►
From YouTube: IETF95-TUTORIAL-ARTOVERVIEW-20160403-1300
Description
TUTORIAL meeting session at IETF95
ARTO/VE/RV 2016
A
A
A
Well,
welcome
to
art.
This
is,
of
course
covered
by
they
note.
Well,
we
don't
really
anticipate
having
any
technical
conversations
in
here,
but
if
you
do
go
to
the
microphone
and
start
talking
about
anything
that
has
IPR
implications,
you
need
to
be
aware
of
the
visions
in
BF
c,
p
79,
and
it's
related
things.
You
should
have
seen
this
when
you
registered
and.
B
Really,
if
it's
to
be
discussed,
you
should
be
talking
about
in
the
working
group
later
strip,
alright.
So
what
is
here?
Yes,
what
is
art?
Well
classically?
It's
the
expression
of
creative
ideas
or
creative
expression
through
painting
music
sculpture
also
happens
to
be
the
time
zone,
we're
all
in
right.
Now
the
Argentine
time
zone
is
listed
as
art
and
at
the
ITF.
It's
also
sometimes
referred
to
as
an
area
review
team.
But
the
real
reason
we're
here
is
because
there's
another
definition
and
that's
the
applications
in
real
time.
A
So
what
is
applications?
Real-Time?
Well,
we
basically
cover
sort
of
the
top
half
of
what's
been
traditionally
the
OSI
stack,
we
hit
applications
and
things
all
the
way
down
to
even
handling
some
of
the
transport
for
things
like
media
video
and
audio.
That
kind
of
thing,
it's
kind
of
a
new
area
that
resulted
from
the
merging
of
an
old
r
I,
which
is
real
times,
application
structure,
group
and
an
apps
or
application
dear
a
group,
and
it
covers
protocols
formats
and
that
sort
of
thing
for
applications,
both
real-time
and
non
real-time.
Now,
right
so.
B
Like
we
said
for
apps,
we
cover
infrastructure,
long
snapper
with
application
infrastructure.
So
this
is
a
HTTP
FTP,
smtp,
IMAP,
pop3,
all
the
things
you
would
be
doing
today
to
communicate
whether
it's
email
its
web
pages.
It's
also
the
application.
Oh
gosh
I,
you
know,
I
read
this
stuff,
so
application
infrastructure
stuff
so
like
DNS
labels,
the
EPP
that
we'll
talk
about
later-
and
it's
also
been
more
traditional
building
blocks
things
like
ldap
auth.
Although
OAuth
is
now
actually
in
the
security
group,
it
did
start
in
apps
things
like
JSON
media
types.
A
Now
a
quick
note
on
the
meaning
of
real
time
here
in
in
computer
science,
more
traditionally,
you'll
hear
real
time,
referring
to
things
that
have
like
millisecond
or
sub-millisecond
timing
and
and
guaranteed
execution
time.
That's
not
what
this
is.
This
is
real-time
communications,
which
means
we're
talking
about
exchanging
media
with
enough
latency
that
you
can
have
informal
conversations
over
without
having
you
know
say
over
at
the
end
of
a
transmission,
and
generally
this
means
you
have
round
trip
time
its
media
on
the
order
of
in
milliseconds
or
less
before.
A
We
move
on
to
the
other
sections
of
this
we're
actually
going
to
be
diving
into
the
specific
work.
I
do
want
to
point
out
that
if
you
have
any
question
comment,
etc,
please
come
with
a
microphone
at
that
time.
We'll
have
a
section
at
the
end
professions
and
answers
as
well,
but
it
works
well
in
the
moment
also
and
we're
happy
to
be
interrupted.
Gardy.
B
B
Yeah
so
now
we're
going
to
dive
into
some
of
the
details
here,
we're
going
to
start
with
the
administrative
things
we've
got
in
art.
One
of
the
first
things
you'll
probably
hear
about
is
dispatch.
What
is
dispatch
well
much
like
we
have
protocols
for
routing
data.
We
have
protocols
for
routing
work
in
this
case.
