►
From YouTube: IETF113-SAAG-20220324-0900
Description
SAAG meeting session at IETF113
2022/03/24 0900
https://datatracker.ietf.org/meeting/113/proceedings/
A
A
A
Okay,
good
morning,
good
afternoon,
good
evening,
everyone
this
is
the
security
area
advisory
group.
Sag
we're
going
to
get
started.
I
think
some
folks
are
going
to
start
filtering
in
welcome.
My
name
is
roman
diniglio.
I
am
one
of
the
security
area
directors
and
up
in
front
of
you
in
the
room
is
our
other
new
security
area.
Director
welcome
paul,
want
to
say
hello,
hello,.
A
Well,
it's
later
in
the
week,
but
I
do
want
to
remind
everyone
that
the
notewell
still
absolutely
kind
of
applies,
and
this
reminds
you
of
your
responsibilities
in
participating
in
the
ietf,
but
really
to
put
a
finer
point
on
it.
I
would
just
like
to
emphasize
to
everyone:
we
all
have
to
live
the
itf
code
of
conduct
and
the
idea
here
is:
we
really
need
to
make
sure
that
when
we
interact
with
each
other,
we
keep
we
keep
things
professional,
we're
respectful
to
our
colleagues.
A
A
A
A
A
No
okay,
perfect.
So
in
that
case,
let's
keep
going.
We
have
a
number
of
working
group
summaries
coming
in.
We
won't
talk
about
the
working
groups
that
sent
a
report.
You
can
either
go
to
sag
to
see
the
ones
that
were
sent
or
we'll
see
kind
of
links.
If
anyone
wants
to
proactively
start
queuing
up
for
work
groups
to
to
give
a
heads
up,
please
by
all
means
kind
of
do
it
so
ace
sent
a
report.
B
A
A
C
A
A
D
A
Thanks
sean
okay,
so
we
have
a
number
of
working
groups
meeting
later
this
week.
You
can
see
them
there.
Some
have
already
proactively
sent
a
report
if
any
of
the
chairs
or
someone
from
those
working
groups
wants
to
come
up
to
to
have
any
words
by
all
means
kind
of.
Do
that
we'll
also
jump
to
the
working
groups
that
are
not
meeting.
A
E
Hi
justin
richer.
The
http
working
group
has
made
significant
progress
on
both
http
signatures
and
http
digests
in
recent
months,
and
I
would
encourage
people
in
the
sec
area
to
go.
Take
a
look
at
both
of
those
two
specs.
They
are
things
that
kind
of
bridge
the
apps
and
sec
areas.
So
even
though
they
are
hosted
in
http,
it's
going
to
be
adventurous
to
a
lot
of
folks.
Here
too,
and
we'd
appreciate
the
eyes.
Thank
you.
F
And
this
is
barry
lieber
talking
about
dmarc,
we
did
not
meet
here.
We're
we're
gonna
have
an
interim
at
some
point.
Soon
we
we're
working
on
the
proposed
standard
version
of
the
former
experimental
spec
and
are
currently
debating
the
what
the
text
is
to
get
rid
of
the
public
suffix
list
usage
and
use
a
tree
walk
instead
and
that's
causing
a
bit
of
controversy
in
the
working
group.
But
it's
it's
resolving.
So
that's
where
we
are.
G
Hey
tim,
capalli,
microsoft
and
w3c,
just
something
to
be
aware
of
there
is
an
effort
going
on
to
redefine
how
authentication
works
in
the
browser,
essentially
bringing
the
browser
into
a
more
active
role
in
things
like
oauth
and
openid
connect.
It's
a
significant
shift.
Obviously,
so
it's
just
something
to
be
aware
of.
There
is
a
community
group
that
I'm
a
co-chair
of
called
the
federated
id
community
group
where
one
of
the
proposals
is
kind
of
sitting
because
it
doesn't
have
a
home
and
that
is
open
to
anyone
to
join,
because
it's
a
community
group.
A
A
Okay?
Yes,
I
think
so
all
right.
Thank
you.
So
the
other
thing
I
would
add
to
none
to
things
happening
outside
the
itf
we've
mentioned
in
a
couple
of
working
groups.
We
had
a
talk
on
it
at
a
previous
itf.
The
nist
round.
Three
pqc
decision
is,
should
be
coming
real
soon
now
real
soon
now,
so
we
I
think
we
are
all
impatiently
waiting
for
the
results
and
that
that'll
probably
trigger
quite
a
lot
of
work
inside
the
the
itf
okay
moving
along.
A
So
that
was
the
that
was
the
the
commentary
on
the
working
groups
agenda-wise.
We
are
now
seamlessly
moving
into
the
a.d
portion
of
this
and
we
have
a
lot
of
material
here.
The
the
motivation
is
that,
over
the
course
of
over
the
course
of
time
from
the
last
meeting,
the
ads
get
all
sorts
of
questions
about
what's
happening
in
the
sec
area,
we're
just
trying
to
be
as
transparent
as
possible.
A
So
we
summarized
all
the
different
inbound
requests
that
we
that
we
get
on
a
I
don't
want
to
say
on
a
regular
basis,
but
things
we
commonly
get
between
meetings
and
want
to
put
it
out
here,
put
it
out
here
to
the
community,
paul
and
ben.
Then
please
kind
of
jump
in
here
kind
of
heckle
me
or
kind
of
make
additional
commentary
as
we
as
we
get
through.
All
of
this
all
right,
so
there's.
In
addition,
all
the
different
working
group
documents.
We,
of
course,
are
sponsoring
different.
A
A
H
I
While
the
author
and
I
tried
to
get
some
agreement
about
what
the
changes
that
actually
were
needed
were-
and
so
I
don't
know,
if
there's
a
clear
plan
for
getting
that
to
happen,
but
I
may
have
some
more
cycles
to
think
about
it.
Now
that
I'm
not
in
the
day-to-day
grind
of
reading
a
bunch
of
documents.
Every
week.
A
A
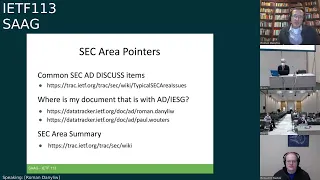
This
is
just
a
list
of
urls.
