►
From YouTube: IETF111-ACME-20210730-2130
Description
ACME meeting session at IETF111
2021/07/30 2130
https://datatracker.ietf.org/meeting/111/proceedings/
C
B
B
B
So,
what's
on
our
agenda
note
12
technical
difficulties
and
advanced
trivia
like
agenda
bashing,
then
we'll
go
over
the
document
status
for
all
the
working
group
documents.
Then
we
have
two
presentations
from
owen
about
acme,
integrations
and
decree
sub
domains,
and
then
we
should
talk
about
where
we
go
from
here.
B
So
document
status,
the
extensions
to
acme
for
end
user
s,
mime
certificates,
also
known
as
draft
itf,
acme
email
s
mime
was
published
in
april
as
rfc
8823.
So
thank
you
for
the
work
galaxy
second
document,
an
acme
profile
for
generating
delegated
certificates,
also
known
as
draft
itf
acme
star
delegation.
B
B
So
there's
going
to
be
a
little
bit
of
back
and
forth
between
the
authors
and
the
ad,
and
hopefully
it's
progressing
soon.
Tn
off
list
profile
for
acme
authority
token
and
draft
acme
authority.
Token
tnfist
submitted
to
asg
review
last
august,
but
it's
waiting
for
the
other
document
in
order
to
progress.
B
B
I'm
sure
this
can
progress
soon,
acme
integration,
that's
the
other
document
that
went
through
working
with
last
call
and
received
all
of
one
review
and
I'd
like
to
say
one
review,
not
from
neither
chair
nor
document
author,
but
then
the
one
review
which
was
from
deb
has
so
that
that
became
a
chair
so
now
there's
zero
reviews
that
are
from
neither
chair
nor
author.
So
we
need
more
reviews
too
and
count.
This
is
having
what
loop
consensus.
B
B
B
B
D
D
D
So
what's
changed
since
I
kf
110
and
drafter,
and
we've
added
an
explicit
section,
integration
considerations
and
added
a
few
more
clarifications
here.
Basically,
some
comments
and
feedback
so
clarified
for
service
operators
that
but
the
use,
easter,
cheap
server
operators
are
expected
to
be
the
main
owners,
and
that's
so
that
they'll
be
able
to
do
them,
challenge
proofs
and
challenge
fulfillments
and
public
units
records
and
clarified
for
csr
attributes
the
club
that
likes
moss
and
the
csr
attributes
to
talk
with
their
clients.
D
Most
tendencies
are
actually
expressed
to
an
esdnt
servers
and
some
clarifications
and
search
change
and
trust
anchors,
because
acme
may
return
not
just
an
identity
circle,
another
to
be
certain
a
chain
of
certificates
of
two
and
potentially
including
the
route
and
verified
exactly
how
that
maps
into
esg
and
team
specifications.
The
handling
is
different
from
both
and
a
section
or
handling
and
giving
we've
given
recommended
mappings
between
acme
cmc
and
keyboard
codes
and
just
any
other
guidance,
and
specifically
the
idkb
cmcra
guides.
We've
consolidated
that
into
that
section
as
well.
B
All
right,
so
this
is
a
draft
that
we
tried
to
get
through
working
with
last
call
and
didn't
get
enough
reviews.
So
I
guess
the
question
for
the
room
is
whether
people
are
willing
to
read
and
write
reviews,
so
we
could
do
the
show
of
hand,
but,
let's
just
say
anything
at
all
in
the
jab
room,
and
if
we
see
several
replies
and
we'll
consider
it.
B
B
B
D
So
changes
we've
reordered
some
sections
and
card
like
examples
we're
using
closer
terminology
alignment
with
the
cab
guidelines.
You'll
actually
see
this
in
the
protocol
in
the
next
slide
as
well,
and
we
could
arguably
do
more
to
launch
terminology,
but
we've
made
some
rewrites
and
changes
to
align
more
closely
with
cfv
terminology
on
pre-authorization
handling.
We've
exclusively
clarified
what
the
mechanism
is
for.
A
client
specified
wants
to
pre-authorize
for
the
domain
name,
space
support
to
give
an
identifier
and
for
new
order
handling
and
based
on
the
feedback.
D
D
If
you
want
to
next
slide,
will
show
you
exactly
what
this
means,
and
so
these
are
screenshots
taken
from
the
draft.
Under
the
new
authorization
payload,
there
is
a
building
flag
indicating
whether
this
pre-authorization
as
far
as
domain
name
space
and
so
for
everything
on
the
reach,
the
indicator,
identifier
for
the
new
order.
Payload,
we
need
to
be
a
bit
more
explicit
because
the
identifier
is
there.
We
also
need
can't
just
listen
feedback.
