►
From YouTube: IETF111-IOTOPS-20210726-2300
Description
IOTOPS meeting session at IETF111
2021/07/26 2300
https://datatracker.ietf.org/meeting/111/proceedings/
A
B
C
C
C
A
Close
enough
so
welcome
everybody
to
our
itf
111
iot
operations,
working
group
meeting
at
the
iatf,
of
course,
alexa-
and
I
hank-
are
you
chairs
of
this
working
group
and
this
thing
to
think
spacesh,
iot
operations
and
up
suspicious
realm.
We
have
prepared
something
for
you.
This
session
is
recorded
next
slide.
Please.
A
We
are
operating
under
the
node.
Well,
it's
very
important
to
understand
that
everything
you
are
saying
or
writing
or
you
are
basically
putting
into
media
channels
here-
is
made
public
under
the
bylaws
that
are
the
noteworld
themselves.
Also,
there
are
some
code
of
conduct,
rule
and
they're.
The
bcb54
so
behave
yourselves,
basically
be
nice
to
each
other,
and
I
think
you
can
all
go
along
also,
if
you're
aware
of
any
patents
or
participation
that
involves
your
ipr
be
careful
to
to
put
that
into
the
public
channel.
That
is
in
notepad
next
slide.
Please.
A
So,
if
you're
new
here
there
is
a
link,
that's
the
participation
guide.
You
can
also
find
that
if
you
type
into
your
search
engine
of
your
choice,
iit
f
agenda
that
typically
brings
up
the
iatf
111
page
and
there
is
a
meet
echo
guide.
How
this
participation,
working
groups
of
the
online
meeting
works
also
there's
a
link
on
the
slide,
so
somehow
you
might
have
made
it
here
and
also
then
you
know
how
this
works.
A
A
A
Yeah,
so
this
is
also
an
iits
procedure.
We
can't
proceed
from
here
on
if
there
is
no
minitaker
there's
a
link
on
this
deck.
Also,
it's
at
the
agenda
there's
a
little.
I
don't
know
pen
icon
in
the
agenda,
hma
page
where
you
can
click
on
which
brings
you
to
kodi
md.
If
you
have
a
itf
account
data
tracker
account,
you
can
edit
that
and
become
a
minutes
taker.
A
A
Yeah,
thank
you.
Kiran,
michael
thanks,
a
lot,
that's
good
enough
for
us
here
and
then
we
can
proceed
to
the
next
slide,
which
is
the
first
slide
of
the
agenda.
I
think
exactly
so.
As
you
can
see
here,
we
have
a
two
hour
slot.
We
are
a
little
bit
conflicting
with
other
interesting
sessions,
unfortunately,
but
I
think
we
make
up
for
a
really
really
good
setup.
A
A
A
D
Yeah,
thank
you.
So
this
is,
I
don't
know
if
this
title
of
our
draft
is
accurate
or
not,
but
what
we
wanted
to
do
was
put
forth
some
of
the
ideas
about
industrial
internet
and
specifically
looking
into
the
infrastructure
related
stuff,
and
we
are
next
slide
please,
and
so
mostly,
we
just
want
to
do
discussion
on
things
which
are
really
related
to
industrial
internet,
not
really
focusing
on
consumer
iot
type
of
devices,
but
the
way
operations,
technology
or
the
process
control
works
in
the
industry.
D
So
this
is
a
typical
scenario
for
industry
control
network
that
it's.
There
is
some
kind
of
a
tiered
model
here
we
have
a
division
between
the
business
logic,
which
is
completely
ip
based
applications
or
they
call
it
id
networks
and
then
process
control
networks
are
somewhat
segregated
from
those
id
applications
and
they
are
operated,
run
managed
on
its
own.
D
Their
job
is
to
collect
the
monitoring
data,
optimize
the
processes
and
make
sure
they
are
run
in
a
very
reliable
and
resilient
manner,
and
these
are
the
things
that
happen
on
the
plants
and
most
of
the
devices
and
the
networks
are
pretty
much
physical
infrastructure
in
nature.
Their
devices
are
not
constrained,
iot
devices,
but
they
are
most
feed
field,
bus
serial
devices
and
how
the
processes
are
done
with
a
certain
time.
Centric
engineering,
those
are
the
important
artifacts
in
industry
control
network.
D
So
what's
happening
now
is
that
automation
is
coming
in
and
automation
actually
drives.
The
con
drives
the
new
applications,
which
requires
a
full
connectivity
between
the
id
and
od
part,
and
what
we
are
trying
to
do
is
to
find
a
relevant
work
in
idf,
where
these
odn
id
technologies
can
converge
and
sit
together
next
slide.
D
D
D
Location
where
it's
going
to
move
around
what
kind
of
things
it's
going
to
do
and
then
the
way
security
is
handled
for
these
industrial
networks
is
just
creating
an
isolation
from
rest
of
the
world.
Very
rarely
things
device
forget
about
the
devices
even
network
themselves
do
not
connect
with
the
internet,
public
internet
or
even
the
idea
applications
they
integrate
with
very
in
a
very
open
manner.
D
D
And
what
that
there
are
some
other
factors
which
are
different
from
iot.
One
is
that
when
we
were
studying
industry
control
and
process
control
protocols,
there
are
roughly
100
of
those
100
of
those
protocols.
A
lot
of
them
are
related
to
field
burst,
like
modbus
profibus,
and
even
though
tsn
ethernet
is
getting
more
and
more
deployed.
There
are
still
a
lot
of
legacy
protocols
being
used.
In
fact,
there
are
gateways
that
brag
about
translation
of
hundreds
of
protocols
and
in
a
very
stateful
manner.
D
D
D
D
You
can
have
multiple
instances
of
which
virtual
plc
is
to
operate
on
your
fieldbus
devices
and
in
an
advanced
case,
which
I'm
not
even
taking
seriously
right
now
is
about
the
digital
twin
instances
where
you
will
have
not
just
one
device
or
a
one
machinery.
You
will
have
combination
of
those
things
that
create
some
kind
of
an
instance
of
your
operation,
so
these
are.
That
is
also
related
to
virtualization
in
some
sense.
So
that's
an
interesting
scenario
to
look
at
and
the
next
slide.
Please.
D
And
the
third
thing
is
implications
due
to
growth
in
data,
as
I
mentioned,
that
more
more
and
more
applications
will
become
compute
intensive.
So,
for
example,
if
you
want
to
have
cameras
for
inspection
on
the
factory
floor,
that's
going
to
generate
a
lot
of
data.
So
what's
your
choice?
Do
you
want
to
process
that
data
on
a
factory
floor
or
somewhere
on
the
remote
side?
D
If
you
want
to
do
it
on
the
remote
side,
you
have
to
increase
the
bandwidth
of
the
entire
network,
or
you
will
have
to
come
up
with
again
some
sophisticated
mechanisms
that
how
do
you
manage
quality
control
and
just
send
a
summary
of
data
to
the
id
network
which
is
outside
your
plant,
and
then
there
is
another
aspect
of
which
is
related
to
data.
Is
that
even
factory
floor?
As
you
start
building
the
automation
component,
your
factory
floor
is
not
just
one
network.
It
is
combination
of
different
infrastructure
networks.
D
You
want
to
do
building
automation,
you
have
your
own
core
machinery
that
needs
to
be
automated.
You
want
to
do
overall,
temperature
control,
the
accident
and
emergency
situations,
intruder
detection,
all
those
applications
have
to
be.
No,
you
will
feel
the
need
to
bring
those
applications
onto
your
factory
floor
and
these,
in
my
mind,
are
somewhat
new
scenarios
and
we
need
to
study
them
from
the
network
perspective.
D
Yeah,
so
those
are
the
three
critical
scenarios
which
I
find
interesting
and
how
do
we
relate
it
to
the
work?
That's
going
on
is
definitely
dead.
Net
is
working
on
the
time-centric
applications,
so
they
will
take
care
of
that
how
your
devices
are
going
to
be
operated
in
a
deterministic
manner,
using
dsn
and
reliability
aspects.
Latency
aspects
are
taken
care
of,
and
I
was
attending
like
iot
ops
last
time
and
there
was
discussion
about
the
life
cycle
and
onboarding
things.
D
So,
to
be
honest,
I
haven't
really
understood
how
those
things
can
fit
into
industrial
field.
Bus
devices
perspective,
because
those
devices
do
not
have
a
lot
of
network
related
presence
in
them,
but
we
can
certainly
look
into
things
such
as
compressed
header.
How
can
we
bring
compressed
header
into
the
ot
devices
and
have
them
interface
with
ip
based
servers
for
itod
integration?
