►
From YouTube: IETF93-UTA-20150721-1740
Description
UTA meeting session at IETF93
2015/07/21 1740
A
A
A
Richard
or
an
area,
can
you
guys
close
the
door,
your
closest
to
it?
Thank
you
thanks
thanks
a
lot
all
right,
so
we
have
a
volunteer,
note-taker
scope
and
there
is
a
remote
q
on
on
meat
echo
today.
So
we
have
act.
We
may
have
remote
participants
right
now.
We
don't
have
any
I
think
and
if
like,
if
we
can
get
a
volunteer
to
do
just
have
a
look
at
Jabbar.
Thank
you.
A
A
We
have
a
few
published
or
disease
and
already
have
gathered
some
arata,
notably
on
the
basically
on
the
attack
documents.
I'm
I'm
actually
going
to
say
that
this
is
not
to
be
this
shouldn't.
Be
that
surprising
to
people
as
these
things
actually
do
evolve
over
time
and
at
some
point
I'm
sure,
we'll
decide
to
to
rev
the
bcp.
A
We
have
one.
We
have
two
upstanding
drafts.
One
of
them
is
the
email
assert
that
Aleksei
is
working
on
elexi.
We
actually
did
pass
through
working
group
last
call
and
and
bri
and
just
as
we
were
closing
working
last
call
Alexa
got
a
couple
of
comments
and
I
believe
you
revving
Aleksei
do
I
do
you
have
anything
you
want
to
add
to
that.
A
Right
there,
okay!
So
at
this
point
to
me
it
looks
like
the
comments
that
you
got
or
you
know
within
this
within
the
scope
of
things
we
could
handle
during
working.
Those
working
with
last
call
durations,
so
I'm
just
going
to
go
out
on
a
limb
and
say
we
don't
need
an
extra
working
with
blast
cold
for
this.
Does
anybody
feel
strongly
that
we
do.
A
A
B
Ok,
so
I
got
an
update
to
the
draft
at
the
last
minute,
so,
like
a
lot
of
people
do
on,
let's
go
ahead.
This
is
just
the
quick
over
you
overview
of
what
the
draft
does
for
people
who
are
curious.
I
won't
go
into
detail
on
this
since
we're
half
hour.
So,
let's
move
on
so
the
changes
in
this
version
of
the
draft
I've
updated
clarified.
The
abstract
use
the
term
confidentiality
instead
of
privacy.
In
most
cases
move
some
sections
added,
you
know
tried
to
clarify.
B
End-To-End
encryption
is
not
covered
by
this
document.
Moving
on
I
swap
the
order
other
sections
chain.
We
change
the
meaning
of
TLS
10
and
12
lashes
to
require
sir
Khalid
ation
for
the
discussion
last
time.
I've
also
replaced
a
cipher
suite
advice
with
reference
to
yo,
are
bcp
and
and
change
the
examples
to
use
the
recommended
cipher
moving
on
so
updated.
B
The
newer
TLS
advice,
yeah
clear
text
in
the
introduction
it
doesn't
cover,
smtp,
relay,
update
references
and
then,
and
then
the
other
substantive
one
recommended
recommend
start
TLS
for
smtp
submission
in
addition
to
employ
pls.
This
is
because
it's
not
clear
whether
one
of
these
two
has
in
that
in
for
that
particular
protocol.
It's
not
clear
whether
one
of
the
two
has
the
majority
deployment,
so
so
that
loosened
the
requirement
to
bid,
but
there's
still
a
general
direction.
Moving
towards
implicit
TLS.
B
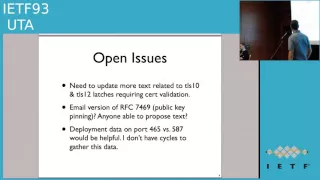
So
the
open
issues-
I
missed
one
of
the
changes
on
the
TLS
10
and
12,
requiring
certain
validation,
so
I'll
fix
that
in
the
next
Rev
on
an
interesting
issue
was
raised
on
Sunday
on
so
there's
a
there's,
an
hgp
standard
for
public
key
pinning.
This
is
a
new
new
RFC,
that's
published.
So
the
question
that
was
asked
is
yo
on.
B
B
You
know
public
key
pinning
raises
the
implementation
bar
quite
a
bit
so
I'm
kind
of
inclined
to
leave
that
till
ad
for
a
subsequent
thing
extension,
but
I
did
want
to
mention
the
possibility,
because
you
know
it
was
an
interesting
question.