D
D
Then
the
response
comes
back
and
when
the
client
creates
an
authorization
actually
declines
to
specify
the
domain
name,
species
are
sorry
server
specifying
its
minions.
This
is
true
and
then
step
two
decline,
content
and
present
a
new
order
request
for
a
sub
domain
within
that
domain.
Name.
Space,
for
example,
we're
showing
is
to
submit,
is
directly
off
the
domain
name
space.
Our
deals,
the
topmost
and
domain
domain
name
space
and
the
client
is
just
specifying
the
identifier,
the
identifier,
with
a
value.
C
D
D
D
D
B
A
D
B
B
B
We
have
this
storage
array
with
dozens
or
hundreds
of
servers
and
they
should
authenticate
to
each
other
with
certificates
and
but
they're,
not
the
web.
So
the
original
acme
is
not
true,
does
not
really
fit
in
there
so
yeah.
Maybe
we
want
our
own
things,
our
own
extension,
our
own
method
affair,
proving
ownership
and
yeah.
I
could
write
a
draft
like
that,
and
that
would
interest
probably
me
and
that's
it
so
it's
hard
to
justify
having
a
working
group
with
only
that
only
that
kind
of
work.
B
C
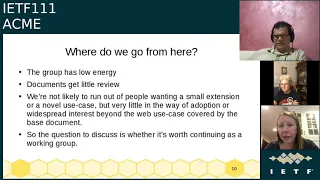
Michael
you're,
absolutely
right,
so
things
have
been
very
slow
and
I
think
that
there
is
a
self-fulfilling
prophecy.
Is
that,
as
things
are,
slow
people
are
reluctant
to
do
things?
My
suggestion
is
not
to
close
the
group
at
this
point.
I
don't
know
if
you
know
this
slide
about
that,
but
maybe
instead
consider
virtual
intro
meetings,
which
tend
to
deal
away
with
scheduling
conflicts.
C
Just
accept
the
the
thing-
and
I
guess
my
question
is:
would
your
document
actually
require
any
kind
of
ayanna
action
to
proceed
like
do
you
actually
need
to
standardize
it?
For
your
case,
like
I
mean
so,
you
said
many
small
extensions,
but
in
some
cases
it's
unclear
whether
they
actually
require
any
kind
of
action.
B
C
E
E
Right
so
I
guess
you
know,
if
there's
no
interest
in
my
particular
draft,
that's
a
fine
outcome
out
of
last
call
I'm
happy
to
stop
working
on
it,
but
if
people
think
it's
interesting
to
have
the
user
one's
automated
and
I
think
digicert
had
already
done
that
that
would
be
good
to
just
get
done
with
it
right.
So
I'm
just
sitting
out
here
waiting
for
it
to
go
to
the
last
call
for
a
year.
E
E
F
Yeah,
generally
speaking,
I
I
like
all
the
questions
that
you
asked
and
I'm
definitely
interested
to
hear
if
there's
additional
feedback.
My
other
question
to
add
to
the
list
is:
are
there
latent?
Are
there
late?
Are
there
latent
extensions
people
want
to
do
that?
You
know
folks
haven't
kind
of
spoken
up
on,
because
one
other
thing
I
would
like
to
do
is
you
know
if
there's
things
people
want
to
do,
let's
batch
them
up,
let's
get
them
kind
of
listed
and
perhaps
they
might
re-energize
the
working
group.
G
Oh
there
I
am
yeah,
I
mean
I
was
just
raising
my
hand
to
say
yes
there
there
is
some
new
stuff
coming
up,
in
particular
hi.
I
work
for
let's
encrypt
and
we
have
not
been
particularly
active
in
this
group
recently,
largely
due
to
turnover
of
people
on
our
group,
but
we're
now
in
a
situation
where,
in
the
face
of
the
mass
revocation
events,
let's
encrypt
is
looking
at
revoking.
G
200
million
certificates
all
at
the
same
time
and
that's
a
problem,
and
so
we
plan
to
propose
I'm
I'm
here
for
the
first
time
to
sort
of
learn
how
things
go.
But
I
plan
to
have
a
draft
in
process
and
able
to
be
presented
at
ietf
112
later
this
year
about
the
acme
renewal
info
thing
that
roland
shoemaker
proposed
sort
of
by
the
by
proposed
on
the
mailing
list
about
a
year
ago.
G
G
H
Yeah
this
thing
about
what
to
do
with
the
end
of
a
security
working
group
always
comes
up,
and
you
know
every
single
one
that
I've
been
in
has
tail.
You
know
tailed
away
at
the
end,
and
I
think
it's
just
intrinsic
to
the
way
that
security
draft
security
things
work.
You
are
never
done
with
a
security
spec,
and
so
I
think
that,
as
far
as
the
working
group
is
concerned,
we've
just
got
to
accept
that.
