►
From YouTube: IETF96-SIPBRANDY-20160721-1830
Description
SIPBRANDY meeting session at IETF96
2016/07/21 1830
A
Okay,
so
now
we
have
rushing
the
room,
we
can
start
now
it
just
turn
half
past
okay.
So
welcome
to
the
sea
Brandi
working
group.
This
is
our
first
session.
We
were
just
some
charter
a
few
weeks
ago
and
this
is
a
node
node.
Well,
if
you
are
not
familiar
with
it,
please
go
and
read
the
document.
These
node
points
to
so
logistics.
We
need
a
minute
taker,
any
volunteer.
We
only
need
like
high-level
nodes
and
decisions.
A
So
the
agenda
are,
we
gonna
have
two
presentations:
jon
is
going
to
be
presenting
the
bcp
draft
and
Alan
will
be
presenting
the
opportunistic
security
trust
any
agenda
brush,
no
okay.
So
so
before
we
we
go
to
the
presentation,
we
have
a
an
issue
with
the
milestone
to
discuss
so
I'm
going
to
present
it
now.
If
we
can
resolve
it
now,
we
do
it.
A
Otherwise
we
can,
you
know,
revisit
it
at
the
end
of
the
meeting,
so
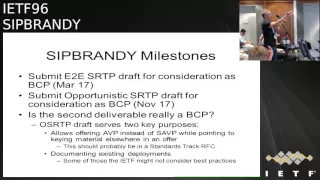
so
these
are
our
milestones,
which
basically,
it's
like
to
submit
the
bcp
draft,
basically
and
then
the
opportunistic
security.
So
the
things
like
the
second
deliverable,
we
mark
it
as
bcp
and
I'm
basically
the
opportunity
security
draft.
Now
it
does
two
things
which
is
basically
offering
secure
all
your
video
profile
instead
of
ya,
been
okay
instead
of
audio
video
profile
and
and
that's
basically,
something
that
is
protocol
mechanism
and
probably
should
be
standard
track,
and
then
it
documents
existing
deployments.
B
A
That's
a
good
point,
so,
basically
yeah
we
were
doing
the
tracker
process.
We
didn't
really
pay
a
lot
of
attention
to
this,
so
it's
good
that
we
we
discuss
it
now
and
so
then
the
question
is
yeah.
Is
it
okay,
so
option
one
would
be
like
you
know,
the
milestones
are
okay
option.
Two
would
be
to
move
the
whole
draft
to
PS
and
option.
A
C
D
C
Or
try
to
get
the
consensus
on
it.
The
issue
again
is
that
if
we
are
going
to
have
the
behavior
that
we're
recommending
as
a
best
practice,
wherever
that's
going
to
live,
incorporate
the
notion
when
you
do
opportunistic
encryption,
you
do
this
thing
with
a
VPS
AVP
they're.
Not
then
that
leap
that
needs
to
live
somewhere.
That
is
at
least
PS.
So
we
can
point
to
that.
Behavior,
no
one
option,
I
didn't
say
in
this
that
I'll
and
I
were
just
discussing
it
out.
C
This
makes
it
any
easier
would
be
just
moving
that
into
the
place
where,
where
we're
going
to
specify
that
normatively
into
my
document
into
the
zipper
and
ERG
piece
set
document
but
I
think
since
L
and
I
was
having
a
kind
of
kind
of
heated
exchange
about
this
before
the
written
group
even
started
in
some
sense,
I
make
sure
people
understand
what
that
specific
technical
issue
is
before
we
talk
about
her
about
it.
Yeah.
E
Yeah
I'm
happy
to
discuss
this
in
as
well,
but
I
think
I
agree
that
the
stuff
about
existing
employments
is
not
really
appropriate.
If
we're
going
to
have
this
in
bcp,
definitely
not
appropriate
if
its
PCP,
even
if
it's
PS
like
it's,
it,
can
muddy
the
waters
as
to
what
the
cases
I
think
splitting
it
somehow
like
wherever
the
pieces
of
land
I.
Think
splitting
it
out
somehow
seems
like
a
good
idea.
Yeah.
F
Alan
Johnson,
my
understanding
when,
when
said
randy
was
chartered
that
we
were
having
two
documents:
one
about
comprehensive
security
and
the
other
about
opportunistic
security
right.
They
are
two
completely
different
approaches
and
you
know
I
think
if,
if
we
stick
with
that
and
if
other
people
have
the
same
expectation
as
I
did
on
that,
that
you
know
that,
will
that
will
work
and
will
we
can
avoid
things
like
number
three
there
I,
don't
think
I,
don't
think
number
one
makes
sense
at
all.
F
Oh
srtp
could
be
PS,
but
if,
if
that
changes,
what
it
says,
then,
then
that's
not
acceptable,
because
opportunistic
security
is
is
what
it
is.
We
have
an
RFC
that
defines
what
it
is
that
had
wide
consensus
here
in
the
IETF
and
and
we're
just
publishing
how
to
do
that
with
srtp.
So
I
don't
think
we
can
decide
this
now,
but
but
we
do
it,
we
should
try
to.
By
the
end
of
the
day
today,
okay.
G
Heard
I
was
actually
going
to
ask
about
or
comment
on
the
milestone
to
the
previous
slide.
Okay
yeah,
this
one
I
didn't
get
it
all,
because
the
opportunistic
srtp
draft
is
really
what
I
would
hope
is
the
least
controversial
and
what
is
already
deployed.
So
I
don't
see
why
that
would
take
a
year
or
more
to
do.
