►
From YouTube: IETF110-EMU-20210308-1200
Description
EMU meeting session at IETF110
2021/03/08 1200
https://datatracker.ietf.org/meeting/110/proceedings/
A
At
our
scheduled
start
time,
welcome
to
the
emu
working
group
meeting
at
ietf,
110,
I'm
joe
salloway
and
mohit
is
also
here.
As
a
co-chair.
I
want
to
thank
everybody
for
attending
this
meeting
in
whatever
time
zone
you
happen
to
be
in
first
thing:
we'll
do
we'll
spend
just
a
few
short
moments
on
the
note.
Well,
I
think
most
people
are
probably
aware
of
it,
but
we'll
leave
it
here,
so
you
can
take
a
look
at
it
to
understand
the
ipr
policies
of
the
ietf.
A
A
A
A
E
Yeah-
maybe
I
can
so
so.
Some
discussion
has
been
going
on
on
some
specific
issues.
If
beza
is
on
the
call,
he
might
actually
be
able
to
give
a
more
detailed
summary
if
we
want
to
go
in
the
details.
But
but
the
short
summary
is
that
discussion
has
been
ongoing
and
some
things
have
been
fixed
on
their
side
and
our
side,
and
they
have
also
wanted
to
have
a
call
to
discuss
this
on
march
17th,
and
we
can
send
some
of
the
call
parameters
to
the
list
after
this
call.
A
A
F
F
F
The
short
summary
is,
it
should
be
pretty
straightforward
to
add.
Tls
1.3
support
with
minimal
code
changes,
presuming
that
the
tls
layer
is
already
abstracted
out.
So
for
the
free
radio
side
it
was
no
more
than
100
line,
200
lines
of
code
just
to
tweak
some
things.
The
main
issue
is
eep,
tls
is
relatively
straightforward.
F
F
So
if
we
go
to
the
next
slide,
so
things
like,
especially
in
open
ssl,
a
lot
of
the
api
calls
are
configuration
allow
this
versus.
Do
it
now,
so
you
it
is
basically
impossible
in
open,
ssl
one
to
actually
send
a
new
session
ticket.
When
you
want
to
send
it,
you
can
just
say:
allow
zero
one,
two,
three
whatever
and
open
ssl
at
some
point,
perhaps
when
it
decides
we'll
send
those
session
tickets.
F
F
F
So
the
the
hope
is
before
we
get
this
published
that
more
than
a
couple
of
implementers
look
at
this
and
sign
off
on
it.
I'm
not
sure
what
tls
library
apple's
using
historically
it
was
open
ssl.
I
think
they
swapped
to
their
own
one,
so
that
may
come
with
more
implementation
issues
as
with
cisco
next
slide,
so
we
tested
both
the
close
notify
and
one
application,
octet
data
or
one
octane
application
data.
So
these
are
client
and
server
configurable
flags.
F
The
application
data
is
preferred.
It
generally
seems
to
be
not
just
easier
to
implement
as
noted
here,
but
it
seems
to
fit
the
the
state
machine
model
better
right,
overloading
tls
signals
to
mean
eep
state
seems
a
little
imperfect.
I
guess,
and
the
feedback
from
the
tls
working
group
was
that
using
the
application
data
to
signify
tls
state
changes
was
also
wrong,
but
if
we're
instead
using
the
application
data
to
signal
beep
state,
that
seems
more
in
line
with
everyone's
concerns,
so
the
key
exporters
are
still
dash
13.
F
F
F
D
D
But
at
least
in
some
cases,
openssl
provides
features
which
other
libraries
currently
don't
and
I'm
not
even
sure
if
they
are
planning
to
add
them
in
the
future-
and
I
know
like
wps
applicant,
for
example,
provides
some
way
of
using
wolf,
ssl
ins
instead
of
open
ssl.
Obviously
it
doesn't
have
all
the
features
so,
for
example,
on
this
number
of
session
tickets-
one
worry
I
have
is
I
I
actually
agree
with
you
that
in
most
cases,
just
issuing
one
ticket
makes
sense.
D
It's
more
like
for
the
web
scenario,
where
you'd
want
to
issue
more
tickets.
But
it's
it's
something
that
I'm
afraid
some
libraries
don't
even
allow.
So,
at
least
on
the
github
issue
that
we
are
discussing
in
iftls,
which
is
issue
48,
I
posted
a
link
to
boring
ssl,
for
example,
where
the
library
has
hard-coded
two
tickets.
D
Obviously
you
could
change
that
to
one
and
recompile
the
library,
but
it
takes
some
effort
so
and-
and
we
can
come
back
to
the
exact
exact
wording,
but
maybe
something
along
the
lines
of
should
issue
one
session
ticket
or
and
and
not
going
with,
must
might
make
sense.
I
don't
know,
what's
your
opinion
on
that.
F
It
really
is
a
hard
question
to
figure
out
exactly
where
that
boundary
is
between
implementation
support
and
theoretical
behavior.
Practically
speaking,
openssl
3
won't
be
released
for
a
while,
even
when
it
is
released.
I
don't
expect
many
of
the
open
source
operating
systems
to
upgrade
to
it,
because
it
has
api
changes.
It's
mostly
compatible,
but
it
has
api
changes
and
require
requires
additional
application
work
so,
realistically
speaking,
we're
stuck
with
openssl
one
for
the
foreseeable
future.
G
F
Sure
I
mean
it's
one
of
these
things,
what
whatever
works?
