we
can
use
a
long
leaf
restart.
So
in
this
case
we
can
keep
that
route
for
adjusting
traffic
longer.
L
So,
in
what's
the
case,
so
even
so,
we
use
this
kind
of
a
great
gr,
try
to
keep
the
route
for
adjusting
trafficker
get
withdrawn.
So
in
this
case
the
worst
case
is
that,
even
though
this
christmas
doesn't
work
for
this
case,
we
go
back
to
the
original
routes.
That
means
we
try.
We
try
to
use
the
rpv
rules
to
adjust
traffic
to
the
base
of
the
routes
we
think,
but
because
of
a
failure,
those
are
adjust
the
votes
for
adjustments
get
withdrawn.
L
A
N
N
Yeah,
so
in
let's
draft
we
mentioned,
I
think,
were
to
refer
to
the
family
of
the
unpassed
telemetry
techniques.
We
include
in
this
terminology
has
the
iom
and
the
alternate
marking
method,
and
we
also
considering
the
iphage
domain.
It
means
that
the
perverse
measurement
domain
so
from
the
security
consideration
size
to
to
avoid
the
I
feed
data
leakage
outside
the
domain.
So
we
need
to
make
sure
that
I
face
the
capsulating
node.
N
That
is
the
tail
nodes
must
remove
the
data
field.
So
so
that's
why
we
extend
to
the
bgp
protocol
to
advertise
the
iphone
the
capsulation
node
capability
to
the
head,
node,
so
taking
less
extension
to
bgp
protocol.
The
head,
node
can
collect
the
information
and
to
know
whether
the
tail
node
can
support
the
specified
effect
capability
before
insert
the
ipad
command
into
the
traffic
packet.
N
So
from
this
motivation,
we
we
defined
two
options
in:
let's
drop,
to
make
the
extension
to
b2p.
The
first
of
all
is
the
extension
to
ipv6
as
v6
and
ipv
4
address
specific,
extended
community,
and
the
second
option
is
to
extend
to
the
bgp
next
top
capability
yeah
from
yes.
Next,
thanks
so
from
first
of
all,
we
we
need
to
define
the
f8
capability,
what
what
is
the
capability,
so
here
we
mentioned
the
format
field
we
defined
in
less
dot.
Here
we
see
this.
This
is
a
16
bit
bitmap
field.
N
N
N
I
mean
the
effects
encapsulation
node,
so
here
from
this
two
figure,
we
can
see
that
the
format
and
in
this
format
the
optional
ipv4
address
and
and
the
v6
address-
is
the
address
of
the
iphas
encapsulation
node
yeah
next
piece,
please
so
yeah
that
this
is
the
option.
Two
is
it
extension
to
the
bgp
next
top
capability.
N
A
I
I
It
is
introduced
in
the
sr
policy
architecture
draft
that
candidate
power
can
be
used
for
path,
protection
and
and
sr
policy
allows
for
multiple
kennedy
powers
and
only
one
hectic
candidate
parts
can
be
provisioned
in
the
forwarding
plan.
At
the
same
time,
so
other
lower
preference
can
in
the
past
may
be
used
as
a
backup
house
when
distributing
sr
policies
using
pdp.
I
Each
candida
path
is
carrying
an
mli
so
far.
There
also
no
mechanism
to
carry
the
protection
relationship
from
kennedy
park
in
bgp
advertisement
and,
of
course,
we
can
do
it
by
local
configuration
and
backup
candidate
provides
protection.
Only
when
the
segment
lists
in
the
active
canada
house
are
invalid.
I
I
If
you
want
to
prove
for
protect
second
laser
one,
so
flows
can
still
be
load
balanced
between
second
laser
two
and
the
back
up
path.
After
seven
minutes,
long
field
using
canadian
parts
for
protection
can
not
achieve
that
goal,
and
this
document
proposes
extensions
of
vgp
in
order
to
provide
pass
protection,
use
segment
lists
when
delivering
as
a
policy.
I
Settlement
list
can
be
used
solely
or
combined
with
kennedy
pass
together
for
pass.