A
G
G
A
C
It's
2017
is
what
it
is:
okay,
so
Andy.
What
one
comment
on
that,
which
is
I,
think
we
understand
bcp
here
in
the
particular
context
of
her
past
being
a
pcp.
In
other
words,
when
we
say
is
your
best
current
practice
and
purp,
as
we
know,
it
is
aspirational
right
in
a
sense
of
there
is
a
current
practice
that
we
think
there's
a
practice
that
we
think
is
best
for
us
currently
and
it
is
treating
pervasive
monitoring
as
a
threat
on
the
internet
and
purpose
was
passed
as
a
bcp
with
that
form.
C
That's
that
is
a
little
bit
different
than
documenting
what
the
reality
is
on
the
ground.
The
round
on
the
ground
is
not
much.
Security
right
looks
like
any
kind
in
any
of
this
stuff,
and
yes,
I
will
utterly
can
see
that
Alan,
like
that,
the
implementations
he's
describing
are
you
know
doing
that
in
places
that
other
things
are
not
then
providing
some
security
in
those
contexts,
but
do
understand
bcp
here
in
those
terms,
in
the
terms
of
there's
a
problem
and
the
best
way,
we
know
how
to
address
that
problem.
C
Welcome
back
to
the
pink
box,
okay,
we're
going
to
talk
about
the
recently
renamed
document,
sip
brandy,
RTP
sec.
Next,
so
Gonzalo
asked
me
to
just
go
over
again
some
of
the
material
that
I
presented
at
the
dispatch
working
group.
That
I
have
some
things
to
say
about
the
new
revision
of
this.
Just
to
make
sure
people
who
are
joining
us
for
the
first
time
get
a
sense
of
what
it
is
that
we're
trying
to
accomplish
here.
C
So
we
want
to
identify
those
best
practices
again
in
that
specific
purpose,
sense,
something
that
will
hopefully
influence
both
implementation
and
or
policy.
One
of
the
really
interesting
side
effects
of
making
something
a
PCP
instead
of
a
PS
potentially
the
most
interesting
side
effect-
is
that
it
is
something
we
can
say
outside
of
the
ITF
represents
the
ITX
consensus.
Call
you
should
do
we
had
a
small
problem
with
network
management
a
couple
years
ago
where
there
was
a
versa
service
providers
who
were
lacking.
C
This
is
one
of
the
points
where
I
were
that
Ellen
and
I
are
feeling
around
right
now.
So
let's
be
clear,
we're
talking
about
that.
What
I
propose
to
do
in
this
document
is
to
very
explicitly
show
to
forking
paths,
I'm,
not
just
going
to
have
like
one
document
that
says,
here's
a
way
to
do
comprehensive
protection
and
then
everything
else
the
Bloods
ever
will.
So
that's
not
the
plan
today,
Ellen
you're
welcome
to
try
to
persuade
us.
C
Otherwise,
if
you
think
that's
that's
inappropriate,
the
idea
now
is
to
have
two
strategies
and
for
the
most
part,
my
document
merely
says
deferred
Allen's
document
for
how
to
implement
the
second
strategy,
and
it's
only
going
to
be
again
in
these
cases
of
what
ends
up
being
like
mandatory
to
implement
like
cipher
Suites,
and
things
like
that.
That
I
think
we
may
have
some
friction
that
we
need
to
work
out
here
today,
but
the
basic
idea
is
we're:
gonna,
try
to
reuse
stuff,
that's
in
stir,
as
we
know,
stir,
is
an
attempt
to
do.
C
An
RFC
was
called
RFC,
4474
piss
again
in
a
slightly
more
tractable
fashion,
some
some
cooler
and
braver
minds
than
myself
injected
themselves
into
this
discussion.
I
think
we
got
a
really
good
place
with
industry
in
this
I
would
call
out.
Chris
went
and
the
great
work
that
he
and
I
have
done
on
passport
and
so
on.
I
could
get
that
into
a
much
more
interesting
shape.
One
of
the
things
it
really
does
better
than
44-second
corpus,
as
if
focuses
on
binding
identities,
two
keys,
that's
really
what
it
does
in
a
way.
I
did.
C
You
know
before
t
%
or
just
had
our
originally
the
4474
had
a
much
broader
scope
of
protection.
It
turned
out
that
that
was
really
just
not
compatible
with
the
way
that
service
providers
were
operating
their
networks.
We
think
this
has
a
much
better
chance
of
just
getting
that
binding
between
identities
and
keys.
C
Sip
limitations
can
now
do
that,
even
though
they
were
not
previously
allowed
to
do
that-
and
this
is
kind
of
think,
the
lynchpin
of
where
Ellen
and
I
are
feeling
around
how
to
organize
this,
and
what
goes
where
so.
My
my
poses
I
at
least
need
to
be
able
to
point
to
something
normatively
and
because
the
way
ITF
specifications
are
structured,
a
bcp
need
to
be
able
to
point
to
something
that
is
at
least
PS
say
that
that's
why?
We
have
these
slides.
F
C
Yeah,
but
that's
telling
you
not
again
I'm
telling
you
to
do
some
specific,
normative
behavior
that
is
allowed.
This
specific
point
again
is
something
that
we
need
a
normative
statement
that
says
that
implementations
can
do
that.
Merely
relaxing
I
mean
we
relax.
I
denne
already
right,
I
mean
it
took
telling
us
not
to
do
something
we
already
are
allowed
not
to
do
is
not
something.
I
need
to
normatively
point
to
that
statement.
That
single
thing
is
the
thing.
That's
different
enough
that
we
need
to
be
able
to
say,
implementations
can
now
do
it
all.
