►
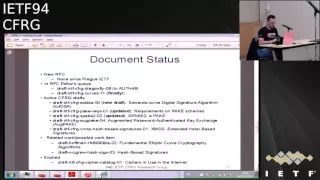
From YouTube: IETF94-CFRG-20151102-1520.webm
Description
CFRG meeting session at IETF94
2015/11/02 1520
A
B
A
Quick
agenda
bashing
any
comments
on
this.
So
I'll
I'll
talk
about
documents,
then
there
would
be
slides
from
Simon
about
Ed
GSA
and
then
there
would
be
one
presentation:
well
actually
two
presentations
and
that
will
have
a
open
discussion
about
what
people
think
chef
reduce
should
be
working
on.
I
know
it's
a
bit
of
a
rat
hole,
but
I
I
think
it's
time
for
to
hear
some
opinions.
Yep
yeah.
B
So
one
thing
to
be
good
to
discuss
is
this
topic
of
the
arm
lifespan
of
algorithms
numbers.
How
many
blocks
you
can
sever
with
them?
So
there's
a
discussion
on
the
list
under
the
arm
with
under
just
saw
and
Watson
and
so
did
other
people
about
openpgp.
But
it's
also
an
issue
for
TLS.
So
right
yeah,
you
know
I'm
referring
to.
C
B
A
A
A
A
David
McGrew
also
updated
the
his
own
draft,
which
we
try
to
accept
as
a
research
group
document
a
year
ago,
but
nothing
happened.
It
expired.
So
I
haven't
looked
at
all
the
changes.
I
think
we'll
need
to
figure
out
whether
we
want
to
have
both
documents
in
the
research
group
all
what
the
status
of
this
is
going
to
be,
and
there
is
also
related
to
work
by
paul
kaufmann
about
fundamentally
CC.
A
A
A
So
for
eg,
eg,
8255,
19
and
the
precast
variant,
they
are
pretty
much
done.
Some
missing
test
vectors
needed
to
be
added,
but
for
the
was
recently
quite
a
big
discussion
on
hash
choices
for
ED
448,
and
there
is
also
some
editorial
work
outstanding,
like
making
sure
that
security
considerations
are
up
to
date
and
that
terminology
is
consistent
with
the
curse
document,
which
is.
A
C
So
I'll
Bryan
Ford
EPFL
I'll
be
the
bad
guy,
but
so
you
know
I
I
don't
have
any
significant.
This
is
fine.
It's
it
just
seems
a
little
crazy,
crazy
and
unnecessary
to
require
two
different.
Oh
sorry,
I
missed
that
that's
shot,
refi
512
for
so
I
write.
My
I
do
remember
my
concern
shot.
35
12
for
the
pre
hash
is
the
thing
that
can
get
that
handles
large,
potentially
large
messages
right.
C
So
I
only
have
a
performance
concern
with
that,
because
sha-3
512
is
operating
the
the
internal
catch
ex
cipher
at
a
kind
of
intentionally
downright
downgraded
performance
level
to
achieve
kind
of
worst
of
all
what
kind
of
absolutely
worst
case
kind
of
security
assumptions
and
that
it
just
seems
unnecessary
to
downgrade
the
performance
like
this.
Well,
it
were
there
any
serious
objections
to
just
using
shake
256
for
both
of
these.
That
was
our
also
proposed.
I.
Think
right.
A
C
C
Yeah
and
so
I,
you
know,
I
mean
there's
nothing
wrong
with
using
shaft
3
512
I'm,
just
a
little
worried
that
you
know.
If
we
just
do
this,
then
you
know
then
I
arm.
You
know
people
will
start
complaining
about
the
performance.
Well,
the
performance
sucks
well
yeah.
Why
does
it
suck
partly
because
we're
running
the
cipher
half
as
efficiently
as
we
could
by
all
all
security
arguments,
that
I'm
aware
of.
H
A
A
I
I
Okay,
those
slides
because
I
don't
have
any
document
yet
I'm.
Writing
a
draft
on
why
it's
bad
idea
to
have
any
mandatory
to
implement
crypto
without
the
crypto
being
any
kind
of
public
review.
We've
seen
a
bunch
of
areas
problem
areas
where
we've
had
a
TLS
extension
for
entropy
dual
drbg
right
there's
calls
to
do.
