►
From YouTube: IETF92-ACME-20150325-1520
Description
ACME meeting session at IETF92
2015/03/25 1520
A
The
IPR
policy
and
in
contributions
that
you
should
make
to
the
ITF,
please
familiarize
yourself
with
our
policy
I
think,
probably
by
this
point
in
a
week.
Most
of
you
have
already
seen
this
possibly
over
a
hundred
times
during
your
career
here
at
the
ITF
for
everybody
who
thinks
they've
seen
the
note
well
more
than
a
hundred
times.
Please
raise
your
hand.
A
A
A
A
Okay,
so
well,
Joe,
who
is
already
volunteered
to
be
our
driver
scribe,
is
taking
care
of
that.
I
would
also
like
to
thank
Cullen
and
Alex
for
having
agreed
to
take
minutes
for
us
today.
Thank
you
very
much.
That
means
our
administrivia
is
already
moving
fast,
because
folks
have
already
volunteered
they've
collected
your
stars
and
I
their
stars
and
I
encourage
you
later
in
the
week
to
collect
your
own.
A
This
is
our
agenda.
For
today
we
are
going
to
have
some
motive:
a
motive
ating
requirements
from
eric
rescorla,
some
additional
possible
requirements,
industry
from
philip
alan
baker,
a
review
of
draft
barnes
acme
and
from
richard
barnes
and
then
discussion.
The
area
director,
who
is
just
arrived
in
front
of
me,
may
have
some
questions
for
the
room:
I,
don't
have
your
slides
loaded
yet,
but
we'll
try
and
get
those
done.
You
sent
slides.
It
looked
like,
and
so
there
may
be
some
questions
from
the
area
director.
A
Seeing
none
I
will
just
follow
up
with
one
reminder:
this
is
not
a
working
group
forming
buff.
You
will
notice
that
nowhere
on
this
agenda
is
there
a
charter
review
or
discussion.
However,
we
want
you
to
think
about
the
work
and
how
it
fits
into
the
ITF
and
during
the
discussion,
think
about
how
the
ITF
could
contribute
to
this
effort
if
it
wanted
to
or
what
other
appropriate
actions
might
be.
Reverend
Laura.
D
Had
a
spinner,
alright,
so
I
was
asked
to
talk
a
little
bit
about
what
we're
trying
to
achieve
with
acne,
so
I
were
from
Mozilla
were
we're
involved
in
this
effort?
Somehow
so
so
what
problem
we're
trying
to
solve
here
on
the
basic
problem
trying
to
solve
is
like
not
enough
TLS
on
the
internet
or
security
in
general,
but
especially
not
FTL
ossicles
outside
the
main
thing
you
do
for
the
web.
D
Debate
on
this
number
is
one
hundred
percent
on
three
110%
really,
but
hundred
it
was
a
setup
for
so
did
a
lot
of
reasons
why
this
numbers
in
his
eyes
would
like,
but
there's
a
general
feeling,
I
think
that
one
of
the
big
reasons
is
hard
to
get
certificates
next
slide.
So
I
show
the
slide
a
lot.
One
of
my
esteemed
colleagues,
Cullen
Jennings,
was
asked
to
get
a
certificate,
and
this
is
the
transcript
of
the
instant
messages
that
I'm
receiving
from
him
about
how
annoying
this
is.
D
D
So
not
not
good.
So
everyone
knows
this.
You
know
there's
been
some
work
in
this
area
on
you
look
at
them.
You
know
over
the
past
couple
years
of
people
sort
of
trying
to
automate
this
process.
So
it's
more
fun.
So
you
look
at
universal
ssl
from
from
cloudflare
or
on.
I
guess
there's
a
this
I'm
spacing
on
the
name,
but
there's
this
dumb
node
package
that
does
this
so
there's
been
sort
of.
Sir.
That's
all
right!
Thank
you
recognition.
D
This
is
a
problem
right
and
so
next
line
so
Missoula
along
with
eff
and
san
Cisco
and
Akamai
and
I
didn't
trust
and
tremor.
One
other
person
now
I
think
has
been
trying
to
figure.
I'd
say
about
this,
and
on
so
the
background
for
this,
for
this
Bluff
I
think,
is
this
new
initiative
called
let's
encrypt,
that
we
announced
on
the
last
IETF
that
aspires
to
do
a
new
free,
transparent,
automatic,
CA.
I'm,
not
gonna,
talk
about
this
very
much.
D
This
is
motivation,
but
the
objectives
we
have
is
it
should
be
free,
it
should
be
automatic,
it
should
be
secure,
transparent
and
blah
blah
blah.
All
these
good
things,
but
easy
is
the
biz
that
it's
like
what
you
should
be
getting
out
of
this
right.
So
if
it's
going
to
be
easy,
it's
going
to
have
to
have
automation,
that's
clear
next
slide.
So
what
does
this
mean
for
a
protocol
machinery
standpoint?
Is
we
automation
of
all
the
major
operations
so
that
it
reduces
the
operational
costs
for
us?
D
So
we
can
do
this
for
free
and
it
is
the
operational
costs
for
the
the
server
operator,
so
they're
incentivized
to
do
it's
not
a
big
pain
in
the
ass.
That
means
the
registration
has
to
be
has
to
be
automatic.
The
domain
control
validation
that
is
verifying
that
you
are
entailed
to
operate
the
domain
that
you
claim
to
be
entitled
to
assert
for
that's
automatic
and
on
something
people,
often
don't
realize,
is
that
the
renewal
is
tificate
has
to
be
automatic
on.
D
So
it's
really
common
to
see
people
who
have
what
a
certificate
of
year
ago
and
they
forget
they
have
to
renew
on
and
then
the
strictly
spira
sanitized
inaccessible,
even
though
it's
accessible
10
minutes
ago,
that's
really
sucky.
So
what
we
want
is
on
a
single
time,
interaction
with
the
ca
from
the
users
perspective.
Where
I
say
I
want
to
certificate
and
then
their
server
continues
to
function
in
perpetuity
with
no
intervention
by
them
whatsoever.