A
F
I'm,
okay,
with
perhaps
with
normatively,
pointing
to
the
opportunistic
security
document.
You
know
when
when
we
open
it
up
and
look
at
it
and
see
what
that
entails,
then
then
it
may
change,
but
I
I
I
disagree
with
the
statement
that
the
only
thing
you
need
from
my
draft
is
that
you
could
offer
a
VP
and
and
still
do
key.
That
is
not
the
only
thing.
F
C
C
C
C
F
H
C
I
wanna
get
through
these
things.
I
just
want
to
make
clear,
though,
that
I
think
one
of
the
elephants
in
the
room
is
is
that
if
the
US
r
QP
draft
is
PS,
it
still
legit,
it
says
you
can
use
s
desk
right,
which
is
something
that
my
document
is
normatively
disallow.
So
I
mean
these
are
the
things
where
I
think
we're
going
to
get
and
again
that
documenting
that
there
is
a
deployment
where
you'll
are
doing.
That
is
reasonable,
provided
its
informational.
It's
not
we're
gonna
be
putting
forward
as
a
standards
document.
I
I
C
At
this
point,
I
think
I'm
still
collecting
requirements
right
now,
again,
I
think
I
am
hearing
acquire
people
wanted.
You
point
to
multipoint,
for
this,
and
perk
would
be
an
example
of
how
to
do
that
and
if
there's
a
best
practice,
we
can
get
consensus
for
I
would
like
to
point
you
in
a
document.
Yes,
okay,.
J
K
One
property
is
on
one
property,
is
the
property
on
the
ellen
alluded
to,
namely
that
you
don't
necessarily
think
at
the
end
at
the
end
points
others,
the
property,
that
you
discover
whether
or
not
the
other
party
is
capable
of
doing
sue,
calm
security
on
but
for
potentially
fall
back
to
know,
security
appear
unable
to
and
so
on.
To
give
you
to
give
you
an
example
of
that.
You
know
we
did
I
think
maybe
apply
some
the
HCP
htp
we
talked
about.
K
K
So
I
think
that
there's
you
know
that
there
are
two
properties
won't
be
interested
in
and
and
and
I
think
they're
distinguishable
and
separate,
and
I
said
I
wanted
to
bait
with
hopper
to
succour,
not
but
I
guess
I
be
I'm,
sorry
interested
buying
the
property,
and
it
seems
to
me
that
that
under
many
conditions
about
you
can't
buy
the
property
that
they
did.
If
you
establish
security,
you
have
an
authenticated
channel,
but
it
may
be
the
case.
K
L
X,
I'm
and
possibly
a
couple
respond
to
this,
maybe
I
mean
so
I
mean
I've.
Extending
that
I
don't
actually
see
a
problem
with
say
having
the
opportunistic
security
grafter
wherever
you
want
to
call,
it
also
might
have
certain
terminology,
say,
must
do
satp,
but
the
bcp
say:
don't
it's
the
other
way
around
I
think
well.
These
are.
L
I
guess
I
mean
I
don't
have
a
problem
early.
I
think.
Maybe
maybe
you
have
to
get
the
2119
language
right,
but
having
one
document
say
you
know,
encourage
you
know,
just
as
you
know,
I
you
know,
I
want
to
fall.
I
know,
I
want
to
use
security
would
fall
back
to
Dale
security
I,
you
know,
I
want
to
use.
Good
security
will
fall
back
the
bad
security
if
necessary,
yeah.
C
C
C
K
On
it,
I
think
Allen's
alluded
that
that
on
the
requirements
are
for
details,
Sgt
provide
and
in
signaling
security,
but
my
reading
the
drafts
as
it
just
he
confirms
about
the
case.
We
of
course
encourage
you
to
do
so,
but
sips
is
I
mean
it's
like,
even
if
you
don't
do
something
it's
kind
of
worthless,
but
on
but
likes
it
but
sips
is
certainly
is.
There
is
certainly
within
the
scope
of
the
rough
yeah.
Of
course,
of
course,
you
know.
We've
already
see
we've
course
not
frightened
is.
It
was
good.
C
A
C
So
I'm
not
going
to
go
into
too
much
of
this
tutorial
information.
Here
we
are
doing
stuff
with
port,
of
course,
NT
for
this.
Basically,
what
stir
creates
an
environment
where
there
is
a
sip
and
Andy
called
an
authentication
service
that
is
responsible
for
assigning
sick
requests
that
creates
that
finding
between
the
identity
and
the
keying
material
in
the
request,
and
that
will
be
caught
by
verification
service
which
will
perform
a
comparable
function.
The
way
that
still
works
that
says
it
can
be
implemented
at
endpoints
are
intermediaries.
C
Typically,
today
and
most
use
cases,
we
see
ferster
people
are
signing
it
at
intermediaries,
so
we
are
going
to
be
doing
something
a
little
different
here,
Thanks
one
of
the
many
headaches
of
the
way
that
stirs
design.
That
makes
this
an
interesting
problem
is
that
stir
only
signed,
sip
requests.
You
cannot
sign
sip
responses
and,
of
course,
the
way
we
typically
think
of
offer
answer
where
you
send
I
an
offer
in
an
invite,
and
you
get
an
answer
in
a
200.
C
Ok,
therefore,
is
not
the
way
we
would
need
to
do
it
if
we
wanted
to
establish
some
kind
of
like
bi-directional
security
association
using
stir.
