►
From YouTube: IETF112-COINRG-20211111-1200
Description
COINRG meeting session at IETF112
2021/11/11 1200
https://datatracker.ietf.org/meeting/112/proceedings/
B
B
I
think
everybody
is
aware
of
this.
I
think
it
for
this
group.
Yes,
it's
important,
but
also
you
know
that
we're
recording
this,
because
we
are
still
virtual
and
I
guess
even
when
we'll
go,
not
virtual
we'll
do
it.
I
think,
what's
also
very
important,
is
all
the
disclosures
of
intellectual
property
which
is
on
on
the
next
slide
or
something
and
the
code
of
conduct,
which
is
also
very
important,
and
I
think
a
few
of
us
have
had
experiences
that
show
us
how
important
it
is
eve.
B
B
So
we
have
a
very
packed
agenda,
so
you
know
I'm
already
two
or
three
minutes
into
this,
so
we're
going
to
go
very
fast.
I
think
we're
very,
very
happy
to
have
scott
chanker
to
present
the
extensible
internet,
which
was
a
ccr
paper
and
essentially
raises
a
lot
of
interesting
questions
about
the
future
of
the
internet
and
also
is
is
connected
to
some
of
the
questions
that
we've
had
in
this
group.
So
we're
very
lucky
with
this.
Then
we
have
the
very
interesting
in
network
aggregation
paper.
B
Then
also
the
information-centric
data
flow
for
distributed
computing
from
dirk,
and
we
we
had
well,
it's
actually
ideas,
but
actually
there's
only
one
alessandro,
because
it's
a
holiday
is
not
going
to
present.
I'm
going
to
present
this
it's
about
an
operating
system
for
distributed
applications
and
in
coin,
we
are
very
big
on
thinking
that
the
internet
is
moving
to
be
more
like
a
computer
board,
and
if
we
have
a
computer
board,
you
need
an
operating
system
next
slide,
then
we
have
the
drafts
update.
B
Obviously
a
research
group
is
not
too
about
doing
only
drafts,
but
we
do
have
very
interesting
work.
This
is
happening
in
the
drafts
with
this
research
group
and
we
would
like
to
give
them
a
chance
to
talk
about
the
ideas
so
use
cases
again
to
show
that
there,
you
know,
there's
a
way
to
use
these
things
transport
protocols,
because
the
this
has
been
an
issue
once
you
start
putting
computing
in
the
system
and
then
the
security
and
privacy
and
again
a
big
issue.
B
B
Here
this
is
good
yeah,
you
found
you
know.
If
you're
there
you
found
the
meat
deco,
which
is
good
the
live
minutes,
it's
integrated
to
meet
techo
codim,
the
mailing
list.
Well,
if
you're
here,
you
probably
know
about
our
mailing
list,
if
you
know,
if
you
don't
well,
please
do
that
and
you
know
we
have
a
ton
of
documents.
B
Turk,
your
document
expired
that
needs
an
update,
because
it's
an
rg
document.
We
have
two
rg
documents.
We
have
again
a
new
new
drafts.
I
think
this
needs
an
update
because
we
have
the
new
draft
from
china
mobile
also
and-
and
we
have
a
ton
of
other
drafts
that
you
know
are
a
different
level
of
maturity,
and
essentially
this
is
something
that
we
will
raise
on
the
list.
The
idea
that
we
need
to
do
something
about
it.
B
The
milestones
we've
done
a
lot
of
it
and-
and
we
need
I'll
go
very
fast,
because
I
know
one
minute
over
we'll
go
very
fast
to
the
last
thing,
which
is,
we
need
a
milestone,
review
and
we'll
do
it,
and
now
we
have
the
presentations
and
the
first
one
is
scotch
anchor
from
berkeley
and
the
extensible
internet.
So
scott.
Thank
you
very
much
for
doing
this,
because
it's
so
early
in
california.
F
F
So
the
core
subject
of
the
talk
is
really
about
architectural
change.
So
when
I
say
the
word
architecture,
I'm
really
referring
to
the
arrangement
of
the
data
plate,
functionality,
that
is
the
layers
and
the
basic
functions
they've
been
assigned.
It's
not
about
specific
protocols
ipv4
to
ipv6.
It's
not
an
architectural
change
in.
In
my
lexicon,
nor
is
it
about
the
control
plane.
F
Now,
there's
been
decades
of
architectural
research
trying
to
make
changes
to
the
the
basic
architecture,
but
I
I
think
it's
pretty
clear
that
you
know
over
20
works
of
20
years
of
clean
slate,
architectural
research,
there's
no
discernible
architectural
impact
and
the
public
internet,
at
least
in
the
eyes
of
certainly
the
researchers,
I
talked
to
seems
doomed
to
architectural
stagnation.
That
we've
tried
it.
Just
we
don't
see
any
movement,
but
that's
not
what
the
hyperscalers
think
the
cloud
and
content
providers
are
building
their
own
large
private,
ip
based
networks.
F
They've
got
many
points
of
presence
and
what's
relevant
to
this
working
group.
These
points
of
presence
apply
extensive
in-network
services,
flow
termination,
caching,
load,
balancing
and
so
forth,
and
these
services
have
had
a
very
significant
impact
on
customer,
latency
and
reliability,
so
they
put
a
lot
of
money
into
it
because
they
actually
see
very
tangible
benefits
in
their
user
community.
F
F
F
F
On
the
other
hand,
it
provides
the
service
model
to
host.
That
is
this
best
effort.
Packet
delivery
is
exactly
what
anything
you
want
to
do
on
a
host.
That's
the
service
that
you
see
and
you
have
to
build
on,
so
it
has
to
support
all
application
requirements
and
these
requirements
are
becoming
more
stringent,
which
is
a
reason
to
change
the
architecture
and
that's
exactly
why
the
these
hyperscalers
have
built
out
their
own
networks
to
extend
the
the
architecture
for
their
own
purposes,
so
they
can
meet
these
requirements.
F
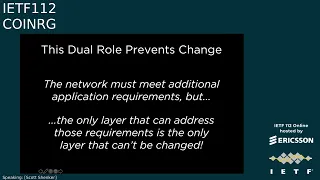
But
it's
this
dual
role
that
prevents
change
because
you
have
demands
coming
from
above.
You
have
constraints
coming
from
below
and
they
are
meeting
in
the
middle
in
a
single
layer,
so
the
network
must
meet
additional
application
requirements,
but
the
only
layer
that
can
address
those
requirements
is
also
the
only
layer
in
the
architecture
that
can't
be
changed.
F
So
that's
the
the
nub
of
the
problem
that
they
coincide
in
the
single
layer,
both
the
demands
and
the
constraints.
So
the
second
question
is
well:
how
can
we
overcome
this
barrier
and
there?
This
is
where
the
extensible
internet
proposal
comes
in.
It's
really
very
simple:
you
use
the
current
ip
protocol
unchanged,
you
don't
do
anything,
but
you
do
introduce
a
new
layer.
Above
it
we
call
it
service,
layer
or
l.
3.5
and
the
service
layer
offers
new
in-network
services
to
host.
So
this
is
the
relevance
to
this
working
group
is
this
network
services?
F
F
So
why
does
this
solve
the
problem
because
it
decouples
layer
three's,
two
roles?