The
other
question
is,
and
this
is
more
policy
but
is
related.
What
do
you
do
about
resumption
across
different
media?
So
if
you
have
wi-fi
and
wired
both
configured
for
eep,
should
you
be
allowed
to
resume
across?
That
should
be
you'd
be
allowed
to
use
the
same
session
ticket
everything,
including
5216,
and
everything
else
in
eep
is,
is
completely
silent
on
this
topic
and
that
is
related
to
the
number
of
session
tickets.
F
F
Yeah
and
the
the
related
issue
is,
you
know,
because
the
application
is
not
really
in
control
of
when
those
session
tickets
get
sent,
there
may
be
early
session
tickets
sent
before
the
tls
finished,
which
are
then
not
usable
and
they're.
Only
implicitly,
not
usable,
there's,
no
explicit
hey
by
the
way
the
session
ticket
I
sent.
You
doesn't
work
so
now
you
have
to
add
more
code
to
the
client
side,
saying:
oh,
I
got
a
session
ticket
before
the
tls
finished.
G
F
H
Hi,
I'm
the
implementer
from
microsoft.
I
think
the
the
main
issue
that
alan
is
speaking
about
with
early
session
tickets
is
mainly
before
the
client
certificate
is
validated
by
the
server.
So
any
session
tickets
sent
before
that
are
valid
in
tls,
but
you
would
not
want
to
actually
accept
those
if
the
eep
negotiation
is
failing,
because
the
client
certificate
is
rejected,
and
so
both
clients
and
servers
need
to
have
some
awareness
that
that
can
happen.
F
Yeah-
and
this
was
a
source
of
issues
in
the
past-
is
one
of
these.
No,
I
can't
help
but
feel
at
least
partially
responsible
for
the
software.
I
wrote
where
openssl
would
cache
these
session
tickets
by
default,
send
them
out
whenever
and
then
it
was
possible
using
eeptls
or
peep
for
the
client
to
start
the
tls
session
not
send
the
password
get
the
session
ticket
hang
up
and
then
resume
that
session,
because
of
that
internal
tls
cache
in
openssl.
F
So
as
an
application
using
openssl,
we
have
to
jump
through
all
kinds
of
hoops
to
say:
oh
no,
no
openssl!
Don't
do
that
and
then
there's
all
kinds
of
ordering
issues
of
you
know.
Openssl
wants
to
do
something
and
we
have
to
catch
it
and
stop
it
and
cash
in
our
internal
cash
for
later
so
yeah
it's.
It
is
definitely
an
issue.
F
Other
implementations-
I
I
haven't
seen
it
I'll
I'll.
Let
george
speak,
I
don't
think
he's
seen
it
either,
but
it
does
seem
to
be
at
least
in
our
our
interop
testing.
It
does
seem
to
be
allowed
and
the
open
ssl
code
is
not
at
all
clear.
So
what
openssl
does
is
something
that
I
tend
to
run
away
from.
F
Pls
was
pls
is
rather
a
lot
simpler
and
straightforward,
and
this
is
you
know
to
reference
rory's
comments
about
fighting
with
with
opens
to
sell
yeah,
it's
impossible
to
say:
please
send
a
session
ticket
now
you
can
either
send
zero
tickets.
One
tickets
two
three
four,
but
you
have
absolutely
no
control
over
when
they're
sent,
and
you
would
hope
that
if
you
said
hey,
please
don't
send
any
session
tickets.
Oh
now
the
session
is
established.
F
F
But,
as
I
was
saying
earlier,
that
is
not
in
open
ssl,
one
which
is
effectively
what
we
have
to
live
with
for
the
first
for
the
foreseeable
future
and
to
address
john's
commentary.
Sorry
mo
he's
coming
to
think
about
host
ap
yeah.
They
have
three
or
four
tls
implementations,
open,
ssl,
wolf
ssl.
They
have
their
own
internal
tls
implementation,
but
the
functionality
there
is
relatively
limited.
I
Hello
watson
lad
cloudflare
all
right,
it
looks
like
it
went
through
great.
I
just
wanna
comment
if
you
are
building
around
openssl
specifically
and
changing
your
standard
modified,
please
don't
because
what's
happening
here
is
the
terrible
design
of
openssl
is
influencing
these
standard
choices
and
ends
up
restricting
what
tls
can
do
and
then
slowing
the
adoption
just
bad
for
the
whole
ecosystem.
G
I
F
F
So
the
the
decision
here
is
how
little
can
we
change
the
standard
or
the
recommendations
to
allow
the
standard
to
be
implemented
with
openssl
one
without
breaking
things
too
much?
Some
of
this
may
be
as
simple
as
recommending
that
you
know
you
just
write
more
code
to
work
through
all
these
other
states
and
say
that
all
these
other
states
are
possible.
Wave
your
hands
due
to
tls
library
issues
and
tls.
1.3
is
a,
as
I
was
saying
earlier,
is
a
substantial
change
from
tls
1.2,
and
so
it
may
just
be
hey.
F
If
you
get
something
keep
the
tls
conversation
going,
even
if
you
get
a
packet,
even
if
you
get
tls
finished,
you
act
that
you
get
a
session
ticket
all
alone.
When
you
expect
application
data,
it's
still
negotiating.
You
should
still
continue
sorry
about
this.
It
really
shouldn't
happen,
but
that's
it
same
thing
with
you
know
the
number
of
session
tickets.