Instead,
we
need
to
use
something
like
L
wells
of
49
16,
connected
identity,
which
allows
you
to
send
the
SDP,
probably
an
update,
request
after
an
early
provisional,
but
this
creates
a
whole
bunch
of
really
interesting
timing,
tweaks
and
questions
about
exactly
when
the
King
material
becomes
available.
C
Now,
as
we
will
see,
this
is
exacerbated
we're
considering
one
of
the
most
interesting
use
cases
which
is
gate
waiting
to
WebRTC
and
trying
to
get
like
end-to-end
a
TLS
to
work
through
that
I.
Don't
think,
we've
really
ever
tried
to
figure
out
how
that
works
before
now
and
as
we're
looking
at
that
for
the
first
time,
we
recovering
all
kinds
of
attention,
see
interesting
edges
on
next
time,
yeah
so
right,
the
algorithms.
C
Obviously
one
of
the
major
concerns
that
we
have
in
this
in
the
initial
version
of
the
draft
I
indicated
that
that
was
appropriate
for
the
bcp
to
indicate
a
mandatory
to
inspect
our
algorithm.
For
this,
and
let's
face
it
mean
of
things
that
we
have
as
standard
algorithms
here
in
the
ITF,
it
seems
pretty
unlikely.
We
would
do
anything
other
than
DTLS
SP.
C
J
C
J
Ones
know
if
Tess
is
not
really
all
that
much
more
insecure
than
the
other
thing
it
changed.
You
trust
all
the
servers
right
instr,
you
trust
all
the
identity
servers.
It
changes
the
set
of
servers.
You
have
to
trust,
but
there's
set
of
servers.
You
still
have
to
trust.
So
what
I'm
interested
in
is
getting
to.
J
I
want
us
to
get
to
one
thing:
that's
widely
implement.
Okay
and
our
problem
of
having
multiple
options
in
this
has
just
been
a
disaster
from
the
beginning,
so
I
don't
mind
deprecating
SS
as
long
as
we're
getting
to
one
thing,
just
one
thing
right,
so
one
thing
with
some
maize
over
here
or
something
not
working
for
me:
I'm,
not
on
board.
J
If
it's
going
to
be
made
for
other
stuff,
it's
like
do
this,
because
it
introduces
constant
complexity
of
we
have
to
keep
designing
for
all
these
different
systems
that
we
see
over
and
over
again,
and
no
one
really
ends
up
building
any
of
them.
Some
people
build
this.
Some
people
build
that.
We
need
to
be
able
to
say
what
the
ITF
recommends
is.
A
best
practice
is
not
a
may
a
best
practices.
We
it's
either
best
practice
or
not.
May
is
not
the
best
practice
so.
C
Again,
we're
going
to
say
that
we
think
the
best
practice
is
using
duty,
less
srtp,
but
just
as
I
said,
there's
a
kind
of
a
two-pronged
form.
With
this
right,
yeah
I
mean
I
think
we
would
be
doing
the
community
in
the
world
a
disservice
if
there
was
a
significant
implementation
base
of
z,
RQ
p,
and
we
believe
that
it
is
securable
with
these
techniques
and
that
it's
better
than
nothing.
I
have
a
hard
time
seeing
us
really
disallowing,
but
this
please
room
up.
A
J
A
K
Yeah
I,
don't
wanna
sit
on
calls,
are
clarifying
questions
on
our
situation.
We
are
now
talking
about
the
first
draft,
the
bcp
draft,
yes,
and
so
your
proposal
called
I
understand
it
is
to
is
to
have
this
draft
say,
details
sister
DP,
you
must
be
hella
sleepy
and
nothing
else.
It's
going
to
have
some
reference
to
the
or
srtp
draft.
What
do
you
want?
The
content
to
those
are
Pee
draft
to
say,
and
what
do
you
want
this
to
say
about
that
referee?
Wonder
same
internal
transitive,
closure
case
as
I
understand
it
wait.
J
Understanding
the
OSR
PT
draft
is,
it
says,
look
there's
this
a
VPS
AVP
hack
that
you
can
use
for
any
one
of
our
keying
protocols,
yeah
and
any
product
that
wanted
to.
If
you
had
a
product
that
was
only
did
Mikey,
but
you
wanted
to
use
this
a
VPS,
EDP
ack,
you
could
say
hey
I
implement
that
draft
for
mikey
and
it
specifies
it
and
you're
all
nice
and
happy
okay
and
what
I
think
that
the
bcp
says
is
for
whatever
chosen
King
protocol
we
have
which
most
likely
detail
SSR
to
people.
J
C
J
C
A
A
J
F
A
I
Watson
reading
current
document
I
understand
that
you
must
implement
stir
but
don't
use
it
and
you
must
implement
sotp,
btls,
srp
and
use
it
is
that
I,
don't
think
I
think
it
only
says
must
implement.
It
may
be
on
the
terminate
inside
that
you
actually
must
act
as
an
authentication
server
on
the
orange
side.
I
can
only
find
implement.
Also,
I
think
this.
These
are
very
earliest
facts.
Here
I
mean.
C
C
C
In
the
last
section
of
my
document
now
is
that
you
must
implement
the
stirrer
client
endpoint
profile
that
is
defined,
and
it
is
the
intention,
even
if
it
does
not
articulate
a
properly
today,
that
that
means
you
implement
both
the
authentication
service
and
verification
service
functions
in
the
end
point
yeah,
but
implement,
doesn't
mean
necessary
use.
Okay,.
A
C
C
J
C
Okay,
we
can
do
that.
I
mean
what
what
was
clarifying
and
that
this
exchange
for
me
was
again.