We
wanted
to
just
continually
continue
to
kind
of
remind
everyone
in
the,
in
the
course
of
of
that
that
grind
to
review
the
documents,
because
that
is
certainly
how
it
feels
sometimes
in
preparation
for
the
telechat,
historically
ben
and
I
and
paul
will
be
adding
kind
of
a
zone.
We
thought
we
find
things
honestly.
We
see
a
lot,
we
wish.
A
We
did
not
see
a
lot
and
we
just
want
to
make
sure
kind
of
in
advance
folk
folks
understand
what
are
common
things
that
we
will
drop
discusses
on.
So
if
you
have
questions
your
colleagues
are
asking,
what
should
I
do
to
make
sure
the
security
review
goes?
Okay
or
frankly,
you're
pushing
a
document
forward
is
how
do
I
make
sure
that
that
things
aren't
discussed
on?
Please
do
consult
that
list
and
share
that
with
your
colleagues.
A
We
also,
we
often
always
get
questions
of
well.
I
see
what's
happening
in
the
working
group,
but
you
know
what
are
the
80s
doing
if
you
want
a
real-time
view
into
what
our
queue
is
and
what
everything
kind
of
the
disposition
of
all
those
things
you
can
directly
click
those
urls
and
get
insight
into
all
of
that
ben,
and
I
also
use
the
history
field
of
the
data
tracker.
And
so,
if
you
know
you
can
look
at
the
states,
the
states
kind
of
describe
where
we
are
in
the
process.
A
But
if
you
want
additional
information
for
example,
what
does
it
mean
to
say
revised
id
needed
like
what
do?
I
revise
for
very
often
you'll
find
those
details
in
that
in
that
history
field
and
then,
lastly,
we're
trying
to
keep
that
wiki
page
about
the
security
area
up
to
date,
especially
to
help
guide
new
work
inbounding
into
the
ietf
and
to
acknowledge
when
it's
been
caught,
but
perhaps
not
in
a
working
group.
Yet
so,
if
folks
from
the
outside
are
are
looking,
we
can
provide
them
a
summary
of
what's
happening.
So
that's
a
link.
A
A
So
working
group
changes
since
the
last
time
we
got
together.
We
in
the
we
we
in
the
itf
had
our
in
an
interim
buff,
something
that
we
don't
do
very
often
on
the
topic
of
of
sharing
credentials,
which
was
called
secret.
It
was
sponsored
out
of
the
art
area
for
folks
that
attended
it.
There
was
some
back
and
forth
about.
Where
would
this
will
ultimately
be
housed?
A
The
decision
was
this:
will
this
is
going
to
be
one
of
those
just
like
skim,
which
is
it's
going
to
stay
in
art
but
overseen
by
a
sec?
A
d
probably
me
so
in
terms
of
kind
of
tracking
sec
area
works.
This
is
in
that
post,
post
buff
phase,
where
it
looks
like
there's
a
lot
of
interest
in
a
working
group.
We
have
a
charter,
but
the
mechanics
of
that
have
not
started
we.
We,
we
spun
up
the
ppm
ppm
working
group
out
of
the
priv
buff.
A
A
A
If
there's
a
lot
of
different
prep
work
so
kudos
to
the
to
the
ppm
kind
of
proponents,
to
having
a
lot
of
things
kind
of
teed
up
in
advance
and
for
having
a
great
community
discussion
to
get
us
here
wanted
to
acknowledge,
acknowledge
some
of
the
changes
we've
we've
had
amongst
our
working
group
kind
of
chairs,
so
in
dance.
Of
course,
paul
is
up
in
front
of
the
room,
so
he
could
not
continue
on
as
working
group
chair,
congratulations
and
thank
you
to
joey
for
for
stepping
up
there.
A
Thank
you,
robbie
for
your
kind
of
service
there
in
kitten
in
ppm,
ben
and
sam
thanks
for
getting
us
getting
us
kind
of
spun
up
and
getting
the
work
started
and
in
skim
aaron.
Thank
you
for
kind
of
stepping
in
to
round
out
our
team.
It
was
just
nancy
there
alone
and
editorially.
We
also
kind
of
forgot
mike
mike
jones.
Thank
you
for
kind
of
joining
the
kosai
team.
A
Overall,
we
put
out
calls,
I
think,
every
time
between
between
meeting
cycles,
certainly
at
least
kind
of
twice
a
year.
If
you
have
interest
in
becoming
a
working
group
chair
by
all
means
gotta,
please
send
us
an
email.
We
do
keep
a
running
list
as
there
are
opportunities,
we
do
consult
that
list
between
kind
of
interest,
skill
set
and
what
we
think
that
working
group
needs
and
I'll
also
just
have
again
kind
of
a
shout
out.
Thank
you,
joey
and
aaron.
You
guys
are
new
time
chairs.
A
We've
gotten
a
couple
kind
of
questions
on
this
one
with
any
ad
turnover
there's
a
reshuffling
of
working
groups.
We
want
to
make
sure
that
you
know
the
skill
sets
of
the
aeds
are
right.
The
needs
of
the
working
groups
are
are
kind
of
satisfied
and
there's
there's
appropriate
kind
of
load
balancing.
So
this
is
the
split
between
paul
and
me.
What
you
see
in
red
is
where
it
wasn't
a
straight
swap,
so
we
started
from
paul
taking
all
of
ben's
working
groups.
A
A
We
are
not
super
great
about
sharing
new
working
group
lists
that
we
create,
so
we're
going
to
be
better
about
that.
So
just
wanted
to
call
out
that
a
couple
weeks
ago
we
made
skit,
which
is
which
is
which
is
mainly
focused
on
supply
chain
integrity
issues.
You
can
get
more
details
about
that
from
the
proceedings.
We
just
talked
about
that
at
the
dispatch
session
on
tuesday.
A
If
you
go
to
the
errata
site,
you'll
see
that
there's
about
250
reported
errata
for
sec
work
so
reported
is
a
precise
label,
which
means
that
someone
has
filed
that
errata
and
nothing
has
been
done
with
it.
