►
From YouTube: IETF111-MBONED-20210730-1900
Description
MBONED meeting session at IETF111
2021/07/30 1900
https://datatracker.ietf.org/meeting/111/proceedings/
A
Just
about
time
to
begin
we'll
wait
a
couple
more
minutes
for
folks
to
join,
but
as
we
wait
while
we
wait,
we
need
a
note
taker
who
would
like
to
be
the
note
taker
and
normally
jake
is
our
notetaker,
but
he
is
the
star
of
the
show
and
we'll
be
doing
most
of
the
talking
today.
So
it's
probably
not
good
to
have
him
so
who
else
would
like
to
be
the
notetaker
today.
A
B
A
C
A
A
A
The
truth
is
jake
has
the
lion's
share
of
the
working
group
documents,
so
he
will
be
think
of
this
as
four
separate
slots,
if
not
more
so,
he's
going
to
cover
those
and
he'll
be
able
to
dive
into
detail
lots
of
exciting
work
going
on
there
and
he
can
hopefully
maybe
talk
about
some
of
the
work.
That's
been
kicked
off
at
w3c.
A
A
There
was
one
more
issue
that
was
addressed
and
that
has
been
sent
on
to
iesg
and
approved
for
publication.
So
I
believe
warren
is
one
of
the
authors
on
that.
I
don't
know
that
any
of
the
other
authors
are
here
but
congrats
on.
Finally
getting
through
the
gate
on
that
one.
I
think
that
had
been
sitting
about
a
year
in
in
a.d
review.
A
A
A
A
A
What
that
would
look
like
also
in
ietf
110
in
the
beer
working
group,
the
some
folks
working
with
giant,
which
is
the
research
and
education
network
in
europe
presented
about
a
a
p4
network
that
they
have
deployed
and
they
recently
added
beer
to
the
routing
stack
and
the
p4
code
and
they
were
able
to
they
demonstrated
or
they
discussed
they
described
that
deployment
and
the
implementation.
I
encourage.
If
that
sounds
interesting,
please
check
out
the
proceedings.
Click
on
these
two
links.
A
But
you
know
the
first
step
that
we've
always
had
working
is
onnet
multicast,
which
is
you
have
native
sources
native
receivers
and
that
just
works.
The
way
multicast
has
always
worked.
That's
been
around
for
20
something
years
and
it
works
today.
The
the
m
bone
is
comprised
mostly
of
research
and
education
networks
like
giant
and
internet2
too,
so
that's
been
working
forever
more
recently,
the
last
few
years
we've
added
off
net
receiving,
which
is
you
can
deliver
native
multicast
sources
to
unicast
only
receivers
through
amt.
A
A
So,
like
I
said,
we're
the
early
stages
of
that.
What
do
we
need?
Most
right
now
is
interesting
content.
All
network
innovation
is
driven
by
compelling
content,
we'd
love
to
believe
that
it
goes
the
other
way
around,
but
the
truth
is
content
drives.
The
network,
cool
content
comes
out
that
people
love
and
the
folks
in
networking
build
architectures
to
support
those
that
content
and
those
applications.
A
B
B
B
B
B
There's
one
more
slide
I
started
adding,
which
is
which
is
not
just
a
single
path
back
to
the
to
a
root
but
a
path
to
many
external
non-multicast
links.
I
have
not
put
that
slide
into
the
into
the
current
deck.
It's
possible
to
pull
it
up.
If
anybody
wants
to
see
that
one,
but
that's
the
that's,
the
take
I've
been
using
on
the
i2
and
ngi
discussions
so
yeah,
but
it's
it
is
the
same
architecture.
B
You
just
have
to
think
of
a
few
different
ingest
points
with
potentially
virtual
links
back
back
to
them
from
from
you
know,
edge
bottlenecks
of
the
path
of
some
sort.
It's
really
just
for
the
rpf,
so
that,
instead
of
propagating
your
join
to
a
to
some
location,
that
does
not
have
a
multicast
capable
next
hop
for
the
rpf.
B
A
B
I
think
I
I
think
I
asked
for
30
minutes.
If
I
remember
it,
I'm
surprised
to
see
that
I
have
60.,
okay,
great
so
I'll,
be
talking
about
the
status
on
on
these
drafts
that
are
working
group
items
and
the,
and
also
the
status
of
our
ongoing
effort
to
sort
of
turn
this
into
a
a
generalized
multi-kit.
You
know
democratization
of
multicast.
I've
heard
a
few
people
call
it
so
as
compared
to
last
time.