D
There
is
a
lot
of
focus
discussions,
at
least
on
the
major
mailing
list,
about
the
addressing
related
efforts,
and
that
could
also
be
a
relevant
work
and
interest.
So
industrial
internet
becomes
a
relevant
use
case
for
those
those
type
of
cases
addressing
related
cases
where
we
say
that
something
like
ipv6
address
is
going
to
be
too
big
for
devices,
because
those
devices
normally
are
fieldbus
with
eight
bit
of
information
or
two
bytes
of
information.
D
So
you
would
want
to
come
up
with
a
slightly
shorter
address
space
and
then
tsn
is
working
on
some
profile
related
to
it
and
ot
integration,
and
this
is
done
under
opc
ua.
So
I
haven't
gone
through
this
part
very
clearly,
but
there
are
some
bits
and
pieces
of
work
going
around,
but
nobody
is
looking
at
things
from
the
network
infrastructure
level.
D
Next
slide.
Please-
and
this
is
what
I
was
talking
about-
that
how
there
is
a
kind
of
difference
between
the
ip
stack
and
the
industrial
protocol.
So
in
industry
we
have
multiple
protocols
sitting
together
and
pretty
much
they
ride
on
top
of
either
the
physical
layer
directly
or
just
on
the
data
link
layer.
As
such,
there
is
no
network
layer
in
between,
but
when
we
start
talking
about
scalability
or
things
that
have
to
extend
all
the
way
to
the
edge
or
the
cloud
and
you
have
may
have
to
transit
through
different
networks.
D
D
Personally,
I
think,
that's
quite
an
interesting
area
because,
as
we
said
that
these
devices
they
have
just
one
address
that
represents
physical
address
net
and
data
link
address,
there
is
no
such
thing
as
network
addresses
associated
with
device.
One
thing
we
could
look
at
is
how
my
network
stack
on
the
device
side
will
look
like
when
it
has
to
communicate
with
some
ip
based
device
or
rfp
based
server
or
application
virtual
plc.
D
D
We
have
let's
say,
for
example,
ip
nodes
that
are
talking
to
directly
talking
to
a
device
with
its
own
address
space,
for
example.
Modbus
is
one
address.
Space
profibus
is
another
address
space.
How
do
we
find
a
communication
between
these
devices?
Not
just
normalizing
everything
into
an
all
ips
same
kind
of
source
and
destination
addresses,
but
having
some
kind
of
asymmetric
behavior
to
those
addresses
next
slide
yeah.
D
So
that
was
my
last
slide,
and
these
are
some
of
the
open
questions
I
had
in
mind
that
does
this
group
think
there
is
a
value
in
supporting
idn,
ot
network
technologies
and
coming
up
with
some
solutions
in
those
directions
and
specifically
starting
from
the
address
framework,
so
that
we
make
can
bottom
up
approach
and
mike
had
raised
one
question
on
the
email
thread
that
we
cannot
do
this
work
on
our
own.
We
need
to
get
stakeholders
and
I
totally
agree
with
this,
and
we
can
try
that.
D
But
I
also
want
to
make
a
point
that
typically
ot
networks
have
used
the
standards
that
are
available
to
them
and
if
we
have
some
kind
of
head
start
or
we
come
up
with
a
clear
problem
statement
and
requirements,
it
might
help
us
get
those
stakeholders
interested
in
this
kind
of
work,
and
there
are
maybe
there
are
other
things
like
security
is
something
I
haven't
added
in
the
document
yet.
But
there
might
be
other
important
things
that
I
haven't
touched
upon.
D
B
So
I
agree
with
you
kieran.
I
think
that
we
need
to
get
ahead
of
this
group.
We
need
to
suck
the
other
the
ot
people
in.
I
think
that,
as
you
say,
they
tend
to
implement
whatever
specs
are
out
there,
and
so
I
think
that
there's
a
little
bit
of
we
need
to
get
ahead
of
them
on
the
specs,
acknowledging
that
it
takes
us
two
years
to
publish
a
document
and
they'll
probably
ignore
it
until
it's
an
rfc.
B
But
at
the
same
time
we
need
to
have
some
credibility.
So
we
have
to
have
some
ot
people
there
and
I
think
that
the
right
solution-
this
has
been
vote,
cunningham's
law
and
which
is
to
say
we
should
put
out
a
smack
and
get
people
shouted
at
us
and
tell
us
why
it's
wrong,
and
I
don't
think,
there's
any
other
way
that
we're
going
to
get
a
progress
on
that,
except
by
doing
something
like
that,
and
it
should
at
least
be
half
right
and
only
half
wrong.
D
Yeah,
I
think,
getting
some
kind
of
verification
from
them
that
this
is
how
we
are
thinking
is
the
right
direction.
Do
they
really
see
these
kind
of
pain
points?
Just
validation
will
be
a
good
start
in
itself
and
we
we
can
always
tr.
There
are
some
well-established
consortium
like
iic.
We
can
bring
people
from
there
to
talk
about
their
pain
points
and
how
itf
can
help
them.
E
Yeah,
I
think
it's
really
important
to
skate
to
where
the
puck
will
be
here.
So
we
should
be
planning
ahead.
We
should
think
about
components
we
can
supply
now,
as
as
the
iitf
that
will
be
useful
to
them.
So,
for
instance,
one
thing
that
came
up
here
is
address
sizes.
That's
of
course
not
a
new
question
and
we
we
started
work
on
that
in
in
various
working
groups.
I
sent
a
message
to
the
chat
with
some
of
them,
but
in
particular
for
for
the
run
ipv6
addresses
in
environments
with
limited
network
resources.
E
We
have
a
pretty
good
solution
which
is
6
low
pen,
and
I
think
we
should
look
at
how
we
can
use
something
like
6
door
pen
to
actually
make
addresses
small
in
the
industrial
internet
environment.
There's
one
problem
here,
which
is
these
weird
devices,
not
only
use
different
kinds
of
addresses.
They
also
use
different
kinds
of
network
schematics,
and
we
will
of
course
run
into
serious
problems
when
we
ignore
that
so
some
form
of
gateway
between
traditional
ite
and
and
various
ot
network
technologies
will
be
necessary.
There
is
no
way
around
that.
E
D
And
so
for
that,
the
way
I
look
at
it
is
that
that
is
at
the
interface
level.
Right
I
mean
just
imagine
a
router.
You
have
some
line
cards
with
copper,
rj45
interfaces
and
some
are
with
gig
optical
ports.
So
it's
similar
to
that.
That's
how
the
gateways
for
a
industrial
network
are
designed
today,
but
beyond
just
those
physical
interfaces.
You
still
need
to
understand
data
in
a
more
meaningful
manner
now
and
what
I
have
I'm
looking
at
emerging
applications.
D
E
Yeah,
so
so
it's
really
easy
to
write
up
an
ip
of
a
network
spec.
So
we
have
an
existing
spec
ipo
mstp.
We
could
just
change
a
little
bit
and
then
it
would
be
ip
over
modbus.
But
there's
no
point
to
that
because
the
devices
that
are
on
the
modbus
have
no
idea
what
ip
packets
are.
So
we
need
to
have
some
some
idea
of
making
these
networks
available,
and
that
is
probably
something
that
only
the
the
seos
that
define
the
net.
These
networks
really
can
do.
So.
E
A
F
It's
interesting
that
both
you
and
michael
said
that
if,
if
we
build
it,
they
will
come,
that
is
to
say,
or
at
least
they'll
scream
at
us
one
of
the
two
in
one
particular
case
they
didn't
either
and
it
was
with
tls.
If
you've
been
involved
in
opc
flc,
you
know
they
pretty
much
reinvented
tls,
which
is
not
so
good
right
because
they
probably
did
it
poorly.
F
F
Here
at
the
ietf
that
work
really
hard
at
it,
but
one
question
we
have
to
ask
is:
why
did
they
do
that
right?
What
is
it
that
about
what
they
did
for
themselves
that
we
couldn't
deliver
to
them?
I
think
that
would
be
a
very
useful
question
and
one
of
the
great
ways
to
start
is
to
say
is
to
ask
the
questions
like
you.
You
have
some
overlapping
technology.
F
F
I
mean
it
might
even
be
a
sort
of
fun
once
we
start
meeting
in
person
again
to
do
like
to
go
to
them
and
have
a
an
interim
meeting
of
this
group
with
somewhere
in
proximity
to
iic.
So
I
love
that
idea.
I
think
it's
great
anyway.
I
just
just
a
caution
about
you
know
not
sometimes
they
don't
even
tell
us
and
so
the
communication
aspects.
