►
From YouTube: IETF93-MILE-20150722-1550
Description
MILE meeting session at IETF93
2015/07/22 1550
A
Okay,
so
I'm
on
we'll
talk
about
his
document
about
three
revisions
published
we'll,
have
a
discussion
about
mutation
report,
which
is
getting
close
to
done.
Rowley
draft
is
nearly
ready
for
working
group.
Last
couple
did
I
promise.
We
probably
should
clipping
the
apps
Directorate,
but
you
probably
should
ask
solids
art
area
Directorate,
about
user
HTTP,
on
the
document
Rowley,
okay,
so
and
on
guidelines
draft
the
panel's
doesn't
have
much
time
to
work
on
it,
but
we
have
a
co-editor
and
co-editor
has
a
source
code.
So
we'll
expect
an
update
soon.
B
Good
afternoon
everyone
Roman
Janeiro,
I'm
going
to
be
talking
about
the
50,
70
bits
and
the
revisions
we've
made
to
it
next
slide.
Please
just
to
orient
everyone
that
might
be
new
to
I/o
defi
to
I/o
defeat.
You
is
primarily
focused
on
revising
a
format
to
help
ceasers
exchange
common
information
that
they
typically
trade,
so
think
incident
reports,
think
indicators
and
at
the
bottom
there
you
see
a
list
of
all
sorts
of
revisions
from
the
base
specification,
50,
70
and
then
some
of
the
other
work
that's
happened.
Kind
of
since
then.
B
That
extends
at
data
model
next
slide,
please!
So,
as
it
looks
I
mentioned,
since
we
got
together
in
gallus,
we
published
three
drafts
and
for
anyone
that's
looked
at
the
minutes.
From
the
interim
meeting
we
had
in
June
I
apologize.
If
some
of
what
I'm
going
to
be
saying
is
a
little
duplicative.
I
gathered
all
the
changes.
That's
happened
you
since
dallas,
not
since
the
inner
meeting
to
present
them
here
for
just
kind
of
helpful
oops
long,
since
we
didn't
have
such
a
great
turnout
for
the
interview
issues.
B
Clothes
I
will
go
into
the
specifics
of
all
of
these,
with
the
exception
of
issue
number
48
and
issue
1
both
of
those
came
up
from
the
conversation
in
gallus
and
where
were
revved
in
dash
12,
and
they
were
primarily
provide
more
clarity
around
what
was
kind
of
in
there,
and
there
was
a
suggested
language
to
put
in
so
I.
Don't
think,
there's
actually
much
discussion
there
well
we'll
jump
into
the
details
of
all
the
rest
of
them
next
slide.
Please,
before
we
do
that
I
just
wanted
or
a
dever
one.
B
We
have
a
running
list
of
all
the
differences
in
50
70
bits
from
from
50-70,
so
things
that
actually
break
compatibility
that
aren't
additive,
and
so,
in
the
last
three
drafts,
we've
introduced
two
additional
things:
they're
incompatible
with
virgin
too.
First
from
the
bottom,
we
changed.
The
format
I
need
to
have
a
hyphen,
and
this
was
just
a
consistency
and
how
attributes
are
named
and
then
the
semantics
of
counter
at
units
changed
and
I'll
explain
how
the
details
of
what
typing
you
now
you
to
give
us
additional
capability
in
the
counter.
So
next
slide.
B
Actually,
quite
a
lot
more
flexible
bless
you
and
we're
doing
two
different
things
there,
so
first
their
support
for
outside
specification.
So
in
the
community
we
have
swig
in
the
community,
we
see
PE
and
so
now
there's
a
way
to
to
to
use
those
outs
outside
specifications,
largely
inspired
by
the
sei
draft,
with
a
way
to
reference,
a
spec
name,
and
then
you
put
the
blob
in
typically
the
XML
or
actually
any
other
kind
of
content
that
you
want
that's
associated
with
either
switz
EP
or
anything
else
from
you
might
want
future.
B
And
then,
if
that
doesn't
work
for
you,
you
can
escape
out
and
just
put
a
blob
of
XML
or
text
that,
hopefully
is
meaningful
to
you,
but
isn't
otherwise
specified
in
the
draft
so
moving
on
to
slide
7.
Now
this
is
issue
48.
We
and
Dallas
talked
about
the
challenge
of
private
extensions,
given
that
we
we
pivoted
from
using
first
all
private
extensions,
then
to
the
N
registry,
then
into
a
hybrid
approach
of
using
both
and
the
challenge
was
voiced.
B
If
I
have
a
private
extension,
how
do
I
know
it's
my
private
extension
or
whose
private
extension
it
might
be,
and
the
thinking
from
that
conversation
was
to
provide
some
way
to
say
this,
this
one's
my
private
extension
inspired,
I.
Think
from
the
discussion
there
was
the
idea
of
a
pen
registry
from
kind
of
IP
fix.
How
do
we
do
something
like
that?
So
what
was
primarily
done
is
cribbing.
B
One
is
private,
enum
name
which
names
the
organization
and
then
should
you
want
to
this
idea
of
an
ID
that
that
organization
that's
named
in
private
enum
name,
can
kind
of
use,
and
that
can
be
two
bales
say
that
there's
different
types
of
private
extension,
this
organizations
publishes
or
perhaps
the
organization
might
want
to
version
them,
but
there
is
that
unique
ID
that
can
be
used.
The
only
downside,
I've
heard
on
this
approach
to
date
is
that
that
this
this
technique
actually
only
allows
you
to
use
one
private
extension
at
a
time.
B
Okay,
on
a
slide
8,
this
is
now
issue
50.
We
had
some
feedback
for
implementers.
That
said,
I
really
love
this
format.