Protection
on
this
figure
gives
an
example.
The
harriet
node
has
received.
Two
candidate
parts
belong
to
the
cmsr
policy,
and
cp1
has
the
higher
preference,
so
cp1
is
chosen
as
a
primary
pass
and
in
cp
1
list.
3
is
a
backup
list,
so
it
will
not
be
enabled
on
the
data
plane
at
first
after
this
one
fails.
The
3
will
take
place
if
list
2,
and
this
3
are
both
invalid.
I
Here
are
the
bgp
extensions
for
sr
policy,
proposing
this
draft
and
the
b
flag
in
segment
list.
Sub-Tree
indicates
the
segment
list
acts
as
a
pure
backup
part
in
the
kennedy
pass,
and
this
identifier
trv
is
used
to
identify
the
corresponding
segment
list
and
it
contains
the
optional
sub
theory
list
protection
theory
which
carries
the
protection
relationship
of
segmentations.
I
I
And
in
the
tlsp
distribution
draft
they
could
describe
a
mechanism
to
collect
the
sr,
the
policy
information
that
is
locally
available
in
the
node
and
advertise
it
into
pgpos
updates
and
it
it
includes
sr
candidate,
pass
state
cov
and
has
a
settlement
list
to
trv
and
the
sab
flag
who
are
originally
defining.
Can
we
deposit
a
tree?
Well,
the
extracting
the
case.
The
candida
parts
is
an
administrative,
sharp
state
and
pay
flag
in
the
case.
Can
it
pass
in
the
active
part
and
b
flat
in
the
case
of
kenya?
I
Park
is
a
backup
and
two
new
flat.
Two
new
flags
are
introduced
in
this
draft
in
sr
segment
list,
tlv
to
offer
more
details
of
the
settlement
list,
states
and
the
s
flat
and
the
b
flat
as
a
similar
meaning
and
the
s
flag
indicates
a
second
list
using
the
administrative
chart
state
and
the
b
flag
indicates.
The
settlement
list
is
a
backup.
Part
can
be
next
like
please
and
anything
will
pass
feedback.
Some
comments.
F
F
F
F
A
K
K
K
They
require
back-end
servers
to
be
very
close
to
the
device
and
also
they
require
multiple
servers
for
the
same
applications.
So
you
could
have
5g
sites
and
each
of
the
cell
tower
to
to
have
this
back-end
server
hosted
and
they
have
virtual
interactive
conference.
All
those
use
cases
being
identified.
There
all
have
the
requirement
of
the
short
delay.
K
So
one
of
the
characteristics
of
5g
system
is
the
size
are
very
close
in
proximity.
So
you
can
have
one
side
like
you:
have
a
bunch
of
ues
user
device
anchored
into
psa
psa
means
packet,
section
anchor
and
they
go
to
the
local
data
network
and
you
could
have
another
psa
too
in
very
close
proximity.
So
for
the
server
back-end
server
you
could
have
multiple
copy
of
them
very
close
nearby.
K
K
So
the
the
benefit
of
anycast
is
really
for
network
to
expose
to
utilize
or
leverage
the
network
routing
layer
to
help
application
to
achieve
better
performance
and
to
eliminate
the
single
point
of
failure
of
the
local
dns
resolvers
or
the
application.
Low
server
load,
balancers
and
also
many
client
in
the
fixed
network
or
in
the
mobile
or
ue,
tend
to
use
their
cache
ip
addresses
for
extended
period
of
time.
K
So,
even
if
you
have
local
dns
resolver
in
each
of
the
local
data
network,
you
when
they
move
to
a
new
location,
they
may
not
resolve
to
find
a
new
ip
address,
so
the
benefits
are
great,
but
they're
also
bring
a
bunch
of
issues.
One
of
the
key
issues
is
when
all
those
servers
are
very
close
in
proximity.
K
K
So
when
the
ue
moved
to
anchor
to
the
psa2,
the
performance
overall
performance
will
be
better
if
they
are
still
served
by
their
original
es1.