B
I
I
put
a
few
slides
in
here
just
to
give
a
reminder
sort
of
overview
of
what
this
architecture
is,
because
I
felt
in
the
last
couple
of
meetings
like
I've,
skimmed
it
and
there.
I
believe
there
are
some
new
people
who
might
be
seeing
some
of
this
for
the
first
time
or
weren't
there
in
the
in
the
earlier
presentations
about
these
things.
So
it'll
it'll
be
brief
and
hand
wavy,
but
it's
the
it's
the
overview
that
that
can
be
that
can
accompany
how
these
things
work.
B
I'll
give
an
update
on
the
on
the
status
of
our
of
our
outreach
efforts
and
and
the
ongoing
development
work
on
this,
and
then
the
next
steps
and
document
status
so
first
off
to
give
a
reminder
overview
of
how
mnat
works.
What
you
have
is
is
a
situation
where,
for
whatever
reason,
you've
got
an
internal
part
of
the
network
that
cannot
handle.
B
B
B
It
would
translate
back
also
by
talking
to
the
mnot
service,
it
will
translate
back
into
the
global
sg
to
subscribe
externally,
and
what
this
allows
is
this
this
will
inter-operate
and
now
allow
the
client
device
to,
for
example,
with
the
authentication
through
ambi.
It's
it's
tied
to
the
global
addressing
scheme.
B
So
it's
important
that
the
client
understands
that
it's
trying
to
join
this
global
address,
but
because
of
various
kinds
of
workarounds
on
the
transport
side,
including
you
know,
either
v4
and
v6
networks
or
v6
and
v4
networks,
as
well
as
the
some
of
the
kinds
of
hardware
things.
I
think
I
have
a
slide
that
mentions
some
of
the
things
we
encountered.
B
You
know
how
you
get
that
metadata,
so
the
idea
is
that
you
know
source
one
and
source
two.
They
each
just
publish
a
srv
record
in
the
dns,
and
this
this
refers
to
a
specific
known,
dorm
server.
This
could
be
the
same
dorm
server
for
the
two
sources,
but
it
doesn't
have
to
be
the
same
dorm
server,
so
the
source
knows
about
the
dorm
server.
B
These
dorm
servers
is
it's
just
using
http,
as
kind
of
the
way
to
and
yang
as
the
way
to
describe
the
structure
of
the
data
and
and
deliver
it
to
anybody
who's
asking
for
it.
So
it's
all
read-only
from
the
from
the
sort
of
generalized
access
and
in
fact,
typically
going
through
a
cdn
least
in
in
my
deployment,
and
then
you
know
you're
making
decisions
about
what
to
do
with
that,
based
on
the
the
rest
of
the
draft.
That
explains
how
you
process
that
data.
B
So
so,
if
you
get
a
packet
that
doesn't
have
the
right
hash
on
it,
that's
on
that.
That's
on
that
channel.
It
means
it
either
got
modified
or
has
been
spoofed,
and
you
should
reject
it,
not
not
try
to
process
it
in
the
application
and
probably
also
in
the
network.
And
then,
if
you
get
any
hashes
for
which
the
packet
never
came
through,
then
you
can
treat
that
as
a
loss
and
and
respond
appropriately.
B
B
B
We
had
them
use
a
wi-fi
router
that
was
one
of
their
their
wi-fi
devices.
We
talked
with
them
about
the
practicality
of
getting
the
wi-fi
deployed.
In
some
cases
they
don't
control
all
of
the
wi-fi
routers
in
their
in
their
customer
base,
but
but
it's
sort
of
increasingly
common
that
they
have
a
significant
footprint.
That's
that's
amenable
to.
B
B
They
can
drive
updates
of
those
to
ensure
there
is
support
for
the
at
the
wi-fi
layer
and
we're
able
to
get
the
get
the
the
devices
that
they
use
for
their
ordinary
networks
to
do
the
multicast
propagation
again.
Sometimes
this
needed
some
discussions
with
their
vendors,
but
but
in
general
they
got
this
working.
However,
three
of
them
needed
to
use
mnat
one
of
them
was
for
ipv6.
B
B
A
B
This
was
a
so
we
had,
we
had
v4
content
running
and
there
was
a
v6
only
network.
Now
we
would
have
been
willing
to
stand
up
v6
content,
but
we
thought
this
was
an
interesting
use
case
and
they
had
some
other
requirements
too.