So
these
are
unadjudicated
errata
in
the
in
the
sec
area.
You
know
if
you
crunch
the
numbers
a
little
bit
about
60
of
those
are
actually
from
open
working
groups,
so
the
other
40
obviously
is
from
work
that
no
longer
kind
of
has
a
home.
So
it's
a
little
harder
to
deal
with.
A
Folks
take
the
time
from
the
community
to
let
us
know
where
we
may
have
gotten
it
a
little
bit
wrong
and,
let's
make
sure
we
figure
out
whether
that's
right
and
maybe
with
document
updates.
We
can
get
those
fixed
in
line
or
or
with
the
new
errata
overlay
tool.
The
those
changes
will
actually
appear.
A
All
right,
so
so
the
we
have
a
couple
thank
yous
that
we
want
to
have
so
first.
This
is
this
is
a
different
kind
of
hybrid
meeting.
We've
previously
had
meetings
where
there
are
remote
kind
of
participants,
but
they
are
not.
They
are
not
an
overwhelming
majority.
The
the
demographics
were
that
almost
two-thirds
of
sec
was
removed
and
only
one-third
was
on
site,
and
this
created
a
very
odd
situation
where,
potentially
there
are
all
sorts
of
folks
in
the
room,
but
all
the
chairs
are
remote.
A
This
was
this
was
kind
of
a
new
thing
for
us,
so
we
really
wanted
to
make
sure
that
we
had
we
had
backups.
So
a
big
thank
you
to
the
different
sec
working
group
working
group
chairs
that
pulled
double
duty
in
addition
to
having
their
own
kind
of
working
groups,
these
chairs
kind
of
stepped
in
to
be
an
extra
set
of
hands
for
those
chairs
that
and
those
working
groups
that
were
going
to
be
all
remote.
So
thank
you.
Thank
you
for
being
our
backup.
A
A
Another
really
big
thank
you
is
to
our
sector,
reviewers
and
and
tearow
for
running
the
sector.
For
us
these,
these
the
reviews
done
in
in
the
working
groups
as
early
review
in
absolutely
an
ietf
last
call
and
as
we
prep
for
the
telechat
are,
are
invaluable.
They
catch
so
many
issues
before
the
documents
are
kind
of
published
and
kind
of
as
an
ad
ben,
and
I
and
I'm
sure
paul
will
rely.
A
A
So
the
last
thank
you
I
I
wanted
to
we
really
wanted
to
make
here
is
to
thank
is
to
thank
ben.
You
know.
Ben
has
served
two
terms
back
to
back,
so
you
know
kind
of
for
those
that
may
not
be
familiar.
That's
four
years
of
his
life,
where,
in
addition
to
whatever
else
he
has
he
has
got
going
on,
he
is
focused
on
making
the
security
area
work.
For
us.
A
One
of
the
things
that
I've
learned
about
the
ad
role
is
that
you
really
turn
it
into
what
you
want
it
to
be.
It's
what
you
invest
in
it
and
ben
has
been
amazingly
generous
with
his
time
and
expertise,
and
you
know
kind
of
personally
here
I
probably
learned
as
much
about
the
protocol
innards
from
the
weekly
sinks.
We
have
to
talk
about
what's
happening,
as
I
did
from
actually
reading
the
documents.
So
really
thank
you
for
that
ben.
A
If
you
published
a
document
in
the
last
four
years,
you
probably
also
know
that
ben
has
redefined
or
really
next
leveled
what
it
means
to
get
a
detailed
security
review.
His
diligence
has,
you
know,
prevented
you
know
so
many
protocols
from
shipping
with
issues
you
know
I.
I
was
kind
of
curious.
So
what's
a
lot
of
protocols,
you
know
what
what
did
ben
really
catch.
So
I
this
isn't.
These
aren't
stats
that
are
easy
to
kind
of
get.
There's
no
interface
for
that.
A
A
So
yeah
ben's
video
is
back,
that's
good,
so
I
don't
know
whether
folks
can
see
what's
behind
ben.
So
for
a
long
time
during
covert,
I
was
looking
at
a
at
a
blank
wall,
and
then
we
had
a
meeting,
I'm
like
what
is
that
blue
box
that
you
have
behind
your
head
so
to
clarify
for
folks
that
can't
see
it.
That's
a
really
nice
blueprint
schematic
of
the
millennium
falcon,
so
saving
the
internet
is
probably
equivalent
to
han
and
luke
saving
the
galaxy
from
the
empire.
A
A
So
your
wall
is
a
little
less
blank
and
there
will
be
we'll
get
that
kind
of
it
would
have
been
more
dramatic
to
give
you
that
kind
of
in
person
we
could
have
maybe
had
a
tall
chewbacca
kind
of
with
you
instead
I'll
make
sure
that
that
gets
shipped
to
you,
there'll
be
a
plaque
inside
it
turns
out.
You
can't
get
things
engraved
with
the
latest
stats
from
the
telechat
from
the
meeting
anytime
soon.
A
So
that's
two
days
away
in
shipping
is
what
I'm
told,
but
you
know
in
all
seriousness
on
behalf
of
the
community
ben.
Thank
you
so
much
for
your
leadership.
You
helped
us
get
the
work
started.
You
made
sure
we
were
on
the
right
track
and
then
you
didn't
let
us
ship
without
frankly
checking
our
work
so
really
much
appreciated.
Then.
Thank
you.
A
I
I
A
H
Okay,
thank
you.
I'd
be
sad.
It's
always
an
interesting
item,
a
lot
of
security
people
wonder
why
is
it
still
there
others
go
like
this?
Is
the
best
thing
ever
so
it's
this
very
dividing
topic,
but
I'll
give
an
introduction,
and
not
that
I
think
I
will
change
people's
minds,
but
maybe
some
of
people
will
know
a
little
bit
better
why
it's
still
around
okay
next
slide.
A
C
H
A
H
H
H
H
H
H
H
So
I'm
going
to
just
briefly
take
off
my
mask
because
it's
hard
to
keep
talking
and
breathing
through
it.
It
includes
various
deployments
and
other
useful
information
configurations
for
various
known
implementations.