F
One
things
I
I
think
we
could
we
might
take
from
this
conversation-
and
maybe
this
is
for
the
chairs
to
consider-
is
if
you
could
put
together
a
couple
of
liaison
statements
to
opc
flc
and
to
iic
along
the
lines
telling
them
about
us
telling
telling
them
about
the
group
and
telling
them
we're
looking
for
open
problems
and
and
also
that,
where
they
found
technology
that
they
couldn't
use
and-
and
you
know
tls
is
just
one
example.
Thank
you.
A
Yeah,
so
this
definitely
is
a
interesting
topic,
but
I
really
have
to
cut
this
short
a
little
bit
to
give
the
other
presenters
that
time
but
again,
kiran.
Please,
please
push
this
on
the
list,
dissect
it
to
a
smaller
items
that
you
want
to
prioritize,
maybe
and
and
and
please
stay
with
us.
This
is
a
good
way
forward.
B
B
B
E
A
B
A
B
So
I'm
going
to
talk
a
little
bit
a
lot
about
locks
and
why
you
care
about
them
and
what
that
has
to
do
with
iot
and
the
simplest
thing
is
to
realize
that
a
smart
lock
is
like
the
simplest
iot
actuator
you
can
imagine,
it
has,
can
have
a
single
single
gpio
pin
that
runs
a
solenoid
that
you
know
does
something
to
make
your
door
open
or
something
like
this.
Now,
it's
not
really
all
about
locks.
B
It's
really
it's
about
everything
that
you've
ever
had,
that
is
an
iot
device
in
your
home
or
or
office
or
building,
because
ultimately
they
all
build
on
this.
But
at
some
point
it's
a
lock.
So
if
you're
in
a
room,
I
would
say
to
you
how
many
of
you
have
a
neighbor
with
your
spare
key,
and
I
bet
half
of
you
at
least
half
you
put
your
your
hand
up.
Do
you
have
your
neighbor's
spare
key
yeah?
B
I
do
and
my
neighbor
used
to
come
every
week
to
use
it
to
and
then
forget
to
return
it,
and
so
we
actually
round
up
with
three
or
four
copies
of
their
spare
key
specifically
because
they
would
forget
to
return
it.
We
gave
them
our
spare
key
and
the
one
time
we
needed
it.
They
couldn't
find
it.
Where
is
my
spare
key
now?
Well,
they've
moved
three
years
ago.
I
don't
know
if
they
threw
it
out
or
found
it.
I
have
no
idea
where
that
spare
key
is.
B
Am
I
gonna
re-key,
my
house,
I
don't
don't
think
so.
I'd
like
to
just
be
able
to
turn
their
key
off,
but
I
can't
do
that.
So
this
is
what
it's
about
here.
You
think
about
this
as
a
fundamental
problem,
and
then
you
translate
this
to
the
digital
world.
How
many
people
have
your
keys?
How
many
people
need
to
have
your
keys?
So
one
way
you
may
have
seen
this
is
like
you
may
have
seen
this
with
realtors
use.
B
Well,
there's
other
ways
of
doing
this.
It
turns
out
you
can
have
these
things
which
are
or
gates
for
the
keys.
So
any
one
of
these
padlocks.
If
you
remove
it,
you
can
then
slide
something
out
and
then
finally,
you
can
remove
the
thing
who
used
which
key
who
has
access
to
those
keys
when
you
take
it
apart,
can
you
add
a
new
or
gate?
The
answer
is
yes,
can
you
build
an
and
gate?
B
Where
so,
who
opens?
Who
puts
your
mail
in
your
mailbox?
You
live
in
an
apartment,
so
the
mailman
may
need
to
enter
the
front
door,
which
you
have
a
code
or
another
key
to
do,
and
then
they
may
need
to
either
go
behind
this
system
of
systems
where
they
can
put
the
mail
in
or
sometimes
there's
no
behind,
and
they
open
the
keys
in
the
front.
Apparently,
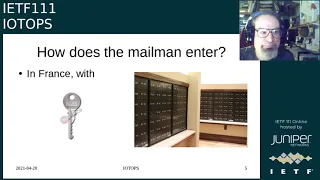
in
france,
there's
an
official
key
for
this,
the
ptt
key,
which
you
have
a
picture
there
of.
B
B
So
I
don't
suggest
you
cut
your
own
key
from
this,
but
that's
an
example
of
a
master
key
and
there
is
a
master
key
in
new
york
and
many
other
cities
that
the
fire
department
and
the
and
the
police
department
have
for
doing
things
like
controlling
elevators,
getting
through
front
doors
and
this
kind
of
stuff-
and
they
recently
showed
up
or
a
couple
years
ago,
showed
up
on
ebay,
and
you
just
got
to
imagine
like
this
is
a
disaster.
You
can't
possibly
have
a
master
key.
B
B
So
how
do
the
police,
if
they
don't,
have
a
key?
Well,
you
know
you've
seen
this
in
movies.
You've
seen
this
in
real
life
and
other
places
like
this.
You
know
it's
basically
battering
ram
and
whether
or
not
they
need
to
announce
themselves
and
whether
they
need
a
warrant
or
not
and
what
conditions?
Well,
that's
a
a
a
different
subject.
Let's
just
talk
about
the
mechanism
of
once
they're
allowed
to
do
it,
how
do
they
do
it,
and
this
is
what
you
see
so
this
picture.
B
Actually
I
found
when
I
was
looking
for
this
and
it
turns
out
it's
an
event
where
the
police,
apparently
in
amsterdam,
broke
into
apartment,
to
rescue
what
they
thought
was
a
woman
in
in
in
who
looked
dead,
but
actually
was
a
sex
doll.
So
you
can
imagine
you
come
back.
You
come
home,
your
door's
blocked,
open
everyone's
know.
What's
going
on,
you
have
to
replace
your
door
because
it's
been
smashed
and
if
only
they
could
have
just
entered
it
with
some
other.
B
You
know
less
violent
way
and
determined
that
oh
okay,
this
was
not
someone
in
distress.
This
was
not
someone
at
all.
The
other
thing
that
I
thought
was
particularly
tragic
was
well.
How
do
they
even
know
which
door
to
enter
and
here's
a
picture?
I
pulled
off
of
a
off
of
a
video
and
here's
the
associated
one
next
to
it
and
if
you've
seen
this
show
called
in
the
line
of
duty.
You
know
this
is
how
it
starts.
B
This
is
how
the
cop
basically
discovers
that
he
didn't
really
want
to
be
in
this
business,
because
essentially,
someone
was
killed
because
a
nail
was
missing
and
a
59
had
become
a
56
and
guess
what
they
entered
the
wrong
home.
And
then
there
was
a
cover-up
and-
and
you
know
it's
tv-
whether
it's
real
or
not,
but
you
can
see
that
that's
a
fairly
realistic
plot
scenario:
it's
not
really
totally
security
theory,
it's
like!
Oh,
my
goodness,
you
couldn't
have
a
cover-up.
B
So
when
you're
locked
out
and
your
neighbors,
don't
can't
find
your
key
and
this
kind
of
stuff,
you
call
a
locksmith
and
they
do
something
drill
out
your
lock
or
they
have
some
other
mechanism
that
they
do.
And
you
know,
then
you
know
they
give
you
new
keys
and
does
locks.
How
does
the
locksmith
know
you're
authorized
and
I
see
pete
resnick
said
in
in
chat
happy
that
my
smart
locks
do
not
have
any
connectivity,
which
is
an
interesting
thing
to
say,
because
what
he's
really
saying
is
that
he's
happy?
B
B
That
picture
didn't
go
well.
What
happened
to
my
picture?
That's
the
right
picture,
yeah,
they
hired
a
locksmith,
and
everyone
watched
him
on
video
drilling
out
the
lock
right.
So
this
was
not
a
digital
lock.
Obviously
this
was
a
block
on
a
digital
key,
but
the
question
was
well.
Can
anyone
do
that?
B
Well,
obviously,
not
they
had
to
get
physical
access
to
the
building
and
a
whole
bunch
of
other
stuff
like
that,
had
to
happen,
but
there's
a
lot
of
layers
of
authorization,
and
you
know
to
do
this
and
that's,
I
think,
an
interesting
thing.
That's
not
what
you
want
to
do
with
your
furnace.
Okay,
if
your
furnace
doesn't
start
anymore,
because
you
don't
have
the
keys,
you
don't
think
you
want
to
replace
it.
You
don't
think
you
want
to
do
a
locks.
B
Do
a
call
a
locksmith
because
they
can't
help
you,
so
you
need
to
think
about
who's
allowed
to
open
your
door,
who
is
allowed
to
change
the
list
of
who
can
open
a
door
and
when
it
gets
open
who
gets
to
know
about
it?
That's
an
interesting
question
right
I
mean.