It's
people
seem
to
feel
comfortable
with
having
Ellen's
draft
eps
and
be
normally
for
your
reference
for
this
purpose
and
well.
If
we
were
going
to
it
that
whale
and
then
really,
I
will
say
very,
very
little
about
this
other
than
like.
You
know
your
opportunity.
Security
is
what's
in
that
document
over
there
and
if
you
can't
do
this,
do
that,
it's
gonna
have
that
statement,
though
right
as
long
as
you're.
C
A
J
G
F
C
Right,
so
what
I
did
is
your
01
I
think
we're
still
collecting
requirements
as
we
started
talking
about
this
people
here
with
work
in
Ascot?
What
about
multipoint
right?
Well,
should
there
be
some
story
we
have
that
is
going
to
interface
this
with
with
perk
or
something
which
we
do.
What
should
we
say
about
b2b
ways?
C
Largely
we
were
talking
about
endpoint
behavior,
and
this
is
it
worth
having
a
reference
in
there
to
78
79
that
talks
about
ways
to
be
to
be
ways
might
behave
theoretically
in
some
alternate
universe
for
BB
UAE's,
listen
to
ITF
IOC's,
so
we
have
a
couple
of
plugs
in
for
things
like
that.
There's
a
warning
about
sip
rack
and
about
the
fact
that,
basically,
you
know,
if
you
send
this
meeting
to
an
end
point
that
can
decrypt
it.
C
C
J
So
I,
it
just
seems
to
me
that,
though,
solving
a
conferencing
situation
be
highly
desirable,
we're
still
very
early
on
that
stage.
We
don't
know
what
we're
doing
yet
and
I.
I
would
rather
I'd
rather
see
this
proceed
with
just
making
the
stuff
that
we
know
well
work
and
worry
about
the
type
of
perk
situations
a
little
bit
farther
down
the
road.
So.
A
J
C
K
So
I
I
always
go
out
so
yeah
I
mean
I
generally
agree
calling
on
this
per
point.
I'm.
No
one
is
more
enthusiastic
about
perk
than
me.
Well,
maybe
someone
is
but
I'm
gonna
give
you
a
fun
but
on
I'm
actually
more
concerned,
but
the
milestone
cases
that
I
think
it's
reasonably
like
the
purple
not
be
finished
by
the
time.
So
I
I'm
happy.
If
we
can
find
some
women
we've
induction
of
pork
and
how
it's
like
all
something
we
should
be
doing.
K
I'm
like
totally
happy
to
do
that,
but
I
don't
want
to
do
is
be
happy.
You
know
that
you
know
March
or
whatever
it
is
have
it
be
like
work
isn't
done
yet
and
now
we're
like
just
stuck
sitting
behind
it
right,
that's
apartment
hard
to
avoid.
So
if
there's
some
way
to
thread
that
needle
I'm
perfectly
happy
with
it,
but
that's
I
think
my
guess
is:
Brooke
won't
really
be
done
for
another
year
or
so.
Okay,
okay,
Andy.
G
So
so
I'm
now
just
express
a
little
bit
more
caution
on
that
I
think.
Actually,
there
is
some
tight
coupling
between
this
and
perk,
at
least
in
that,
as
far
as
I
sip
endpoints,
because
then
it
has
to
be
able
to
initiate
both
without
knowing
prior
knowledge
of
what
recession
is
going
to
be,
whether
it's
gonna
be
a
multi-party
Oh
point-to-point.
A
G
A
G
E
I
spent
a
bunch
of
time
in
boss
this
week
and
I
think
we
have
a
clear,
well
scope
problem
here
with
just
covering
point-to-point
like
I.
Think
perk
is
significantly
different
enough,
that
it
makes
sense
to
handle
it
separately
if
we
need
to
handle
it
separately
like
if
it
logistically
works,
put
it
together.
Fine,
we
can
put
it
together,
but
I,
don't
think
it's
a
big
deal
to
treat
them
separately
either.
I
think
we
can
do
this
in
park
and
you
know
take
whatever
solution.
E
We
do
there
and
anoints
it
as
as
bcp
later
and
cover
that
case
in
and
to
the
point
about
sip,
endpoints
I
think
it's
actually
completely
within
the
realm
of
the
design
space
right
now
that
there
wouldn't
be
actually
that
much
difference
between
what
we
would
be
proposing
here
and
what
you
would
do
in
dude
from
the
end
point
perspective
to
do
part
so
I
think
there
may
not
actually
be
that
much
too
24
perk.
Ultimately,
it
may
just
be.
You
know,
go
over
and
do
this
thing
over
here:
okay,.
I
C
C
A
C
Flipboard
again
thanks
right,
so
we
are
starting
to
build
what
is
effectively
a
profile,
I
think
for
using
stir
where
we
assume
that
endpoints
reacting
is
both
the
authentication
service
and
the
verification
service,
the
hard
edge
on
that,
of
course,
is
getting
certs,
and
so
we
have
some
text
about
that.
Now.
C
I
guess
I
am
now
starting
to
sketch
out
in
my
head
what
the
acme
use
case
for
this
looks
like
both
for
using
an
acme
task
to
acquire
a
cert
for
a
telephone
number
and
four
green
fields
of
your
eyes,
and
that's
probably
not
work
that
we're
gonna
complete
in
the
scope
of
this
timeline
either
so
yeah,
we're
not
going
to
argos
will
be
done
in
acting
yeah,
so
I
mean
is
a
consequence.
We're
gonna
have
to
figure
out
from
aspect
friendship
perspective.
