►
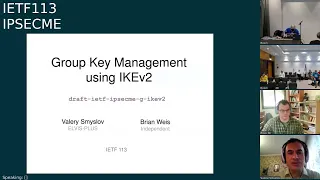
From YouTube: IETF113-IPSECME-20220325-1130
Description
IPSECME meeting session at IETF113
2022/03/25 1130
https://datatracker.ietf.org/meeting/113/proceedings/
A
A
Lady
is
no
longer
benjamin.
Kharook
is
now
a
roman
who
is
probably
also
oh
he's.
I
can
see
him
he's
not
online
but
anyway,
so
let's
go
forward
then.
So
this
is
the
note.
Well,
it's
pretty
have
probably
noted
well
already
for
at
least
this
point
of
view,
and
we
don't
need
to
have
blue
seats
because
they
are
taking
automatically
care
of.
If
you
use
the
meat
echo
either
the
online
you
know
version
or
the
full
version,
if
you're
using
full
version
make
sure
you
might
mute
out.
A
The
audio
peter
already
agreed
to
take
notes,
but
it
would
be
useful
to
have
somebody
else
also
helping
him
in
case
he
misses
something
and
I
don't
think
we
actually
need
the
choppers
right.
I
would
try
to
try
to.
You
know,
check
the
chamber
myself
also
because
I
can
detach
it
now.
So
it's
much
more
easier
to
do
that.
A
A
A
A
This
is
the
odds,
and
I
need
to
do
that
all
right,
so
working
group
report.
What
is
the
current
status?
So
we
have
now
icos
and
two
intermediate
which
I
think
was
actually
approved
a
couple
of
days
ago.
So
it
says
in
rfc
editor
queue,
iptfs
draft
3,
the
the
base
star
after
the
young
amp
document
are
now
in
the
ist
or
actually
sorry,
the
adq
waiting
for
edit
to
read
and
put
them
out.
A
D
Hi
is
my
voice
working
hopefully
yeah
great.
I
just
wanted
to
mention
that
we
we
are
starting
work
on
linux,
implementation
of
the
iptfs
and
so
just
wanted
to
add
some.
Maybe
a
little
bit
of
you
know
push.
I
know
it's
not
in
your
guys's
hands
anymore,
but
I
don't
I
don't
know.
If
is
it
ben
that
has
to
still
sign
off
on
it
or
has
it
shifted
to
roman
now.
A
D
A
So
so
this
is
more
detailed.
As
I
said,
the
group
key
management
for
using
like
version
2.,
we
did
get.
You
know
a
new
version
of
that
and
it
should
be.
You
know
it's
still
on
the
vacuum.
Pro
blast
call
because
I
didn't
want
to
close
it,
because
there
was
so
little
reviews
on
that,
but
I
will
close
it
after
this
meeting
and
if,
if
I
don't
get
any
other
comments
on
that,
then
I
will
still
put
it
out
and
post
it
there,
because
I
want
to
get
it
out.
It's
not
really.
E
A
Okay,
so
I
will
wait
anyway
for
at
least
one
more
revision
before
I
put
it
forward
all
right
good,
but
so
that's
the
status
and
then
I
did
guys
we
could
actually
go
to
the
presentation
and
you
are
the
first
one
to
talk
about
the
group
key
management
using
our
question
too
so
valerie.
If
you
just
go
ahead
and
they
want
to
actually
I
will
pass
you
the
slides.
I
think
you
can.
Oh.
E
E
E
E
So
these
issues
that
are
resolved
in
this
version,
so
terra
asked
for
a
terminology
section,
and
I
have
added
one
and
I
mostly
borrowed
all
the
terms
from
second
judo
documents
and
is
probably
choose
which,
which
definition
are
the
best
because
they
differ
slightly.
And
so
I
do
my
best
and
I
think
that.
E
E
G
G
G
E
E
G
G
G
E
G
G
E
E
G
E
G
G
E
E
G
E
G
E
A
This
is
they're
not
giving
a
commenting
in
notation
share,
but
you
know
I
think
we
should.
We
need
to
move
to
portfolio
4500,
because
we
want
to
have
a
different
format
with
having
the
you
know
the
european
capsules
of
our
esp
and
for
ike.