If
you
can't
control
when
they
get
sent
out,
you
know
pick
one
that
comes
out
after
the
client.
Certificate
has
been
verified
as
jorge
was
noticing
or
noting,
throw
the
rest
away.
F
F
I
I
do
not
recommend
breaking
standard
in
order
to
work
with
openssl.
I
do
recommend
making
sure
that
there's
enough
information
in
the
standard
that
implementers
can
work
with
both
openssl
and
other
implementers
who
choose
to
use
openssl
without
going
through
all
kinds
of
code
spelunking
into
internals.
A
All
right,
so
if
we
have
any
other
implementers
on
the
call,
it
would
be
great
to
get
more
participation
as
much
as
we
can
in
implemented,
implement
interop
events.
So
we
can
work
out
issues
like
these
with
other
tlf
libraries
as
well.
I
think
it'll
be
good
for
obviously
for
epls
community
and
I
think
it'll
be
helpful
for
the
tls
community
as
well.
G
G
My
hope
is
that
we
can
hopefully
reach
see
that
there
is
rough
consensus
on
some
of
these
things,
and
then
we
can
close
these
issues
and
maybe
submit
the
version
15,
which
might
not
be
the
final
version,
but
at
least
we
have
something
submitted
to
work,
and
then
we
can
agree
what
we
don't
have
consensus
and
what
needs
more
work
yeah.
So
next
slide.
G
G
G
G
So
here
are
the
major
technical
changes
that
was
suggested
by
the
idf
last
call
directorates
and
mainly
iesd
and
ben's.
Discuss
and
ben's
discusses
was
partly
based
on
input
from
the
tls
working
group.
So
major
change
was
change
from
application
data
to
close
notify
suggestion
to
update
the
key
duration
to
be
more
modern
with
different
labels,
as
well
as
using
type
code
appended
to
the
labels
instead
of
in
the
context,
and
these
changes
may
or
may
not
have
working
group
consensus
at
this
part
of
the
consensus
call
that
you
started.
G
No,
I
think
the
key
derivation
will
be
this
guy.
The
label,
the
con
use
of
context
or
label
will
be
discussed
on
the
next
slide,
the
other
two
things
I
don't
have
any
specific
slides
for
so
this
would
be
the
case
to
discuss
the
use
of
labels
more
labels
at
all
and
the
application
data
versus
close
notified.
A
D
A
G
G
So
discussion
is:
does
it
make
sense
to
have
have
the
old
where
the
type
code
goes
into
the
context
or
the
zero
14
version
where
it
goes,
is
appended
to
the
labels
and
and
no
context
context
is
mixed
up
here
should
be
the
opposite
order.
There
was
also
a
recent
comment
by
alan
on
the
on
the
list
that
is
pre,
adding
things
to
the
labels
or
going
against
the
ayanna
register,
and
that
this
should
be
consulted
with
tls.
A
Yeah,
as
far
as
the
you
know,
I
I
think
it
is
a
little
bit
problematic
to
include
them
in
the
label
for
the
inr
registry.
I
think
for
epls
you
would
you
could
easily
specify
that
the
type
code
would
be.
I
think
you
say
it's
a
heck
so
0d
or
something
like
that,
and
that
would
be
the
label
registered
with
iana.
D
D
D
G
F
In
terms
of
you
know,
the
tls
review
per
mo
eats
comments
that
the
context
should
be
session
information.
The
the
simple
pushback
there
is.
There
is
no
session
information
in
eep
right
because
eve
can
go
over
ppp
802
on
x.
You
know
anything,
there's
there's
pana
collab
now,
apparently
there
is
no
session.
F
G
I
agree,
I
think,
that's
the
best
solution.
That's
why
we
had
that
solution
from
the
beginning.
Do
we
know
if
we
can
get
that
past
ben's
discuss,
or
should
we
try
to
do
that?
That's
also
what
have
been
tested
in
the
hackathon.
I
guess
so
should
we
try
to
go
for
the
context
again
unless
ben
says
that
this
is
not
okay
and
then
we
go
for
different
labels.
A
B
A
F
Yeah,
I
know
no
one's
implemented
the
type
code
in
the
label
that
that's
not
done,
there's
no
configurable
flag
for
that
and,
realistically
speaking,
it's
not
huge
amounts
of
code
to
change
it.
It's
just.
Why
have
an
unused
field
and
then
make
your
life
more
complicated
when
you
can
just
use
a
field?
That's.
A
There,
okay
yeah,
so
we'll
probably
want
to
check
to
you
know.
Obviously
we
don't
want
the
block
document
blocked
on
this,
but
it
seems
at
least
from
the
list
and
and
from
this
discussion
here-
that
going
with
the
type
code
in
the
context
would
be
the
preferred
approach
and
it,
but
it's
not
something
that
is
a
blocking
issue
if
we
had
to
change
it
for,
for
some
other
reason,.
G
So
these
are
two
pull
requests
based
on
the
these
are
based
on
the
isd
and
the
previous
comments
that
we
didn't
miss
to
put
into
14..
So
it
was
several
comments.
How
this
document
relates
to
alan's
documents
on
tls
types,
so
now
to
this
has
been
added
as
a
reference
and
in
two
sections,
both
in
the
beginning
and
in
the
key
derivation
then
also
a
comment
that
these
message
flows
how
they
relate
to
earlier
versions.
So
it
has
been
added
that
is,
example,
message,
flows
specific
to
tls103.