It
also
has
a
lot
of
configurations
for
and
and
the
the
sorry
the
nist
and
fips
recommendations.
So
if
you
want
to
immediately
be
be
fip
certified,
you
can
read
through
it
and
we'll
give
you
all
the
guidance
there
as
well.
As
I
say,
it's
a
it's
a
steal
at
only
149
pages.
H
H
So
the
problem
with
ipsec
is
that
it's
actually
a
really
really
powerful
tool
and
you
can
do
everything
with
it
and,
as
with
swiss
army
knives,
anyone
who
owns
one
has
cut
themselves
with
it,
probably
more
than
once.
So
it
can
do
a
lot
of
things.
It
is
complicated,
but
it
is
possible
to
only
just
use
that
one
favorite
tool
you
have
in
there.
You
don't
need
to
use
all
of
these.
H
You
know
tools,
you
can
just
use
the
knife
or
you
can
just
only
use
a
screwdriver,
so
you
pick
what
you
want
and
and
don't
worry
too
much
about
all
the
other
things
that
are
there.
Modern
software
comes
with
fairly
good
defaults,
so
so
configuration
should
be
fairly
minimal,
and
so
so
don't
be
too
daunted
by
your
big
tool.
You
can
you
can
you
can
use
it
pretty
easily
next
slide.
H
So
one
tricky
thing
is
that,
what's
quite
different
from
other
things,
such
as
such
as
tls
is
that
ipsec
consists
of
kind
of
two
protocols.
One
is
the
control
channel,
which
is
the
internet
key
exchange
that
is
used
to
negotiate
everything
and,
of
course
it
has
to
be
done
securely,
so
it
itself
is
also
using
a
whole
crypto
set.
So
so
it
will
do
an
encrypted
session
and
then
once
it
has
an
encrypted
session
it
will.
H
There
are
different
protocols
for
doing
that,
or
there's
encapsulated
security
payload,
which
is
the
one
you
would
be
using,
which
is
just
the
sort
of
standard
packet
encryption
there
used
to
be,
or
technically
still
is,
authenticated
header,
which
is
the
non-encryption
one.
Mostly
due
to
you
know,
25
years
ago,
export
regulations
limited
cpu
powers
of
doing
things.
H
H
H
I
previously
talked
about
this,
so
the
ike
protocol
establishes
the
the
state
and
authenticates
and
authorizes
the
peer,
and
then
it
will
negotiate
ipsec
just
for
for
to
avoid
some
confusion
when
you
send
an
ipacket
and
you
get
a
reply
back,
that's
what
they
call
an
exchange.
So
it's
not
like,
like
exchange,
is
sort
of
a
word,
that's
being
used
in
different
different
ways
with
different
protocols,
but
but
for
ike
it
really
means
you
know
a
request
and
a
response
that
go
together
next
slide.
H
Some
other
confusing
terminology-
and
this
is
really
because
things
are
like
you
know:
25
25,
30,
30
years
old
and,
and
so
things
have
changed,
and
without
dragging
up
too
much
mud
and
old
things
from
the
past
be
aware
that
some
terms
are
used
interchangeably,
depending
on
the
year
of
the
documentation,
was
published.
So
while
I
prefer
personally
to
talk
about
ike
assay,
I
say
sends
for
security
association
and
it's
basically
the
the
state
with
all
the
all
the
information
in
there.
H
H
So
what
does
ibsec
provide?
Roughly
speaking,
there's
like
three
three
things
you
can
do
with
it.
You
can
do
a
host
to
host
encryption
where
it's
only
really
one
host
to
one
host.
It
has
some
advantages
that
you
don't
have
to
encrypt
everything,
including
a
full
ip
header
and
this
network's
a
network
encrypted,
and
that
can
be
like
very
easy.
You
can
have
multiple
networks
to
multiple
networks.
You
can
have
zero
zero
as
your
network.
This
is
like
the
the
tool
that
is
these
days
used
everywhere
to
hook
up
things
together.
H
H
Other
people
use
it
for
connecting
hypervisors,
making
sure
that
there's
a
multi-tenant
isolation,
vxlan
encryptions
tunneling
over
gre
over
an
ipsec
tunnel
like
it,
is
really
sort
of
a
you
know:
secure
ethernet,
cable
that
you
can
stick
in
there
and
and
you
can,
you
can
tie
it
down
as
much
as
you
want.
Some
people
tie
down
a
lot
with
the
policies
and
you
can
be
very
specific.
H
H
H
It
is
protocol
number
50,
and
I
say
they
are
not
port
50,
because
that
is
probably
the
most
hurt
support
question:
when
people
can't
get
it
to
work
because
they
see
the
number
50
they
just
assume
it's
like
udp,
50
or
tcp
50..
They
don't
understand
that
esp
is
a
different
protocol,
because
most
non-ietf
humans
have
only
heard
of
like
udp,
tcp
and
icmp,
and
they
don't
know
about
anything
else,
so
that
is
in
practice.
This
is
a
bit
of
a
problem
I'll
get
back
to
that
later.
H
So
what
is
it?
What
is
a
packet
like
that?
Look
like
it's
a
fairly
standard
like
it.
It's
it's
similar
to
to
how
the
lesson
groups
think
it's
similar
to
how
other
other
encryption
protocols
work,
because
it's
actually
mostly
the
property
of
the
of
the
cryptography
there's
some
identifying
answers
to
to
detect
which
tunnels,
if
you
have
more
than
one
ipsec
connection,
you
want
to
be
able
to
distinguish
them,
so
the
spies
are
there.
H
H
Does
traffic's
like
us
in
them
that
can
sort
of
dictate
policy
for,
for
what
is
what
is
which
packets
are
allowed
to
go
in
and
out,
and
you
can
do
padding.
You
can
send
obfuscation,
packets
that
are
basically
like
empty
packets
just
to
make
it
harder
for
for
an
observer
to
figure
out.
What's
exactly
going
on,
it
supports
compression,
it's
a
really
complicated
story.
I
really
don't
want
to
get
into
right
now,
but
in
general
you're,
just
better
off,
not
not
trying.
You
can
also
do
very
high
speed
things.