So
I
don't
think,
there's
an
option
not
to
move.
We
could
have
a
more
option
to
move
some
other
port
and
you
know,
but
we
need
to
have
some
way
to
identify
whether
it's
in
using
this
four
four
bytes
in
the
beginning
or
not.
E
Non-Usb
prefix
is
present,
yes,
bug
fought
for
for
esp,
but
if
it,
if
you
talk
about,
I
can
say,
there's
no
difference
in
format
from
whichever
port
you
use
so
and
for
esp.
We
are
talking
now
about
unicast,
like
I
say
from
group
member
to
group
controller,
the
registration
say
so
if
it
starts
from
fourth,
eight
four
eight
should
and
not
is
detected.
E
A
A
E
E
So
the
next
some
architectural
question
should
we
allow
a
registration,
a
group
member
from
the
group,
so
I
don't
have
strict
opinion
because
in
most
cases
this
group
control
kisera
doesn't
care
about
the
population
of
the
group,
because
most
operations
are
multicast
and
you
don't
know
how
many?
How.
G
E
Subscribed
to
it,
but
in
some
cases
this
may
be
useful,
in
particular,
if
some
key
management
method
like
linear
key
hierarchy,
lkh,
is
used
in
this
case.
A
group
controller
k7
need
to
keep
a
trace
of
all
the
members
of
the
group
just
to
know
which
member
it
can
exclude
from
the
group,
for
example,
and
in
this
case,
if
a
group
member
can
explicitly
say
well,
I'm
leaving
this
will
allow
to
keep
some
resources
or
group
control
like
a
survey.
But
anyway
it's
it's,
it's
unreliable.
G
G
E
E
E
E
G
G
E
G
G
E
To
to
be
known
that
it
is
in
the
group,
so
it
authenticates
it.
The
the
message
that
it
received
is
authenticated
by
the
fact
that
a
group
member
having
its
current
key
can
correctly
decrypt
and
verify
the
suv.
So
it's
an
exp,
implicit,
implicit,
shared
key
authentication
and
it
has
well
there
were
very
similar,
but
there
is
a
difference
with
explicit
character,
authentication.
E
Dedicated
symmetric
character
that
is
used
for
authentication
and
that
group
controller
provides
transfers
to
group
members
and
within
places
there
is
no
dedicated
charity.
Key
every
key
operation
which
change
keys
that
are
used
to
protect
multicast
tricky
messages,
will
change
this
authentication
key.
So
this
key
are
used
for
the
fact
that
the
message.
E
E
A
E
A
Yeah,
so
this
is
not
the
chair,
so
one
of
the
things
I
think
that
is
a
difference.
There
is
really
that.
Okay,
if
you
have
a
two
keys,
then
you
can
change
change
the
you
know,
king
keys,
you
know
you
can
change
the
authentication
case
faster
than
the
you
know,
the
keys
to
protect
the
messages,
but
I
don't
think
it's
actually
going
to
be
the
case
that
you
would
actually
want
to
do
the
other
way
around.
A
Usually
so,
and
you
can
change,
you
know
the
key
that
you
encrypt
the
pocket
faster
than
the
other
degrees
of
keys,
because
you,
you
can't
actually
see
the
authentication
keys.
Unless
I
mean,
even
if
you
miss
some
pockets
and
not
get
update,
if
you
don't
know
get
down
the
encryption
key,
you
can't
read
the
packet,
so
even
if
the
authentication
is
the
same,
it
doesn't
help
you
at
all.
So
I
was
thinking
about
they
are
in.
In
my
sense,
they
are
exactly
same
in
in
a
point
of
view.
A
E
G
E
G
E
A
So
they're,
okay,
so
I
think
we
can.
Actually,
there
is
also
we
could
also
put
them
into
the
actual.
When
we
are
sending
the
key
materials
to
the
you
know
or
updating
the
key
materials
or
the
keys,
we
could
also
you
know,
send
and
update
the
highest.
You
know
32
bits
of
the
es,
and
so
so
in
that
case,
even
if
somebody
joins
a
lathe
and
misses
some
frames,
they
can
still
do
the
very
short
search
of
the
higher
order.
Bits.
No.