One
of
the
requirements
was
that
that
the
source
of
the
traffic
had
to
be
from
inside
their
network,
so
it
had
to
use
one
of
their
assigned
ips.
B
This
was
a
a
business
requirement
from
their
side,
so
this
was
not
going
to
be
possible
to
integrate
with
the
authentication
scheme
using
the
global
ips
unless
we
arranged
something
in
that
way,
we
wanted
to
be
able
to
use
the
same
sort
of
globally
authenticated
delivery,
and
so
we
thought
this
was.
This
would
be
a
good.
You
know
this
was
after
we
had
already
gotten
em,
not
working
for
for
two
other
cases,
and
so
it
was
a
sort
of
natural
fit
to
keep
to
keep
trying
it.
B
A
B
Correct,
no
s
local
g
local,
they
were
both.
They
were
both
remapped,
so
you,
you
could
stick
anything
into
the
into
the
assignment
pool
you
know,
but
but
in
in
fact,
for
this
it
was
a
a
local
group
assignment
also
so
there
I
can.
I
can
speak
to
another
case
we
encountered
as
well.
There
was
actually,
I
think
I
mentioned
it
here-
the
there
was
a
nokia
olt.
B
So
so
this
meant
that
the
traffic,
when
it
collided,
would
get
assigned
into
the
wrong
vlan
and
would
get
sent
to
like
their.
You
know
their
their
set-top
box
instead
of
being
sent
to
the
subscriber
that
was
that
was
trying
to
receive
it,
and
so
mnat
was
was
a
an
effective
workaround
for
that,
because
they
could
ensure
that
the
that
the
group
spaces
in
the
assignment
pool
just
were
divergent,
and
so
they
could
always.
They
could
always
make
sure
that
they
were
assigned
to
the
right
vlan.
B
What
they
have
instead
is
a
sort
of,
in
some
cases
it's
just
sort
of
over
over
a
quan
layer,
for
instance,
that
I'm
not
sure
if
I
pronounce
it
right.
It's
qam
that
that
is
used
in
cable
and
what
they've
got
is
just
a
static
assignment
of
multicast
group
address
to
to
a
specific
comp,
qualm
and
then
so
they've
got
the
sort
of
list
of
static
group
addresses
that
they
use
for
their
most
popular
tv
stations
and,
and
sometimes
what
they'll
say
is
well.
B
I
guess,
as
long
as
it's
under
the
the
rate
that
we
use
normally,
then
it
would
be
okay
for
us
to
take
our
our
few
least
popular
tv
stations
and
let
you
use
the
groups
that
are
assigned
to
those,
but
we
don't
want
to
reconfigure
the
network,
and
so
what
we'll
do
is,
and
so
for
this
case
mnat
actually
can
work.
Just
fine,
where
what
you
can
do
is
give
a
you
know.
The
the
pool
of
assignments
can
be
configured
to
whatever
those
static
groups.
B
Are
that
they've
that
they've
set
up
to
be
to
be
assigned
to
the
to
the
broadcast
transport
that
they're
sending
the
the
packets
over
and
then
and
then
it'll
get
cha
it'll
get
sent
through
without
having
to
reconfigure
all
their.
You
know
other
whatever
d,
slams
or
or
cmts's,
and
then
it
can
get.
You
know
unpacked
back
to
the
global
sg
back
on
the
back
south
of
the
of
that
access
layer,
so
that
that's
the
intended
operation
did
we
do
the
static
assignment,
I
think
the
well.
B
A
B
It
so
it
was
actually
on
the
receiver
yeah.
They
only
had
v6
connectivity,
but
inside
it
can
yeah.
I
guess
I
guess
that's
the
case.
What
we
actually
did
was
we
ran
it
at
the
os
layer,
so
we
set
up
an
internal
interface
that
had
v4
connectivity
and
the
the
joins
were
routed
into
that
internal
interface,
and
then
that
interface
was
running
our
instance
of
the
m-nat
egress.
B
The
egress
was
talking
to
the
server
which
was
configured
with
the
assignment
pool
and
and
was
configured
with
the
upstream
being
the
actual.
They
just
had
the
the
one
upstream
interface
for
the
for
the
received
device,
and
so
on
that
external
interface
for
the
for
the
actual
receive
device
it
had
been
turned
into
a
v6
join,
and
so
the
only
thing
that
the
network
saw
was
the
b6
join,
except
just
right
inside
the
the
m-nat
server
and
the
egress
and
ingress.
A
B
So
I
was
digging
around
on
that
a
little
bit.