D
That's
what
I
mean
by
seamless
on
the
we
have
some
demos,
our
site,
there's
nothing
particular
special
too
complicated,
especially
the
demos
that
you
know
you
type
some
crap
at
the
command
line,
apache
and
say
like
I,
want
the
sword
and
it
goes
and
it
just
retrieves
it
and
a
few
minutes.
I
your
system
is
running
so
and
then
from
then
on
it.
She
continues
to
work,
that's
what
you
want
and
finally,
we
wanted
to
be
flexible
on.
D
So,
if
cas
changed,
their
policies
and
practices
we'd
like
to
have
a
face
to
fighting
chance,
because
it
said
that
your
server
will
continue
to
operate
on
even
under
those
changes.
So
say
the
ca
decides,
for
instance,
that
they
on
that
require
sha-3
certificates
on
it
really
be
nice.
If
you
didn't
have
to
do
anything
to
make
that
work
next
slide.
So
here's
some
examples
of
the
kinds
of
challenges
that
we
think
that
a
protocol
does.
This
has
to
be
able
to
arm.
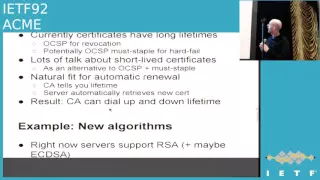
D
You
know
encounter
to
v
mq,
so
here's
an
example
on
certificate
lifetimes
right
certificates
now
tend
to
have
relatively
long
lifetimes
year,
five
years
ten
years
whatever
and
we
rely
on
ocsp
for
revocation
and
as
low
CSP
is
like
good
you're,
going
to
have
a
bad
day
so
on
right
now
on
I,
don't
believe
any
major
browser
or
hard
fails.
Oh
no
CSP
ocsp
failures
on
so
on
it
certificates
revoked
on.
Basically,
all
the
attacker
has
to
do
is
gag
the
ocsp
server
and
the
browser
will
continue.
That's
not
so
awesome.
D
Basically,
you
can
get
ocsp
response,
and
then
you
can
stop
at
the
TLS
handshake
and
there's
a
way
to
indicate
in
the
certificate
that
that
better
be
there
or
you
should
fail
feels
like
I
doing
that
with
hard
fail
on,
by
which
I
mean
that,
if
that
weren't
there
you
actually
fail,
you
would
even
try
to
use
P
query.
There's
also
a
lot
of
talk
about
shortlist
certificates,
on
what
students
are
stiff
achatz,
which
have
a
lifetime
on
the
same
order.
A
D
We
have
adapt
our
policies
on
with
people
who
are
you
know
without
requiring
the
user
to
go
through
a
horrible
horrible
birds,
as
opposed
to
you,
Daniel
lead
and
it's
a
hassle.
So
it's
one
kind
of
challenge.
You'd
like
to
have
this
be
a
result.
Next
slide.
Another
example
being
you
over
those,
so
right
now
you
know
servers
typically
support
RSA,
sometimes
in
support
ecdsa
certificates.
D
So
what
if
we
now
know,
CFR
G,
is
defining
to
curse
and
let's
go
do
signatures
perhaps
over
those
curves
or
Moody's
EDD
essay,
or
you
know,
last
signatures,
your
post
quantum
or
whatever
right
on
so
the
you
can't
make
this
quite
a
seamless,
because,
obviously
you
can't
preemptively
add
these
things
to
your
client
before
you
know
they
exist,
but
on.
If
you
have
an
automatic
negotiation.
One
thing
that
can
happen
is
that
basically,
the
ca
can
add
the
capability
to
issue
for
these
new
kinds
of
keys.
D
And
then,
when
you
update
your
server
software,
it
says
oh
I
noticed
the
ca
can
now
assume
eeeddd
SAS
I'm
going
to
get
one
of
those
as
well
on.
So
it's
not
quite
as
nice,
but
you
can
still
do
automatic,
upgrade
something
that's
the
future
you
like
to
have
next
slide.
The
final
feature
that
again,
this
is
all
exemplary
I'm,
not
like
the
sauce
posting
exhaustive
list,
but
trying
to
give
you
a
sense
of
the
kind
of
things
challenges
we
think
we
have
to
face
so
delegate
issuance.
D
So
on,
say
you
have
a
big
server
farm
and
you
have
I.
Don't
know
lots
of
lots
of
servers
for
a
given
domain
or
lots
of
domains
for
a
given
server
boat
engine,
or
you
have
some
Nixon
mask
thing
where
you
have
like
a
big
server
farm
that
serves
hundreds
of
the
mains
on
thousands
of
servers.
We'd,
like
some
comment,
we'd
like
to
know
some,
you
know
a
binary
selection
for
each
one
goes
which
unchanged
in
a
daily
basis.
D
So
it's
really
a
pain
if
you
have
to
keep
revalidate
and
it
should
be
really
nice
if
you
could
establish
control
hood
of
each
domain
once
and
then,
whenever
you
want
a
new
server
that
stands
up
and
supports
a
new
subset
of
the
other
names.
You
simply
say:
okay,
give
me
a
certificate
that
matches
that
exactly
and
if
you
look
at
the
way
actvities
done.
This
is
a
pia.
It
works,
obviously
there's
an
authentication
key
which
is
tied
to
some
class
of
domains,
and
then
you
can
request
issuance
for
any
subset
of
that.
D
D
Some
of
them
are
validation,
mechanisms,
it'd
sure
be
nice
to
have
a
system
that
was
there
was
flexible
about
that,
in
particular
in
this
contest,
which
really
relevant
as
Dane
and
so
right
now
you
know
if
you
offer
Dane
on-
and
you
know,
there's
only
a
very
small
fraction
of
line
if
any,
which
can
accept
that
right
on
but
I
mean
the
future.
That
might
not
be
the
case,
but
there's
a
chicken
and
egg
problem,
because
it's
hard
use
Dane
without
getting
a
backup
certificate
for
ordinary
TLS.
D
So
one
thing
that
is
very
nice
about
a
sort
of
automatic
protocol
is,
you
can
simply
say
you
can
simply
transition
from
date.