C
How
we're
going
to
approach
that
right
now,
I
think
we're
just
we're
just
saying:
there's
going
to
be
a
way
that
they're
gonna
be
able
to
get
certs.
One
way
we
are
in
described
next
slide
is
basically
using
some
kind
of
a
self-signed
sir,
and
this
is
what
I'm
saying
is
like
I'm,
the
opportunistic
approach
to
stir
where
you'll
have
a
you
know,
a
self-signed
Keith
who
at
least
give
you
trust
on
first
youth
kind
of
properties,
and
that's
that's
the
only
benefit
to
this
that
goes
beyond
you
know,
just
doing
nothing
at
all.
So.
C
L
C
D
C
Well,
we
would
have
to
go
through
and
specify
what
exactly
is
before
the
TN
cert,
especially
that
would
that
would
be
complex,
but
we'll
do
it
I'll.
Do
it
right
next,
I,
don't
you
wanna
get
down
slides,
I
know
one
of
the
things
that's
come
through.
That
scare
me.
This
is
that
we
are,
for
the
first
time
trying
to
figure
out
really
how
to
align
the
and
n
security
model,
potentially
even
gateway
between
web
urgency
and
&
M
sep
on
this.
This
is
the
first
time
I.
Think
we've
really
taken
a
hard
look
at
that.
C
That's
why
you
know
how
Adam
wasn't
it
raised
said
I'm
here?
Oh
yes,
I
see,
consent
right
as
a
good
example
of
something
that
we've
never
really
had
a
place
in
sit
where
we
asked
you
to
do
I
style
consent,
as
we
do
in
where
Ricky
see,
and
it
does
seem
to
belong
here
so
getting
the
timing
of
consent
and
ice
and
connected
identity.
You
know
in
the
keying
that
comes
in
these
different
places
in
stp,
potentially
that
wooden
web
RTC.
That's
an
interaction
we
need
to
study
and
we
make
sure
it's
right
I'm.
C
Having
some
conversations
with
mt
about
that
to
make
sure
that
we
get
that
lockdown
I,
don't
we
aren't
seeing
I
think
any
showstoppers,
it's
it's.
You
know,
I
I,
don't
think.
There's
real
problem,
but
I
do
want
to
make
sure
we
really
understand
that
and
that
we
have
a
plausible
story
about
how
this
work
with
existing
web
RTC,
implementations
or
potentially,
if
you
know
there
needs
to
be
some
kind
of
a
delta
good.
So
what
do
you
guys
think
I
mean
given
roughly
what
we're
discussing
here
is
this.
C
You
know
I,
don't
know,
given
how
the
discussion
is
gone.
If
we
want
to
talk
about
adoption
of
items
yet
definitely
use
more
eyeballs
I've
been
glad
to
get
a
fair
amount
of
eyeballs
in
the
spec.
Already,
though,
not
much
less
discussion
I
want
to
make
sure.
There's
no
require
sir
missing
right.
Things
like
the
perk
thing
came
up
and
we're
now
going
to
take
that
off
the
plate.
That's
cool
I
suspect
there
could
be
other
kind
of
education
as
a
corner
cases.
C
K
So
afternet
I
haven't
read
the
lady
first
draft,
so
I
care.
If
it's
in
here
but
on
you,
you
mentioned
you've,
been
mentioning
sort
of
outside
for
sweets,
ciphers
whatever,
but
I
mean
the
relevant
question.
I.
Think
inside
of
dtls
is
what's
what
separates
you
require
details,
I
30
p.
So
where
did
you
already
have
some
requirements?
I
assume
we
simply
import
those
yeah
good.
C
K
K
D
C
D
A
B
C
F
Ok,
I'm
going
to
talk
about
the
opportunistic
srtp
draft
on
behalf
of
Bernard
Andy,
Laura
and
Thomas
next
slide.
Oh
just
just
a
note
about
the
motivation
for
this
sum,
which
has
been
talked
about,
one
thing
is
documenting
existing
practice.
What
used
to
be
known
as
best
effort
srtp
another
is,
though,
the
the
needs
of
the
SIP
forum,
their
sip
connect,
sip
trunking
recommendation
currently
is
all
clear
text
and
we
desperately
would
like
to
introduce
srtp
encryption
and
the
only
way
to
do
that
is
to
do
it.
Opportunistically
and
of
course.
F
F
So
this
is
just
reiterating
the
definition
in
RFC
7435
and
our
charter
does
reference
RFC
7345
by
name.
So
this
is
our
definition
of
what
opportunistic
security
is.
Okay,
thank
you,
okay.
So
the
approach
has
been
a
we've
talked
about
this
already
here.
Basically,
it's
offering
AVP,
but
upgrading
essentially
you
know
doing
doing
secure
if
you
possibly
can
and
and
never
failing.
F
If
you
can't
that's
the
basic
approach
and
it's
it's
not
specific
to
any
to
any
keying
method,
and
the
draft
right
now
talks
about
three
of
them:
DTLS
stp
security
descriptions
or
esta
as
its
informally
called
and
Zed
RTP.
Now
the
current
version
of
the
draft
is
informational,
so
it
just
says
here:
are
you
know
here
they
are,
and
it
gives
some
examples.
If
we're
changing
it
to
proposed,
then
you
know
we
can
do
things
a
little
differently.
F
C
C
C
F
F
J
F
Yeah
I
mean
I
would
prefer
to
keep
them
in,
because
I
hate
drafts,
where
you
know
it's
all.
You
know,
there's
no
examples
and,
and
the
like,
so
I
would
prefer
to
keep
them
in.
The
other
point
is
about
their
relaxing
the
authentication
requirements.