I
think
I
did
it
through
a
regex
that
I'm
not
super
confident
about,
but
I'll
be
looking
for.
You
know
for
some
feedback
on
that.
At
some
point,
I
think
I
think
it
might
have
just
been
like.
Does
it
contain
a
colon
which
ip6
addresses
do
and
ip4
addresses
not
so
much,
but
but
there
might
be
a
better
one
to
use.
B
Right
but
yeah
I
mean
the
point.
The
point
being
that
that's
mentioned
is
one
of
the
use
cases
in
the
mnet
draft.
You
know
it
doesn't
need
any
special
defining
exactly
because
all
you
do
is
you
map
it
into
whatever
the
locally
assigned
address
is,
and
so
as
long
as
you're
allowed
to
specify
a
v6
address,
as
as
your
local
address
and
a
v4
address
is
your
local
address,
it
can
be
anything.
B
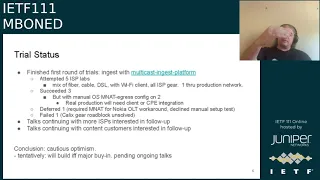
We
are
actively
continuing
some
talks
with
some
after
these
trials
have
concluded
we're
we're
following
up
with
some
other
isps
that
have
also
expressed
interest
in
and
deciding
whether
it
makes
sense
for
them
we're
basically
trying
to
drum
up
as
most
as
much
interest
as
we
can
at
this
point
and
sort
of
see,
do
we
really
have
the
critical
mass
to
to
roll
this
out
and
have
confidence
that
we're
going
to
be
able
to
deliver?
You
know
substantial
traffic
this
way.
B
Likewise
our
content
customers
with
the
prototypes
that
we
put
together.
We
we
believe
that
there
will
likely
be
some
changes
required
for
the
content
customers
for
the
video
side.
We
think
that
that
it,
it
can
be
done
in
most
cases
by
just
using
a
different
player,
but
sometimes
they
have
restrictions
on
their
players
and
on
on
you
know
wanting
like.
Sometimes
there
will
be
custom
extensions
to
the
player
that
they're
using
or
something
along
these
lines.
B
So
we
want
to
make
sure
that
that
it's
going
to
be
a
player
thing
that
can
make
sense.
Also,
the
you
know
the
browser
work
hasn't
hasn't
really
been
pinned
down,
yet
it
might
be
that
we
can
get
that
we
can
get
it
fully
transparent
and
put
into
the
browser,
at
least
for
segment
transport
for
the
video
support,
but
that's
all
sort
of
still
in
development.
B
Something
else
in
there
is
is
still
a
sort
of
ongoing
thing,
but
we're
trying
to
nail
down
the
the
expectation
both
that
we'll
be
able
to
deliver
traffic
if
we
have
traffic
and
that
we
we
will
in
fact
be
able
to
deliver
the
the
the
content
customers.
We
have
will
in
fact
be
able
to
do
this
because
it
takes
it
takes
all
three
right:
it
takes
the
network
and
the
customer
and
the
cdn
any
of
us
can
say
we
don't
think
this
content
should
be
multicasted
right
now
and
then
it
would
not
be
multicasted.
B
B
But
we
think
that
that
particularly
for
these
big
events
there's
enough
value
in
making
it
multicast
that
as
long
as
we
all
all
three
do
want
to
do
it
that
that
it's
looking
like.
Maybe
we
can
get
this
to
happen,
I'm
calling
this
cautious
optimism.
I
think
it.
None
of
this
is
really
a
done
deal,
but
but
everyone
we've
talked
to
is
still
saying
this.
This
this
looks
like
it
might
work.
I
don't
see
anything
wrong
with
it
and
boy.
Would
it
be
nice
to
not
have
these?
B
B
B
B
Web
traffic,
of
course,
has
a
lot
of
security.
Work,
that's
been
done,
and
that
has
been.
You
know
necessary
for
the
development
of
the
web
over
the
internet,
and
we
are
keen
to
not
break
any
of
that.
You
know
so
we're
trying
to
make
sure
that
we
that
we
get
all
these
pieces
in
place
to
to
get
that
to
happen.
To
that
end,
we've
we've
created
a
a
w3c
community
group.
I
think
I
sent
out
a
note
about
that
to
the
list.
B
Actually,
I
think
somebody
else
sent
it
out.
First,
I
think
it
was
probably
brett
and
thank
you
brett,
I'm
trying
to
get
all
caught
up
on
on
keeping
everybody
in
the
loop
who
should
be
in
the
loop,
but
but
that
group
started
last
month.