I
Oh,
we
should
just
adopt
this
newly
nice
little
short
symmetric,
crypto
called
spec
I,
don't
actually
mean
for
there
to
be
an
underlying
thread
to
all
of
these
kinds
of
things,
but
it
just
turns
out
that
those
are
the
three
examples
that
come
to
mind.
So
if
anyone
has
other
examples
of
places
where
we
adopted
for
private
area
crypto-
and
it
turned
out
to
be
really
bad
and
broken
arm
like
to
know
that
there's
other
impacts
on
things
being
patented,
where
it's
hard
to
get
public
review
for
patent
things.
I
So
like
examples
of
that,
and
also
as
an
argument
for
having
crypto
agility
when
we
need
to
swap
something
out
secondary
issue.
Anyhow
contact
me,
you
know
our
souls
at
Akamai,
calm
with
us
all
the
female,
wherever
I'm
easily
found
on
the
mailing
list.
I
just
wanted,
if
any
mall
setting
comments
at
this
point,
I
know
it's
complete
new
thing
but
feel
free
to
catch
me.
You
know
be
here
all
week,
all
that
kind
of
stuff.
A
B
So,
let's
see,
there's
been
some
discussion.
The
mailing
list
of
the
sort
of
lifetime
of
various
kinds
of
ciphers
and
the
relevant
point
here
is
say
you
have
a
system
like
TLS.
You
know
connection
has
very
very
long-lived
on
interaction
and
this
kind
of
probably
any
situation
on
we're
on.
You
have
a
lot
of
data
being
pumped
through
the
system.
How
long
should
you
be
using
the
symmetric
cipher
before
you
decide
to
flip
the
keys
on
this
tip?
This
typically
isn't
actually
with
modern
ciphers
is
an
issue
with
underlying
set
for
construction.
B
It's
an
issue
of
the
fact
that
probably
you're
using
counter
mode
in
counterman
has
certain
properties
on
the
distinguish
it
from
being
on
the
situation
from
a
real
random
number
generator
over
one
period
of
time,
so
I
the
absolute
upper
limit,
at
least
in
that's
an
upper
limit
typically
for
GCM,
is
depending
on
the
date
depending
on
the
structure.
96
296
264
blocks,
I,
guess
it's
a
dad,
so
TLS
is
to
the
64,
because
on
anytime
you
anytime,
you'd
like
a
record
based
protocol
like
TLS
or
IPSec.
B
Typically,
what
you
do
is
you
break
things
up?
So
you
have
a
proper
record
nonce
and
then
you
have
a
counter
inside
the
records
and
a
classical
break
up
is
64
bits
of
the
record
sequence,
number
and
32
bits
for
the
interior
counter
and
so
obvious.
That
means
you
can't
do
more
than
juicy
for
records
because
you
start
the
cycle,
it's
that's
very
serious,
but
on
and
but
as
I
recall,
even
the
even
the
number,
even
the
block
limits
are
much
closer
to
60
for
them
to
the
96.
B
So,
as
I
said,
there
was
some
discussion
on
the
mailing
list
about
this
between
Watson
and
underage.
If
solve
and
I,
don't
think
game
accrues
here
either
on?
But
somehow
we
need
to
resolve
this
because
we
need
to
provide
guidance
applications
for
what
they
ought
to
do
on.
This
is
particularly
relevant
for
TLS,
because
we
actually
remove
the
functionality,
but
let
you
change
keys
and
if
we
need
to
change
keys,
we
want
to
be
able
to
take
care
of
that.
B
It's
not
a
big
deal,
but
if
you
guys
to
know
now,
rather
than
or
later,
but
even
even
for
systems
already
have
key
changing
functionality
on
there.
Basically
is
no
good
guidance.
What
to
do
in
counter
mode
I'm
pleased
to
be
good
constituency
PC
mode,
but
that
is
now
gone.
So
that's
unfortunate,
I,
don't
know
if
anybody
here
feels
qualified
to
talk
about
this
I
feel
almost
qualified
to
talk
about
it.
B
J
J
So
one
of
the
concerns
that
was
raised
was
about
being
able
to
detect
a
potential
attack
is
detect
with
is
to
detect
whether
blocks
are
padded
blocks
or
not,
and
that
the
limit,
maybe
even
if
we
know,
then
that
the
clear
text
is
all
zeros
for
padded
blocks.