I
really
would
love
to
share
kind
of
indicators
with
it,
but
I
want
to
share
10,000
indicators.
I.
Do
I
really
have
to
wrap
each
individual
indicator
in
all
this
XML
business
to
share
it
well?
Well,
no,
let's
come
up
with
a
better
way
for
that.
B
So
now,
there's
an
escape
in
a
new
class
called
bulk
observables
in
the
in
the
indicator
kind
of
class,
where
what
you
can
do
is
create
that
little
bit
of
XML
and
then
inside
that
bulk
observable
list
put
effectively
effectively
a
blob
of
indicators
specified
by
the
type
attribute.
It's
pretty
much
everything
that
the
iaf
currently
supports.
Fqdn
IP
addresses
ASNs.
The
long
list
is
obviously
the
draft
and
you
can
pretty
much
just
make
a
very
long
list
of
indicators
in
there
with
very
minimal
XML
slide.
So
we're
balanced.
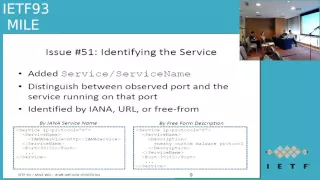
B
Like
nine
issue
number
51,
there
was
concern
about
the
ability
to
convey
what
was
the
observed
protocol,
not
the
port
number
associated
with
that
protocol.
So
there's
this
desire
to
distinguish
between
what
I
saw
on
the
wire
and
what
the
actual
court
was.
So
in
the
first
revision
of
this.
This
showed
up
in
ugly
dash
12
there.
B
The
the
simple
technique
was
diana,
has
a
services
registry.
Let's
just
use
that
so
referencing,
the
I
n
reference
name.
You
could
put
that
in
and
it
should
be
as
simple
as
that.
The
feedback
to
that
approach
was
that's
great,
but
there's
a
whole
lot
of
other
teams
that
aren't
in
that
registry.
How
do
I
reference
those
so
from
the
interim
eating
some
flexibility
got
added
now
and
so
there's
the
ability
now
to
there's
a
more
complicated
class
called
service
name,
which
allows
you
to
specify
a
service
of
protocol
in
three
different
ways.
B
You
can
either
make
a
call
out
to
the
I
n
registry,
we
via
the
I
in
a
services
class,
or
you
could
include
a
URL
that
would
be
I,
guess
an
explanation
of
what
that
service
is
all
about
or
there's
a
description
class
which
is
pretty
much
thinking.
That
is
a
free
form
text
log
to
say
you
know
here:
here's
what
here's!
What
the
protocol
I
think
that
it
is,
is
that
new
class
of
flexibility
cover
everything
that
the
community
might
want.
B
Was
your
idea
yeah?
That's
like
an
so
we're
now
in
issue
52.
This
was
this
was
introduced
to
help
capture
the
idea
of
how
do
I
convey
more
complicated
rates
about
how
things
are
happening.
So
how
do
I
convey?
You
know
Pete
d,
das,
for
example.
What
you
know?
How
would
that
rate
isn't
all
we
were
able
to
do
previously
was
counts
of
things.
So
there
is
some
redefinition
of
the
type
of
the
type
attribute
in
the
unit
attribute.
B
That
will
now
give
us
the
flexibility
not
only
to
give
a
count
what
you
see
there
on
the
left
side
of
how
many
packets
occurred.
But
now
you
have
the
ability
to
say
we
saw
a
peek,
a
peek
rate
of
you
know
in
this
example.
293
megabits
is
that
so
kind
of
giving
me
some
flexibility
with
different
types
of
rates
are
in
there.
So
there's,
like
average
rate
I,
think
peak
rate
and
memory
escapes
me.
What
some
of
the
other
kind
of
rates
are?
B
Okay,
next
slide,
please
so
here
it's
just
that
well
have
a
particular
example.
Latakia
was
really
helpful
in
processing
the
scheming
kind
of
pointing
out
that
there
were
some
gaps
about
how
namespace
was
just
declared.
If
you
try
to
use
the
new
xml
lang,
they
got
dropped
in
I.
Think
in
the
dash
11
draft
G
support.
Internationalisation
wasn't
exactly
right.
So
there's
a
there's,
a
bunch
of
changes,
honestly
kind
of
made
about
how
many
spaces
ratted
and
where
some
of
the
classes
got
dropped.
B
Okay,
so
that's
all
the
things
that
have
been
done
into
completeness
since
we
last
got
together
in
galas.
There
are
four
outstanding
things
that
we
need
to
talk
about,
but
before
I
do
that,
let
me
go
through
another
list,
which
is
my
at
least
my
running
list
of
what
it's
going
to
take
to
to
submit
this
document,
there's
a
bunch
of
different
reviews.
We
want
to
do
and
so
reading
kind
of
from
the
bottom.
The
checks
needs.
Obviously
just
general
polish.
B
You
know
fixed
kind
of
the
grammar,
I'm
sure,
there's
all
sorts
of
formatting
things
we
need
to
talk
through
I
I
also
believe
that
it
would
be
fair
to
reread
a
number
of
the
classes
to
include
some
of
the
classes.
We
didn't
actually
update
to
make
sure
that
they're
consistent
with
the
new
way
we're
using
we're
using
kind
of
io
death
and
just
make
sure
they're
kind
of
clean
and
kind
of
any
place
where
you've
been
reading
stuff
and
you're.
B
B
So
this
brings
us
to
last
for
things
I'd
like
to
kind
of
talk
about
which
I
would
call
the
outstanding
issues.
All
of
them
are
in
track.
