►
From YouTube: IETF110-BFD-20210311-1430
Description
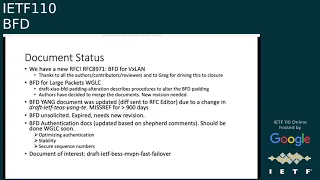
BFD meeting session at IETF110
2021/03/11 1430
https://datatracker.ietf.org/meeting/110/proceedings/
B
C
A
B
D
B
A
A
You're
basically
agreeing
to
everything
the
itf
policies,
the
agenda,
so
that's
the
chairs,
update
from
jeff
and
myself,
then
we'll
go
to
bfd
and
sold
sister.
That
will
be
me
bfd.
Secure
numbers,
I
believe,
is
from
mahesh
and
not
so
now.
Right
now,
mahesh
will
continue
vfd
stability
and
then
we'll
have
bfd
on
our
feet.
An
affiliated
echo
next
slide.
Please.
A
C
A
A
A
Bfd
for
large
packets
there's
been
discussions,
there's
been
a
relate
that
was
in
working
group.
Last
call
there's
been
a
a
more
recent
draft
regarding
how
to
other,
if
you
guys
remember,
but
bfd
large
packets
allows
you
to
have
large
packets
to
detect
mtu
issues,
but
it
doesn't
address
procedures
to
alter
the
bfd
padding
size
and
that
draft
bf
debating
alteration
describes
procedures
to
do
so.
The
authors
have
decided
to
merge
documents
together.
A
Thank
you,
bfd
yang
document.
It's
been
a
while
we've
had
to
send
diffs
to
the
rfc
editor
do
a
change
in
one
of
the
modules
it
depends
on
the
t's
yankee.
That
document
has
been
in
miss
ref
for
close
to
three
years
now
I
haven't
checked.
What
are
the
state
of
the
other
documents?
I
mean
the
ones
it
depends
on,
so
I
don't
have
a
good
idea.
What
a
potential
eta
would
be.
B
So
a
quick
point
on
this
one.
It
was
mentioned
in
one
of
the
other
meetings
this
week.
I
have
to
pull
my
notes
to
exactly
which
one
I
think
was
in
the
chat
that
one
of
the
options
we
could
consider
doing
to
maybe
move
things
forward
is
to
take
the
document
back
from
the
rfc
editor
and
split
out
the
mpls
component
and
ship
it
without
the
mpls
component
in
the
main
document
and
do
a
second
document
with
mpls.
B
E
Hello
jeff.
That
was
me
who
suggested
that
this
ac
and
lsi
suggest
that
in
lsr,
because
I
had
done-
I
had
done
some
homework
and
I
saw
that.
Not
only
are
you
work
waiting
on
yang
te
you're,
waiting
on
yang
t-e-r-s-v-p,
which
t
e
references,
so
you
got
to
get
both
of
those
done
just
to
get
that
one
reference
to
the
tunnels
or
those
I
mean
those
those
references
to
the
tunnels
in
the
mpls
document.
B
Thank
you,
ac,
I'd
forgotten
that
it
was
you
yeah
so,
and
I
think
part
of
the
relevant
point
here
since
was
mentioned
lsr-
is
that
we're
also
holding
up
other
people
that
are
importing
the
module
that
we
asked
them
to
use
as
the
grouping
to
make?
You
know
life
consistent
for
the
rest
of
the
bfd
users,
so,
unfortunately,
what
we're
trying
to
do
the
right
thing
for
everybody.
Mpls
is
sort
of
messing
that
up.
A
F
F
G
A
A
There
was
yeah,
there
was
one
thing
for
lsps
versus
lsp
from
what
I
remember
right:
okay,
bfd
unsolicited.
It's
expired
recently.
We
need
eurovision
there's
going
to
be
a
quick
update
immediately
after
the
bfd
authentication,
docs
there's
been
updates
recently,
based
on
the
comments
from
the
shepherd.
We
should
be
done.
Working
group
last
call
soon,
there's
going
to
be
an
update
on
two
of
the
documents.
After
I
think
it's
fairly
minor,
minor
stuff
left
well,
the
document
has
come
a
long
way.
I
think
we're
close
to
being
there.
Yes,
greg.