That's
what
the
dispatch
of
working
group
does.
B
A
Of
the
important
notes
to
be
made
about
dispatches
is
not
something
that's
required.
People
can
still
come
in
and
coughs
sponsored
by
area
directors.
You
can,
if
you
know
the
work,
long
specific
working
group,
you
can
take
it
directly
there.
This
is
to
help
people
on
board
work.
It's
not
something.
That's
required
for
incoming
work.
B
So
another
kind
of
administrative
working
group
we
have
in
our
today
is
AB
sock,
and
this
was
the
area
working
group.
This
was
the
working
group
where,
if
you
have
something
that
requires
more
than
simple
ad
sponsorship,
the
ad
doesn't
feel
comfortable
running
it
themselves,
but
it
didn't
look
like
there
was
a
working
group
that
would
fit
and
it
didn't
feel
like
spinning
up
a
new
one.
This
is
where
it
went
so
there's
a
number
of
just
very
small
things
that
are
currently
in
the
in-app
Zog.
B
However,
as
the
slide,
it
mentions
we're
looking
at
click.
That
working
group
is
looking
at
being
closed,
like
with
the
emphasis
on
trying
to
do
smaller.
You
know
working
groups
that
spin
up
get
the
work
done
and
shut
down.
Having
one
general
area
working
group
running,
all
the
time
doesn't
seem
to
fit
that
model
anymore.
So
it's
got
some
things,
it's
finishing
up
and
then
hopefully
be
closing
before
too
long.
A
A
So
the
groups
that
work
on
this
historically,
this
was
all
done
in
one
working
group
called
a
for
audio
video
transport,
but
the
workload
became
somewhat
larger
than
could
be
reasonably
handled
by
a
single
group.
So,
a
few
years
ago
we
broke
that,
apart
into
four
groups,
we
have
a
bt
core
that
works
on
sort
of
the
stuff
that
impacts
the
entire
core
protocol,
for
example
those
work
going
on
right
now
for
multipath
RTP.
A
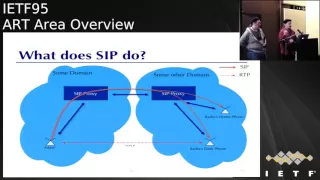
So
that's
how
the
media
gets
from
one
end
to
the
other.
We
also
have
to
be
able
to
set
up
those
media
streams
and
there
are
actually
a
few
different
protocols
that
do
this.
The
one
that
has
received
the
most
work
in
the
ITF
and
this
started
back
in
like
nineteen.
Ninety
seven
is
sip
the
session
initiation
protocol,
and
once
it
does,
is
it
basically,
it
provides
two
fundamental
services.
Let's
say
I
want
to
talk
to
terraria
sip
is
going
to
help
me
get
messages
to
her
device
to
her
phone.
For
example.
This
is
rendezvous.
A
Her
phone
is
going
to
register
with
the
network's
eight
here's
where
I
am,
and
that
allows
me
to
contact
her
server
and
have
messages
routes
to
her.
It
also
performs
negotiation
where
our
endpoints
will
talk
to
each
other
and
determine
what
kind
of
session
we're
going
to
the
voices
video
that
both
is
it
going
to
have.
You
know
which
codex
is
going
to
use
those
sorts
of
things.
What
other
capabilities
the
session
can
have.
A
So
here's
you
know
a
rough
network
diagram
of
how
this
is
typically
deployed.
This
is
going
to
look
an
awful
lot
like
email
to
those
you
familiar
with
that.
We're
like
I,
have
a
home
server
ready
as
a
home
server
and
I
send
stuff
to
my
server.
It
sends
it
her
server
sends
it
to
her
Klein
and
that's
kind
of
the
way
things
end
up.
Getting
set
up.
The
only
real
difference
between
dwai
email
typically
works
in
the
way
that
sip
typically
works
is
with
email.
A
A
So
there
are
a
lot
of
working
groups
that
have
spun
up
and
spun
down
over
time.