G
A
G
Good
so
45,
so
this
is
related
to
new
session
tickets.
This
was
a
lot
of
discussion
during
alan's
comments,
so
this
no.
So
this
is
yeah.
This
is
clear.
Some
guidance
by
resumption
is
needed
and
also
some
where
the
new
session
ticket
can
be
sent.
So
there
was
a
lot
of
discussions.
Why
you?
Why
do
you
need
resumption
at
all
and
what
is
beneficial
for-
and
conclusion,
I
think,
is
that
resumption
is
very
beneficial
in
etls,
due
to
the
number
of
due
to
packet,
fragmentation.
G
G
G
Then
there
was
comment
from
alan
that
we
should
have
much
more
guidance,
and
this
text
in
green
here
was
what
was
suggested
on
the
issue
in
github.
I
think
I
been
worried
you
I
don't
remember
so
that
is
that
they
should
take
into
account
that
fewer
new
session
tickets
will
likely
be
needed
for
etls
and
in
most
cases
the
single
new
session
ticket
will
be
sufficient.
G
G
G
G
A
Okay,
yeah.
I
think
this
is
going
to
probably
take
a
little
bit
more
discussion,
especially,
I
think
the
what
became
a
little
clearer
to
me
in
allen's
implementation
report
was
that
there
are
problems
potentially
with
implementation,
sending
new
session
ticket
early.
I
I
have
to
go
back
and
look
at
the
tls
1.3
spec,
because
I'm
not
sure
if
that's
a
valid
thing
to
do,
because
I
thought
the
resumption
key
was
derived
from
both
the
client
and
the
server
finished.
G
D
What
remains
is
how
do
we
then
like
schedule
when
this
new
session
ticket
is
sent
because
in
in
in
the
web
scenario
like
there
is
very
rarely
any
client
authentication,
whereas
in
epls
predominantly
there
is
client
authentication.
So
you
would
want
to
issue
session
tickets
only
after
receiving
the
client
certificate
and
verifying
it,
and
if
libraries
currently
don't
allow
you
to
like
pick
an
appropriate
time
when
to
send
that
new
session
ticket,
then
that
also
needs
to
be
documented.
F
Yeah
helen,
for
me,
that's
real
yeah.
It
really
just
needs
to
be
documented,
as
here
be
dragons
right.
Otherwise,
what
happens
is
you
know
jorge,
and
I
and
various
other
people
working
on
host
ap
have
just
been
beating
our
heads
against
this
for
months.
Exactly
what
does
the
tls
layer
do?
How
do
you
control
it?
It's
it's
best
to
write
all
this.
You
know
interoperability,
hackathon,
report
stuff
down
and
go
by
the
way
with
tls
one.
Three
almost
anything
can
happen
and
you
have
to
be
aware
of
it.
Sorry.
A
A
Okay,
any
other
comments
on
new
session
ticket.
I
think
there's
a
we.
I
think
we've
made
progress
on
the
issue
of
how
how
many
session
tickets
need
to
be
sent.
I
think
that
we
can
give
clearer
guidance
there.
I
think
the
issues
of
the
ordering
of
the
tickets
and
the
how
those
are
handled
is
still
open
issues
that
need
to
be
resolved.
A
Yeah,
it's
a
good
point.
I
also
posted
to
the
list.
I
don't
know
if
we
had
done
that
previously.
I
can't
remember,
but
I
did
post
where
the
repository
is
in
github
and
it's
a
vassal
authors
to
use
pull
requests
so
that
we
can
track
the
issues
better
going
into
the
document
and
having
comments
in
the
github
are
is
is
good.
G
G
Then
there
has
been
a
discussion
on
guitar.
I
think
the
conclusion
is
that
the
tls
is
quite
it's.
I
think
this
academic
paper
about
protected
failures
was
they.
They
tried
to
focus
too
narrowly
on
one
attack,
but
there's
basically
any
number
of
other
attacks
that
do
the
same
thing.
Basically,
any
package
you
send
to
tls
makes
it
fail.
So
there's
basically
nothing
we
can
do
here,
but
that's
probably
acceptable,
because
you
can
always
try
to
connect
again
and
there's
a
comment
from
you
one.
So
these
two
have
been
added
to
the
pull
request.
G
G
J
D
F
This
is
alan.
I
I
think
for
me
the
main
purpose
to
have
protected
failure.
Is
it's
it's
generally
good
to
protect
your
your
application
signaling,
but
the
only
thing
I
really
care
about
is
that
the
errors
get
back
to
the
end
user
and
administrator
and
protecting
them
seems
to
make
that
they
make
the
correct
errors
go
back
right,
so
you
get
you
know,
certificate
expired
or
whatever,
rather
than
the
ubiquitous
failed,
and
now
nobody
knows
what
to
do
or
how
to
fix
it.
F
K
Guys,
thanks
for
the
opportunity
to
comment-
and
I
think
this
is
okay-
just
to
allen's
point
anytime,
you
say
errors
get
back
to
users,
be
careful
with
that
one,
because
there
might
not
be
a
user
on
at
least
one
end
of
the
connection.
And
and
if
that's
your
goal,
we,
you
know
it's
it's
a
deep,
deep
rabbit
hole
which
I
don't.
F
K
K
A
C
G
Good
then,
next,
so
here's
an
issue
that
I
opened
so
tls
working
group
has
decided-
or
at
least
they
have
adopted,
rfc
8446.
