►
From YouTube: IETF112-TSVWG-20211108-1430
Description
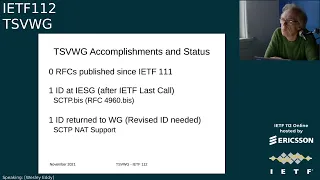
TSVWG meeting session at IETF112
2021/11/08 1430
https://datatracker.ietf.org/meeting/112/proceedings/
D
A
C
A
E
C
A
A
E
C
David's
rejoining
and
gory's
gonna
fix
his
audio,
but
I'll
go
ahead
in
the
meantime,
the
there's
a
brief
reminder
if
you're
gonna
submit
any
drafts-
and
you
want
the
working
group
to
notice
them
add
the
tsvwg
to
the
id
title
and
for
meet
echo
today,
use
the
hand
icon
to
join
the
mic
queue.
So
we
can
see
that
you
want
to
say
something.
C
There
are
a
lot
of
documents
in
the
working
group
that
we're
trying
to
get
input
on
and
have
reviewed
one
good
way
to
make
sure
that
your
documents
get
reviewed
is
to
review
other
people's
documents.
So
we
always
encourage
people
to
do
that.
Some
particular
ones
of
interest
right
now
are
the
ones
on
udp
options
and
dscp
related
ones
which
we'll
talk
about
in
a
second.
C
C
D
Yeah
l
for
lfrs
has
been
kind
of
pre-kind
kind
of
preempting
us.
I
think
we
need
a
a
paragraph
or
two
of
carefully
crafted
text
for
the
first
of
them.
As
noted
on
the
slide.
The
second
draft
is
also
is,
is
is
ready
to
go,
but
the
first
one
is
still
caught
still
causing
headaches
and
bob,
and
I
just
been
putting
too
many
cycles
into
l4s
and
my
day,
job
continues
to
get
in
the
way
of
my
ietf
activity.
C
C
So
aside
from
those,
there
are
a
number
of
other
working
group
drafts
that
are
in
progress.
There's
the
operational
guidance
on
l4s,
the
nqb
diffserv
php
draft
udp
options,
datagram
plp
mtud
for
udp
options,
which
we
have
added
to
the
charter
and
plan.
To
finish
up.
In
parallel
to
the
udp
options,
there
is
dta
tls
with
sctp
updates
and
there's
been
some
discussion
of
the
ipr
disclosure
related
to
that
there's.
A
new
draft
on
the
diffserv
default
dscp
selection,
which
martin
has
recently
sent
his
comments
on,
and
we
adopted
the
multi-path
dccp
work.
C
All
right,
so
here's
some
changes
to
milestones
so
the
nqb
php
we
plan
to
submit
around
the
april
time
frame
and
both
the
transport
options
for
udp
and
the
well.
The
acronym
is
messed
up
on
this
chart,
but
the
datagram
plpmtud
for
udp
options.
Those
are
both
planned
to
go
around
the
same
time
in
may.
D
C
And
the
first
two
items
on
this
chart
are
the
ecn
drafts
that
we've
been
holding
for
a
while
that
david
will
be
working
with
bob
to
try
to
get
updated
and
then
there's
still
going
to
be
a
good
amount
of
activity
to
be
done
here
on
the
l4s
drafts,
as
we
try
to
wrap
up
on
those
figuring
out
how
to
how
to
proceed
with
some
of
the
changes
that
the
working
group
last
call
is
calling
for
and
we
have
no
liaison
updates.
But
there
are
some
liaison
requests
listed
here,
david
or
corey.
D
C
A
A
A
C
Okay,
so
for
today
the
agenda
is
summarized
here:
we're
going
to
have
martin
talk
about
code
of
conduct
a
bit,
then
we
have
updates
on.
What's
going
on
with
the
l4s
working
group
last
call
the
updates
to
the
drafts
and
the
operational
guidance,
and
if
time
should
permit
greg,
has
some
material
on
the
nqb
drafts.
C
G
Thank
you.
Do
you
have
the
slide
yep
good
day,
everyone?
I
just
have
the
one
slide.