H
The
the
limiting
factor
on
the
protocol
used
to
be
the
sequence
number,
but
with
extended
sequence
number
we
basically
just
display
the
last
bits
and
we
remember
the
higher
bits
and
don't
send
them
over
the
wire,
but
we
make
them
part
of
the
the
calculation
of
the
crypto
and
the
the
signature
checks.
So
you
can
actually
reach
like
a
100,
gig
or
more
per
second
speeds.
H
H
So
there's
there's
kind
of
two
modes:
there's
transport
mode
and
tunnel
mode
and
transform
mode
is
really
used
for
the
host
to
host
and
it
has
less
overhead
it.
Doesn't
it
it
reuses
part
of
the
ip
header
and
and
protects
the
parts
of
the
ip
header
that
can
be
protected,
that
that
don't
change
between
hops
and
and
the
good
thing
is
that
there's
less
overhead,
so
you
get
a
more
of
your
original
mtu.
H
Of
course,
this
completely
fails
with
nat.
As
soon
as
that
happens,
then
things
get
rewritten,
there's
various
clever
hacks
to
make
it
work
anyway.
That's
how
sort
of
microsoft
kept
l2p
with
ip
second
transport
mode
through
net
working
and
when
I
say
sort
of
working
you
can
see
the
last
line
there.
It
is
what
you
end
up
is
in
ip
pack
it
into
ppp
packet
into
an
l2p
packet
into
an
esp
packet
into
a
udp
packet,
and
that's
just
what
you're
doing
yourself.
H
Then
your
isp
is
probably
doing
something
like
ppoe,
so
this
is
pretty
terrible.
An
empty
uf
of
the
inner
packet.
There
are
useless
to
be
set
to
something
like
1200
to
even
have
a
chance
to
to
make
it
over
the
internet
and
then
there's
of
course,
issues
because
you're
using
sort
of
the
pre-netted
ip
address.
H
You
get
issues
on
the
server
where
the
server
has
like
multiple
connections
to
the
same
pre-net
ip
address
to
different
entities.
So
now
it
needs
to
do
more
complicated
state
to
separate
these
so
long
story.
Short
transport
mode
is
great
for
host
host
encryption
in
your
data
center
or
wherever
you,
where
you
control
everything
in
your
own
cloud,
where
you
can
do
this
as
soon
as
you
like
sort
of
go
through
an
administrative
boundary
where
there's
something
like
net
involved,
you're
better
off,
just
not
using
transport
mode.
H
So
tunnel
mode
is
conceptually
a
little
easier.
You
just
have
a
packet
that
you
want
to
encrypt,
so
you
encrypt
it
and
then
you
stuff
it
into
another
packet.
This
is
like
conceptually
it's
much
easier.
Of
course,
the
the
the
problem
is
that
there's
a
whole
new
ip
header,
because
you
create
a
whole
new
packet.
So
you
you
lose
a
little
bit
more
mtu.
H
Now
you
need
to
be
careful
with
policies,
because
if
the
inner
packets,
for
instance,
has
let's
say
888
as
a
source
address,
you
don't
really
want
to
reply
to
google
dns
with
your
ancestor.
So
you
have
to
be
sure
to
to
understand
what
it
is
that
you're
receiving
and
sending
and
making
sure
that
those
policies
match
what
you
actually
have
negotiated
or
what
is
allowed
to
be
be
transported
in
the
tunnel.
But
the
good
thing
is
that
you
can.
H
You
can
have
sort
of
arbitrary
ciders
that
can
go
through
the
tunnel,
there's
still
an
issue
that
that
esp
doesn't
really
transfer
over
the
internet.
So
what
usually
happens
is
that
it
gets
stuffed
into
udp
packet.
Then
the
outer
packet
doesn't
really
matter
because
you
just
look
at
the
crypto
from
the
inside
encrypted
packet
anyway,
so
it
doesn't
matter,
it
gets
rewritten
by
nat
routers
and
you
can
just
sort
of
decapsulate
it
later
in
the.
J
H
H
There
were
some
issues
early
on
in
the
days
with
nat
routers
trying
to
be
helpful.
They
sort
of
tried
to
be
too
helpful
sort
of
screwed
our
original
ike
port,
which
is
on
500,
so
the
protocol
switched
to
port
4500
to
avoid
these
helpful
assistants
and
so
that
that
is
usually
still
in
use
to
to
transport
ipsec
over
the
internet.
So
it's
encapsulated
over
port
4500..
H
H
So
there
were
some
non-standard
ways
of
doing
tcp,
encapsulation
of
ipsec.
Of
course
remember.
This
is
a
terrible
idea,
because
if
your
inside
connection
is
a
tcp
connection
and
your
outside
connection
is
a
tsp
connection
and
there's
some
kind
of
packet
loss
happening,
then
then
you
have
like
two
tcp
layers
fighting
each
other
over
how
how
to
re-transmit
and
what
to
do
so.
H
H
H
It
was
a
bit
tricky
because,
like
it
sort
of
breaks
what
we
are
supposed
to
do
with
itf,
it
is
sort
of
a
circumvention
technique,
but
but
we
were
also
seeing
that
not
having
this.
This
circumvention
technique
really
caused
the
plethora
of
non-standardized
vpn
protocols
to
be
out
there,
and
so
we
really
kind
of
had
to
do
this.
So
it's
a
interesting
political
maneuvering
next
slide.
H
H
But
if
you
look
at
the
the
the
policy
in
the
data
state
that
you
have
you've
got
the
security
policy
database
and
the
security
association
database.
The
security
association
database
is
like
the
endpoint
information
which
crypto
keys.
Are
you
using
which
host
do
you
need
to
send
the
packet
to
on
what
port
which?
What
protocol
and
you've
got
things
like
counters
sequence,
numbers
to
make
sure
that
your
crypto
is
going
right?
H
Then
the
security
policy
database
basically
has
to
see
if
it
the
list
of
rules
to
see
to
say
I
have
a
packet.
I
need
to
encrypt
it
which
policy
applies.
Who
does
it
go
to?