From
date
from
you
know,
Dame
+
509
to
Dane
only
in
a
gradual
way,
with
the
automatic
system,
picking
up
the
slack
of
basically
automatically
recien
your
certificates
based
on
your
Dean
records,
so
that
on
so
basically,
this
gives
you
a
temporary
bridge.
While
we
should
get
why
didn't
deployment.
D
D
Let
us
move
forward
in
a
way
that
requires
minimal
user
intervention
on
as
we
sort
of
try
to
figure
out
what
kind
of
policy
please
early
best
fit
the
internet
on
in
terms
of
what
on
our
interest
is
as
far
as
ITF
or
rather
read,
lots
encrypt
interest
which
I'm
sort
of
like
representing
today,
though
I
don't
work
for
them,
is
we
have
to
develop
this
on?
We
understand
other
people
working
this
area.
D
F
C
Iran
Sheva,
a
more
requirement
request
for
requirement
in
a
question
world
gardens
turns
out
that
in
many
cases
it's
it's
more
cost
effective
to
use
a
commercial
CA
than
to
set
up
your
own
internal
CA
for
servers
that
are
not
on
the
internet.
Yes,
I
would
have
liked
for
this
or
a
flock
of
this
or
whatever,
to
be
usable
for
internally
within
enterprises
right.
D
H
D
H
D
So
I
think
there's
a
let's
encrypt
answer
and
a
acne
and
serve
either
a
little
different
on
I.
Think
from
let's
your
perspective,
we're
not
primarily
focused
on
either
those
cases
initially,
although
you
know
at
some
point
in
the
future,
we
might
be
interested
in
doing
non-web.
It's
just
a
web
is
the
first
target
on
from
an
acne
perspective.
D
D
A
F
Jj
hi
Daniel
can't
Gilmore,
so
I
just
wanted
to
point
out
that
it
actually
isn't
completely
orthogonal
to
certificate
transparency,
particularly
in
the
section
that
you
talked
about
ramping
down
the
time
for
the
certificates.
One
of
the
things
that
ocsp
lets
you
do
is
you
have
fewer
certs
in
the
log
and
then
you
have
regular
ocsp
update.
D
D
D
True
on
on
so
actually
been
a
nitride
about
this
a
little
bit
on
and
I,
think
I
think
I
suggested
to
bend
that
perhaps
it'd
be
nice
if
CT
with
log
key
identity
pairs
route
in
logging
certificates.
For
precisely
that.
For
precisely
this
reason,
Oh
fantastic
follows
a
better
wife,
so
but
I'm
just
just
generally
you're,
quite
right,
yeah,
obviously
CT
will
not
scale
well.
If
you
have
to
like
issues
because
every
22
minutes
yeah.
I
So
I'm
talk
so
when
I
was
talking
from
experience
here,
it's
it's
confined
to
komodo,
but
I
only
speak
of
a
promoter,
but
I
think
is
probably
the
same
for
most
other
large
cas.
So
where
we
are
now
is
we
actually
have
tools
that
make
automation
of
certificate
issue
possible
and
raise
reasonably
straightforward,
so
we
have
standards-based
sitting
at
the
enrollment.
We've
got
easy
to
use
and
they're,
not
the
same
thing.
They're
two
completely
separate
paths.
We
would
like
these
two
things
to
be
one
now.
I
Why
do
we
want
to
go
from
our
proprietary
standards
to
the
to
a
standard,
sorry,
proprietary
schemes
to
a
standards-based
one
next
slide?
Well,
the
answer
is
that
plugins
just
don't
deliver
at
the
moment
to
use
our
automated
schemes.
You
have
to
put
a
plug-in
in
your
server
and
the
administrative
costs
of
the
plug-in
is
vastly
greater
than
the
time
saved
in
cut
and
pasting
a
csr
and
yes,
I,
know
that
it
I
know
that
it's
a
45
minutes
for
current.
I
Well,
you
know
what
putting
a
plug-in
into
your
web
server
is
a
lot
more
than
45
minutes
and
I'm.
The
problem
with
plugins.
Is
you
can't
test
them
because
yeah
one
plug-in
works
too,
is
a
combinatorial
problem
at
three?
Well,
so
you
just
can't
test
the
interactions.
I
want
to
go
to
a
standards-based
mechanism,
because
that's
the
only
way
that
I
can
automate
this
scheme
in
a
way
that
makes
things
actually
easier
for
my
customer
rather
than
harder
next
slide.
I
The
user
should
not
need
to
do
anything
differently
when
setting
up
a
secure
website
to
setting
up
a
regular
website
unless
some
additional
information
is
required
from
the
user,
and
we
definitely
want,
though
short-lived
certs
a
killer
for
us
would
be
no
any
new
SN
1
here
from
my
prom
to
view
the
Canon
of
SN
1
schema
has
closed.
We
have
burned
all
our
asn.1
compiler
tools,
we
don't
want
any
new
stuff.
I
We
want
Jason
and
the
reason
for
that
I'll
come
to
that
little
bit
later,
but
it
makes
it
possible
to
solve
all
the
additional
requirements
that
I'm
going
to
come
to
without
making
the
base
spec
to
too
complicated.
We
also
want
whatever
I
mean
Acme
in
some
ways
is
going
to
be
the
first
Jason
based
security
spec.
We
would
like
whatever
tropes,
that
Acme
introduces
in
producing
a
protocol
to
be
tropes
that
we
can
use
on
other
security
protocols
without
having
the
how
we're
going
to
use
JSON
discussion
coming
up
every
time.
I
We
also
need
to
interrupt
with
existing
back-end
systems
and
we
have
hardware
security
modules
and
lockdown
systems
that
expect
to
see
a
CSR
for
proof
of
possession.
So
that's
one
place
where
we
want
to
see
a
maintaining
compatibility
with
existing
sn1,
but
we
don't
want
to
see
any
new
sn1
structures
appear
next
slide.
So
looking
at
it
from
our
point
of
view
specific
requirements,
we
obviously
want
a
choice
of
CA
there
and
we
also
want
a
way
of
charging
the
customer,
and
we
also
want
to
support
all
our
p
kicks
based
products
I.
