►
From YouTube: IETF93-INTAREA-20150720-1850
Description
INTAREA meeting session at IETF93
2015/07/20 1850
A
B
C
A
B
G
F
Thanks,
okay,
so
if
you're
not
going
to
spend
much
time
on
the
document
status
like
it's
all
in
the
data
tracker,
so
you
can
look
at
it,
but
we
just
want
to
give
like
a
shot
summary.
So
we
don't
have
too
many
working
of
documents
here.
So
the
GRE
empty
document,
yeah
I,
see
low
okay,
perfect.
So
we
don't
have
too
many
documents
here.
F
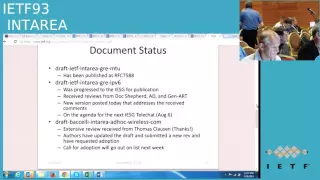
So
we
have
like
two
documents
in
flight
like
one
of
them
got
published
in
as
out
of
CSUN
588
like
very
recently,
and
thanks
a
lot
wrong
for
like
a
quick
turnaround
on
everything
and
the
other
document
is
like
I
was
sent
to
the
ESG.
So
we
got
a
ad
review
and
we
got
a
genet
review
and
Carlos
like
who's
the
document
Shepherd.
He
also
did
a
review
so
again,
thanks
Ron
for
like
turning
on
quickly
on
that,
and
so
it's
on
the
agenda
for
the
next
stella
chat.
F
So
I
don't
know
if
it's
gonna
stick
there
or
get
reschedule,
but
it's
on
the
agenda
in
two
weeks,
so
hopefully
it's
going
to
get
through
soon
and
this
document
the
death
virtually
interior,
ad
hoc
wireless.
Even
though
it's
like
a
01
version,
it's
been
around
for
a
bit
and
it's
just
got
a
new
name,
so
it's
been
around
since
the
mani
autocom
those
kind
of
times-
and
it's
been
revised
quite
significantly.
F
H
F
Thank
you
so
for
people
who
don't
have
the
context,
we
had
a
working
group
document
four
years
ago
for
the
four
tunnels
and
it
expired,
and
it's
been
expired
since
and
there's
been
like
significant
updates
happening.
So
it's
like
being
slowly
happening
every
meeting.
We
get
like
some
few
things
so,
but
we
haven't
had
a
new
version
so
just
promise
to
post
a
new
revision
very
soon.
Yeah
thanks,
okay,
go
ahead!
Chuck
Shelly!
Did
you
have
a
question
this.
I
Name
is
Charles
Perkins,
so
we
did
go
through
a
college
class
and
made
quite
a
few
comments
and
we
did
revise
the
draft
in
response
to
those
I.
Think
some
of
the
comments
were
really
oriented
towards
a
significant
enlargement
of
the
scope
of
the
draft
around
security
and
description
of
some
wireless
security
mechanisms
for
four
layer.
Two
in
that
I
pretty
sure
that
would
that's
that
belongs
in
a
different
draft,
so
that
I
think
I
just
want
to
mention
sorry
the
scoping
issue
for
that
right.
F
F
H
J
J
Okay,
so
my
name
is
a
christian
vittima
from
microsoft
and
I'm
presenting
here
a
walk
that
I
did
with
the
dev
tara
about
basically
metadata
and
the
use
of
names
as
metadata
yeah
I've
been
walking.
We
have
been
working
on
privacy
issue
for
some
time
and
we
have
been
looking
at
various
aspects
of
privacy
and
this
is
11
to
do
so.
Please.
J
And
then,
if
you
are
doing
something
like
say,
bonjour
or
windows,
a
lemon
are,
you
would
have
names
that
says
hey.
My
name
is
Christian.
Is
that
someone
by
the
same
name
here
I
mean
all
these
are
little?
Tokens
of
names
have
come
on?
We
are
specifically
for
that
going
on
Mekon,
economization,
dhcp,
anonymity
and
privacy
address
for
ipv6
a
deprived
for
the
dns,
but
we
definitely
that
we
have
a
generic
problem
with
host
names
and
I'd
like
to
elaborate
on
that.
J
J
J
Then
you
have
what
you
find
in
organizations,
organizations
may
manage
say
holy
thousand
or
million
computer,
so
they
need
to
have
some
order
them
in
order
to
do
ordering
they
have
some
names
that
are
locally
registered.
In
our
case,
it's
your
login
name
on
the
company
and
some
suffix.
Well,
that's
very
informative
about
who
you
are.
J
Even
if
you
are
computers
that
you
have
in
your
home.
Typically,
you
assign
some
men
that
you
like
I,
close
the
door,
I,
don't
know
Jupiter
or
whatever
and
those
you
might
say:
hey,
it
doesn't
identify
me
no,
it
doesn't
but
think
of
that
they
are
taken
in
dictionary.