Can
you
detect
whether
something
is
an
all
zero
block
or
not
on
the
basis
of
collecting
the
tail
end
of
the
TLS
records
that
have
the
padding
and
and
looking
for
collisions
after
a
certain
space?
B
B
B
B
G
Just
wanted
to
remind
that
the
TLS
the
thread
in
the
TLS
list
about
this
started
by
someone
calculating
how
much
data
you
could
encrypt
with
a
single
key,
and
he
can
omit
the
mistake
of
dividing
by
the
record
length
rather
than
multiplying
by
the
rate
and
got
to
something
that
was
a
lot
of
bites,
but
only
a
lot
of
gigabytes.
Wouldn't
it
should
have
been
several
petabytes
right.
G
B
H
A
D
I'm
Mikiko
cot,
oh
yeah,
I'm
going
to
present
with
a
new
identity
based
authenticated,
X
key
exchange
named
FSU,
and
this
presentation
is
based
on
three
draft.
A
nurse
ride
extract
in
recent
years.
Argument
of
IOT
is
hot.
Talking
idea,
yeah.
It
is
expected
that
from
two
or
three
billion
devices
will
receive
in
2020
ya.
Cryin
client
authentication
is
required
for
the
Provost
oops
transferred
to
an
informational
securing
from
the
best
to
server
to
achieve
crime.
Authentication
jada
need
to
mr
Cochrane
credentialed
in
device
and
server.
Yes,
credential
will
you
know
several
types?
D
Considering
the
use
case
is
operated,
magnesium
document
/
to
/,
psk
based
creditor
and
psk
based
grading,
shall
provide
simple
and
lightweight
protocols.
It
is
expected
expected
to
spread
for
IOT
to
buy
aight
what
you
are
and
just
try
to
show
some
example
and
use
cases
and,
for
example,
1
and
example.
3
and
operators
should
send
change
it
ID
or
Posada,
and
to
the
authentication
pass
Sabha
and
drink.
Those
informations,
for
example,
to
yeah
just
a
table,
simple,
simple
management,
but
jay.
Is
there
a
possibility?
D
D
This
rail
shows
a
development
model
for
our
pk-pk
I
based
grading
sharp.
This
model
is
based
on
that
tapsee.
A
trust
trusted
third-party
pki
based
credential
dissolve
almost
management
costs
over
suicide
authentication,
server
and
mine
in
sabah,
secretive
and
the
public
input
information
for
the
devices
and
likely
subjugate
and
poverty,
and
this
mother
has
advantage
folder
compared
to
the
psk
model,
and
that
is
ed
and
public
key
and
secret
key
was
automatically
generated
to
buy
on
them.
D
D
This
rail
showed
up
deployment
model
for
ID
basic
credential.
This
model
is
based
on,
KGC
is
drafted,
Sal
party
and
at
stake
as
well.
Pkr
best
must
stop
secret
key
and
public
parameters
are
emitted
from
this
image.
In
this
ride,
I
did
unknown
ID
dash,
peas
and
no
information
for
the
factory
Amelia
Tory
we
just
just
that
devices
need
not
generate
secretly.
D
D
Pk
based
credential,
almost
resorbable
deployment,
any
programs
to
Twitter
nonverbal,
credential,
ID,
basic
prudential
hub,
automate,
ma
just
low
cost
of
generations,
sk
+,
PK,
o
device
on
the
factory
and
centralization
of
the
key
generation,
and
that
is
kg
chi
or
a
performed
generation
of
secret
key
ID
champion
at
k,
kg
kg
and
suburb
can
generate
public
key.
Previously,
that
is
say
kg.
She
can
generate
sulk
static
secret
key
previously.
D
D
Disraeli
showed
what
security
mother,
how
no
this
radish
shows
all
of
you
is
if
you
agree
su
key
exchange
protocol
and
master
Paolo,
Ricci
master
public
key
and
public
public
prometi
I
omitted
from
teammates,
also
a
kg.
She
generates.
A
such
a
secret
key
for
initiator
and
a
responder
and
initiator
makes
effeminate
are
tricky
and
sin
and
responded
to
with
initiated
IE
and
apology.
D
D
D
This
security
model
is
most
versatile,
10,
most
strongest
steketee
model
and
against
the
secret
key
wreckage.
Total
55
secret
keys
exist.