So
the
many
factors
are
affecting
where
the
routing
is
another
issue
that
quite
different
bring
in
by
this
edge
computing
is
from
the
psa2
the
package
session
anchor
2.
M
K
Okay,
okay,
so
in
in
today,
especially
if
you
look
at
ipv6
right,
they
have
a
flow
label.
So
many
today's
routers
support
putting
all
the
flows
all
the
packing
within
one
flow
into
one
path.
Okay,
that's
one
criteria
later
on.
I
can
explain
some
of
the
criteria
for
them
put
into
the
ingress
router
so
that
they
can
guarantee
that
a
packet
belonging
to
one
flow
always
anchor
into
one
particular
instance
of
anycast
server.
M
A
O
Okay,
good,
I
don't
know
linda
if
it
helps.
I
see
that
you're
I
mean.
I
see
one
slide
that
talks
about
within
the
market.
I
see
another
slide
that
talks
across
markets
and
I
know
you're
trying
to
kind
of
represent
the
ip
network,
but
I
don't
know
if
it
helps.
If
you
can
draw
out.
You
know
the
du
cu
upf,
because
you
know
in
the
old
days
that
was
all
you
know,
backhaul
now
between
frontal
mental
and
backhaul.
K
John,
if
you
can
bring
up
the
previous
page
so
in
this
network,
obviously
from
the
base
station
e
note
b
to
the
psa,
that's
within
5g
system,
so
they
have
ip
network
as
well.
There's
a
draft
in
the
dmn
on
the
tn
aware,
mobility
about
network
within
the
5g.
They
have
net
ip
network
here.
I'm
talking
about
a
local
data
network
after
the
upf,
so
upf
and
psa
is
psa,
is
a
function
of
the
upf
user.
K
K
Okay,
so
then,
so
this
page
is
about
in
the
5g
edge
computing
service
to
select
a
particular
edge
server.
Traditionally,
anycast
is
purely
based
on
the
network.
Routing
cost
right,
but
in
the
5g
edge
computing
environment,
for
example,
s1
here,
and
they
are
in
three
different
locations,
because
three
different
local
network
and
the
network
routing
distance,
maybe
there's
difference
the
round-trip
time,
maybe
a
little
bit
different,
but
there's
other
factors.
For
example,
s1
could
be
a
bigger
capacity.
K
K
K
There
could
be
that
for
particular
ue1
that
he
actually
initially
anchored
to
psa1
upf1
and
go
to
the
ldn1
s1
when
he
moved
to
the
side
b,
which
is
maybe
very
close
to
each
other.
The
capacity
over
taking
the
network
delay
so
the
quite
a
few
different
factors
for
the
ingress
router
to
consider
to
choose
optimal
optimal
of
any
cast
location.
K
K
Okay,
so
here
is
why
we
need
this
mat
application
metadata.
So
this
is
a
new
path
attributes
which
include
load
measurement,
meaning
for
the
each
of
the
egress
router,
which
have
the
server
application
servers
directly
attached
be
able
to
do
some
measurement
on
the
traffic
flow
to
and
from
the
server.
There
is
a
capacity
index.
K
This
capacity
index
can
be
pre-configured
or
could
be
learned
based
on
historic
data,
and
there
is
a
site
preference,
so
the
site
preference
can
be
dynamic
based
on
who
is
accessing
it
depending
on
different
ue.
The
preference
could
be
different
so
with
all
those
combinations
added
together,
the
ingress
router
can
make
intelligent
decision
in
the
draft
there's
a.
We
give
an
example
algorithm
how
the
ingress,
router
utilize
different
attributes
to
compute
the
index
to
choose
which
side
to
use,
there's
also
other
factors
to
be
considered
in
the
rtg.
K
So
basically,
that
drive
is
about
within
the
5g
that
gdp
tunnel,
they
use
udp
port
range
to
represent
different
priority
or
different
slicing
of
the
network,
and
those
information
can
be
passed
through
the
5g
network
exposure
function
to
the
local
ip
network
and
that
information
can
also
be
carried
by
the
pgp's
app
metadata
tlb
to
pass
to
relevant
routers
next
page.