Dispatch
came
out
of
the
right
side
of
things,
so
we've
had
a
lot
of
working
groups
that
were
intended
to
be
small
single
purpose
type
things
we
also
have
a
couple
of
long-standing
maintenance
groups
and
music
is
the
great
granddaddy
of
all
this.
A
This
is
the
group
that
originally
developed
sip
and
it
does
multimedia
and
multi
putted
multi-party
multimedia
session
control,
which
right
now
includes
mostly
things
having
to
do
with
a
session
description
protocol
that
we
use
inside
sip
and
WebRTC
and
some
other
technologies.
Sip
core
is
another
long
standard
group
that
works
on
the
core
sip
protocol
itself.
A
So
if
we
want
to
change
something
about
the
way
that
I
think
it's
like
we're
working
right
now
on
how
to
make
it
work
better
over
ipv6,
for
example-
and
there
might
be
some
work
done
on-
you-
know,
dtls
tensions
that
sort
of
stuff
would
end
up
in
sip
for
there.
Also,
a
number
of
these
typically
small
spin
up
do
a
task
spin
down
sort
of
groups
that
are
going
on
right
now,
not
go
through
them.
A
In
a
way
that
can
be
authenticated-
and
this
is
actually
work
that
the
FCC
has
come
to
us
and
asked
to
do.
There
was
a
lot
of
interest
in
making
certain
this
works,
because
now
it
is,
the
public
telephone
network
is
largely
based
on
sip,
and
this
is
key
to
preventing
fraudulent
calls.
This
is
not
just
telemarketing.
These
are
you
know.
A
People
are
actually
delivering
invalid,
caller
ID
for
the
purpose
of
perpetrating
fraud
they're
also
because
these
things
spin
up
and
spin
down
a
lot
of
working
groups
that
are
kind
of
in
their
Twilight
they've,
basically
done
their
work.
You
know
they
have
documents
in
front
of
the
iesg
or
in
the
RFC
I
to
rescue
their
around
to
handle
any
cleanup,
questions
that
might
arise
associated
with
them,
but
they're
basically
done
I'm
not
going
to
go
through
these
I
just
wanted
them
in
the
slide
deck.
A
If
there's
something
up
here
that
someone
wants
to
know
more
about
I'm
happy
to
talk
to
it,
but
because
these
are
basically
going
away,
we're
not
really
going
to
spend
time
on
them.
Okay,
we
also
have
some
working
groups
dealing
with
codex,
which
is
the
way
of
taking
media
and
transforming
it
into
typically
a
compressed
format
that
can
be
stored
or
sent
across
the
network
without
taking
up
too
much
space.
As
you
know,
audio
and
video
would
and
uncompressed
form.
A
Let's
see
these
are
now
vertical
orders.
So
it's
not.
The
seller
is
a
relatively
recent
working
group
that
actually
it's
one
of
the
things
that
I
think
demonstrates
how
dispatch
works.
Well,
we
had
a
group
of
participants
come
into
the
IETF
who
had
previously
not
done
I
HTF
work.
They
just
knew
that
they
had
these
these
formats.
A
They
wanted
to
have
work
done
on
in
the
ITF
and
then
formal
specifications
published
for
them,
so
they
came
in
to
dispatch
and
within
a
relatively
short
period
of
time,
got
a
working
group
and
what
they're
working
on
is
standardizing
a
couple
of
lossless
formats.
Ffb
one
is
a
lossless
video
codec
black
is
the
lossless
audio
codec
and
then
matroska,
which
is
a
container
format
for
storing
these
sorts
of
things
like
on
discs,
as
well
as
the
binding
between
that
container
and
the
protocols
themselves
the
codex
themselves.
A
We
also
have
a
mostly
done
working
group
called
codec.
This
was
the
first
codec
work
we
did
in
the
ICF,
so
the
name
was
codec.
It
developed
a
wideband
audio
codec
called
opus,
where
the
goal
was
to
help
with
something
that
was
state-of-the-art
or
better
and
believed
to
be
royalty
free
and
they
met
the
actually
met
both
of
those
goals.