This
isn't
all
that
long,
but
these
are
just
a
few
highlights
from
the
code
of
conduct.
The
ieb
and
iesg
are
have
committed
to
make
another
effort
to
encourage
the
tone
of
conversations
in
the
ietf
for
reasons
that
I
think
are
probably
obvious.
G
There
are
some
remedies
in
the
code
of
conduct
for
people
who
aren't
observing
these
these
tenets,
but
for
the
time
being,
we're
going
to
focus
on,
as
maybe
you've
might
have
observed,
on
the
list
going
to
focus
on
just
sort
of
identifying
behavior
that
we
don't
believe
corresponds
to
the
code
of
conduct
and
calling
it
out
and
hopefully
establishing
norms
that
get
us
in
a
better
place.
I'm
just
going
to
ask
you
to
do
a
couple
things
number
one.
G
G
You
may
have
a
good
beer
and
laugh
about
that
afterwards,
but
that
that
kind
of
sets
a
bad
tone
for
other
people
might
have
ideas
that
they
might
think
would
be
received
harshly
and
then.
Finally,
the
other
thing
I
would
ask
is,
I
think,
many
of
you.
There
are
two
ways
to
react
to
this
effort
and
this
stuff
about
the
code
of
conduct.
One
is
to
think
about
all
the
ways
in
which
you've
been
wronged,
and
many
of
you
have
been,
but
it'd
be
much
more
constructive.
G
Think
about
how
you
know
how
maybe
you
have
not
lived
your
best
self
in
with
respect
to
this,
so
I
ask
you
all
to
use
that
constructive
attitude
towards
it
and
not
worry
about
the
former.
We
can't
really
do
anything.
What's
happened
in
the
past,
we're
gonna
try
to
fix
what
happens
in
the
future.
So
that's
really
all
I
had.
Does
anyone
have
any
comments
or
questions.
G
G
Yeah
I
mean
like
tswg
obviously
is,
is
a
group
where
this
has
been
a
problem.
Historically,
specifically
the
air
force
debate
and
oh
yeah,
I
it
I
mean,
certainly
again,
I
I
don't
want
this
to
be
out
pointy
fingers,
but
like
there's,
certainly
we
do
not.
This
is
not
an
environment
that
is
conducive
to
newcomers
and
and
differing
opinions
coming
out
into
the
open.
So
it's
one
reason
I
wanted
to
personally
get
up
in
front
of
this
group
and
talk
about
this.
Any
other
comments.
G
C
This
was
a
great
working
group
last
call
in
terms
of
the
number
of
responses
we
got,
which
I
know
I've
been
working
in
the
itf
for
a
long
time
and
don't
recall
ever
seeing
that
many
responses
to
a
working
group
last
call
in
in
this
working
group.
So
that
was
really
good.
We
got
the
full
spectrum
of
possible
responses
that
you
could
imagine.
C
C
The
chairs
didn't
see
that
this
is
something
the
working
group
really
has
consensus
on.
At
least
it
didn't
seem
like
it
yet.
However,
we
thought
there
might
be
appetite
to
plan
to
do
that
in
the
future
if
the
l4s
experiment
is
looking
successful,
so
we
thought
that
before
going
forward
with
this,
we
should
at
least
try
to
sketch
what
the
working
group
thinks.
The
long-term
plans
are
that
this
is
a
part
of
and
that'll
help
the
iesg
understand.
D
D
If
you
look
for
the
word,
compromise
you'll
find
the
initial
attempt
to
write
those
aspects
up
which
is
not
as
clear
not
as
clear
as
it
could
be,
and
there
will
need
to
be
significant
discussion
to
make
sure
we've
got
this
right
and
a
particular
we're.
Just
we
correctly
describe
the
places
in
which
it
does
not
align
with
options
does
not
align
with
option
three.
B
D
D
But
I
mean
it
is
jonathan,
it
is
as
a
foundation.
I
think
it
is
clear
all
concerned
that
l4s
does
not
fully
comply
with
option
with
option
three,
which
is
a
peaceful
coexistence,
and
I
forget,
I
think
it's
peace
code,
just
something
or
something
like
that
with
existing
traffic
and
the
extent
to
which
it
does
not,
and
whether
that's
a
problem
are
things
things
that
that
the
working
group
gets
gets,
gets,
gets
to
sort
out
in
discussion.