Please.
K
Here
is
the
load
measurement
as
the
router
itself.
We
most
likely
applications
are
encrypted.
They
don't
give
us
information
about
the
internal
logic
and
from
the
plumbing
side
we
can
only
see
the
packets
going
into
the
router
going
to
the
server
and
coming
from
the
server
and
from
historic
data.
The
an
analytic
tool
will
be
able
to
measure
like
like
this
particular
hours.
K
K
Suppose
the
router
egress
router
have
the
information
so
for
load
measurement.
So
far
we
defined
two
types
of
load
measurement.
One
is
the
raw
measurement.
The
raw
measurement
can
be
useful
for
analytic
tool.
Like
suppose,
there
is
a
little
tool
attached
to
the
raw
reflector
and
that
need
the
raw
data
for
future
prediction.
K
Another
matrix
to
be
propagated
is
aggregated
index
so
that
suppose
all
the
routers
belonging
to
belong
to
same
provider.
They
can
have
the
same
algorithm,
for
example,
here
kind
of
waited
about
all
those
different
measurements,
they've
added
weight
together
to
come
up
with
the
aggregated
load
index
and
this
index
being
propagated
to
the
ingress
router
next
page.
Please.
A
A
K
K
Application
server
the
computing
services
can
expose
the
internal
logic
to
the
network
and
having
the
routers
in
the
network
to
be
aware
of
the
computing
resource
being
utilized
by
different
app
server
and
be
able
to
forward
it
appropriately.
So
those
kind
of
information
can
also
be
carried
by
those
app
metadata
path,
attributes.
Of
course,
they
may
introduce
some
new
subtleties
to
indicate
the
detailed
attributes
exposed
by
the
app
server.
K
K
K
A
B
Thank
you,
john
linda
one
question:
I'm
a
bit
worried
about
is
bgp
right,
like
transport
or
tool
for
sending
clothes
measurement
information,
because
information
about
particular
load
of
this
aggress
node
will
be
delivered
with
delay
right
handling
delay.
So
it
will
be
information
about
load
in
the
past,
and
my
concern
is
about
how
actual
this
information
will
be
to
make
this
change.
B
K
That's
a
good
question
so
here
we're
not
talking
about
transit
measurement,
we're
talking
about
historic
measurement,
so
you
are
talking
about
like,
for
example,
last
24
hours,
measurement
versus
last,
one
hour,
average
and
or
last
one
month
average.
So
it's
not
about
very
transit.
So
the
goal
is
really
to
estimate
the
load
measurement
compared
to
the
historic
data.
K
So
here
I'm
just
not
giving
the
specifics
on
how
actual
measurement
could
be
done.
It
could
be
that,
like
in
the
compute
first
network,
the
server
themselves
being
able
to
expose
that
they
could
use
other
information,
maybe
genevieve
header,
to
be
able
to
expose
the
internal
requirement
a
desire.
So
that
is
not
specified
here
here.
O
I'm
guessing
you
can
hear
me,
this
isn't
just
semantics:
it's
not
technical,
but
you
know
you
started
with
saying
edge
compute
and
I
see
multiple
ip
networks.
You
know
you
know
you
get
to
think
about
what
qualifies
as
edge.
You
know
if
you
go
across
multiple
isps
and
your
way
across
the
line.
Is
that
really
an
edge
compute?
So
I
think
it's
semantics,
I
I
know
I
looked
at
it
some
pages.
K
All
right,
let's
continue.
Okay,
so
in
terms
of
propagation
of
the
app
metadata
we
could
use
the
ifc
4684,
the
rt
constraint.
Distribution
only
distribute
the
information
to
the
relevant
routers,
because
if
you
look
at
those
services
like
edge
servers,
they
are
not
everywhere
and
also
that
not
every
ingress
or
psa
would
have
the
user
device
interested
in
those
services.