A
They
met
the
first
goal
with
flying
colors
there's
it's
hard
opus
is
probably
the
best
audio
codec
out
there
right
now
and
at
the
moment
it's
still
believed
by
most
people
to
be
royalty
free,
so
it
met
its
goal.
Net
bc
is
going
on
right
now,
where
the
goal
is
to
do
the
same
sort
of
thing
for
video
codecs,
so
we're
developing
next-generation
video
codec
we're
actually
meeting
this
week
if
you're
in
that
sort
of
thing
come
by
I'm
advertising
it
because
on
the
chair
it
is
a
lot
of
math.
A
It
is
a
lot
of
math,
yes,
sit
down
with
one
of
the
guys
who
are
actually
working
on
the
code
and
they're
more
than
happy
to
explain
this
stuff
to
you,
and
you
will
learn
about
entirely
new
branches
of
mathematics.
You
probably
didn't
know
before
perk,
so
this
one
is
also
close
to
my
heart:
I'm,
not
not
sharing
it,
but
I
think
this
is
some
really
cool
work.
A
That's
going
on
right
now,
so
there's
privacy,
enhanced
communications,
is
what
the
working
group
is
called
and
it
was
chartered
develop
protocol
extensions
to
mostly
RTP
than
the
other
protocols
sort
of
in
that
area
that
allow
multi
party
conferences
to
be
encrypted
and
to
end
and
there's
also
some
work.
That's
going
to
go
on
networking
group
to
show
exactly
how
to
work
that
in
sip,
WebRTC
and
clue,
which
is
one
of
the
working
groups.
I
didn't
really
talk
about
its
telepresence
using
sip
protocols.
A
So,
and
this
really
is
a
simplified
view
of
how
this
all
works.
But
the
general
idea
is
that
we
have
a
key
management
function
that
resides
in
a
trusted
domain
and
it
hands
out
the
encryption
keys
to
all
the
participants
and
they
use
that
to
encrypt
the
media
that
they're
sending
to
each
other.
But
the
conference
server
doesn't
have
access
to
those
keys.
Now
there
are
some
keys
that
the
endpoints
use
with
the
conference
server
to
encrypt
the
parts
that
the
conference
server
needs
to
see
and
then
potentially
change.
A
But
which
you
don't
necessarily
want
to
have
exposed
to
the
world
at
large,
so
why
is
it
important?
Like
I
said
you
have
a
number
of
interesting
architectures
where
the
conference
server
itself
can
reside
in
the
middle
of
a
network
in
potentially
an
untrusted
cloud,
or
that
kind
of
thing,
but
for
enterprise
use
cases,
for
example,
you
might
want
to
have
inside
your
trusted
enterprise
domain.
This
key
management
function
which
ensures
that
the
cloud
service
doesn't
have
access
to.
A
Actually,
a
significant
amount
of
work
needs
to
happen
between
the
web
browsers
and
the
content
that
runs
in
them,
as
well
as
a
lot
of
work
needs
to
happen
between
the
web,
browsers
and
the
network.
So
this
has
been
a
cooperative
effort
between
the
IETF
and
the
w3c
or
the
w3c
is
working
on
the
web
ap
eyes
and
the
IETF
is
working
on
the
stuff
that
goes
across
the
network.
Like
the
social
negotiation
protocols,
stp
the.
C
A
So
I
covered
all
of
this
Oh.
Actually,
the
last
bullets
will
interesting
one.
So
over
the
years
of
dealing
with
sip,
there
have
been
a
number
of
things
that
have
sort
of
developed
as
known
best
practices,
at
least
in
the
IETF
they're,
not
necessarily
well
deployed,
but
the
web
pardesi
effort
incorporated
these
as
mandatory.
So,
for
example,
there's
no
way
to
send
unencrypted
RTP
with
WebRTC
it's
all
encrypted
using
DTLS
srtp.
A
So
you
basically
have
you
know
a
tippy
helmet
handshake
between
the
two
endpoints,
which
means
that
if
there's
someone
in
the
middle
you're
going
to
be
able
to
detect
it-
and
we
also
use
ice,
which
I
said
we
use
for
nat
traversal,
but
it
also
serves
the
important
purpose
of
determining
that.