I
For
me,
it's
not
going
to
be
a
very
exciting
move
to
move
just
my
TLS
customers
with
DV
certificates
to
a
new
enrollment
protocol.
It's
only
really
going
to
be
interesting
to
me
is
if
I
can
move
all
my
cust
of
this
to
all
my
customers
for
all
their
needs,
so
that
if
they
choose
to
have
six
TV
sets
and
then
upgrade
to
EV,
then
that's
possible
for
them.
We
want
to
do
TLS,
and
we
also
want
to
do
s
mine.
I
We
actually
have
a
large
number
three
quarter
of
a
million
s
mindsets
paid,
which
shocked
the
heck
out
of
me
when
I
found
that
out,
but
it
turns
out
to
be
what
we
have
also.
So
one
thing
that
this
means
that
you
can't
assume
the
issue
is
the
issue
of
the
certificate
is
going
to
happen
immediately
if
you're
doing
extended,
validation
or
organizational
validation,
you're
going
to
start
the
the
attempt
to
register,
and
then
other
information
is
going
to
have
to
come
in
out
of
bound,
and
so
it's
not
going
to
be
a
run.
I
This
tool
once
and
then
you're
done,
there's
going
to
have
to
be
some
delay
and
some
ability
to
pick
up
certificates
after
the
fact.
But
actually
that's
not
all
that
difficult
different
from
the
certificate
renewal
problem,
which
also
has
to
be
solved,
and
obviously
we
need
to
have
the
ability
to
add
in
those
additional
criteria
for
the
validation
for
EV,
etc.
Oh
and
private-label.
Certs
are
also
quite
big
that
we
have
quite
a
lot
of
certs
that
don't
appear
in
TLS.
Our
public
CA
is
at
all
so
next
side.
I
That
of
prophecy
a
can
provide.
We
also
not
to
be
able
o.
So
it
was
one
thing
that
might
have
a
long
term
is
obviously
one
cases.
This
is
going
to
be
the
device
talking
Acme
protocol
to
the
LRA.
It's
also
possible
that
they
may
be
talking
another
Jason
based
protocol.
That
is
higher
level,
and
it
might
be
that
the
way
you
want
to
configure
that
in
the
cloud
is
when
a
new
web
server
comes
up
or
a
new
mail
server
comes
up.
It
might
be
saying:
hey
I
want
to
do.
I
I
We
want
to
be
able
to
have
provide
customers
with
management
tools,
so
they
can
see
all
the
certificates
that
they
have
subscribed
for
that
are
currently
active
and
we
can
see
oh
yeah
there's
a
device
there,
666
example.com
we've
got
a
certificate
for
it.
What's
it
doing,
you
know,
and
in
some
cases
you
might
want
private
key
information
to
be
traveling
from
the
LRA
to
the
device.
I'll
explain
the
reason
for
that
on
the
list
they're
a
bit
complicated
here.
I
Okay,
some
technical
points:
we've
got
that
there's
a
record
the
certificate
authority
authorization
record,
which
is
an
existing
RFC.
There
are
hooks
in
that
it
was
designed
to
be
expandable
where
you're
trying
to
discover.
Where
is
my
CA?
What
CA
should
I
register
under
CA
records
might
be
one
way
that
we
can
do
it
and
paul
hoffman
when
we're
discussing
the
CAA
record,
he
in
he
actually
proposed
using
dns
name
for
identifying
the
ca
for
this
very
purpose,
and
I
think
that
was
a
very
good
extension
of
CIA
record.
I
We
don't
necessarily
need
to
go
to
market
with
an
ACME
specification
day,
one
that
supports
every
feature
provided
that
we
don't
have
bits
in
the
code
that
nailed
down
and
exclude
particular
applications.
One
of
the
nice
things
about
Jason
is,
you
can
add
in
slots,
as
required,
provided
you've
not
made
some
brain-dead
assumption
in
the
system.
I
So,
for
example,
don't
assume
that
when
you're
making
these
requests
of
the
ca
or
the
server
or
whatever,
don't
assume
that
the
key
that
the
server
is
going
to
use
is
going
to
be
the
same
key
that
so
the
key
that
the
service
is
going
to
use
for
TLS
is
going
to
be
the
same
ski
that
they're
going
to
be
used
for
subscribing
for
certificates
and
authenticating.
That
request,
you
probably
want
those
to
be
different.
I
Actually
so
next
slide
and
one
thing
that
I
have
to
rate
this,
isn't
our
IPR,
but
when
you're
designing
the
validation
protocol
will
need
to
be
sensitive
to
the
fact
that
there
are
quite
a
few
cas
out
there
that
have
read,
have
patents
pending
or
issued
that
cover
methods
are
validating.
Dv,
certs
and
I
know
that
you
know
our
scheme
took
us
a
long
time
to
work
out
because
we
were
dancing
around
I.
I
All
this
I
PR
I,
don't
have
that
all
that
I
PR
in
my
head,
sorry
I
would
have
to
do
quite
a
bit
of
research
to
work
out
who
owns
what
and
so
on.
But
when
we're
designing
this
protocol
we
should
not
assume
that
there's
going
to
be
just
one
way
of
validating
the
cert,
because
if
we,
if
we
do
that,
then
we'll
end
up
being
sued
up
the
ass
and
that's
it
sir
questions
gosh
I
answered
all
your
questions.
A
J
So
my
name
is
richard
barnes
I
worked
for
mozilla
and
I've,
been
helping
out
with
drafting
the
spec
for
the
letter
code
projects
which
we're
trying
to
generalize
out
that
projects,
be
this
general
acne
protocol
next
slide,
please.
So
the
idea
is,
you
know
you,
you
install
some
piece
of
software
is
going
to
do
all
the
acne
magic
and
auto
configure
server
with
the
cert
and
all
that.
But
what
really
happens
under
the
sheets
when
we
do
the
protocol
here,
so
I
thought
it
was
helpful
and
oak
what
yeah
yeah.
J
So
if
you're,
not
your
laptop's
out
what
you
all,
do
you
love
the
URL
at
the
top?