Is
it
the
right
ip
addresses
traffic
selectors
and
which,
which
then,
which
state
to
use
these
entries
are
unidirectional?
So
you've
got
one
for
inbound
one
for
outbound.
If
you
got
like
an
ipsec
connection,
you
you
actually
have
two
states
in
the
kernel.
One
for
for
in
and
on
for
out
and
then
same
for
policy.
H
So
next
slide
it's
probably
hard
to
see,
but
if
you
later
look
at
the
presentation
or
maybe
people
online
can
see
better.
This
is
an
example
from
from
the
linux
output
of
the
of
the
sad
entry.
This
is
one
entry
I
just
did
earlier
today
bringing
up
a
vpn
from
the
idf
network
to
my
server
in
amsterdam.
H
So
it
gives
you
sort
of
a
rough
idea
of
the
parameters
involved
and
there's
the
state
capped
next
slide
and
same
for
the
policy.
So
here
you
can
see
the
policy
database
entry
for
it.
You
see
a
third
one,
because
in
tunnel
mode
there's
this
sort
of
ip
in
ip
and
the
way
linux
has
done.
This
is
with
a
sort
of
what
they
call
a
forward
rule.
So
so
you've
got
inbound
and
outbound
and
forward
and
forward
is
where
you
can.
H
H
So
ike
negotiates
all
the
parameters
both
for
ike
itself
and
for
ipsec.
It
starts
off
with
a
ephemeral
diffie-hellman
exchange.
I
was
quite
surprised.
Coming
come
I've
done
ipsec
longer
than
than
tls.
I
was
quite
surprised
to
find
out
that
that
tls
wasn't
really
common
to
do
ephemeral,
diffie-hellman
exchange
and
have
perfect
or
secrecy
inside,
and
that
there
were
static
keys
on
tls
servers
that
were
used.
I
was
I
was
shocked
when
I
found
it
out.
First,
I
was
like
really
surprised
like
but
30
years
ago.
Ipsec
already
did
this
like
why.
H
Why
is
this
still
happening
very
surprised
anyway?
So
after
dielman
there's
there's
a
peer
authentication
and
there's
a
authorization
as
well?
Usually
that's
x509
could
be
based
on
made
up
strings
for
ids
com
in
combination
with
a
pre-shared
key
could
be
an
eep
method,
there's
various
ways
of
doing
that.
H
In
addition
to
the
initial
provisioning
that
happens
in
the
ike
protocol,
the
next
slide
so
originally
1998
rfc
2409,
I
think
the
author's
in
the
room.
Yes,
the
editor
author
is
in
a
room.
Thank
you
very
much,
and
I
really
want
to
say
that,
even
though
I've
been
making
moves
to
to
make
this
historic,
it
is
still
secure.
It
hasn't
really
been
broken.
There
have
been
some
weak
configurations
have
been
implementation
problems
where
the
complexity
has
led
to
to
code
mistakes
and
buffer
overflows
and
compromises.
H
It's
actually
still
pretty
good
like
there
are
some
some
things
where
you
know:
we've
we've
improved
on
on
the
years,
but
it's
actually
a
really
pretty
solid
document.
There's
been
no
no
cryptographic
attacks
that
broke
it
or
anything,
and
so
in
that
sense,
even
though
people
don't
like
to
hear
it,
I
feel
that
it's
been
been
more
stable
and
secure
than
tls,
which
has
seen
a
number
of
attacks
that,
like
are
so
fundamental,
that
the
villa
to
quickly
kill
the
old
tls
versions.
H
Next
slide,
so
there
are
many
extensions.
The
net
reversal
was
one
dead.
Peer
detection
was
another
one
that
was
mostly
needed,
also
because
of
interference
with
net
routers.
There
were
new
algorithms,
there
were
more
configuration
happening,
dns
windows,
net
bios,
other
things
were
added
mode.
Cfg
was
added
to
to
to
to
also
configure
and
do
multiple
things
additional
authentication.
H
All
of
these
things
added
also
multiple
round
trips
and
also
on
on
a
model
that
didn't
really
do
retransmits
very
right.
So
so
what
happens
was
that
both
sides
would
start
ending
up
re-transmitting.
It
would
very
much
complicate
the
state
machine
in
our
code.
Our
implementation,
I'm
working
on
the
ikv
2
state
machine
is
actually
much
nicer
than
that
v1
state
machine
and
again
it's
not
because
ike
v1
is
bad.
It's
just
that
it
had
some
different
design
goals.
H
One
interesting
one
is
that,
for
instance,
ike
v1
is
more
secure
against
quantum
computer
attacks
than
ikv2,
but
it
came
at
a
hefty
price,
namely
that
if
you
somehow
did
the
authentication
wrong,
you
would
just
get
encrypted
goblet
you
you
couldn't
read,
so
you
couldn't
get
proper
nice
error
messages.
So
so
it's
all
been
like
different
considerations,
putting
the
weight
somewhere
else.
It's
not
that
that
the
iphone's
actually
broken
next
slide.
H
One
issue
was
amplification
attacks
and
and
dos
attacks
because
of
the
the
retransmit
not
being
strictly
done
by
only
one
site,
and
they
would
go
to
both
ways
and
also
there's
a
dos
attack
where
you
can
trigger
more
packets
than
more
than
one
packet
in
a
reply.
Sometimes
that's
implementation,
for
instance.
At
some
point
I
was
for
I
noticed
that
for
one
year
one
I
paired
us
on
the
internet,
every
30
seconds
sent
me
an
ike
packet
and
it
was
because
I
once
sent
them
one
packet.
H
So
so
so,
although
that's
obviously
not
a
protocol
error,
but
an
implementation
error,
but
dos
attacks
is,
is
an
important
thing
to
fix.
There
are
many
modes
that
also
confuse
people
main
mode,
aggressive
mode,
revised
mode,
hybrid
mode,
revised
and
hybrid
were
not
really
used,
but
main
mode
in
aggressive
mode
was
main
mode,
is
a
more
round
trips
but
protects
more
identity.
Information
against
passive
attackers,
aggressive
mode
basically
said.