This,
which
changes
the
terminology
for
tls,
1.3
and
tls
1.2,
and
this
terminology
change
is
to
remove
master
everywhere
and
replace
it
with
main
and
where
master
was
not
really
needed,
it's
just
removed.
G
G
G
Yeah
and
then
comment
on
github,
I
think
from
you
that
user
cancel
behavior
needs
to
be
clear.
When
we
talk
about
error-
and
I
agree
problems
with
this-
is
we
probably
need
to
wait
on
the
consensus
for
protected
indication,
success
of
failure
before
writing
something
about
user
cancelled
and
then
the
use
of
user
cancel
in
tls
103
is
unfortunately
unclear.
G
C
G
G
And
this
references
three
seven,
but
but
only
in
the
info,
it
references
it
describes
how
you
would
implement
according
to
4137.
But
as
this
is
an
informal
document,
it
tries
to
not
make
it
normative
to
follow
four
one.
Three
seven,
even
it
seems
that
my
understanding
now
is
that,
basically,
all
implementations
are
following.
D
J
Bernard
yeah-
and
this
is
probably
more
of
a
question
for
alan
and
jorge,
but
given
the
issues
in
the
tls
libraries
about
sending
a
closed
notify,
are
you.
It
seems
like
that.
The
question
is
closed,
at
least
for
you
guys,
or
am
I
interpreting
that
correctly-
that
it
really
has
to
be
the
application
data,
because
you
can't
get
the
close
notified?
You
can't
control
it.
F
From
most
of
the
issues
is
from
my
side
and
open
ssl
I'd
say
it's
an
open
question
right.
I've
had
my
my
guys
looking
into
this
and
it's
one
of
these.
You
know
tell
openssl
not
to
do
a
quiet
shutdown
where
it
just
closes
the
connection
and
doesn't
send
close
notify,
so
it
should
be
sending
the
close
notify.
F
We
say:
please
shut
down
the
tls
connection,
it
appears
to
we
say:
is
there
data
available
to
send
to
the
other
end,
and
the
answer
is
no,
so
the
question
is:
are
we
using
the
openssl
api
incorrectly
or
is
openssl
1
just
completely
broken
here?
I
I
don't
know
enough
to
say
what
I
do
know
is
sending
the
one
byte
of
application
data
is
a
well-tested
code
path,
not
just
for
eep
because
of
peep
and
ttls,
but
for
tls
in
general.
G
Down,
I
personally
think
application
data
seems
like
the
most
logical
choice
now
when
we
are
talking
about
protected
success
and
not
commitment
to
not
send
more
handshake
question,
do
we
know
that
application
data
will
work
with
all
the
other
e
methods
and
do
we
know
if
application
data
will
pass
ben's
discuss?
I
don't
think
I've
seen
a
clear
answer
on
that,
but
I
assume
ben
would
not
have
a
problem
with
application
that
that
data
has
a
predicted
success.
F
G
D
I
think
we
should
just
put
this
in
15
with
application
data,
and
you
know
this
will
go
back
to
the
the
new
isd
that
gets
seated
and
we
will
see
my
feeling
is
if,
if
I
understood
ben's
previous
review
was
that
it
was
mostly
because
we
were
using
it
as
a
commitment
to
no
more
both
handshake
messages
that
was
causing
the
problem
and
using
it
as
a
success.
Indication
should
be
fine
and,
and
it
should
pass
through
the
iesg,
so
I
don't
think
we
should
wait
for
that.
A
Yeah
so
yeah,
I
think,
unless
I
I
think
for
me,
we
we
have
interoperable
implementations
with
application.
Data
and
closed
notified
seems
like
even
if
we
can
get
it
to
work,
there's
a
little
bit
of
question
as
to
how
much
control
you
all
have
over
that
message,
and
I,
I
also
think
that
you
know
the
iesg
comment
is
something
that
was
more
on
it.
The
way
it
was
phrased
to
be
a
control,
how
tls
was
behaving
than
how
he
was
behaving,
so
I
think
yeah.
A
A
E
G
I
think
this
was
raised
by
martin
thompson
and
you
and
I
think
it
seems
to
be
consensus
that
no,
if
more
in
additional
information
is
needed
in
the
key
derivation,
whoever
it
seems
to
be
consensus
that
the
text
in
rfc,
521,
6
is
lacking
and
that
more
guidance
is
is
needed,
and
this
is
currently
only
an
issue.
There's
no
pull
request.
G
G
G
G
G
F
F
Neither
neither
the
epir
nor
the
server
side
put
maximum
limits
in
the
supported
tls
version
and
those
definitely
caused
deployment
issues.
So
my
two
sensors.
We
have
no
idea
what
tls
1.4
is
going
to
do
so.
This
document,
based
on
past
pain,
should
suggest
that
we
do
tls
1.3
and
everybody
forbids
tls
1.4
until
such
time
as
we
know
that
what
that
means.
D
Well
about
this
tls,
1.3
or
higher
at
least
I'll,
have
to
double
check.
If
I'm
quoting
rob
correctly
from
his
isg
review,
he
was
also
saying
that
the
previous
epls
document
was
not
tied
to
a
specific
tls
version,
and
why
is
this
document
specifically
tied
to
tls
1.3,
of
course,
knowing
that
none
of
us
are
at
least
I
don't
know
what
tls
1.4
would
look
like.
Maybe
it
has
all
sorts
of
post
quantum,
magic
and
whatnot,
and
maybe
we'll
have
to
do
everything
in
etls
from
scratch.