You
can
see
this
form
on
your
laptop,
but
the
idea
here
is
I
thought
it
was
helpful
to
look
at
what
an
existing
free
cert
issuance
process
looks
like.
So
this
is
a
web
form
from
whoa
sign
of
Chinese
CA.
That
is,
offers
a
free,
ssl
cert
service
and
they
collect
a
bunch
of
different
information
here.
J
So
you
have
to
tell
them
the
domain
name
and
whatever
else
you
want
to
go
in
the
certificates
they
have
like
duration
fields
and
things
like
that.
They
have
a
couple
of
different
ways.
You
can
verify
that
you
control
the
domain.
You
can
provision
a
file
on
your
web
server.
I,
think
they'll,
do
the
email,
style,
verification
as
well.
You
have
to
provide
them
a
CSR
to
show
that
you
own
the
private
key
that
you
want
corresponding
the
cert
you
want.
J
You
provide
them
a
contact,
an
email
address
and
a
password
so
that
you
can
prove
that
you
are
your.
You
know
you
are
the
guy
who
requested
this
cert
and
verified
it,
possession
of
the
domain.
When
you
go
to
pick
up
the
cert
from
them,
they
also
have
a
CAPTCHA
and
a
subscriber
agreement
which
it
turns
out,
is
required
by
the
ca
browser
for
them.
If
you
want
to
be
a
CA,
so
this
is
sort
of
an
example
of
the
sorts
of
things
that
we
probably
want
to
capture
in
the
acting
protocol
right.
J
These
are
the
sorts
of
information
that
the
the
web
server
or
the
thing
requesting
a
cert
is
going
to
need
to
provide
to
the
CA
in
order
for
the
CA
to
be
able
to
issue
a
certificate
so
next
slide.
This
is
a
diagram
out
of
the
out
of
the
act.
Nice
back
of
sort
of
how
the
acne
protocol
reflects
these
pieces
of
information.
J
I'm
sorry,
the
green
is
so
bright
might
be
a
little
hard
to
read,
but
the
idea
is,
we
have
three
basic
types
of
object
with
one
kind
of
sub
object:
we
talk
in
terms
of
registrations,
authorizations
and
certificates,
so
registrations
cover
the
Who
am
I
the
identity,
the
contact
information,
the
authentic
the
credentials
that
you're
going
to
use
to
to
access
the
acne
service.
So
that's
where
we
have
contact
information
and
authentication
and
the
subscriber
agreement
concept.
J
So
registration
is
you
when
you
first
show
up
at
an
acting
server,
you
register
you
go
to
the
new
registration
endpoint,
you
get
a
registration
and
then
you
head
over
to
the
new
authorization
endpoint.
At
that
point,
you
say:
I
would
like
to
prove
that
I
own
example.com,
you
put
in
the
domain
name,
you
want,
and
you
do
this
authorization
process.
Acne
then
has
a
challenging
response,
sort
of
protocol
for
verifying
domain
control
and
it's
extensible
to
support
bunch
of
different
a
few
different
types
of
ways
to
do
that:
domain,
validation,
I,
use
domains
here.
J
As
an
aside,
we
use
domains
in
the
slides
here,
but
the
way
the
protocol
structured,
there's
it's
an
ed
there's
a
typed
up
for
the
identifier
structure
has
a
type
and
a
value,
so
you
can
currently
define
type
as
domain
name,
but
you
in
principle
the
protocol
could
support.
Other
types
of
identifier
is
like
phone
numbers
or
mac
addresses
or
whatever
the
CA
can
validate.
You'd
need
different
challenge
types
to
verify:
possession
of
those
identifiers,
but
in
principle
the
protocol
is
extensible
in
that
way.
J
So
you
go
through
this
challenge
and
response
thing
to
prove
you
own
the
domain
name,
and
then
you
can
hop
over
this
new
cert
endpoint
and
drop
your
CSR
in
and
get
a
cert.
If,
once
you
proved
you're
authorized
the
reason
for
the
separations.
We've
got
here
is
twofold:
the
separation
between
authorizations
and
certificates.
J
So
the
idea
is
you
do
the
authorization
to
prove
that
you
control
each
name,
and
then
you
can
issue
certificates
with
any
combination
of
the
names
that
you
control.
The
separation
between
registration
and
authorization
was
to
try
and
separate
things
that
are
generally
regarded
as
public
from
things
that
are
generally
regarded
as
private
in
particular,
and
let's
encrypt
we're
going
to
try
and
publish
all
of
the
authorizations
and
certificates
and
sort
of
as
transparent
certificate,
transparency
mode,
and
but
we
didn't
want
to
have
to
publish
all
the
contact
information.
J
We
were
getting
three
people
because
for
obvious
sort
of
spam
and
privacy
reasons
that
also
lets
us,
it
opens
up
the
door
for
acne
to
support
sort
of
user
management
models.
Maybe
groups
and
things
like
that
adds
an
additional
level
flexibility.
So
that's
the
overall
architecture
of
how
the
protocol
hangs
together.
I've
got
some
examples
of
concrete
protocol
messages
on
the
subsequent
slides.
The
whole
protocol
runs
in
JSON
messages
over
HTTP.
J
All
the
messages
from
the
client
to
the
server
from
the
subscriber
to
the
CA
are
signed,
with
a
key
pair
that
key
pair
acts
as
the
account
identifier
for
the
the
entity
replying
for
certificates
in
the
document,
without
an
account
key
pair.
So
with
registration.
We
begin
by
associating
contact
information
and
agreement
with
some
terms
with
that.
J
Key
pair,
so
that
is
initiates
the
user
into
the
into
the
ca's
management
system
and
the
CA
just
says
yes,
sure
I've
got
this
next
slide
when
the
once
you've
registered
and
have
sort
of
said
this
is
my
public
key
and
Who
I
am
you
can
then
sign
requests
to
authenticate
to
be
authorized
for
a
domain
with
that
key
pair?
So
this?
J
The
message
on
the
left
here
says,
is
the
subscriber
saying:
I
would
like
to
request
authorization,
for
example
org
for
that
domain
name
and
the
signature
by
the
account
key
pair
vine
associates
this
authorization
request
with
that
entity.