So
if
we
can
move
to
the
next
loss,
so
we
got
all
sorts
of
feedback,
not
on
the
how
the
schema
works
or
what's
in
the
schema,
but
actually
how
the
schema
is
is
produced
how
the
scheme
is
architected,
so
get
a
fair.
You
gonna,
basically,
obviously,
there's
a
bunch
of
white
spacing
kind
of
thing.
B
Generators
and
code
generators
have
different
kind
of
flavors,
and
so
the
circuit
has
been
super
super
helpful
and
trying
different
revisions
and
saying
no,
no,
this
one's
still
breaks
make
it
work
this
way,
so
I
think
what
we've
arrived
at
is
something
that
works,
and
this
would
be
a
place
to
get
kind
of
feedback
if,
if
you're
automatically
trying
to
parse
the
schemer
ideas
and
ways
to
make
it
more
readable
in
the
in
the
final
instance.
So
the
declaration
of
elements
will
now
follow
this
convention,
your
which
is
when
you
have
nested
elements.
B
You
have
a
complex
declaration
kind
of
schema,
they're
all
made
by
reference,
so
they
use
kind
of
a
ref
to
call
out
to
another
place
in
the
schema
where
every
element
is
defined,
whether
it's
a
simple
element
or
a
complex
element.
We
previously
were
nesting,
complex
definitions
and
simple
definitions
and
sometimes
not
following
actually
the
new
approach.
So
now
the
schema
looks
in
all
cases
where
the
element
is
is
declared.
It
looks
like
the
new
style
if
you
have
a
preferred
way,
that's
different
than
this
I'd
love.
B
To
kind
of
hear
about
that
I
mean
we're
not
married
to
any
particular
approach
right
now,
the
other
bit
of
feedback
was
declared
attributes
consistently,
especially
the
enumerated
attributes.
So
what
is
done
now
is
that
all
enumerated
attributes
are
explicitly
declared
as
a
simple
type
outside
of
where
they
are
used,
so
they're,
no
longer
nested
definitions
and
they're
dropped
just
in
a
different
place
in
the
schema
and
they're.
All
look
approximately
like
that
on
the
mailing
list.
I
actually
have
a
number
of
questions.
B
Kind
of
referencing
that
specifically
asking
cuz,
you
are
automated
code
generators
going
to
be
happy
with
this
new
approach.
The
other
question
on
the
mailing
list,
related
to
the
Declaration
of
enumerated
attributes
is,
is
twofold.
First,
is
there
a
desire
to
pull
enumerated
attributes
into
a
separate
XML
document
that
is
referenced
by
the
base
specification?
So
we
would
have
the
Declaration
of
the
elements
declaration,
the
attributes,
then
it
would
point
to
all
the
different
enumerations
that
we
have
and
the
driver
for
that
would
be
twofold.
A
A
B
So
at
this
point
they
are
all
pulled
out.
None
of
them
are
nested
definitions.
They
are
not
in
a
blob
at
the
end
of
the
file.
They
are
the
one.
The
enumerated
attributes
that
are
used
in
multiple
places
are
at
the
bottom
of
the
file
and
in
numerator
values
that
are
only
used
once
are
actually
just
what
are
declared
right
below,
where
they're
used
by
the
element,
so
I
mean
that's
another
kind
of
suggestion
to
pull
all
the
enumerated
attributes,
pin
it
to
the
bottle.
B
B
We
have
kind
of
the
discussion
started
on
the
mat
and
list
I
see
at
least
five
different
options
that
there
hasn't
been
kind
of
any
feedback
on
today
we
can
one
and,
on
the
by
the
way,
on
the
mailing
list,
there's
pros
and
cons
to
to
all
of
these
options,
and
so
for
memory
we
can
choose
option
one,
which
is
to
say
we're
going
to
do
nothing.
The
sei
draft
right
now
lets
you
reference
external
approaches
that
talk
about
almost
kind
of
weaknesses,
so
we
could
say
that's
sufficient.
B
We
could
import
the
I,
the
the
weakness
class
from
the
sei
draft
into
the
method
class.
If
we
thought
that
was
important,
we
could
just
say
we
have
the
SEO
drat,
that's
good,
we're
also
going
to
just
put
in
a
free
form
field.
We
could
say-
and
I
guess
I
should
note-
that
options
number
three
four
and
five
are
not
mutually
exclusive
to
option
one,
because
you
can
always
use
option
one.
In
addition,
two
three,
four
five
and
potentially
other
things
are
suggested.
So
do
we
want
to
add
another
free
form,
field?
B
Yeah
cut
you
know
up
up
and
down
on
that
is
he
add,
a
free
form
field,
but
again
machine
parsing.
It's
going
to
be
difficult,
for
we
could
add
in
an
extensible
numerator
value
the
only
kind
of
challenge
there
is.
We
have
to
kind
of
see
that
and
it
be
extensible
in
all
the
different
ways.
All
the
other
enumerated
attributes
are
extensible
and
then
option.
Five
is
a
hybrid
of
three
and
four,
which
is,
let's
just
do
both
so
open
to.
D
E
I
think
this
is
good
idea.
That
heating
is
both
one
on
four
five,
six
or
two
and
four
five,
six
afraid
I
guess.
On
the
other
hand,
number
four
seems
not
so
easy
for
us
to
determine
the
values
of
that
least
I
guess,
because
if
we
know
that
value
already
for
number,
four
people
who
are
working
for
weakness
has
already
listed
by
now,
I
guess
so
going
to
number
three
in
conjunction
with
number
one
and
two
would
be
my
idea.
C
D
B
Middlemost
about
exactly
that,
okay,
so
this
brings
us
to
slide
15
and
issue
number
38,
and
this
one
actually
is
relatively
easy.
Looking
just
looking
for
ideas,
we
have
for
existing
examples
in
in
the
crimp.