That
does
maybe
ten
thousand
possibilities,
so
you
have
given
their
something
like
10,
12
bits
of
information
that
identify
you
and
even
if
we,
if
we
don't
do
that
mean
we
are
going
to
lick
that
information.
J
J
So
why
is
that
important?
Why
is
this
little
token
of
metadata
important?
Why,
knowing
that
the
name
of
your
computer
is
rosebud
or
or
Jupiter
or
whatever
is
important?
It's
because
tracking
opens
by
tracking
happens
by
looking
at
all
the
bread
crumbs
that
you
live
over
the
internet
and
putting
them
in
a
big
bucket
and
getting
them
to
identify
something
and
very
quickly.
What
you
find
is
that
if
you
have
identified
MAC
addresses
and
maybe
IP
address
of
all
time
and
maybe
email
address
that
you
read.
J
This
was
India
SSD,
so
dear
SSDs
about,
but
our
publishing
a
service
name
I'm
publishing
that
maybe
have
a
printer
on
my
on
my
computer,
that
you
can
use
and
that's
fine
I
mean
I,
given
them
to
the
service.
People
can
look
at
that
name.
It's
Anne
Tolley
under
my
control,
I
wonder
what's
happening.
I
may
make
mistakes
by
giving
a
name
that
is
to
identifying,
but
is
under
my
control
and.
J
Someone
will
look
for
that
and
I
will
respond
to
the
query
by
Osiris
advertisement
and
that's
fine,
that's
what
I
wanted
to
do.
It's
not
a
surprise
for
the
user.
What
is
the
surprise
is
that
if
you
look
at
the
details
of
the
response,
we
stick
in
that
her
host
name
and
the
reason
we
do.
That
is
because,
in
order
to
connect
back,
what
will
be
done
is
that
you
will
get
the
air
the
service
record.
J
You
will
get
the
host
name
of
the
host
offering
the
service,
and
then
you
will
do
an
advanced
resolution
at
them,
but
because
of
that,
you
have
hidden
in
the
transaction.
You
have
published
an
M
and
the
user
didn't
know
it
was
published,
and
now
you
have
given
the
name
of
your
computers
on
the
network
and
that's
not
a
good
pattern.
Ok,
that's
a
pattern.
That's
not
necessary!
Even
if
you
had
given
directly
the
address,
for
example,
we
would
not
have
that
flick.
J
So
that's
an
example
of
the
kind
of
scrubbing
that
will
need
to
do
if
we
want
to
get
rid
of
those
leaks
and
DNS
SD
by
no
mean
the
worst
case
scenario,
domina
I'm,
sure
that
are
plenty
of
other
scenarios
like
that.
You
know
the
practice
in
mdns
or
a
lemon
our
offer
just
visiting
and
then
by
doing
a
broadcast
of
your
own
them.
J
J
The
way
the
way
we
have
done
that
so
far
is
that
several
of
us
has
been
going.
I've
been
going
to
values,
walking
groups
and
I've
been
checking,
hey
can
I
fix.
This
can
I
fix
that,
and
we've
done
that
for
the
HTTP.
We
are
doing
that
for
the
IP
addresses
we
are.
You
will
do
be
doing
that
for
some
protocols,
but
I
mean
I
can
be
busy,
death
can
be
busy.
Also,
volunteers
can
be
busy,
but
we
cannot.
J
Possibly
we
don't
know
everything
that's
going
on
and
that's
why
I
would
like
to
challenge
you
to
take
on
that
kind
of
thing
and
says:
hey
is
my
application
leaking
metadata
director?
Is
it
leaking,
in
particular
the
hostname,
and
if
it
is
well,
can
we
fix
that?
Can
we
fix
that,
maybe
by
not
using
the
hostname
at
all?
If
we
don't
need
to
because
maybe
sometimes
graduados
can
we
avoid
singing
sticking
them
in
headers?
If
we
don't
have
to
like
an
example
of
that
which
is
not
in
this
area?
J
Are
the
smtp
headers,
which
are
lots
of
generation
in
that?
Maybe
will
not
need
it
and
also
a
way
that
we
leak
information
is
sometimes
we
build
up,
devicenet
service
names
or
things
like
that,
and
we
take
an
existing
string
like
username
or
machine
them,
and
we
derive
the
name
of
the
cell
is
for
that?
Well,
that's
not
very
good
practice,
so
the
proposition
there
is
that
hey,
we
should
scrub
this
protocol.
F
B
From
IV
versus
ietf
IETF
consensus
is
stronger
than
I
be
consensus,
and
so,
if
the
internet
area
wants
to
pick
it
up,
that
would
be
preferable
to
an
IV
document.