H
H
H
That,
at
some
point
also
runs
into
scaling
issues,
and
one
I
found
in
our
own
implementation
at
the
time
was
that
not
all
the
fields
in
an
ike
packet
are
actually
integrally
protected.
So
you've
got
things
like
vendor
ids
that
you
could
actually
that
they
weren't
part
of
the
the
signature
of
all
the
data,
and
so
you
could
actually
modify
them
and
and
do
maybe
weird
things
we
found
it
out,
because
the
software
I
was
working
on
at
the
time
tried
to
be
clever
to
putting
a
vendor
id
payload.
H
In
that
basically
said,
we
can
do
ike
v2.
Why
didn't?
Why?
Did
you
talk
if
you
want
to
us
and
we
thought
we
really
clever
to
prevent
a
downgrade
attack,
but
the
attacker
could
just
strip
it
out
because
it
wasn't
actually
part
of
the
of
the
signature,
so
there's
actually
no
way
to
do
to
prevent
a
downgrade
attack.
Unfortunately,
so
if
you're
migrating
it's
better
to
to
be
aware
of
this
and
try
to
do
it
quickly,
next
slide.
H
It's
like
video
improvements,
so
it's
actually
so
so.
One
thing
that
was
kind
of
neat
about
ike
v1
was
that
you
could
start
your
ike
protocol.
You
could
negotiate
ipsec
assays
and
then
you
could
tear
down
the
ike
state
like
you,
don't
need
it
anymore.
The
ipsec
state
is
there
and
by
the
time
your
your
ipsec
assays
are
about
to
expire,
then
you
could
re-trigger
and
do
a
new
ike
negotiation
and
bring
up
bring
up
that
state
that
worked
really
well
until
we
had
to
do
things
like
that.
H
Peer
detection,
because
at
that
point
you
always
needed
to
have
that
that
I
can
say
information
there,
because
you
needed
to
send
like
hey.
Are
you
still
there?
Yes,
I'm
still
here
and
for
that
you
needed
that
crypto
state.
That
was
part
of
the
I
can
say
so
so
in
practice
you
couldn't
really
work
anymore
without
that,
so
in
ikv2,
if
the
iksa
vanishes,
it
basically
takes
down
all
of
its
ipsec
assay
children
as
well,
so
that
it's
it's
one
bundle
that
you
have
to
keep
keep
keep
there
retransmetrofix
only
the
initiator
re-transmits.
H
So
the
responder
just
sends
an
answer
and
it's
all
the
responsibility
to
initiate.
It
avoids
a
lot
of
race
conditions.
There
are
some
anti-ddos
protection
added.
So
if
you're,
seeing
too
many
connections,
you
could
send
cookies
and
if
they
they
don't
come
back
with
the
right
cookie,
then
you
can
sort
of
ignore
them.
They
even
extended
that
to
to
to
puzzles
which
you,
which
is
sort
of
a
proof
of
work,
kind
of
thing
where
you
even
put
more
cpu
usage
on
a
client
before
they're
allowed
to
connect.
H
So
there
are
some
good
good
protection
mechanisms
there.
Another
important
one
is
that
the
the
round
trips
were
reduced
by
combining
the
establishment
of
the
iksa
with
the
first
ipsec
essay.
So
you
can
sort
of
do
a
few
things
in
a
somewhat
faster
way,
so
you
don't
have
to
have
as
many
round
trips
before
you
get
your
first
ipsec
essay
going.
H
Support
for
eep
was
added.
Eep.
Is
it's
interesting
because,
for
instance,
one
of
the
most
popular
modes
of
authentication,
with
with
with
I
can
ipsec,
is
eep
tls,
which
basically
means
you're
running
a
tls
connection
inside
your
eye
connection,
to
sort
of
to
you
to
eat
back-end
to
to
to
authenticate
that's
a
lot
of
round
trips
like
eight
or
more,
and
so
so,
for
instance,
if
you're
using
microsoft
windows,
you
can
use
eptls
for
your
vpn
tunnel
and
then
you
don't
need
administrative
access
on
your
on
your
machine.
H
But
if
you're
using
straight
certificates,
it's
considered
a
host
or
machine
property,
and
then
you
need
administrative
access
to
get
that.
So,
while
you
could
do
the
exact
same
thing
with
just
simple
certificates,
without
administrative
access,
you
suddenly
have
to
use
ipt
less
and
you're
like
eight
to
ten
round
trips.
Further
down
before
you
have
your
your
ipsec
tunnel
up,
so
not
as
nice,
but
but
anyway,
the
support
is
there.
I,
if
you
can
avoid
eep,
I
would.
I
would
avoid
e
personally
there's
the
combination
of
many
traffic
saxophones.
H
H
H
I
can
say
in
it
that
is
the
divi
helmet,
then
there's
one
exchange
that
does
the
auth
and
which
also
has
enough
information
for
for
samsung
ipsec
assay.
If
you
want
more
different
ipsec
assays,
you
can
use
to
create
child
essay
to
to
establish
more
and
there's
an
informational
exchange
for
doing
various
management
things
that
peer
detection,
mobile
mobility
updates
deletes
and
those
are
all
additions
in
ikev1,
they're,
all
sort
of
part
of
the
course
back
in
night.
V2
next
slide,
so
some
interesting
extensions,
mobike
mobility
and
multi-home.
H
Basically,
you
can
set
up
an
eye
connection
with
an
ipsec
connection.
Then
you
can
probe
from
a
second
entry.
So,
for
instance,
you've
got
a
phone.
Has
two
interfaces.
You
can
use
the
second
interface
to
send
an
informational
packet
to
the
other
end
saying
hey
by
the
way.
It
could
also
be
that
you're
going
to
send
packets
to
to
this
ip
address
here,
and
this
is
an
authenticated
way.
So
it's
not
just
looking
at
the
last
ip
does
that
you
receive
the
packet
from
and
replying
to
it.
H
It's
actually
an
authenticated
way
of
saying
I
have
different
ip
addresses
that
I
can
send
and
receive
these
packets
on.
So
if
my
wi-fi
link
goes
down,
let's
go
use.
My
my
lte
link
this
session
resumption,
obviously
also
to
sort
of
help.
Mostly
the
phone
case
use
with
your
phone
goes
to
sleep.