That's
requesting
it
now!
Here's
where
it
gets
kind
of
interesting,
so
the
subscriber
says
I
would
like
to
prove
control.
Of
example.
Organ
the
server
responds
with
an
authorization
object,
so
it
has
a
status.
We
have
sort
of
pending
valid
invalids
sort
of
status,
as
you
would
expect.
It
echoes
back
the
identifier
and
the
key.
J
That's
that
were
requested,
and
then
it
actually
issues
a
set
of
challenges.
It
says
the
service
says:
okay,
if
you
want
to
prove
that
you
own
example,
org.
Here's
how
I
require
you
to
do
it
next
slide?
Please
so,
like
I
said,
acne
has
an
extensible
set
of
challenge
type.
So
each
challenge
message
has
a
type
thing
that
says
here
is
the
mechanism
you
should
use
to
to
prove
your
control
of
this
domain.
I
think
there's
two
or
three
in
the
document
right
now.
J
Obviously,
especially
as
if
additional
identifier
types
are
added,
you
will
need
different
types
of
challenge,
but
then
the
other
fields
and
the
challenge
say:
here's
some
properties
of
the
URI
is
how
you
respond
to
the
challenge
and
then
the
token
is
the
the
stuff
you're
supposed
to
provision.
So
simple
HTTPS
asks
you
to
go
provision
of
files
of
a
given
path
on
a
web
server
and
then
the
response
says:
here's
how
you
go
check
that
I
fulfilled
that
challenge.
Yeah
Ellis
connects.
J
Believe
in
the
document
right
now
we
have
simple
HTTPS,
a
one
mechanism:
it's
based
on
server,
name,
indication
in
TLS
and
a
DNS
based
mechanism.
Okay.
Obviously,
if
people
have
other
ideas
for
for
ways
that
a
third
party
could
validate
that,
another
party
owns
a
domain
name
yeah
we're
open,
and
it
may
be
also
that
there's
sort
of
pre
validation
cases
can
be
handled
with
different
challenge.
Challenge
types
as
well
so
yeah
the
flow
is,
you
know
you
get
this
challenge
in
the
authorization
method,
and
then
you
post
this
response
back
to
the
URI.
J
That's
in
the
challenge,
so
you
respond
to
a
challenge
specific.
You
are
on
and
I
sort
of
leave
out
a
step
there,
but
once
you
once
you've
completed
this
and
the
the
servers
has
gone
off
and
verified
to
the
domain
control,
the
client
can
pull
that
authorization
URL.
It
got
and
look
for
that
authorization
to
turn
green
to
turn
from
pending,
and
then
it
knows
it's
bent
is
that
the
ca
considers
it
authorized.
For
example,
calm
next
slide,
please!
So
now
the
client
knows
that
authorized
for
example.com.
It
can
go
ask
for
a
certificate.
J
This
is
pretty
minimal.
Eve
generates
a
PK.
Cs10
CSR
sends
a
link
to
the
authorization
that
the
client
believes
authorizes
a
certificate
signs
it
to
prove.
You
know
that
it's
bound
to
his
authorized
account
key
and
sends
it
up
to
the
server
and
the
server
sends
back
the
certificate
if
he
agrees
and
sends
back
an
error
code,
if
not
yeah
suppose.
C
D
B
D
B
Google,
so
we've
just
had
a
whole
bunch
of
sites
discovering
you
shouldn't
allow
users
to
register
user
names
like
administrator.
If
you
provide
them
email
access,
I'm
also
going
to
have
a
bunch
of
sites
realizing
they
shouldn't
allow
users
to
register
the
name
dot
well-known.
Can
we
require,
like
a
weird
content
type
on
this
thing
or
something
that
is
going
to
be
less
error-prone,
yeah.
B
J
There
is
not
an
email,
validation
mechanism
in
the
document
right
now.
Maybe
we
should
add
one.
Maybe
now
it's
worth
noting,
the
cab
form
has
been
working
on
tightening
down
their
list
of
validation
mechanisms,
so
this
will
probably
require
some
coordination
with
them
in
terms
of
making
sure
that
whatever
gets
the
pod.
A
B
J
I
think
the
thing:
that's
it's
a
really
important
point
that
this
is
validates
at
a
point
in
time
and
it
may
be
useful
to
have
some
sort
of
reauthorization
or
scoping
of
authorization
so
force
revalidation
yeah
next
slide.
Yes,
this
is
just
summary
of
the
overall
process.
You
know
you
sign
up
for
your
new
registration.
If
the
ca
requires
some
sort
of
subscriber
agreement,
it
sends
back
the
URL.
You
indicate
your
agreement,
then
you
request
authorization
for
your
domain.
J
The
ca
sends
back
challenges,
you
respond
to
the
challenges
and
then
you
poll
to
see
to
see
if
your
authorization
is
valid
and
then
once
your
valid
you
issue
a
certificate,
so
try
to
sort
of
make
it
as
minimal
as
possible
within
the
set
of
use
cases
we
wanted
to
require.
We
wanted
to
support
so
any
further
clarifying
questions
on
the
protocol
as
we
have
it
today,.
F
J
Right
there
there's
a
couple
mechanisms
that
I
think
we
kicked
around.
We
were
drawn.
We
were
drawing
this
up
and
I,
don't
think
either
of
them
is
reflected
in
the
current
draft.
It
seems
like
it
would
be
desirable
to
have
the
ca
be
able
to
express
basically
the
policies
for
what
it
will
issue
so
covering
key
lengths,
key
algorithms,
key
and
extensions
it
might
allow
or
not
allow.
J
We
had
thought
about,
there's
sort
of
two
approaches
to
getting
to
that.
You
could
do
it
at
the
certificate
request
stage
as
by
returning
arrow
types
or
someone
requests,
something
that
you
don't
like,
or
you
could
have
some
sort
of
policy
publication
mechanism
as
as
an
adjunct
to
the
existing
queries.
You've
got
here,
I,
don't
think,
there's
anything
in
the
document
right
now
to
do
that,
but
it
would
probably
be
a
good
thing
to
add.