You
know,
since
this
is
sort
of
doing
HH
STS
for
email.
You
know
the
other
recent
a
cheapy
security
improvement
is
the
public
key
pinning
and
and
so
that
that's
an
issue
wondering
if
anyone
has
opinions
on
that.
C
So
I
actually
haven't
processed
this
question
about
whether
we
should
do
something
like
public
keep
inning
as
well.
There
has
been
a
bunch
of
discussion
about
h,
st
s
and
how
we
would
do
that
differently
for
the
web.
If
we
had
the
planning
experience
that
we
now
have
and
I
don't
know,
no
exactly
sorry.
This
is
daniel
congo.
More
I,
don't
know
that
that
applies
to
email
in
the
same
way,
so
you're
framing
of
it.
Just
now
is
like
making
me
think
about
how
to
apply
it
and
I.
C
C
D
B
Thanks
done,
then,
the
final
thing
on
my
oh
I'm
I,
open
issues
list
is:
it
would
be
nice
to
have
deployment
data
of
port
465
versus
587
for
email
submission
on
how
widely
those
are
used.
I
know
they're
both
used
out
in
the
wild
I,
don't
know
how
widely
they
are
relative
to
each
other.
I
don't
have
this
equals
to
gather
this
data
due
to
other
work
things
going
on
so
I.
B
E
B
G
A
B
The
goal
should
be
interesting
so
other
than
those
three
issues.
I'm.
Basically,
you
know
I
think
this
document
is
is
very
Cleo.
It
is
ready
for
working
group.
Last
call
at
this
point.
You
know
I
I'm,
not
aware
of
any
major
major
problems
then
so
at
the
text.
Massaging
I
want
to
do
so.
I
could
do
a
quick
rev
after
the
meeting
on
and
but.
A
I
want
to
do
the
usual
thing
in
Pig
people
for
volunteers,
committing
to
review,
because
before
we
do
working,
that's
called
really
need
a
couple
of
people
saying
on
the
list.
Yes,
I've
reviewed.
This
looks
good
right,
so
this
is
a
good.
This
is
a
good
time
to
volunteer
to
to
do
a
review.
A
document
I
see
then
tkj
is
volunteering.
Oh
and
an
Alexa
is
volunteering.
A
Your
names
are
going
on
the
on
the
notes
now
come
on
at
least
one
more
person,
volunteering
to
review
Oh
perfect.
Thank
you,
I
didn't
get
your
your
name
Erin!
Thank
you
perfect
and
victor
is
volunteering
from
from
from
yabber,
so
we
got
four
people
want
to
interview.
This
is
excellent.
If
you
guys
can
do
that
relatively
soon,
then
we
can
maybe
actually
be
in
your
past
working
best
quote
by
your
comment.
That
would
be
fantastic.
Yeah.
F
B
I
mean
where
it
would
common
useful.
Is
there
there's
the
ones?
You
know
that
you
know
the
text
in
in
the
document
currently
that
registers
that
rhetoric
that
modifies
the
registry
so
that
port
65
465
is
registered
for
both
purposes
it's
actually
used
for,
rather
than
only
one
of
them,
you
know
the
one
that
actually
makes
the
registry
reflect
reality.
That's
going
to
be
a
controversial
change
in
the
wider
IETF.
B
We
know
that
if
you
know,
if
the
data
we
see
is
that
everybody
who
supports
port
465
also
supports
start
TLS
on
yeah,
and
we
get
a
lot
of
pushback
on
that.
That
gives
us
a
fallback.
If
the
data
we
see
is
there's
yo,
there's
lots
of
providers
or
key
clients
that
only
support
for
65
and
don't
support,
start
TLS.
Then
we
have
ammunition
to
push
back
on.
You
know
on
on
the
people
who
don't
like
awarded
yo,
don't
like
award
in
the
registry
that
reflects
reality.
B
H
This
is
a
venir
I'm,
channeling,
keith,
moore
from
Jabra.
Well,
since
three
things,
first
I
concur
with
Chris
that
we
could
wait
to
define
a
general
public
opinion
spec
for
email.
Second
thing,
someone
tell
Chris
that
Kurt
has
volunteered
to
pull
m3a
AWG
on
ports,
and
the
third
thing
is
to
clarify:
are
we
expecting
reviews
prior
to
what
group
last
call,
or
are
these
people,
volunteering
to
review
as
part
of
working
group?
Last
call
up.