D
D
C
So,
thank
you
and
and
yeah.
Finally,
the
third
item:
I
think
that
was
a
big
one
for
us
was
there's
a
disagreement
in
the
comments
we
received
about
the
sort
of
results
of
risk
analysis
and
how
likely
there
are
to
be
problems
and
if
the
is
significant
enough
to
motivate
not
going
forward
or
not.
So
we
have
more
of
a
challenge
with
that
one.
C
So
there
will
have
to
be
a
little
bit
more
discussion
around
that
and
confirmation
through
the
mailing
list,
and
there
are
a
number
of
additional
concerns
that
need
more
work.
These
were
the
big
ones
that
we
had
agreed
amongst.
The
chairs
that
could
drive
interims
if
needed,
but
were
most
important
to
resolve.
C
A
number
of
them
are
we're
considering
lesser
criticality,
for
instance,
there
are
a
number
about
specifics
of
the
dual
queue
construction,
but
since
that
is
a
sort
of
optional
component
of
the
l4s
architecture,
there
are
alternatives
to
it.
It's
not
something
we
think
is
blocking
everything.
The
way
that
these
other
big
issues
are,
and
that's
all
I
have
on
the
working
group
last
call
status-
is
going
to
present
the
updates
to.
D
D
H
Yep,
good,
okay,
so
the
giraffes
have
that
the
draft
numbers
are
there
there's
a
number
of
other
people
have
helped
with
this,
but
they're
the
three
main
authors.
If
I
move
to
the
next
or
if
you
could
move
to
the
next
slide,
please
just
to
recap
for
anyone
that
doesn't
know
what
l4s
is.
Essentially,
it
enables
more
high
fidelity
marking
more
high
fidelity
congestion
control
so
that
you
don't
have
this
compromise
between
either
low
queueing
delay,
low
amplitude
variation
of
queuing
delay
or
low
utilization.
H
H
There
look
into
all
those
tests-
and
I
I
guess
the
main
things
that
have
been
coming
out
recently
are
a
work
on
bursts
from
bursty,
lynx
upstream
of
l4s
and
unbestie
flows,
and
I
I'll
I'll
talk
later
about
particularly
the
latter
of
those,
but
also
well,
both
of
them
actually.
But
so
these
are
really
heads
up.
In
fact,
the
whole
presentation
is
heads
up
because
there's
not
really
enough
time
to
go
into
everything.
H
That's
happening
in
detail,
so
the
next
one
is
that
tokay
and
eric
dimaze
have
released
a
patch
and
it's
been
applied
to
the
release
of
limits
that's
currently
being
merged
in
for
the
for
net
next,
which
essentially
takes
an
existing
part
of
fq
coddle.
That
was
designed
for
data
centers
with
a
low
shallow,
immediate
threshold
and
makes
it
so
that
it
will.
H
Toki
has
done
that
with
a
nice
using
using
the
classification
architecture.
So
with
the
traffic
control
command
you
can
you
can
set
it
up,
so
you
can
also
use
diff
service.
You
want
as
part
of
the
classifier
but
I've
given
the
command
there
to
give
the
ust1
field
as
the
classifier
for
that
threshold,
and
then
you've
got
alpha
support
in
fq
coddle.
So
people
can
test
it
use
it.
Try
it
out
all
the
rest
of
it.
H
F
F
H
Yeah
thanks
next
slide,
then,
so
the
I've
got
three
slides
one
on
each
draft,
and
this
is
a
summary
so,
as
well
said,
there
was
a
lot
of
response
and
you
know
other
than
the
sort
of
plus
ones.
And
yes,
I
agree
or
don't
agree
or
whatever
there
was
some
substantial
reviews
and
shown
here
for
each
draft
from
each
person
and
I've
added
on
the
end.
H
You
know
conversation
that's
been
going
on
with
the
chairs,
particularly
about
the
text
on
4774
and
also
the
authors
themselves
have
generated
quite
a
bit
of
churn
in
the
in
the
by
noticing
things
in
the
drafts.