Would
you
do
you
want
to
know
what
time
your
teenager
came
home
last
night
or
if
they
did
and
as
I
said
you
just
don't
want
to
have
to
drill
out
your
furnace?
This
is
really
not
just
about
locks.
B
Was
everything
else
there
so
who
does
the
authorization
for
you?
Well,
of
course,
you're
going
to
say
you.
I
do
all
the
restoration
of
you
well,
okay,
so
maybe
you
now
have
a
spouse,
or
maybe
you
have
a
more
complicated
family
home
relationship
and
probably
at
some
point
you
have
a
teenager
that
you
wish
would
an
adult
an
adult
child
who
you
wish
would
move
out,
and
now
you
have
to
ask
yourself:
are
they
allowed
as
an
adult
to
decide
who
can
enter
and
exit
your
house?
Is
there
house
two?
B
B
So
now,
apparently,
you
may
not
even
have
access
to
your
own
locks
because
someone
else's
power
of
attorney,
so
that
may
be
terrible
from
your
point
of
view,
but
from
the
rest
of
our
point
of
view,
it's
probably
a
good
thing
since
you're
not
authorizing
santa
claus
to
enter
your
house
in
a
pr
other
than
on
the
25th.
So
the
issue
is
well.
How
did
that
work?
How
did
this
transition
work
out?
Did
you
have
to
replace
the
locks
each
time?
B
That
would
be
crazy,
because
I'm
not
just
talking
about
your
front
door,
I'm
talking
about
everything
and
if
things
go
badly
for
you,
does
your
house
get
foreclosed,
I
mean
that
does
happen
at
which
point
you
know
it's
not
really
well,
it
doesn't
really
do
everything.
It's
not
slide
transitions,
at
which
point
it's
actually
the
sheriff
that
controls
your
lock.
So
how
do
we
manage
that?
How
do
we
manage
an
orderly
transition
from
you?
B
Bought
the
house
alone,
shared
it
with
your
your
family,
with
your
children,
your
caregiver,
and
now
the
bank
gets
it.
This
is
a
legal
process.
This
is
not
something
that
is
like.
Oh,
my
goodness,
these
are
hackers
attacking
your
thing.
This
is
a
legal
process.
How
are
we
going
to
manage
that
problem?
So
am
I
talking
about
installing
back
doors,
and
the
answer
is
no.
No
back
doors
are
something
installed
without
your
knowledge.
B
B
So
am
I
talking
about
some
kind
of
kia
scroll.
Well,
that
would
work,
but
that's
not
what
I'm
talking,
because
there's
no
at
no
point
do
you
want
to
install
the
local
sheriff's
key
in
your
lock
so
that
they
can
do
this?
What
you
want
is
somehow
to
because
that
key
will
expire.
It'll
get
compromised,
it'll
be
attacked,
so
you
somehow
need
to
say.
B
I
want
to
allow
a
judicial
entity
to
access
my
house
according
to
some
judicial
process,
and
I
want
to
do
it
like
pete,
without
having
a
without
without
having
to
necessarily
be
online
or
have
a
cloud
service
delegated
to
me.
So
why
would
we
standardize
such
a
thing?
Well,
obviously,
because
we
need
to
have
good
libraries
and
has
to
be
better
understood
and
we
can't
be,
it
can't
be
obscure.
B
B
B
F
F
It's
not
just
the
door
lock
right!
It's!
As
you
said,
it's
everything
it's
the
heater,
it's
the
temperature
sensor
and
there's
probably
an
architectural
argument
that
there
needs
to
be
a
at
least
a
control
function
within
the
house
to
manage
all
of
this,
so
that
when
you
take
possession
one
way
or
the
other
you're
taking
possession
of
all
of
this,
but
I
actually
had
some
practical
advice,
which
was
simply
to
inventory
what
the
heck
is.
F
There
that's
a
hard
enough
job
right
so
that
when
you,
when
you
leave
the
house,
when
you
go
in
you
act
when
you're
buying
you,
you
say
hey,
what
do
you
got
right
and-
and
somebody
should
be
able
to
tell
you
that
and
if
they
can't
tell
you
that
right
if
they
can't
tell
you
how
the
heater
is
going
to
work
when
you,
when
you're
moving
in
you
got
a
problem.
So
just
I
think
some
document
along
this
line
is
probably
worth
a
at
least
an
informational
comment,
or
something
like
that.
F
A
H
G
B
Actually,
I
was
going
to
ask
the
hip
rc
rg
to
review
this
and
there's.
I
think
you
and
I
both
saw
the
same
presentation
two
years
ago
from
a
woman
from
imperial
college
about
this,
and
I
was
going
to
ask
her
for
her
comments
as
well
on
places,
because
I
think
that
is
additionally
a
really
big
deal
yeah.
I
think
that's.
A
A
I
I
Yep,
you
know
it
just
didn't
want
to
unmute.
While
I
was
looking
for
the
slide
so
so
sorry
for
I,
I
actually
published
a
draft,
but
I
didn't
get
it
done
before
the
deadlines
is
actually
there
now,
but
this
is
sort
of
building
on
some
other
things
and
expanding
on
some
things
that
were,
I
think,
talked
a
bit
about
at
the
interim
as
well
back
in
march,
but
go
ahead
next
slide.
I
This
is
looking
very
small
on
my
screen
for
some
reason,
but
so
I
mean
part
of
what's
been
talked
a
fair
bit
about
at
the
itf.
Is
you
know
you
know
networking
the
networking
aspect
of
onboarding
right
that
we
need
to
grant
some
access
to
the
the
network?
Is
it
just
a
local
network?
Is
its
access
to
the
internet?
I
We've
done
this
stuff
in
the
idea
for
a
long
time.
You
know
people
do
things
with
mac
addresses.
We
have
this
nea,
whatever
various
things
where
you
might
have
to
your
laptop
will
have
to
go
through
some
assessment
before
it
gets
full
access,
etc.
Right,
I
think
that
you
know
iot
the
only
thing
that
iot
changes
here,
which
ugly
quite
significant
is
that
we're
no
longer
assuming
that
we
have
a
ui.
I
So
you
know
people
have
talked
about
the
stuff,
the
noob
stuff
sort
of
partly
came
out
of
the
irtf.
You
know,
there's
other
things
that
have
been
discussed
from.
You
know
brisket
and
dpp
whatever
right,
but
there
could
also
be
cases
when
the
the
network
access
itself.
Onboarding
is
trivial
because
it's
the
physical
access
inside
the
plant,
you
plug
in
the
ethernet,
cable
and
you're
done,
but
there's
still
plenty
of
onboarding
going
on.
Let's
need
that
next,
one.
I
So
so
one
thing
that
might
come
up,
is
you
know?
Yes,
you
might
get
access
to
the
network,
but
it's
just
something:
fine
and
grain
like
the
notion
that
you
have
something
like
mud
and
it
might
say:
well,
you
are
only
allowed
to
connect
to
these
ip
addresses
this
rate,
these
port
numbers,
whatever
right,
yeah,
there's
some
assumptions
here
about
a
device
equals
one
application
or
the
set
of
applications
being
fixed
on
the
device.
Let's
get
more
to
that
later.
Next.
I
If
you
look
at
the
whole
scope
of
things
is
a
fairly
specific
case
in
general
and
there's
more
or
less
the
aspect
of
yeah.
Can
this
be
managed
by
some
management
system
or
some
controller
or
whatever,
and
and
these
things
are
actually
in
principle,
quite
hard?
If
you
say
it
needs
to
be
secure,
well,
you
could
try
to
find
it,
but
what
does
it
mean
to
actually
having
setting
up
the
mutual
trust
and
that
might
include
verifying
that
the
actual
device
that
is
managed
is
actually
legitimate?
I
You
know
at
the
station
type
things
like
rats
whatever
right,
what
what
do
you
actually
need
to
check
before
you
do
that,
but
a
key
thing
that
actually
comes
in
and
the
document
actually
talks
a
bit
more
of
this
sort
of
the
continuum
where,
if
you
look
at
the
iot
ops
charter,
it
talks
about
things
that
are
deployed
at
scale
that
don't
have
a
user
interface
or
have
very
limited
user
interface.
Well,
those
things
are
not
necessarily
resource
constrained.
Some
of
them
are,
but
not
all
right.
I
So
it
seems
like
sort
of
splitting
this
apart
and
thinking
about
onboarding
devices,
and
maybe
part
of
that.
Maybe
that
has
multiple
pieces
as
well,
because
there
could
be
a
hardware
maintenance
player
in
this
picture
that
might
want
to
be
able
to
see
that
this
device
is
there,
and
so
they
can
actually
look
at
hardware
diagnostics.