Currently
it's
the
interface
to
both
l2,
which
gives
it
the
constraints
and
l4
which
gives
us
the
demands
and
in
the
ei
l3,
is
still
the
interface
to
l2.
It
does
a
perfectly
good
job
of
that,
but
l
3.5
is
the
interface
to
the
hosts
and
there's
no
reason
for
l
3.5
to
be
in
every
router.
F
F
All
the
service
layer
communication
is
tunneled
over
ip
and
the
source
specifies
which
service
to
invoke
using
the
tunneling
protocol
when
the
packet
gets
to
the
service
node
and
it's
this
ability
for
clients
to
signal
to
the
service.
Node,
what
service
they
want
that
allows
this
to
go
beyond
what
the
hyperscalers
are
doing,
which
needs
to
be
backwards,
compatible
to
actually
we're
able
to
offer
services
like
multicast,
where
the
host
needs
to
know
that
you've
changed
the
semantics
of
what
they've
asked.
So
this
is
the
basic
outline
of
the
design.
F
F
Now
the
key
point
here
is
that
all
these
services,
that
these
in-network
services
that
I
talk
about
are
in
software,
so
standards
are
not
detailed.
Written
specifications,
they're
open
source
code
and
there
are
three
necessary
software
components
on
the
service.
Node
one
is
the
service
modules
that
is,
for
every
service,
whether
it's
multicast,
whether
it's
ddos
protection.
F
There
is
a
service
module,
that's
implemented,
that's
running
on
a
service
node,
it
runs
in
a
standardized
execution
environment.
If
this
execution
environment
has
a
very
simple
set
of
primitives
pack,
it
in
out
ephemeral,
storage,
stable
storage,
maybe
one
or
two
others,
but
it's
a
write
once
run
anywhere
environment.
If
you
write
your
service
module
to
run
inside
this
environment,
it
can
run
on
any
service
node
and
then,
of
course,
in
the
service
node.
You
need
some
kind
of
runtime
or
orchestration
to
scale
up
scale
down
recover
from
failures.
F
This
doesn't
need
to
be
standardized.
You
know,
there'll
be
open
source
versions
available,
whether
it's
kubernetes
or
openstack
or
whatever
comes
next,
and
when
I
talk
about
in-network
services,
this
is
limited
computation.
This
is
not
where
you
run
your
machine
learning
jobs.
This
is
basic
packet,
forwarding,
payload,
processing,
simple
functions
like
caching,
so
it's
more
complicated
than
just
simple
ip
forwarding,
but
it's
not
general
computation,
it's
fairly
limited
and
these
service
nodes
don't
just
have
to
be
generic
processors.
F
They
can
have
secure
enclaves,
they
can
have
hardware
accelerators,
but
everything
you
do
has
to
run
on
a
commodity
processor,
but
if
there
happens
to
be
an
accelerator
that
can
be
used
to
to
get
better
performance
now
choosing
the
services.
This
is
where
you
have
some
kind
of
governance
process,
whether
it's
itf
or
something
else.
You
know
it's
way
too
early,
but
there's
some
body
that
decides
what
are
the
set
of
public
services
and
and
their
implementations
and
all
of
these
public
services
are
run
on
all
service
nodes.
F
That
is,
if
you're
offering
internet
service
so
you're
supplying
a
service
node.
You
have
to
download
all
of
the
service
modules
that
are
in
the
service
model
that
have
been
approved,
and
so
this
is
really
the
biggest
change
to
ei,
meaning
that
ei
brings
this
deployment
model.
That
is
because
they're
approved
software
modules
they
can
be
rolled
out.
They
can
be
deployed.
There's
no
per
vendor
per
domain
decision
process
of
is
cisco
going
to
support.
This
is
juniper
going
to
support
this,
that
is
18t
or
deutsche
telekom
going
to
deploy
it.
F
F
You
can
also
incorporate
other
frameworks
that
are
becoming
quite
popular.
They
can
be
running
on
these
service
nodes,
istio
and
then
oppa
for
the
policies,
various
telemetry
kinds
of
frameworks
and
then
support
for
radical
new
architecture,
something
like
icn,
whether
it's
the
donor
style
or
the
ndn
style.
This
now
just
becomes
a
service.
You
just
roll
it
out,
you're,
not
replacing
all
the
routers.
It's
just
a
piece
of
software
there'll
be
host
support,
obviously,
of
course,
for
all
the
services-
and
this
just
gets
rolled
out
like
another
standard.
F
F
F
Given
the
failures,
why
do
we
think
this
might
succeed
and
there
are
three
reasons:
one
backwards:
compatibility
ip
just
continues
to
be
used.
If
you
don't
want
to
change
anything,
you
just
use
ip.
You
know
maybe
20
years
from
now
that
will
go
away,
but
when
we
roll
ei
out
nothing
changes
about
ip
and
the
kind
of
resources
you
need,
you
just
need
the
service
nodes
which
could
use
edge
computing
or
existing
pops.
They
have
these
facilities
out
there
I
mean
we've
talked
to
some
carriers
and
they
say.
F
Oh
you
know
we
could
run
this
tomorrow
that
we've
got
all
these
facilities
available.
Obviously
there's
more
involved,
but
this
isn't
talking
about.
You
know
major
capital
outlays.
The
second
reason
is
fear
is
a
great
motivator.
You
know
the
internet
architecture
has
resisted
change
and
mark
handles
this
great
essay
on.
You
know
why
the
internet
just
barely
works
and
his
reasoning
is,
you
know,
sort
of
you
know.
Basically,
why
should
it
change
unless
it
has
to?
But
what's
implicit
in
his
essay?
Is
that
there's
no
alternative
that
the
internet
is
just
there?
F
F
Not
in
hardware,
and
the
point
is
the
private
networks
have
proven
every
aspect
of
this
conjecture:
they're
up
in
the
running
they're
running
at
scale,
they're
running
with
real
traffic
at
an
unimaginable
scale,
so
ei
is
really
the
architecturally
co-version
of
what
of
the
approach.
These
private
networks
have
already
proven
to
work.
So
that's
why
we
think
it
might
succeed.
F
So
my
last
real
slide
is
you
know:
where
are
we?
We
built
a
prototype,
really
murphy
mccauley?
Who
has
built
the
prototype
while
teaching
four
classes
a
week,
so
progress
has
been
a
little
slower,
but
you
know
we
want
to
finish
development,
which
should
be
in
a
couple
of
months,
deploy
it
on
fabric
and
other
test
beds,
engage
the
community
by
providing
this
test.
F
But
we
say:
if
you
have
a
new
service,
we
can
deploy
it
if
you
want
to
write
applications
on
top
of
these
services
like
pub
sub
or
whatever
you
can
do
that
too.
Continuing
our
discussions
with
industry
and
we'd
love
to
have
your
participation
you
here,
meaning
as
individuals
as
a
research
group
or
the
broader
community.
With
that,
thank
you
and
I'll.
Take
your
questions
and
eve.
Why
don't
you
kick
it
off.
A
C
Thank
you
eve
and
thank
you
scott
for
for
this.
As
you
said
the
second
time,
I've
sort
of
heard
this,
and
and
finally,
it's
sinking
in
a
little
bit.