K
So
the
distribution
doesn't
have
to
be
broadcast
to
every
router,
since
there
are
many
more
much
more
numbers
of
edge
servers,
application
servers
than
like
rt
constraint
being
meant
for
for
the
routers
we
could.
Another
alternative
is
to
create
this
app
server
bug
group,
so
this
group
can
be
statically
configured
or
can
be
each
ingress.
Router
can
ask
for
the
network
controller,
who
are
the
ones
interested
in
this
particular
service,
also
need
a
time
to
live,
because
for
any
service.
K
K
K
I
want
the
service
to
go
to
e2
or
e3,
so
in
networking
we
have
done
a
lot
of
protection
right.
This
is,
can
be
achieved
by
assigning
multiple
addresses
into
one
app
server
we
can
achieve.
We
call
soft
anchoring
because
it's
not
specifically
anchored
to
our
r1
or
this
app
server.
The
way
to
achieve
that
is
we
create
for
this.
App.Net
will
create
a
group
of
anycast
addresses
g4,
being
the
address
which
not
relevant
to
the
location
is
not
location.
Preferred
l1,
address
is
preferred
to
be
anchored
to
r1.
K
L2
address
is
preferred
to
be
anchored
to
r2.
L3
address
is
preferred
to
be
anchored
into
r3,
so
with
different
cost,
and
the
network
can
be
able
to
consider
all
the
other
costs
like
network
delay.
There
could
be
site
capacity
index,
some
other
information,
all
consolidated
together
to
make
the
intelligence
decision
and
when
the
like,
for
example,
if
it's
anchored
to
r1
if
something
fail,
and
then
they
will
be
equally
distributed
by
r2
or
r3,
depending
on
the
other
factors.
K
P
P
K
K
Okay,
so
so,
if
you
look
at,
there
was
a
talk
at
the
nanak
a
couple
of
land
ups
ago
they
talked
about
using
any
cash
to
provide
for
all
their
services.
They
talk
about
like
they
can
change
the
cost.
They
can
change
the
peering
policy,
but
they're
talking
about
in
terms
of
month.
The
traffic
pattern
can
change.
So
that's
with
the
manual
intervention.
K
Q
K
Q
Yeah
yeah,
but
this
is
bgp.
You
cannot
use
your
own
algorithm.
You
have
to
be
compliant
with
the
existing
bgp
decision
processor.
Of
course
you
can
specify
a
new
standard
which
is
taking
into
account
additional
parameters
somewhere
in
the
existing
decision
process,
but
you
cannot
simply
do
something
else.
K
K
Oh,
oh,
okay,
yeah
yeah,
this
page,
so
the
the
goal
of
this
bgp
is
to
distribute
the
information
once
the
information
is
distributed
to
the
ingress
router
here
and
today
he
used
bgp
to
choose
appropriate
egress
router,
that's
all
true,
but
in
this
5gh
computing
environment,
the
the
ingress
router
is
part
of
the
up,
upf
or
psa
passion
packet
session
anchor,
and
he
will
not
only
just
use
the
network
routing
as
the
only
criteria
to
choose
the
egress
router.
He
has
to
consider
other
factors
because
different.
Q
I
completely
agree
with
you
linda.
My
point
is
just
because
you
are
using
bgp,
you
have
to
comply
with
bgp,
which
means
that
you
cannot
simply
override
the
current
decision
process.
You
can
insert
something
into
the
existing
decision
process,
but
you
cannot
bypass
it
completely.
Otherwise,
you
become,
you
have
a
non-compliant
bgp
implementation
and
if,
if
it's
the
way,
you
want
to
do
simply
don't
use
bgp
and
and
and
write
your
own
protocol.
K
K
In
addition
to
this
cost
matrix
from
r1,
it
may
need
other
factors
to
choose,
because,
for
example,
in
this
our,
for
example,
let's
just
talk
about
the
router
b
right,
but
rather
b
when
he
has
the
ue
traffic
coming
to
s1.
If
it's
original
ue,
he
would
choose
the
s1
closest
to
him,
based
on
the
routing
distance
or
other
conflict
matrix.