A
G
Yeah,
actually,
I
had
the
same
question
as
terror,
so
thanks
for
answering
that
I
just
want
to
say
like
you
should
not,
that
must
not,
because
there
might
just
be
high-speed
applications
that
really
rely
on
this.
Otherwise
they
get
too
many
re-keys.
So
I
disagree
with
must
not.
I
might
even
disagree.
E
E
E
G
G
E
E
A
Yeah,
so
I
think,
if
it's
important
for
the
application
to
protect
against
that
there's
a
very
simple
solution,
then
they
can
do
the
reiki
of
the
iksa
immediately
when
they
create
it
and
that
will
protect
it
against
these
attacks.
Also
so
because
we
already
have
a
simple
standard,
standardized
way
of
solving
decision.
I
don't
think
we
actually
need
to
do
anything
specific
here,
except
to
say
that
if
you
care
about
the
group
policy
and
discuss
this
kind
of
attacks,
ludoriki
has
described
it.
D
E
G
J
J
Back
to
er
to
esn,
I
think
in
my
opinion,
it
should
be
a
must
not
because
of
the
complexity.
However,
if
you
do
allow
it,
you
need
to
actually
outline
how
it
works.
How
does
a
group
member
who,
who
does
learn
the
high
order
bits
if,
if
it
doesn't
you're
it's
a
different
implementers,
will
do
different
things
and
it
will
not
interoperate
we've
done
that
before
it's
a
it's
ugly.
E
E
E
J
A
Yes,
one
and
each
try
is
sorry,
four
gigabytes
of
data
or
sorry,
four
billion
packets
in
that
stream,
which
is
going
to
be
like
you
know,
I
would
say
four
terabytes
about
each
of
those.
So
if
you
need
to
do
you
know,
10
checks
for
one
bucket
for
every
you
know
40
terabytes
of
data.
That
should
be
true
that
I
don't
think
it's
actually
going
to
be
that
resource
control
resource
expensive.
In
that
sense,
I
mean.
J
A
A
E
G
E
That
was
that
you
used
before,
but
somehow
you
skip
a
lot
of
packets
and
you
want
to
resync.
You
know
what
to
start
with,
because
you
have
a
previous
version,
but
previous
value,
for
this
extended
high
audience
standard
esm
and
with
grow
per
se.
It
is
not
the
case,
and
probably
if
you
start
from
zero
and
run
to
two
in
32
power,.
B
A
Yeah
disclaimer,
I
I
agree
on
that
and
I
think
actually
we
could
we
could.
I
mean
it's
not
unreasonable
to
allow
you
know
the
group
members
who
already
has
the
key
and
know
the
highest
es
and
bits
to
actually
notify
the
you
know
the
key
manager,
every
4
billion
packets,
that
oh,
my
esn,
actually
increment
got
incremented
by
one
now,
so
we
could
have
some
kind
of
mechanism
where
they
could
actually
send
a
notify
to
the
you
know
what
what
is
the
name
of
the
key
manager
remember
but
sending
notified.
A
They
could
send
that
every
now
and
then
you
know
every
billion
packets
or
something
like
that,
and
then
you
know
when
the
when
the
new
device
joined
he
could
get
that
information
along
with
the
key
to
say
that
last
time.
Last
time
I
heard
the
es
and
high
order
bits
was
77.,
so
start
your
search
from
there,
so
so
that
actually
would
solve
the
problem
that
we
actually
don't
have
to
go
too
far
in
the
future.
A
Because
I
mean,
if
it
updates
every
bill
on
pockets,
they
shouldn't
be
missing
that
many
four
billions
of
pockets,
so
you're
going
three
or
four
in
forward
is
enough
and
then
you
can
stop
and
if
you
can't
find
it
that,
then
you
might
actually
go
back
to
the
you
know.
Your
your
group
controller
and
say
that
I,
this
key,
isn't
working,
do
something
or
request
the
key
again
and
get
the
new
esn
value.
Perhaps.
A
A
But
he
but
he
hasn't,
but
but
the
group
members
are
part
of
the
same,
they
can
send
the
notifies
over
the
I
channel
to
the
to
the
he
doesn't
need
to
be
in
the
key
environment.
Key
server
doesn't
have
to
be
the
member
of
the
group.
He
just
needs
to
be
getting
the
information
from
other
group
members.