In
the
current
document,
there
are
a
little
data
just
in
tone
and
frankly,
they
haven't
been
updated
for
all.
The
different
changes
are
happening
kind
of
an
eye
of
death,
so
the
question
back
out
is
we're
going
to
pull
those
examples
out.
B
We
could
refresh
those
examples,
but
what
do
you
think
would
be
better
and
more
representative
to
put
there
that
would
new
Marie
both
the
pet,
that
we
just
show
examples
of
what
the
power
is
kind
of
iota
for
potentially
show
what
you
think
are
really
common
use
cases.
So
it's
easy
for
implementers
as
the
reading.
The
draft
I
would
posit
I'm
going
throughout
Canada
examples
are
showing
what
is
a
bare
bare
minimum
I,
oh
def
documents,
so
mandatory
classes
only
nothing
else,
and
you
know
that's
four
or
five
lines.
B
I
would
also
say
a
candid
example
is
just
conveying
a
simple
list
of
indicators
with
you
know
very
little
kind
of
context.
Just
to
say,
if
you
wanted
to
just
share
your
txt
file
watch
list-
and
you
know
you
put
it
in
iof-
this
is
how
you
do
it
in
incident
report,
and
this
is
kind
of
where
it
gets
a
new.
B
D
Sorry
so
I
think
that
Kathleen
Moriarty
I
think
that's
a
good
list.
You
could
also,
if,
if
the
guidance
documents
not
going
to
go
anywhere,
you
could
take
examples
from
there
or,
if
you
have
other
ones
to
use,
and
then
incident
report
like
I
think
I'd
probably
want
to
see
real
use
cases
that
we
see
often
right
like
can.
D
B
B
D
E
It's
just
an
information:
maybe
you
know
that
we
have
got
a
new
editor
for
the
guide.
A
draft
from
this
meeting
me
haces
aquí
will
be
working
for
that
and
he
intend
to
include
example
regarding
definite
definite,
instant
information
expression
for
the
document
information
sharing.
They
did
not
use
most
of
their
I,
your
def
field,
so
the
IO
they've
used
for
the
purpose
of
that
definite
should
be
minimal,
so
one
example
could
be
included
in
that
kite
astra
already
by
now.
Okay,
that's.
B
Good
feedback
and
in
hearing
hearing
some
of
this
feedback,
I
aside
there's
another
one,
I
would
ask,
so
we
had
previously
been
doing
full
examples
in
there.
Would
there
be
interesting.
This
is
periscope
question
with
the
with
the
guidance
document.
Would
there
be
interest
in
just
perhaps
including
snippets
that
perhaps
show
how
contact
can
be
used
in
all
the
different
ways
that
it
can
be
gone
to
show
how
some
of
the
indicator
stuff
can
be
done?
B
A
Alex
is
just
speaking
personally,
you
can
spend
as
much
time
on
this.
Is
you
want
early?
So
I
know
that
you
know
some.
You
know
other
working
groups
like
they
have
like
example,
mind
up.
You
know
messages.
This
is
separate
information
on
RC,
so
it
is
an
option.
I
think
it's
sort
of
up
to
you
how
long
you
want
to
wait
for
until
the
this
is
complete.
You
know
I'm.
D
B
Perfect
thanks,
so
this
brings
us
to
related
dns
slide
16.
So
out
of
dallas,
we
had
four
options
about
what
to
do
there
and
so
to
refresh
everyone's
memory.
Related
dns
was
this
idea
of.
We
currently
have
the
ability
to
represent
most
of
an
a
record,
but
wouldn't
it
be
really
great
if
we
could
do
all
the
other
ones,
so
that
turns
out
to
be
fairly
heroic.
We
had
talked
about
four
different
options.
We
said
that
there
was
a
json
representation.
That
paul
did.
That's
that's
option.
One
you
see
listed
there.
B
There
was
there
was
something
on
the
list
about
comma
separated
values
of
dns
fields
and
that
one
was
a
little
under
specified.
There
was
option
3,
which
was,
let's
not
specify
at
all.
Let's
just
say:
that's
additional
data,
that's
for
someone
else
to
kind
of
sort
out,
and
ultimately
the
group
rattling
around
option,
for
which
was
no.
No.
We
really
are
going
to
put
that
in
into
the
spec
and
go
through
the
time
of
working
through
those
classes,
so
that
was
coming
out
of
dallas.
B
There
was
some
delay
and
then
at
the
interim
meeting
we
could
have
talked
about
well.
We
haven't
really
made
progress
from
the
kind
of
the
quick
look
at
paul's
draft,
which
is
option
one
that
just
did
it
in
JSON
and
then
looking
at
can
that
be
made
a
little
simpler.
It
turns
out.
No
it's
actually
fairly
complicated
to
do
so.
The
option
are
really
do.
We
still
want
to
put
it
in
50
70
this
or
do
we
do?
We
could
be
really
revisit
option
3,
which
is
separate
draft
and.
C
And
I
have
had
a
side
conversation,
so
there
is
a
definition
in
weirds
which
is
kind
of
a
automated
who
is
replacement,
which
does
include
a
bunch
of
information
about
dns
and
it
might
be
able
to
do,
and
so
that's
RFC
track.
It
is
JSON,
they
do
have
other
representations,
but
it
might
be
usable
to
crimp
that
data
model
for
dns,
so
I
did
sector
review
on
the
draft.
But
honestly
I
don't
remember
enough
details
to
be
able
to
like
kind
of
just
do
it.
Chris
and
I'll
see
a
kind
of
mill
I.