The
only
reason
have
an
IEP
document
when
I
ETF
could
have
done.
It
is,
if
somehow
had
some
scope,
that
spanned
outside
the
IETF
but
I,
don't
think
that's
necessary
here.
In
other
words,
if
the
internet
area
wanted
to
pick
up,
this
document,
I
think
it
would
be
perfectly
appropriate,
Eric
you're
on
the
IEP
as
well.
Yes,
somebody.
K
B
K
B
E
J
H
E
B
F
B
Dave
favor,
my
opinion
is
this:
is
the
right
place
to
give
the
guidance
there
the
audience?
Okay?
In
other
words,
this
is
the
area
that
created
and
owns
the
what
a
host
name
is.
They
are
users
of
it
at
a
higher
layer,
and
so
as
far
as
I'm
concerned,
they
are
on
the
receiving
end
of
this
guidance
and
they
may
have
to
do
their
own
scrub.
B
Okay,
but
as
far
as
if
this
was
going
to
be
a
document
about
general
principles
and
requirements
and
appropriate
uses
of
host
names,
there
a
specific
use
of
it
and
they
may
say
well.
How
does
this
apply
to
me
and
there
would
be
evangelization
that
would
be
necessary
to
said
okay.
Well,
if
we
had
working
group
consensus
on
this
document,
we
could
then
go
to
say
the
app
Siri
or
art
area
meeting
that
says
look.
This
is
what
the
Internet
area
working
group
has
a
Kree
ana's
guidance.
L
Lee
Howard
site,
specifically
like
this
document,
think
we
ought
to
think
we
ought
to
do
something
with
it
move
it
forward
in
other
areas.
The
one
comment
I
had
was
gee
when
you
talk
about
net,
prevents
leakage
of
name
through
reverse
DNS,
because
you
have
one
address
and
multiple
hosts
behind
the
net,
then
that
made
me
think
of
the
document
that
I've
been
bringing
to
DNS
up
for
a
while.
L
That's
purely
operational,
it's
ops
area,
but
it's
still
appropriate
for
it
to
be
here,
because
we
can
give
guidance
about
how
these
things
affect
operations
as
well.
I,
don't
think
there'd
be,
and
then
I
have
a
question
for
you.
Whether
you
should
refer
to
my
document
or
I
should
refer
to
yours,
but
that's
our
both.
K
I
Okay,
so
I'm
here
to
tell
what
I
know
about
or
what
I
think
I
know
about
tunnel
MTO
go
ahead,
so
in
arrow,
we've
put
together
tunnel,
MTU
mitigation
mitigations,
and
what
we're
observing
is
that
in
RC
45
459,
there
are
four
different
alternative
solutions
to
tunnel
MTU
fragmentation
and
reassembly
by
the
tunnel.
Endpoints
signaling,
lower
MTU
to
the
sources
encapsulated
only
when
there's
a
free,
MTU
and
fragmentation
of
the
inner
packet,
and
what
arrow
observes
is
that
there's
not
really
any
one
size
fits
all
solution.
I
I
So
what
we're
saying
is
that
when
the
tunnel
ingress
tunnel,
egress
and
original
source
are
all
within
the
same
administrative
domain,
that's
well
managed.
Where
there's
no
source
address
spoofing,
then
you
can
use
standard
path,
MTU
discovery
exactly
as
it
is
so
a
packet
gets
sent
out
if
it's
too
big
at
MTU
path,
MTU
discovery
message
comes
back
pack
into
big
message
comes
back.
So
when
we
have
these
situations
present,
we
can
use
standard,
ipv4,
ipv6
or
ipv4
path.
Mtu
discovery
on
next
chart.
I
When
the
original
source
and
or
the
tunnel
egress
are
in
different
administrative
domains
than
the
tunnel
ingress,
the
tunnel
ingress
treats
each
packet
according
to
it,
sighs
as
follows.
If
the
packet
is
smaller
than
twelve,
eighty
minus
the
header
length
of
for
encapsulation
encapsulate
and
send
the
packet,
because
1280
is
the
minimum
em
to
you
for
an
ipv6
link.
I
If
the
packet
is
greater
than
1500
bytes
encapsulated
in
senate,
if
the
packets
not
too
big
to
go
to
the
first
time,
first
taught
them
to
you
and
the
expectation
there
is
that
if
that
packet
gets
dropped,
silently,
then
we're
expecting
that
the
original
source
is
used
in
RFC
48-21,
probing
to
make
sure
that
the
1500
in
greater
packers
are
getting
through.
But
then
we
have
this
middle
zone.
If
the
packet
is
greater
than
twelve.
I
I
So
then,
there's
fragmentation
of
the
inner
paca-
and
this
only
applies
to
ipv4.