My
question,
which
draws
on
some
of
the
the
stuff
in
the
chat,
is
about
the
layering
here
and
in
particular
the
relationship
with
with
transport
protocols,
so
in
in
your
very
simple
example
of
source,
snsn
dest
would
the
would
you
see
the
transport
protocol
running
end
to
end
so
source
to
destination?
F
So
there
will
definitely
be
an
end-to-end
reliability
layer
and
because
for
reliability,
we
want
the
failure
of
a
service
node
to
be
no
more
serious
than
the
failure
of
a
router
today.
So
they'll
definitely
be
end
to
end
whether
the
pipe
that
goes.
We
view
that
ip
is
providing
a
pipe,
whether
the
the
pipe
that
goes
between
these
two
implement.
Some
kind
of
reliability
is
an
open
question,
but
but
it's
not
mandated
by
the
architecture.
The
essential
transport
is
end
to
end
where
congestion
control
is
done.
C
Right
because
I
think
I
think
this
sort
of
factors
into
things
like
transport
layer,
encryption
as
well,
and
whether
the
sms
are
able
to
access
the
data
to
do
anything
unless
those
transport
sessions
are
terminated
and
restarted,
and
this
is
kind
of
making
me
wonder.
I
I
don't
dispute
at
all
the
all
your
points
about
needing
to
introduce
some
additional
layering
to
to
get
the
development,
and
I'm
just
wondering
whether
this
is
really
go
should
go
in
at
layer
4.5
rather
than
at
3.5,
but
I'll.
Let
others
talk.
F
Well,
I
actually
can
I
I
mean
this
is
a
very
active
area
of
investigation
for
us
and
our
current
thinking
is
that
the
end
to
end
first
of
all,
all
the
pipes
will
be
encrypted
at
the
low
level,
but
but
that's
trivial,
but
and
service
node
to
service
node
pipes.
But
at
the
end-to-end
transport
layer
there
will
be
encryption,
but
I
we
want
to
have
an
option
for
the
endpoints
to
say
here
are
the
parts
that
we
are
willing
to?
F
Let
the
intermediate
node
see
versus
here
are
the
parts
that
they
can't,
and
so
they
can
decide
like
they
want
to
take
care
of.
You
know,
take
advantage
of
caching,
then
they
might
expose
certain
aspects,
but
if
they
want
to
keep
certain
material
private,
they
don't,
and
so
we
want
to
give
that
leave
that
flexibility
to
the
application
itself.
I
I
Isn't
that
a
barrier
to
entry,
though
I'm
I'm
not
really
quite
understanding.
The
reason
for
doing
so,
because
also
the
culture
asks
the
right
question:
who
has
the
incentive
to
really
deploy
this?
But
if
I'm,
if
I
have
to
ramp
up
my
sn
deployment
by
really
essentially
running
any
public
service
over
it,
isn't
it
preventing
me
for
just
quickly
roll
out
my
owner's
end,
where
all
I
want
to
do
is
run
my
service
on
it,
because
it's
a
low
barrier
to
entry.
F
That
our
point
is
that,
once
you
support
the
execution
environment,
implementing
these
other
services
is
simple.
It
it
does,
require
extra
resources,
but
if
you
don't
make
it
uniform,
then
the
internet,
you
know
the
beauty
of
the
growth
of
the
internet.
Is
you
knew
wherever
you
plugged
in
you
had
a
set
of
services?
F
You
could
depend
on
if
we
now
go
to
the
space
of
ip
options,
which
you
know
is
no
fun,
that's
not
going
to
work,
and
so
that
really
is
critical
to
this,
that
you
can
build
an
application
that
relies
on
a
public
service
and
that
will
be
available
wherever
the
user
is
so
that
that's
critical
part
of
the
proposal,
and
given
that
it's
not
about
changing
equipment,
it's
just
about
the
scaling
of
your
service
nodes.
We
think
there's
a
chance
that
that's
gonna.
F
F
F
F
So
there
might
be
like
a
particular
stack
that
says:
okay,
you're
going
to
get
an
ip-like
service
and,
on
top
of
it,
you're
going
to
get
this
kind
of
transport
service.
And
on
top
of
that,
there's
going
to
be
this
kind
of
ddos
prevention,
and
you
know
whatever,
as
a
a
set
of
what
we
might
think
of
individual
features.
F
E
F
Yeah,
so
in
our
current
implementation,
what
we
would
do
is
we
would
say.
Well,
if
this
is
the
composition,
then
we
would
have
that
ball
of
code.
I
mean
take
those
several
different
pieces
of
code,
merge
them
together
and
then
have
them
run
as
a
single
service
module,
so
that
we've
actually
made
sure
that
these
code,
that
the
code
bases
work
together
and
and
so
we're
not
doing
enough
chaining,
it
is
actually
we
decide
to
put
it.
F
J
F
So
I
I
think
for
both
of
them
it
is
the
extensibility
so
for
service
chaining,
you
tell
it
to
go
through
various
boxes,
but
it's
not.
The
network
is
not
making
you
a
promise
of.
I
will
deliver
multicast
packets
for
you.
It
is
go
through
this
box.
This
box
can
do
something,
but
but
service
chaining
doesn't
give
you
any
global
service
definition
that
that's
your
job.
F
You
have
to
sort
of
you
know
if
you
say
you
go
through
a
firewall
and
then
go
to
this
and
go
through
that
you're,
the
one
figuring
out,
eventually
what
what
that's
giving
you.
So
I
think
that's
the
difference
so
something
like
ddos
prevention,
that
you
know
we're
architecting
it
to
provide
it's
a
service-wide
thing:
it's
not
just
a
single
box,
it's
not
just
a
scrubbing
box!
So
that's
what
I
think
that
the
key
difference
is.
I
don't
know
whether
that
helps.
A
D
F
So,
yes,
we
will
have
some
kind
of
discovery
process
for
service
nodes
to
discover
each
other,
but
if
you
want
to
have
an
sdn
like
control
for
a
domain
to
have
the
service
nodes
know
about
each
other,
that
would
be
fine,
so
the
control
plane
we.
I
was
completely
silent
on
the
control
plane
for
this
we're
open
to
a
wide
variety
of
how
you're
going
to
manage
your
domain.
A
B
A
F
A
K
Here
we
we
viewed
our
working
data
center,
so
we
have
the
flexibility
to
customize
everything
and
it's
different
from
the
internet.
I'm
happy
to
introduce
our
work
in
network
application
for
multi-tenant
learning.
So
this
is
a
joint
work
from
colleagues
from
chiang
mai
university
and
the
university
of
wisconsin
medicine.
K
Machine
learning
algorithms
is
used
in
various
scenarios,
such
as
natural
light
reprocessing
computer
reading,
so
with
the
increasing
size
of
the
data
set
and
the
model,
so
the
algorithm
is
implemented
as
a
as
a
distributed
system.
So
the
ps
architecture
is
a
typical
architecture
that
can
support
this
kind
of
distributed
system
in
the
ps
architecture.
K
So
recently,
the
chain
or
network
competition
provide
an
opportunity
to
solve
this
problem.
The
programmable
switches
offer
in
intrinsic
packet
processing,
so
the
switch
pipeline
has
registers
which
can
store
the
network
states
and
the
user
specified
programs
can
be
loaded
to
customize
the
packet
processing.