I
believe-
and
we
are
starting
our
regular
monthly
meetings
first
wednesday
of
every
month,
starting
next
week
on
the
on
the
4th
of
august.
B
B
There
also
were
some
considerations
raised
about
the
one
of
the
things
that
was
said
as
a
minimum
for
web
traffic
is,
is
encryption
which
we
don't
have
as
part
of
ambi,
so
we're
looking
for
the
right
solution
on
how
to
approach
that-
and
this
is
this-
is
one
of
the
key
questions
in
the
security
considerations
document
is
about
like
when
you
have
a
a
encrypted
session.
That's
one
to
many.
B
B
I
think
that
discussion
is
is
really
just
getting
started
and
there
is
some
risk
that
the
conclusion
would
be
that
there
should
be
no
ip
multicast
on
the
internet
according
to
a
security
perspective,
and
if
that's
the
kind
of
ietf
consensus
that
emerges
then
well,
we
can
close
this
group
down.
I
suspect,
but
I
don't
think
that's
really
what
it
should
be,
because
it
just
moves
the
security
problems
elsewhere
in
the
in
the
ecosystem.
B
In
there
there
was
a
there
was
a
side
meeting
yesterday
that
that
went
pretty
well
where
we
we
talked
about
some
of
these
ideas,
and
you
know
I
specifically
asked
if
anybody
thought
that
this
is
doomed
and
a
bad
idea
and
among
the
people
who
chose
to
join
that
side
meeting.
Nobody
thought
that
so
that
was
good,
but
I
think
that
there's
there's
still
some.
B
You
know
a
few
miles
to
cross
before
we
get
before.
We
really
have
ietf
consensus
that
that
this
is
going
to
be
possible
to
do
in
a
secure
way,
but
we're
trying
to
get
all
those
t's
crossed
and
eyes
dotted
as
we
as
we
move
this
forward.
So
we'll
see
how
that
discussion
goes
we're
trying
to
find
the
right
itf
venue
for
that
discussion.
Certainly,
I
encourage
people
to
join
the
w3c
multicast
group.
B
That's
a
multicast
community
group
and
discuss
and
and
raise
concerns
on
there
and
we'll
see
if
we
can
get
them
addressed
to
me.
These,
the
the
problems
that
have
been
raised
do
look
addressable
and
under
a
proper
consideration
of
the
threat
models.
I
think
we
can.
We
can
come
to
consensus,
there's
a
good
way
to
deliver
a
set
of
safe
traffic,
but
we
need
to
write
down
what
all
those
things
are
before
this
can
go
into
the
web
browser.
B
So
we
were
trying
to
do
that
in
the
meantime,
I'm
carrying
a
fork
of
chromium
and
anybody
who
wants
to
try
it
can
find
it
if
you
search
for
chromium.
I
hope
I
have
a
link
to
here,
but
I
can
send
it
if
I
need
to
and
I'll
follow
it,
but
it's
a
chromium
underscore
fork
under
the
grumpy
old,
troll
github
repo,
oh
yeah
there.
It
is
yes
right.
This
is
mostly
what
I
just
said
forgot.
I
had
another
slide
for
this.
B
B
But
there
is
no
need
under
ambi
to
share
any
sort
of
authentication
keys,
and
so
what
you
get
is
is
a
really
solid
authentication
protection
if
you
use
ambi
and
some
the
the
sort
of
hopefully
appropriate
degree
of
multicast
privacy
protection
through
and
confidentiality
protection
through,
that
you
can
get
through
the
use
of
shared
encryption.
Key
shared
decryption
keys,
at
least
in
a
multicast
stream.
B
So
so
yeah!
That's
our
that's
our
kind
of
next
project
that
we're
that
we're
going
to
be
trying
to
dig
into
and
make
sure
we
can
get
this
move
forward.
I
don't
exactly
know
how
long
it
will
take.
We
haven't
started
this
work
yet,
but
but
we
will
be
investigating
that
and
trying
to
make
sure
that
it
can
that
can
move
us
in
the
right
direction
and
actively
seeking
feedback
from
anyone
who
will
give
it
to
us.
B
B
Yep
and
the
the
more
shielding
the
community
group
right
so
in
terms
of
our
ietf
docs,
I
did
some.
I
I
got
a
yang
doctor
review
from
from
rashad.
I
addressed
the
feedback
that
he
gave
in
the
dorms
and
see
back
drafts.