The
far
end
wants
to
receive
the
media
that
you're
about
to
send
them.
A
Otherwise
you
could
just
start
blasting
UDP
at
arbitrary
people
on
the
network,
and
this
could
easily
be
used
to
build
a
very
effective
browser-based
dido
system,
which
we
didn't
want
to
happen
in
terms
of
adoption
there.
It's
not
standardized
yet
obviously,
but
we're
getting
close,
and
we
have
opera,
firefox
and
chrome
already
have
priests
and
implementations
of
this
and
not
sure.
Well,
you
can
read
that
up
there,
but
edge
on
their
status.
A
B
So
now
we'll
talk
about
some
of
the
things
that
have
been
or
formerly
apps
and
one
of
the
biggest
ones
that
we
have
in
apps
was
HTTP
for
those
that
may
or
may
not
be
familiar
with
that.
What
what
exactly?
It
is?
It's
respect.
It's
a
request
response
protocol,
so
the
client
makes
a
request.
The
server
comes
back
with
a
response.
B
Most
of
this
has
been
handled
by
the
https
working
group,
so
they're
the
ones
that
first
sat
down
and
formalized
HTTP
11
dot.
One
updated
that
for
the
cover
all
the
errata
and
issues
everybody's
found,
they've
also
worked
on
h2,
so
you
can
think
of
h2
HTTP
two
as
taking
the
core
of
the
core
ideas
of
HTTP
one
and
providing
essentially
multiplexing.
So
clients
can
ask
for
multiple
things
at
one
time.
B
If
the
client
asks
for
something
and
the
server
knows
that
that
one
thing
really
you're
going
to
need
for
more
things,
it
could
start
sending
those
to
you
without,
without
obviously
without
direct
pushing
of
it
without
directly
asking
for
it.
It's
also
helped
with
header
compression
so
to
reduce
the
size
of
each
request
response.
B
These
guys
have
also
worked
very
closely
with
the
TLS
working
groups.
There's
a
number
of
things
that,
because
of
how
HTTP
works,
it
would
be
very
helpful
to
have
this
in
TLS
they've
worked
with
the
TLS
working
group
to
get
that
core
protocol
there
and
there's
been
things
that
TLS
is
made
sure
would
play
nice
with
HTTP
when
they've
come
about,
so
the
to
do
work
very
closely
together,
even
if
they're
not.
This
is
one
of
the
same,
so
things
that
do
work
with
or
use
relate
to.
B
Http
we've
got
CD
and
I,
so
this
is
taking
content,
delivery
networks,
that's
the
Occam
eyes
and
the
other
cat
global
caches
and
and
trying
to
find
a
way
that
these
guys
could
talk
together.
That's
what
this
working
group
is
for.
There's
also
web
push,
so
you
could
think
of
this
as
the
kind
of
enabling
the
things
you
get
today
with
a
P&S
and
GCM
for
pushing
data
to
your
phone,
making
that
accessible
for
web
based
applications,
some
more
things
to
deal
with
HP
you're
looking
to
be
like
our
core.
B
So
this
is
iot
over
something
that
looks
an
awful
lot
like
HTTP.
They
are
four
reasons
to
keep
it.
You
know
fitting
within
the
constraints
of
very
small
low
power,
low
memory
devices
they've
taken
some
things
press
even
further
for
their
use
cases.
Although
there
are
some
mapping,
they
are
working
defining
a
mapping
to
http
of
their
of
their
work,
there's
also
skin.
So
you
could
think
of
this
as
user.
B
Some
directories
over
HTTP,
so
this
is
often
used
between,
say
large
organizations
to
populate
a
you
know,
a
cloud
service
with
their
users
and
what
the
groups,
those
users
long
in,
and
help
share
that
data
in
a
relatively
quick
and
searchable
manner.
Then
there's
also
TZ
dist,
which
is
actually
closing
down
this
week.