A
A
B
F
Hi
Nick,
Sullivan
cloudflare,
so
I
have
a
question
about
this.
That
is
a
little
bit
about
the
scope
of
this
document
itself
on
acne
is:
why
was
the
decision
may
made
to
make
the
account
key
the
authentication
mechanism
for
getting
certificates?
The
main
question
I
have
about
this
is:
is
that
if
you
do
have
a
wide
deployment
and
a
lot
of
sort
of
cloud
instances
that
you're
spinning
up
you
have
to
send
this
very
sensitive
account
key
to
each
one
of
these
machines
in
order
to
get
a
machine
from
it?.
D
Yeah,
absolutely
so
the
assumption
was
quite
the
contrary.
So
maybe
we've
messed
this
up.
But
the
idea
was
exactly
to
address
that
use
case
and
the
idea
was
that
when
the
Machine
spin
up,
they
would
send
their
public
keys
to
whatever
box
intermediated
the
the
CSRs
through
the
box.
That
we've
had
the
account
key
and
that
would
ask
for
and
that
would
ask
for
approval.
So
if
there's
some
I
mean
the
idea
was
precisely
to
precisely
to
avoid
the
problem
you're
talking
about.
So
maybe
it's
bungled,
but
that's
the
idea.
I
Phil
hung
back
yeah
I
think.
Maybe
what
we
should
do
is
to
split
the
protocol
into
two
and
have
an
ACME
direct
and
an
acne
lra
and
describe
the
two
separately,
because
connecting
up
directly
to
the
CA
is
one
set
of
use.
Cases
connecting
up
through
some
intermediary
I
think
is
a
different
set
of
issues,
and
we
probably
want
to
separate
that
out
and
separate
protocol.
F
F
This
is
Joe
channeling
yon
from
the
gabba
room.
Are
there
people
in
this
session
who
would
really
like
wild
cards?
What
are
their
use
cases?
Oh
wait.
Sorry
yeah
wondering
how
people
generally
feel
about
support
for
issuing
wild
card
DV,
certs
and
Acme.
Are
there?
People
in
the
session
would
really
like
wild
cards.
What
are
the
use
cases
we've
heard
from
a
few
people
for
whom
that
wouldn't
work,
for
example,
randomly
generated
domain
names
on
the
fly.
K
Go
ahead
and
max
fauna-
and
I
was
thinking
about
this
work
and
actually
then
it
seems
to
me
beside
the
fact
that
most
most
of
the
format
that
is
chosen
kind
of
duplicates
the
work
that
we've
been
doing
in
a
PK
x
working
group
a
long
time
ago
with
CMC
so
managing
the
certificate
life
cycles
with
CMS.
But
besides
the
format
which
is
not
very
important.
One
thing
that
I
wanted
to
point
out
is
that
and
one
of
the
biggest
problem
that
we
are
always
faced
in
the
ca
world
was
discovering
services.
K
And
this
is
something
that
we
started
to
tackle
a
little
bit
in
the
PK
x
but
I
working
group
and
died.
And
it's
something
that
he
deep
I
think
pointed
out
when
using
the
dns
records.
But
it's
something
that
I
think
we
should
focus
a
lot
more
because
it's
the
biggest
problem
when
I
want
to
have
look
for
which
CA
I
want
to
get
my
services
from
and
how
to
discover
the
different
services
provided
and
maybe
looking
at
the
fact
that
there
might
be
Federation
of
types
of
CAS.
K
A
F
You
Elliot
layer,
three
quick
comments
and
a
question
comment
number
one:
it
answered
your
question:
I
think
this
is
a
very
important
problem.
I'm
at
number
two
I
think
it's
a
very
nicely
constrained
solution
and
comment.
Number
three
is
keep
on
going
and
question
is:
have
a
various
CA
vendors
shunt
risk.
A
G
Have
something
George,
moccasin,
I
panic,
so
I
have
a
small
number
of
comments
in
like
sense
to
make
without
attempting
to
objectify
any
one
individual.
What
I
believe
I
heard
on
entry
was:
please
preserve
my
bread
business
model
and
that
concerns
me,
because
there
are
qualities
in
the
currency,
a
business
model
that
I
actually
think
we
do
not
wish
to
preserve.
So
I
just
want
to
make
that
observation.
The
second
observation
I
wanted
to
make
is
intermediaries
are
somewhat
concerning
to
me.
G
I
understand
the
CA
are
a
split,
but
in
effect
we
partly
here
because
some
intermediaries
acted
badly
and
issued
certs.
We
don't
think
should
have
existed
so
there
are
qualities
and
intermediaries
that
make
me
extremely
uncomfortable.
Okay,
a
third
comment
slightly
to
one
side:
I
am
very
very
concerned
about
the
traction
behind
day.
I
want
deign
to
succeed
and
there's
a
limited
amount
of
clue
the
universe,
and
if
we
divide
the
clue
into
this
room
in
the
dining
room
before
Dane
is
complete,
we
won't
get
Dane.
G
I
need
Dane
modules
in
browsers,
I
need
Dane
modules
in
systems.
Dane
is
very
important,
and
one
of
the
reasons
Dane
is
important
is
because
it
gets
rid
of
the
see
a
business
model,
which
is
one
of
the
main
goals,
so
I'm
slightly
concerned
about
aspects
of
this
project.
Having
said
which
I
think
it's
a
really
cute
model,
hey.
A
J
J
So
it's
probably
something
when
working
group
is
going
to
want
to
take
a
look
at
and
consider
whether
the
different,
what
validation
methods
might
be
appropriate
to
that,
and
what
the
security
considerations
should
be
around
the
issuance
of
wildcards,
ultimately,
is
probably
going
to
come
down
to
operational
decisions
by
cas
using
this
interface.
But
it's
worth
to
think
at
least
having
some
discussion
in
the
working
group
and
the
last
point
on
Dane.
J
I
actually
think
this
is
a
supportive
technology
for
Dane,
in
the
sense
that
it
has
the
potential
to
interact,
really
well
and
be
a
use
case
for
DNS
SEC
in
the
sense
of
using
DNS
signatures
to
prove
possession
of
a
domain
and
signatures
over
objects.