I
think
there's
some
similar
stuff,
that's
gonna,
go
into
ambi
and
actually
I'll
also
be
applying
some
of
the
concepts
in
mnat,
but
in
dorms
and
see
back
in
the
latest.
B
B
I
was
thinking
about
it
and
I
think
it
makes
sense
to
do
the
dorms
last
call
ahead
of
trying
to
do
the
sea
back
in
ambi,
because
if
there
are
any
changes
that
end
up
needed
in
dorms,
then
it
may
impact
what
we
have
to
do
in
ambient
sea
back.
So
I'd
like
to
sort
of
get
dorms
pinned
down
and
then
and
then
have
that
ready
to
go.
A
B
B
Thoughts
on,
I
think
it
would
make
sense
to
put
them
in
a
cluster.
However,
I
don't
think
that
a
cluster
means
that
they
have
to
be
submitted
together.
If
I've
understood
it
correctly,
it
just
means
that
these
are
related
in
some
way
that
that
provides
value
in
in
keeping
them
linked
at
the
at
the
rfc,
editor
sort
of
level
and
right
now
in
dorms.
B
B
A
D
Or
not,
I
would
adjust,
I
would
suggest
getting
them
as
much
done
as
possible
and
they
can
just
sit
and
wait
in
the
rfc
editor
queue
and
miss
ref
state
until
other
things
happen.
That
way.
You
know,
there's
progress,
everybody
knows
what's
moving
along
and
you
don't
end
up
with
sort
of
making
many
tweaks
to
the
document
and
and
everything
waiting
on
everything
else.
B
B
Great,
but
preferably
we
don't
need
any
errata
that
doesn't
always
work
out
so
anyway,
yeah
ambi
had
some
substantial
updates,
we'll
be
trying
to
fold
these
into
the
the
next
stage
of
the
implementation
work
we're
trying
to
to
start
doing
as
well
as
kind
of
get
that
discussion
rolling
on
the
security
considerations
and
getting
it
to
a
place.
We
can
seek
good
consensus
there
again.
B
We
haven't
fully
decided
whether
the
right
way
to
do
the
encryption
is
via
quick
or
via
some
kind
of
an
extension
to
amv.
That
adds
encryption
at
that
sort
of
layer,
I'm
leaning
toward
quick
if
we
can
get
it
to
to
work
right,
but
I
would,
I
would
still
take
ambi
as
a
extending
ambi,
in
some
sense,
to
provide
an
encryption
capability
either
as
a
separate
document
or
as
a
as
a
rev
on
the
current
document.
B
B
B
Mnat
has
a
few
pending
changes
that
have
not
been
submitted.
Yet
I
didn't,
I
didn't
get
the
latest
updates
in
and
then
you
know
some
bugs
in
the
implementation
that
I'll
be
trying
to
sort
out,
but
that
is
the
doc
status.
So
I
guess
the
main
action
I'm
looking
for
is
to
consider
the
the
last
call
of
dorms
at
the
stage.
A
B
B
A
Think
it
would
probably
be
a
good
night
that
that
seems
like
a
good
idea.
Just
you
know
he,
he
made
the
suggestions
and
he
would
for
the
review.
Maybe
you
know,
send
it
on
and
see
if
he
thumbs
up
on
those
and
then
you
know
at
the
same
time,
ask
you
know:
does
this
obviate
the
need
for
a
regular
review,
a
late
review,
or
is
this
good
enough
and
then
yeah?
Okay,
take
it
from.
B
B
E
E
B
Great
thank
you.
I
appreciate
that
feedback
and
and
yeah.
That's
that's
good
to
hear.
I
I
think
there
are
still
some
improvements
to
make,
but
but
yeah
I
think
it's
I
think
it's
coming
along
and
I
was
I
also
have
been
pleasantly
surprised
with
like
how
well
mnat
has
worked
around
some
of
the
the
just
problems
in
practice
from
the
vendor
implementations
of
multicast,
that
you
know
that
the
isps
have
had
to
wrestle
with.
So
I
think
there
there
are
some
legs
there
that
that
might
be
useful,
yeah.
A
All
right:
well,
I
promised
we
would
be
done
early
and
we
are
so
go
enjoy
your
friday
afternoon,
at
least
until
the
next
working
group
and
thank
you
for
joining
and
hopefully
we'll
someday
have
another
we'll
meet
in
person
in
madrid.
But
I
don't
know
that
that's
going
to
happen,
but
if
not
we'll
do
this
online
again
and
look
forward
to
seeing
you
all
again,
then.