I
tried
to
make
that
point
with
DTLS
and
failed.
I
think,
due
to
terminology
I'll
try
another
example
you're
doing
a
dtls,
srtp
handshake
and
you
fail
to
get
a
fingerprint
or
for
the
fingerprint
all
you've
got,
is
an
md5
hash
to
compare
it
with
now
in
a
comprehensive
security
mode.
F
K
I'm
trying
to
argue,
I
don't
mean
to
be
arguing
but
I'm
put
the
example
in
d5
was
a
fantastic
example:
the
not
get
a
fingerprint
I,
don't
the
wait.
I
thought
that
getting
the
fingerprint
was
how
you
need
for
us
to
do.
Dtls
ons
I
think
that
that
that
part
airline
wouldn't
work
also
confused
or
wrong.
K
Um-Hmm
III
wanna
I,
don't
argue,
but
I
want
to
put
a
pin
in
it.
Cuz
I
think
that
I'm
wondering
if
that's
actually,
if
that's
active,
if
that's
a
done
thing
for
the
world,
then
feeling
what
sort
of
basic
attacks
you
to
fail.
Beef,
I
think
I
think,
is
right,
but
I
worry
that
I
think
the
long
finger
print
it's
like
well,
something
is
basically
busted
on
your
in
and
maybe
you
should
go
fix
it
rather
than
try
to
try
to
find
sure
yeah.
D
Come
back,
I
think
it
is
necessary
because
of
the
user
experience,
if
you
call
somebody
who
doesn't
support
any
srtp
method
and
you
simply
cut
get
hang
up,
you
don't
know
what's
wrong
and
we
get
the
code
so
right
and
in
this
mode
you
can
signal
to
the
user.
Okay.
This
is
a
connection,
but
it's
not
secure.
So.
D
K
This
is
I
think
this
is
fantastic.
I
think,
there's
like
you're
a
playwright
is
the
only
way
to
deploy
security
in
the
current
environment.
I
guess
on
the
philosophical
question
I
think
we
will
be
asking
ourselves
in
that
mud
huts
on
this
is
as
I
sort
of
neutral.
Is
that
there's
there's
like
things
which,
like
there's
like
the
guy,
didn't
didn't
support?
What
I
wanted
to
do,
and
so
that's
fantastic.
K
The
thing
that
you
wanted
the
support,
but
they
actually
feel
too,
but
it's
worth
trying
to
be
compensate
for
this
guy's
or
if
it's
like
basic
is
people
were
doing
they
don't
and
and
then,
if
you
cling
to
it
doesn't
work
they
like
a
screws,
yes
I'm,
just
like
I'm
a
fighter,
so
I
love.
You
get
thoughts
on
that
yeah.
F
L
Linux,
so
I
mean,
I
think,
that
you
know
particularly
the
CRT
PKS
and
ZEB
handshake
fails
I
mean
the
guy
thinks
you're
doing
z
RTP.
If
he's
do.
If
this
year
there
was
zero,
DB
handshake
so
trying
to
play
back
his
audio
as
g.711
is
probably
not
a
good
idea.
I
guess
you
could
send
a
reinvite
without
the
CRT
p
in
hopes
that
maybe
got
a
middle
box
of
trying
to
transcode
his
know.
F
F
L
F
L
L
K
I'm
thinking
that
you
have
consistency
at
both
ends
but
John
than
John
makes
a
good
point
which
other
cases
where
for
any
of
these
cryptic
handshake
protocols,
work
where
the
last
guy
to
speak,
fix
it
worked
and
he
screws
up.
I
thinks
it
didn't
work
and
so
I
wonder
like,
and
so
at
that
point
you
basically
have
two
choices,
which
is
to
try
to
recover
what
I
felt
a
call
right,
yeah.
So.
F
L
D
A
H
Realized
about
the
overall
pressure
in
the
details,
so
one
thing
that
I've
seen
systems
do
differently
than
this.
Is
that
precisely
about
Jonathan's
point
about
mismatch
between
expectation
of
security,
you
offer
a
VP
along
with
some
keys,
but
then
you
answer
svb.
If
you're
expecting
to
do
security,
because
you
think
is,
the
answer
should
have
a
good
idea
of
both
sides
are
going
to
be
ready
to
do
security,
whereas
in
your
case
your
answer
with
a
vp,
regardless
of
whether
you're
going
to
try
it
or
not,
it
seems
a
little
bit
more
ambiguous
yeah.
F
K
K
So
it's
the
reason
that
that's
that's
unfortunate
because
on
motor
seized
currently
requiring
exactly
the
opposite
approach,
so
maybe
maybe
you
could
sense
a
male
look
that
the
ark
you
have
less
saying
that
were
idiots
because
we
actually
require
you
to
send
the
right
thing.
The
denominator
aight
thing.
So
if
you
said
re,
rt-pa
vpf,
when
we
require
to
send
you
to
eat
blah
blah
blah
UDP
TLS
blah
blah.
So
so
so
maybe
you
could
sense.
Another
list
telling
us
for
morals,
yeah.
N
F
An
example:
let's
get
that
another
example
changes
yeah
go
go
back
to
what
ok,
so
it
has
an
applica
bility
statement.
Well,
we
can,
we
can
wordsmith
it.
Basically,
it
says,
do
comprehensive
unless
you
know
you're
trying
to
transition
existing
stuff,
and
it
has
a
mission
of
cap
neg
now,
but
it
says,
doesn't,
doesn't
help
because
we
don't
do
it
anyway.
So
I
think
that's
storrington,
ok,
yeah,
so
because
there
Mikey
modes
that
it
won't
work.
