►
From YouTube: IETF93-OPSAREA-20150720-1740
Description
OPSAREA meeting session at IETF93
2015/07/20 1740
A
Microphone
I
guess
project
pretty
well
in
here
anyway.
Oh
yes,
let's
put
the
phone
right
next
to
it
too
yeah
the
operations
and
management
area
meeting.
It
is
also,
curiously,
the
joint
meeting
with
the
ops
AWG,
which
is
actually
not
meeting
this
time.
So
therefore,
we
have
an
agenda
item
that
comes
from
them,
so
I'm
Julie
egli.
This
is
Benoit
clays
or
your
friendly
neighborhood
area
directors.
A
A
So
the
plan
this
time
is
to
bash
the
agenda,
look
at
some
notable
events
and
then
we
have
three
presentations
and
a
brief
discussion
of
the
pen
practice
and
I
in
a
registration
document
in
the
queue.
This
is
estimated
to
take
something
like
45
minutes,
so
there
is
room
for
commentary
and
we'll
move
on.
A
A
I
took
one
document
under
my
wing
to
be
ad
sponsor,
so
I
think
we
should
congratulate
ourselves
for
tying
off
loose
ends,
leather,
rather
than
leaving
them
dangling,
and
I
think
that's
it
and
we
can
move
on
to
actual
items,
so
I
think
Doug
goulash
is
going
to
be
Doug,
Doug,
gosh,
gosh.
Sorry,
it's
going
to
be
the
first
presenter
on
textplus
and
and.
B
A
A
C
Yep,
first
of
all,
is
actually
multiple
people
presenting
so
I'm,
just
during
the
first
part
of
the
presentation
and
then
I
hand
over
to
Mike
to
Douglas
will
finish
and
then
all
three
of
us
can
actually
answer
all
the
questions.
People
either
might
have
yes,
so
we
are
try
together
with
that
three
people
in
square
yeah.
Thank
ya.
A
D
C
So
roughly,
what
I'm
going
to
talk
about
is
what
we
want
to
do
and
why
we
want
to
do
it
and
then
Douglas
and
Andrea
can
talk
about
how
we
planning
to
do
it.
It's
hopefully
pretty
straightforward
arm,
so
I
actually
hope
that
we
can
spend
the
most
time
on
like
discussions
and
comments
and
not
really
with
like
slide
presentation.
Powerpoint
karaoke
stuff
connect.
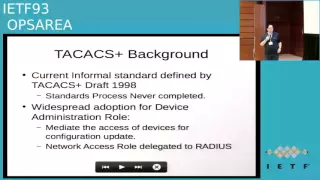
Next
slide,
please
a
little
bit
of
background
for
people
that
are
not
that
familiar
with
textplus.
C
It's
actually
was
a
quite
old
draft
from
98
that
was
a
bit
of
IDF,
but
it
never
made
it
to
senate
at
state
a
draft
for
whatever
reasons,
and
we
decided
that
we
want
to
finish
the
job
that
people
started
back
in
98
and
finally
just
make
it
a
standard.
So
that's
one
of
the
main
motivations.
Why
I'm
here
today
and
you
know
the
other
guys
as
well
of
course,
so
one
of
the
main
things
actually
is
that
the
two
original
orders
from
the
draft
from
98
I
still
listed
as
co-authors
of
the
current
draft.
C
D
C
C
C
C
A
C
It's
also
probably
worth
mentioning
that
this
is
actually
a
joint
effort,
because
Douglas
actually
works
for
cisco,
where
the
two
of
it
rogers
used
to
work
back
98
as
well
and
andrew
massive
work
for
google.
So
this
is
like
not
a
single
person
effort
and
we
actually
had
quite
a
very
good
collaboration
between
just
like
google
on
this.
So
what
we
actually
try
to
to
do
mainly
is
let.
D
C
Yes,
that
actually
what
I
meant
like
the
three
of
us
at
the
pretty
good
collaboration.
We
just
accidentally
work
for
different
companies,
but
it
has
actually
nothing
to
do
with
the
motivation
of
what
we're
doing
here
and
also
like
the
main
focus
for
tag.