A
A
F
B
F
B
F
A
Alright,
so
that
will
be
within
the
next
couple
of
weeks:
I
guess
then
quiz
or
Oh
fantastic,
that's
excellent,
alright,
see
if
I
can
move
us
back
to
our.
So
thank
you
Chris.
So
we
have
the
these
are
documents
that
are.
These
are
working
working
with
documents,
obviously,
and
then
we've
had
a
request
to
present
a
an
individual
draft
that
by
Pascal
are
you
in
the
room
there
you
are,
and
so
so.
A
I
Right:
okay,
thanks
so
everybody's,
so
my
name
is
bisceglia
from
to
the
camp
attic
france.
So
this
is
a
draft.
That's
a
proposal
for
defining
security,
module,
40s
and
DTS.
So
next
slide,
please
so
the
goals
TLS
and
DTS
are
widely
used
for
HTTPS,
extensible,
authentication
protocol
or
cope.
And
so
what
is
the
idea
of
chilies
and
DTS
security?
I
So
the
draft
works
over
I
pls,
which
is
a
well-know
AFC
and
I.
Pls
is
a
way
to
transport
chilis
without
any
ipv4,
v6
favors,
and
so
the
idea
is
to
to
use
it.
Yes,
as
a
as
a
way
to
define
the
binary,
only
room
for
the
transport
of
GS
and
to
reuse
it
for
dtls
and,
let's
say
informally,
it's
fgts
so
next
slide.
Please
so
she's
a
global
architectures
of
this
draft.
So
you
have
the
right:
the
chill
sdt,
less
security
module.
I
It's
a
black
box,
so
everything's
dealing
with
TLS
or
DTS
is
computing
in
this
black
box,
and
then
you
have
in
the
middle
is
called
software
bridge,
and
this
software
bridge
is
a
proxy,
so
there's
an
interface
with
the
networks.
So
at
this
level
this
software
bridge
sent
els
and
DTS
packet
over
the
networks
and
the
interface
between
the
transport
between
software
region.
Terrasse
de
clases
is
male,
/,
ETS
or
and
formerly,
if
DTS.
I
So
let's
say
if
GTS
is
not
very
different,
because
if
I
use
the
same
same
frameworks
so
on
the
upper
side,
you
see
the
application
that
could
be
HTTP,
co-op
or
other.
And
let's
say
when
the
terrace
of
the
test
session
has
been
booted.
It
says
that
you
at
the
end
of
the
unshaken
fat.
We
say
when
both
finish
heed.
The
message
has
been
exchanged
between
the
server
or
the
client.
Then
there's
to
proceed.
I
I
I
So
let's
say
about
10
billions
of
this
kind
of
chip
manufacturers
today
every
year,
and
so
there
are
secure
I
evaluated
according
to
certification,
evaluation,
I,
also
common
catia,
either
Chrome
on
katella
or
hips,
and
so
on.
It
was
just
a
recall
of
tip
support
in
smart
card.
It's
a
drive,
you
know
the
29th
Russian
today
and
this
try.
I
This
draft
describe
the
way
to
transport
a
TLS
/,
iso
7816,
and
his
draft
works
as
a
client
and
server
even
in
this
first
version
of
this
draft
is
focus
on
client
features
of
the
security
mohammad
yours,
but
to
mine
command
at
the
azo
7816
level,
which
are
reset
to
reset
the
state
machine.
Let's
say
the
chilis
or
DTS
state
machine
and
process.
I
It
which
is
a
way
to
transport,
TLS
and
DTS
packet
over
each
pls
and
detail
or
DTS,
and
then
/
iso
7816,
who
give
you
an
idea,
is
a
memory
for
footprint
of
the
security
modules
for
Charis
or
DTS,
is
about
25
kilobyte.
That's
not
a
lot,
but
to
be
frankerz
of
both
for
code
and
data,
but
it's
mean
or
option
of
chillicothe
TLS
are
not
supported
according
to
the
application
and
all
the
crypto
is
performed
by
crypto
processor,
with
phipps
c'mon,
creepy
evaluation.
So
next
type
is
so.
I
As
you
say,
this
is
a
nice
tration
of
the
ISO
7816
interface.
Those
are
two
main
commands
which
are
processed
eep
and
the
reset
state-
and
all
this
is
more
precisely
described-
is
a
previous
draft
if
smart
cards,
so
next
type
is
so
just
a
recall
of
the
segmentation
of
GLS
or
DTS
right
over
pls.
So
here
you
see
on
the
software
bridge,
software
bridge
produce
a
request.