I
Nicht
ich
I'm
coming
from
dns
land
I
would
say
that
you
really
want
to
throw
away
number
two,
because
a
comma
separated
list
would
just
give
you
a
whole
lot
of
pain
and
you'll
never
be
able
to
end
parse
it
out.
You
really
need
to
have
some
kind
of
wrecked,
like
record
type
to
data
types
kind
of
representation.
B
A
C
B
E
B
D
Does
that
matter
to
folks
in
the
room
like?
Would
you
use
that
separately?
Is
that
something
we
should
progress,
and
does
that
make
it
make
sense
to
have
this
encapsulated
or
do
we
do
it
in
two
formats,
or
we
just
put
it
in
XML
and
we'll
get
used
if
it's
an
XML
Nick
had
a
preference,
so
maybe
I
mean
I'm.
I
Probably
unlike
when,
in
my
day,
job
I'm,
probably
unlikely
to
use
the
the
wealth
of
my
lyric
iota,
but
as
far
as
I
taking
and
continuing
to
use
like
DNS
data
in
JSON,
then
that
is
more
applicable
to
what
I
do
daily.
So
for
me,
in
that
kind
of
like
deploying
it
and
using
it,
and
you
know
pulling
it
in
and
pushing
it
back
out,
and
everything
else
is
more
useful
to
me
in
that
format,
then
having
to
basically
go
and
translate
it
from
XML
and
then
put
it
in
JSON
anyway.
A
A
B
C
A
C
A
C
C
D
And
the
weirds
work
is
done
right.
So
all
of
the
specs
are
published
it's
running
code.
It
hasn't
gotten
too
much
use
yet,
but
there
is
some
use
of
it
at
this
point
and
it's
a
matter
of
population
and
that
could
have
some
advantages
right
because
everybody
in
the
incident
response
base
is
going
to
have
to
switch
over
to
our
deaf
at
some
point
from
who
is
for
some
of
their
functions.
So
there
there
could
be
some
advantages
if
there's
enough
there
or
if
we
just
need
to
update
registries.
Okay,.
A
D
B
D
B
D
I,
you
know
if
we're
gonna
split
it
out
and
we
make
that
decision.
Then
we
make
that
home.
It
has
to
be
an
informed
decision.
So
it's
a
matter
of
looking
at
weirds,
seeing
if,
if
that's
that
might
be
that,
if
that's
there
I'd
say,
that's
probably
the
strongest
answer
rather
than
creating
yet
something
else
sure.
D
D
A
D
B
B
B
If
it's
going
to
be
more
than
that,
then
it's
another
draft
and
that's
what
I
think
we
kind
of
talked
about
at
the
interim
ed
and
did
a
conclusion
kind
of
coming
into
this
meeting
was
it
was
going
to
be
more
than
a
couple
of
inches
to
do
so.
My
recommendation
would
have
been
another
draft,
so
I
feel
like
that's
not.
I
A
metric
for
me,
I,
nicked,
Evie,
and
not
so
much
on
whether
it
should
be
a
document
or
anything
else,
but
just
to
mention
about
weird,
is
and
also
other
things
going
on
with.
The
NSA's
is
probably
weird
already
gives
you
an
extensive
ility
level
extensibility.
It
already
encompasses
a
logic
around
internationalized
domain
names
and
you
know
encodings,
which
I
don't
think
the
JSON
one
does.
So
you
have
those
considerations
as
well
take
into
account,
but
also
because
us
and
everybody
else
world
is
coming
bolting
things
on
a
BGP
and
dns
and
anything
else.
I
A
D
A
B
B
A
B
A
B
I
B
A
A
B
What
will
help
with
that
from
the
group
is
again:
how
do
you
address
this
one,
and
so
this
is
back
to
the
idea
of
how
do
we
deal
with
the
cause
of
the
incident
so
again,
if
anyone
had
a
better
idea
than
one
in
three,
I
think
is
what
we
chose.
We
just
talked
about
reorganizing
schema.
I
have
queued
up
some
of
the
examples
that
we
can
drop
in
I'll.
Look
at
the
implementation
draft
and
put
that
incident
report
come
in
there
and
then
we
just
have
you
tables
are
related
to
us
yeah.
B
E
B
Point
I
haven't
actually
thought
of
that.
Yet
that's
a
good
question,
so
I
think
the
two
things
you
suggested
or
would
the
extension
itself
get
rev
to
make
sure
that
it
can
be
included
in
v2
or
the
question
is:
are
all
the
things
that
are
ready,
inefficient
draft
ending
already
begun
in
in
viju
I?
Don't
know
the
answer
that
I
suspect
you
can't
do
everything
in
v2.
B
All
right,
then,
we're
saving
it
for
a
working
group.
Last
call
and
again,
if
you
could
respond
to
issue
46.
If
you
have
thoughts,
if
you
have
a
code
generator,
please
please
let
you
know
about
issue
kind
of
54
and
if
you
want
to
see
an
example
that
you
think
would
be
really
the
best
way
to
you
know
to
explain:
I'm
def
rebuke,
easy
example.
Are
that
isn't
going
the
implementation
guidance?
Let
me
know
we
could
drop
it
as
one
of
the
four
or
five
that
we
have
in
issue
number
38,
okay,.
C
F
Hello,
DC
desk
me
on
speaking
so
now
Myra
implementation
report.
This
draft
Anna
provides
on
our
friction
about
my
implementations
that
support
an
IO
DF,
including
on
a
propriety
products
and
an
open
source
software.
So
next
slide,
please
so
in
this
an
update
on
this
budget-
and
we
are
now
right
about
an
hour-
support,
opana
isaac,
information
sharing,
an
RC
centers
and
as
it
findings,
and
also
on
a
support
and
other
implementations,
aircel
cyber
fit
and
trend
micro
steering
systems.