K
There
exists,
there
is
an
existing
work
that
applies
in
network
of
aggregation
to
to
distributed
chain
html.
This
work
target
a
single
chart,
a
single
rack
setting.
So
there
is
a
wrap
connect,
multiple
workers,
so
the
switch
is
offload.
The
ps
is
offloaded
to
the
switch,
so
the
workers
gradients
are
aggregated
in
the
switch
to
support
micro
jobs.
The
switch
resource
is
statically
partitioned
and
assigned
to
each
job.
K
So
we
propose
our
solution
with
three
key
goals.
The
first
goal
is,
we
should
maximumly,
you
use
the
network
condition
for
performance
gain
on
targeting
the
production
network.
We
should.
The
solution
should
support
multiple
simultaneous
job
change
efficiently,
and
it
should
also
support
a
multi-rack
quality.
K
K
So
the
assignment
use
a
hash
function
to
hash
the
job,
id
and
sequence
number
so
for
four
packets
from
one
job,
with
the
same
sequence
number,
but
from
different
workers,
they
would
be
hashed
to
the
same
position
and
get
a
repeated
there.
So
the
the
vision
result
is
sent
to
the
ps.
Then
the
ps
return,
the
result
to
the
switch.
K
K
First,
because
the
switch
the
aggregator
assignment
is
decentralized,
it's
possible
to
to
have
hash
clearance,
for
example,
job
tools,
gradient
packet
is
a
is
a
assigned
it's
hashtag
keeper,
which
is
occupied
by
another
job
job.
Three,
in
this
case,
all
the
packets
would
pass
through
the
switch
and
arrive
at
the
on
the
ps.
The
ps
do
the
aggregation
and
send
the
result
back
to
the
switch.
K
There
is
another
case
of
inconsistency
or
membership
inconsistency.
It
causes
incomplete
aggregation,
for
example,
the
first
packet
is
sent
to
a
aggregator
which
is
reserved
by
drop
three,
then
this
packet
it
passes
through
passes
through
to
the
ps,
but
at
this
time
job3
completes
its
application
and
deallocated
the
switch
memory.
The
grid
guitar.
The
remaining
package
is
sent
to
the
aggregator
and
the
aggregated
there.
So
both
the
switch
and
the
ps
have
a
partial
result.
They
are
waiting
for
each
other.
This
is
a
deadlock
and
they
are
what's
worse.
K
Is
that
there
is
no
return
packet
of
results
to
dialogue.
This
switch
memory
causing
a
memory
leak
problem,
so
we
design
a
re-transmission
antenna
and
host
with
the
duplication
in
the
switch
so
for
for
packet
a
it
has
that
it
is
a
stock
under
the
switch
and
the
ps,
but
it's
it's
a
following
package
may
be
maybe
successfully
aggregated
and
returned.
So
if
the
sender
observed
reduplicated
the
ack
the
result
packet,
it
would
re-transmit
the
missing
the
packet
that
is
missing
the
result
it
will
all
workers
would
retransmit
a
so.
K
K
So
with
this
design,
we
have
a
correct
protocol
that
can
guarantee
the
the
correctness
to
support
microreact
aggregation.
We
need
a
aggregation
hierarchy
in
the
topology.
Ideally,
this
aggregation
hierarchy
can
be
can
be
of
many
levels.
We
consider
the
data
center
topology
in
the
data
center
topology,
the
core
network
has
multiple
passes
and
it
uses
non-deterministic
locking.
K
Currently
we
have
a
two
level
aggregation
design,
so
all
the
packets
would
aggregate
at
the
walkers
tour
first,
then
they
are
sent
to
the
ps4
and
the
second
level
aggregation
is
happening
at
the
ps4.
The
final
result
is
send
it
to
the
ps,
so
in
this
in
this
multiple
racks
part,
we
also
overcome
another
challenge,
because
the
higher
level
switch.
This
is
the
hierarch
aggregation
hierarchy
or
the
previous
in
the
paris
page.
K
So
in
each
of
the
guitar
we
have
a
big
map
which,
where
each
b
that
he
knows,
I
always
children.
But
so
there
is
one
bit
of
four
in
the
switch
two
which
indicated
the
switch
to
zero.
But
the
one
meter
here
cannot
denote
the
all
the
possible
aggregations.
These
always
work
because
there
are
two
workers.
K
So
the
previous
design
also
overcome
other
challenge.
Other
challenges
on
our
reliability
when
the
the
re-transmission,
with
the
duplication,
can
also
handle
the
packet
loss
correctly
and
one
pack
loss
happens
in
the
host
of
the
re-transmitter
and
the
bitmap
in
the
switch
can
guarantee.
There
is
exactly
wax
application
and
we
also
redesigned
the
congestion
control.
The
essential
problem
is
what
should
be
the
congestion
signal,
because
some
many
packets
are
consumed
in
the
switch,
so
they
do
not
have
round
sweep
time.
So
there
is
no
rtt.
K
We
use
the
ecl
as
the
congestion
signal
use
eimd
for
congestion
control
and
on
the
in
the
host.
The
switch
can
only
compute
on
integrals.
It
does
not
support
floating
point
arithmetic,
so
we
do
compensation.
We
scale
with
scale.
The
float
point
block
points,
two
integers
bioscanning
factor
and
this
because
we
skills
the
floating
numbers
it's
possible
to
have
overflow
at
the
switch
to
handle
this
problem.
We
just
use
the
fallback
mechanism,
we
reuse
the
fallback
magnesium
when
switch,
detect,
detects
our
flow
overflow.
K
K
Sometimes
it's
the
performance
skin
is
very
significant.
Atp
can
benefit
the
network
intensive
workloads
more
than
the
competition
intensive
workloads
and
comparing
atp
with
the
ring
or
reduce
with
hardware
acceleration
atp
is
slightly
better
than
ring
or
reduce,
but
more
importantly,
it
only
uses
half
of
the
batteries
that
we
already
use.
K
K
K
Okay,
there
are
more
evaluations,
so
in
atp
we
co-designed
the
host
and
the
switch
logic.
The
switch
to
service
security
service
is
best
effort.
It
has
dynamic
resource
allocation.
The
host
networking
stack,
has
fallback
mechanisms
for
correctness,
guarantee
and
also
reliability
and
congestion
control
to
ml
jobs.
Such
a
design
can
provide
performance,
skill
and
correctness,
and
we
achieve
our
goal
of
multi-tenant
but
to
draw
support.
K
So
there
is
takeaway
so
usually
when
we
do
a
network
competition,
usually
we
can
get
a
very
significant
performance.
Scan
switch
computes
much
faster
than
a
server,
but
correctness
guarantee
is
very
difficult
because
the
network
competition
introduces
new
schematic
into
the
network,
for
example.
Practice
can
be
consumed
instead
of
lost.
Then
hosts
need
to
distinguish
these
cases
and
usually
we
do
switch
and
host
the
co-design.
K
B
L
So
in
coin,
so
far
in
my
view,
we
have
mainly
been
discussing
like
two
strengths
of
of
work,
so,
like
one
is
coming
from
like
data
plane
probability
and
then
seeing
how
this
could
be
put
to.
You
know
a
useful
purpose,
for
you
know
having
distributed
applications
and
improving
their
performance
and
so
on,
maybe
also
evolving
some
protocols
to
support
certain
use
cases
better.