Let's
say
each
EEP
requests
are
used
to
fragment,
GLS
or
dtls.
I
The
flight
number
of
flight,
for
example,
for
the
full
mod
for
TLS
46
of
the
full
mod
in
DTS,
and
this
fragment
are
acknowledged
by
EEP
response,
small
small
packet.
So
this
is
an
illustration
of
segmentation.
Let's
say
for
a
packet
fight
son
by
the
software
bridge,
so
next
slide
please,
and
he
has
a
slide
just
the
reverse
illustration
of
Charis
or
DTS
flight
that
are
sent
by
the
security
modules
tour
of
the
software
bridge.
So
each
slice
is
a
segmented
in
a
number
of
fragment
according
to
jo-ann.
I
7816
requirement,
it
is
acknowledged
by
the
software
bridge.
So
next
slide,
please
about
the
fragment
size,
late
sides
as
they
should
be
between
50
to
200
bite,
so
it's
mean
which
was
a
smaller
or
back
yet
next
slide
please.
So
this
is
a
new
tration
of
EDG
egts
over
deep.
So
let's
say
it's
exactly
the
same
things
that
the
idea
is
to
simply
reuse
pls.
I
So
the
same
things
accepted
the
same
fragmentation
rules
for
the
for
the
flight
accepted
that
it's
not
EGS,
it's
not
jealous
back
yet
that
are
transported
it's
just
ggs
back
yet
so
for
the
full
model,
six
fights
for
EPS
and,
if
dtls
so
next
slide.
Please
all
for
software
bridge.
The
goal
of
this
proxy
is
to
send
and
receive
GS
and
DTS
rise
to
from
the
networks.
So
this
is
networks
interface,
so
software,
which
perform
segmentation
and
reassembly
operation
operation
with
the
security
modules
for
for
Charis.
I
It's
not
a
big
deal,
because
TRS
is
a
offer
free
stream.
So
everything
is
corrected
by
by
by
tcp.
So
there
is
not
a
big
job
for
the
software
bridge
at
this
level
for
DTLS
it's
more
complex
because
main
difference
between
GS
in
DTS
is
that
DTS
perform
segmentation
at
the
unshakeable
involve
on
shake
message.
So
the
convention
we
use.
I
Then
after
we
need
to
other
things.
A
from
to,
we
need
to
add
towards
things
from
Ottawa
for
apts
I've
dtls.
We
need
to
have
some
procedural
to
sand
and
to
send
encrypted
and
a
schmucky
the
record
packet,
and
we
need
a
procedure
to
decrypt
and
check
the
receive
encrypted
and
a
schmucky.
The
record
packet,
so
next
I'd
piece-
and
this
is
illustrated
by
this-
to
operation
fog
for
encryption.
I
Which
sorry
with
Clare
text
and
then
the
security
module
produce
and
encrypted
the
record-low
hallelujah
and
with
the
ash,
mac
and
so
on
and
obviously
or
the
segmentation
operation
are
performed
by
the
hip
protocol
and
four
decryption.
So
the
software
moon
bridge
receive
a
packet
encrypted
and
ash
market
and
the
a
schmuck
is
check
it
and
the
packet
is,
is
decrypted
by
the
security
module
so
next
type
is
it
means
no
more
so
in
the
draft
more
detail,
obviously
about
our
of
this
rocks.
C
Hi
dkg,
so
it
sound
like
you're
doing
I
had
a
hard
time
following
I
think
because
I
know
very
little
about
I,
so
I'm
even
know
at
the
ISO
numbers
anymore.
It's
already
out
of
my
memory,
but
I
know
about
smart
cards.
So
it
sounds
like
you're
doing
both
the
handshake
and
the
application
data
indiamart.
I
I
Our
data
rate-
let's
say
that
I
rate
is
about
shoe
kilobyte,
this
dependence,
the
device
you
use-
but
let's
say
yes,
kilobyte
parser
countries
as
it's
sufficient
for
Internet
of
Things,
for
example.
The
gore
is
more
Internet
of
Things
than
the
goal
is
more
cherries
and
DJs
and
jealous
because
for
the
Internet
of
Things,
you
have
very
small
that
afro
put.
If
you
take
a
look
at
the
current
specification.
I
Some
usually
people
speak
of
data
right
between,
let's
say,
100
bits
per
seconds
to
a
few
kilobits
per
second,
so
thinking
about
low
throughputs
but
which
is
can
be
used
for
is,
for
example,
GLS.
If
you
use
a
pls
for
authentication,
I
mean
you
may
use
in
your
things.