Is
the
disk
slash,
ssd
wearing
out
whatever
right,
as
well
as
other
players
that
are
worried
about
the
sort
of
device
itself
and
the
operating
system
on
it,
as
well
as
the
individual
applications
that
are
being
run?
I
So
now
you
can
actually
know
without
trying
things
too
closely
to
the
manufacturer
be
able
to
do
this,
but
but
it's
still
fairly
complicated,
so
there's
could
be
other
ways
as
well.
Like
one
thing,
that's
quite
simple
is
sort
of
configuring
things
once
and
then
figuring
out
how
that
imprinting
actually
flows
through
the
system.
I
I
I
think
the
next
one
is
just
the
summary
slide
right.
So
if
I
remember
my
slides
yeah
so
so,
basically,
the
contribution
of
this
is
getting
people
to
think
about
yeah,
don't
assume
that
there's
a
single,
predetermined
application
or
even
two
predetermined
applications.
I
think
that
we
need
to
think
about
devices
separate
from
the
actual
applications
running
on
them.
I
If
you're
a
networking
person,
you
can
think
of
those
as
nfvs,
but
it
could
be
your
ai
application
or
whatever
and
it
could
be
different
policies,
you're
sort
of
tying
back
to,
and
this
is
sort
of
very
sketchy,
but
that
you
know
sort
of
the
network
access,
authentication
authorization
as
opposed
to
the
the
onboarding
from
the
to
the
management
station.
Slash
controller.
Well,
what's
the
relationship
between
those
things?
I
don't
think
that
there's
a
single
model
that
fits
all
here
and
then,
finally,
the
you
know
figuring
out
what
are
actually
the
roots
of
trust.
I
A
I
I
So
so
it
I
mean
it
sort
of
you
want
to
get
to
a
state
where,
where
the
the
device
actually
trusts
a
root
certificate
of
some
form
right,
saying
anybody
who
who
has
a
certificate
under
this
route,
I
will
actually
trust
to
get
configuration
and
you
want
to
have
likewise.
Have
the
controller
actually
have
a
list
of
the
set
of
device
certificates
that
it
will
actually
talk
to
right
and
then
how
do
you
actually
get
there
get
from
from
scratch
to
that?
Well,
and
you
know
the
different
different
models.
I
They
can
actually
do
this
do
this,
but
it's
sort
of,
if
you
look
at,
I
don't
know.
If
you
looked
at
the
the
fido's
stuff,
more
sdo
there's
actually
another
project
in
lf
edge,
which
is
called
sdo,
which
is
secure
device
onboarding,
which
is
actually
implementing
open
source
implementation
of
the
fibo
spectrum,
but
but
that
has
more
complex
things
to
actually
enable
you
to
track
things
through
the
actual
supply
chain.
What
we
have
in
project
eve
is
actually
quite
minimalistic,
but
but
it's
it's.
You
know
yeah
public
key
crypto
right,
basically
standard.
You
know!
I
I
A
H
So
we
got
lots
of
good
things,
but
not
a
lot
of
detail
on
exactly
how
it
fits
together
and
not
a
lot
of
detail
on
what
kind
of
security
benefits
you
get
if
you
put
it
together.
So
the
idea
behind
this
draft
is
to
provide
some
kind
of
idea
on
what
happens
when
you
put
all
these
pieces
together
next
slide,
please.
H
So
we
have
some
fundamental
questions
that
we
need
to
ask
when,
when
building
a
device
so
or
when
operating
one,
what
software
is
my
device
running?
Where
did
it
come
from
and
who
can
do
software
updates
and
and
under
what
circumstances,
and
and
more
than
that?
How
is
the
software
actually
installed?
H
H
So
the
the
really
interesting
question
here
is:
where
is
all
the
trust
in
this
system?
Now
I've
left
teep
out
of
this
because
it's
a
whole
other
layer
of
something
similar
on
top
of
this
diagram.
But
I
think
this
one's
probably
the
more
interesting
one
since
teep
already
does
a
good
job
of
covering
its
trust
diagrams.
H
So
this
actually
looks
like
some
of
the
technologies
that
we've
been
looking
at.
There's
a
variety
that
that
map
onto
this,
so
we've
got
rats
for
handling
the
attestation
and
the
communication
with
the
verifier
we've
got
mud
for
network
access
requirements,
we've
got
coast,
wood
or
perhaps
co-rim
for
the
information
coming
from
the
application
author
and
going
to
the
verifier
and
and
we've
got
suit
for
doing,
updates
and
a
a
fair
selection
now
for
doing
key
provisioning
next
slide,
please.
H
So
what
this?
What
I've
come
up
with
here
in
this
in
this
diagram
or
in
this
document,
is
a
set
of
recommendations
for
what
the
various
parties
in
the
iot
ecosystem
should
do
so
devices
should,
or
I
guess,
device
developers
should
a
test.
Their
application
should
support,
secure
remote
update
and
use
a
secure,
onboard
onboarding
protocol
and
use
trusted
execution
environments
to
protect
any
valuable
assets,
be
those
applications
keys
personally,
identifying
information.
H
And
they
should
issue
network
access
requirements
with
those
updates
as
well.
Verifiers
should
consume
model
attestation,
evidence
and,
and
so
what
that
means,
essentially
in
in
that
case
since
I
realize
it
doesn't
map
completely
onto
what
I've
written
there.
The
idea
here
is
that
you'd
use
something
like
a
co-rim,
and
that
would
say
what
you
should
expect
when
you
do
an
attestation
and
then
that
would
be
an
input
to
the
verifier.
H
So
the
verifier
can
then
take
that
and
produce
a
a
good
idea
of
whether
a
device
is
trustworthy
or
not,
and
network
operators
should
do
a
bit
to
protect
their
networks
from
devices
that
may
have
been
compromised.
So
to
do
that
they
can
place
a
device
in
a
demilitarized
zone
until
an
attestation
report
is
received
and
they
can
also
apply
restrictive
network
policies
to
devices
that
are
out
of
policy
like
might
require
an
update
and
enable
network
access
requirements
based
on
those
attestation
reports,
and
that's
it
so
very
quick
overview.
K
K
So
those
are
kind
of
the
questions
in
my
mind
and
the
last
thing
I
was
just
going
to
say
and
I'll
just
let
you
respond
to
anything
else,
which
is,
I
think
your
analogy
to
teep
is
accurate
because
kind
of
your
picture.
There
mapped
to
a
lot
of
what
teep
did
and
having
an
architecture
that
just
kind
of
puts
those
together.
Maybe
it
actually
is
a
road
map
and
architecture
that
would
just
be
informational,
so
open
to
your
thoughts.
So.
H
Yeah,
I
think
that
it,
one
of
the
things
that's
hindered,
iot
deployments
so
far-
is
that
each
of
these
parties
just
claims
that
they
are
doing
their
own
little
bit
and
and
the
rest
of
it's
not
their
problem
and-
and
I
think
that's
one
of
the
big
issues
that
we
face
is
that
we've
got
too
many
people
and
all
of
them
are
abdicating
responsibility
so
having
something
where
you
know,
we
together
do
actually
conform
to
this
recommendation.
I
think
that
would
be
really
useful
and
maybe
that's
something
that
that
is
too
big
for
this.
H
I'm
not
sure,
but
it
is
a
whole
system,
and
I
think
that
it's
important,
that
the
parties
that
are
that
are
part
of
iot
deployments
do
have
to
work
together
and
they
should
together
conform
to
you
know,
recommendations.
I
don't
know
what
those
recommendations
will
be.
You
know
here's
a
suggestion
for
some,
but
in
the
end,
who
knows
yeah,
so
I
I
I
take
your
your
point
that
that
there's
four
different
sets
of
parties
here,
but
at
the
same
time
they
do
have
to
work
together.
K
K
I
don't
know
if
what's
one
or
a
set,
I
don't
know
so,
I'm
supportive,
but
given
that
I'm
kind
of
thinking
about
what's
the
right
intended
status
right,
is
this
saying
this
is
a
proposal
for
an
informational
document
or
a
bcp
or
some
standard
track
thing,
and
maybe
bcp
is
kind
of
what
we're
thinking
about
here
and
what's
the
right
way
to
organize
that
if
it's
a
bcp
given
that
there's
multiple
parties
here,
how
would
we
go
about
that,
but
overall
yeah?
I
think
this
is
great
stuff.
I'm
supportive.
A
Thank
you
dave,
and
we
will
come
back
to
the
point
of
adoption
of
documents
later
and
I
will
make
sure
that
we
are
covering
this
before
this
session
ends
and
and
to
enable
that
we
will
move
on
to
ellen's
presentation
but
be
assured.