You
might
put
in
the
dns
to
prove
your
control
of
a
domain
to
provide
a
higher
degree
of
authentication
into
the
as
a
basis
for
issuance
of
certificates.
As
I
pointed
out,
I
think
this
can
also
provide
a
sort
of
a
bridge
today
by
lowering
the
costs
of
certificates.
J
E
Mark
nottingham
Akamai,
but
not
wearing
the
Akamai,
let's
encrypt
hat,
this
is
good.
I
think
this
is
important.
I
agree
with
the
previous
speakers
from
an
HTTP
perspective.
I
suspect
I
have
issue
with
some
of
the
ways
it
uses
HTTP
and
I'm
willing
to
help
improve
that,
because
I
would
cry
with
joy
if
we
could
get
one
RFC
that
uses
HTTP
well
out
of
the
IETF.
That
would
be
fantastic
ever
yeah,
but
I
would
love
to
what.
B
B
D
Erika,
scroll,
amazon,
yeah,
I,
guess
I,
guess
I'm
a
little
confused
by
a
book
by
the
heat,
but
I
hate
from
from
my
esteemed
on
former
colleague,
I
mean
this
certainly
isn't
about
impacting
the
see
a
business
model
is
about
the
fact
that
the
browser
browser
and
other
clients
accept
certificates
and
nothing
else,
and
this
is
about
allowing
people
to
talk
to
those
browsers
securely
as
much
as
possible
on
as
far
as
on
as
far
as
Dane
goes
on
honestly.
I
think
that
the
analysis
that
was
offered
there's
actually
put
you
backwards.
D
So
on
that
the
problem
with
dane
now
as
people
can
tell
you
is
that
there
is
it.
We
have
a
standard,
collective
action
problem,
which
is
to
say
that,
because
there
are,
no
clients
are
set
except
dane,
there's
no
value
in
an
offering
dane,
are
practically
no
clients
and
because
there's
no
and
because,
because
practically
no
one
offers
damn
there's
no
incentive
for
the
clients
to
accepting,
and
so
what
one
of
the
Acme
and
in
general
automatic
issuance
offers
the
possibility
to
break
that
log
jam
by
giving
you
a
valuable
reason
to
detain.
D
Even
nobody
accepts
it
to
use
for
to
use
as
a
stronger
form
of
issuance
and
also
to
allow
you
to
deploy
it
in
certificate,
while
only
some
small
fraction
of
people
accept
Dane
in
the
rest,
except
certificates.
So,
as
Richard
said,
this
is
a
bridge
universal
day
deployment
and,
in
fact,
back
to
the
only
scenario
I've
ever
understood
where
you
could
get
browser
based
in
deployment
on
from
0
to
100,
almond
or
any
plausible
scenario.
So
quite
the
contrary.
A
Okay,
so
I
know
the
area
director
was
going
to
send
me
some
questions
to
ask
and
I
never
got
them.
So
I'm
going
to
ask
some
different
questions
almost
certainly
and
then
turn
the
microphone
to
him.
For
the
the
last
thing,
how
many
people
in
the
room
are
either
have
currently
read
the
draft
or
intend
to
after
having
seen
today's
presentations
and
that's
good,
forgive
the
bad
language
so
shocked.
A
A
A
Michael
Richardson
and
Jeff
Houston
were
the
only
hands.
I
saw,
oh
no,
there's
one
more
in
the
corner,
so
there
are
three
very
trusting
people
and
the
rest
of
you
think.
There's
some
work
to
do
here.
Otherwise,
I
assume
you're,
not
reading
the
drafts
and
doing
the
joining
the
mailing
list.
Okay,
so
I
think
what
I'm
hearing
I'm
going
to
risk
the
next
22
hums.
This
is
not
a
working
group
forming
buff,
so
this
is
just
the
sense
of
the
room.
A
A
Okay,
that
was
funny,
but
I
need
to
ask
the
hum
again
because
the
laughter
over
wrote
it
if
you
think,
there's
no
work
here
for
the
ITF.
Please
come
now:
okay,
one
one
person
near
a
microphone,
something
okay,
so
the
last
words
will
go
to
our
esteemed
area
director
to
see
what
questions
he
would
have
had
me.
Ask
that
weren't
those.
L
Those
were
good,
I
guess:
I
I
only
have
one
further
question.
I
guess
so.
I
think
the
plan
here
is
that
there
seems
to
be
people
willing
to
do
this.
It
seems
I
think
there
should
be
agreement,
there's
nothing
to
be
done
and
so
I
guess.
A
question
is
whether
we
should
just
go
ahead
and
do
it
from
former.
You
know
get
start
getting
people
writing
a
charter,
maybe
not
in
the
next
week's
put
in
the
next
month
or
two
or
whether
we
should
have
another
buff
before
we
do
that.
So
how
many?
L
B
Adam
Langley,
google,
so
so
the
ITF
does
have
a
tendency
to
take
things
and
take
a
really
long
time
and
then
come
up
with
something
that's
slightly
different
from
what
used
in
practice.
So
the
reason
why
I
hummed
against
having
the
IETF
to
do
something
here
was
that
I
hope,
let's
encrypts
like
spit
out
of
working
CA
shortly
and
then,
if
the
IETF
were
to
standardize
something
that
wasn't
what
they
were
using
and
wasn't
what
the
world
was
using,
which
is
quite
possible.
That
would
be
quite
a
sad
outcome.
There.
D
Visually
plastic
creeper,
my
understanding,
listen
Chris
posture
is-
is
that
we
intend
to
spit
something
out
prior
to
ITF
standardization
and
would
hope
to
harmonize
the
IETF
as
long
as
it
was
not
to
radically
different
insanely
cell,
which
I
understand
is
not
the
best
outcome
in
the
world
on,
but
we'd
also
don't
think,
and
we
should
be
more
than
pleased
to
people
just
adopt
it.
Whatever
the
hell,
we
get.
Ok,
so
we're
bracket
euro.