Xd
stays
for
us
actually
is
authentication
on
devices
itself.
So
basically,
if
your
network
engineer,
you
want
to
connect
your
router,
you
switch
and
then
authenticate
yourself.
That
was
like
what
we're
really
looking
for
here
and
I
think,
if
we
can
get
our
presentation
back,
I'm
ready
for
the
next
slide.
C
Motivation
on
why
we
do
this
well,
as
I
said,
it's
actually
a
draft
still,
and
we
just
really
want
to
have
a
standard,
because
it
makes
a
lot
of
things
much
much
easier.
We
have
like
an
accepted
standard
than
just
a
very
old
draft
document
floating
around
in
the
internet.
A
lot
of
people
still
think.
Actually
it
Cisco
proprietary
protocol,
which
is
not
true.
C
F
So
I
thank
south
austin
and
kudos
for
kids
kick
starting
the
process
of
getting
the
standard
standardized
of
a
draft
standardized
it
honestly.
We
were
gonna
get
around
to
do
it.
I
heard
his
18
years
ago,
but
it
was
definitely
on
the
agenda.
So,
as
thorson
mentioned,
the
primary
focus
is
to
make
sure
that
the
tax
bus
protocol
and
does
achieve
as
RFC
status
if
possible.
F
But
while
we're
doing
this,
we
do
want
to
address
issues
that
may
be
really
definitely
do
need
to
be
addressed
in
one
of
those
is
the
encryption,
so
the
packets
plus
protocol
does
actually
have
a
formal
encryption.
That's
based
on
mp5,
it
is
the
agile
implementing.
That's
used,
does
have
some
design
flaws
and
it's
very
much
regarded
now
pretty
much
as
clear-text.
F
Obviously,
one
thing
that
is
important:
you
know
that
there
is
a
lot
of
use
of
tax
out
there.
So
from
the
point
of
view,
this
standard
of
this
time,
we
didn't
want
to
invalidate
that.
So
from
that
perspective,
you
know
that
that's
why
we
went
for
the
it
had
to
be
backwards,
compatible
that
next
slide,
please.
F
F
The
approach
that
we
actually
went
for
was
for
start
TLS,
at
least
that
I
should
say
the
approach
we
went
for
in
the
first
draft
was
start
TLS,
there's
a
couple
of
aspects
of
the
tax
protocol
which
do
lend
itself
more
to
this
direction,
or,
let's
say
they
mitigate
some
of
the
issues
that
will
come
up
with
with
start
TLS.
One
thing
with
tech
axe
is
the
pair's
the
client
and
the
server
both
have
pretty
full
configuration
of
each
other.
So
the.
F
Letting
you
finish
the
slide.
Okay,
so
they're
going
to
be
the
devices
that
are
being
configured,
they
were
actually
configured
specifically,
which
service
to
use
but,
more
importantly,
the
service
have
the
full
list
of
all
the
clients
I.
So
from
that
perspective,
we're
not
using
start
TLS
for
a
service
discovery
or
for
the
case
of
the
optional
security,
but
actually
it's
just
a
way
of
switching
on
or
off
TLS
on
the
same
port.
D
Skarner,
since
this
is
the
ops
area
and
ops
area
working
group,
there's
certainly
an
operational
advantage
to
having
a
separate
port,
because
then
you
can
enforce
it
at
the
network
layer
and
having
been
bit
really
bad
by
a
vendor
protocol.
It's
not
using
a
separate
port
at
Harvard,
where
it
turned
out
that
all
of
the
communication
was
in
clear
text,
because
the
server
refused
the
clients
request
for
encryption,
and
yet
nobody
knew
that
I
would
urge
serious
consideration
of
a
separate
court.
I.
F
Think
that
certainly
is
the
of
the
of
the
cleanup
and
the
various
changes
were
made
to
do
the
specification.
One
thing
we've
got
most
comments
on
is
whether
to
use
start
TLS
or
a
separate
part
in
the
first
revision
of
the
draft.
We
did
use
start
TLS
I
think
that
on
the
next
revision
will
probably
you
know,
look
to
see
we
can
get
the
you
use
the
correct
solution
and
there
may
be
on
the
third
one.