So
when
the
tunnel
egress
receive
ingress,
receives
an
inner
packet
with
D
F
equals
zero
I
if
the
packet
is
larger
than
the
smaller
1500
and
the
path
MTU
fragment
the
inner
packet
in
224
bite
that
fragments
and
encapsulate
each
fragment,
and
the
reason
for
this
is
that
sources
that
send
ipv4
packets
with
DF
equal
0
have
to
have
some
way
of
knowing
that
the
destination
is
able
to
reassemble.
I
So
the
fact
that
the
tunnel
is
the
one
that's
doing
the
fragmentation
is
immaterial.
There
needs
to
be
some
contract
by
which
the
source
knows
that
the
destination
can
reassemble
these
packets.
But
if
the,
if
the
packets,
no
large
than
1500
bytes
in
the
tunnel
path,
MTU
is
an
unknown
will
still
have
tunnel
fragmentation.
So
we
would
have
fragmenting
the
inner
packet
and
fragmenting
it
of
the
tunnel
packet.
Both
next
chart.
I
Next
chart
then,
and
then
the
aspect
of
encapsulating
when
there's
only
a
free
up
to
you,
we're
seeing
that
more
and
more
links
that
are
in
the
middle
of
the
network
between
the
ingress
and
egress
configure
em
to
use
that
are
larger
than
the
size
required
to
pass
a
59
or
byte
packet.
So
we're
seeing
more
and
more
links
in
the
core
of
the
network
supporting
mt
use
like
9k
bites.
But
the
question
is:
how
can
the
ingress
tell
when
this
is
the
case?
I
One
possible
answer
is
to
probe
the
forward
path
with
a
1500
bite,
probe
packet.
Look
the
problem
with
that
is
there's
no
way
of
knowing
whether
the
probe
packets
will
follow
the
same
paths
as
the
data
packets,
because
the
tunnel
ingress
is
not
the
source
of
the
original
packet,
it's
the
source
of
the
tunneled
packet,
and
it
could
be
that
there's
link
aggregation
gateways
or
equal
cost
multipath
than
them
in
the
path
that
would
cause
the
data
packets
to
take
a
different
path
than
the
probe
packets.
I
So
if
there's
operational
assurance,
though
that
the
probes
will
follow
the
same
path
is
the
data,
then
we
can
use
this
probing
otherwise
use
path,
MTU
discovery
when
possible
and
if
all
else
fails
tunnel
fragmentation
always
works.
So
that's
what
I
know
about
tunnel
MTO
and
David
black
mentioned
that
Joe
touches
as
promised
to
bring
back
the
tunnels
in
the
internet
architecture
draft.
This
is
the
kind
of
test
I'd
like
to
propose
towards
that
document.
H
H
David
black
I'll
watch
resulting
debate
to
between
you
be
between
you
and
Joe,
with
with
great
interest.
I
got
to
say
something
else,
though,
which
is
that
the
packet
two
big
main
general
ICMP
responses.
If
you
have
nested
tunnels,
eventually,
you
run
out
of
ICMP
payload,
and
you
can't
decap
I'm,
not
quite
sure
what
to
do
about
this.
I
Nested
tunnels
is
actually
something
you
got
to
concern
yourself
with
and
that's
why
we
had
the
the
RSC
2460
saying
that
you
have
1500
s
is
the
expected
value
of
the
link,
but
we
say
12
80s
that
we
have
room
for
nesting.
That's
in
the
that's
in
the
path
mt
probing
case
when
you're
using
fragmentation
fragmentation
will
handle
infinite
levels
of
recursion,
recursive
nesting.
K
American
Mike,
so
when
I
talked
about
some
VX
LAN
related,
you
know
tunnel
empty
issues
in
dowlas,
some
on
the
list
folks
stood
up
and
said
they
tried
this
thing
on
the
real
internet
and
they
found
that
one
of
the
issues
that
they
saw
would
list,
but
that's
not
specific
to
Lisp.
Is
that
there's
a
bunch
of
router
is
that
only
include
eight
bytes
of
the
transport
header
in
the
ICP
error,
even
though
the
RFC
that
said,
please
don't,
please
include
more,
is
from
20
years
ago,
but
there's
still
routers
that
do
this
out
there.
K
I
On
where
you
deploy
this,
that
that
first
one
you
talked
about
where
it's
only
including
a
bite,
so
the
the
the
packet
in
the
the
ICMP
Bob
packing
an
error.
What
can
happen
there
is
the
tunnel
ingress
can
cat
you
can
cash
the
size
that
it
received
and
when
the
next
packet
comes
to
be
encapsulated,
if
that
packets,
too
big,
then
you
can
send
back
a
bona
fide
packet
too
big
to
the
original
source.