If
we
should
prosper,
Christian
key
will
be
self,
even
if
attack
cockade
and
in
any
non-trivial
combination.
Zobel
secret
keys
in
this
sphere
and
combinations
community
denoted
by
circle
are
secure.
Combinations
of
secret
key
wicked.
D
D
177
t3
smart
chain
chain,
this
table
shows
comparison
with
every
cylinder.
Other
ieak
pairing
time
is
total
count
of
sabah
and
r
and
g
side
and
payroll
estimated
are
using
shattering
256
post-rock,
and
you
might
see
that
SEC
is
best.
The
signature,
significant
point
or
basis
is,
if
we
assume
eric,
is
a
security
model.
Next
type
I.
D
D
D
Maintain
of
this
present
age
is
every
few
key
exchange,
but
we
wrote
three
IDs.
This
chart
shows
that
that's
why
we
wrote
three
IDs
Eddie
epic
card
crypt
can
be
divided.
Two
three
layers:
it
ki
khabar
how
to
calculate
how
to
how
to
calculate
scaramouche,
fry
and
signing
method.
Also
pairing
base
to
crypt
can
be
divided,
three
rial
other
a
lot
as
well
of
the
ECC.
D
Now
reaches
a
pairing
graveyard
and
as
well
and
opal
optical,
optimal
rate
appearing
in
today's
fastest
yeah,
fair
enough
I'll
go
is
now
it
computation.
Time
is
about
ten
times
or
more
fast.
As
a
ted
pairing,
you
find
other
bun
Franklin.
Now
apt
car
reaches
bien
Cubs
that
have
128.
We
take
security,
it
is
suitable
for
target
for
parent
next
I.
D
D
K
Hana
Stephanie
I
work
for
armed
and
we
often
get
these
ideas
proposed
to
have
different
ways
to
provision
the
chips
of
some
keying
material
and
the
concerns
that
we
typically
have
around
iprs.
Is
it
any
better
than
existing
schemes
that,
for
example,
with
certificates
that
people
provision
to
devices?
Does
it
make
a
huge
difference?
Because,
often
once
you
start
provisioning
one
piece
of
information,
it
doesn't
matter
whether
it's
one
pit
or
a
5-bit
or
ten
bit.
You
already
start
the
process
anyway,
you
need
to
negotiate.
K
You
need
to
do
all
sorts
of
things,
so
it
depends
on
like
what
you
really
see
as
the
main
benefits
over
an
established
schemes,
and
the
third
thing
is:
there's
obviously
some
uncertainty
regarding
the
security
of
those
provided
schemes.
So
that's
probably
the
reason
why
some
of
the
identity
based
mechanism
haven't
found
widespread
use
and
that's
why
we
used
the
sort
of
classical
public
key
based
approach,
and
we
use
that
in
millions
of
devices
and
we
plan
to
use
those
of
variety.
K
K
K
K
D
A
A
A
A
A
C
One
wants
to
talk
the
Brian
Ford
epfl,
so
I
would
so
I
already
basically
made
this
point
on
the
mailing
list.
I
would
definitely
support
the
suggestion.
Dkg,
I
believe,
made
of
of
looking
into
standardizing
the
way
merkel
trees
work.
It's
you
know,
kind
of
a
very
fundamental,
primitive
used
all
over
the
place
and
inconsistent
and
sometimes
slightly
not
usually
seriously,
but
slightly
broken
ways.
You
know
it
would
be
a
way
to
kind
of
improve
things,
they're
armed
another,
possibly
more
kind
of
far-reaching,
maybe
in
a
distant
thing.
C
I
brought
this
up
in
the
context
of
the
open,
PDP
mailing
list
and
also
posted
a
quick
note
about
it
on
the
HR
PC
list
and
again
I,
don't
know
where
it
belongs.
Maybe
here
maybe
not,
but
the
question
of
in
in
encrypted
data
formats,
where
there
for
data
at
rest
or
data
on
in-flight
in
protocols
kind
of
a
cross-cutting
concern.
C
Can
we
develop
protocols
to
not
leave
so
much
metadata
it
unencrypted
like
magic
numbers
and
protocol
numbers,
and
you
know
unencrypted
negotiation
things
that
basically
tell
attacker
is
exactly
what
kind
of
file
this
is
or
exactly
what
kind
of
packet.
This
is
exactly
how
long
these
TLS
segments
are
exactly
what
version
of
which
protocol
this
is
exactly
which
old,
broken
cipher
like
our
c4.