A
E
D
B
So
that's
one
of
the
hold
up
points
it
didn't
get.
You
know
the
wider
review,
even
an
idr,
and
I
think
the
it
hasn't
hit
my
iq
as
a
new
idr
chair
yet
but
john
may
have
a
better
sense
of
what
it
was
last
status
wise,
but
the
need,
for
you
know
this
being
a
more
generic
mechanism
is,
I
think,
one
of
the
sticking
points
we
have
to
figure
out
what
that
goes
on
with
there.
H
So
speaking
of
specific
best
coaches,
it's
currently
in
the
rlc
editor's
queue,
I
believe
it
went
through,
invest
mostly
because
it's
fairly
specific
to
or
is
considered
fairly
specific
to
to
to
vpns,
but
that
may
be
you
know.
Some
people
have
different
different
opinions
on
that,
but
I'm
not
sure
stefan,
my
co-chair
was
actually
shepherding
it.
So
I
don't
know
if
he's
tracked,
the
he's
not
in
this
call
attract
any
of
those
issues
that
you
mentioned
more
closely.
B
Yeah,
I
don't
know
that
there's
serious
issues,
I
did
leave
some
specific
comments.
You
know
as
part
of
my
own
review
of
the
thing,
and
that
was
before
I
took
on
the
chair
job,
so
I
think
a
conversation
will,
you
know,
probably
need
we
need
to
close
off
on
those
points
minimally.
The
point
libraries
need
to
be
addressed
and
past
that
point
more
eyes.
D
D
D
D
A
A
D
D
Ambivalent
to
that,
so
I
hope
that
I
know
I
recall
that
jeff
looked
at
this
draft
and
shared
his
expert
opinion
on
working
group
chair,
but
I
don't
think
that
it
really
was
accepted
because
it
was
not
on
the
mailing
list.
It
was
a
small
group
discussing
so
if
somebody
or
some
experts
from
the
group
can
share
their
opinion
on
mpl's
mailing
list,
whether
it's
useful,
whether
it's
a
reasonable
solution,
I
would
greatly
appreciate
that.
A
A
A
A
For
this
feature,
you
know
when,
when
the
document
was
adopted,
we
had
a
young
doctor
review,
which
required
a
small
change
in
the
main
bfd
young
model
that
was
sent
to
the
rfc
edit
that
was
sent
to
the
rfc
editor
and
because
of
the
yang
model.
We
change
the
document
from
informational
to
standards,
we'll
talk
about
that
on
the
next
slide
and
then
working
group
last
call
was
was
requested
last
august
next
slide.
Please.
A
A
A
A
A
A
Personally,
I
don't
really
mind
either
way
whether
it's
informational
or
standards
tracked.
I
know
there
was
a
push
to
keep
it
informational
because
there's
no
protocol
changers
there,
but
there
is
a
yang
okay
model.
So
john,
we
may
need
your
well
not
me.
We
will
need
your
help
just
to
close
on
this.
A
B
C
B
B
This
is
more
about
here's,
how
you
use
existing
mechanisms,
mostly
via
configuration
and
that
sort
of
thing,
so
that
was
the
real
reason
to
have
it
informational
and
the
ambiguity
is
strictly
what
does
having
a
yang
module
inside
of
your
document
do
to
things
the
the
question
effectively
devolves
down
to
we're
polluting
the
ietf
namespace
for
modules,
by
putting
our
stuff
in
there
and
ietf
effectively
has
to
manage
that.
So,
while
we're
not
changing
bfd
we're
changing
the
yang
tree
that
ietf
as
a
whole
manages.
B
C
C
F
F
F
F
So
one
of
the
questions
that
was
raised
as
a
result
of
the
shepherd's
comments
was
has
to
do
with
the
fact
that
we
do
talk
about
symmetric
algorithm
that
is
used
to
compute
the
ciphertext.
For
this
sequence
number
itself,
the
suggestion
from
richard
was
whether
we
should
mandate
or
even
propose
actually
a
minimum
algorithm.
I
don't
remember
richard,
which
is
the
one
you
maybe
said
as
the
minimum
that
we
might
want
to
propose
in
the
draft
for
the
purpose
of
interoperability.