Yes,
I.
K
Did
I
think
that
when
they
did
someone
the
list,
could
they
did
something
even
more
creative
than
that
I?
Don't
remember
quite
why?
But,
okay
like
they
actually
detected,
someone
is
doing
a
traceroute,
so
maybe
I
should
help
them,
but
by
knowing
how
to
treat.
Did
the
different
flavors
of
tracer
applications
actually
send
packets,
but.
M
Okay
in
many
mobile
Senderos,
also
the
mobile
hotspot,
violence
and
errors
we
often
used
in
trdt
knows
they
should
be
deployed
between
the
word
is
termination
point
and
the
access
point
to
carry
the
euro
data.
We
already
has
that
use
the
cat
web
channels
for
tandem
elephant,
but
for
the
not
scale
usage
the
charity
knows
where
use
should
be
out
configurable
and
also
dynamically
manageable,
so
well,
three
requirements
use
the
access.
M
Router
address
should
be
distributed
to
the
word
list,
termination
point,
so
they
can
start
the
I
Jared
handle
automatically,
and
for
that
we
actually,
you
know
yours
very
simple
solution
here:
use
DHCP
option
to
Lotus
fight
the
specific
address
letter
addressed
to
the
various
transit
intimidation.
Point
next
page,
please.
M
That's
how
this
mechanism
works,
the
access
daughter,
actually
the
channel,
consider-
is
discovered
by
the
HTTP
protocol
to
set
up
a
TI
channel.
The
various
termination
point,
since
a
DHCP
requested
to
dhcp
server
to
obtain
the
GRE
relevant
configuration
parameters,
including
the
access
data,
address,
the
dhcp
server
reply
they
disappear
apply
to
the
word
estimation
point
with
the
address
in
our
data
safety,
je
discovery
option
which
is
newly
proposed
in
the
document.
M
After
that,
the
word
is
termination
point
can
say:
I
established
the
jerry
channel
with
those
information.
The
access
daughter
knows
the
a
request
Val
by
receives
the
Jie
encapsulation
package
from
the
worries
termination
point,
then
let
Jarrett
hello
information
and
address
of
where
this
termination
point
is
checked
and
restores
as
destination
of
j.e
hello
so
for
Ford,
a
stream
package.
So
that's
very
straightforward
and
simple
next
page
give
some
code,
for
you
know
what
the
package,
what
the
extended
dhcp
option
use.
We
have
both
disappear
for
a
dhcpv6
options
for
each
of
them.
M
N
Ron
bhaneko
juniper
I,
like
the
idea
of
the
draft
and
dynamic
tunnels,
there's
a
very
similar
draft,
an
eye
dr,
where
they're
using
bgp
to
signal
dynamic
tunnel
endpoints.
It
makes
sense
to
have
two
mechanisms,
one
for
the
enterprise
one
for
the
white
area.
I
wonder
if
there's
anything
any
part,
that's
so
common
between
the
two
drafts
that
you
should
abstract
them
out
in
a
few
common
sex.
For
that
information,
I
will
go
back
to
study.
That's
draft
sexy.
L
J
Can
we?
So
if
you
go
to
the
Windows
10
Wi-Fi
you
are,
you
will
find
the
option
to
pick
a
network
and
if
you
go,
you
know
to
pick
a
network.
If
you
draw
scroll
down,
you
see
things
like
advanced
options
and
manage
Wi-Fi
options,
which
gives
you
way
to
get
more
about
your
Wi-Fi
connection.
So
if
you
go
to
the
global
control
to
the
manage
Wi-Fi
option,
a
you
will
give
me
scroll.
J
You
will
get
an
an
option
in
the
UI
to
turn
on
the
random
auto
address
for
the
Wi-Fi
connection.
So
what
that
does?
Is
that
if
you
do
that,
we
will
immediately
start
using
random
numbers
instead
of
registered
mac
address
when
you
are
between
two
networks,
when
you
are
probing,
so
it
takes
care
of
the
issue
that
you
have
a
phone
in
your
pocket.
That
is
constantly
looking
for
Wi-Fi
networks
and
constantly
telling
to
the
world
hey.
J
I
have
the
mac
address
number
this
and
that,
and
is
the
network
out
there
that
I
can
connect
to
so
instead
of
having
you
in
here,
ID
there
you
have,
a
random
number
doesn't
reveal
anything.
Then
if
you
are
connecting
to
a
new
network,
so
you
arrive
at
the
ATF
and
say:
hey
I
want
to
collect
the
ietf.
What
we
will
do
is
that
will
pick
a
new
random
number
for
that
network.
J
J
Otherwise,
you'll
get
the
same.
Mac
address
each
time
you
visit
again
I
and,
of
course,
toggling.