L
The
other
strand
you
could
say,
is
coming,
but
from
the
distributed
computing
where
we
say
okay,
what
can
we
learn
from?
This
will
be
computing
and
how
does
it
affect
our
view
on
networking
and
maybe
then
re-imagine
the
relationship
and
in
the
end,
have
more
programmable
systems,
also
like
the
ones
that
scott
talked
about,
and
so
I
think
the
the
like
the
thesis
of
this
group
in
in
general
is
maybe
is
there
some
confluence
at
the
end
of
these
two
strains?
L
I
invite
you
to
check
out
the
paper
and
the
demo
video
after
this,
so
in
distributed
computing,
we
know
that
there
are
many
different
types
of
interactions,
so,
like
simple
message,
passing
remote
method,
indication
data
sets
implementation,
key
radio
stores
and
so
on,
and
so
I
think
some
itfs
ago
we
presented
a
system
that
we
called
compute.
First
networking
that
was
essentially
a
yeah,
too
incomplete,
really
general
distributed
computing
system
based
on
an
icn.
L
L
Can
this
fundamental
paradigm
can
be
used
to
implement
batch
as
well
as
stream
processing
so
in
steam
processing
you
you,
like
conceptually,
you
look
at
each
data
object
independently
in
an
unbounded
stream
of
data
in
batch
processing.
You
group
data
and
typically
the
systems
allow
you
to.
You
know,
implement
groupings
dynamically
so
based
on
some
predicate
or
some
time
window
specification
and
so
on.
L
So
windowing
is
a
common
concept
here
that
allows
this
grouping
and
slicing,
and
this
can
also
lead
to
situations
where
you
have
something
like
a
predicate
that
allows
you
to
put
like
one
data
object
into
like
multiple
windows.
For
like
consumption
by
by
different
functions,
for
example,
but
you
can
also
split
this
up
in
in
different
ways.
L
L
You
can't
really
predict
the
processing,
transport
delays
and
so
on
and
typically
what
you
try
to
achieve
is
that
you
match
the
production
rate
with
the
input
rate,
and
so
the
task
of
a
data
flow
system
then,
is
to
adjust
the
processing
graph
to
the
application
requirements
and
the
data
production
rate,
and
you
can,
you
can
see,
there's
all
like
some
kind
of
variable
performance
and
systems
can
be
compared.
How
well
they
maybe
keep
up
with
the
offered
load.
L
Perhaps
there
are
a
couple
of
really
widely
used
implementations,
so
apache
beam
is
basically
the
unified
programming
model
that
many
data
from
invitations
use,
so
sometimes
they're
called
runners.
So
you
may
have
heard
about
apache,
flink
spark.
Of
course,
google
cloud
dataflow
is
a
product
and
so
on,
and
the
picture
here
on
the
right
hand,
side
depicts
the
architecture
of
a
system.
I
think
it's
probably
inspired
by
flink,
where
you
on
the
bottom
here
you
you
see
the
the
notes,
so
these
this.
L
What
is
called
task
manager
here,
so
this
could
be
something
like
a
a
compute
node
in
your
network,
which
is
offering
several
slots
for
computation,
and
this,
like
the
job
manager
on
the
top
right
here,
is
kind
of
orchestrating
this
whole
system.
So
it's
kind
of
having
an
overview
about
the
available
slots
and
is
responsible
for
allocating
tasks
for
for
certain
jobs
and
then
also
managing
the
connectivity
between
those
those
jobs.
L
L
You
know
matching
of
like
your
compute
performance
with
the
network
performance
and
having
also
really
responsive
systems.
In
the
end,
you
don't
you
have
you,
don't
have
this
full
visibility
of
both
the
computing
and
the
networking
resources
now
in
the
system.
I
wanted
to
talk
about
today,
and
so
we
call
this
ice
flow
information
senior
data
flow.
We
assume
that
we
have
a
network
of
nodes
and
in
in
icn
we
we
name
everything
so
the
assumption
here.
L
They
would
also
be
announced
in
this
routing
system
and
so
we'll
be
able
to
construct
compute
graphs,
and
what
we
do
in
this
system
here
is
that
we
are
kind
of
not
establishing
connections
to
functions
or
to
to
nodes.
We
are
actually
just
asking
for
input
data,
and
so
when
there
is
new
input
data,
we
this
triggers
computation
at
the
like,
downstream
function
and
so
on.
L
They
return
name.
Data
object
with
the
usual
icn
properties,
so
they
are
immutable,
they
can
be
cached
and
they
can
be
authenticated
encrypted
and
so
on,
and
so
the
interesting
challenge
is
here
is
that
we
have
asynchronous
data
production.
So
we
have
to
know
when
data
is
available
so
like
push
semantics,
which
is
typically
not
idiomatic
in
icn,
and
then
you
have
to
think
about
flow
control.
So
how
do
you
couple
consumers
and
producers
and
then
in
the
icn
system?
Typically,
you
you
publish
data.
That
means
you
make
data
available.
L
L
We
are
using
an
icn
technology
called
dataset
synchronization
for
that,
where
so,
logically,
the
producers
produce
data
under
a
known,
prefix
and
consumers
can
subscribe
to
that
prefix
and
then
they
would
learn
when
there
is
new
data
under
that
prefix,
and
then
they
can
decide.
Okay,
I'm
interested
in
text
to
lines
object
one,
and
then
I
can
fetch
that.
L
So
there
are
implementations
of
this
concept
like
psync
in
in
icn,
which
in
the
end
which
you
may
have
heard
about,
and
so
that
means
so
in
the
on
the
like
very
low
layer.
This.
That
means
consumers
have
to
kind
of
send
update
interests,
to
learn
about
new
names
perfectly
and
then
from
an
application
perspective.
L
L
You
know
runtime
information
and
configuration
information.
So
what
is
the
static
flow
graph?
What
is
the
actual
dynamic
flow
graph?
What
are
available,
compute
slots
in
the
system
and
so
on,
but
also
implementing
this
loose
coupling
between
consumers
and
producers?
So
we
have
conceived
something
that
like
what
we
call
consumer
reports
where,
basically,
we
publish
what
windows
have
been
processed
by
each
consumer,
and
so
this
is
also
a
like
a
organized
data
structure
in
in
icn
way,
and
we
also
use
this
data
set
synchronization
scheme
to
share
this
information.
L
Okay,
just
very
quickly
so
this
approach
allows
us
to
deal
with
congestion,
control
and
yeah
like
a
proper,
receive
window
configuration
in
a
different
way,
so
we
can
really
adapt
like
the
interest
rate,
for
example,
to
our
actual
processing
speed,
so
avoiding
that
we
asked
for
too
much
data.
We
cannot
process
in
in
real
time
and
observing
the
performance
of
my
downstream
consumers
could
be
a
trigger
for
an
upstream
producer
to
initiate
scaling
out
and
so
by
creating
a
new
subgraph.
So
if
I'm
constantly
realizing
that
my
downstream
cannot
keep
up.
L
L
L
L
This
system
would
basically
need
additional
infrastructure,
so
like
a
name-based
routing
infrastructure,
for
example-
and
there
are
solutions
for
that
that
in
principally
principal
work,
but
maybe
in
terms
of
research,
this
system
could
also
be
supported,
perhaps
better
by
a
routing
system
that
gives
you
more
information
so,
for
example,
resource
education,
information
directly
and
not
only
reachability
information
and
so
for
coin.