This
was
time
zones,
so
this
is
past
my
under
each
time
zone
database
files
over
HTTP.
B
The
other
thing
that
we've
also
dealt
with
more
in
our
apps
and
now
art
has
been
data
format.
So
we
heard
some
things
about
data
formats
for
real-time
media,
the
Codex.
Well,
we
have
similar
thing
more
broadly
here:
oftentimes
we're
all
pretty
familiar
with
the
content
like
when
you're,
making
that
HTTP
request
and
that
that
stuff
you
get
back
with
that
content,
you're,
pushing
or
posting
up
work.
Very
quick!
That's
thing
like
JSON!
That's
your
content
types!
That's
your
content,
but
there's
also
other
places,
but
its
context
for
this.
B
So
things
like
saying
our
media
types
or
link
relating
to
language,
there's
also
how
we
identify
how
we
tag
these
things:
the
URLs,
the
paths,
the
domain
labels.
These
are
all
data
formats,
and
these
are
all
things
that
do
get
worked
on
within
art,
one
of
the
biggest
ones
still
around
is
JSON
related
ones.
So,
there's
the
JSON
this
working
group
that
was
taking
the
original
well
now
the
the
standards
track,
7159
and
updating
this
for
fixing
some
errata
and
aligning
better
with
heckman.
B
This
is
the
group
that
actually
defines
JavaScript
the
making
sure
everything
lines
correctly
with
them.
We're
covering
you
could
kind
of
sort
of
think
of
this,
as
what
we've
done
is
the
over
the
wire
stuff
and
they
were
dealing
with
the
the
abstract
understanding
of
what
JSON
is
so
making
sure
these
two
documents
are
in
full
alignment
now
and
going
on.
We
also
building
on
top
of
that
have
geo
JSON.
This
is
representing
geographical
information,
geographical
location
in
JSON
there
some
people
may
be
familiar
with
geo,
JSON
org.
B
That
is
one
that
is
the
most
common
definition
people
have
used.
This
working
group
is
working
on
the
document
or
set
of
documents
to
essentially
ratify
that
as
a
standard
trac
document
in
the
IETF
related
to
these
formats,
we've
got
things
that
are
related
to
language,
so
there
was
pracy
the
preparation
and
comparison
of
international
a
string.
B
So
this
was
a
spiritual
successor
to
string
prep
once
we
realized
that
this
problem
was
even
harder
than
we
all
imagined
and
we
were
realizing,
it's
even
harder
than
we've
imagined
the
second
time
around,
but
the
idea
is,
if
I'm
getting
strings
from
other
places.
How
can
I
see
if
this
matches
something
in
my
database?
Well,
you
could
just
say
well
if
the
octet
Saul
lineup,
but
everybody
types
things
differently,
especially
if
you
have
things
that
you
know
case
differences
and
whatnot.
B
There
need
to
be
a
set
of
rules
to
help
computers
understand
what
human
kind
of
into
intuitively
know
for
their
region
and
Percy
was
one
attempt
to
try
to
get
there.
We
also
have
lager.
This
is
a
working
group,
that's
dealing
with
helping
to
define
what
those
rule
sets
look
like
for
people
that
have
validation
rules.
So
most
common
one
is
usually
DNS
registrar's.
When
you
enter
a
name
there.
How
do
you
know
that
it's
going
to
be
valid
to
use?
Well,
everyone
has
a
different
name.
Has
some
rules?
B
This
is
to
help
define
what
those
rules
are
and
be
able
to
disseminate
that,
and
then
we've
got
slim,
so
the
selection
of
Internet
meet
on
the
the
selection
of
language
for
internet
media.
So
so
far
we've
talked
about.
You
know
what
type
of
things
it
helps
also
understand.
What
is
the
language
being
expressed
here
so,
for
instance,
in
a
audio
video
call
to
be
able
to
say
I'm
going
to
be
speaking
English,
but
someone
so
might
be
speaking
French
and
try
to
collect
that
together
or
the
case
of
email.
B
If
I
could
send
something
already
translated
to
be
able
to
say,
I
have
multiple
translation,
here's
what
the
translations
available
are.