F
So
next
I'll
please
so
this
is
used
but
not
doing
enough
these
years,
and
so
in
this
time
I
just
talking
about,
I
suppose
and
other
implementations.
So
next
I'll
freeze,
okay,
so
let's
go
ahead
so
on
sorry.
So
a
pw
j
is
an
anti
fishing
working
group
and
the
biggest
anak
region
when
a
counter
increasing
and
as
they
also
need
this
wanna
direct
and
informations
in
a
structured
way.
So
they
are
using
an
I/o
DF
for
the
reporting,
the
tools.
So
this
is
the
finding
someone
else.
F
Crackling
methodologies,
but
Anna
I'll
DVF
is
the
one
of
them
one
of
supported
format
by
I
ACDC.
So
next
price,
rang
Isaac,
is
an
a
special
interest
group
about
an
hour
research
and
education
network
and
I
us
and
the
designer.
Also
neither
groups
under
they
are
not
really
on
a
similar,
interesting,
a
use
of
an
IDF
and
as
a
not
recommended
to
use
an
io
devo
attach
the
provided
by
the
notification
emails,
so
they
send
you
email
and
the
iod
FF
is
attached
in
the
email.
F
This
is
really
similar
to
when
our
nachos
and
a
CI,
ms
collaborative
ancient
management
systems
I
think
under
so
next
please.
So
these
three
and
isaac
are
not
supported.
I
of
the
EF
and
the
Saudis
are
no
other
implementations
air.
Third,
that
was
not
provided
by
an
asset
of
a
Carnegie
marentina
east
of
the
engineering
students
at
divisions
and
which
was
designed
doing
Auto
Commission's
under
to
Anna
to
correct
the
informations,
and
the
users
in
FML
was
implemented.
A
combination
of
the
sea
on
the
power,
and
maybe
Chris,
knows
everything
yeah.
F
So
next,
please
also,
this
was
an
I
intend,
it
will
rush
scale
distributed
deployment
and
eventually
the
ability
of
two
scientists
data
to
be
shared
across
at
the
meter
domains.
There
are
errors,
so
this
is
my
explanation
of
my
ear
cells.
So
next,
please
so
decent
I,
US
Department
of
Energy
type
of
it
this
one
now
by
an
argon,
National
repertory,
and
that
is
also
supposin.
I
ODF
in
their
systems
under
the
systems
is
a
production.
F
The
automations
autumn
is
something
automate,
friction
automate
converts
and
the
user
ID
message
wrapping
a
xml
extension
to
Anna
manager,
Roger
array
of
indicators.
So
next
please
so
this
on
a
summer.
So
now
these
types
of
document
can
be
showing
Anna
y
ou
D
minor,
implementers,
bhajans
05,
and
so
this
is
an
explanation
about
an
hour
cyber
of
it
so
support
a
multiple
exchange
format,
including
I
winna
six,
so
also
an
io
f-
is
now
one
of
the
supporting
format
by
anna
side
of
it.
Next,
please
so
trend
micro
steering
system.
F
This
isn't
a
BD.
So
now,
maybe
we're
finishing.
Maybe
next
idea
yokohama
sink.
So
next
please.
So
this
is
a
progress
summary
of
progress,
so
we
are
doing
on
a
section,
2
and
Isaac
support
in
design,
io,
TI
IDF
and
a
section
3
with
an
open
source
implementations
and
the
late,
the
agent
and
ifs
CNN,
asking
six
that
this
might
be
almost
done
under
Section.
Four
is
a
bender
implementations,
including
a
propriety
products,
and
a
section
5
is
a
bender
with
prawns
supports
section
6,
another
implementation.
F
So
what
I
want
to
say
then
we
are,
we
is
Orion,
as
he
also
saw
that
this
draft
reason
are
going
to
be
completed,
but
Anna
we
r
vs,
reduces
that
highly
appreciated
to
Anna
your
feedback.
This
types
of
information
in
these
types
of
implementation,
suppose
I
odious,
so
such
kind
of
information
dreary
and
appreciate
it
under
otherwise
we
will
run
on
so
prepare
a
button
on
watch
orosco
because
I.
Now
all
our
image
on
the
position
was
a
dispersion.
F
Dun,
dun,
dun,
dun,
I,
think
and
ongoing
projects
are
just
pushing
20
microts
runs
so
next,
please.
So
this
is
summary
open.
A
history
of
updating
so
based
on
a
draft
amore.
A
team
armed
with
machine
reported,
might
be
an
hour
presenting
I,
give
1889
thanks
and
they
an
updated
on
a
monkey's
and
CMS
and
other
Brava
Brava
Brava,
and
in
this
IDF
and
the
AP
GG
and
ac/dc
realizing
things.
F
G
So
first
I
would
like
to
give
you
short
outlook.
What
I
would
like
to
tell
you
so,
oh
well,
because
the
agenda
has
already
gone
but
never
mind.
I
am
a
researcher
of
the
university
of
applied
sciences
in
darmstadt
and
there
we
had
some
projects
and
yeah.
As
you
might
know,
your
project,
you
have
problems
or
challenges
and
I
would
like
to
give
you
a
short
overview.
What
was
the
problem
I
faced
and
how
I
try
to
solve
it
and
later
on?
G
I
would
like
to
have
your
feedback
and
what
you
think
about
this
work,
and
so,
let's
start
with
who
I
am
my
name
is
jessica
steinberg,
I'm
working
at
university
of
applied
sciences
and
I'm
shut
and
I'm
a
PhD,
an
external
PhD
of
the
University
of
deventer,
so
next
slide
and
I'm
focusing
on
mitigation
and
response.
So
this
is
the
main
topic
of
my
PhD
next
slide.