D
But
if
1.4
is,
is
you
know
similar
or
exactly
with
minor
modifications
to
1.3?
Maybe
we
won't
require
another
update
to
the
epls
document
and
it
should
be
independent
of
the
dls
version.
I'm
not
saying
I
have
strong
opinions
on
on
this,
but
I
also
see
rob's
point,
at
least
from
his
isd
review,
that
maybe
we
can
leave
it
open
and
if
there
is
a
dramatic
change
in
the
next
tls
version,
we'll
we'll
revisit
and
update
or
obsolete
this.
G
I
agree
with
allah
that
or
higher
should
be
removed,
because
we
don't
know
how
tls
1.4
or
2,
but
top
0
will
look
like,
but
I'm
I
would
prefer
to
keep
it
open,
just
writing
me
and
that
we
don't
know
how
this
will
work
with
with
future
versions.
Rfc
5216
works
quite
well
with
three
different
versions
of
tls
before
it.
I
G
Yeah,
I
think
it
has
been
during
this
work.
There
has
been
very
different
comments
on
what
epls
should
be.
We
have
having
comments
that,
if
tls
should
not
specify
anything
about
the
tls
version
at
all.
Yes,
the
interfaces
between
tls
and
103,
and
then
we
have
comments
from
implementers
that
need
to
specify
very
much.
Otherwise
it
will
be
security
issues
yeah.
K
Elliot
yeah,
so
I
think,
there's
I
think,
mohi
you
just
captured
it
right
that
that
that
is
definitely
where
I,
where
I
see
things
as
well.
What
I
was
going
to
say,
though,
was
that
I
think
one
of
the
things
that
should
come
out
of
this
document
is
a
bit
more
participation
in
the
tls
working
group
from
non-web
users
of
tls.
K
K
Don't
forget,
don't
forget
about
us
the
next
time,
maybe
even
a
short
document.
If
somebody
wants
to
write
it
and
I'd
be
willing
to
help
along
those
lines,
because
I'm
sort
of
waiting
in
the
wings,
because
you
know
I've
got
another
document,
that's
sort
of
going
to
have
to
track
what
you
guys
are
doing
here
and-
and
I'm
just
you
know,
scared
you
know
quite
a
bit
well,
I
was
going
to
say
another
a
word
I
shouldn't
say
here,
but
I'm
I'm
rather
scared
about
how
I'm
going
to
proceed
with
that
document.
K
A
F
Yeah,
so
I
you
know
I'll
go
back
a
while
and
say
that
in
fact,
the
key
exporters
in
tls
were
defined
coming
out
of
the
needs
of
etls
going
back
to
gosh.
I
think
it's
25
16.
I
don't
remember
on
the
original
epls
doc
reached
into
the
internals
of
tls
and
and
mucked
with
it
in
order
to
do
what
etls
needed
realistically
practically.
I
think,
if
you
know
tls
call
it
plus
one
doesn't
change
the
key
exporters
or
if
it
doesn't
change
the
key
exported
apis,
we're
probably
mostly
okay.
F
K
F
A
Well,
I
think
tls
1.3
made
some
fundamental
changes
to
the
protocol
that
were
kind
of
in
order
to
reduce
round
trips,
and
things
like
that
that
you
know
were
on
were
sort
of
unavoidable
in
the
design
that
were
going
to
cause
this
type
of
problem,
and
we
should
have
do.
We
certainly
should
have
done
better,
probably
in
keeping
the
two
groups
in
sync,
especially
since
you
have
a
chair
between
the
two
groups,
but
that
didn't
happen
as
well
as
we
would
have
liked.
G
J
G
Yeah
any
any
guidance
here
how
to
improve
security,
for
this
would
be
very
helpful.
I'm
not
against
that.
I
think
that
these
documents
add
peer
authentication.
I
think
it's
not
correct,
but
any
guidance
on
this,
maybe
someone
can
suggest
something
based
on
seems
like
this
is
sounds
like
this
is
security
problems
that
are
known
and
what
to
do
with
them.
G
G
F
G
G
G
F
I
think
in
the
end,
tls
can
probably
just
rely
on
the
tls
layer
to
say:
hey,
you
have
session
tickets,
whatever
magic
goes
on
in
tls.
This
session
has
been
authenticated
and
has
been
tied
to
a
previous
user
session.
It
just
seems
to
me
that
there's
no
real
benefit
to
using
this
encrypted
tls
sk
identity
in
the
eep
identity
field.
F
I
I
So
if
you
resume
a
session
and
you
don't
store
the
client
certificate,
you
don't
have
it
in
the
resume
session,
and
so,
while
it's
true
that
the
that
the
you
have
some
way
of
of
storing
this
in
the
ticket,
so
it
might
not
always
be
possible
depending
on
what
implementation
is
doing.
How
they're
hooking
in
dope
is.
I
suspect
that
this
is
part
of
the
part
of
the
issues
that
we're
seeing
with
with
session
tickets.
G
G
I
think
we
open
an
issue
for
this
identity.
Then
next
bullet
is
defines
key
exporters
for
tl
other
tls
base
the
methods,
the
working
group
order
document,
which
covers
this
topic,
except
as
working
group
document.
Prior
to
these
changes,
I
don't
think
this
document
specifies
key
exporters
for
other
methods.
I
think
it
specifies
a
key
exporter
for
eptls
1.3.