You
may
need
to
have
this
ET
les
authentication,
so
you
may
underboss
in
the
same
security
module
or
may
use
VPN
or
whatever.
I
But
let's
say
if
you
want
to
set
up
pls
or
detailer
session,
because
it's
basically
the
same
things
same
cryptography
accepted
for
the
fragmentation
issue.
That
is
not
a
really
big
issue,
because
no
cryptographic
equation
are
performed
with
other
fragments,
which
means
the
security
Momo
Momo
George
did
with
full
packet.
That's
not
really
a
big
difference
between
TSN
DJ
s.
I
So
if
you
want
to
set
up
a
pterosaur,
dt
recession,
its
takes
between,
let's
say
1
seconds
to
10
seconds,
depending
on
the
kind
of
chip
you
use,
the
price
of
the
chip
and
so
on
without
strong
difference
and
the
foot
boots
and
cryptographic
capacity
between
the
different
chip
available
in
the
market
could
be
sim
card.
For
example
the
ID,
if
you
have
a,
for
example,
for
your
thinking's
to
the
Internet
of
Things,
if
you
say,
I
use
cryptographic,
module
and
run
this
in
the
sim
card.
I
H
I
Talking
about
applications,
that's
for
internet
of
things
that
thats
collecting
data,
for
example,
if
you
as
a
client
for
GTS
its
menu,
are
collecting
data
and
if
you
have
a
server
for
the
GRS,
its
mean
module
sinks
and
you
need
some
kind
of
trustworthy
computing
in
order
to
sign
your
data
to
somebody.
This
is
a
trusted
entity
and
if
you
are
boss,
you
are
simply
dealing
with
plus
wapsi
Internet
of
Things
frameworks.
I
C
F
C
C
I
Well,
looking
the
goal
or
the
security
module
is
to
provide
a
trust
for
C
computing,
it's
mean
if
it
doesn't
work,
it
doesn't
works.
There
is
no.
If
you
are
sinks,
it's
not
the
same
thing.
If
you
are
behind
a
browser,
for
example-
and
you
see
something
say
they
knew
that
it's
the
wrong
certificate
on
whatever
you
are
yeah,
it's
a
it's
a
human
interface,
so
it's
mean
you
have
ok,
you
may
choose
to
do
things
or
not.
I
If
you
always
thinks
it's
difficult,
if
its
phase,
you
say
its
phase,
you
know
things
doesn't
think
so
it's
little
different
so
about
the
profile,
obviously,
due
to
the
let's
say,
to
the
size
of
this
kind
of
chip,
because
our
small
chip
and,
let's
say
the
memory
from
the
application,
let's
say
for
the
chairs
or
DTS
staff-
is
about
to
come
on.
Please
about
100
kilobytes,
it's
quite
secure,
but
it's
quite
small.
So
you
have
to
choose,
depending
on
your
application,
what
kind
of
an
of
the
chip
capacity?
I
What
kind
of
cryptography
and
the
option
you
want
to
support
for
chairs
or
DTS.
With
this
kind
of
chip
you
can
deal
with
LSA,
for
example,
or
or
elliptic
curve.
It
doesn't
really
matter
else
because
the
same
kind
of
complexity.
So
after
maybe
you
will
not
deal
on
a
given
ship
if
we
with
both
with
Ariza
or
elliptic
curves,
and
you
may've
supports
an
option
for
some
poor.
I
You
may,
depending
on
the
blade
you
use
specially
for
the
Internet
of
Things
you,
maybe
you
could
be
interesting
to
deal
with
pressure
fee,
for
example,
to
use
a
symmetric
staff,
because
you
operate
a
lot
of
stuff
likely.
You
will
be
more
interested
by
symmetric
cryptography,
which
both
certificate
for
servers
and
pre-shared
key
for
for
folio
for
your
samsung
on
whatever.
So
it
means
there's
a
lot
of
to
do.
You
want
to
go
in
this
direction
and.
F
So
we
have
a
way
we
have
had
a
good
discussion
here,
and
the
point
that
I
would
like
to
make
is
the
internet
status
of
this
chaffed
is
experimental.
So
my
question
is
what
what
do
you
expect
from
utah
by
presenting
the
document
here?
Are
you
targeting
in
it
in
towards
the
in
individual
experimental
RFC?
Is
a.
F
I
Sometime
parties,
it
is
a
software
bridge
which
is
kind
of
proxy.
It
seems
to
meeting
the
target
of
this
working
group
and
take
a
look
at
the
security
Momo
Momo
module.