G
Mack,
unlike
Scott,
wearing
a
a
transport
Directorate
hat,
got
a
bunch
of
scars
from
exactly
this
issue.
In
the
port
used,
wrap
and
Scott,
you
didn't
see
half
of
a
the
email
that
hit
main
box
on
this
good,
so
Scott
Singh
the
operational
perspective.
Allow
me
to
add
two
more.
The
security
perspective
effectively
defers
to
what
you
just
described,
to
the
extent
that
a
single
port
and
start
TLS
makes
sense
for
your
protocol.
That's
fine
and
the
transport
to
our
perspective
is
one
less
part
is
one
more
part
of
other
people,
and
that
would
be.
G
A
Yeah
I
mean
it
Joey
ugly,
with
a
non
ad
hat
on
I.
Think
there's
an
advantage
that
is
conferred
by
being
able
to
say,
oh
by
the
way,
I
only
accept
TLS
from
you
in
your
configuration
and
then
so
this
can.
This
has
a
slightly
different,
maybe
a
problem
space
that
does
say
client
and
servers
that
are
not
already
have
having
mutual
configuration
for
each
other,
so
that
may
confer
a
benefit
or
it
may
be
undesirable,
but
the
nice
part
about
a
standards
action
is
you
don't
actually
have
to
go?
F
F
The
slight
disadvantage
of
them
is
that
there's
one
single
namespace,
which
is
pretty
much
unregulated.
This
makes
it
pretty
productive,
it's
pretty
straightforward
to
add
the
attributes
as
needed,
but
there
is
the
issue
with
conflicts
for
potential
different
meanings,
the
same
attributes
from
different
vendors,
and
so
from
this
respect.
It's
it's
an
open
question
that
we
have
and
it's
not
something
we
actually
covered
in
the
first
version,
but
it
is
certainly
something
that
we
intend
to
look
at
in
within
the
next
version.
F
If
we
could
get
it
I
think
as
a
standard,
then
you
know
it
may
be
more
universally
deployed
and
I
think
that
that
would
make
sorry
and
that
might
make
the
the
job
for
organizations
as
they
implement
their
device
administration
policy
simpler.
So
that's
the
reason,
for
my
main
reasons
that,
with
you
know,
resurrecting
out
the
tech
x
protocol
and
hoping
to
moving
forward
from
our
singing.
H
H
I
mean
my
two
cents
on
this.
We
already
have
to
triple-a
protocols
if
this
is
an
individual
submission
and
an
informational
draft,
great,
not
yourself,
but
the
only
reason
that
radius
doesn't
do
device,
authorization
or
command
authorization.
Is
the
vendors
have
refused
to
implement
it
or
sand
realizing,
and
that
would
be
rather
less
work
than
coming
up
with
a
new
protocol
and
with
the
extensions
we've
had
to
radius
with
TLS
transport,
increased
attribute
size,
increased
attribute
space,
there's
no
technical
reason
why
any
of
that
could
not
be
done
in
an
existing
protocol?
H
F
A
So
I
mean
I,
yeah
I
mean
I,
have
a
vantage
point
here
as
an
operator
and
I.
Think
I
saw
the
motivation
of
this,
as
is
not
bringing
say,
a
lot
of
work
related
to
tak
kak,
X
plus
to
the
ITF,
but
more
they're.
People
who
use
it
today
who
have
interoperability
problems
because
of
their
vendors,
don't
implement
tak,
X,
plus
in
precisely
the
same
way.
H
A
Yeah
no
I
completely
agree
yeah,
it
also
had
I
mean
diameter
and
so
on.
Right
I
mean
you
know,
I
think.
So.
The
motivation
of
this
really
is
like
to
roll
a
clock
back
to
nineteen
ninety-eight
kind
of
and
say
well
the
version
of
the
protocol
that
was
there-.
The
stuff
that
turns
out
to
be
super
evil
is
just
the
one
that
actually
exists
out
there
and
I
wouldn't
have
I,
have
a
lot
of
trouble.
Imagining
like
a
lot
more
work
than
that
coming
out
of
this.