A
So
whoever
is
sending
lots
of
data
to
the
group.
The
group
could
send
updates
every
you
know
every
now
and
then
you
don't
want
to
have
everybody
sending
the
updates,
but
you
want
to
have
some
somebody
sending
updates
every
now
and
then
it
could
be
so
that
actually
people
send
it
after
you
know
a
certain
amount
of
after
after
they
have
sent
certain
amount
of
pockets.
G
E
A
That
center,
they
could
then
actually
update
that.
So
we
perhaps
would
have
a
text
saying
that
you
shouldn't
be
using
esn
unless
you
have
a
setup
where
you
have
one
sender
at
that
sender
can
update
the
key
manager
key
server
with
the
latest
es
and
every
time
it
wraps
around,
and
then
we
have
a
you
know
some
kind
of
mechanics
of
sending
it
to
the
group
members
when
they
join.
A
E
E
E
G
E
E
E
E
E
E
A
J
H
E
J
E
A
K
K
Yeah
I
was
actually
going
to
make
a
similar
comment
to
the
previous
speaker.
I
also
don't
mind
taking
a
look
at
it
and
then
echo
the
comment
and
chat
about.
There
is
a
working
group
on
multicast,
but
you
know
I
have
a
little
experience
multicast,
I
don't
mind
looking
at
it,
but
I
do
think
if
you're
not
supporting
something,
that's
in
a
base
rfc,
you
really
should
do
abyss
on
that
rfc
saying
you're,
not
support.
You
know
that
mode
really
isn't
supported.
E
E
E
A
Yeah
I
was
actually
more
or
less
thinking
about
it's.
Not,
I
don't
think
we
actually
need
if,
if
there's
a
nuts
in
the
middle,
I
think
the
multicast
probably
don't
work
with
them
anyway,
but
but
the
udp
encapsulation
might
actually
be
useful
in
the
other
cases,
because
I
have
seen
also
networks
that
doesn't
allow
you,
the
port,
50
co
protocol
50
go
through,
but
mike
dalla,
you
know
even
the
multicast
with
udp
go
through.
A
They
don't
do
not,
but
they
don't
they
just
filter.
You
know
things
that
they
don't
understand.
The
right
basic
is
that,
oh,
it
seems
to
be
complicated.
I
don't
understand,
I
block
it,
so
it
might
be
actually
in
some
cases
might
be
useful.
But
of
course
one
of
the
problem
there
is
that,
because
if
we
are
sending
a
data
in
multicast
that
we
have
to
send
it
to
everybody
in
the
same
format,
meaning
that
we
are
sending
either
import
protocol
50
or
in
in
a
udp
port,
five
4500,
it's
not
really
a
per
device.
A
Yes
and
and
then
I
think
we
need
to
actually
have
a
sp
use,
transfer
type
or
something
like
that
and
as
the
multicast
as
currently
defined
in
I
question
one
doesn't
support
that.
I
don't
think
we
actually
need
to
add
that
feature
now,
because
we
are
not
qualified
to
be
experts
or
this
is
better
to
actually
understand
the
implications
of
it.
So
I
think
it's
better
to
just
say
that:
okay,
let's
not
add
it
now,
but
if
we
but
know
that
if
if
somebody
comes
back
and
say
oh,
we
would
actually
really
like
that.
G
J
E
E
Concurrently
in
the
draft
to
signal
transport
mode
well,
if
the
problem
so
group
security
association
may
have
some
ipsec
say
created
in
internal
mode
and
sum
in
transfer
part
it's
currently
and
how
to
indicate
which
say
from
this
set
of
assays
is
created
in
which
mode.
So
currently
the
draft
change
the
semantics
of
use
transmit
mode
when
it
is
used
in
the
context
of
gip2.
E
G
G
E
It
has,
it
doesn't
use,
and
now
we
are
defining
jquery
2
will
define
it,
so
the
protocol
in
this
pair
fields
are
used
to
indicate
which
say,
use
transport
mode
and
another
different
sensors.
Is
that
multiple
instances,
multiple
instances
of
this
notification
can
be
sent?
So
each
instance
indicates
that
this
particular
essay
identified
with
spi
is
created
with
transport
mode.
So
I
think
that
it
is.
It
is
not
an
update.