The
control
only
affects
what
you
do
between
networks
and
what
you
do.
A
new
network
does
not
not
connected
before.
If
you
are
connected
before
to
network,
you
will
have
a
profile
for
the
network
that
specifies
what
to
do
a
little
bit
of
caveat.
J
This
function
is
only
present
if
you
have
a
recent
driver,
because
I
mean
in
order
to
implement
that
we
need
to
have
an
extension
of
the
dry
for
model
to
be
able
to
tell
the
hardware
that
hey,
please
change
your
mac
address.
Now
there
there
are
things
that
did
exist
before,
but
they
they
require
that
you
change
your
mac
address
and
then
effectively
reboot
your
car,
and
we
don't
want
to
at
least
rebooting,
because
it
was
too
long
that
it
will
affects
their
user
experience.
E
E
J
It
changes,
okay,
okay
and,
and
so
I
said
you
into
a
recent
driver,
which
in
practice
means
that
you
need
to
have
recent
hardware,
like
all
the
machine
that
have
been
designed
for
Windows
10,
maybe
some
of
the
computer's
been
shipped
say
in
2015.
That
will
be
it
because
I
mean
what
happens
in
reality
is
that
they,
the
vendors,
are
building
those
existing
Wi-Fi
cards
once
they
have
solved
your
card
is
considered
too
old
and
they
don't
change
hot
water
bottle
this
once
we
do.
The
driver
next
slide,
please.
J
So
to
come
back
to
what
we
do
pal
network,
you
have
an
option
that
allows
you
to
see
what
you
are
doing
on
the
network
in
particular.
So
if
you
click
on
this
advanced
setting
there,
you
see
that
option
and
we
have
really
three
options
for
the
network
we
can
have
randomization
on,
in
which
case
we
have
a
mac
address
which
is
picked
once
for
the
network,
but
it's
different
for
the
mac
rights
of
any
other
network
that
you
use.
J
We
could
have
off,
of
course,
in
which
case
you
will
use
your
hardware
MAC
address
and
we
could
have
an
option
called
the
daily
change,
in
which
case
you
get
a
new
mac
address
every
day.
For
that
network,
that's
easy
enough
to
understand
the
this
option.
In
particular
in
enterprise
enjoyment,
enterprise
can
install
script
with
a
script.
J
So
first
question
is:
is
it
on
by
default?
Well,
the
answer
is
no.
We
we
want
to
have
a
user
action
to
enable
it
and
the
reason
we
want
that
is
that
dark,
dark.
Some
cases
we've
seen
some
cases
well
strange
stuff
happens,
so
we
want
to
collect
enough
telemetry
a
to
understand.
What's
the
frequency
of
those
issues
that
we
can
decide
whether
we
turned
on
by
default
or
not?
If
we
don't
turn
on
tonight
or
by
default
URI
for
effectively
advanced
users,
people
like
us
to
exploit
first
I
said
a
lot
Enterprise.
J
They
can
install
a
can
with
a
script,
install
a
Wi-Fi
profile
for
the
enterprise
network
and
turn
the
video
off
on
the
Wi-Fi
network,
but
that
work
there
is
one
see
my
popular
feature
in
Wi-Fi
network
that
people
sometimes
use
which
is
mac
address
filtering
that
you,
you
program,
the
mac
address
of
the
authorized
station
in
your
water.
What
if
you
want
to
do
that,
you
would
have
to
turn
the
video
off
for
your
network.
J
J
J
J
If
you
change
your
mac
address
all
these
potholes
in
the
hotels
and
the
and
the
stuff,
don't
recognize
you
anymore,
and
so,
as
they
don't
recognize
you
anymore,
they
will
prompt
you
to
accept
the
terminal
conditions.
If
you
are
paying
for
the
Wi-Fi,
they
may
prompt
you
to
pay
again.
We
will
not
want
that
at
least
not
by
default,
and
so
that's
why
we,
if
you
visit
the
same
network
again
and
again,
we
keep
the
same
mac
OS
on
that
network.
J
What
about
the
phone
while
the
phone
is
running
the
same
software
as
it
walks
on
the
phone
as
well?
And
is
that
enough
to
be
anonymous?
Of
course
not.
We
know
that
you
guys
are
leaking
metadata
all
over
the
place,
but
it's
the
first
step.
Okay
and
then
a
little
personal
experience.
I
have
been
self
hosting
this.
For
the
last
six
months,
I
was
running
it
at
the
IETF
in
Doris.
Actually,
I
have
basically
it
works
them
in
a
way
I
hear
it
works
just
fine.
It's
no,
no
particular
issue.
J
I
have
observed
one
case
in
which
I
could
not
connect
to
a
network.