So,
as
you
might
know,
we
have
some
network
based
attacks
and
I
just
mentioned
one,
which
was
quite
big
in
the
newspapers
or
in
news.
G
So
there's
an
NTP
distributed.
Denial
of
service
attack
so
next
slide.
Please
and
what
we
do
in
our
working
group
is:
we
make
the
detection
of
those
attacks
based
on
flow
based
data,
so
we
have
net
flow
or
IP
fix
and
we
detect
some
kind
of
anomalies
within
this
data
and
you
can
find
some
outliers
and
that's
basically
all
next
slide.
Please
and
what
I
try
to
do
is
to
mitigate
or
react
somehow
on
these
what
they
detected.
So
my
topic
is
not
basically
the
detection,
but
what
is
done
after
this?
G
So-
and
there
are
some
possible
solutions,
for
example
clean
the
traffic
rear
out
the
traffic
and
whatever,
but
another
thing
is
make
people
collaborate
so
next
slide
please.
So
what
I
would
like
to
do
is
make
people
collaborate
in
the
context
of
Internet
service
providers.
I
know
that's
a
challenging
topic,
because
those
people
actually
do
not
collaborate
it
because
of
competitor
stuff-
and
this
is
I,
think
a
known
topic,
but
next
slide
please
next,
so
the
cinema
yo
I
was
focusing
on.
Is
we
collect
the
NetFlow
data
or
the
IP
fixed
data?
G
We
analyze
it
find
some
outliers
within
this
in
this
data
and
then
we
want
to
notify
collaborating
partners.
So
this
is
the
scenario
which
I
tried
to
visualize
here
next
slide,
but
I
didn't
want
to
reinvent
the
wheel.
So
I
just
had
a
look
on
all
these
formats,
which
already
have
been
published,
and
you
find
a
lot
of
them
here
and
then
I
focused
on
intrusion,
detection
and
incident
management
and
I
made
the
survey
I.
G
So
next,
what
we
have
is
kind
of
a
security
event.
It
looks
like
this
so
typical
five
tuple
from
net
flow,
and
we
have
some
additional
data,
for
example,
related
flow
to
this
suspicious
flow
we
detected,
but
we
do
not
have.
Basically
all
these
information.
You
provide
an
iodophor
ID
muf,
so
next
slide.
J
B
G
So
out
of
the
survey,
I
received
the
feedback
that
people
do
not
like
to
change
other.
I
think
the
internet
service
provider
people
do
not
like
to
change
the
network
they
want
because
they
do
not
have
the
resources.
I
am
aware
of
taxi
and
sticks
and
sidewalks,
but
the
feedback
was
that
they
want
to
have
something
that
that
is
easily
2d
boy
and
works
like
out
of
scratch.
That
that's
the
reason
why
I
focus
on
my
messages
and
I
recognize
that
free,
at
least
for
Germany
people
work
on
X
off.
G
G
It's
a
bit
different
to
this
I,
oh
def
stuff,
but
so
this
was
one
which
was
mentioned,
the
most
that
people
are
aware
of
and
it
is
used.
That's
the
reason
why
I
built
this
format
I
use
on
x,
arf,
so
next
slide.
Please
next,
so
I
call
it
flex
because
I
I
think
it
should
be.
You
should
include,
for
example,
IP
fix,
netflow
version,
5
version
9,
maybe
as
flow,
so
it
should
be
flexible
to
carry
this
information.
G
That's
why
it
I
call
it
flex
and,
as
you
can
see
here,
it
has
this
flex
container.
I
will
show
some
pieces
of
our
snippets
out
of
this.
How
it
looks
like,
and
you
can
see,
that
I
added
a
mime
signature
and
it's
encrypted,
because
I
thought.
Okay,
we
will
have
this
privacy
issue
and
people
do
not
want
to
share
actually
netflow
or
raw
NetFlow
data.
So
if
you
have
a
trusted
partner,
you
should
it
should
be
somehow
secured,
and
I
used
the
transport
smtp
because
it
is
available
in
all
of
the
sides
and
stomp.
G
G
What
kind
of
flow
information
I
am
going
to
transfer?
Which
version?
Do
I
have
additional
detection
field?
That
means
m-maybe,
the
detection
engine
is
able
to
provide
me.
Is
there
not
behind
this,
this
network
or
whatever?
So
I
can
add
additional
detection
fields,
detection,
engine
fields
and
for
some
reason
it
might
be
interesting
to
have
more
than
just
one
flow,
and
you
can
have
correlation
correlate
flows
inside
this
as
well.
G
The
Excel
format
it
was
mentioned
so
I
just
used
it
for
flex
as
well.
Basically,
the
difference
between
X
6
f
is
x,
is
x,
6,
I've
and
flex
x.
6
f
has
three
containers
and
you
have
three
times
the
same
information
and
I
thought.
That's
not
needed
and
I
skipped
it
and
I
had
this.
This
kind
of
representation
for
flex.
H
H
D
H
Firstly,
I
I
just
say:
I
like
your
idea,
because
we
also
have
the
same
idea
by
extended
or
by
using
the
IP
fix
to
to
collector
the
network
flow
information
to
help
to
detector
the
network
attacks,
and
we
also
have
some
chapter
I
have
went
after
in
dos.
We
can
group
so
I
think
we
really
need
the
discard
later.
Okay
and
then
I
have
several
questions
and
foster.
H
Is
that
that's
your
research
include
the
content
that
how
to
what
information,
what
net
flow
information
should
be
concluded
and
can
be
used
to
detect
actor
the
network
attack?
This
is
the
first
one
and
the
second
why's
that
I'm
not
a
very
sure
that
what
is
your
current
information
motor
or
your
current
content,
to
be
sended
between
the
different
elements.