While
we've
been
editing
it
all.
So
I
would
also
say
that
the
probably
the
the
left
hand
most
reviews,
particularly
the
the
left
foremost,
have
done
a
really
good
pass
through
a
couple
of
them
all
three
documents
and
two
of
them
two
of
the
documents
and
picked
up
a
lot
of
things.
H
H
H
The
basis
of
and
I'd
never
actually
checked
the
code,
and
it
wasn't
right,
and
that
meant
some
of
the
references
we
use
where
we
did
all
the
original
maths
and
things
in
that
the
dual
queue
relies
on
were
had
errors
in
them.
It
turns
out
the
errors,
didn't
actually
change
anything
anything
in
the
code,
because
most
of
the
code
relied
on
the
worst
case
to
reno
not
cubic,
but
it
just
meant
that
we
couldn't
refer
to
all
these
papers.
H
We'd
written
all
the
cubic
stuff
in
so
essentially
had
to
rewrite
all
that
so
that
we
could
refer
to
it
and-
and
that's
made
appendix
c
in
the
dual
q
draft
a
lot
longer,
because
that
has
sort
of
re-create
all
that
maths
and
and
in
ascii
and
and
that
that
caused
a
lot
of
work,
which
is
one
of
the
reasons
why
all
the
responses
to
everyone
else's
comments
took
so
long
to
get
started.
Because
I
wanted
to
make
sure
that
we
had
the
foundations
there
again
and
it
turned
out
the
foundations.
H
H
And
so
but
but
I
guess,
once
you're
in
working
group
last
call
you
sort
of
get
out
of
the
itf
meeting
cycles
a
bit
and,
for
instance,
you're
allowed
to
post
drafts,
even
when
the
servers
are
closed,
and
things
like
that.
So
please
bear
with
bear
with
us
and
I'm
sure
the
chairs
will
give
some
time
for
people
to
now.
Look
at
the
new
text
that
has
now
appeared,
and
I
can.
H
I
can
confirm
that
I
believe
all
those
reviews
have
been,
or
I've
attempted
to
address
all
the
points
in
all
those
reviews,
some
of
which
were
considerably
deep,
involving
quite
large
amounts
of
change.
So
thank
you.
Everyone
and,
if
you
think
yours
hasn't
been
dealt
with
your
review
of
the
the
documents,
then
that
means
I've
missed
it.
H
So
I
I've
also
because
of
the
rush
in
the
last
few
days.
I
I
normally
give
a
summary
of
the
diffs
of
each
draft.
I
will
do
that
on
the
mailing
list,
rather
than
having
to
rely
on
going
and
looking
at
the
full
text
diffs
with
which
don't
tell
you
which
of
the
important
diffs
compared
to
the
unimportant
editorial
stuff
or
less
important,
and
apologies
again
for
just
in
time
posting
now
the
next.
H
If
you
can
move
the
next
three
slides
on
the
next
slide,
I'll
go
through
each
slide,
giving
normative
technical
editorial
changes
and
on
the
alphas
architecture
there
are
no
normative
changes,
because
it's
not
a
normative
document.
In
fact,
it
doesn't
even
have
a
section
saying
anything
about
must
and
should
and
what
and
what
they
mean.
It
doesn't
refer
to
rfc
2119
about
that
sort
of
stuff.
H
H
I
I've
said
there
are
no
technical
changes
in
the
off-road
architecture.
I
mean
all
the
editorial
stuff
is
pretty
technical,
but
it's
not
it's
not
changing
the
description,
the
technical
stuff.
It's
it's
clarifying
it.
So
I
would
you
know,
there's
no
technical
changes,
but
there
there
was
quite
considerable
rewriting
of
the
descriptions
of
the
technical
stuff.
C
H
H
No,
no,
I
don't
intend
to
discard
them,
but
I
mean
say
for
instance
jonathan's
I
I
I
was
going
to
go
on
the
list
now
I
I
needed
to
get
the
draft
sorted.