It's
a
particular
network
in
a
mall
in
Bellevue,
and
basically
you
could
connect
if
you
turn
randomization
off
and
you
could
not.
If
you
have
it
on
and
I
assume
that
they
have
some
kind
of
software
in
the
control
system
to
check
the
the
bits
in
the
mac
address,
and
they
say
no,
if,
if
they
see
something
random
and
I
could
speculate.
Why
but
I
actually
don't
know
and
couple
of
Fernand
interactions.
J
They
attempted
to
publish
DNA
speakers
for
the
computer
and
because
you
are
something
like
six
five
or
six
leases
for
the
same
computer.
That
would
want
to
have
five
or
six
AV
cords
publishing
the
internal
local
dns,
and
that
was
very
not
tested,
and
the
host
of
car
blew
up
all
right
of
all.
Apart
from
these
tiny
things,
it
works
great
and
and
and
I
hope
that
as
we
ship
it,
people
will
fix
their
bugs
and
it
will
walk
even
better.
O
J
O
Ssid,
ok
and
the
connection
ID
that
gets
hash
to
produce
the
random
mac
address
that
doesn't
change
as
long
as
the
network
is
in
my
preferred
network
list
right,
that's
going
to
yet
so
well,
that
is
nice
for
the
the
hotel
doesn't
make
me
pay
twice.
It
means
that
every
time
I
go
to
say
the
coffee
shop
I'm
going
to
get
the
same,
the
same
mac
address,
and
then
they
know
that
a
see
you
again
damn
drinks
coffee
at
eight
o'clock
every
day.
Yes,.
C
O
Somebody
with
this
MAC
address
does,
and
god
he
just
have
to
correlate
with
with
with
Dan,
and
that's
so
that's
why
we
ask
these
auction
that
you
can
go
to
the
control
and
says
please
change
it
every
day,
okay
and
this,
my
third
question
is:
has
there
been
any
large-scale
testing
of
this
on
your
network
at
Redmond?
We.
P
Vent
ability
at
two
questions,
so
this
molar
this
motor
is
turning
you
down.
I
wonder
if
it's
looking
at
the
mac
address
from
the
probe
and
then
the
MAC
addresses
from
the
association
or
question
saying:
oh
I,
don't
know
about
this
go
away.
I
could
speak
to
it.
I,
don't
know
why.
But
then,
because
there's
gonna
be
they're
gonna
be
using
software,
that
other
people
are
using.
There's.
J
P
It's
still
one
not
working
a
second
question
like
we
in
v6
ops.
We
have.
We
do
all
this
hand-wringing,
sorry,
but
insects.
When
we
do
all
this
hand-wringing
about
collisions
and
64-bit
spaces
he's
like
Oh
dad
doesn't
work.
That
means
to
work
better,
that
that
needs
to
work
horse.
We
should
kill
it.
We
should
make
it
reliable
and
so
on
what
about
your
a
46,
Mac
or
forty
six
bits?
What
are
you
doing
with
collisions
there?
Yeah.
J
P
J
P
P
I
Fred
template
from
Boeing,
so
Lorenzo
just
asked
the
question
I
was
going
to
ask,
which
is:
how
can
you
tell
that
you're
not
going
to
have
two
nodes
showing
up
on
the
same
link
and
configuring
the
same
mac
address,
so
there
needs
to
be
some
analysis
about
collisions
and
and
duplicate
address
in
the
mac
space
and
the
guy
behind
you
at
the
knowledge
of
that
analysis.
Ok,.
E
C
E
In
the
probing
mode,
if
you
keep
the
same
address
for
for
a
certain
time,
we
know
of
this
use
case
of
the
of
the
trash
bins
and
in
the
City
of
London
that
we're
tracking
users
on
the
street.
So
if
the
same,
if
one
mac
address
shows
off
on
one
corner
and
finishes
up
in
the
different
corner
every
day,
well
and
then
the.
E
O
Want
to
quickly
address
the
probability
of
a
collision,
because
I
have
been
running.
These
numbers
I've
been
having
this
Argan
with
people
for
a
long
time.
So
the
issue
is
that
the
collision
has
to
occur
in
the
same
broadcast
on
the
same
subnet
and
the
way
people
build
networks.
They
don't
have
networks
that
have
forty
thousand
nope
people
connected
to
it.
It
just
doesn't
work.
You
know.
O
F
K
So
thanks
for
making
some
time
on
the
agenda
for
this
I
did
this
draft
just
before
the
cutoff.
So
I
talked
about
this
stuff
in
Dallas
briefly
as
well,
so
in
intentionally
partition
partially
whatever
likes
something
next
slide.
So
the
main
reason
me
standing
up
here
is
to
get
you
guys
to
read
the
draft
so
I'm
here
to
actually
and
and
also
if
people
are
interested
in
collaborating
on
this
stuff
and
ironing
out
some
of
the
details,
I'm
interested
in
not
as
well.