F
A
C
F
B
E
F
E
E
B
F
F
So
it
essentially
extends
the
idf
yang
model
to
add
iftf
bft
stability
documents
for
each
one
of
the
potential
uses
of
pft.
In
this
case,
what
you're
seeing
is
an
example
for
a
single
up
ip
bft,
where
it's
adding
a
lost
packet
count
a
very
fairly
small
yang
module,
but
it
does
require,
I
guess
now,
a
young
doctor's
review,
which
I
think
richard
has
already
initiated
and
it
also
mis
necessitated
an
update
to
the
ayana
consideration
section
and
the
security
consideration
section.
So
those
were
the
changes
for
this
particular
draft.
F
A
Well,
sorry,
I
didn't
mean
to
keep
in
trouble.
Just
saying
I
mean
if
the
I
mean,
if
you
don't
support,
I
think
what
you
were
implying.
My
ish
was:
if
you
don't
support
this,
then
you
don't
there's
one
counter.
So
if
you
don't
implement
this,
you
don't
that
module
would
not
be
in
the
yang
library
and
all
that
right
and
whereas,
if
you
do
it's
the
only
counter,
that's
what
you
were
implying.
B
I
J
J
J
The
second
add
more
details
on
procedures
into
section
3.,
the
third
one
improve
the
section
four
on
the
application
applicability
of
a
uniquely
data.
Bfd
ico
functions
the
last
one
added
a
new
section
8
to
list
contributors,
and
we
move
one
course
to
contribute,
because
the
number
limitation
for
the
courses
next
page.
J
J
J
J
The
the
maximum
number
the
destination
udp
port
is
cited
to
37
85
and
the
the
the
next
action
the
device
b
will
look
back.
The
received
bfd
ico
packets
by
the
normal
forwarding
wii
without
any
special
processing
and
the
last
step
the
device
a
will
receive
the
the
bfd
ico
packet
and
lead
to
bfd
change.
So
this
is
a
very
simple
procedure.
Next
page.
D
My
concern
is
that
it
affects
the
security
considerations,
because
the
reason
for
this
restrictions
put
in
5880
to
use
echo
function
was
for
the
remote
ad
and
to
be
able
to
either
regulate
their
rate
of
echo
packets,
transmitted
to
it
or
even
not
to
accept
them
at
all.
So,
for
example,
by
setting
this
value
to
zero,
it
indicates
that
the
remote
pier
doesn't
want
to
receive
any
echo
packet.
D
J
E
E
H
I
Up
comments:
we
got
into
greg's
comments.
I
think,
for
this
affinity
pfd
echo
process
this
is,
it
is
totally
transparent
today
to
the
remote
system.
So
it's
just
like
just
like
a
data
packet,
you
don't
know
you
don't
know
any
thing
about
the,
whether
it's
a
bfd
packet
or
a
data
packet
so
same
size.
For
me
as
there's
no
security
issue.
B
So
I'm
going
to
insert
myself
into
the
queue
ahead
of
greg,
potentially
make
the
point
that
greg
would.
It
would
be
normally
a
security
consideration
in
the
sense
that
one
of
the
reasons
we
have
signaling
for
echo
support
is
so
that
the
systems
can
do
regulation
and
also
indicate
their
willingness
to
do
so.
B
J
B
D
D
G
D
B
E
B
Make
one
last
point
and
then
return
the
presentation
back
using
your
own
slide.
One
of
the
discussion
points
that
will
need
to
be
in
the
document
is
that
by
entering
you
know
one
of
the
down
or
in
it
states
that
normally
implies
that
the
bfd
async
mechanism
is
running
and
will
be
generating
packets,
so
part
of
our
procedure.
Changes
that
need
to
be
in
here
is
that
we're
allowed
to
be
in
the
down
state
without
transmitting
packets,.
J
J
J
D
D
D
A
B
B
J
J
Thank
you
so
next
type,
I
think
we
need
more
reviews
and
comments
and
we've
got
quite
a
lot
of
feedback
and
comments
just
now.
I
think
we
will
revise
this
draft
to
resolve
those
comments
as
well
as
some
further
action
will
be
taken
after
the
meeting,
and
then
we
would
like
to
ask
for
a
working
group
last
fall.
Thank
you.