H
A
A
F
I
F
A
A
K
D
B
Okay,
I'm
and
de
volta,
the
third
quarter
or
fifty
bent
on
how
we
planted
Scott.
Thank
you
for
actually
addressing
and
giving
part
of
my
answer
back
always
feels
good
to
have
somebody
else
answer
for
you,
I
think
one
part
is
I,
don't
see.
This
is
the
third
protocol.
I
see
this
as
a
widely
deployed
current
protocol,
which
has
a
lot
of
issues
because
it's
never
been
formally
standardized.
This
is
something
that
we
act
since
end
of
90s
and
comparing
to
other
protocols
triple-a
protocols.
L
L
B
We
are
looking
for
consensus
through
the
idea,
because
this
shouldn't
be
addressed
and
cannot
be
addressed
by
a
single
vendor,
because
there
are
differences
on
the
ground
and
when
disambiguating,
some
of
the
points
we
would
expect
and
wish
for
a
group
of
people
to
actually
explain
what
the
differences
are.
Weather
problems
is
and
find
a
consensus.
What
to
put
in
protocol
while.
L
Just
to
go
on
this
one,
one
of
the
Assumption
here
is
that
you
would
like
to
have
backward
compatibility
with
existing
deployment,
because
you
are
seeing
that
it
is
something
widely
deployed
and
the
fact
that
you
cannot
ensure
that
what
would
be
done
in
any
working
group
within
IDF
will
fit
with
what
is
already
deployed,
because,
if
I
decide
and
if
there
is
a
consensus
that
this
update
will
be
good.
But
it
conflict
with
the
existing
deployment.
We
don't
even.
We
are
not
to
ensure
that
this
could
be
applicable
in
the
field.
L
So,
based
on
that
and
based
on
other
experiences,
I
would
say
that
for
other
protocols
defined
in
IDF
and
other
protocol
was
defined
by
thunder
having
something
terrifying
in
a
draft
reviewed
by
ATF
and
so
on.
Explaining
how
we
should
use
the
ax
today,
with
maybe
some
clarification
and
even
some
proposed
enhancement
of
the
protocol,
but
without
defining
a
new
standard
protocol
was
before
that
would
be
acceptable.
So
would
mean
that
having
something
informal,
informational
with
a
wide
review
from
a
GF
folks,
it
will
be
acceptable
because
otherwise
I
think
it
would
be
even
contradictive.
L
B
A
As
much
as
hold
on
yeah
I,
don't
think
we
I
don't
think
we
need
to
explore
that
area
too
much.
Yet
I
think
that
is
actually
a
question
for
the
working,
but
I
think
one
of
the
things
that
I'm
going
to
want
to
hear
from
is
implementers
I'm
about
this,
because,
obviously,
if
you
have
to
dust
off
code
that
you
last
touch
in
2004,
you
know
that's
going
to
alter
your
opinion
of
this
a
little
bit.
A
J
B
All
right
so
I'll
be
giving
an
update
on
the
yang
model,
a
commission
group,
so
it
would
be
kind
of
stuff
to
stand
the
pink
square
and
look
in
the
screen,
so
sometimes
you'll
see
my
back
alright,
so
first
light.
So
what
is
this
that
this
is
Directorate
reporting
the
up
Sadie
by
the
way?
Who
knows
about
this?
This
directory?
B
Ok,
a
few
Oh.
Quite
a
few
people?
Ok,
very
good!
So
we
are
actually
four
in
there.
We're
spending
one
third
of
our
time
on
yang
modeling,
young
models,
coronation
and
everything.
So
it
started
it
like
in
February.
We
have
people
for
one
year
and
the
goal
is
help
with
development
condition
of
the
numerous
yang
models
within
the
ITF
and
the
promotion
of
yang
modeling
in
the
industry.
Alright,
so
in
the
next
two
slides
I've
got
basically
a
high-level
description
of
what
the
job
is.
I
won't
spend
too
much
time
here
for
two
reasons.
B
First
of
all,
it
was
more
beneficial
for
the
scrub
discuss
back,
express
so
I'll
squeeze
this
session
and
second
of
all,
I'll
be
repeating
that
in
net
mod,
so
net
mod
is
only
about
yang
models.