Is
this
page?
Is
your
define
the
syntax?
Oh,
oh,
oh
because
I
have
seen
the
iod
f
syntax
in
your
previous
failure.
So
that's
this
dress.
Alexandra
is
not
your
proposal.
H
G
G
H
I
prefixes
latest
abortion,
so
we
as
we
are
in
the
ITF.
We
have
the
chance
to
extend
it,
that's
our
work,
so
I
think
that
smoke,
maybe
more
more,
more
more
appropriate
yeah.
We
can
discuss
yeah
yeah
and
the
man
made.
My
first
question:
have
you
done
some
study
on
what
information
can
be
used
for
the.
H
G
G
I
G
I
G
I
G
G
I
would
like
to
have
a
PhD
which
is
from
from
practical
value,
and
so
when
I
receive
the
third
or
false
rejection
from
a
conference
from
the
science
scientists
group,
then
I
decided
okay,
ask
kathleen
if,
if
this
work
is
worth
to
present
somewhere
else-
and
she
told
me
okay
go
to
a
mile
and
discuss
about
your
work
and
let's
see
what
the
people
think
about
it.
So
that's
why
I'm
here.
D
I
Nicht
ich
I
was
just
gonna
ask
as
far
as
it.
I
think
it
for
me.
It's
the
word
collaboration
because
I'm
trying
to
understand
what,
because,
if
it's,
if
you're
using
d
das,
is
an
example
right
usually
for
collaboration,
it's
a
case
it
because
you
want
it
to
stop
yeah.
So
if
you
can't
communicate
it
till
after
the
factor.
Now
all
your
analysis
and
it's
already
gone
away,
then
the
collaboration
is
questionable
as
to
what
you
know
what
you
can
achieve
from
it.
I
Similarly,
if
you're
with
d
dose
as
well,
so
many
things
spoofing
everything
else
that
flow
data
has,
you
know,
I
mean
half
the
time.
You
just
want
to
say
it's
an
NTP
attack
and
then
just
block
all
ntp
coming
in.
So
that's
where
the
collaboration
thing
I
suppose
I
could
have
some
I,
don't
have
Delta
I'm,
just
like
I
just
want
to
understand
what
you
you
know
what's
at
either
end
of
the
collaboration
and
but
during
what
time
frames
does
it
occur?
And
so
what
do
you
try
to
coordinate
with
it?
I
guess
is.
G
What
I
would
like
to
do
is,
for
example,
in
my
network,
I,
acted,
detect,
something
suspicious
and
then
I
can
inform
the
other
collaborative
partners
and
that
that
this
kind
of
approach
moves
to
a
proactive
approach.
But,
for
example,
if
if
in
the
network
a
you
detect
this
attack-
and
he
does
not
receive
any
peaks
or
stuff
like
this
right
now,
but
maybe
later
on,
because
it
is
a
scan
out
of
this
list,
then
he
might
already
have
some
configuration
and
does
not
get
these
effects
inside
its
own
network.
So
I
think
that's
worse.
D
Kathleen
Moriarity,
so
thank
you
very
much
for
coming
and
speaking
and
sharing
these
ideas.
After
doing
all
of
your
research,
I
think
that
there's
definite
value
at
least
because
you've
done
work,
a
value
in
in
your
collaboration,
because
you've
done
this
work,
we've
done
research,
you've
experimented
a
bit
and
I.
Don't
know
what
would
happen
with
your
exact
work.
D
Yet
I
think
more
discussion
would
be
needed,
might
also
be
worth
figuring
out
if
there's
any
plugins
with
what's
happening
with
XRF
already,
since
that's
used
by
the
marf
and
was
it
was
out
of
the
marf
working
group
and
it's
used
by
the
mall
community,
it
our
plug
in
there,
because
that
would
be
a
very
direct
fit.
Is
it
more
alike
the
work
that's
happening
here?
There's
other
protocol
proposals
and
maybe
there's
some
way
you
plug
into
that
work,
but
you're
also
trying
to
get
a
PhD.
D
So-
and
this
is
this-
is
your
project
for
that
right,
so
I'm,
just
hoping
you
know,
a
number
of
people
said
that
they
would
work
with
you
and
I'm,
hoping
that
that
helps
to
generate
some
ideas,
because
you've
done
practical,
hands-on
work,
but
all
the
folks
has
stood
up
it
to
ask
questions
and
say
they'd
like
to
collaborate
with.
You
have
also
right
so
so
I
think
you're
doing
some
good
good
work.
It's
appreciated
and
I
s
I
asked
to,
for
you
know
those
collaborating
with
her.
D
If
this
isn't
going
to
go
forward,
can
we
help
her
with
ideas
of
what
would
be
useful
because
she's
gone
down
this
path,
she's
in
this
space
and
maybe
there's
something
we
can
help
her
with
as
well,
and
she
could
simultaneously
help
us
with
some
aspect
of
work.
That
would
be
productive
and
maybe
you
have
specific
feedback
from
Germany.
That's
helpful
to
the
group
as
well
right,
so
I
think
that's
one
of
the
benefits
of
this
group
and
you
can
see
from
all
the
folks
standing
up
throughout
the
meeting.
D
A
And
the
other
thing
from
the
male
perspective,
if
you
know
you
try
to
use
I'll
def,
so
if
there
are
any
things
that
you
think,
I'm
missing,
I
think
we're
probably
a
good
point
to
fix
or
add
stuff
if,
if
it's
not
low
hanging
fruit,
hopefully-
and
so
thank
you
at
this
point-
I
think
we're
done
any
other
business.
Any
other
comments,
announcements,
alright,.