H
That's
just
the
way
that
it
is-
and
this
is
something
that
we
probably
want-
should
address
as
a
security
area
issue,
and
I
think
that
we
should
have
a
standing
committee
for
maintaining
security
specs,
because
you
know
you,
you
can
never
be
just
done
with
security.
You're
always
going
to
be
adding
new
validation
methods,
you're
always
going
to
be
adding
new
algorithms
and
you're
always
going
to
want
to
review
those.
B
Well,
unlike
say,
ipsec
me
or
pkx,
with
acme,
the
first
document
dealt
with
the
web
and
was
the
case.
Everyone
was
interested
in
and
then
said.
Well
what
about
mail
certificates
yeah?
I
guess
we
can
do
them
too,
and
then
one
about
my
server
certificates
and
the
user
certificates
and
all
the
other
kind
of
certificates
that
are
hardly
ever
in
use.
B
B
H
Yeah,
I
I
think
that
that,
in
part
comes
from
a
misunderstanding
about
what
certs
are.
I
mean
like
because
of
the
way
that
the
web
and
tls
search
came
out,
people
think
of
them
as
server
certs
they're,
not
they're
organizational
certs
or
they
are
domain.
Certs
they're
describing
a
host
that
is,
has
been
validated
by
some
process
for
mail.
Certs
you've
got
a
person,
that's
been
validated
by
some
person,
but
when
they
got
tied
to
their
role
in
the
tls
protocol,
everybody
got
confused
and
that
confusion
has
stayed
with
us
for
25
years.
H
So
I
think
that
some
of
the
low
energy
may
be
that
some
of
us
just
don't
believe
that
this
is
a
separate
type
of
certificate,
and
maybe
we
don't
show
up
to
say
no,
it's
the
same
certificate.
You
don't
need
to
do
this
at
all,
but
there
are
other
folks
who
insist.
Oh
we've
got
to
have
a
different
way
of
doing
validation
for
smtp
client
auth.
B
F
F
What
is
where
is
their
appetite
to
do
new
work
and
let's
not
raise
the
bar
too
high,
to
say
that
you
even
need
to
come
with
a
ready
draft,
but
let's
talk
about
what
additional
scope
might
be,
and
let's
see
what
that
tells
us.
If
it
turns
out
that
there
is
not
a
lot,
a
lot
more
new
scope
to
kind
of
cover,
then
this
is
kind
of
a
question
of
do
we
stay
open
to
do
to
do
maintenance
and
how
long
we
would
set
a
timer
for
that.
F
F
A
A
B
We
don't
really
consider
algorithms
in
the
acme
work.
It
was
always
use
a
tls
connection
and
whatever
tls
uses
is
dls
uses
and
you
sign.
If
the
algorithm
changed
on
the
certificate,
it
doesn't
really
make
any
difference,
still
a
mechanism
for
getting
certificates.
I
don't
think
that's
changing,
but
he
could
be.
F
G
Yeah
I
mean
I
think
this
is
on
on
the
topic
of
there
being
energy
for
things
in
general.
I
think
this
is
a
ietf
wide
thing,
not
just
an
acne
working
group
thing,
but
in
particular
like
just
a
few
minutes
ago,
when
we
were
asking
for
hey
how
many
people
have
read
this
draft
who's
willing
to
stand
up
and
do
a
a
non-chair
review
of
it.
G
I
I
did
not
come
forward
and
say
I'm
willing
to
do
an
on-chair
review
of
it,
because
I
don't
even
know
what
that
process
involves
yet
right
and
so
like
yeah.
I,
and
presumably
other
people
like
me,
who
are
relative
newcomers
to
the
space,
are
willing
and
able
to
do
things,
but
I
don't
feel
like
I've
had
resources
placed
in
front
of
me.
All
of
the
resources
that
were
placed
in
front
of
me
were
show
to
a
meeting
and
see
how
it
goes
and
you'll
learn
everything
by
watching
and
so.
B
B
F
A
B
A
Lanes
kathleen's
document
and
then
three
to
schedule.
An
interim
I
think
late
september
early
october
is
good,
look
sort
of
splits
the
middle
between
here
and
november
and
then
possibly
when
we
look
for
meeting
time
in
november,
we
need
to
be.
Is
it
a
gather,
it's
quite
difficult
to
not
have
conflicts
at
all.
It
sounds
like
we've
been
subject
to
conflict
issues.
B
C
Just
to
say
that,
actually
in
physical
sessions
we've
had
historically
eight
common
patterns,
so
conflicts
will
continue.
If
anything,
you
know
you
can
attend
two
sessions,
much
easier
in
the
virtual
scenario
than
than
physically
but
anyway,
that
wasn't
what
I
that's.
Why
I
suggest
that
we
have
a
virtual
interim
because
they
tend
they
don't
tend
to
have
any
conflicts.