We
think
this
could
be
an
example
for
like
new
protocol
work,
so
I'm
not
saying
that
this
is
the
the
best
way
of
doing
this.
L
So
this
is
has
to
be
something
that
you
know
ends
up
in
a
protocol
spec.
But
it's
it's
an
interesting
example,
so
how
you
can
break
up
overlays
and
leverage
systems
like
icn
to
do
that,
and
so
today
I
talked
about
data
flow,
but
you
can
imagine
that
other
interaction
classes
could
be
promising
as
well,
so
other
systems
may
be
like
kafka
like
published
broker
systems,
and
so
on
with
that,
thanks
for
your
attention
are
there
any
questions.
A
A
So
I
think
in
the
interest
of
time
we
will
go
forward
in
the
program
we
had
segmented
the
program
into
you
know,
papers
that
have
been
published
elsewhere
and
that's
been
really
fruitful.
Thank
you
all
for
your
presentations.
The
next
section
is
gonna,
be
brief.
It's
sort
of
new
ideas
section
and
then
we're
gonna
get
to
the
drafts
and
draft
updates,
and
then
then
a
new
draft.
A
B
A
A
B
B
B
That's
been
put
together
by
a
large
group
of
people
and
it's
a
european
wide
project
and
the
idea
started
from
essentially
a
lot
of
us
actually
a
lot
of
people
on
the
moda
team
or
will
be
when
we
once
we
see
the
slides
are
very
familiar
to
this
group,
because
a
lot
of
them
are
involved
and
one
of
the
ideas,
oh,
my
slides,
are
coming.
Thank
you.
Thank
you
so
much
eve
and
the
the
id
and
we
can
go
directly
to
the
first
slide.
B
B
Everything
is
fragmented
and
for
essentially
in
iot.
What
people
do
is
they
put
a
sensor
somewhere?
They
put
a
gateway
in
they
connect
to
the
cloud,
and
they
claim
that
the
problem
is
solved.
The
problem
is
not
solved
because
the
minute
that
you
want
to
start
having
applications
and
services
and
artificial
intelligence
that
cover
more
than
one
thing
you
you're
in
you're,
in
your
agriculture.
Well,
you
may
want
to
take
decisions
that
are
based
on
the
market,
but
then
how
does
that
work?
When
you
need
to
det?
B
You
need
for
that
to
know
or
how
much
disease
do
you
have
in
your
farm
or
maybe
what's
the
building
temperature,
because
that
will
increase
or
decrease
depending
on
you
know
the
time
of
year
or
the
time
of
day,
and
it
will
increa
increase
or
decrease
your
production,
which
yeah
will
go
back
to
your
your
modeling
of
decision,
and
now
you
would
the
minute
you
do
that.
Well,
you
have
people
involved.
You
have
a
ton
of
different
systems
that
don't
talk
to
one
another.
Next.
B
So
oops
so
essentially
in
this
fragmented
environment,
the
application
development
has
very
very
important
pain
points.
So
all
these
fragmented
systems
that
require
overlays
multiple
gateways,
different
cloud
applications,
the
different
cloud
providers
that
don't
talk
to
one
another
and
there's
issues
always
of
that
in
security
and
privacy,
because
there's
data
privacy,
there's
digital
sovereignty,
there's
multiple
customers
who
are
involved
and
it
creates
a
big
problem.
B
Data
valorization
is
key.
I
think
scott
mentioned
that
you
know
you.
You
use
open
source
approaches,
and
this
is
exactly
what
we
want
to
do,
because
in
fact
it
is
not
the
algorithms
or
the
software
that's
worth
and
the
words
a
lot.
It's
actually
the
data
itself,
and
so
we
want
to
make
sure
that
we
can
actually
maximize
data
valorization
by
acting
it
on
it
inside
the
network.
Next
slide.
B
B
B
So
the
format
didn't
work
very
well
here,
the
main
mode
of
functionality.
I
don't
want
to
go
I'll,
go
fast,
because
I
don't
want
to
go
into
everything
this,
but
obviously
we
want
to
do
some
orchestration.
There
was
discussion
about
orchestration
before,
but
we
feel
that
we
can
actually
look
into
this
and
again
on
device
computing
over
a
trojan
system
we
want
to
have
if
we
can
as
much
as
possible
reusability
and
that's
actually
a
problem
on
those
verticalized
applications
is
if
you
change
vendor
or
if
you
change
supplier.
B
Your
system
doesn't
work
anymore
because
they
use
different
protocols,
different
semantics,
different
everything
you
would
like
to
have
modularity
as
a
design
choice.
I
usually
when
I
teach
my
class
on
distributed
systems.
I
talk
about
the
lego,
blue,
brick
approach,
so
that
you
know
we
want
to
have
a
lot
of
lego
bricks
and
we
connect
them
when
we
need
them
and
we
don't
use
them
when
we
can't
or
when
we
we
won't
and
actually
also
in
iot
systems.
It's
important
because
a
lot
of
times
you
have
limited
resources.
B
You
want
to
be
able
to
manage
the
the
network
processing
units
themselves,
so
the
in-network
computation
that
allows
the
packets
and
the
information.
I
would
think
I
would
speak
more
of
information
in
this
case
to
be
properly
managed
and
properly
sent
to
the
right
interfaces
and
the
right
end,
devices
and
end
system,
and
obviously
we
want
to
support
data
and
intelligence
services.
More
and
more
data,
driven
until
it
is,
is
actually
the
basic
of
a
lot
of
networking.
B
Last
year
with
andy
schuster,
we
did
a
study
for
the
nsf
on
the
future
of
broadband,
and
actually
the
conclusion
was
that
everybody
who
does
broadband
wants
data,
so
data
driven
made
required
to
have
new
new
features
inside
moda
and
inside
the
network
itself
and,
of
course,
there's
there's
ai.
That
is
not
only
in
the
applications
but
more
and
more
in
the
network
in
terms
of
network
management
and
even
management
of
loads
inside
data
centers
and
elsewhere.
B
Next
slide.
I
think
it's
almost
the
last
one
yeah.
I
think
the
previous
slide
is
an
overview
of
of
what
it
looks
like,
but
the
picture
is
not
very
good,
so,
let's
we
can
skip
it
and
the
link
to
the
coin
rg.
Well,
actually,
again,
it's
not
just
that.
There's
a
lot
of
people
involved
in
mode
that
are
also
members
of
this
community
is
actually
there's
a
lot
of
common
research
topics.
I
mentioned
discovery.
B
We
would
like
to
discover
storage
function
from
you,
know,
functional
functions
and
and
computation
so
functional
discovery,
storage,
discovery,
computation
discovery.
We
would
like
more
and
more.
I
think
both
and
that's
actually,
since
I
know
I
have
two
hats
here,
so
I
can
say
as
I
as
now
as
maybe
as
a
current
chair,
that
distributed
distractions
and
protocols
are
also
very
important
to
both
groups.