Arguing
more
details
here:
this
is
to
address
the
broader
audience,
so
good
next
slide,
so
compelling
publishing,
maintaining
inventory,
documenting
discussions,
participating,
etc,
next
slides
and
the
next
one.
B
Now,
if
we
learn,
if
we,
if
you
look
at
this,
we
could
work
in
phases
right.
The
first
one
is
to
list
all
the
young
models
and
we've
got
money
all
over
the
place.
The
phase
number
two
is
well
tuning,
I
mean.
If
you
want
Yankee,
be
a
success.
We
must
have
the
associated
tools
right
next
is
we
need
to
help
people
with
the
compilation
you
see
numbers.
We
still
have
a
lot
of
young
models
that
don't
compile.
Well,
then,
training
is
the
next
thing
I'll
address
that
an
education
by
the
way.
B
Now
there
is
also
the
notion
of
combination
across
SDOs
and
open-source
you'll
see
we'll
have
plenty
of
yang
models
in
open
source
as
well,
then
I've
been
asking
what
to
study
dice
first
in
terms
of
yang
models,
you'll
see
that
and
finally,
the
model
condition
within
the
ITF.
So
the
first
one
the
list
of
young
models
during
the
hackathon.
We
generated
this
figure
by
the
way
you've
got
all
the
URLs
at
the
bottom.
B
So
what
we
see
is
a
growing
number
of
yang
models,
150
right
now
right
up
to
250,
because
there
are
some
other
examples,
some
that
don't
extract
correctly
etc.
So,
what's
interesting
is
that
the
the
green
curve
is
the
one
that
compile
without
problems
without
any
way,
without
even
warnings,
the
red
one
is
with
warnings
all
right.
So
somehow,
if
we
want
to
be
successful,
all
these
should
be
compiling
without
errors.
Okay,
so
the
new
tests
there
with
the
arrow
is,
whenever
im
a
distinction
between
errors
and
warnings.
B
Does
the
IP
hang
patch
is
something
that
we
patch
in
hackathon
to
improve
their
own
message
and
because
we're
working
on
yang
won
at
one?
There
are
errors
that
we
should
not
pay
attention
to
any
longer
and
the
third
one
the
yang?
Well,
you
later
is
an
online
tool
that
we
put
the
web
so
I'll
cover
that
as
well.
B
Yes,
so
if
I
look
at
numbers,
I
mentioned
between
1
and
50
and
250
yang
models
in
the
ITF
right
I'm
collecting
the
yang
models
from
the
MAF
right
now,
they've
got
to
standards
already
they've
got
five
existing
documents,
I,
don't
know
how
to
call
that
I
think
draft,
or
something
like
that
on
the
next
slide,
I'm
compelling
also
that
you
want
them.
I,
Triple
E,
because
you
see
I
mean
it's
not
only
the
ITF,
its
many
different
SDOs.
B
Ok
right
now
they
don't
compile,
but
it
doesn't
matter
to
start
with
right.
It's
a
stupid,
utf-8
error
in
that
situation.
No
big
deal
opendaylight
473
young
models
right.
So
do
you
see
why
this
Directorate
is
very
important
to
make
sure
that
we
coordinate
across
open
source
msdos?
If
you
want
to
play
with
you,
choose
I'm,
creating
the
tar
file
with
all
the
young
models
that
you
can
import
everything
directly.
Ok,
next
slide
tooling.
B
At
the
last
hackathon
we
created
to
to
to
extract
the
young
models
directly
from
ITF
dress
and
we're
using
that
to
extract
and
okay
second
bullet
point.
We
just
post
it
on
the
web,
the
yang
body
data
in
there
you
can
post
your
draft
and
you
would
we
extract
the
young
model
and
compile
them
right
seaweed
care
directly.
Get
the
error
messages
from
the
compilation
we
were
trying
to
work
on
integrating
this
directly
in
ID
Nets
during
the
hackathon,
its
work
in
progress,
we're
working
with
Henrik
from
the
two
sides
we
need.