These
are
some
of
the
things
that
are
being
worked
on
that
just
so
we're
not
done
with
formats,
yet
there's
a
few
other
ones
that
are
better
come
that
have
come
in.
So
along
the
lines
of
our
our
small,
fast
working
groups,
we've
got
just
fond.
This
is
defining
what
today
is
usually
application.
B
/Font
dash
blah
trying
to
define
an
actual
top-level
font
media
type.
This
certainly
helps
browsers
to
understand
when
they're
looking
at
content
coming
through.
Is
this
a
font?
And
what
is
the
subdivisions
within
this
font?
What
is
it
open
type
is
a
true
type.
Is
it
WR
woff
what
it?
What
is
the
type?
So
the
idea
here
is
to
find
new
top
level
and
to
automatically
register
a
number
of
ones
that
we
already
know.
B
We've
also
got
calyx,
so
this
is
taking
our
calendaring
and
providing
extensions
to
this,
whether
it's
CalDAV
I
calor,
the
ITP,
I
tip
protocols
and
finally,
we've
also
got
your
end
this.
This
is
defining
what
you
know.
Uniform
resource
names.
Look
like
right.
Most
of
these
documents
today
are
all
informational.
The
goal
of
this
working
group
is
to
try
to
take
those
apply,
the
everything
we've
learned
about
dealing
with
you
our
ends
and
make
that
more
standards
track.
B
Now.
One
thing
that
we've
kind
of
touched
on
well,
we
definitely
have
touched
on,
is
applications
deal
wat
with
security,
whether
it's
real
time,
whether
it's
email,
whether
it's
some
of
our
other
things,
we
have
a
lot
of
things
to
touch,
email,
the
touch,
security
and
so
there's
been
a
especially
in
the
last
couple
of
years
abroad.
Movement
to
me
to
do
more
of
this
work
and
see
how
it
directly
relates
to
applications
being
done
here.
It's
mostly
since
we
are
focused
on
how
we
are
getting
bits
around
it's.
B
It
seemed
to
have
made
sense,
put
these
groups
here
so
groups
like
Utah
or
using
TLS
with
applicant
applications.
They
started
off
by
defining
the
best
practices
of
how
TLS
should
be
applied
to
your
application,
whether
it
be
HTTP,
although
a
lot
of
that
focus
happened
it
to
be
this,
but
also
things
like
XMPP
and
moving
forward.
How
this
relates
to
the
various
pieces
of
email
with
submission,
with
your
submission
servers,
your
eye
maps
and
how
TLS
ought
to
be
applied
there.
You've
also
have
v-mart
what
this
is.
B
My
understanding
of,
though
some
people
here
might
correct
me
here
how
to
know
that,
essentially
how
to
know
that
email
is
coming
from
the
domain
that
it
was
being
delivered
from
and
there's
a
number
of
pieces
here
that
deal
with
if
that
doesn't
match
up.
What
should
I
be
doing
with
this?
Is
this
hard
error?
Is
this
something
I
just
need
the
flag?
Is
it
okay
and
so
there's
the
core
protocol
that's
been
defined,
but
this
working
group
is
spinning
up
to
try
to
deal
with
some
edge
case.
B
Well,
so
not
so,
some
edge
cases
are
actually
fairly
common
things.
The
redirect
what
we,
what
they
call
the
redirect
the
indirect
flows.
Things
like
I
send
to
a
mailing
list.
This
mailing
list
for
words
it
out
to
a
thousand
people.
Well,
that
didn't
come
for
me
directly.
Didn't
come
from
my
email.
Server
directly
came
through
this
mailer.
B
Also
with
it
related
to
security,
is
d
bound
or
domain
boundaries
in
a
nut.
The
primary
question
they
are
trying
to
answer
is:
is
the
administrator
for
a
domain?
Say
food
example?
Calm
is
the
administrator
for
that
the
same
as
example.com
for
a
lot
of
us
would
say.
Well,
yes,
it
turns
out
it's
not
anywhere
near
that
simple.