It's
mean
it's
not
full.
It
could
not
be
full
implementation
of
TLS
or
dt
less.
It
should
require
profile
depending
to
some
application.
I,
don't
know
yet
what
else
this
application
so.
A
I
suggest
that
next
steps
for
you
is
to
solicit
the
response
and
review
on
the
mailing
list
and
we'll
we'll
see
what
happens.
I'm
not
seeing
a
a
torrent
of
enthusiasm
for
adopting
this
is
a
working
group
today
document
today
and
not
ensure
that
it
would
be
in
or
shorter.
But
I
think
you
know
continue
the
discussion
on
the
utah
list.
If,
if
there
is
sort
of
a
a
surge
of
interest
and
I
think
we.
A
D
Steve
Francisco
I've
got
a
draft
on
UTA
I've
got
it
I,
put
out
a
draft
on
search
verification
for
MTA
2mp.
A
communication
is
actually
to
close.
An
in
Outlook
360
there's
been
a
desire
to
expand
that
right.
You
have
to
eat
the
microphone.
Ok,
I'm
going
to
eat
the
microphone.
Now,
there's
been
a
desire
to
expand
that
and
basically
it
addresses
you
know
the
deep.
The
deep
draft
calls
out
it
doesn't
do.
Mt
8,
MTA,
TLS
or
its
alexys
calls
out.
A
I
actually
do
believe
we
had
a
guy
from
comcast
sort
of
pop
pop
their
head
up
on
the
last
ITF
and
say
they
were
sort
of
interested
in
working
on
that.
Let
me
let's
talk
off
right
afterwards
and
make
sure
I
dig
up
my
notes
on
that,
but
I
think
we'd
be
more
than
happy
to
see
a
draft
anybody
else
in
the
room
here.
Will
they
would
be
interested
in
contributing
helping
out
Aleksei,
excellent
anybody
else?
A
A
A
Don't
mind
having
that
discussion
now,
I
think
just
to
put
some
color
on
this.
We
we
have
the
on
more
or
less
what
the
working
group
set
out
to
do.
Publish
bcp
in
attack
attack
drafts
republished
an
XMPP
profile
for
the
PCP.
The
email
work
is
sort
of
getting
there
right
with
the
the
MTA
to
MTA
stuff.
Coming
at
all
right,
we
could
be
looking
at
a
a
fairly
sort
of
complete,
rounded
out
set
of
documents
in
a
in
a
in
a
few
miles
right.
C
Dkg
I
was
just
going
to
say
that
the
other
place,
the
other
application.
That's
in
the
process
of
trying
to
figure
out
whether
using
TLS
is
a
good
idea
is
dns
and
the
drafts
that
are
at
work
for
that
are
in
deprived
and
they're
not
here,
but
if
we
want
to
have
a
UTA
style
guidance
about-
and
you
know
what
kind
of
profiling
of
TLS
should
be
done,
I
don't
know
I.
Maybe
we
just
leave
that
in
deprived
all.
G
G
A
G
J
Those
last
two
I
mean,
I
think,
deprived,
is
kind
of
chunked
me
away.
I
don't
think
they
know
it's
not
at
the
stage
where
you'd
want
to
know
this,
so
I
think
that
would
be
better
there
and
phor
tak.
I
think.
If
work
was
we
do
not
have
a
nice
that
would
be
that's
workable,
so
again,
I,
don't
that
would
be
here.
A
Yeah
so
anyway,
for
if
you're
sitting
in
some
in
some
of
it
somewhere
figuring
figuring,
you
wanna,
you
want
your
draft
sort
of
in
UTA
or
you
think
its
scope
to
UK.
Now
it's
the
time
to
do
it,
whip
it
out,
because
we're
not
necessarily
going
to
stick
around
for
very
much
longer.
If
they're,
if
we're
done
with
the
email
stuff,
then
it
may
actually
be
appropriate
for
us
to
to
wind
down.
So
you
know
the
drafts
don't
improve,
improve
with
within
each
their
own.
Wine
seem.
J
A
I
think
this
working
group
should
be
friday.
It
should
be
proud
of
itself
because
we've
progressed
very
quickly.
We
actually
did
good
work
and
and
the
and
the
documents
are
getting
reference.
So
you
know,
as
you
said,
Stephen,
it's
not
failure
its
success.
So
if
nobody
else
has
anything
then
calling
the
meeting.
Thank
you
yeah.
Please
tender
blue
sheets
forward.