It
wakes
up.
You
can
do
session
resumption.
H
Various
algorithm
updates
poli,
cha-cha
algorithms
were
added
to
kind
of
modern
things.
Asgcm
was
already
added
to
ipsec,
but
not
to
igv1.
It
was
added
to
ikv2
mike
fragmentation
support.
There
was
sort
of
a
non-standard
way,
nike
v1
of
doing
that.
It's
been
standards
and
ikv2
in
a
much
nicer
way,
so
so
the
ikev1
version,
if
you
got
one
corrupted
corrupted,
fragment
you
sort
of
screwed
with
all
of
them,
you
have
to
get
all
of
them
back,
like
v2,
has
a
nicer
way
where
you
sort
of
authenticate
the
fragments
by
themselves.
H
So
if
you're
missing
one,
then
you
can
just
get
the
one
back.
So
so
it's
it's
a
harder.
It's
it's
harder
to
to
do
a
denial
of
service
by
just
making
sure
you
you
will
always
get
one
fragment,
bogus,
fragments
and
sent
to
before.
The
real
one
is
the
intermediate
exchange.
This
is
to
support
post
quantum
key
blobs
that
are
really
big,
so
they
don't
fit
in
one
udp
pack,
it
back
and
forth.
H
So
this
intermediate
exchange
is
sort
of
a
chain
of
events
that
can
happen
in
between
the
I
can
say,
init
and
ike
auth
process
to
to
sort
of
get
that
infrastructure
in
place
for
for
post
quantum
algorithms,
there's
post
quantum
pre-shared
keys.
That
thought
was
the
one
item
that
said
ikv
one
is
more
secure
with
the
nike
v2,
so
it's
been
added
as
an
extension
to
ikev2.
So
you
can
still
add
that.
H
So
it
might
have
seen
that
that
everything
I
said
was
pretty
complicated
and
you
want
to
run
away
screaming.
Let
me
just
remind
you:
this
is
my
client
configuration
for
ipsec
on
my
laptop.
You
can
just
see
you
know
left
pick
up
any
any
ip
address
left
certificate
is
my
actually
have
an
eye
certificate.
H
I'm
saying
give
me
everything.
You
got
for
left,
subnet
and
write
subnet.
So
for
the
local
and
remote
subnets
you
see,
narrowing
is
yes
so
I'll.
Let
the
server
narrow
me
down,
so
the
server
will
narrow
the
selectors
down
to
one
ip
address,
and
that
is
like
you
know
my
my
dhcp
obtained
ip
address
that
I
then
use
and
next
slide.
H
H
A
A
H
A
A
F
This
is
barry
lieber
well,
since
nobody
else
has
anything
substantive
to
say
I'll.
I
want
to
just
say
something
about
ben.
When
I
was
on
the
iesg
with
ben,
we
had
a
iesg
retreat
where
alyssa
came
up
with
this
game
that
we
played,
where
everybody
gave
secretariats
some
fun
facts
about
themselves,
and
we
did
a
little
mixer
where
you
tried
to
figure
out,
which
fact
went
with
which
person-
and
that
was
where
I
learned
that
ben
is
one
of
the
most
interesting
people
I
have
ever
met.
F
I
K
H
Yeah
there
is
a
beat
mode
and
there's
also
something
called
like
a
wrapped
esp
mode,
and
so
there
are
a
few
experiments
that
that
were
were
done,
that
weren't
very
successful
and
haven't
really
seen
much
deployment,
although
I
think
there's
some
interest
in
doing
something
with
beat
again,
but
but
terror
is
giving
a
more
complete
answer.
Yeah.
L
There
are
given
it
so
be.
It
was
bitmore
was
one
of
those
that
were
actually
done
part
of
in
hip
also
because
he
was
using
actually
esp
also-
and
there
was
this-
it's
actually
expired
in
the
aircraft.
I
don't
think
it
actually
went
very
well.
There
were
some
interesting,
I
think,
two
or
three
years
ago
somebody
was
wanting
to
resurrect
it
and
move
it
back
the
basic
idea:
there
is
it's
a
transport
mode,
payloads
internal
model,
semantics.
L
L
So
instead
of
taking
the
ip
addresses
outside
of
the
outer
ip
addresses
and
putting
putting
them,
you
take
throw
them
away,
they
out
their
ip
addresses,
put
them
in
put
in
ipads
from
the
policy
and
recreate
the
new.
You
know
ip
header
and
send
out,
so
it
actually
compresses
things
you
don't
have
to
send
extra
ip
header
and
so
on.
L
M
M
Looking
back
over
this
ietf
and
the
previous
one,
I
think
a
really
interesting
development
has
been
the
emergence
of
these
kind
of
oblivious
protocols
where
essentially,
the
general
model
has
been
to
take
an
existing
two-party
protocol
and
insert
an
intermediary
node
that
can
perform
a.
I
don't
know
if
this
is
a
verb,
but
an
obliviating
function
between
the
two
and
I
mean
so
oblivious
doe
is
one.
Ohio
is
another
one
that
we've
been
talking
about
this
week.
M
M
A
I
M
Not
straightforward
answers
no
worth
pursuing,
and
that
was
partly
what
struck
me
was.
There
are
really
good
arguments
on
both
sides
in
many
of
those
instances,
and
I
was
trying
to
figure
out
a
way
of
of
teasing
them
apart.
I
see
also
in
the
chat
rus
russ
has
maybe
suggested
floating
this
in
the
t
model
group,
which
is
another
good
idea.
Thank
you.
Russ.
I
N
I
just
wanted
to
mention
that
there
are
things
just
like
that
in
the
non-network
world,
for
example,
there
are
freedom
of
information
act,
queries
you
can
make
to
government
agencies,
at
least
in
the
united
states,
and
the
agencies
keep
a
record
of
everybody
who's
made
such
a
query,
and
I
guess
the
information
has
been
returned
to
them.
So
there
are
companies
whose
business
is
to
accept
such
requests
and
then
forward
them
to
the
government
agency.
So
all
the
government
agencies
record
say
is:
there
were
a
whole
bunch
of
these.