I
G
F
G
A
All
right
great,
I
think
we
should
open
up
github
issues
for
most
of
these
or
the
ones
that
we
still
need
to
have
more
discussion
on
which
I
think
is
most
of
them,
and
then
I
think
we
can.
I
think
most
of
these
will
be
relatively
straightforward
to
resolve
a
couple
of
them.
Maybe
take
some
more
discussion,
all
right.
F
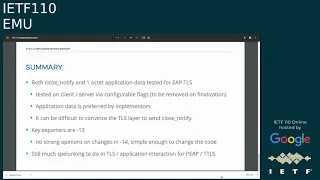
In
short,
things
mostly
work
resumption
is
easy,
open,
ssl
is
horrible,
and
the
question
is:
what
text
do
we
put
in
to
go?
Hey
would
like
to
fix
open
ssl,
but
we
can't
so
here
are
the
corner
cases
that
you
have
to
worry
about
and,
as
jorge
was
noting
earlier,
these
these
corner
cases
are
specific
more
to
peep
and
ttls
than
to
etls,
which
seems
to
be
pretty
much
okay.
At
this
point,.
A
One
of
the
things
I'd
like
to
see
is
is
more
discussion
on
this
particular
document
and
the
other
eat
methods
as
we're
going
through
these
ftls
issues,
because
these
these
discussions
may
have
implemented
implications
on
these
other
documents.
It
would
be
good
to
get
those
out
now
so
that
we
can
get
this
document
maybe
out
at
the
same
time,
or
at
least
shortly
following.
A
A
A
E
Yes,
all
right,
so
this
is
the
beast
document
for
37.48,
which
was
published
17
years
ago,
and
you
can
see
the
obviously.
The
draft
is
in
the
iotf
directories,
but
you
can
see
the
difference
to
the
original
rfc
in
this
our
code.com
link
and
if
you
go
to
the
next
slide,
so
what
are
we
about
to
do?
Well?
The
first
thing
is
that
you
should
not
panic,
we're
not
doing
something
horrible
here,
there's
nothing
fundamentally
wrong
with
the
existing
rs.
It's
it's
pretty
good
and
we're
also
not
changing
the
protocol.
E
E
E
The
authors
of
this
particular
update
thought
that
it
would
be
a
good
idea
to
change
one
or
two
of
the
terms.
I
will
talk
about
that
in
a
bit.
We
could
update
the
references
and
I
guess
overall,
there's
nothing
earth
shattering
here.
We
could
go
on,
but
there's
opportunities
to
clean
up
and
provide
more
information.
E
You
can
think
about
this.
Like
the
you
know,
your
car's
a
yearly
maintenance
and
if
you
didn't,
do
the
yearly
maintenance
in
17
years,
there's
quite
a
few
dents
in
the
car
that
you
know,
maybe
you
should
have
fixed,
and
some
of
that
might
actually
give
you
some
headache
next
slide,
please
so
the
specific
updates-
and
I
I
don't
want
to
spend
too
much
time
on
any
any
of
these
balls-
let's
very
briefly
mention
what
what
this
is
about.
So
there's,
actually
one
errata,
a
minor
thing,
that's
fixed
here.
E
A
bigger
thing
is
that,
like
obviously,
we
know
now
more
about
the
various
eap
methods
and
some
of
the
algorithms,
so,
for
instance,
there's
some
text
on
md5
and
so
on
and
and
the
issues
with
that.
We
also
point
to
the
newer,
newer
methods,
because
we
felt
that
that's
reasonable.
We
added
one
security
claim.
That's
remember
this:
a
set
of
security
claims
requested
for
for
all
methods.
We
added
one
I
could
discuss
if
that's
the
right
one
or
if
other
other
things
could
be
added,
but
we
did
add
one.
E
E
So
there's
some
open
questions
as
well
likely
you
could
say
more
about
security.
We
did
not
make
a
full
listing
of
all
the
attacks
and
everything
that
that
we've
learned
since
then
that
that
might
actually
be
a
useful
exercise
and
also
since
we
do
have
some
of
those
other
documents,
part
of
the
core
eap
specifications.
It
might
be
that
some
parts
of
this
document
could
be
thinner
and
point
to
those
other
other
rfcs.
E
The
ieee
references
and
discussions
are
fairly
dated.
I
felt
we
felt
I
could
probably
update
that
and
finally
there's
a
comment
around
passwords
and
passphrases
in
general
for
all
eap
methods
and
they
point
to
sassoprep
and
some
of
these
international
characters
at
issues
and
that
reference
is
like
very
old
and
it's
been
updated,
two
or
three
times
to
newer
rfcs,
and
I
did
not
at
least
know
what
to
do
with
this.
I
don't
know
if
the
old
rfc
still
is
valid.
E
J
J
Usually
well,
I'm
not
sure
that
usually
what
you
do
right
for
the
standard
process
is
you
try
to
document
that
everything
has
two
implementations
or
more
and
potentially
find
areas
that
weren't
implemented
or
interop
issues
that
were
encountered?
You
know
that's
what
that
that's
what
this
that's,
what
the
advancement
process
specifies?
It's
not
just
you
know,
especially
if
something's
17
years
old,
we
don't
really
rev
rcs.
For
the
reasons
you
describe
right
just
to
change,
update
references.
There
is
no
yearly
maintenance
process
in
the
ipf.
J
G
J
There
you
know
there
are
things
that
you
do
to
advance
that
aren't
on
this,
and
it
is
a
lot
of
work.