So
what
are
these
things?
While
we
have
these
things?
K
Examples
of
this
are
split
horizon
for
dsl.
There's
similar
things
for
cable
I
haven't
found
a
good
reference
for
how
the
cable
does
this
stuff,
but
and
then
there's
private
vlans,
and
they
all
have
these
properties
that
you
presented
to
IP
as
here's
a
link
and
yeah
allocate
a
subnet
prefix
to
it,
but
the
layer,
2
forwarding
characteristics
of
this
is
non-uniform
right.
K
Not
everybody
can
talk
to
everybody,
and
typically
it's
done
in
a
way
where,
where
all
the
deployments
I
know
about
it's,
about
hosts
being
able
to
talk
to
the
routers
at
layer,
2
and
and
in
the
reverse
direction,
but
host
not
being
able
to
talk
to
hosts
the
private
VLAN
stuff
is
actually
a
super
sad.
As
far
as
I
can
tell
from
the
split
erosion
mechanisms
in
two
ways,
one
is
that
well,
first
of
all,
it
has
three
different
types
of
ports
in
the
network.
It
has
promiscuous
ports,
community
ports
and
and
isolated
ports.
K
The
promiscuous
ports
is
where
you
connect
your
router's,
but
you
can
have
multiple
of
those,
so
you
can
actually
deploy
this
in
a
network
where
you
have
two
or
more
routers
on
the
subnet,
and
that
makes
it
would
make
some
of
these
things.
Interesting
and
I.
Think
that
that's
where
there's
some
stuff
that
we
actually,
it
would
be
useful
to
actually
write
down
how
we
want
those
things
to
behave,
and
the
other
thing
in
house
are
the
this
community
porch,
which
is
basically
being
able
to
say
I,
have
some
subsets
of
these
three
ho's.
K
K
You
have
to
be
careful
in
gentleman
proxy
arp.
If
you
happen
to
run
with
address
conflict
detection,
you
have
to
make
sure
that
your
proxy
arp
implementation
doesn't
respond
to
to
the
probes
that
RFC
52-27
us,
because
then
the
host
will
say:
oh
I
have
a
duplicate
and
just
go
away
right
so
and
since
proxy
arp
isn't
specified
anywhere
in
any
RFC
or
any
any
specification,
it's
probably
useful
to
write
that
down.
So
you
don't
respond
to
that.
K
The
other
one
shows
up
when
you
have
multiple
routers,
because
then
you
can
have
if
that,
if
Radha
one
needs
to
send
an
ARP
request
for
the
host
well
and
the
other
router
is
proxy
harping
for
everybody.
How
do
you
prevent
that
router
from
responding?
There
is
a
way
I,
don't
know.
If
people
have
built
anything
to
do
this
in
existing
products,
you
can
tell
it
because
it's
showing
up
on
it
on
the
basically
on
the
on
the
what
is
it
called?
It's
called
the
not
the
default
VLAN,
basically
the
promiscuous
VLAN.
K
It
shows
up
with
that
VLAN
ID,
so
you
can
tell,
but
that's
that's
the
thing
that
you
know
I
need
to
find
out
more
and
people
are
welcome
to
help
how
the
products
actually
do
this
stuff
today,
but
for
neighbor
discovery.
Proxy
Andy
works.
Well,
sorry
proxy
dad
works
well,
it
has,
and
you
know
it's
ending
Ras
with
on
link
equal
0
works.
Well,
there
is
a
question
about
if
you
send
link
local
packets-
and
you
expect
us
to
reach
other
hosts
that
are
in
the
same
subnet,
you
would
have
to
have
the
routers
forward.
K
Those
things
and
you
end
up
with
similar
issues
to
the
the
you
know,
ARP
for
our
ping
answered
by
the
other
rod.
Or
how
do
you
prevent
getting
a
rotting
loop
or
router?
One
says:
oh
I
should
forward
this
link
local,
but
I,
don't
know
where
it
is,
and
the
second
router
picks
it
up
and
their
ping-pong
it
back
and
forth.
I
need
some
care
in
that
space
as
well.
K
So
that's
basically
the
set
of
issues
that
I've
run
into
so
far
in
terms
of
figuring
out.
How
do
these
things
actually
work?
So
there's
a
question
at
the
bottom
on
this
slide.
I
think
you
know.
If
people
have
read
this
document,
I
would
be
glad
to
find
out.
I
suspect.
Not
many
people
have,
but
I
did
send
a
note
to
the
list
of
all
back.
But
if
people
have
stuff
to
discuss,
let's
do
it
on
the
list
or
catch
me
in
the
hallway.
Okay,.