I
was
going
to
go
on
the
list
and
and
talk
about
those
points,
but
I
could
you
know
the
the
attempts
we're
doing
to
to
talk
about
the
deficiencies
and
and
things
in
the
drafts.
H
D
H
D
We,
if
you
could
send
a
note
to
the
list
that
basically
summarizes
the
peoples
whose
names
aren't
on
this
slide
because
of
what
you've
just
got
what
you've
just
gone
through.
We
would
at
least
acknowledge
that
as
part
of
the
process,
those
comments
are
those
comments.
Are
there
and
we
will
we'll
get
are
in
need
of
being
dealt
with.
I
mean,
for
instance,.
H
Let
me
just
say
this:
pete
heiss
gave
her
pointers
to
all
his
experiments,
and
then
he
reviewed
the
three
drafts
and
at
the
moment
I've
only
dealt
but
I've
still
got
or
someone
some
one
of
the
proponents
has
got
to
deal
with
talking
about
each
of
the
each
of
the
points
he's
raised.
Obviously,
a
lot
of
them
have
come
up
in
in
talking
about
the
the
the
points
he's
made,
reviewing
the
reviewing
the
drafts,
but
you
know
just
to
just
for
a
process
point
of
view.
H
H
Actually,
the
first
two
sub-bullets
of
normatives
haven't
yet
involved
any
change,
but
I'll
go
through
all
four
and
I've
got
a
spare
slide
on
the
on
the
last
two
sub
bullets
of
normative.
If
we
need
it
so,
firstly,
on
the
prague
requirements,
particularly
on
the
one
about
detecting
classic
ecn,
aqms,
as
amazingly
didn't
have
any
comments,
except
for
jake.
H
So
in
fact,
all
through
since
we've
written
all
that
no
one
has
commented
on
that
normative
text
in
in
section
4.3,
except
for
jake
and
and
jake,
tried
to
improve
it.
I've
I've
responded
to
jake
and
he
probably
had
no
time
to
process
it
because
it
was
yesterday.
I
think
it
feels
like
a
hours
ago,
but
I
think
it
was
yesterday
and
so
there's
likely
to
be
some
more
conversation
on
that.
H
H
What
the
center
does
on
whether
it's
an
fq
or
a
dual
queue,
but
we
we
deliberately
didn't
want
to
do
that,
because
it,
the
center,
doesn't
know
for
sure
what
it
is.
So
we
we
tried
to
condition
it
on
problems
in
quotes.
You
know
what
detecting
problems
so
anyway,
there's
like
to
be
more
on
that
the
sorry
someone
trying
to
speak
jake.
I
H
H
H
H
Okay
right,
okay,
that's
fine!
Then,
let's
jump
to
the
final
slide.
This
final
spare
side,
then,
for
those
last
two
bullets
keep
going.
No,
the
the
the
spare
slide
right
at
the
end
right.
So
here
there
are.
There
are
three
areas
where
normative
text
it's
difficult
to
say
whether
it's
changed.
It's
it's.
The
subject
of
the
text
of
the
of
the
normative
statement
has
changed
to
correct
it,
but
just
th
these
aren't
actual
diffs
they're,
just
sort
of
paraphrased
diffs.
H
H
H
So
it
didn't
really
change
the
sense
of
the
mandatory
statement,
but
it
changed
the
subject
of
it
and
the
last
one,
both
pete
heist
and
stuart
picked
this
one
up
and
and
I'm
still
not
sure
whether
it's
right
or
even
necessary.
So
maybe
we
can
take
that
discussion
to
the
list,
but
it's
essentially
if,
if
an
l4s
is
about
excluding
certain
machines
that
are
trying
to
you,
know
wanting
to
use
l4s
from
being
able
to.
H
H
H
C
H
H
Yeah,
okay,
so
just
move
to
heads
up
then,
rather
than
explaining
things,
there
was
technical.
New
technical
texts
put
in
about
limiting
packet
bursts
both
from
upstream
links,
particularly
from
upstream
links,
but
also
added
some
open
questions
on
bursty
traffic
and
had
some
conversation
on
the
list
about
that
and
and
trying
to
do
more
work
on
that
and
next
slide
the
editorial
we
can
jump.