H
E
H
G
E
For
example,
it
can
be
called
encapsulation
mode
in
gsa
preload
so
that
we
can
indicate
which
mode
says
created
per
in
a
per
se
basis
or
prohibit
policy
when
someone
say
created
in
transport
mode
and
some
created
internal
mode.
So
in
this
case
all
the
data
security
say
in
this
group:
security
essay
will
be
either
created
in
transport,
mode
or
roll
will
be
created
internal
mode,
and
so
we
can
reduce
use
transport
modification
disease,
so
any
opinion.
A
As
we
don't
really
know
whether
these
people
are
going
to
be
using
transport
motor
tunnel
mode
and
so
on,
and
we
have
a
mechanism
saying
that
use
two
different
csa:
payloads,
meaning
okay,
extra
payload
extra
round
trip,
because
I
think
you
need
to
do
one
router
with
first
gsa
with
that
you
start
transport
and
second
one
with
that
without
use
transport.
More,
so
I
think
it's
actually
simple
to
say
that,
okay,
you
are
not
allowed
to
use
a
mixer
transport
and
tunnel
mode
in
same
gsa.
A
A
Yeah,
so
to
do
it
in
different
groups
and-
and
you
know,
and
if
people
later
come
back
and
say
that
oh
we
use
this
feature
very
frequently,
and
we
want
to
use
this
and
we
don't
want
to
pay
the
extra
penalty
of
doing
that.
So
then
we're
going
to
come
back
and
make
a
modification
I
want
to
pick.
I
I
think
we
should
get
this
out
as
simple
as
possible
out
now
and
not
you
know,
try
to
think
what
people
might
be
thinking
or
requiring
in
the
future
we
should
think
about.
A
G
E
I
will
issue
a
new
version
and
I
think
at
least
one
more
route
and
review
is
definitely
needed
again.
The
document
is
big
and
it's
easy
to
to
leave
something
very
important
just
because
it's
dropped
from
my
mind
and
I'll
be
very
grateful.
If
people
look
at
the
document
and
send
comments
to
the
list
on
any
of
the
issues
that
I
just
we
discussed
now,
I
try
to
have
a
discussion
now
or.
A
A
A
L
Okay,
thank
you,
hello,
everyone
and
I'm
weipan
from
huawei,
and
I'm
glad
to
present
this.
The
updates
of
this
draft
and
this
draft
has
been
gone
through,
maybe
three
years
and
I'm
very
happy
to
see.
Many
people
are
interested
in
this
draft
and
provided
many
useful
and
comments
and
suggestions,
and
this
is
the
recap
of
the
solution.
L
E
G
G
A
A
It's
like
for
this
essay,
but
here
we
are
talking
about
some
other
essay.
That's
why
I
think
the
reiki,
the
you
know
ricky
sa,
actually
is
using
into
the
payload,
because
it
it's
it's
not
it's
talking
about
some
other
sp
and
like
this
one,
and
I
think
this
one
should
be
also
using
the
same.
It's
just
a
payload
and
it's
okay
to
have
it.
Have
it
in
the
payload,
because
we
can.
This
is
a
new
notifier.
We
can
actually
add
it.
There.
A
So-
and
I
think
this
is
not
expressed
down
in
our
charter,
but
this
is
the
minor
extensions
on
an
update,
so
I
think
we
can
actually
fit
into
that
says,
so
I
think
we
can
actually
get.
You
know
our
id
to
allow
us
to
take
care
of
this.
Of
course,
the
80
now
changed.
He
might
have
different
opinions,
so
I
probably
need
to
ask,
but
is
there
any
objections
of
here
in
there
who
would
actually
say
that
we
shouldn't
be
starting
the
working
group
last
working
group?
Adoption
call
for
this
document.
A
A
G
Sorry
I
couldn't
find
my
window
and
tap
and
button
for
the
end
up
on
my
laptop.
I
just
want
to
briefly
point
out
the
the
the
multi
sa
document.
We
still
have
a
linux
implementation
that
is
not
merged
into
the
main
line
because
they
don't
want
to
merge
it
before
we
are
further
in
the
process
and
I
actually
dedicated
to
it.
So
I
would
like
it
if
people
would
review
and
comment
on
our
proposal.