This
is
this
stream
might
be
using
without
even
making
the
attacker
do
any
bit
of
analysis
to
discover
that
it's
that
it's
a
you
know
old,
broken
cipher.
C
C
F
Stay
in
Paris,
oh
yeah,
I-
think
some
of
that
might
but
probably
big
chunks
of
the
wouldn't.
You
know
how
protocols
used
feels
is
not
particularly
good
for
graphically
related,
but
I
mean
maybe
something
like
you
know.
How
to
mechanism
that
make
sense
for
using
padding
might
make
some
sense.
You
know.
So,
if
we're
adding
padding
to
a
whole
bunch
of
protocols
and
then
maybe
there's
scope
for
people
the
graph
community
to
help
with
figuring
out
how
to
do
that.
J
So,
in
addition
to
so
I
think
traffic
analysis
is
a
place
where
we
don't
have
much
research,
that's
actively
been
done
and
I
don't
know
it's
not
exactly
crypto,
so
I
I
don't
know
whether
people
are
okay
with
that,
but
I
would
we
have
I
think
multiple
times
in
the
last
two
years.
Had
people
come
and
say
here's
a
post
quantum
mechanism,
and
we
basically
said:
please
don't
bother
us
with
that
right
now.
J
B
Ecker
I
would
agree
with
EKG
that
they
post
wanted
to
something
that
useful
to
know
about
I
think
what,
frankly,
would
be
useful
would
be
not
necessarily
perhaps
it'd
be
useful
to
have
a
you
know,
see
frg
recommendation
for
post
quantum
I
strongly
suspect
we're
not
ready
for
that.
Yet
what
would
be
useful
would
be.
A
here
is
a
survey
of
the
state
of
the
art,
and
here
are
the
things
that
we
have.
B
You
know
you
know
if
you
got
Cochrane
reports
right
here,
you're
the
85
postpone
things
who
supported
here
are
the
ones
we
think
probably
work
with.
You
know:
here's
our
level
of
confidence
in
them
and
here's
how
much
they
cost
in
terms
of
various
things
would
be
very
useful
piece
of
paper
to
have
in
heaven
one's
hand
on.
B
You
know
right
now,
I'm
at
the
point
where
you
know
where
I'm
like
I
gotta,
go,
call
somebody
who's
an
expert
and
get
and
get
their
opinion
about
it,
but
a
consensus
document,
the
sort
of
reflected
what
the
feeling
they're
working
group
was
of
how
well
the
post
various
common
things
work
to
be
very
useful.
On
the
other
thing
would
be
useful
would
be
on
some
work
on
the
interaction
of
compression
and
encryption.
So
you
know
work
hunt.
B
B
May
perhaps
the
answer
is
no,
but
we
spent
like
an
enormous
amount
of
mental
effort,
just
getting
H
back
to
work,
and
it
still
has
leakage
on
so
it'd.
Be
really
nice
to
have
some
better
on
perhaps
on
you
know,
has
a
better
threat
model
for
what
for
what
you
actually
thought
about
for
compression
on
some
sort
of
better
security
models.
That
kind
of
it.
J
J
No
worse
than
the
strongest,
yes.
Thank
you
yes,
yeah.
Let's
do
it
that
way,
so
so
people
have
proposed
multiple
combination
approaches
so
that
with
the
idea
being
that
well
maybe
this
post
con
scheme
doesn't
work
out,
but
at
least
you
still
have
the
elliptic
curve
to
fall
back
on
that
op
C
doesn't
protect
you
against
a
quantum
computer,
but
it
would
be
really
bad
if
it
turned
out
that
these
combination
mechanisms
actually
made
things
weaker
than
the
elliptic
curve
stuff
that
they're
trying
to
to
mix
in.
E
Robin
Wilton
from
the
internet
society
again,
this
is
not
one
hundred
percent
crypto
related,
but
something
where
I
think
CFO.
You
might
have
the
expertise
to
give
an
informed
view,
and
it's
above
anonymization
techniques
for
data
seems
to
me
that
a
number
of
those
use
crypto
like
algorithms
or
techniques,
and
increasingly
we
rely
on
third-party
assertions
that
something
has
been
anonymized,
some
guidance
as
to
whether
we
can
trust
those
assertions
and,
if
so,
for
how
long
along
the
lines
of
you
know.