B
We
haven't
really
addressed
that
a
lot
in
coin,
but
it
is
something
that
we
could
look
at,
because
federated
learning
needs
some
form
of
in-network,
maybe
not
pure
computation,
but
at
least
some
form
of
trending
and
and
connections
and
orchestration,
and
obviously
there's
all
the
use
cases,
and
actually
the
people
right
after
me
will
talk
about
use
cases,
so
I
won't
go
there
so
this
was
this
was
a
very
short
presentation.
This
is
moda.
B
We
know
that
this
is
right
now
being
proposed,
we've
been
evaluated,
we
don't
know
if
it's
going
to
go
through,
but
I
think
the
team
and
I'd
like
to
really
acknowledge
the
architecture
team
that
did
this
and
a
few
of
them
are
on
the
call
right
now.
This
was
an
incredible
effort.
This
was
an
incredible
fun
thing
to
do
and
we're
thinking
that
maybe
we
want
to
continue
the
work
inside
this
community
and
outside.
Thank
you.
A
B
A
A
M
M
So,
first
of
all,
we
have
regrouped
the
use
cases
so
from
the
historically
grown
structure
to
the
one
that
we
have
right
now,
so
we
thought
of
four
ways
how
we
could
think
about
the
use
cases,
the
first
one
and
our
really
kind
of
new
user
experiences
that
can
be
enabled
using
coin.
So
the
arvr
stuff
that
marie
jose
has
presented
quite
a
few
times
is,
for
example,
in
that
category.
M
The
third
category
is
on
improving
existing
coin
capabilities,
so
we
already
have
networks
which
use
some
form
of
coin
and
so,
for
example,
cdns
have
kind
of
already
some
coin
functionality
in
there
and
those
use
cases
are
now
really
on
how
those
networks
can
even
be
improved
further
and
then.
Finally,
we
have
entirely
new
coin
capabilities
that
can
be
enabled.
M
As
a
second
aspect,
we've
then
also
tried
to
sharpen
and
tighten
the
taxonomy,
so
it
was
not
that
focused
before,
and
we've
tried
to
do
that
now.
I'll
come
to
that
in
a
moment
again,
and
finally,
we've
also
already
started
to
prepare
the
actual
analysis
that
we
want
to
do
later,
mainly
focusing
on
the
research
questions
and
requirements.
M
So
with
that,
let's
have
a
look
at
the
current
draft
structure.
So
what
you
can
see
is
that
we
have
actually
done
the
regrouping
already.
We
also
have
this
one
new
use
case
provided
by
xavier
that
he
has
already
presented
last
time
or
in
our
last
meeting
and
then
also
we
have
already
the
analysis
in
the
structure
right
now,
so
we're
all
only
waiting
to
get
started
with
that,
basically
and
then.
M
M
So
next
steps
that
we
are
planning
to
do
is
first
finish,
aligning
the
use
cases
according
to
the
the
new
taxonomy,
so
really
pinpointing
the
requirements
and
aligning
the
descriptions
a
bit
better.
Then
we're
also
trying
to
think
about
the
terminology
that
we're
currently
using,
whether
that's
everything
that
we
need
or
whether
there
are
additional
terms
that
we
might
require,
and
then
also
maybe
as
a
question
to
the
the
complete
research
group,
where
we
would
like
to
collect
that
terminology.
M
Finally,
we
would
also
like
to
start
with
the
analysis,
so
we
first
try
to
condense
the
opportunities,
research,
questions
and
requirements
and
then
afterwards
try
to
identify
aspects
similar
across
all
of
the
use
cases,
so
that
we
can
then
perhaps
give
a
collected
input
into
the
second
charter
item
of
this
research
group,
and
that's
it
thank
you
and
I
think
comments
we
can
take
them
to
the
list.
If
there's
not
that
much
time.
B
G
H
I
Very
good
still
a
bit
new
with
the
ui
and
colin
has
given
a
good
tutorial.
Thank
you.
Transfer
protocol
issues,
even
network
computing
systems.
That's
another
draft,
like
clouds
and
myself
have
been
working
on.
It
had
expired
initially
in
in
the
last
meeting,
because
of
the
focus
we
had
mainly
on
research,
presentations
and
and
and
and
it's
not
quite
as
outstanding
outdated
as
the
date
on
the
first
slide
gives.
It
was
obviously
presented
at
the
11th
of
november
2021
or
not
2020.,
the
the
premise
I
highlighted
the
main
piece.
I
I
don't
intend
to
read
this,
so
this
is
about
what,
if
you
have
functions
of
the
communication
system,
I'm
sorry
if
the
part
of
the
intent
function
may
be
provided
as
part
of
a
communication
system.
That's
the
network
premise
really
of
coin.
This
is
a
quote
from
the
end-to-end
paper
from
the
original
indian
paper
and
and
we're
looking
at
the
challenges
to
the
traditional
intent
transport
protocols.
You
know
trying
to
outline
opportunities,
research,
questions
for
the
design
of
transport
protocols
that
may
arise
from
the
availability
of
in-network
computing
capabilities.
I
That's
the
the
premise
really
as
a
recap.
So
the
intention
is
to
provide
insights
into
various
transport
technology
areas.
Research,
question
changes
already
mentioned
ongoing
efforts
and
concepts
that
are
currently
under
studies,
so
we're
not
limiting
ourselves
only
to
existing
rfcs,
but
we're
also
looking
at
ongoing
work
research,
whatever
we
can
find
outline
possible
future
work
in
coin
and
elsewhere,
that's
starting
with
coin,
but
doesn't
necessarily
mean
that
all
of
the
work
needs
to
be
done
in
coin,
obviously,
and
provide
that
in
a
gap
analysis.
I
So
the
goal
is
to
contribute
to
the
objectives
of
coin,
and
I
mentioned
I
I
quoted
here
the
coin
chart
or
scope
number
four,
namely
the
research
and
potential
new
transport
protocol
required
or
enabled
by
in-network
commute
resources.
So
that's
a
dedicated
item.
That's
chartered
really,
and
we
believe
that
and
hope
that
the
draft
contributes
to
that
the
general
structure
we
made
a
similar
changes
a
bit.
You
know
aligned
in
some
sort
of
locks
up
to
to
the
changes
we
also
made
in
the
in
the
use
case.
I
Traffic
presenters
are
trying
to
sort
this
a
bit
more
into
various
areas
of
discussion.
So
in
this
case
for
the
transport
draft,
we
divided
the
or
collected
the
separate
chapters
from
before
into
a
single
technology
areas
section
now
that's
a
section
three,
so
that
has
been
entirely
restructured
and
everything
has
been
fl
was
was
was
integrated
under
that
section
and
then
started
with
the
gap
analysis.
I
This
is
just
to
present
the
technology
areas
and
the
gap
analysis
more
visibly
in
the
structure,
so
there's
edit
here
for
future
extensions
and
in
particular
with
a
possible
formation
of
future
needed
work.
So
this
is
much
more
gearing
the
the
I'm,
the
document
towards
the
charter
item
that
I
mentioned
before
right.
I
So
in
section
three,
so
everything
that
really
was
before
in
the
various
I
think
section
initially
three
to
seven
are
now
all
found
here
and-
and
that
also
helps
us,
then
to
link
back
from
the
gap
analysis
in
section
five
into
the
appropriate
technology
section
later
on.
So
it
makes
the
editing
easier.