H
I've
explained
the
stuff
that
got
put
into
the
dual
queue,
which
is
the
fourth
sub
bullet
there
about
choosing
the
coupling
factor
and
rtt
independence
and
all
the
maths
there
and
again,
that's
where
the
stuff
on
potentially
bursty
traffic
or
the
bursty
trafficking.
The
potential
problem
and
potential
solution
is
in
appendix
a
there's,
been
some
discussion
on
the
parameters
in
the
pi
2
parameters.
Paper.
That's
been
updated
and
that's
the
sorry
I'm
working
backwards
up
the
bullet.
H
H
F
Thank
you
for
that
presentation.
Bob
you
mentioned
my
name
on
one
of
the
slides
and
said
you
wouldn't
presume
to
try
to
sum
up
what
I
said,
which
I
understand
took
me
while
thinking
about
it
I'll
try
to
give
a
summary
now
of
my
main
points
there
in
recent
years
on
the
internet,
there's
been
lots
of
work,
increasing
bandwidth,
that's
been
enormously
successful,
gone
from
dial
up
to
megabits
to
gigabits,
but
working
latency,
latency
under
load
has
not
improved,
and
my
real
worry
is.
We
should
not
become
complacent.
F
We,
this
community,
should
not
casually
assume
that
the
internet
will
continue
to
exist.
We
know
there
are
various
communities
around
the
world
working
on
creating
a
replacement
for
the
internet,
and
you
can
see
all
their
web
pages
saying
how
great
they
are,
which,
incidentally,
run
over
our
internet,
but
leave
that
aside,
the
people
working
on
x25
in
america
online
probably
thought
that
those
would
continue
to
exist
too.
F
F
B
F
Uses
ecm
that's
a
billion
devices.
We
have
found,
basically,
no
networking
equipment
run
by
any
operator
ever
marks
the
packets.
That's
what
I
meant
by
it's:
a
failure.
We've
for
five
years,
we've
had
ecm
turned
on
on
every
iphone
and
linux
has
it
turned
on
as
well,
and
we
see
no
ce
marking
in
the
network
ever.
I
Yeah
just
to
respond
as
dirt's
point,
I
I
do
think,
there's
good
evidence
that
there
are
tens
of
millions
of
devices
deployed.
They
don't
mark
very
frequently,
but
the
problem
here
is
that
as
we
get
into
their
their
deployment
and
their
presence,
there
causes
trouble
for
other
traffic
marked
or
not.
But
you
know
it's
it's
the
it's
the
backward
incompatibility
in
the
signaling
here.
I
I
guess
we've
hashed
this
out
a
bunch
but
yeah
the
while
we
well.
I
would
not
disagree
with
the
characterization
that
it's
failed.
You
know
it
doesn't
help
that
much
and
it's
it's
a
pretty
expensive
location,
but
but
that
doesn't
mean
that
there's
no
deployment
and
that
we
don't
have
to
worry
about
it,
and
this
is
yeah.
This
is
the
the
core
of
the
problem
to
me,
but
I
guess
we
can
discuss
it
more
on
this.
Thanks.
J
Hi
hi
hi
david
and
everyone
yeah
this
this
slide
deck
is
just
effectively
a
diff
of
you
know
the
edits
that
have
been
made
in
the
draft
since
the
last
published
version.
So
I
think
I
can
do
it
in
a
minute
and
then
people
can
look
offline
and
see
if
they
have
comments
to
take
to
the
list.
So
if
you
want
to
go
to
the
next
slide
quest
yeah,
I
won't
talk
about
this
one
actually
going
to
the
next
one.
J
This
is
the
summary
I
sent
to
the
mailing
list
verbatim
so
and
I
have
in
this
deck
a
slide
for
each
one
of
these.
That
goes
into
a
little
bit
more
detail
about
what
the
changes
were.
So
that's
the
next
eight
slides
then-
and
I
think
you
can
just
at
this
point
flip
through
those
for
just
so
folks
know.
What's
in
the
deck
and
again
we
can
take
discussion
to
the
list.
I
think
on
this
one.