I
will
try
to
have
this
five
minutes
to
talk
about
next
steps,
which
includes
an
plan
forward
for
working
group
documents.
L
L
The
problem
is
that
getting
on
the
net
is
hard,
this
document's
about
60
pages,
about
10
of
which
are
various
polite
description
of
what
vendors
do,
and
this
is
phone
vendors,
os
vendors,
mainly
personal
devices,
not
bio
iot
devices,
and
this
is
just
random
changes
in
the
last
10
years.
It's
really
really
bad
really
hard
to
do.
L
L
L
L
You
can
verify
to
the
user
that
you've
gone
to
the
correct
domain,
downloaded
the
correct
certificate.
Everything's
signed,
everything's,
known,
everything's
trusted,
and
now
the
user
knows
you
can
enter
his
password.
So
next
slide
there
is
running
code
and
it
doesn't
require
any
changes
to
eep
supplicants.
L
Eep
servers,
it's
just
put
some
stuff
in
dns,
put
some
stuff
in
the
web,
run
a
utility
script
and
it
will
spit
out
a
wpa
supplicant
configuration
file
or
a
os
x
mobile
config
file
that
you
can
then
use
to
get
network
access,
and
this
is
not
then
trust
on
first
use.
It's
end
to
end
trust
verified
at
every
step.
G
L
F
Down
the
reason
I
ask
you
to
present
here
is
that
every
problem
that
you
hit
in
the
user
space
we
hit
over
here
in
the
iot
space
in
spades,
and
so
one
of
the
things
that
we
might
want
to
think
about
as
you're
developing
the
draft
is
whether
we
can
apply
some
of
the
concepts
which
take
the
username
out
of
it
in
in
and
assert
a
different
identity
type
as
we're
going
forward.
I
don't
know
if
you're
amenable
to
that,
but
it's
something
we
might
want
to
think
about.
L
A
M
Presentation
is
up-
and
I
can
say
next
slide
right,
so
so
we're
leaving
the
space
of
device
centric
and
security
and
going
into
addressing
a
completely
different
planet,
but
maybe
interesting
as
well.
That's
what
I'm
here
for
and
so
the
motivation
was
that
you
know
in
other
working
groups
and
in
irtf.
M
So
you
know,
a
couple
of
us
are
starting
to
look
into
you
know
what
problems
may
we
have
with
addressing
and
can
we
evolve
beyond
what
we
have
in
ipv6,
whether
it's
within
ipv6
or
with
the
newer
network
protocols
or
so
is
completely
open
and,
and
is
part
of
you
know
an
answer,
but
really
it's
about
the
question
right.
What
what
what
are
you
know
possible
challenges
that
we
have
with
existing
addressing,
and
so
you
know
I
had
some
of
my
personal
answers
to
that,
and
you
know
from
that.
M
I
I
started
to
try
to
you
know
come
up
with
an
idea
for
how
we
could
potentially
solve
that,
and
here
I
just
wanted
to
talk
about
what
I
think,
as
part
of
the
problems
would
potentially
apply
to
iot
but
then
ultimately
raising
overall.
The
question
you
know
is
is
looking
into
problems
with
addressing
specifically
for
iot,
something
just
you
know
to
bring
together
and
collect
the
information
about
problems
interesting.
So
next
slide.
M
Yeah,
so
this
is
this
is
my
view
of
the
world
right
and
that's
basically,
the
that
you
know.
There's
a
lot
of
talk
about
just
the
internet
and
the
internet
is
everything
and-
and
so
even
even
you
know,
folks,
like
brian
carpenter,
you
know
started
to
say
no,
that's
that's
not
true.
I
mean
we
basically
have
only.
Maybe
you
know
this
is
my
scientific
number.
M
You
know
constrained
device,
iot
networks
that
have
been
dominating
a
lot
of
the
iot
work
in
the
itf,
but
even
you
know,
service
providers,
enterprise
federation-
you
know,
non-iot
networks
are
pretty
much
not
quote
on
the
internet,
but
in
their
own
domains,
and
there
is
a
lot
of
issues
you
know
that
are
different
than
the
internet
and
potentially
addressing
is
one
of
them
and
of
course,
there's
also
a
much
wider
use
of
you
know.
Itf
protocol
extension
features
in
these
networks
than
on
quote
the
internet,
and
you
know
when
looking
at
it.
M
I'm
not
even
thinking
that
for
many
of
these
networks,
ipv6
is
an
improvement
over
ipv4.
I
don't
want
to
go
into
all
the
details.
I've
written
down
here,
they're
all
in
a
giraffe
but
I'll
I'll
regurgitate
on
the
ula,
the
unsigned
local
address.
Sorry,
the
unique
local
addresses
thing
now
and
how
it
compares
to
in
1918
next
slide.
M
M
Addressing
space
isn't
really
helping
anybody,
and
you
know
you
almost
never
even
need
any
to
any
communication,
but
you
know,
as
we've
also
seen
with
the
network,
we
actually
do
like
in
these
networks
to
have
very
explicit
provisioned
or
you
know,
automatically
provisioned.
You
know
connectivity
and
the
ability
to
rebuild
these
things
very
flexibly
without
having
to
figure
out.
You
know
what
does
that
mean
for
addressing
and
that
that
you
know
in
industrial,
but
even
in
transportation
networks
that
are
is
as
large
as
countries
or
so
is.
M
In
my
opinion,
a
problem
and
so
next
slide
one
of
the
very
common
approaches
on
how
you
do
addressing
in
these,
and
that's
why
you
know
if
you
look
at
an
industrial,
ethernet
switch
you'll
always
find
some.
You
know
explicitly
provisioned
static,
not
net
functionality,
and
the
reason
why
that
is
is
because
you're
using
generic
addresses
right.
So
let's
say
you
have
a
machinery
with
com,
some
sensors
actors
and
a
plc
you
give
when
you
build
this
product
this
machinery.
Each
of
you
know
these
components
a
fixed
ipv4
address.
M
You
know
you
build
thousands
of
these
machineries
that
you
don't
give
them
different
addresses
and
you
don't
provide
mechanisms
for
you
know
changing
the
address
on
each
of
these
devices,
but
it's
just
the
gateway
that
will
support
net
and
so
showing
here
how
you
plug
together
the
same
or
different
type
of
equipments
netting
them
into
one
lan
for
let's
say
the
system,
and
then
you
may
have
another
layer
of
the
netting
where
you
go
then
into
let's
say
this:
production
line
level
right
and
with
ipv4.
That's
very
easy.
M
With
the
you
know,
middle
two
bytes
of
the
address,
so
you've
got
two
layers
that
you
can
build
and
astoundingly
you
can't
even
do
more
with
ipv6
when
you
use
the
unique
local
addresses,
because
they
also
only
have
16
bits
free
for
you.
So
this
this.
This
really
is
one
of
these
problems
which
I'm
calling
you
know
independent
address
spaces
and
how
you
connect,
whether
hierarchically
or
in
more
interesting
topologies
networks
together
without
having
to
do
a
lot
of
re-addressing
in
these
right
and
we've
seen
in
ipv6.
M
A
lot
of
people
standing
up
against
the
ietf
dogma
of
nat
is
evil.
Go
away
with
nat
and
have
you
know
in
the
last
five
years,
or
so
we've
seen
more
and
more
net
also
happening
in
the
ipv6
space.
To
handle
problems
like
this
and
well.
We've
got
a
total
of
26
or
more
ipv4
to
ipv6
net
solutions,
so
this
is
all
a
very
convoluted
space
where
maybe
you
know
more
work,
even
starting
by
you
know
putting
together
a
list
of
problems
may
be
beneficial.
I
think
that's.
M
What
I
had
right
next
slide
is
more
yeah,
so
I'll
be
presenting
my
proposed
solution
together
with
these
intro
slides
in
in
the
area
and
routing
working
groups
later
in
this
week.
So
if
you're
interested
join
there,
but
as
far
as
iot
ops
is
concerned,
right
forget
about
my
solution
proposal
right
here,
whether
you
like
it
or
not,
but
you
know
how
about
addressing
right.
Security
is
great
device.
Onboarding
is
great,
but
if
we
want
to
be
more
comprehensive,
what
do
we
think
about?
M
A
Much
well
actually
thank
you,
toless
for
condensing
down
the
take
home
message
here,
which
I
think
on
the
chat
already
found.
Some
positive
reinforcement,
yeah.
That
seems
to
be
a
interesting
conundrum
and
also
it
is
a
little
bit
associated
with
our
very
first
presentation,
where
we
have
absolutely
different
address
spaces.
But
then
again,
how
do
you
mix
them
into
a
a
layered
ip
network?