I
I
Addressing
but
there's
a
discussion
going
on
at
the
moment
and
the
section
3
also
added
ongoing
work
in
the
ic
energy
and
then
the
working
group,
so
these
were
content
changes
as
well
to
the
structural
changes
question,
obviously
to
the
group.
We
would
like
to
ask
here
and
happy
to
get
any
ideas
either
in
the
chat
or
on
the
mailing
list
is
what
research
question
related
concept
ongoing
efforts?
I
Our
intention
is
really
to
you
know
also
approach
the
new
community
with
that
question
specifically
and
because
we're
sure
that
we're
missing
concepts
simply
because
we're
not
aware
of
them
or
we,
you
know-
haven't
worked
through
all
the
various
ones.
So
if
you
have
anything
any
research
question
in
a
related
concept,
you
want
to
share
with
us.
Please
do
so
gap
analysis.
I
At
the
moment,
we
only
added
an
introductory
paragraph
outline
the
intentions.
We
have
no
content
in
the
individual
sections,
yet
question,
obviously
also
to
the
list
is
or
to
the
community
is
to
be
one
such
such
section
or
not
for
coin,
so
we
believe
that
it
may
help
us
to
working
towards
the
charter.
If
we
don't
want
this,
we
can
remove
it,
but
that
was
the
suggestion
we
made
and
that's
a
question.
We
would
like
to
get
some
feeling
from
the
community.
I
Future
plans,
so
we
mentioned
already
the
last
time
and
we
we
haven't
really
made
too
many
changes
to
do
that,
but
we
want
to
because
we
also
made
changes
to
the
use
cases,
and
I
think
now
that
we
structure
the
use
cases,
as
you
could
see
in
ike's
presentation
more
clearly
around
the
notion
of
capabilities.
We
want
to
also
make
clearer
linkage
to
the
use
cases
and
particular
with
that
taxonomy
that's
being
used
now
in
the
use
case
draft
in
a
in
the
next
version
of
the
transport
draft.
I
We
want
to
add
more
existing
work.
We've
already.
There
was
a
communication
between
the
chairs,
but
unfortunately
we're
a
bit
too
late
to
bring
this
to
the
chairs
work
that
has
been
presented
at
hotnet's,
2021
and
bharaji.
The
one
of
the
co-authors
of
that
piper
is
actually,
I
hope,
he's
still
online,
but
at
least
he
was
online
before
so.
We
tried
to
bring
more
existing
work
here,
even
to
the
point
that
we
may
also,
you
know
have
this
work
that
we
find
present
to
the
wider
community.
I
Gab
analysis
to
fill
this
I
mean
if
the
question
I
asked
before
is
answered
positively,
so
we
would
like
to
have
a
gab
in
ours,
because
it's
useful
to
have
that
we
really
would
need
help
here,
would
invite
contributors
to
that
and
and
and
with
the
view
on
the
charter.
The
question
here
that
was
the
bit
of
the
confusion
I
had
wanted
to
do
because
I
thought
the
use
case
craft
was
an
rg
document
already.
I
Gab
analysis
related
work,
new
work
that
exists,
even
if
you
just
send
us
links
if
you
can't
be
bothered
to
get
it
as
a
course
or
into
properly
written
up
we're
happy
to
get
any
material
that
you'll
find
that
you
think
is
relevant
should
be
listed
in
the
in
the
draft.
Please
do
contact
us
to
do
that
if
you
want
to
become
a
bit
more
active
in
helping
us
absolutely
welcome,
certainly
wouldn't
that
would
want
that.
A
I
Yes
yeah,
so
so
the
the
linkage
to
diecast
is
still
in
the
draft,
even
though
I
think
the
draft
actually
have
expired,
and
there
are
aspects
that
are
mentioned
in
the
dyncast
work
that
I
think
would
need
to
be
pulled
more
properly
into
the
draft.
It's
correct,
so
it's
a
little
bit
a
loose
issue
at
the
moment
of
the
draft
it
needs
to
be.
It
needs
to
be
clarified.
Yeah.
I
G
I
A
Thanks
so
much
dirk
really
great
progress,
I
in
the
interest
of
time
we're
going
to
move
forward
in
the
program.
Let's
see,
we
have
the
enhancing
security
and
privacy
draft
and
if
again,
if
you
could
condense
your
talk,
I
know
we've
given
you
ten
minutes
originally,
but
if
you
could
cut
it
down
to
seven
or
eight,
that
would
be
wonderful.
Thank
you
very
much.
N
O
O
O
H
J
A
A
K
K
O
A
A
A
A
O
Oh
yes,
okay,
so
yeah
very
quickly.
There
is
work
which
tries
to
implement
encryption,
also
secure
cryptographic,
functions
for
encryption
and
hashing
in
the
data
plane,
so
this
lays
the
foundation
for
security
and
privacy
applications
such
as
implementing
security
standards,
for
example,
ipsec
or
macseg
in
the
data
plane,
and
it
might
also
allow
for
onion
routing
or
message
authentication
in
the
future.
O
O
O
Yeah,
we
can
also
use
computing
in
the
network
to
improve
intrusion
detection.
One
one
potential
here
is
to
allow
for
inline
detection
and
a
quick
reaction
to
anomalies,
but
we
can
also
reduce
the
load
on
existing
intrusion
detection
systems,
and
this
is
exactly
what
lewis
and
I'll
do
so
here.
They
apply,
rule-based
pre-filtering
in
the
data
plane
and
by
that
they
achieve
a
traffic
reduction
of
up
to
75
percent
at
the
actual
ids.
O
Okay,
next
slide,
and
last
we
looked
into
network
monitoring,
which
can
be,
for
example,
used
for
network
forensics,
and
here
soundcheck.
I,
for
example,
propose
flow
monitoring
on
p4
based
hardware
switches,
so
they
pre-process
packets
in
the
data
plane
and
then
very
efficiently
create
floor
records
in
the
control
plane,
and
this
offers
a
high
performance
and
cost
efficient
alternative
for
accurate
flow
monitoring
in
comparison
to
existing
solutions.
O
Yeah
so
to
conclude,
we
see
increasing
interest
of
research
community
and
that
underlines
our
intuition
about
the
possibilities
that
coin
provides
for
security
and
privacy
and
also
its
relevance,
and
this
is
confirmed
by
recent
publications
which
match
the
ideas
of
our
draft
and
they're
published
at
high
rank
values.
For
example,
usenix
security
and
existing
work
also
provides
first
proofs
of
concept
which
show
that
implementing
security
in
the
network
is
actually
feasible.
O
A
O
A
A
A
One
is
just
that
if
you
have
don't
know
already
that
hot
nets
is
going
on
in
parallel
this
week
and
there's
some
very
interesting
work,
and
the
second
point
of
interest
is
that,
of
course,
we've
been
threatening
to
have
an
interim
in
order
to
review
our
scope,
and
I
think
we
really.
We
would
like
to
do
that
halfway
between
this
ietf
and
the
next
so
stay
tuned.
A
For
that
we
welcome
your
inputs
on
the
mailing
list
and
thank
you
to
so
many
of
you
for
sticking
it
out,
despite
the
network
errors
for
arriving
at
whatever
hour,
it
is
in
your
time
zone
many
of
those
time
zones
it's
an
inconvenient
hour.
So
thank
you
for
being
here
and
to
all
the
presenters
for
the
terrific
presentations.