People
often
don't
like
to
do
it,
but
you
know
that
would
be.
It
would
be.
An
implementer-focused
thing
that
you
know
you'd
have
to
you'd
have
to
get
into,
and
maybe
some
testing
you
know
as
an
example,
I
I
often
wonder
how
things
work
in
practice
when
you
use
the
non-standard
eap
type
space
you
know,
is
that
interoperable
between
implementations,
those
are
things
I
don't
know
that
we
fully
tested.
J
E
Right
yeah,
I
mean
in
general
I
love
to
have
that
that
sort
of
thing
here.
I
do
think,
though,
that
there's
two
categories
of
things
that
we
can
update
rfcs
for
and
what
one
is
this
implementation
experience
and
the
other
one
is
new
information
and
fixes
to
documents
and-
and
both
are
valid
reasons
and-
and
we
usually
fold
documents
in
in
that
that
have
both
components,
but
I'm
not
disagreeing
with
you.
I
I
agree
that
that
would
be
a
wonderful
thing
to
have.
D
Sorry,
I
was
a
little
distracted.
Apologies
for
that
or
joe.
Could
you
go
back
to
the
slide?
I
don't
know
one
slide
or
yeah
this
one
so
about
eight
now,
I'm
so
what
would
happen
when
we
use
encrypted
identifiers?
If
we
are
now
saying,
should
omit
the
peer
name
portion,
so
I
know
3gpp
uses
encrypted
identifiers
and
if
we
are
going
to
say,
should
omit.
Isn't
that
an
issue,
or
am
I
missing
something
here.
G
D
D
When
we
started
updating
for
tls
1.3,
we
realized
that
two
things
would
be
very
helpful.
Make
make
save
save
some
round.
Trips
was,
if
we
can
add
a
payload
to
eep
success
and
make
the
success
protected,
because
mostly
methods
export
keys,
and
you
will
have
keys
to
protect
that
message
and
if
you
could
send
the
new
session
ticket,
for
example,
in
the
eep
success
or
sends
and
other
time
types
of
configuration
data.
So
I
remember
there
was
a
presentation
from
huawei
to
do
that.
D
B
Just
wanted
to
jump
in
with
with
a
process
kind
of
commentary
on
what
we
had
just
talked
about
about
what
we
standardized
so
ignoring
some
of
the
details
of
what's
on
the
screen
right
now,
because
I
think
those
changes
fall
into
a
lot
of
different
categories
of
what
you're
doing.
But
I
would
say
the
conversation
of
how
we
do.
Protocol
maintenance
varies
across
kind
of
the
ietf,
and
I
think
that
there's
two
different
things
to
consider
here.
There
is
the
conversation
around.
B
How
do
we
document
implementations
and
how
do
we
elevate
things
from
ps
to
higher
levels
of
standard
and
that's
one
level
of
administrative
bureaucracy
and
then
the
other
element
of
kind
of
bureaucracy?
Is
you
know
what
triggers
of
this
is
that
in
chartered
to
trigger
kind
of
abyss?
Does
that
change
kind
of
the
protocol?
And,
I
would
say,
the
idea
of
collecting
a
package
of
erratas,
certainly
that
are
areas
where
we
don't
have
a
lot
of
clarifications
and
we
jam
that
into
abyss
without
necessarily
changing
a
protocol
version
of
her.
K
Hey
there,
joe
and
thanks
and
thanks
yari
for
the
draft,
I
want
to
say
that
I
totally
appreciate
your
car
analogy
in
terms
of
maintenance,
which
leads
me
to
want
to
ask
a
bunch
of
questions
which
are
probably
inappropriate
for
the
working
group.
But
what
I
did
want
to
ask
is:
if
we're
going
to
go
to
these
lengths,
if
we're
going
to
open
up
abyss
document,
is
it
worth
stepping
back
a
little
bit
and
asking
the
question
you
know
at
more
general
levels?
K
Are
there
things
we
really
ought
to
be
doing
differently,
and
I
mean
it's
a
very
lengthy
conversation
right
and
maybe
we
should
be
testing
you
know,
what
are
we
protecting?
What
are
we
not
protecting
is
the
connection
model
still
appropriate
is
the
the
is
the
model
we're
using
still
appropriate
for
for
tunneling.
These
are
all
questions
that
I
think
it's
at
least
worth
considering.
If
we're
talking
about
doing
abyss
for
this
and
which
is
to
say,
I'm
perfectly
fine.
K
K
Is
it
what
we
want
at
the
end
of
the
day
and
and
to
give
you
just
one
example
of
the
the
applicability
and
we
should
be
thinking
about
that
is
the
applicability
good
across
not
just
3gpp
and
and
802
networks
are
there?
Is
there
other
applicability
that
we
should
be
considering
in
answering
that
question
and
I'm
not
trying
to
reach
it
prejudge
the
the
answer?
I'm
just
saying.
I
think
we
should
be
asking
some
of
these
questions
all
right.
Thanks.
E
E
Yeah.
One
more
thing
on
this,
this
discussion
by
started
by
bernard
and
what
roman
said.
I
I
think
the
awareness
of
what's
working
and
what's
not
working
would
be
really
good
to
have.
There's
also
a
category
that
I
did
not
see
anyone
mention
yet,
which
is
you
know,
maybe
there's
some
parts
that
we
could
just
deprecate,
because
you
know
this
is
not
up
to
today's
standards
anymore.