F
That's
that's
what
your
time
I
don't
know
enough
about
my
key
to
say:
yes,
there
probably
is
good.
There
are
so
many
to
choose
from
yes,
okay,
so
yeah.
So
the
only
question
is
you
know
right
now
the
draft
is
written
as
if
it's
informational
right
but
I,
think
it
could.
We
could
just
change
it
to
PS
and
I.
Don't
think
we
have
to
change
anything
yeah
in.
What's.
A
P
D
A
P
Is
there
was
a
problem
just
re-read
Allen's
draft,
while
we
were
sitting
here
I,
don't
think
that
the
the
split
the
split
you
describe
where
you
just
take
any
normative
text
out
is
not
this
flip.
It
was
proposed
to
being
in
the
front
either
and
I
also
don't
think
it'll
work
with
the
document.
So
if
you
skim
it
real
fast
you'll
see
how
that
breaks.
I
thought
I
heard
some
consensus
building
towards
just
leaving
the
text
in
the
document.
P
As
is
it
looks
like
things
work
with
it,
we
can
reference
it
make
it
PS
if
we're
only
making
it
PS
so
that
we
have
a
normative
reference
to
it
without
doing
some
sort
of
dance
in
the
IETF
I.
Don't
care
I,
just
assume,
leave
it
informational
and
just
call
it
out
as
it
down
Raph
when
we
send
it
up.
I
don't
have
an
opinion
on
that
soon.
Right.
B
I'm
been
the
big
gamble
again,
reminding
that
the
Charter
has
comments
to
say
about
doing
standards
work.
Here
again
we
can
fix
that,
but
we
need
to
think
about
how
we
want
to
do
that.
Roberts
solution
is
well,
it's
kind
of
a
workaround
to
the
Charter,
but
it
seems
to
work
around
it.
Oh
a
wet
solution
to
do
it
PS.
B
C
B
J
A
K
Perfectly
comfortable
with
this
being
PS
and
having
and
just
fixing
the
Charter
thing
that
says,
we
can't
update
our
music.
If,
for
some
reason,
that's
like
impossible,
then
I
guess
we
can
like
take
the
two
lines
and
put
it
where
else,
but
like
that
just
seems
kind
of
silly
frankly.
So
right
I
proceeded
to
make
this
PS
and
let
the
area
directors
direct
as
they
were
supposed
yeah.
L
I
some
two
things:
first,
I,
don't
exactly
know
where
this
would
fit
in,
but
I
said
I
would
rely
for
Joe
Joe
Hall,
who
had
to
leave
early
said
I
have
to
leave
early
I'd
like
to
preemptively
hum
no
to
Estes.
Sorry.
The
goal
here
is
to
avoid
PMI
feel
estes.
Contrary
to
that,
I
don't
know
exactly
how
that
fits.
It
was
a
good
discussion,
but
I
said
I'd
relay
it.
Okay,
mom.
The
the
other
point
I'd
make
is
I,
think
what
this
is
actually
updating.
L
C
Yeah
I
mean
to
the
M
music
thing:
I
mean
the
problem
is
I
suspect
there
are
going
to
be
a
couple
things.
We're
gonna
have
to
go
to
em
music
for
right,
and
so,
if
we're
going
to
do,
can
send
and
that
like
needs
to
go
to
music,
and
it
could
turn
out
that
what
they're
actually
like
a
shadow
overall,
I'm
using
this
one
I
just
hadn't
considered
before,
but
the
thinking
about
doing
consent.
C
D
D
I
C
Is
the
M
music
ice
sdp
draft
I?
Think,
though,
that
is
where
this
stuff
needs
to
at
least
that's
the
traffic
only
craft
I
know,
of
course,
some
of
this
stuff
was
today
so
I
mean
it's
like.
If
that
belongs
there,
then
the
consent
stuff
belongs
for
that
belongs,
and
so
you
could
make
an
argument
that
what
we
need
is
some
have
musics
back
that
shadows.
Any
standards
track
changes
that
we're
making
testp
here
right.
A
A
H
D
A
Good
perfect,
so
now
I
mean
we
are
finishing
the
session.
It
seems
that
we
have
kind
of
a
clear
way
forward.
So
the
only
thing
we
have
to
do
now
is
to
decide
to
take
these
two
drafts
as
working
group
items,
so
I'm
going
to
take
hands
on
both
threads
so
who
is
in
favor
of
taking
the
Jones
trapped,
the
bcp
draft
as
a
working
group
item
for
our
milestone.
Please
hum
anyone
opposed
anyone
opposed.
Okay,
that's
unanimous
for
a
note
taker!
A
N
So
strong
consensus
that
it
was
at
least
one
day,
New
York
there's
at
least
one
hung
in
the
chat
room,
although
I
would
just
say
to
people
who
are
remote
if
you're
gonna
say
hum
SE
hum
yes
or
hum
no
or
something
I
said
humming
favor
and
opposed
alright
I
understand
it's,
the
lag
people
go
and
they
just
say
hum.
But
then
you
have
no
clue
what
they're
actually
heyeayeayea.
D
N
A
So
and
the
next
one
is
taking
Alan
threat
forever.
Our
second
milestone,
so
everybody
in
favor,
please
ham.
Now
anyone
opposed
okay,
perfect.
So
please,
if
you
guys,
can
submit
the
both
drafts,
as
working
group
items
of
the
group
I'll
be
happy
to
approve
them
as
as
soon
as
I
get
them.
So.
Thank
you.
Yes,
one
last
comment
so.