B
During
the
hackathon,
we
have
a
young
Explorer,
that's
a
GUI
in
which
you
could
load
your
yang
models
and
that
will
show
you
directly
the
RPC,
the
RPCs
in
net
Andres
conf.
You
will
find
them
of
it
during
the
bits
and
bytes
look
at
the
hackathon
table
very
interesting.
If
you
want
it
to
even
do
testing
of
network
elements
right.
B
B
We
improve
peeing,
okay,
I'll
skip
a
detail
for
that.
It
will
be
a
discussion,
mad
mods,
okay,
next
slide,
and
what
we
produce
is
every
single
drive
there
that
has
got
a
young
model.
You
will
see
yang
model
draft
compilation,
errors,
review
your
draft
and
make
sure
that
you
compile
the
yang
models.
Compile
correctly
looks
like.
B
And
by
the
way,
we've
got
this
yang
eating
advice
session
on
sunday
at
each
ITF.
It's
like
free
young,
consulting
right,
come
with
your
yang
models.
We
will
give
you
advice.
Okay,
next
one
trang,
we
have
a
training,
it
will
be
online.
Two
weeks,
it's
on
yang.
It's
on
that
comp.
We
made
a
mistake.
There
is
that
we
call
some
a
professional
service
to
make
a
very
nice
training
and
we've
been
delayed
by
three
months,
so
I'm
hoping
it
would
be
perfect
intern
medication.
There
is
like
one
draft
which
isn't
on
the
classification.
B
We
have
many
different
types
of
young
models,
standard
provider,
extension
generated,
etc.
In
this
draft
we
want
to
explain
all
this.
It
will
also
help
was
the
discussion
with
a
different
SDOs
right
next,
like
all
right
on
the
second
bullet.
I'm
tracking,
what's
happening
in
terms
of
yang
models
throughout
the
industry
feel
free
to
review
that
we're
involved
with
the
mes
were
involved.
I
Triple
E
I
have
interests
from
BBF.
Now
they
want
to
have
like
a
young
doctor
for
more.
You
know,
10
ones.
B
Excite
now,
with
my
ad
hat
on
I've,
been
asking
all
the
operators
that
are
working
the
ITF.
What
yang
model
should
be?
Should
we
be
working
on
first
right
because
it
was
a
pile
of
them
and
to
try
to
summarize
this
in
one
sentence?
This
is
basically
all
that
we
need
to
create
an
l-3
p.m.
and
by
the
way,
there
is
no
trippy
and
service
module
working
group
right
so,
and
we
know
which
young
modalities
are
like
interface
done
right.
Vrf
a
nexus
is
to
kill
us
all
the
routing
ones
right
away.
I'm,
ideally.
B
C
B
B
So
if
I
have
to
rate
us
on
a
different
faces
and
by
the
way,
it's
part
of
our
charter
that
we
have
to
give
like
regular
status
status
updates.
So
I
would
say
the
list
of
young
mothers.
Were
there
the
tooling
its
ongoing
right?
Will
you
will
see
more
tools
as
we
go,
the
help
is
compilation.
You
see.
The
curve
is
going
up
as
soon
as
will
have
the
gang
in
the
ID
in
it
I'm
sure
to
be
taken
care
of
training.
B
It's
almost
done
coronation
of
difference
deals,
that's
a
topic
which
is
top
of
my
mind.
We
just
get
up
again
yesterday
was
the
IP
Polly
liaison
person
than
on
a
scanner,
so
on
going
getting
their
priorities,
it's
almost
done.
If
we
achieve
in
let's
say
a
year
maximum
to
you
know
being
able
to
configure
in
at
3pm,
that
would
be
great
and
the
model
condition
inside
the
ITF.
I
would
say
it's
a.
B
We
should
do
more
again.
This
morning,
we
we
saw
like
a
couple
of
eternal
related
young
model
draft
right.
Why
do
we
have
some
money?
We
should
we
should
do
it
once
right
and
I
think
the
last
slide
is
any
questions
and
by
the
way,
if
you
interested
to
join,
but
there
is
a
time
commitment
link
to
that
and
mailing
list
is
open,
but
we
have
just
a
meetings
between
us
like
WebEx
meetings.