That
is
inheriting
old
problems
here?
So
I
think
that's
interesting
problem
statement.
I
don't
know
where
are
you
presenting
your.
M
G
M
A
great
place
to
go
yeah
and
by
the
way
you
know
even
what
I've
completely
forgot.
When
writing
it,
and
just
reminded
now
in
ipv6
one
of
the
things
they
tried
to
do
and
then
gave
up,
because
quote
the
internet
doesn't
need.
It
is
the
scoped
addressing
right
so,
and
I
lived
through
that
because
we
still
have
them
in
multicast,
so
yes,
they're,
complicated
and
they're,
probably
easier
solution,
and
in
unicast
we
gave
up
on
them
right
there.
M
You
know
they
were
these
designated
as
the
ipv6
addressing
solution,
for
you
know
private
scope
domains,
so
that
was
given
up
on
so
yet
another.
You
know
aspect
of
ipv6
being
split
back
to
the
internet
which,
by
the
way
you
know
it
is
the
single
big
it's
in
10
right.
Everything
else
is
is
smaller
individually,
but
in
in
total
it's
just
a
a
lot
more
and
so
yeah.
B
Yeah
about
decade
ago,
I
started
a
flame
thread
on
the
aaron
policy
list
about
essentially,
why
was
it
so
hard
for
manufacturers
to
get
address
space
that
they
didn't
necessarily
want
to
route
right
and
they
should
have
been
giving
this
away
like
candy,
and
I
think
you
hit
the
nail
on
the
head.
You
know
I.
If
I
want
to
build
a
piece
of
equipment
and
I
need
internet
con,
I
need
ip
connectivity,
but
not
internet
connectivity
within
it.
B
Then
I
should
just
be
able
to
use,
get
a
block,
a
reasonably
large
block
of
ipv6,
and
I
can
stamp
out
a
slash,
56
or
even
60s-
probably
sufficient
for
each
device,
but
make
them
all
unique
and
there's
great
advantages
to
doing
this.
But
the
problem
is
you're,
looking
at
several
hundreds
of
dollars
to
thousands
of
dollars
a
year
of
fees
which
someone
has
to
approve,
and
then
the
manager
is
manager
who
says
well,
why
don't
we
just
use
rfc
1918,
that's
free,
yep
and
and
the
problem
this
guy.
B
You
know
what
he
doesn't
want
to
cut
a
check
for
two
thousand
dollars
to
aaron.
Okay,
when
he
can
you
do
this.
For
a
tree
he
doesn't
understand
even
the
difference
of
this
issue.
What's
the
what's
the
problem
back
in
my
day,
we
just
used
squatted
on
11
at
dressness
right,
you
know,
that's
what
he's
going
to
say.
So
this
is
a
problem.
B
But
you
know
what,
if,
if
we
care
about
having
reasonable
addressing
in
iot
assemblies,
then
I
think
that
you
know
we
need
to
push
it
to
somewhere
and
get
it
done,
and
I
don't
care
if
it's
ula
central
or
you
know
four
thousand
slash
three
or
whatever
it's
not
four
thousand
right.
You
can't
call
it
thousands
when
it's
hex,
but
I
don't
have
a
better
word
for
it.
We
should
do
something.
M
Anyway,
thanks
yeah,
I
mean
just
as
a
final
note
right.
I
think
that
something,
like
you
know,
a
problem
statement,
iot
or
even
beyond
that
without
suggesting
solutions.
Might
you
know
raise
more
awareness
to
that
and
I
think
there
is
certainly
a
lot
of
stuff
that
8799
from
bryant
doesn't
mention
about
the
addressing
stuff
right.
So
maybe
that's
that's
the
starting
point.
A
A
Let's
call
it
documents
for
now
that
might
be
aggregated
later
on,
but
from
from
from
precise
statements
here
that
that
really
summarize
them
to
to
be
digestible
for
external
audiences
and
and
yeah.
If
you
can
be
able
to
provide
that
a
big
thumbs
up
now,
transitioning
to
our,
I
think,
last
presentation
for
today
from
kent,
the
oh
sctp
at
iot
ops.
I
know.
A
N
N
The
provisioning
steps
are
able
to
update
the
boot
image,
commit
an
initial
configuration
and
execute
arbitrary
scripts
to
address
auxiliary
needs,
and
here
actually
it's
kind
of
where
it's
different
than
brewski.
I
think
briskey
just
does
the
domain
certificate
part
of
it
and
then
grasp
past
to
do
the
other
part
number
four.
The
updated
device
is
subsequently
able
to
establish
secure
networking
connections
with
other
systems.
Your
orchestration
controller
nms,
whatever
you
want
to
call
it,
but
those
those
secure
subsequent
secure
connections
are
mutually
authenticated.
N
It
supports
both
internet
and
non-internet-based
deployments.
So
private
networks
is
okay,
several
possible
sources
of
bootstrapping
data,
removable
storage
device.
So
here's
sort
of
something
new
and
different,
but
actually
you
could
pre-load
everything
onto
a
usb
flash
drive
and
or
whatever
nfv
device
and
have
it
nearby
or
plugged
into
the
device.
N
Next,
any
such
source
may
be
may
direct
a
device
to
a
bootstrap
server,
so
if
device
connects
to
a
dcp
or
dns
server
or
whatever
even
removable
storage
device
or
or
a
bootstrap
server,
any
of
those
sources
of
information
can
do
nothing
except
redirect
the
device
to
yet
another
bootstrapping
server,
and
we've
seen
this
in
deployments
helpful.
Where
you
know
you
want
to
go
to
a
regional
bootstrap
server,
which
then
takes
you
into
a
a
local,
more
local.
N
N
Lastly,
as
in
the
name,
it
is
secure
so
secure
zero
trash,
mutually
authenticated
certificates.
There
is,
of
course,
the
identity
certificate
on
the
device.
Actually,
it
doesn't
necessarily
require
activity.
Any
secure
identity
certificate
such
as
802
one
ar
would
suffice
and
then
there's
the
manufacturer's
trust
anchor
certificate
also
on
the
device.
N
And
lastly,
here
it
says
bootstrapping
data
may
be
encrypted
with
the
device's
public
key.
So
this
is
actually
interesting
in
the
sense
that,
when
uploading
data
onboarding
data
which
might
contain
sensitive
configuration
or
scripts
or
whatever,
how
well
do
you
trust
the
administrators
of
the
server
that
are
maintaining
the
bootstrapping
server
like
like,
because
they
can
see
anything.
Do
you
trust
them?
Well,
if
you
have
any
concerns
whatsoever,
of
course,
you
can
encrypt
that
data
with
the
device's
public
key
next
slide.
Please.
N
I
think
this
is
pretty
straightforward,
but
you
know
boot.
Bootstrap
on
power
on
you
know,
is
scp
bootstrapping
configured.
If
no,
this
is
boot.
Normally,
even
if
it's
yes,
it's
pretty
much,
I
mean
it
kind
of
depends
on
the
device,
but
many
devices
boot
normally
and
then
it's
kind
of
a
race
condition.
N
Does
the
device
manage
to
bootstrap
itself
off
the
network,
or
does
someone
actually
access
the
console
and
configure
the
device
that
way
either
way
it
would
ultimately
cause
the
device
to
boot
normally,
but
anyway,
if
bootstrapping
is
configured
then
yes,
it
then
it
goes
into
this
loop.
Is
it
able
to
boost,
draw
bootstrap
from
any
source
and
so
to
left
there?
It
says
for
each
source
of
bootstrapping
data
such
as
dns
server,
dhcp
server,
bootstrap
server,
removal,
storage
server,
you
know,
tries.
N
Can
I
can
I
get
any
data?
Can
I
boot
shop
here?
If,
yes,
then
it
configures
itself,
possibly
updating
its
operating
system,
installing
configuration
running
pre-configuration,
scripts,
post
configuration
scripts
etc,
and
it's
fully
provisioned
ready
to
join
the
network,
otherwise,
and-
and
this
might
simply
because
otherwise,
no
bootstrapping
server
is
found.
N
N
Okay,
so
there
are
three
bootstrapping
artifacts
conveyed
information,
ownership,
voucher
and
owner
certificate.
Only
the
first
one
is
needed.
If
for
transport,
if
transport
level,
security
can
be
assumed,
and
otherwise
all
three
artifacts
are
needed.
Sorry,
I
need
to
go
downstairs
here,
because
people
are
talking
upstairs
the
conveyor.