E
G
Hi,
you
have
no,
sir
speaking
as
a
developer
and
writer
of
RF
season
in
the
IETF,
especially
regardless
running
a
post
quantum
cryptography.
There
was
this
publication
by
think
the
NSA
few
months
ago
said
that
we
have
to
start
using
post
quantum
cryptography
and
therefore
you
should
use
shot,
384
and
P
384
for
key
generation
and
signatures,
and
we
were
all
expecting
to
wait
to
have
to
use
totally
new
algorithms.
G
I
Rich
sauce,
Akamai
I
want
to
+1
what
Brian
said
about
Merkel
trees.
It's
used
in
transparent,
get
transparency,
there's
other
proposals
to
use
it
now.
So
it's
like
12
we've
got
a
trend,
so
I
think
it'd
be
easy
for
us
to
write
the
right
guidance
and
it
would
be
ahead
of
the
game
rather
than
after
things
were
already
deployed.
F
A
E
F
I
think
would
be
interesting
because
then
you
know
I,
don't
think
that
there's
not
too
many
of
that
kind
of
group
here
today.
As
far
as
I
know,
maybe
there
maybe
I'm
wrong,
but
so
I
think
I
wouldn't
just
go
on
what
people
are
saying.
I
want
I
want
I
want,
maybe
also
in
those
kind
of
for
a
try
and
get
somebody
to
say.
What
do
you
want
to
give
us
sure.
A
A
B
K
B
Is
even
more
hand
waiting
last
thing,
I
said,
but
one
thing
that
would
actually
be
really
useful
would
be
some
way
to
get
the
people
doing
formal
protocol
verification
involved
in
working
with
us
better.
So
we've
been
doing
with
doing
a
lot
of
that
in
TLS,
working
with
like
the
group
it
in
RIA
and
group
at
Oxford
Mahalo.
Why?
B
B
I
don't,
I
don't
know,
is
less
like
a
working
group
action
items
that
doesn't
make
any
sense,
but-
and
these
people
do
sort
of
have
places
to
publish,
but
if
there
was
some
way
to
make
it
a
better
to
use
this,
to
you
see
if
RG,
together,
better
next
to
fitting
that
community
in
the
community
that
does
the
protocols
line
here.
Let
be
useful.
I
do
not
have
a
good
idea.
Fred
do
that,
but
it'd
be
nice
to
have.
B
F
Sits
yeah,
I
think
that's
good,
that's
kind
of
go
to
the
end,
but
I
mean
one
way.
I
mean
I.
Remember
many
years
ago,
there's
some
some
guys
came
along
with
a
result
of
a
Kerberos
and
people
found
a
very
interesting.
Maybe
in
that
kind
of
case
just
getting
people
to
come
along
to
a
meeting
or
something
would
be
good
nominate
them
for
the
ANR.
Pilars
can
still
open
ours.
K
Question
harness
on
so
there's
there's
some
work
on
these
password
strong
password
based,
authenticated
key
exchange
mechanisms
in
CF
achee.
That
sort
of
relates
to
working
in
the
TLS
working
group
and
I
was
wondering
what
the
appetite
is
orbited
as
a
possibility
to
do
some
different
different
techniques,
standardized
different
mechanisms,
including
dls
psycho
suites,
or
is
that
out
of
question.
K
A
K
A
H
That
so
web
crypto
API
has
a
set
of
algorithms
that
are
being
included
and
one
of
the
requests
we
got
was
to
review
the
recommended
uses
for
those
algorithms,
because
some
of
them
are
being
included
only
for
backward
compatibility
and
are
really
not
recommended
for
use
in
modern
protocol
design.
So
see,
FRG,
review
of
that
document
and
improvement
of
the
review
so
that
in
future,
implementers
have
a
place
to
look
for
best.
Practices
in
using
crypto
algorithms
would
be
very
helpful.
Yeah.
A
I
think
chairs
default
preference
is
to
accept
this
document
and
there
are
a
couple
of
informal
or
there
is
at
least
one
message
of
support.
Well,
it's
message
of
support
and
also
saying
here's
a
lot
of
things
he
need
to
fix,
which
is
which
is
exactly.
We
feel
that
we
need
so
so
that's
another
work
item
for
the
research
group
to
work
on,
hopefully
new
over
in
your
future.