So
any
question
answer
please.
E
B
Separate,
for
example,
from
the
I
Triple
E
I
take
this
one
public
directory
from
Mei
from
github.
It
would
be
great
if
you
would
have
a
single
github
for
all
the
young
models
in
the
world,
practically
I'm,
not
sure
if
it's
going
to
happen
so
ideal.
For
example,
we
discussed
with
don
omar
scanner,
but
actually
it
would
be
great
if
you
could
have
one,
but
there
are
some
implications
about
I
PRN
read
the
boilerplate
and
something
like
that
to
be
worked
on
right.
B
D
You
don't
have
to
go
back
to
the
source
and
work
on
it
there,
because
it's
it's
in
process
until
it
gets
to
be
an
internet
draft,
it's
different
in
other
skaters
bodies
where
they
might
not
have
a
public,
publicly
accessible
draft
working
working
group
document.
So
in
that
case,
going
straight
to
the
source
like
github,
would
be
more
useful.
F
M
Anyway,
I'm
tim
was
in
ski
I'm,
one
of
the
co-chairs
of
DNS
op
Suzanne
was
supposed
to
do
this,
but
she
had
other
IAB
things
to
do
and
Joel
ask
me
I
think,
because
in
the
last
six
months,
we've
moved
a
lot
of
stuff
through
the
working
group,
probably
for
the
first
time
in
a
while
that
and
he's
sort
of
so
pleased
by
that
much.
He
wanted
me
to
come
up
and
sort
of
speak
about
it.
M
M
Some
of
these
are
sort
of
updates
that
we're
doing
an
update
on
5966
biz,
which
is
about
TCP
implementations,
which
is
becoming
very
interesting
along
in
the
d
Pryde
group,
which
is
doing
a
lot
of
stuff
at
els
in
terms
of
privacy
and
confidentiality,
and
the
tcp
keep
alive
draft
is
very
much
tied
to
that
as
well.
It's
what
we
see
more
people
doing
TCP
type
situations
where
they
want
to
sort
of
do
lots
of
lots
of
packets
back
and
forth
the
Dina's
cookies
and
the
queue
name.
Minimization
are
both
slight
protocol
modifications.
M
Keyname
minimization
is
a
confidentiality
he
/
privacy
attempt
to
drop
the
fully
qualified
domain
name
when
you're
doing
queries
all
the
way
to
the
root
and
the
cookies
one.
Is
it
temp
to
do
small,
DNS,
cookies
between
client
and
server
as
a
way
of
handling
or
add
wrestling
sort
of
possible
d?
Das
type
situations,
so
they're
very
minor?
If
you
know,
if
it,
the
client
or
the
server,
doesn't
have
it
nobody
sort
of
breaks
or
anything
like
that?
This
is
just
small
tweaks
kind
of
thing.
M
Whoo.
We
put
a
couple
other
things
in
here
that
I,
don't
think
we're
actually
working
on
well.
Client
subnet
is
definitely
the
biz
is
the
one
that
a
lot
of
the
CDN
Jews
and
it
was
very
contentious
when
it
was
in
DNS
X.
This
one
is
definitely
just
an
attempt
to
document
what
the
big
vendors
use,
Google's,
aqua,
etc,
etc
and
I
believe
they're
actually
going
to
try
and
then
go
back
and
think
of
better
ways
of
doing
that.
And
yes,
there's
a
lot
of
privacy
concerns
about
client
subnet.
M
However,
it
does
exist
out
there
and
there
is
it.
There
is
a
usefulness
to
document
what
operationally
exists
today
as
y'all.
Well,
no
next
one,
the
the
top
one,
the
Dena's
terminology
draft
is
it's
a.
It
started
off
with
very
noble
ambitions.
It's
trying
to
actually
collect
all
the
DNS
terms
and
all
the
RFC's
that
exists
today
and
then
try
to
put
in
one
place
and
and
what
we
realized.
What
the
authors
realized
is.
Many
of
the
RFC's
have
incorrect
definitions.