But
there's
when
there's
a
ue1
coming
from
5g
side
a
re-anchored
to
psa2,
then
this
particular
flow
need
to
go
to
prefer
to
stick
to
the
original
server.
K
Okay,
so
based
on
the
source,
he
may
need
to
forward
it
to
a
different
server
and
maybe
using
a
tunneling
or
maybe
use
the
sr
technology
to
forward
to
send
it
to
the
egress
r1.
So
the
decision
point
should
be
considered
that
that
not
only
just
the
matrix
themselves,
the
the
computer
cost
the
other
factors
to
be
considered.
Q
O
Much
yeah,
I
heard
the
comment
about
hours
linda.
I
wouldn't
make
a
blanket.
I
wouldn't
make
a
blanket
say
but
about
hours.
Think
about
you
know:
5g
is
not
one
use
case
and
you've
got
consumer,
you
have
enterprise
and
you
have
critical
services.
You
have
some
other
stuff.
So
if
don't
build
your
solution
out
that
the
you
know
the
measurement
is
going
to
be
in
hours
because
in
some
use
cases
that
won't
be
helpful.
So
just
keep
that
in
mind.
K
K
K
K
We
want
to
have
a
new
tunnel
type,
sd1,
hybrid
or
other
existing
tunnel
types
and
we
color
it
with
a
specific
color
extender
community
and
then
the
update
2
for
the
node
will
have
the
tunnel
egress
endpoint
to
describe
which
endpoint,
which
port
this
tunnel
ends
terminate
and
we'll
have
the
port
subtly,
which
include
the
isp
information
for
this
particular
one
port
like
whether
it's
from
company,
a
or
company
b,
would
include
geolocation
of
this
node.
Just
assume
that,
when
sd1
deployment
they
can
be
far
apart
in
different
countries
or
different
states.
K
The
lisp
has
this
septual
v
geo
location,
which
is
can
be
very
useful
to
be
included
and
also
optionally,
to
include
all
the
ipsec
sub
tods
episode.
Some
theory
can
be
tricky
because
episode
security
associations
are
pairwise,
meaning
every
node
between
two
every
node.
They
have
different
keys,
so
the
the
attributes,
as
defined
in
the
secure
evpn
you
can
see
is
there
are
many,
of
course
they
can
be
included,
but
also
we
could
include
security
essay
identifiers
which
is
pre-configured
as
well.
K
K
So
one
way
to
do
it
actually,
with
this
present
at
the
bath
yesterday,
we're
just
using
the
tunneling
attributes
with
the
new
tunnel
type
sd1
hybrid,
which
can
include
all
the
needed
information,
and
you
will
have
the
color.
You
will
have
the
detailed
endpoint
subtle.
You
will
have
the
ip
sub
tovs
or
ipsec
sa
ids.
K
K
K
K
K
So
with
the
sd-wan
survey,
just
to
make
the
implementation
easier
when
the
receiver
received
the
update,
the
color
hd1
color
will
be
applicable
to
all
the
paths.
All
the
tunnels
attached
in
this
update,
just
like
sr's
color
and
here
here
are
the
detailed
information
underneath
the
hybrid
sd1
tunnel
type
next
page
for
the
savvy
sd1
sappy,
we'll
have
two
two
types:
one
is
assuming
that
sd1
deployment
is
managed
by
one
single
company
or
all
their
locators
can
be
represented
by
a
local,
significant
identifier.
K
Another
type
is
for
a
large
deployment
where
you
would
require
the
geo
geolocation
sub-glv
to
be
included
to
uniquely
identify
the
location.
The
geolocations
sub
tov
is
from
the
lisp
geolocation
draft.
You
have
a
local
id
port
id
like
suppose
that
you
may
have
a
group
of
cpes
there.
They
may
have
a
local
significant
number
to
represent
different
port
number,
so
that's
has
a
local
id
and
then
you
have
a
coloring
which
represents
the
common
properties
shared
by
all
the
tunnel
attributes
next
page,
please.