Traditionally,
we've
used
something
called
the
domain.
Suffix
list
try
to
figure
out
whether
something
where
those
kind
of
administrative
boundaries
existed.
B
However,
that
that
only
helps
for
things
like
the
till
these
the
top-level
domains.
It
doesn't
help
us
in
cases
where
we
may
have
a
hosting
provider.
That
is
allowing
us
to
have
a
name
first,
a
banding
name
under
their
system,
and
are
they
the
ones
that
are
administrative
lyra
sponsible,
for
it
is
the
owner
of
the
subdomain
one
responsible?
Today
we
don't
actually
know
people
take
guesses
and
they're,
usually
wrong.
So
the
idea
what
this
working
group
is
to
try
to
help
define
what
those
boundaries
are,
so
that
clients
can
figure
this
out.
B
The
most
direct
impacts
are
to
web
browsers.
So
things
like
cookies
is
this:
is
it
okay
for
me
to
be
providing
cookies
or
to
accept
cookies
from
these
sites
in
a
related
fashion?
It
might
be
okay
for
food
OCH
example:
coms
cookies
along
there,
it
may
be
okay
for
example.com
if
they're
in
the
same
administrative
zone
they're.
Not
that
could
be
a
leak
of
that
could
be
us
very
serious
privacy
leak
and
possibly
even
other
problems,
the
other
one,
that's
very
important,
is
validating
certificates.
Today
we
match
on
the
whole
name.
B
A
It
did
just
a
real
quick,
I
wanna.
I
want
to
go
ahead
and
plug
be
bound
if
this
problem
sounds
interesting
to
you.
Please
show
up
subscribe
to
the
mailing
list.
Bait.
Go
there
meeting
this
week,
they're
actually
having
a
little
bit
of
difficulty,
making
progress
right
now
and
some
additional
I
balls
and
brains
behind
it,
but
certainly
be
helpful.
Now,
Oh
or.
B
A
B
Another
thing
with
in
art
is
dealing
with
security
is
port
or
the
captive
portal
interaction,
so
we've
just
about
everybody
here
has
traveled,
so
we've
all
experienced
these
captive
portals.
These
are
the
hotel
wireless.
The
internet
cafe
wireless.
These
are
networks
that
are
highly
restricted.
For
instance,
you
can
only
load
a
specific
web
page
until
you've
gone
through
whatever
login
or
Terms
of
Service
Agreement
whatnot
before
they
grant
you
access
threat
to
the
rest
of
the
internet
or
even
a
larger
network
within.
B
However,
today
this
seems
to
work,
but
it
works
because
it
looks
so
much
like
man
and
middle
attack
that
well
it's
madame
el
jack.
It's
there's
no
way
for
us
to
really
truly
tell
if
these,
whether
I'm
talking
to
the
hotel
wireless
to
help
me
get
access
or
if
there
is
somebody
sitting
in
the
middle
trying
to
capture
all
my
traffic
today.
B
Those
look
identical
the
one
of
the
goals
of
this
working
group
is
to
try
to
figure
out
how
we
can
have
those
announcements,
how
clients
can
figure
out
that
they're
connecting
in
such
a
network
and
how
they
can
talk
to
that
Network.
You
know
what
is
the
URL
I
need
to
go
to
to
do
login.
What
are
the
capabilities
of
this
kind
of
network,
these
kinds
of
things?
This
is
also
another
group.
I,
don't
think
they've
made
a
terrible
amount
of
progress.
B
Now
we're
getting
into
some
things
that
don't
all
don't
always
fit
together,
the
more
traditional
things
for
applications
even
before
HTTP
in
some
ways.
So
one
of
these
is
protocols
for
email
right
now,
there's
just
really
one
working
group
other
than
Demark.
That's
imap
append
that
stealing
with
how
making
I
the
append
command
and
imap
work
better
for
uploads
from
clients,
so
that
you
know
right
now,
their
clients
have
to
do
a
lot
of
guessing
whether
file
up
whether
a
message
upload
is
going
to
work
or
not.