M
First
is
what
are
people
using
today
versus
other
things,
and
so
it's
that
their
first
attempt
is
to
actually
just
document
what
exists
and
then
once
we
get
that
through
the
working
group,
it's
actually
gone
through
working
group
last
call,
but
there's
still
things
that
are
keep
coming
up.
I
think
their
hope
is
it
within
a
year.
They
would
actually
do
a
biz
document
that
actually
tried
to
fix
those
specific
definitions
that
are
considered
contentious
but
I.
M
Think
it's
a
really
good
document,
because
it
puts
everything
in
one
place,
so
I
can
implement
their
trying
to
understand
DNS
hero,
basically
the
classroo
of
all
the
bits
that
that
make
things
work
so
and
then
some
of
these
are
sort
of
definitely
around
DNS
SEC,
bata,
dena
security,
stuff.
The
key
time
draft
I'm,
sort
of
handling
rolling
keys
over
it's
gone
through
a
couple,
different
iterations
and
actually
sitting
in
the
editors
key
right
now
and
the
roadblock
avoidance,
which
is
something
we
did
during
the
hackathon
on
over
the
weekend.
M
M
Oh
yeah,
freaking
person,
okay,
yeah
trust
anchors-
that
one
is
moving
along
as
well,
so
we've
done
a
lot
of
stuff
with
DNS
SEC
a
lot
of
operational
stuff,
because
it's
we've
got
to
start
to
point
that,
but
the
big,
the
big
stuff,
that's
operated,
just
a
pile
of
quicksand
that
you
know
you
should
never
wish
on.
Anyone
is
the
special
use
domains
the
onion
1.
This
is
something
that
the
tour
people
came
to
us
and
they
wanted
us
to
basically
adopt
dot
onion
and
the
only
the
real
reason
they
wanted
it
into.
M
The
special
use
registry
is
because
the
cab
form
will
refuse
to
issue
them
certificates
after
a
certain
date,
unless
the
unless
the
domain
is
either
in
DNS
or
excluded
from
being
in
DNS,
which
is
the
whole
point
of
6761.
That's
like
the
dot
local
stuff
that
Apple
uses
and
stuff
like
that.
But
that's
kicked
off
literally
a
firestorm,
and
if
you
anybody
around
the
IETF
mailing
list
you're
seeing
that
as
we're
going
through
I
ETF
last
call
on
that
we've
had
in
our
meetings
on
it.
M
M
Is
it's
the
wrong
way
to
solve
the
problem
and
so
we're
trying
to
actually
figure
out
the
right
way
to
sort
of
answer
the
right
questions
there,
how
to
sort
of
separate
DNS
from
the
namespace,
because
there's
a
lot
of
requests
coming
in
for
people
who
basically
I
sort
of
maybe
gaming,
the
I
kin
system
and
saying
we
have
this
thing:
that's
sort
of
squatting
in
the
root
zone.
So
we
should
have
it
excluded
at
all
times.
It's
it's
a
just
I,
don't
know
any
other
way
to
say
it,
but
just
a
political
mess.
A
Yeah,
so
thanks
a
lot,
I
think
one
of
the
things
that
I
wanted
to
underscore
in
bringing
this
into
ops
person
opsys
was
that
I'm
rate
of
change
that's
going
on
here,
even
though
its
most
of
them
are
relatively
small,
is
pretty
high,
and
so
some
of
these
things
are
things
that
need
to
be
exposed
outside
the
DNS
op
community.
Some
of
them
are
sort
of
general
interest
to
the
entire
IETF
community,
and
we
can
even
we
don't
even
have
time
to
discuss
in
in
the
DNS
op
working
group
the
overview
of
the
work.
M
B
So,
actually,
during
the
ops
of
an
hour,
please,
we
have
like
a
request
on
the
private
enterprise
number
and
can
come
to
the
mic
there
on
a
draft
tubidy
sponsor
it,
and
actually
we
be
a
good
idea
for
the
update
value
G
to
get
feedback
on
this
one.
So
there
were
no
slide
prepared
because
it
was
like
short-short
timing.
But
if
you
want
to
say
few
words
about,
it
would
be
great.