N
So
what
I
mean
by
that
is,
if
shipped
from
manufacturing
the
device
may
have
awareness
of
a
well-known
server,
perhaps
maintained
by
the
vendor
of
the
device
itself,
so
something
like,
for
instance,
redirect.vendor.com
and
the
device
knows
how
to
you
know
it
knows
how
to
trust
that
tls
certificate,
so
it
can
establish
transport
level
security
and
therefore
it
only
needs
the
top
artifact.
The
conveyed
information
artifact.
N
So,
within
that
first
category
of
information
conveyed
information.
We
mentioned
earlier
redirect
information
again
just
telling
the
device
to
some
other
device
where
it
can
go
to
look
for
some
data
and
that
redirect
information
can
also
convey
another
tls
certificate
that
the
device
the
bootstrapping
device
can
use
to
establish
trust
with
that
second
location.
N
The
other
bit
of
information
is
onboarding
information,
and
this
is
the
one
that
actually
contains
the
information
about
what
boot
image.
It
should
run.
Initial
configuration
arbitrary
scripts,
okay,
so
that's
the
first
artifact,
the
other
two,
the
ownership
voucher.
I
think
everyone
on
the
call
is
pretty
familiar
with.
The
owner's
certificate
is
like
the
domain
certificate,
but
how
it's
used
is
different
and
it's
only
used
for
trusting
signed
data
which
we'll
cover
in
the
next
slide
in
the
lower
right
hand
corner
recently.
There's
sorry:
can
you
go
back
to
the
previous
slide?
N
So
what
this
a
draft
does
and
it
updates
http,
is
enable
the
very
first
exchange
that
happens
when
the
device
reaches
out
to
the
bootstrapping
server.
For
the
first
time,
the
bootstrapping
server
and-
and
if
the
device
supports
the
this
this
draft,
then
it
sends
also
input
parameters
regarding
whether
or
not
it
supports
the
generation
of
ldl
database
certificate.
N
If
it
does,
then
does
it
support
generating
a
new
private
key
or
does
it
can
only
reuse
the
existing
id
private
key
if
it
does
support
generating
a
new
private
key?
What
algorithms
to
support
you
know
what
and
you
know
all
that
information.
What
what
and
also
what
certificate
signing
formats
does
it
support?
Is
it
just
you
know,
p10
or
cmp
or
crc
also
cmc
also
supported.
N
All
right
so
conveying
truss
so
again,
a
device
in
his
feet
in
his
factory
default
condition,
can
only
trust
certificates
authorized
by
its
manufacturer
using
trust
anchors.
The
trust
anchor
certificate
is
used
in
two
ways
right.
So
the
first
way
is
what
we
spoke
of
initially,
which
is
to
authenticate
the
remote
tl
server
certificate
is
signed
somewhere
in
shame
by
manufacturing.
So
this
is
that
well-known
service
like
redirect.vendor.com,
the
other
way
is,
is
by
authenticating
the
voucher
right.
N
The
voucher
is
signed
by
the
manufacturer
or
its
delegate,
so
you
can
authenticate
the
voucher
from
the
voucher.
You'll
extract
the
domain
certificate
and
from
the
domain
certificate
you
can
validate
the
owner's
certificate
that
the
domain
certificate
signs
the
owner
certificate
and
then
from
the
under
certificate.
You
extract
out
the
public
key
to
authenticate
the
signed
data,
which
is
that
conveyed
information.
The
first
of
the
three
artifacts
is
the
one
that's
been
signed,
so
you
can
validate
that
that
has
been
signed
by
a
signature.
That's
traceable
through
the
voucher
and
then
last
bullet
point
here.
N
N
So
either
it's
going
to
return
something
to
you,
that's
unsigned,
meaning
you
don't
have
to
trust
it
or
not,
but
a
redirect
response
can
be
unsigned,
and
so
you
can
just
be
redirected
to
go
somewhere
else
looking
for
data
and
maybe
that's
that
other
location
will
be
able
to
hand
back
a
signed
response
or,
as
the
second
and
last
bullet
point
says,
a
signed
response.
So
that
of
course,
is
the
conveyed
information
that's
been
signed,
which
includes
also
the
ownership,
voucher
and
owner
certificate.
N
Next
and
last
slide,
please,
okay,
so
here's
an
eye
chart,
but
essentially
the
power
on
the
device
first
discovers
the
bootstrapping
server
on
the
network.
So,
however,
that
might
be
it
could
be
layer,
2,
layer,
3,
removable
storage,
device,
dns,
dhcp,
well
known
service
or
or
anything
else.
The
rfc
8572
does
not
limit
the
number
of
kinds
of
transports
that
could
be
used
for
discovery
mechanisms.
It's
just
a
strategy,
that's
been,
and
four
such
mechanisms
were
scoped
out
in
that
rfc,
but
once
a
bootstrap
server
has
been
discovered.
N
The
next
line
down
you
can
see
it's
doing
a
post
to
get
this
tracking
data
to
the
bootstrapping
server
whereby
the
id
certificate
is
authenticated
and
then
inside.
That
request
is
information
about
sorry.
I
got
ahead
of
myself,
so
the
bootstrapping
server
sends
a
request
over
to
the
ca,
or
maybe
it's
otherwise
been
configured,
and
it
comes
to
determination
that
the
device
requires
an
ldvd
certificate,
so
it
sends
back
to
the
device,
the
400
bad
requests
containing
selected
algorithms.
J
A
A
N
A
M
M
I
don't
show
what
the
right
terminology
server
or
so
right,
so
that
the
workflow
that's
exercised
on
the
client
device
that
the
pledge
that's
enrolling
is
controlled
much
more
by
by
the
server
and
when
we
had
the
discussion
about,
you
know
how
to
do
certificate.
Enrollment
couple
years
back,
you-
and
I
you,
I
think,
were
pointing
me
at
existing
yang
models
that
could
be
used
with
netcon
f2,
for
example,
push
an
ldf
id
completely
independent
of
what's
happening
in
before
into
a
device
through
net
convent.
M
So
I
was
imagining
that
the
proposed
solution
to
keep
things
modular
and
let
it
up
to
the
server
to
figure
out
what
to
do
would
be
to
you
know:
first
establish
an
author
or
authorize
the
server
through
you
know,
pushing
down
the
vouchers
through
the
zero
touch,
bootstrap
and
then
use
an
existing
model
to
you
know,
push
an
ldf
id,
so
this
solution
here
sounds
different
from
that
more
integrated,
less
modular.
So
I
was
wondering
about
the
motivation
of
this
approach.
N
Yeah,
that's
actually
a
really
interesting
point
and
you're
right.
It
is
more
integrated,
but
I
I'd.
Actually
I
see
that
it
says
strength
like
in,
like
in
storage
systems.
These
days
they
found
that
you
know
by
bringing
together
the
lower
level,
drivers
and
the
higher
level.
You
know,
array
logic.
They
were
able
to
simplify
things
and-
and
you
know,
make
it
less
complex
overall
and-
and
I
think
that
might
be
the
case
here
as
well.
N
N
G
A
N
A
No
problem
without
offline
discussions
are,
of
course
encouraged,
but
so
the
the
the
topic
of
ones
that
bring
up
here
in
our
last
five
minutes-
and
I
I
already
highlighted
that-
is
the
route
towards
adoption
of
documents
in
this
working
group.
So
this
has
been
brought
up
in
the
chat
I
think
already,
and
I
would
like
to
offer
multiple
lanes
towards
that
goal.
A
A
Did
maybe
yeah
but
yeah,
but
if
you
think
that
is
worthwhile
for
us
to
do
contact
us,
so
we
are
not
arbitrarily
now
just
adding
all
the
documents
on
the
agenda
list
here.
If
you
think
this
is
worthwhile
to
to
be
detract
here,
contact
us
this
is
not
a
self
a
fulfilling
procedure,
so
to
speak.
You
have
to
do
at
least
one
step
for
this
to
happen
and
and
again
otherwise.
A
So
is
there
any
other?
I
don't
know
a
question
about
how
to
progress
work
here.
If
you
want
to
do
that,
so,
for
example,
I
saw
documents
that
might
be,
I
think,
associated
with
this
working
group
and
are
not
yet
so
so
that
would
be
a
fire,
namely
name,
but
there
are
the
other
questions
about
this:
how
to
proceed
or
how
to
find
together
here.
A
A
I
I
really
enjoyed
the
two
hours
of
it
and
here
in
germany,
it's
like
three
a.m,
and-
and
that
is
saying
something
I
think
so-
I'm
I'm
I'm
still
with
you,
and
so
I
hope
everybody
else
in
this
audience
also
was
as
engaged
as
I
felt.
Thank
you
for
your
contributions
and
please
again
contest
contact
us
directly
or
we
are
a
follow-up
questions
on
the
list
and
and
show
some
noise
there.
